Cryptanalysis of a Group Key Establishment Protocol
Abstract
1. Introduction
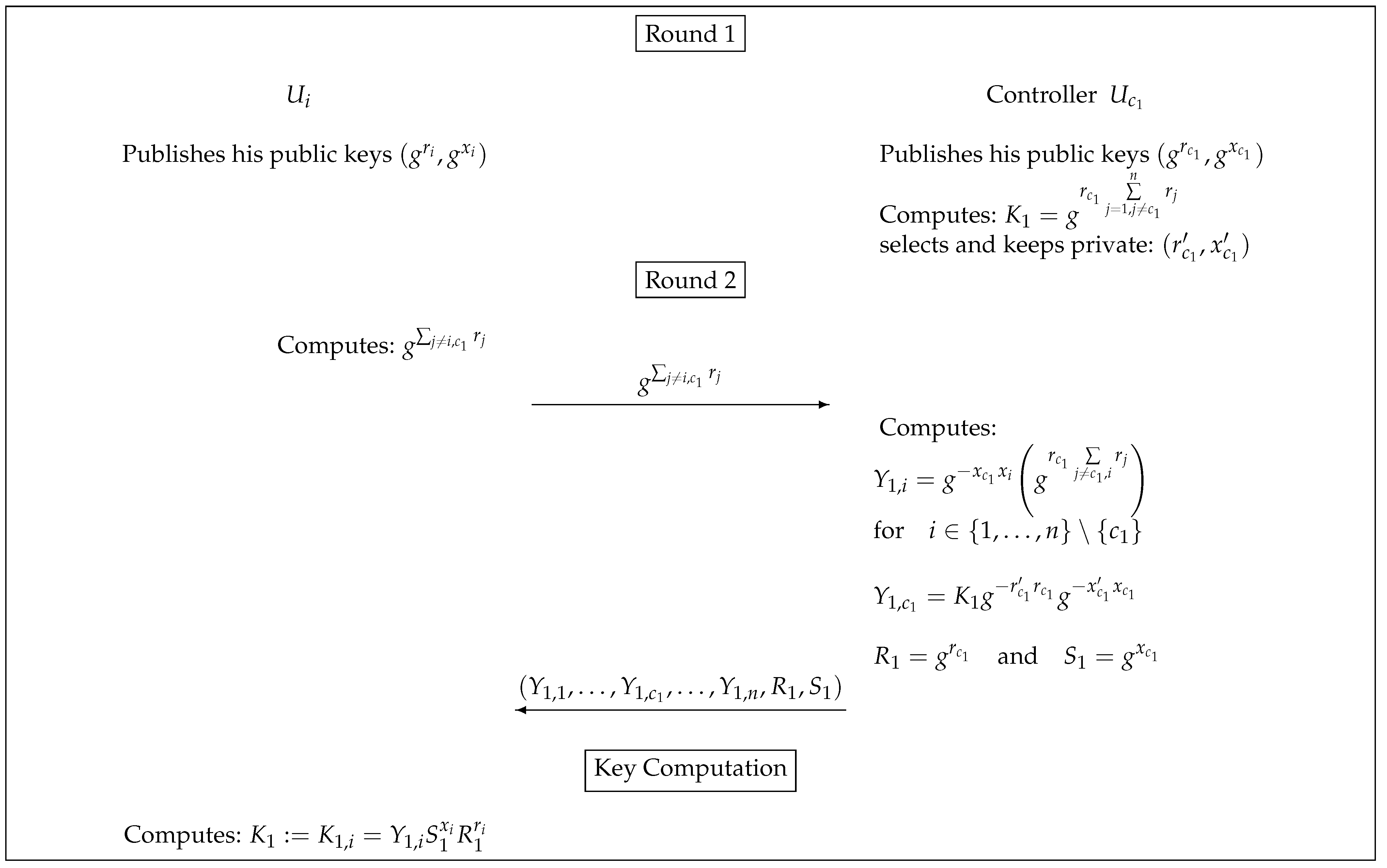
2. The Protocol of López Ramos et al.
- Initialization
- Round 1
- Each user publishes his pair of public keys (We assume that these keys are sent to the users, hence the adversary can potentially manipulate those values).
- The group controller calculate , which will be the session key.
- The group controller will choose a new pair of elements that will be privately kept and will become his new private information at a later stage.
- Round 2
- Key Computation
3. Security Model
Security Goals: Semantic Security and Authentication
- Participants:
- :
- stores the identities of the parties user aims at establishing a session key with (including itself);
- :
- is a variable storing a non-secret session identifier to the session key stored in ;
- :
- is a variable which indicates whether the session key in was accepted;
- :
- is a variable which indicates whether the protocol execution has terminated;
- :
- is a variable which indicates whether this instance is taking part in a protocol run;
- :
- this variable is initialized with a distinguished null value and will store the session key.
- Communication network and adversarial capabilities:
- when querying this oracle, message M is sent to instance of user . The output will be the protocol message that the instance outputs after receiving message M. This oracle can also be used for the adversary to initialize a protocol execution, by using the special message to an unused instance . This oracle initializes a protocol run among . After such a query, sets , , and processes the first step of the protocol.
- if the instances have not yet been used, this oracle will return a transcript of a complete execution of the protocol among the specified instances.
- this oracle returns the session key stored in if true and a null value otherwise.
- this query returns ’s long term secret key.
- Security notions:
- the adversary queried for an instance that is partnered with ;
- the adversary queried for a user before a query of the form ;
4. Cryptanalysis of the Proposal of López-Ramos et al.
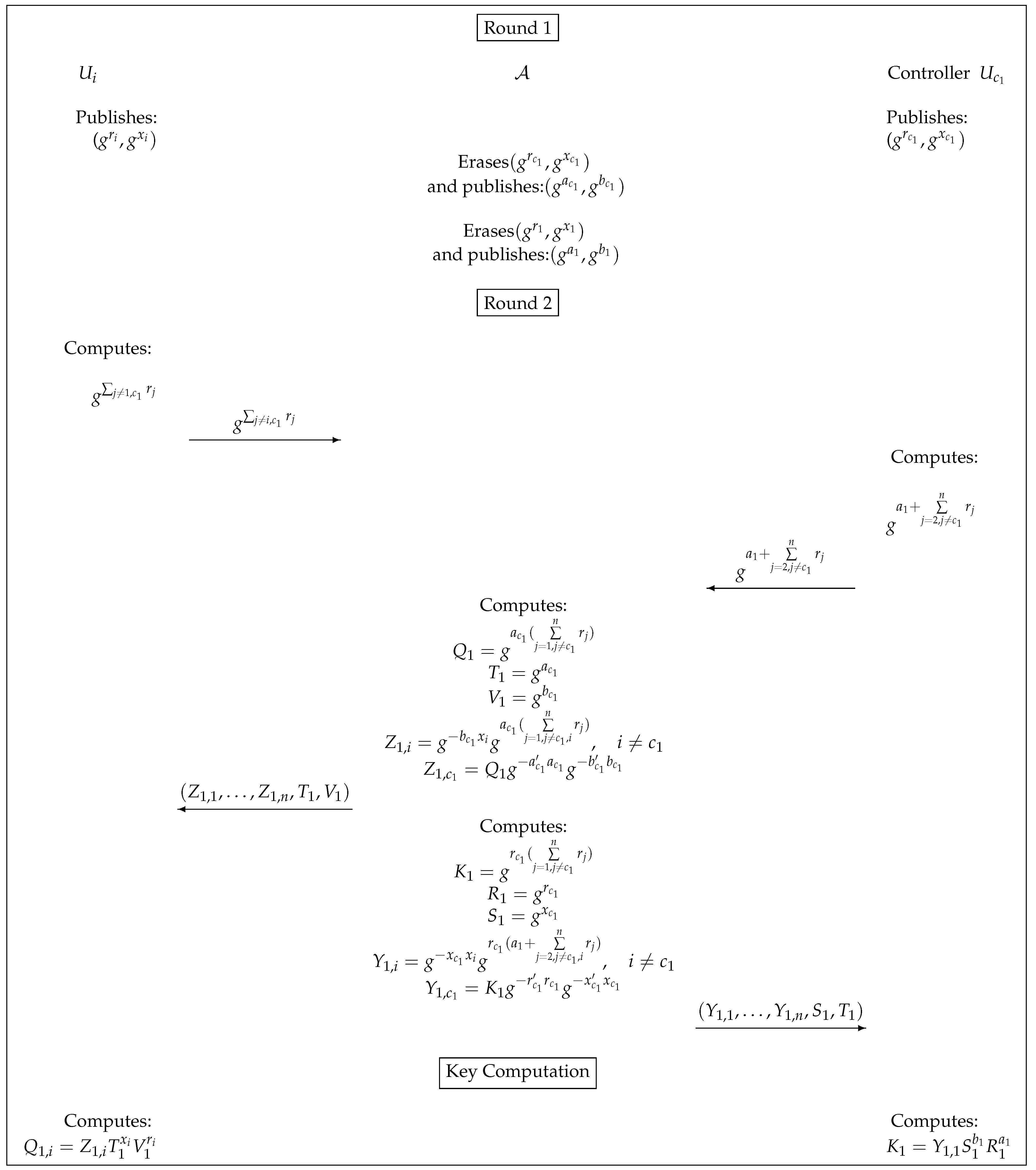
4.1. Active Attack
- The attacker queries , to initiate a protocol instance. After this query, the first step of the protocol is executed. In particular, the adversary obtains every users’ pairs of public keys , with .
- The adversary will delete the message sent by the controller to the rest of the users and delete the public keys sent by user to .
- The adversary generates its private keys and public keys and queries , for all . the adversary generates its private keys and public keys and queries .
- 4.
- The adversary will compute the session key and the values and , along with the keying values
- 5.
- The adversary will query oracle, for all .
- 6.
- The adversary will compute the session key and the values and , along with the keying values
- 7.
- The adversary will query oracle.
- The attacker queries , to initiate a protocol instance. After this query, the first step of the protocol is executed. In particular, the users send their public keys and thus, the adversary obtains , with for all the participants .
- The adversary will delete the message sent by the controller to user and the message sent by user to the rest of the participants.
- The adversary , will choose random values , and queries , for all , including .
- 4.
- The attacker will delete the message sent by to the superseded user , and queries , where
- 5.
- With the information received, the users, following the protocol, will compute the subsequent keys:
- (a)
- The superseded user will compute .
- (b)
- Every user , computes .
- (c)
- Adversary computes and .
4.2. Forward Secrecy
- The attacker queries , obtaining the private keys and .
- Afterwards, he queries, , obtaining a protocol transcript. In particular, he gets the values and .
- The adversary now can compute the key as user would do according to the protocol description: .
- The adversary now queries on any user instance involved in the above execution. Since he knows the key established, he wins the game with probability one.
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Bellare, M.; Rogaway, P. Entity Authentication and Key Distribution; CRYPTO, Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 1993; Volume 773, pp. 232–249. [Google Scholar]
- Bellare, M.; Pointcheval, D.; Rogaway, P. Authenticated Key Exchange Secure against Dictionary Attacks; EUROCRYPT, Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1807, pp. 139–155. [Google Scholar]
- Boyd, C.; Mathuria, A. Protocols for Authentication and Key Establishment; Information Security and Cryptography; Springer: Berlin/Heidelberg, Germany, 2003. [Google Scholar]
- Burmester, M.; Desmedt, Y. A secure and scalable Group Key Exchange system. Inf. Process. Lett. 2005, 94, 137–143. [Google Scholar] [CrossRef]
- Bohli, J.; Vasco, M.I.G.; Steinwandt, R. Secure group key establishment revisited. Int. J. Inf. Sec. 2007, 6, 243–254. [Google Scholar] [CrossRef]
- Boyd, C.; Davies, G.T.; Gjøsteen, K.; Jiang, Y. Offline Assisted Group Key Exchange; ISC, Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2018; Volume 11060, pp. 268–285. [Google Scholar]
- Vasco, M.I.G.; del Pozo, A.L.P.; Corona, A.S. Group key exchange protocols withstanding ephemeral-key reveals. IET Inf. Secur. 2018, 12, 79–86. [Google Scholar] [CrossRef]
- Katz, J.; Yung, M. Scalable Protocols for Authenticated Group Key Exchange; CRYPTO, Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2729, pp. 110–125. [Google Scholar]
- Abdalla, M.; Bohli, J.; Vasco, M.I.G.; Steinwandt, R. (Password) Authenticated Key Establishment: From 2-Party to Group; TCC, Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2007; Volume 4392, pp. 499–514. [Google Scholar]
- Neupane, K.; Steinwandt, R.; Corona, A.S. Group Key Establishment: Adding Perfect Forward Secrecy at the Cost of One Round; CANS; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7712, pp. 158–168. [Google Scholar]
- Vasco, M.I.G.; Robinson, A.; Steinwandt, R. Cryptanalysis of a Proposal Based on the Discrete Logarithm Problem Inside Sn. Cryptography 2018, 2, 16. [Google Scholar] [CrossRef]
- Steinwandt, R.; Corona, A.S. Cryptanalysis of a 2-party key establishment based on a semigroup action problem. Adv. Math. Commun. 2011, 5, 87–92. [Google Scholar] [CrossRef]
- Vasco, M.I.G.; del Pozo, A.L.P.; Corona, A.S. Pitfalls in a server-aided authenticated group key establishment. Inf. Sci. 2016, 363, 1–7. [Google Scholar] [CrossRef]
- Baouch, M.; López-Ramos, J.A.; Torrecillas, B.; Schnyder, R. An active attack on a distributed Group Key Exchange system. Adv. Math. Commun. 2017, 11, 715–717. [Google Scholar] [CrossRef]
- López-Ramos, J.A.; Rosenthal, J.; Schipani, D.; Schnyder, R. An Application of Group Theory in Confidential Network Communications. Math. Methods Appl. Sci. 2016. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Carracedo, J.M.; Corona, A.S. Cryptanalysis of a Group Key Establishment Protocol. Symmetry 2021, 13, 332. https://doi.org/10.3390/sym13020332
Carracedo JM, Corona AS. Cryptanalysis of a Group Key Establishment Protocol. Symmetry. 2021; 13(2):332. https://doi.org/10.3390/sym13020332
Chicago/Turabian StyleCarracedo, Jorge Martínez, and Adriana Suárez Corona. 2021. "Cryptanalysis of a Group Key Establishment Protocol" Symmetry 13, no. 2: 332. https://doi.org/10.3390/sym13020332
APA StyleCarracedo, J. M., & Corona, A. S. (2021). Cryptanalysis of a Group Key Establishment Protocol. Symmetry, 13(2), 332. https://doi.org/10.3390/sym13020332





