Evidence-Based Analysis of Cyber Attacks to Security Monitored Distributed Energy Resources
Abstract
1. Introduction
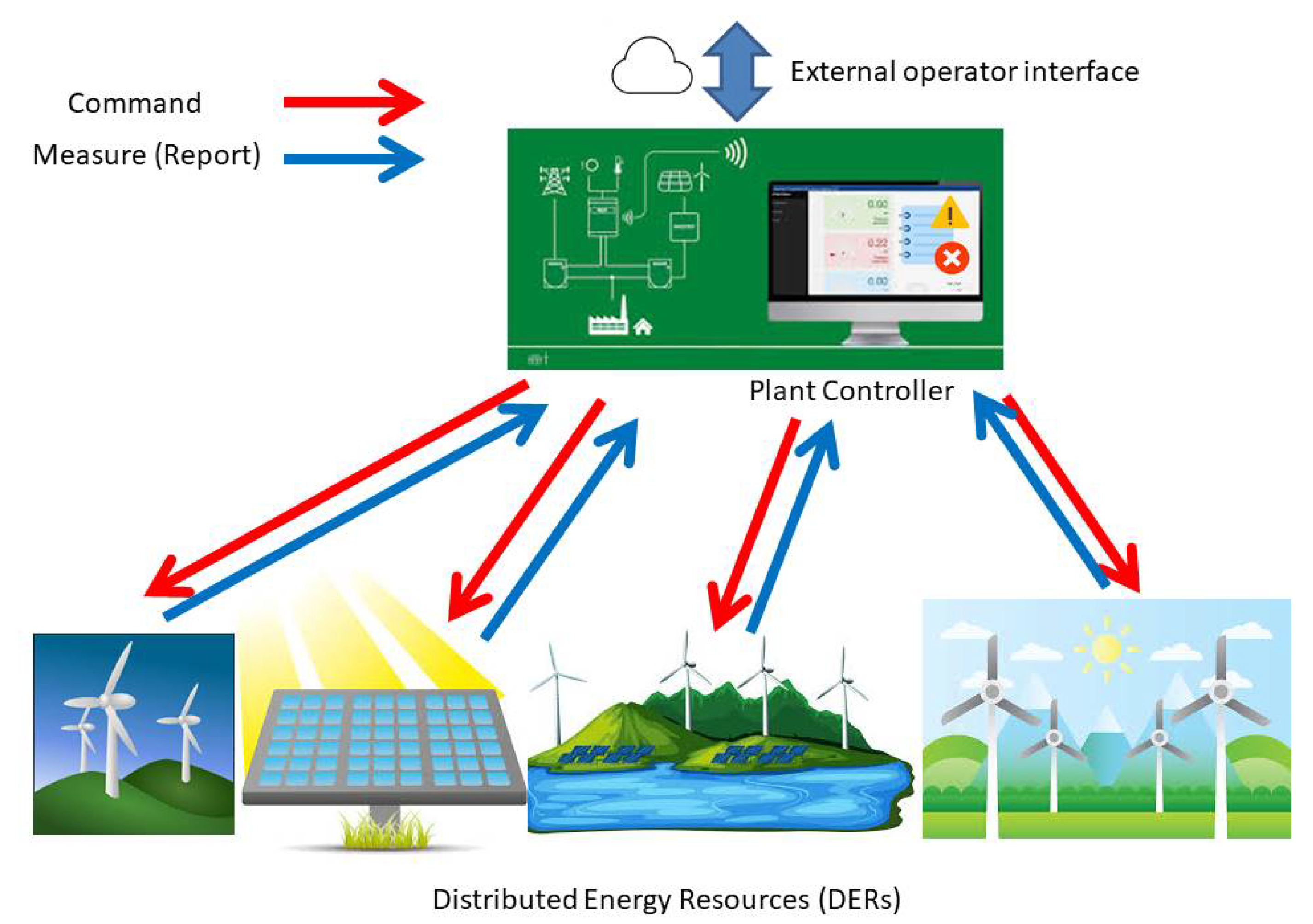
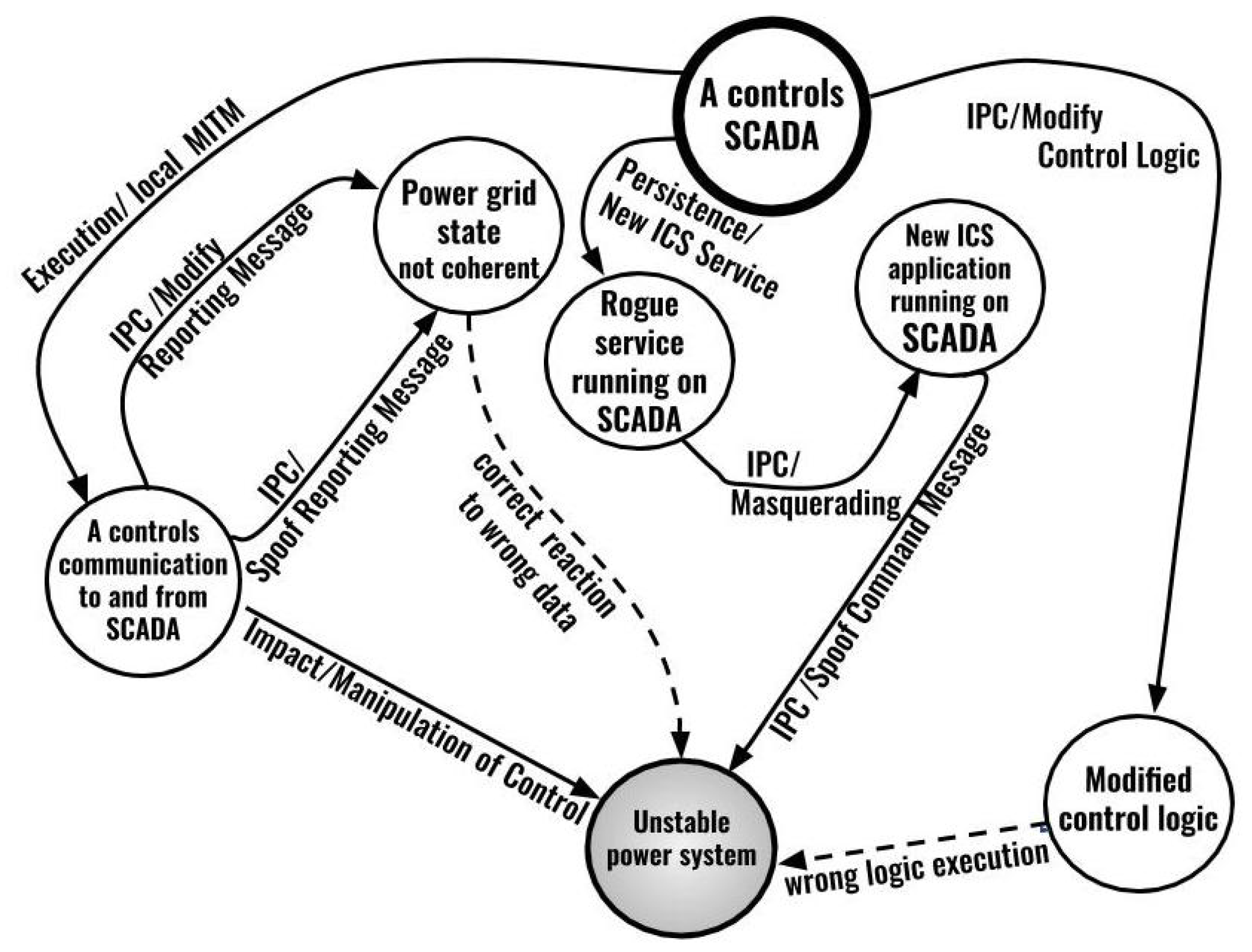
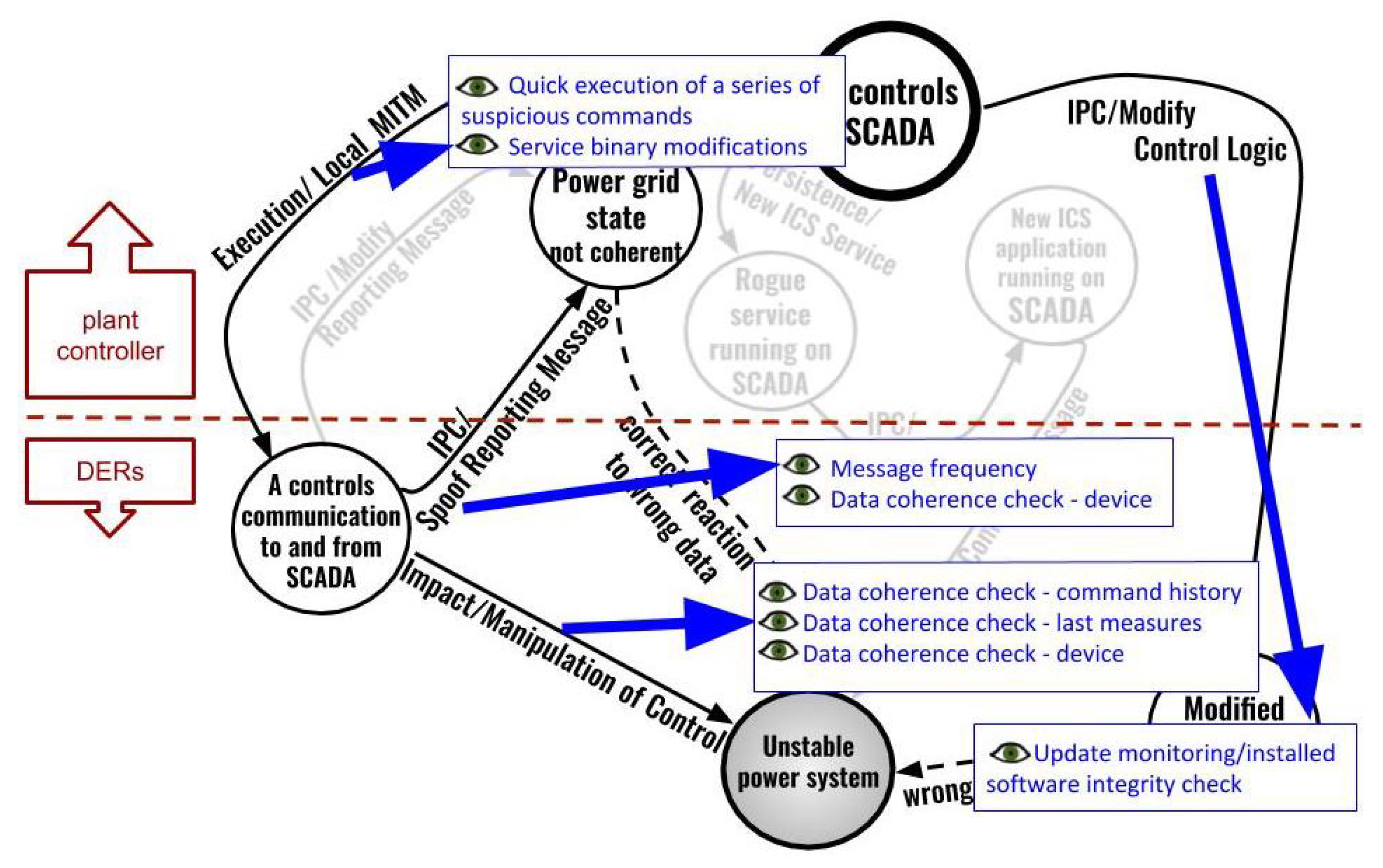
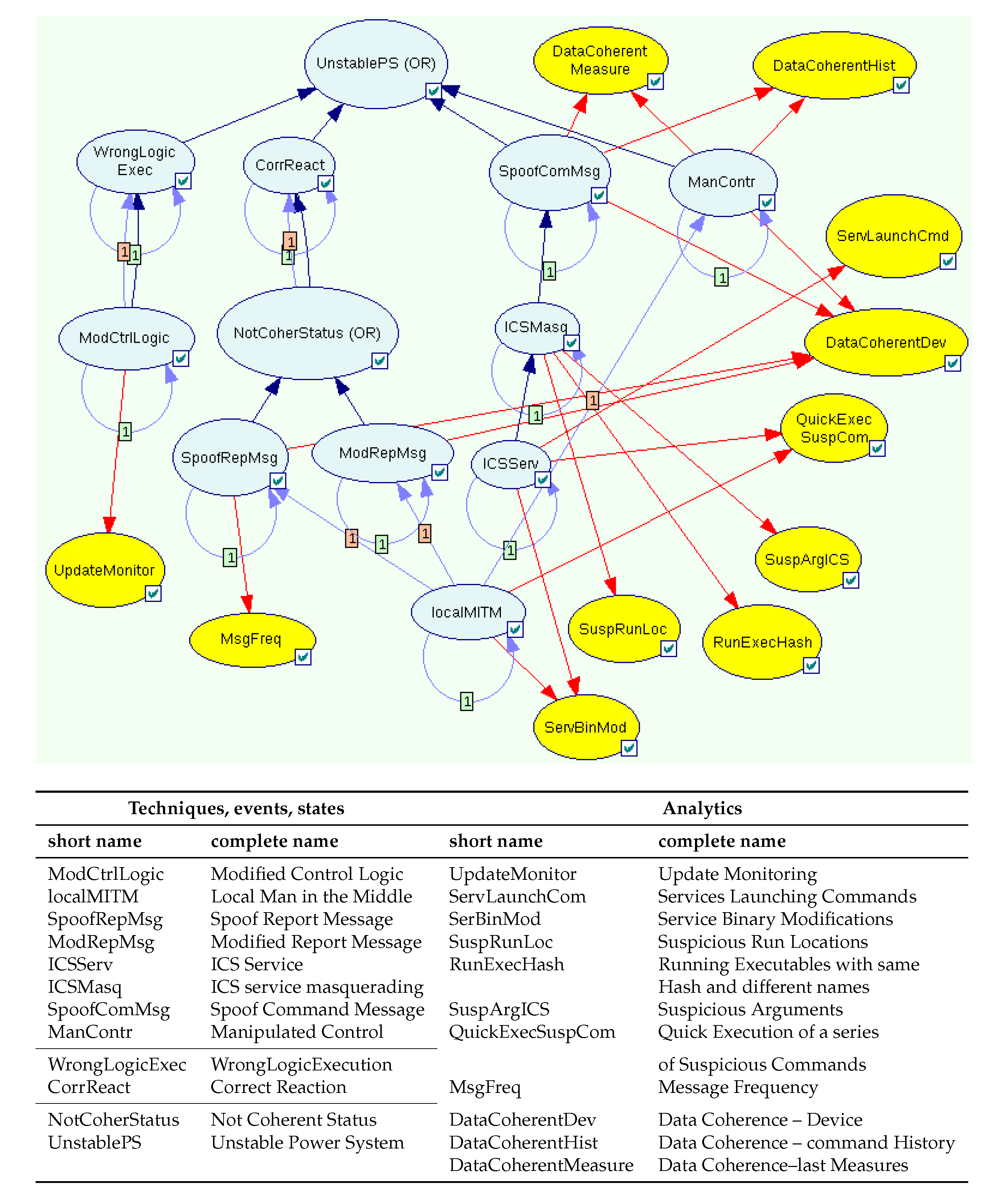
1.1. DER Control and Attack Processes
1.2. Related Work
1.3. Structure of the Paper
2. Methodology
2.1. MITRE Knowledge Bases
2.2. Attack Graphs
2.3. Security Analytics
2.4. Dynamic Bayesian Networks
3. Case Study Analysis
3.1. Inference Tasks
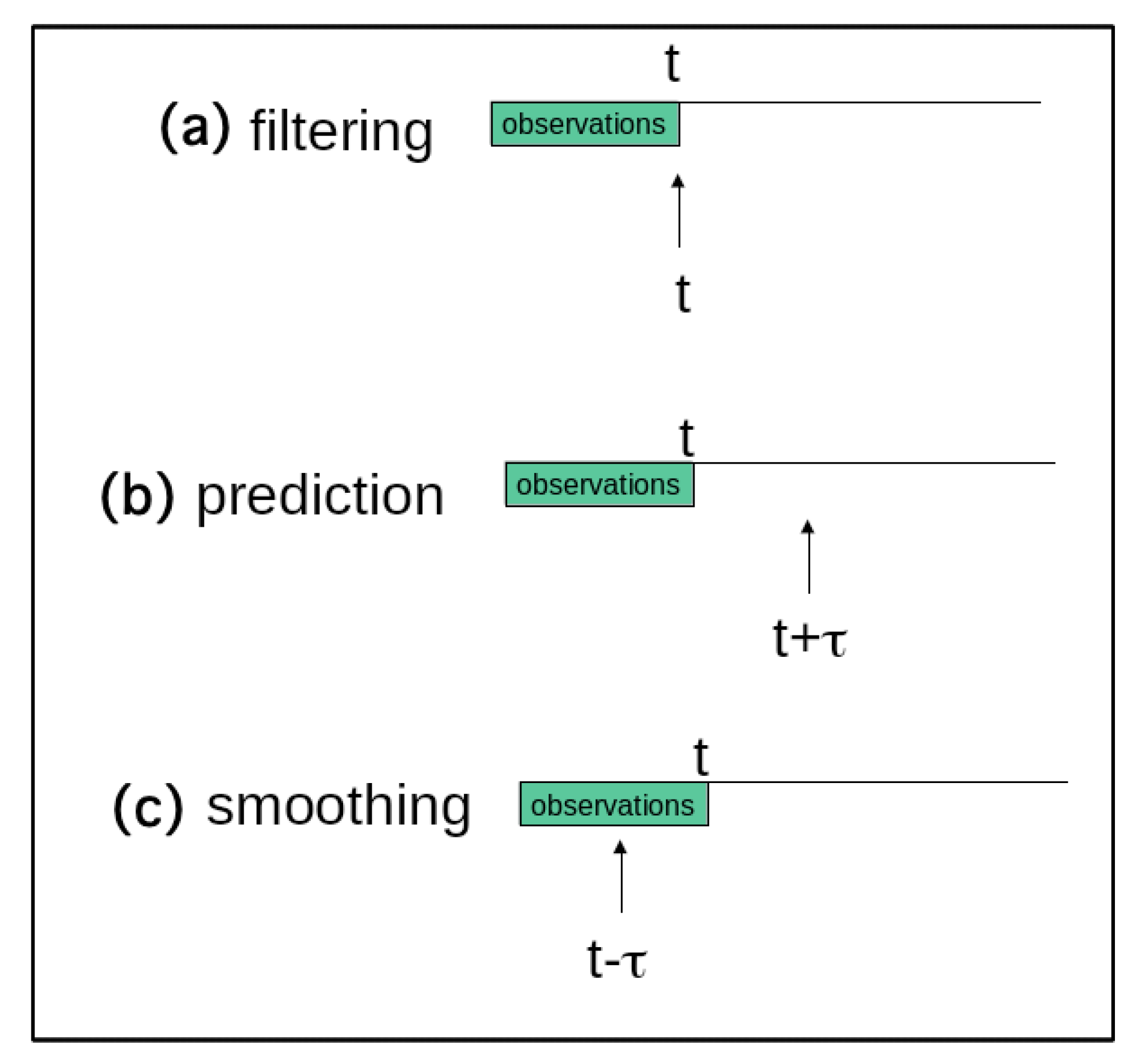
- Monitoring can support the security analyst or system in online diagnosis and early detection, providing a means to compute in real time the chance that an attack attempt is taking place, according to the observations gathered by the analytics. It is enabled by the filtering approach that consists of computing , i.e., the probability of event X at time t, given the observations at all instants up to t. This means tracking the probability of the system states, taking into account the stream of observations (see Figure 5a). When this probability value exceeds a given threshold, the analyst/system can infer that an attack attempt is in progress.
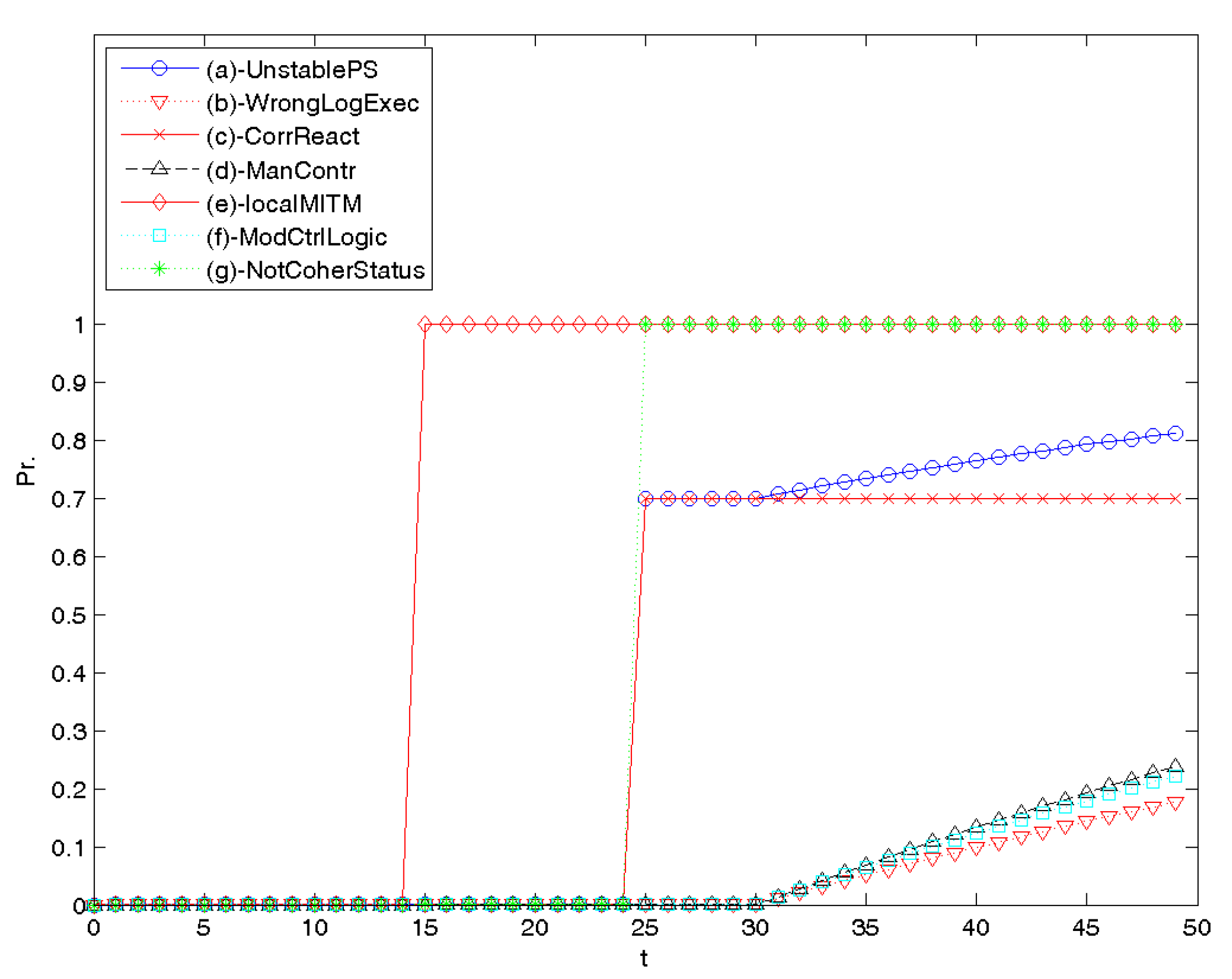
- Prediction can support the analyst/system in identifying, on the basis of evidence obtained from the analytics, the subset of techniques that the attacker will more likely exploit in the future, thereby enabling the setup of defensive actions. The filtering approach is used in this case for computing for some horizon (see Figure 5b), i.e., predicting a future state, taking into consideration evidence gathered up to now (filtering is a special case of prediction with ).
- Offline diagnosis allows determining the probable causes of security events, either online, using filtering, or offline with smoothing. The latter consists of computing for some , i.e., estimating what happened steps in the past given all the evidence (observations) up to now (see Figure 5c). Therefore, while filtering enables diagnosis in real time, smoothing makes it possible to conduct a deeper post-incident investigation based on evidence collected by the monitoring system during the DER operation.
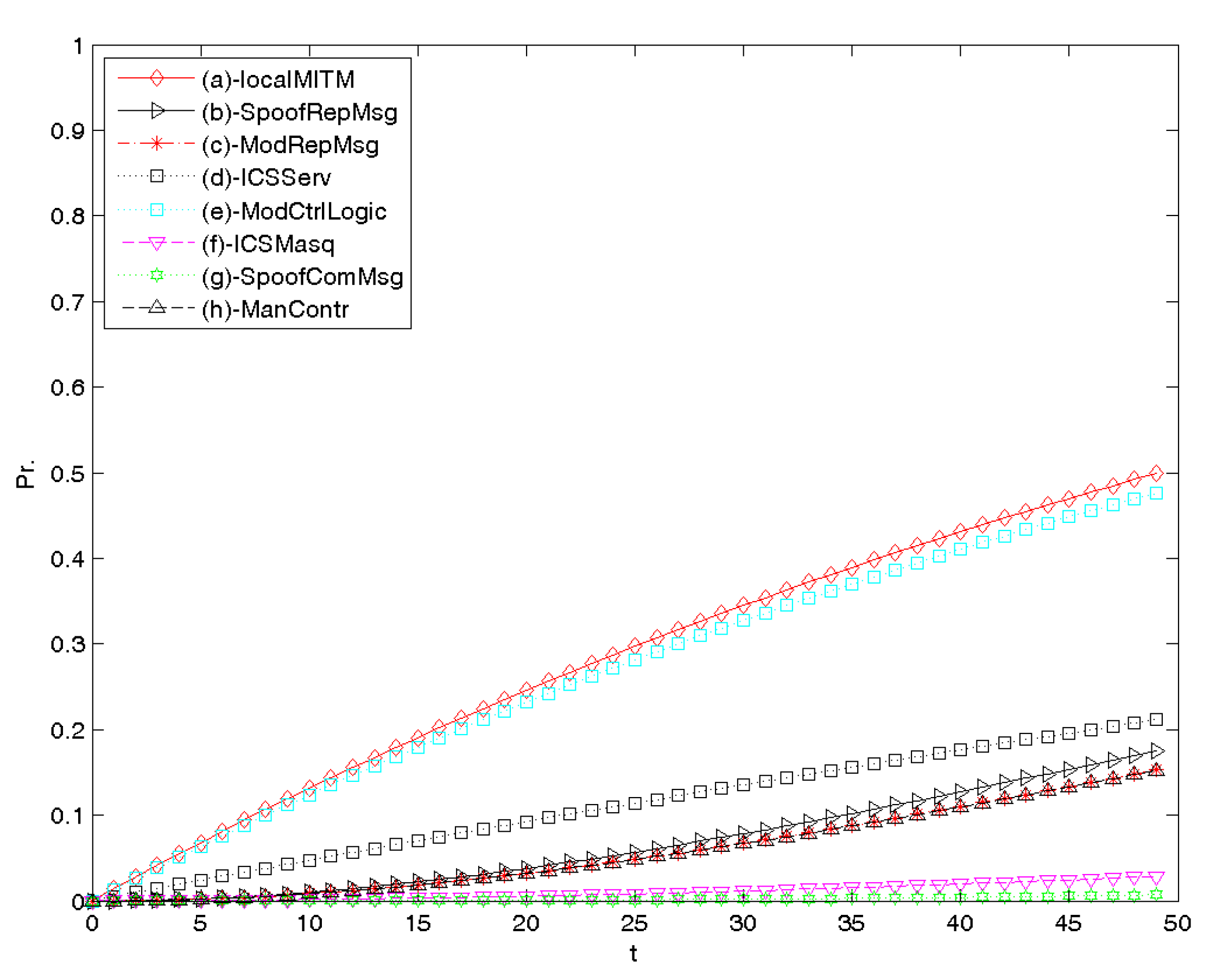
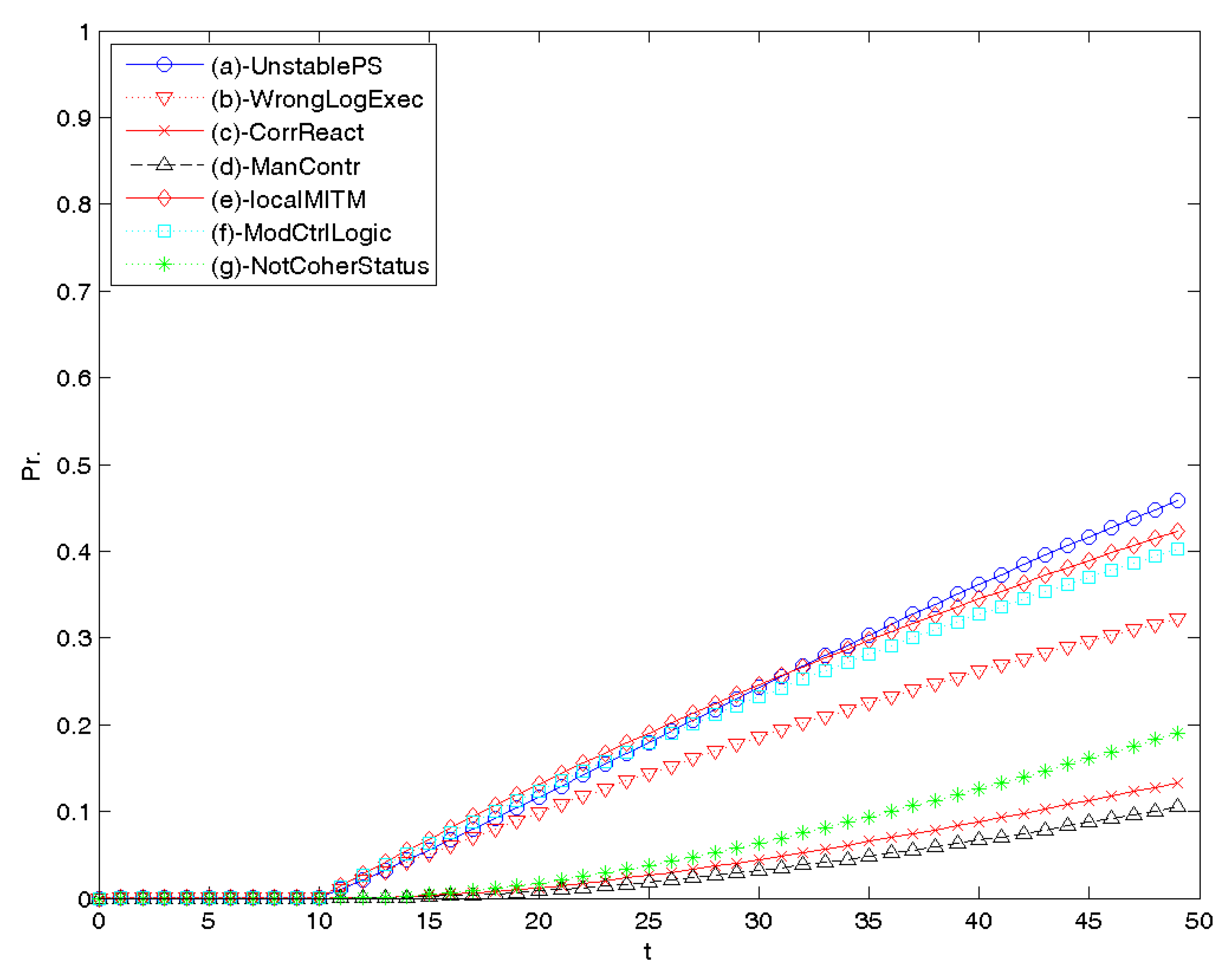
3.2. Inference Results
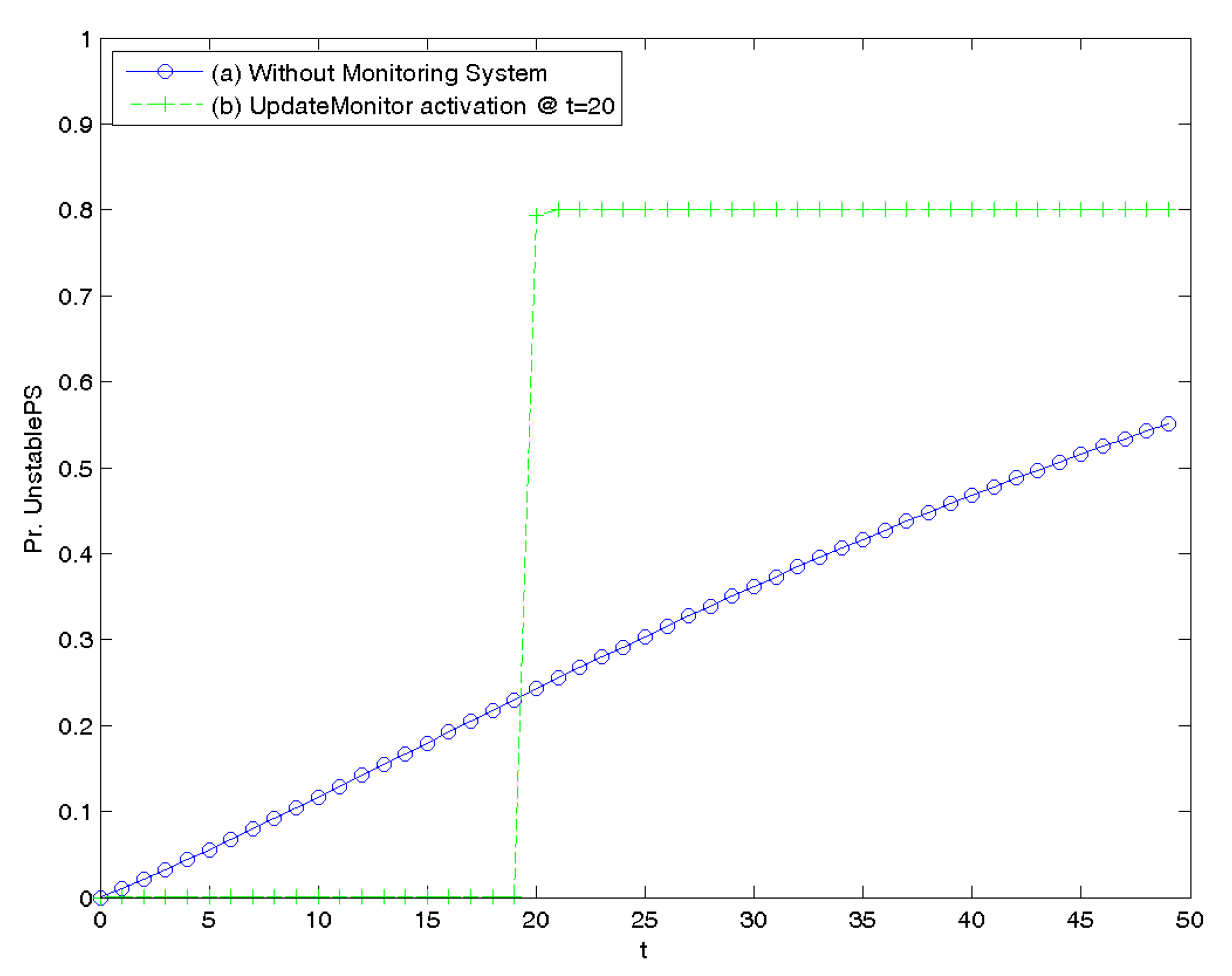
3.3. Monitoring and Online Diagnosis
3.4. Prediction
4. Discussion and Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| AG | Attack Graph |
| ARP | Address Resolution Protocol |
| AT | Attack Tree |
| BN | Bayesian Network |
| CAR | Cyber Analytics Repository |
| CVSS | Common Vulnerability Scoring System |
| DBN | Dynamic Bayesian Network |
| DER | Distributed Energy Resource |
| DMZ | Demilitarised Zone |
| DSO | Distribution System Operator |
| ICS | Industrial Control System |
| ICT | Information and Communication Technology |
| IoT | Internet of Things |
| IPC | Impair Process Control |
| IT | Information Technology |
| MITM | Man in the Middle |
| OT | Operational Technology |
| SCADA | Supervisory Control and Data Acquisition |
| SGU | Significant Grid User |
| TSO | Transmission System Operator |
Appendix A. Detailed Analysis of Experimental Results
Appendix A.1. No Evidence
Appendix A.2. With vs. without a Monitoring System
Appendix A.3. Attack Path
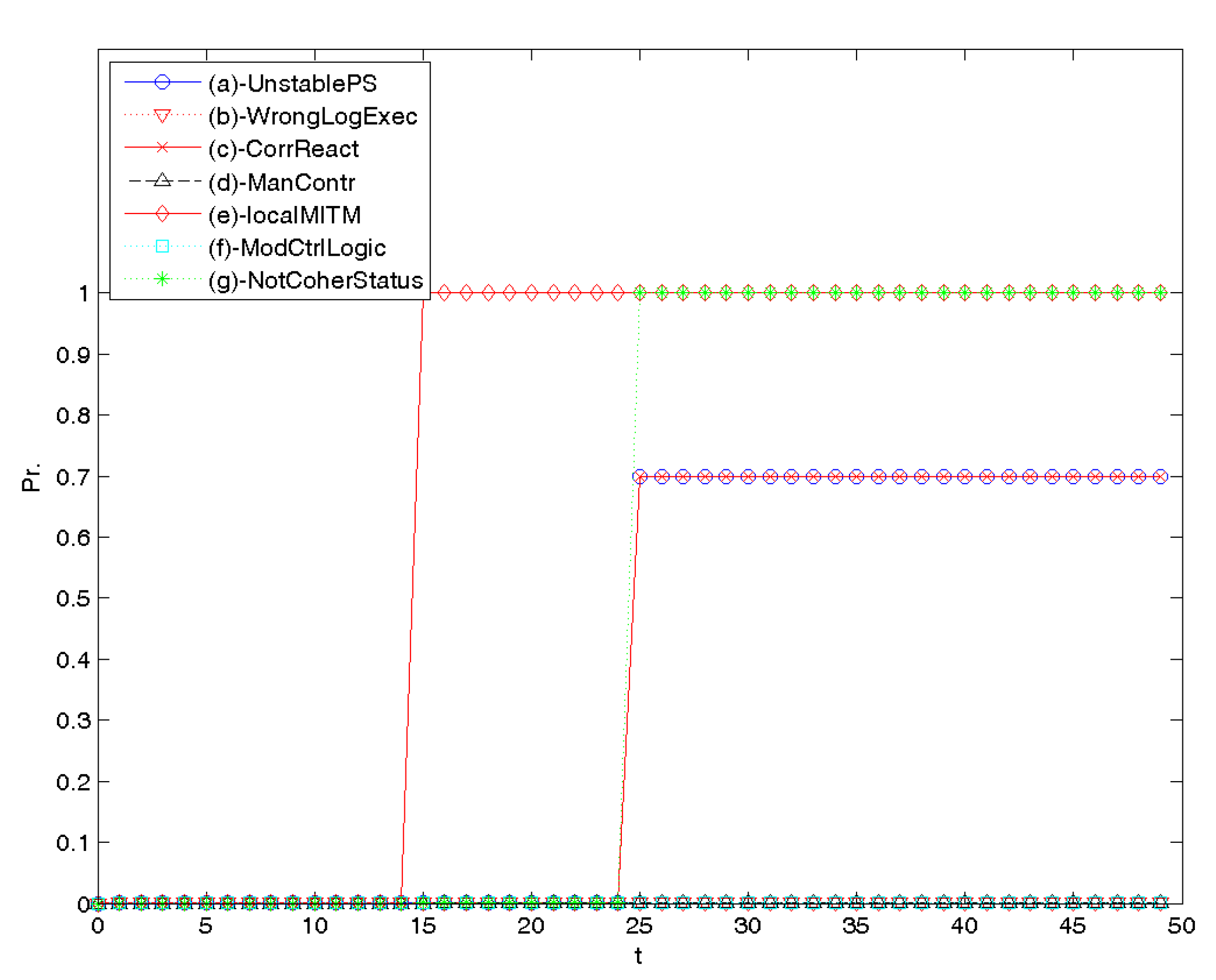
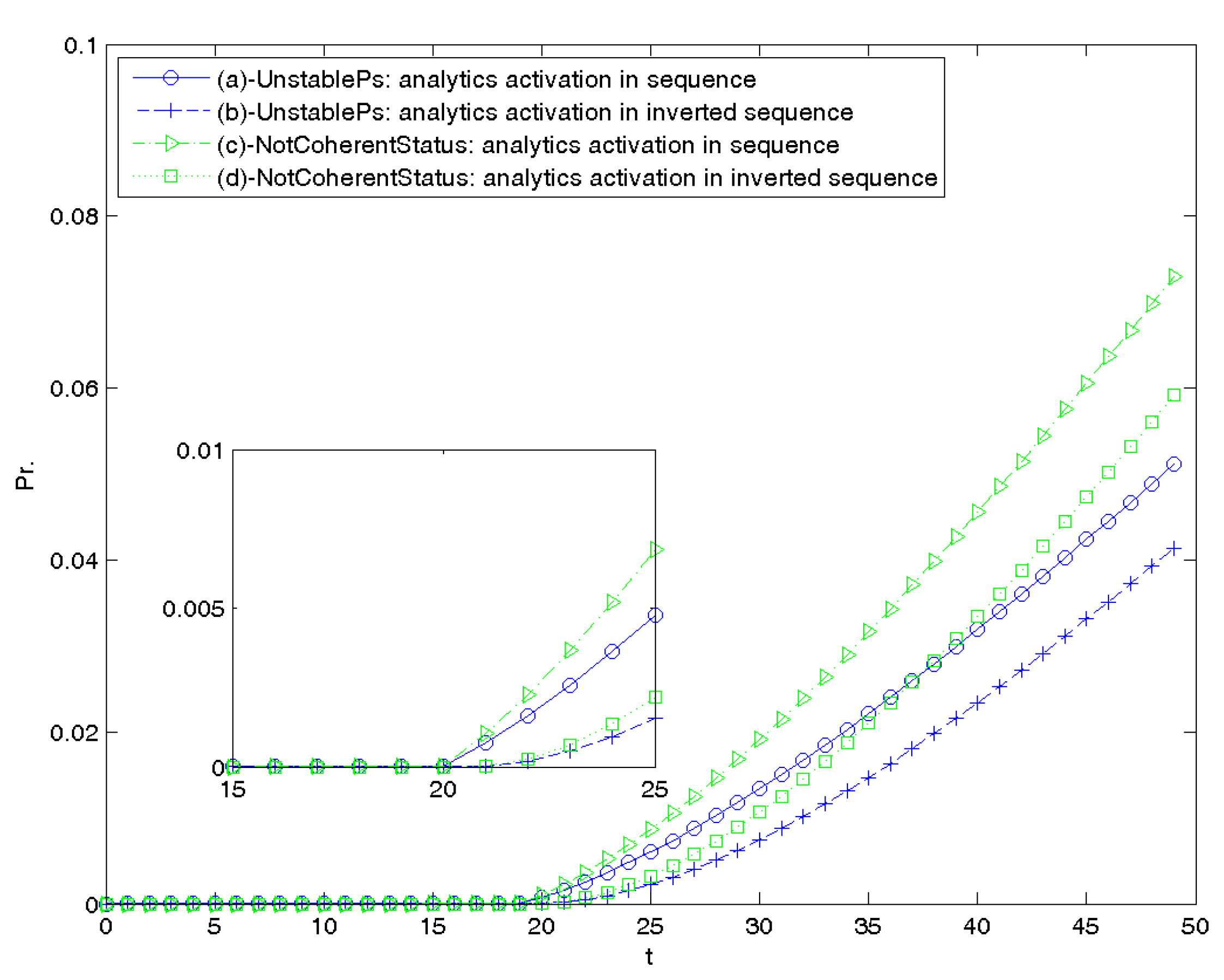
Appendix A.4. Order of Alerts
- Correct order: at , quick execution of a series of suspicious commands raises an alert (suggesting a local MITM at plant controller is in progress) and at something wrong is detected in the message frequency of DER reporting messages (which is a sign that the attacker might be trying to do some spoofing);
- Reverse order: at , the analytic message frequency raises an alert, at quick execution of a series of suspicious commands does.
Appendix A.5. Predictions
References
- European-Union. The Directive on Security of Network and Information Systems (NIS Directive). Available online: https://ec.europa.eu/digital-single-market/en/network-and-information-security-nis-directive (accessed on 15 June 2020).
- Portinale, L.; Codetta, D. Modeling and Analysis of Dependable Systems: A Probabilistic Graphical Model Perspective; World Scientific: Singapore, 2015. [Google Scholar]
- Cerotti, D.; Codetta, D.; Dondossola, G.; Egidi, L.; Franceschinis, G.; Portinale, L.; Terruggia, R. Analysis and Detection of Cyber Attack Processes targeting Smart Grids. In Proceedings of the Innovative Smart Grid Technologies Europe (ISGT), Bucharest, Romania, 29 September–2 October 2019. [Google Scholar]
- The MITRE Corporation. General Resources MITRE ATT&CK. Available online: https://attack.mitre.org/resources/ (accessed on 15 June 2020).
- ICS-CERT. Advisories. 2018. Available online: https://ics-cert.us-cert.gov/advisories (accessed on 15 June 2020).
- CVSS SIG. FIRST. Available online: https://www.first.org/cvss/ (accessed on 15 June 2020).
- Hutchins, E.; Cloppert, M.; Amin, R. Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains. Lead. Issues Inf. Warf. Secur. Res. 2011, 1, 80. [Google Scholar]
- The MITRE Corporation. Threat-Based Defense. Available online: https://www.mitre.org/capabilities/cybersecurity/threat-based-defense (accessed on 15 June 2020).
- ICS-CERT. Primary Stuxnet Advisory. Available online: https://ics-cert.us-cert.gov/advisories/ICSA-10-272-01 (accessed on 15 June 2020).
- ICS-CERT. Cyber-Attack Against Ukrainian Critical Infrastructure. Available online: https://ics-cert.us-cert.gov/alerts/IR-ALERT-H-16-056-01 (accessed on 15 June 2020).
- ICS-CERT. CRASHOVERRIDE Malware. Available online: https://ics-cert.us-cert.gov/alerts/ICS-ALERT-17-206-01 (accessed on 15 June 2020).
- Sun, C.C.; Hahn, A.; Liu, C.C. Cyber security of a power grid: State-of-the-art. Int. J. Electr. Power Energy Syst. 2018, 99, 45–56. [Google Scholar] [CrossRef]
- Dondossola, G.; Terruggia, R. Security of communications In voltage control for grids connecting Distributed Energy Resources: Impact analysis and anomalous behaviours. Cigrè Sci. Eng. Innov. Power Syst. Ind. J. 2015, 2, 30–39. [Google Scholar]
- Korman, M.; Valja, M.; Bjorkman, G.; Ekstedt, M.; Vernotte, A.; Lagerstrom, R. Analyzing the effectiveness of attack countermeasures In a SCADA system. In Proceedings of the Workshop on Cyber-Physical Security and Resilience In Smart Grids, Pittsburgh, PA, USA, 18–21 April 2017; pp. 73–78. [Google Scholar]
- Kaur, K.J.; Hahn, A. Exploring ensemble classifiers for detecting attacks In the smart grids. In Proceedings of the Fifth Cybersecurity Symposium, Coeur d’ Alene, ID, USA, 9–11 April 2018; p. 13. [Google Scholar]
- Hassanzadeh, A.; Burkett, R. SAMIIT: Spiral Attack Model in IIoT Mapping Security Alerts to Attack Life Cycle Phases. In Proceedings of the Industrial Control Systems Cyber Security Research ICS-CSR, Hamburg, Germany, 29–30 August 2018; pp. 11–20. [Google Scholar]
- Touhiduzzaman, M.; Hahn, A.; Srivastava, A. ARCADES: Analysis of Risk from Cyber Attack against DEfensive Strategies for power grid. IET Cyber-Phys. Syst. Theory Appl. 2018, 3, 119–128. [Google Scholar] [CrossRef]
- Kim, J.; Park, J. FPGA-based network intrusion detection for IEC 61850-based industrial network. ICT Express 2018, 4, 1–5. [Google Scholar] [CrossRef]
- Yang, Y.; Xu, H.; Gao, L.; Yuan, Y.; McLaughlin, K.; Sezer, S. Multidimensional Intrusion Detection System for IEC 61850-Based SCADA Nets. IEEE Trans. Power Deliv. 2017, 32, 1068–1078. [Google Scholar] [CrossRef]
- Karlsen, D.; Uhlen, K.; Vormeda, L.K. Introducing PMU-based Applications In the Control Room Setting. In Proceedings of the CIGRE—International Council on Large Electric Systems Session, Paris, France, 26–31 August 2018. [Google Scholar]
- Byres, E.J.; Franz, M.; Miller, D. The use of attack trees In assessing vulnerabilities In SCADA systems. In Proceedings of the International Infrastructure Survivability Workshop, Lisbon, Portugal, 5–8 December 2004. [Google Scholar]
- Ten, C.; Manimaran, G.; Liu, C. Cybersecurity for Critical Infrastructures: Attack and Defense Modeling. IEEE Trans. Syst. Man Cybern. Part Syst. Hum. 2010, 40, 853–865. [Google Scholar] [CrossRef]
- LeMay, E.; Ford, M.D.; Keefe, K.; Sanders, W.H.; Muehrcke, C. Model-based Security Metrics Using ADversary VIew Security Evaluation (ADVISE). In Proceedings of the International Conference on Quantitative Evaluation of Systems, Aachen, Germany, 5–8 September 2011; pp. 191–200. [Google Scholar]
- Yegnanarayana, B. Artificial Neural Networks; PHI Learning Pvt. Ltd.: New Delhi, India, 2009. [Google Scholar]
- Arrieta, A.B.; Dıaz-Rodrıguez, N.; Del-Ser, J.; Bennetot, A.; Tabik, S.; Barbado, A.; Garcia, S.; Gil-Lopez, S.; Molina, D.; Benjamins, R.; et al. Explainable Artificial Intelligence (XAI): Concepts, taxonomies, opportunities and challenges toward responsible AI. Inf. Fusion 2020, 58, 82–115. [Google Scholar] [CrossRef]
- Qin, X.; Lee, W. Attack Plan Recognition and Prediction Using Causal Networks. In Proceedings of the ACSAC, Tucson, AZ, USA, 6–10 December 2004; pp. 370–379. [Google Scholar]
- Xie, P.; Li, J.; Ou, X.; Liu, P.; Levy, R. Using Bayesian Networks for cyber-security analysis. In Proceedings of the International Conference on Dependable Systems & Networks (DSN), Chicago, IL, USA, 28 June–1 July 2010; pp. 211–220. [Google Scholar]
- Zhang, S.; Song, S. A novel attack graph posterior inference model based on Bayesian network. J. Inf. Sec. 2011, 2, 8–27. [Google Scholar] [CrossRef][Green Version]
- Lyu, X.; Ding, Y.; Yang, S. Bayesian Network Based C2P Risk Assessment for Cyber-Physical Systems. IEEE Access 2020, 8, 88506–88517. [Google Scholar] [CrossRef]
- An, X.; Jutla, D.; Cercone, N. Privacy intrusion detection using dynamic Bayesian networks. In Proceedings of the ICEC, Cambridge, UK, 20–22 September 2006; pp. 208–215. [Google Scholar]
- Frigault, M.; Wang, L.; Singhal, A.; Jajodia, S. Measuring network security using dynamic bayesian network. In Proceedings of the Workshop on Quality of protection, Alexandria, VA, USA, 27 October 2008; pp. 23–30. [Google Scholar]
- Codetta, D.; Portinale, L.; Terruggia, R. Quantitative Evaluation of Attack/Defense Scenarios through Decision Network Modelling and Analysis. In Proceedings of the IEEE International Carnahan Conference on Security Technologies, Rome, Italy, 13–16 October 2014; pp. 432–437. [Google Scholar]
- Dondossola, G.; Garrone, F.; Szanto, J. Cyber risk assessment of power control systems—A metrics weighed by attack experiments. In Proceedings of the IEEE Power and Energy Society General Meeting, Detroit, MI, USA, 24–28 July 2011; pp. 1–9. [Google Scholar]
- Foreseeti. securiCAD. Available online: https://www.foreseeti.com/securicad/ (accessed on 15 June 2020).
- Analytics, K. Blade RiskManager. Available online: https://kdmanalytics.com/cybersecurity-products/blade-riskmanager/ (accessed on 15 June 2020).
- Cerotti, D.; Codetta, D.; Dondossola, G.; Egidi, L.; Franceschinis, G.; Portinale, L.; Terruggia, R. A Bayesian Network Approach for the Interpretation of Cyber Attacks to Power Systems. In Proceedings of the ITASEC, Pisa, Italy, 13–15 February 2019. [Google Scholar]
- Strom, B.E.; Applebaum, A.; Miller, D.P.; Nickels, K.C.; Pennington, A.G.; Thomas, C.B. MITRE ATT&CKTM: Design and Philosophy; Technical Report; The MITRE Corporation: McLean, VA, USA, 2018. [Google Scholar]
- The MITRE Corporation. Adversarial Tactics, Techniques and Common Knowledge (ATT&CK). 2015. Available online: https://attack.mitre.org/ (accessed on 15 June 2020).
- Alexander, O. Launching ATT&CK for ICS. Available online: https://medium.com/mitre-attack/launching-attack-for-ics-2be4d2fb9b8 (accessed on 15 June 2020).
- The MITRE Corporation. ATT&CK for Industrial Control Systems. 2020. Available online: https://collaborate.mitre.org/attackics/index.php/Main_Page (accessed on 15 June 2020).
- The MITRE Corporation. Cyber Analytics Repository (CAR). Available online: https://car.mitre.org/wiki/Main_Page (accessed on 15 June 2020).
- IEC 61850 International Standard—Communication Networks and Systems for Power Utility Automation. IEC Technical Committee 57—Working Group 10. IEC 61850:2020 SER. Available online: https://webstore.iec.ch/publication/6028 (accessed on 15 June 2020).
- IEC 60870-5-104 International Standard—Telecontrol Equipment and Systems—Part 5-104: Transmission Protocols—Network Access for IEC 60870-5-101 Using Standard Transport profiles IEC Technical Committee 57—Working Group 3. IEC 60870-5-104:2006+AMD1:2016. Available online: https://webstore.iec.ch/publication/25035 (accessed on 15 June 2020).
- Bayes Net Toolbox for Matlab. Available online: https://github.com/bayesnet/bnt (accessed on 15 June 2020).


| Entry | localMITM | () | (t) | prob. |
|---|---|---|---|---|
| 1 | 0 | 0 | 0 | 1 |
| 2 | 0 | 0 | 1 | 0 |
| 3 | 0 | 1 | 0 | 1 |
| 4 | 0 | 1 | 1 | 0 |
| 5 | 1 | 0 | 0 | 0.982844 |
| 6 | 1 | 0 | 1 | 0.017156 |
| 7 | 1 | 1 | 0 | 0 |
| 8 | 1 | 1 | 1 | 1 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cerotti, D.; Codetta-Raiteri, D.; Dondossola, G.; Egidi, L.; Franceschinis, G.; Portinale, L.; Terruggia, R. Evidence-Based Analysis of Cyber Attacks to Security Monitored Distributed Energy Resources. Appl. Sci. 2020, 10, 4725. https://doi.org/10.3390/app10144725
Cerotti D, Codetta-Raiteri D, Dondossola G, Egidi L, Franceschinis G, Portinale L, Terruggia R. Evidence-Based Analysis of Cyber Attacks to Security Monitored Distributed Energy Resources. Applied Sciences. 2020; 10(14):4725. https://doi.org/10.3390/app10144725
Chicago/Turabian StyleCerotti, Davide, Daniele Codetta-Raiteri, Giovanna Dondossola, Lavinia Egidi, Giuliana Franceschinis, Luigi Portinale, and Roberta Terruggia. 2020. "Evidence-Based Analysis of Cyber Attacks to Security Monitored Distributed Energy Resources" Applied Sciences 10, no. 14: 4725. https://doi.org/10.3390/app10144725
APA StyleCerotti, D., Codetta-Raiteri, D., Dondossola, G., Egidi, L., Franceschinis, G., Portinale, L., & Terruggia, R. (2020). Evidence-Based Analysis of Cyber Attacks to Security Monitored Distributed Energy Resources. Applied Sciences, 10(14), 4725. https://doi.org/10.3390/app10144725






