A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting
Abstract
1. Introduction
2. Information on the Blockchain Concept
2.1. Consensus Protocols
2.2. Blockchain Network Types
3. Blockchain Current Applications
4. Information on Electronic Voting Systems
- Receipt-Freeness should not produce any receipt to prove the voter’s choice for a particular candidate [1].
- Data Integrity ensures that each vote is recorded as intended and cannot be tampered with in any manner, once logged [33].
- Reliability/Robustness, election systems must operate safely without loss of votes. Software and methods should be developed in such a way without any malicious code nor errors [35].
- Verifiability, voters should be able to confirm that their ballots are counted correctly [38].
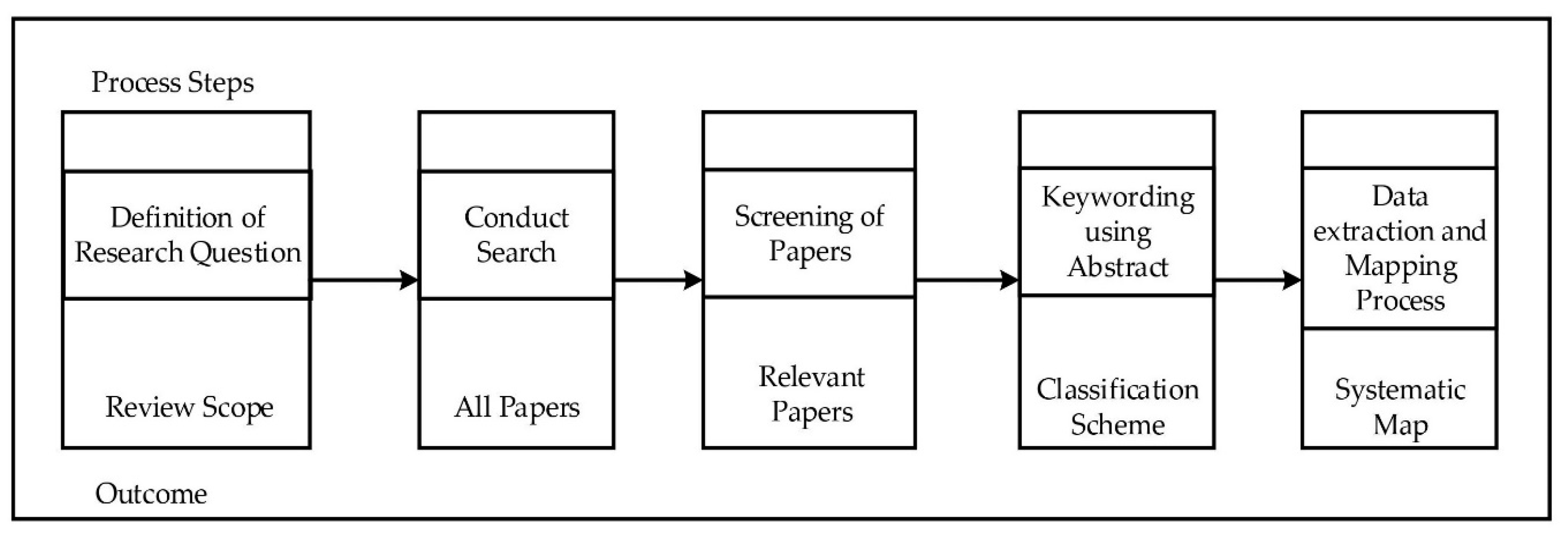
5. Research Methodology
5.1. Research Questions
- RQ1: What are the current e-voting system gaps?
- RQ2: Can the blockchain concept improve e-voting systems?
- RQ3: What are the research topics and proposed solutions that have been published in blockchain-based e-voting?
- RQ4: Which blockchain platforms/consensus models are used?
- RQ5: What are the future research directions for the blockchain-based e-voting system?
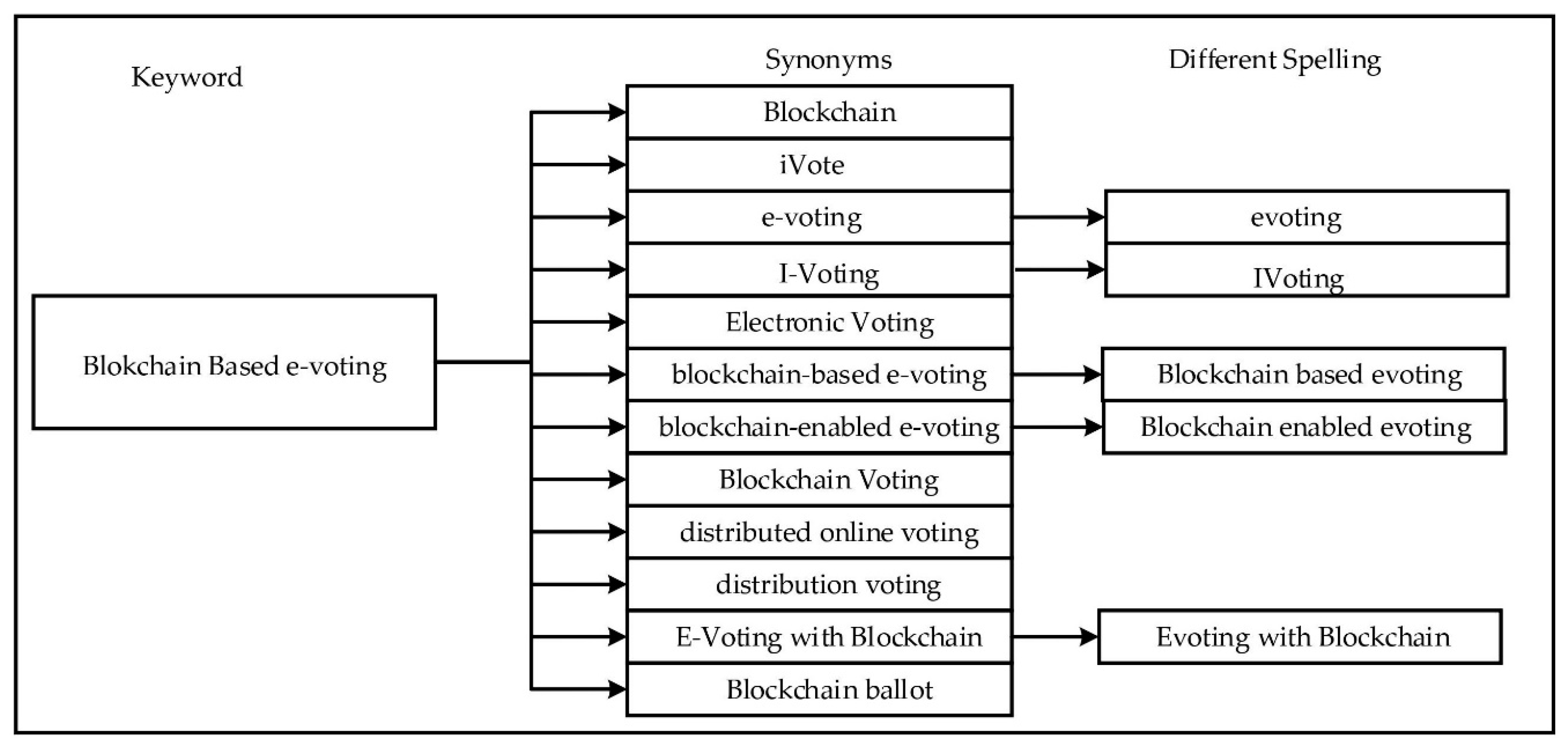
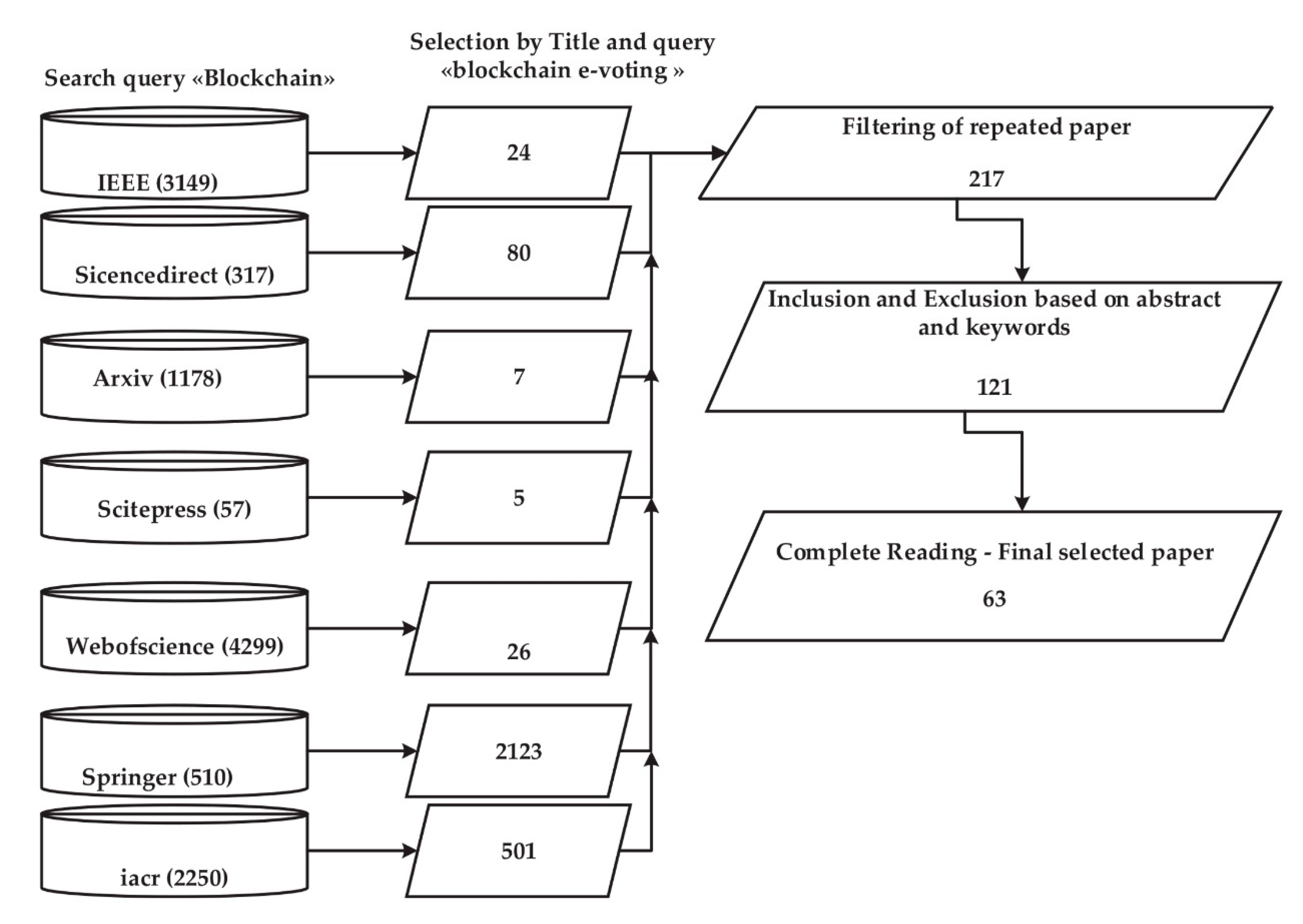
5.2. Data Sources and Search Process
5.3. Selection of Results
6. Research Questions and Findings
6.1. RQ1: What Are the Current E-Voting Systems Gaps?
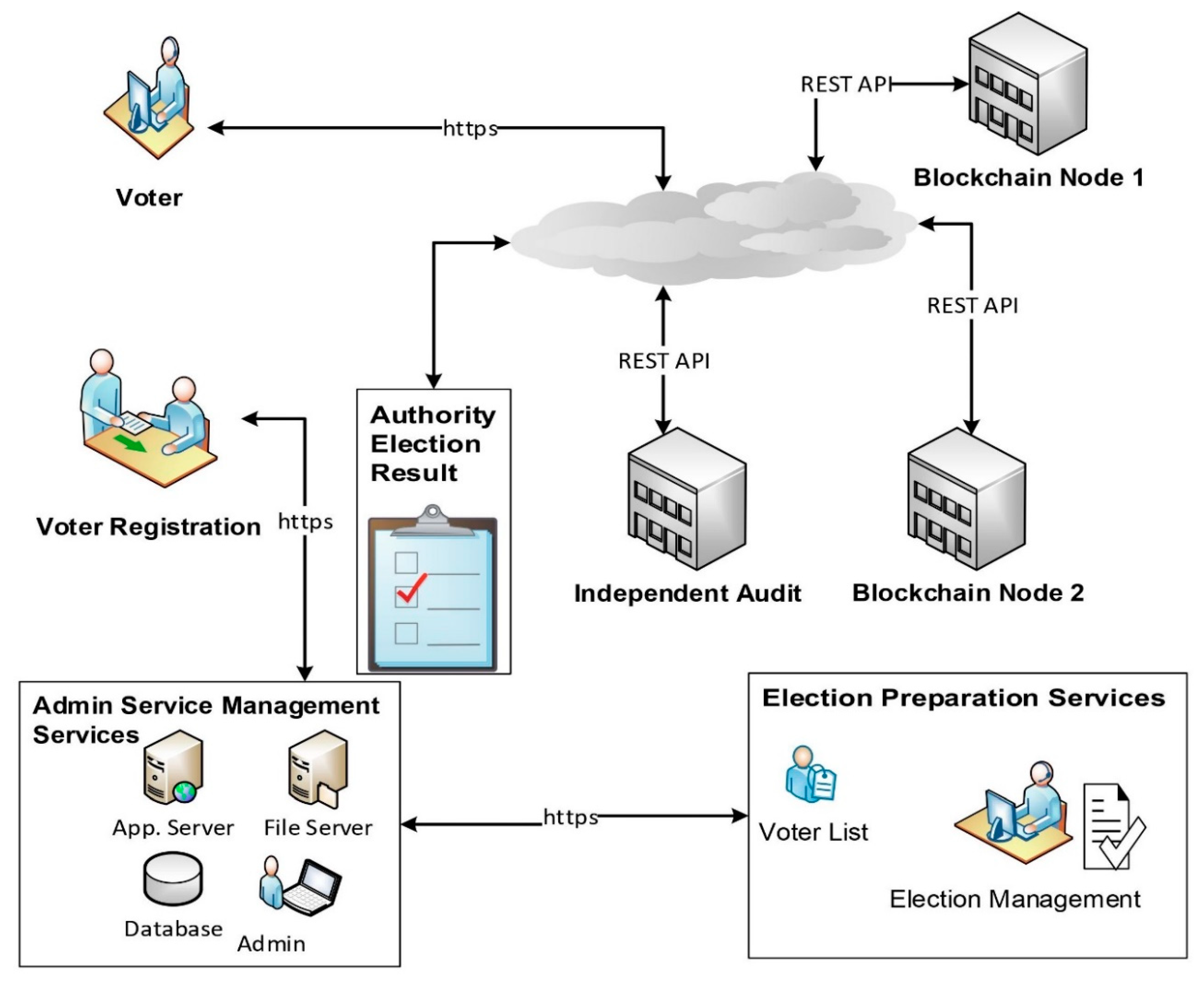
6.2. RQ2: Can the Blockchain Concept Improve E-Voting Systems?
- (i)
- DDOS attacks are one of the most critical challenges that are faced by the leading experts in cyber-attacks today. If some of the nodes on blockchain networks become offline as a result of the DDoS attack, the system then will continue to operate without any interruption due to its distributed nature. Whenever the nodes are brought back, everything is synced back to ensure consistency, practically making protocol and irrepressible and there would be no risk of data loss. The general architecture of blockchain is designed to avoid single points of failure. Blockchain nodes run independently and simultaneously. Therefore, blockchain provides high availability [44,51,117].
- (ii)
- Blockchain is considered an immutable ledger for recording transactions and all participants can access the distributed ledger and its immutable records. This immutable transaction will be recorded only once and it is verifiable [14]. Therefore, none of the system participants can either modify or delete these recorded transactions leading to increase integrity and trust.
- (iii)
- Blockchain-based e-voting provides both transparency and privacy. The participants or independent external observers can approve the voting results that are stored in the blockchain; thus, it can ensure election integrity [51].
- (iv)
- Blockchain systems promise a cheaper cost in the long run. Installing and operating a secure data storage system in distributed architecture involves high cost and security risks. Blockchain is claimed to be safer and cheaper than standard database applications.
- (v)
- It provides instant results. In some e-voting methods, votes should be reviewed in various voting areas and then collected in central units. While these processes consume a considerable amount of time, the announcement of the election results may also take longer. By employing e-voting with blockchain, the election results can be safely disclosed in minutes rather than hours [52].
- (vi)
- After the first voting process, with increased confidence, more voters can participate in elections [52].
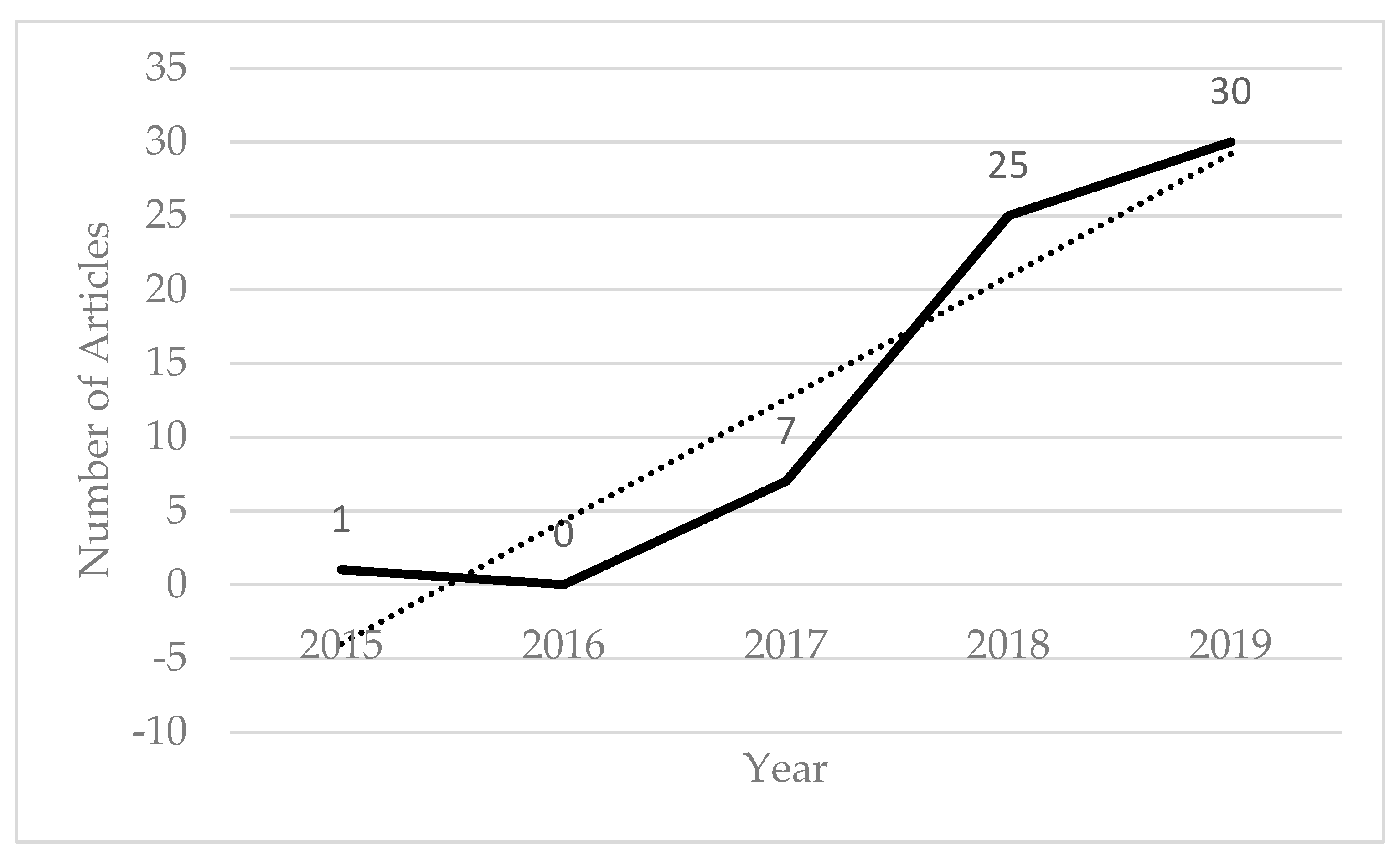
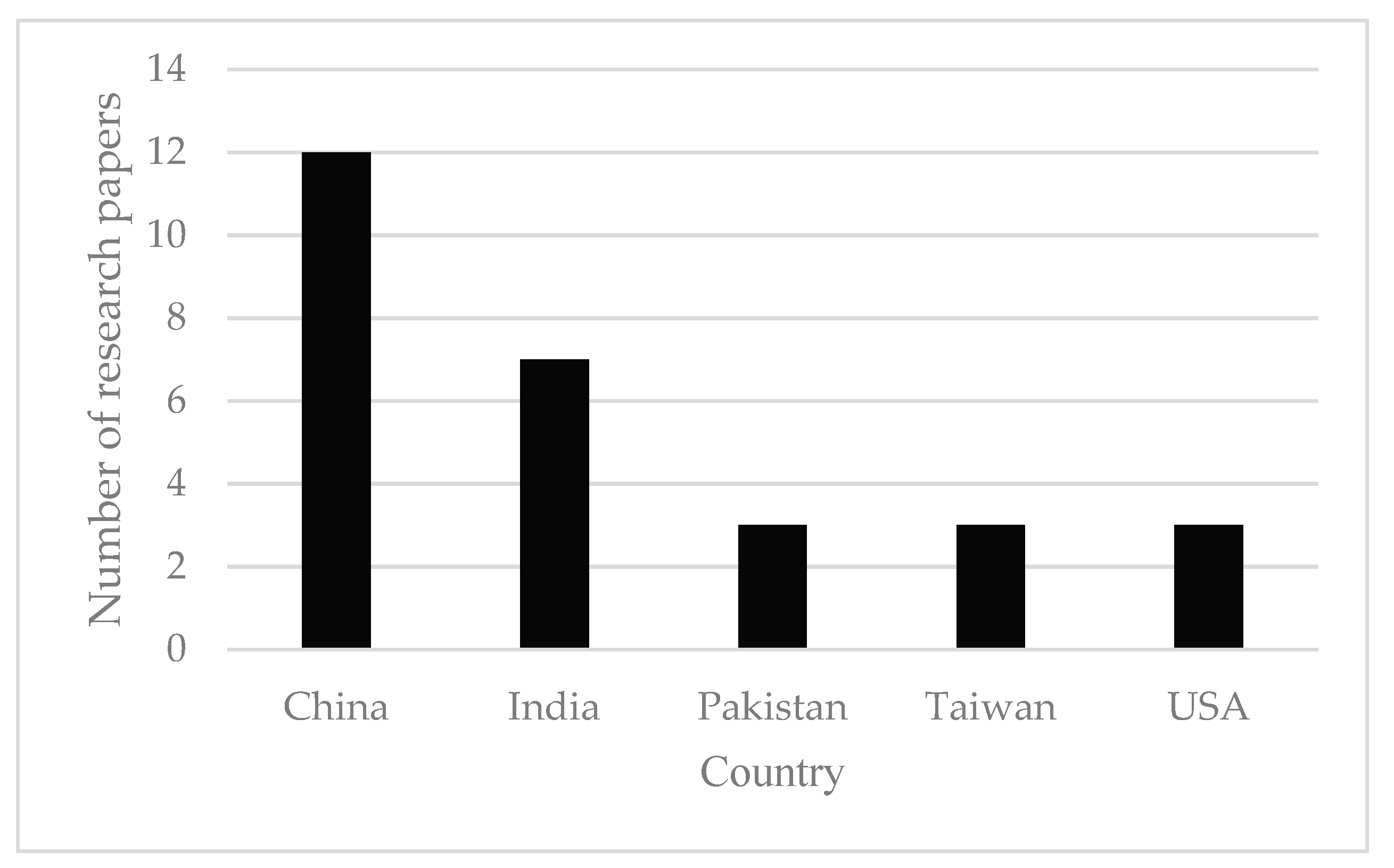
6.3. RQ3: What Are the Current Research Trends/Proposed Solutions in Blockchain-Based E-Voting System?
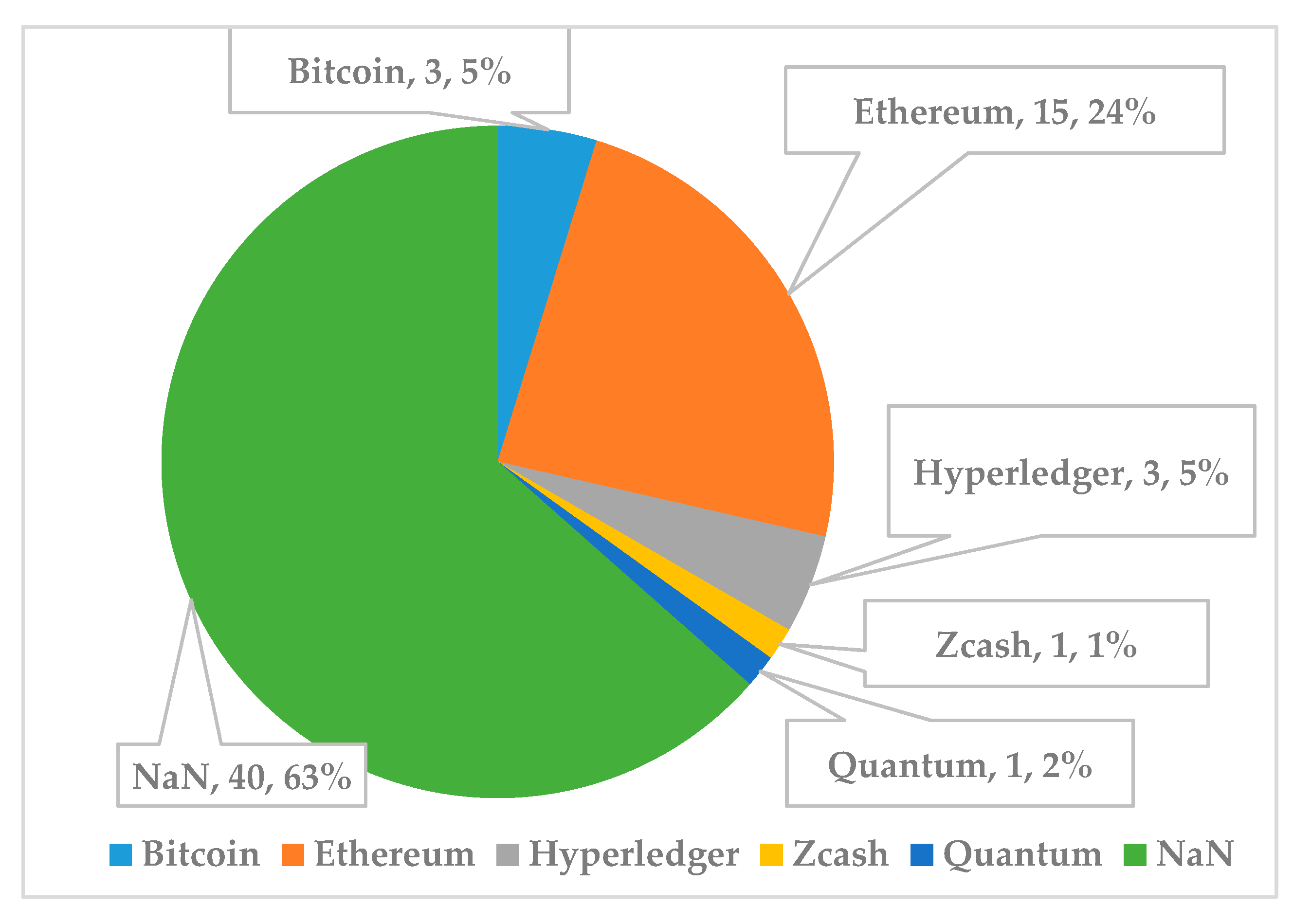
6.4. RQ4: Which Blockchain Platforms/Consensus Models Are Used?
6.5. RQ5: What Are the Future Research Directions for E-Voting with the Blockchain Platforms?
7. Threats to Validity
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Ali, S.T.; Murray, J. An Overview of End-to-End Verifiable Voting Systems. arXiv 2016, arXiv:160508554. [Google Scholar]
- Daramola, O.; Thebus, D. Architecture-Centric Evaluation of Blockchain-Based Smart Contract E-Voting for National Elections. Informatics 2020, 7, 16. [Google Scholar] [CrossRef]
- Ryan, P.Y.A.; Schneider, S.; Teague, V. End-to-End Verifiability in Voting Systems, from Theory to Practice. IEEE Secur. Priv. 2015, 13, 59–62. [Google Scholar] [CrossRef]
- Esteve, J.B.; Goldsmith, B.; Turner, J. International Experience with E-Voting. Available online: https://www.parliament.uk/documents/speaker/digital-democracy/IFESIVreport.pdf (accessed on 15 July 2020).
- Zhang, S.; Wang, L.; Xiong, H. Chaintegrity: Blockchain-enabled large-scale e-voting system with robustness and universal verifiability. Int. J. Inf. Secur. 2020, 19, 323–341. [Google Scholar] [CrossRef]
- Haber, S.; Stornetta, W.S. How to time-stamp a digital document. J. Cryptol. 1991, 3, 99–111. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 27 August 2019).
- Bitcoin Homepage. Available online: https://bitcoin.org/ (accessed on 17 August 2019).
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In Proceedings of the 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar]
- Lin, I.-C.; Liao, T.-C. A Survey of Blockchain Security Issues and Challenges. Int. J. Netw. Secur. 2017, 19. [Google Scholar] [CrossRef]
- Luo, Y.; Chen, Y.; Chen, Q.; Liang, Q. A New Election Algorithm for DPos Consensus Mechanism in Blockchain. In Proceedings of the 2018 7th International Conference on Digital Home (ICDH), Guilin, China, 30 November–1 December 2018; pp. 116–120. [Google Scholar]
- Solat, S. RDV: An Alternative to Proof-of-Work and a Real Decentralized Consensus for Blockchain. arXiv 2019, arXiv:170705091. [Google Scholar]
- Hölbl, M.; Kompara, M.; Kamišalić, A.; Nemec Zlatolas, L. A Systematic Review of the Use of Blockchain in Healthcare. Symmetry 2018, 10, 470. [Google Scholar] [CrossRef]
- Hanifatunnisa, R.; Rahardjo, B. Blockchain based e-voting recording system design. In Proceedings of the 2017 11th International Conference on Telecommunication Systems Services and Applications (TSSA), Lombok, Indonesia, 26–27 October 2017; pp. 1–6. [Google Scholar]
- Moura, T.; Gomes, A. Blockchain Voting and its effects on Election Transparency and Voter Confidence. In Proceedings of the 18th Annual International Conference on Digital Government Research, Staten Island, NY, USA, 7–9 June 2017; pp. 574–575. [Google Scholar]
- Tan, B.Q.; Wang, F.; Liu, J.; Kang, K.; Costa, F. A Blockchain-Based Framework for Green Logistics in Supply Chains. Sustainability 2020, 12, 4656. [Google Scholar] [CrossRef]
- Yahaya, A.S.; Javaid, N.; Alzahrani, F.A.; Rehman, A.; Ullah, I.; Shahid, A.; Shafiq, M. Blockchain Based Sustainable Local Energy Trading Considering Home Energy Management and Demurrage Mechanism. Sustainability 2020, 12, 3385. [Google Scholar] [CrossRef]
- Gupta, Y.; Shorey, R.; Kulkarni, D.; Tew, J. The applicability of blockchain in the Internet of Things. In Proceedings of the 2018 10th International Conference on Communication Systems & Networks (COMSNETS), Bengaluru, India, 3–7 January 2018; pp. 561–564. [Google Scholar]
- Javed, M.U.; Javaid, N.; Aldegheishem, A.; Alrajeh, N.; Tahir, M.; Ramzan, M. Scheduling Charging of Electric Vehicles in a Secured Manner by Emphasizing Cost Minimization Using Blockchain Technology and IPFS. Sustainability 2020, 12, 5151. [Google Scholar] [CrossRef]
- Villegas-Ch, W.; Palacios-Pacheco, X.; Román-Cañizares, M. Integration of IoT and Blockchain to in the Processes of a University Campus. Sustainability 2020, 12, 4970. [Google Scholar] [CrossRef]
- Raikwar, M.; Mazumdar, S.; Ruj, S.; Sen Gupta, S.; Chattopadhyay, A.; Lam, K.-Y. A Blockchain Framework for Insurance Processes. In Proceedings of the 2018 9th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Paris, France, 26–28 February 2018; pp. 1–4. [Google Scholar]
- Li, J.; Liu, Z.; Chen, L.; Chen, P.; Wu, J. Blockchain-Based Security Architecture for Distributed Cloud Storage. In Proceedings of the 2017 IEEE International Symposium on Parallel and Distributed Processing with Applications and 2017 IEEE International Conference on Ubiquitous Computing and Communications (ISPA/IUCC), Guangzhou, China, 12–15 December 2017; pp. 408–411. [Google Scholar]
- Yuan, Y.; Wang, F.-Y. Towards blockchain-based intelligent transportation systems. In Proceedings of the 2016 IEEE 19th International Conference on Intelligent Transportation Systems (ITSC), Rio de Janeiro, Brazil, 1–4 November 2016; pp. 2663–2668. [Google Scholar]
- DeCusatis, C.; Zimmermann, M.; Sager, A. Identity-based network security for commercial blockchain services. In Proceedings of the 2018 IEEE 8th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 8–10 January 2018; pp. 474–477. [Google Scholar]
- Demestichas, K.; Peppes, N.; Alexakis, T.; Adamopoulou, E. Blockchain in Agriculture Traceability Systems: A Review. Appl. Sci. 2020, 10, 4113. [Google Scholar] [CrossRef]
- Zhao, Z.; Chan, T.-H.H. How to Vote Privately Using Bitcoin. In Information and Communications Security; Qing, S., Okamoto, E., Kim, K., Liu, D., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2016; Volume 9543, pp. 82–96. ISBN 978-3-319-29813-9. [Google Scholar]
- Jardí-Cedó, R.; Pujol-Ahulló, J.; Castellà-Roca, J.; Viejo, A. Study on poll-site voting and verification systems. Comput. Secur. 2012, 31, 989–1010. [Google Scholar] [CrossRef]
- Oo, H.N.; Aung, A.M. A Survey of Different Electronic Voting Systems. Int. J. Sci. Eng. Technol. Res. IJSETR 2014, 3, 3460–3464. [Google Scholar]
- Fatrah, A.; El Kafhali, S.; Haqiq, A.; Salah, K. Proof of Concept Blockchain-based Voting System. In Proceedings of the 4th International Conference on Big Data and Internet of Things, Tangier-Tetuan, Morocco, 23–24 October 2019; pp. 1–5. [Google Scholar]
- Yi, H. Securing e-voting based on blockchain in P2P network. EURASIP J. Wirel. Commun. Netw. 2019, 2019, 137. [Google Scholar] [CrossRef]
- Anane, R.; Freeland, R.; Theodoropoulos, G. e-Voting Requirements and Implementation. In Proceedings of the 9th IEEE International Conference on E-Commerce Technology and the 4th IEEE International Conference on Enterprise Computing, E-Commerce and E-Services (CEC-EEE 2007), Tokyo, Japan, 23–26 July 2007; pp. 382–392. [Google Scholar]
- Fujioka, A.; Okamoto, T.; Ohta, K. A practical secret voting scheme for large scale elections. In Advances in Cryptology—AUSCRYPT’92; Seberry, J., Zheng, Y., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 1993; Volume 718, pp. 244–251. ISBN 978-3-540-57220-6. [Google Scholar]
- Keshk, A.E.; Abdul-Kader, H.M. Development of remotely secure e-voting system. In Proceedings of the 2007 ITI 5th International Conference on Information and Communications Technology, Cairo, Egypt, 16–18 December 2007; pp. 235–243. [Google Scholar]
- Zhang, W.; Yuan, Y.; Hu, Y.; Huang, S.; Cao, S.; Chopra, A.; Huang, S. A Privacy-Preserving Voting Protocol on Blockchain. In Proceedings of the 2018 IEEE 11th International Conference on Cloud Computing (CLOUD), San Francisco, CA, USA, 2–7 July 2018; pp. 401–408. [Google Scholar]
- Ryan, P.Y.A.; Bismark, D.; Heather, J.; Schneider, S.; Xia, Z. PrÊt À Voter: A Voter-Verifiable Voting System. IEEE Trans. Inf. Forensics Secur. 2009, 4, 662–673. [Google Scholar] [CrossRef]
- Bokslag, W.; de Vries, M. Evaluating e-voting: Theory and practice. arXiv 2016, arXiv:160202509. [Google Scholar]
- Sun, X.; Wang, Q.; Kulicki, P. A Simple Voting Protocol on Quantum Blockchain. Int. J. Theor. Phys. 2019, 58, 275–281. [Google Scholar] [CrossRef]
- Liu, Y.; Wang, Q. An E-voting Protocol Based on Blockchain. International Association for Cryptologic Research. 2017. Available online: https://eprint.iacr.org/2017/1043.pdf (accessed on 28 August 2019).
- Osgood, R. The Future of Democracy: Blockchain Voting. Available online: http://www.cs.tufts.edu/comp/116/archive/fall2016/rosgood.pdf (accessed on 26 June 2020).
- Petersen, K.; Feldt, R.; Mujtaba, S.; Mattsson, M. Systematic mapping studies in software engineering. In Proceeding of the 12 International Conference on Evaluation and Assessment in Software Engineering, Swindon, UK, 26–27 June 2008; pp. 68–77. [Google Scholar]
- Riemann, R.; Grumbach, S. Distributed Protocols at the Rescue for Trustworthy Online Voting. arXiv 2017, arXiv:170504480. [Google Scholar]
- Tarasov, P.; Tewari, H. Internet Voting Using Zcash. International Association for Cryptologic Research 2017. Available online: https://eprint.iacr.org/2017/585.pdf (accessed on 18 August 2019).
- Li, K.; Li, H.; Hou, H.; Li, K.; Chen, Y. Proof of Vote: A High-Performance Consensus Protocol Based on Vote Mechanism & Consortium Blockchain. In Proceedings of the 2017 IEEE 19th International Conference on High Performance Computing and Communications; IEEE 15th International Conference on Smart City; IEEE 3rd International Conference on Data Science and Systems (HPCC/SmartCity/DSS), Bangkok, Thailand, 18–20 December 2017; pp. 466–473. [Google Scholar]
- Akbari, E.; Wu, Q.; Zhao, W.; Arabnia, H.R.; Yang, M.Q. From Blockchain to Internet-Based Voting. In Proceedings of the 2017 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 14–16 December 2017; pp. 218–221. [Google Scholar]
- Shaheen, S.H.; Yousaf, M.; Jalil, M. Temper proof data distribution for universal verifiability and accuracy in electoral process using blockchain. In Proceedings of the 2017 13th International Conference on Emerging Technologies (ICET), Islamabad, Pakistan, 27–28 December 2017; pp. 1–6. [Google Scholar]
- Wang, B.; Sun, J.; He, Y.; Pang, D.; Lu, N. Large-scale Election Based On Blockchain. Procedia Comput. Sci. 2018, 129, 234–237. [Google Scholar] [CrossRef]
- Hardwick, F.S.; Gioulis, A.; Akram, R.N.; Markantonakis, K. E-Voting with Blockchain: An E-Voting Protocol with Decentralisation and Voter Privacy. arXiv 2018, arXiv:180510258. [Google Scholar]
- Bao, Z.; Wang, B.; Shi, W. A Privacy-Preserving, Decentralized and Functional Bitcoin E-Voting Protocol. In Proceedings of the 2018 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Advanced & Trusted Computing, Scalable Computing & Communications, Cloud & Big Data Computing, Internet of People and Smart City Innovation (SmartWorld/SCALCOM/UIC/ATC/CBDCom/IOP/SCI), Guangzhou, China, 8–12 October 2018; pp. 252–256. [Google Scholar]
- Panja, S.; Roy, B.K. A Secure End-to-End Verifiable E-Voting System Using Zero Knowledge Based Blockchain. International Association for Cryptologic Research 2018. Available online: https://eprint.iacr.org/2018/466.pdf (accessed on 18 August 2019).
- Wu, W.-J.L. An efficient and effective Decentralized Anonymous Voting System. arXiv 2018, arXiv:180406674. [Google Scholar]
- Hjálmarsson, F.P.; Hreioarsson, G.K.; Hamdaqa, M.; Hjalmtysson, G. Blockchain-Based E-Voting System. In Proceedings of the 2018 IEEE 11th International Conference on Cloud Computing (CLOUD), San Francisco, CA, USA, 2–7 July 2018; pp. 983–986. [Google Scholar]
- Kshetri, N.; Voas, J. Blockchain-Enabled E-Voting. IEEE Softw. 2018, 35, 95–99. [Google Scholar] [CrossRef]
- Dagher, G.G.; Marella, P.B.; Milojkovic, M.; Mohler, J. BroncoVote: Secure Voting System using Ethereum’s Blockchain. In Proceedings of the 4th International Conference on Information Systems Security and Privacy, Funchal, Madeira, Portugal, 22–24 January 2018; pp. 96–107. [Google Scholar]
- Srivastava, G.; Dhar Dwivedi, A.; Singh, R. Crypto-democracy: A Decentralized Voting Scheme using Blockchain Technology. In Proceedings of the 15th International Joint Conference on e-Business and Telecommunications, Porto, Portugal, 26–28 July 2018; pp. 674–679. [Google Scholar]
- Srivastava, G.; Dwivedi, A.D.; Singh, R. Phantom Protocol as the New Crypto-Democracy. In Computer Information Systems and Industrial Management; Saeed, K., Homenda, W., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2018; Volume 11127, pp. 499–509. ISBN 978-3-319-99953-1. [Google Scholar]
- Fusco, F.; Lunesu, M.I.; Pani, F.E.; Pinna, A. Crypto-voting, a Blockchain based e-Voting System. In Proceedings of the 10th International Joint Conference on Knowledge Discovery, Knowledge Engineering and Knowledge Management, Seville, Spain, 18–20 September 2018; pp. 223–227. [Google Scholar]
- Lai, W.-J.; Hsieh, Y.; Hsueh, C.-W.; Wu, J.-L. DATE: A Decentralized, Anonymous, and Transparent E-voting System. In Proceedings of the 2018 1st IEEE International Conference on Hot Information-Centric Networking (HotICN), Shenzhen, China, 15–17 August 2018; pp. 24–29. [Google Scholar]
- Heiberg, S.; Kubjas, I.; Siim, J.; Willemson, J. On Trade-offs of Applying Blockchains for Electronic Voting Bulletin Boards. International Association for Cryptologic Research 2018. Available online: https://eprint.iacr.org/2018/685.pdf (accessed on 18 August 2019).
- Venkatapur, R.B.; Prabhu, B.; Navya, A.; Roopini, R.; Niranjan, S.A. Electronic Voting Machine Based on Blockchain Technology and Aadhar Verification. Int. J. Innov. Eng. Sci. 2018, 3, 12–15. [Google Scholar]
- Yu, B.; Liu, J.; Amin, S.; Nepal, S.; Steinfeld, R.; Rimba, P.; Au, M.H. Platform-Independent Secure Blockchain-Based Voting System. International Association for Cryptologic Research 2018. Available online: https://eprint.iacr.org/2018/657.pdf (accessed on 18 August 2019).
- Bartolucci, S.; Bernat, P.; Joseph, D. SHARVOT: Secret SHARe-based VOTing on the blockchain. In Proceedings of the 1st International Workshop on Emerging Trends in Software Engineering for Blockchain-WETSEB’18, Gothenburg, Sweden, 27 May–3 June 2018; pp. 30–34. [Google Scholar]
- Yavuz, E.; Koc, A.K.; Cabuk, U.C.; Dalkilic, G. Towards secure e-voting using ethereum blockchain. In Proceedings of the 2018 6th International Symposium on Digital Forensic and Security (ISDFS), Antalya, Turkey, 22–25 March 2018; pp. 1–7. [Google Scholar]
- Pawlak, M.; Poniszewska-Marańda, A.; Kryvinska, N. Towards the intelligent agents for blockchain e-voting system. Procedia Comput. Sci. 2018, 141, 239–246. [Google Scholar] [CrossRef]
- Dricot, L.; Pereira, O. SoK: Uncentralisable Ledgers and their Impact on Voting Systems. arXiv 2018, arXiv:180108064. [Google Scholar]
- Shukla, S.; Thasmiya, A.N.; Shashank, D.O.; Mamatha, H.R. Online Voting Application Using Ethereum Blockchain. In Proceedings of the 2018 International Conference on Advances in Computing, Communications and Informatics (ICACCI), Bangalore, India, 19–22 September 2018; pp. 873–880. [Google Scholar]
- Khoury, D.; Kfoury, E.F.; Kassem, A.; Harb, H. Decentralized Voting Platform Based on Ethereum Blockchain. In Proceedings of the 2018 IEEE International Multidisciplinary Conference on Engineering Technology (IMCET), Beirut, Lebanon, 14–16 November 2018; pp. 1–6. [Google Scholar]
- Adiputra, C.K.; Hjort, R.; Sato, H. A Proposal of Blockchain-Based Electronic Voting System. In Proceedings of the 2018 Second World Conference on Smart Trends in Systems, Security and Sustainability (WorldS4), London, UK, 30–31 October 2018; pp. 22–27. [Google Scholar]
- Na, S.; Park, Y.B. Web-based Nominal Group Technique Decision Making Tool Using Blockchain. In Proceedings of the 2018 International Conference on Platform Technology and Service (PlatCon), Jeju, Korea, 29–31 January 2018; pp. 1–6. [Google Scholar]
- Li, Y.; Susilo, W.; Yang, G.; Yu, Y.; Liu, D.; Guizani, M. A Blockchain-based Self-tallying Voting Scheme in Decentralized IoT. arXiv 2019, arXiv:190203710. [Google Scholar]
- Leonardos, S.; Reijsbergen, D.; Piliouras, G. Weighted Voting on the Blockchain: Improving Consensus in Proof of Stake Protocols. In Proceedings of the 2019 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), Seoul, Korea, 14–17 May 2019; pp. 376–384. [Google Scholar]
- Zhang, Q.; Xu, B.; Jing, H.; Zheng, Z. Ques-Chain: An Ethereum Based E-Voting System. arXiv 2019, arXiv:190505041. [Google Scholar]
- Schiedermeier, M.; Hasan, O.; Mayer, T.; Brunie, L.; Kosch, H. A transparent referendum protocol with immutable proceedings and verifiable outcome for trustless networks. arXiv 2019, arXiv:190906462. [Google Scholar]
- Sadia, K.; Masuduzzaman, M.; Paul, R.K.; Islam, A. Blockchain Based Secured E-voting by Using the Assistance of Smart Contract. arXiv 2019, arXiv:191013635. [Google Scholar]
- Fan, X.; Li, P.; Zeng, Y.; Zhou, X. Implement Liquid Democracy on Ethereum: A Fast Algorithm for Realtime Self-tally Voting System. arXiv 2020, arXiv:191108774. [Google Scholar]
- Bulut, R.; Kantarci, A.; Keskin, S.; Bahtiyar, S. Blockchain-Based Electronic Voting System for Elections in Turkey. In Proceedings of the 2019 4th International Conference on Computer Science and Engineering (UBMK), Samsun, Turkey, 11–15 September 2019; pp. 183–188. [Google Scholar]
- Gajek, S.; Lewandowsky, M. Trustless, Censorship-Resilient and Scalable Votings in the Permission-based Blockchain Model. Int. Assoc. Cryptologic Res. 2019. [Google Scholar]
- Lee, J.; Choi, J.; Kim, J.; Oh, H. SAVER: SNARK-friendly, Additively-homomorphic, and Verifiable Encryption and decryption with Rerandomization. Int. Assoc. Cryptologic Res. 2019. [Google Scholar]
- Dimitriou, T. Efficient, Coercion-free and Universally Verifiable Blockchain-based Voting. International Association for Cryptologic Research 2019. Available online: https://eprint.iacr.org/2019/617.pdf (accessed on 11 November 2019).
- Sudharsan, B.; Tharun, R.V.; Krishna, N.M.P.; Raj, B.J.; Arvindh, S.M.; Alagappan, M. Secured Electronic Voting System Using the Concepts of Blockchain. In Proceedings of the 2019 IEEE 10th Annual Information Technology, Electronics and Mobile Communication Conference (IEMCON), Vancouver, BC, Canada, 17–19 October 2019; pp. 0675–0681. [Google Scholar]
- Vijayalakshmi, V.; Vimal, S. A Novel P2P based System with Blockchain for Secured Voting Scheme. In Proceedings of the 2019 Fifth International Conference on Science Technology Engineering and Mathematics (ICONSTEM), Chennai, India, 14–15 March 2019; pp. 153–156. [Google Scholar]
- Bosri, R.; Uzzal, A.R.; Omar, A.A.; Hasan, A.S.M.T.; Bhuiyan, M.Z.A. Towards a Privacy-Preserving Voting System Through Blockchain Technologies. In Proceedings of the 2019 IEEE Intl Conf on Dependable, Autonomic and Secure Computing, Intl Conf on Pervasive Intelligence and Computing, Intl Conf on Cloud and Big Data Computing, Intl Conf on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech), Fukuoka, Japan, 5–8 August 2019; pp. 602–608. [Google Scholar]
- Lyu, J.; Jiang, Z.L.; Wang, X.; Nong, Z.; Au, M.H.; Fang, J. A Secure Decentralized Trustless E-Voting System Based on Smart Contract. In Proceedings of the 2019 18th IEEE International Conference on Trust, Security And Privacy In Computing And Communications/13th IEEE International Conference on Big Data Science And Engineering (TrustCom/BigDataSE), Rotorua, New Zealand, 5–8 August 2019; pp. 570–577. [Google Scholar]
- Teja, K.; Shravani, M.; Simha, C.Y.; Kounte, M.R. Secured voting through Blockchain technology. In Proceedings of the 2019 3rd International Conference on Trends in Electronics and Informatics (ICOEI), Tirunelveli, India, 23–25 April 2019; pp. 1416–1419. [Google Scholar]
- Murtaza, M.H.; Alizai, Z.A.; Iqbal, Z. Blockchain Based Anonymous Voting System Using zkSNARKs. In Proceedings of the 2019 International Conference on Applied and Engineering Mathematics (ICAEM), Taxila, Pakistan, 27–29 August 2019; pp. 209–214. [Google Scholar]
- Sathya, V.; Sarkar, A.; Paul, A.; Mishra, S. Block Chain Based Cloud Computing Model on EVM Transactions for Secure Voting. In Proceedings of the 2019 3rd International Conference on Computing Methodologies and Communication (ICCMC), Erode, India, 27–29 March 2019; pp. 1075–1079. [Google Scholar]
- Bellini, E.; Ceravolo, P.; Damiani, E. Blockchain-Based E-Vote-as-a-Service. In Proceedings of the 2019 IEEE 12th International Conference on Cloud Computing (CLOUD), Milan, Italy, 8–13 July 2019; pp. 484–486. [Google Scholar]
- Gao, S.; Zheng, D.; Guo, R.; Jing, C.; Hu, C. An Anti-Quantum E-Voting Protocol in Blockchain with Audit Function. IEEE Access 2019, 7, 115304–115316. [Google Scholar] [CrossRef]
- Vangulick, D.; Cornelusse, B.; Ernst, D. Blockchain: A Novel Approach for the Consensus Algorithm Using Condorcet Voting Procedure. In Proceedings of the 2019 IEEE International Conference on Decentralized Applications and Infrastructures (DAPPCON), Newark, CA, USA, 4–9 April 2019; pp. 1–10. [Google Scholar]
- Matile, R.; Rodrigues, B.; Scheid, E.; Stiller, B. CaIV: Cast-as-Intended Verifiability in Blockchain-based Voting. In Proceedings of the 2019 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), Seoul, Korea, 14–17 May 2019; pp. 24–28. [Google Scholar]
- Thuy, L.V.-C.; Cao-Minh, K.; Dang-Le-Bao, C.; Nguyen, T.A. Votereum: An Ethereum-Based E-Voting System. In Proceedings of the 2019 IEEE-RIVF International Conference on Computing and Communication Technologies (RIVF), Danang, Vietnam, 20–22 March 2019; pp. 1–6. [Google Scholar]
- Shahzad, B.; Crowcroft, J. Trustworthy Electronic Voting Using Adjusted Blockchain Technology. IEEE Access 2019, 7, 24477–24488. [Google Scholar] [CrossRef]
- Chaieb, M.; Koscina, M.; Yousfi, S.; Lafourcade, P.; Robbana, R. DABSTERS: Distributed Authorities using Blind Signature to Effect Robust Security in e-Voting. In Proceedings of the 16th International Joint Conference on e-Business and Telecommunications, Prague, Czech Republic, 26–28 July 2019; pp. 228–235. [Google Scholar]
- Khan, K.M.; Arshad, J.; Khan, M.M. Investigating performance constraints for blockchain based secure e-voting system. Future Gener. Comput. Syst. 2020, 105, 13–26. [Google Scholar] [CrossRef]
- Johnson, D. Blockchain-Based Voting in the US and EU Constitutional Orders: A Digital Technology to Secure Democratic Values? Eur. J. Risk Regul. 2019, 10, 330–358. [Google Scholar] [CrossRef]
- Li, J.; Wang, X.; Huang, Z.; Wang, L.; Xiang, Y. Multi-level multi-secret sharing scheme for decentralized e-voting in cloud computing. J. Parallel Distrib. Comput. 2019, 130, 91–97. [Google Scholar] [CrossRef]
- Tso, R.; Liu, Z.-Y.; Hsiao, J.-H. Distributed E-Voting and E-Bidding Systems Based on Smart Contract. Electronics 2019, 8, 422. [Google Scholar] [CrossRef]
- Nevo, S.; Kim, H. How to compare and analyse risks of internet voting versus other modes of voting. Electron. Gov. Int. J. 2006, 3, 105. [Google Scholar] [CrossRef]
- Abazorius, A. MIT Researchers Identify Security Vulnerabilities in Voting App. Available online: http://news.mit.edu/2020/voting-voatz-app-hack-issues-0213 (accessed on 3 April 2020).
- Lauer, T.W. The risk of e-voting. Electron. J. E-Gov. 2004, 2, 177–186. [Google Scholar]
- Cardillo, A.; Essex, A. The Threat of SSL/TLS Stripping to Online Voting. In E-Vote-ID 2018: Electronic Voting; Krimmer, R., Volkamer, M., Braun Binder, N., Kersting, N., Pereira, O., Schürmann, C., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2018; Volume 11143, pp. 35–50. ISBN 978-3-030-00419-4. [Google Scholar]
- Susskind, J. Decrypting Democracy: Incentivizing Blockchain Voting Technology for an Improved Election System. San Diego Law Rev. 2017, 54, 785–821. [Google Scholar]
- Bernhard, M.; Benaloh, J.; Alex Halderman, J.; Rivest, R.L.; Ryan, P.Y.A.; Stark, P.B.; Teague, V.; Vora, P.L.; Wallach, D.S. Public Evidence from Secret Ballots. In Electronic Voting; Krimmer, R., Volkamer, M., Braun Binder, N., Kersting, N., Pereira, O., Schürmann, C., Eds.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2017; Volume 10615, pp. 84–109. ISBN 978-3-319-68686-8. [Google Scholar]
- Palas Nogueira, J.; de Sá-Soares, F. Trust in E-Voting Systems: A Case Study. In Knowledge and Technologies in Innovative Information Systems; Lecture Notes in Business Information Processing; Rahman, H., Mesquita, A., Ramos, I., Pernici, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 129, pp. 51–66. ISBN 978-3-642-33243-2. [Google Scholar]
- Achieng, M.; Ruhode, E. The adoption and challenges of electronic voting technologies within the South African context. arXiv 2013, arXiv:13122406. [Google Scholar] [CrossRef]
- Security Assessment of Winvote Voting Equipment for Department of Elections. Available online: https://www.wired.com/wp-content/uploads/2015/08/WINVote-final.pdf (accessed on 3 April 2020).
- Zetter, K. Experts Find Serious Problems with Switzerland’s Online Voting System Before Public Penetration Test Even Begins. Available online: https://www.vice.com/en_us/article/vbwz94/experts-find-serious-problems-with-switzerlands-online-voting-system-before-public-penetration-test-even-begins (accessed on 8 January 2020).
- Kuenzi, R. These are the Arguments that Sank E-Voting in Switzerland. Available online: https://www.swissinfo.ch/eng/e-voting_these-are-the-arguments-that-sank-e-voting-in-switzerl;/45136608 (accessed on 8 January 2020).
- Lewis, S.J.; Pereira, O.; Teague, V. The Use of Trapdoor Commitments in Bayer-Groth Proofs and the Implications for the Verifiabilty of the Scytl-SwissPost Internet Voting System. Available online: https://people.eng.unimelb.edu.au/vjteague/UniversalVerifiabilitySwissPost.pdf (accessed on 3 April 2020).
- Stone, J. Backdoor Discovered in Swiss Voting System Would Have Allowed Hackers to Alter Votes. Available online: https://www.cyberscoop.com/swiss-voting-system-flaw-encryption/ (accessed on 3 April 2020).
- Specter, M.A.; Koppel, J.; Weitzner, D. The Ballot is Busted Before the Blockchain: A Security Analysis of Voatz, the First Internet Voting Application Used in U.S. Federal Elections. Available online: https://www.usenix.org/system/files/sec20-specter.pdf (accessed on 3 June 2020).
- Bollinger, L.C.; McRobbie, M.A. Ensuring the Integrity of Elections. In Securing the Vote: Protecting American Democracy; National Academies of Sciences: Washington, DC, USA, 2018; pp. 103–105. ISBN 978-0-309-47647-8. [Google Scholar]
- Abuidris, Y.; Hassan, A.; Hadabi, A.; Elfadul, I. Risks and Opportunities of Blockchain Based on E-Voting Systems. In Proceedings of the 2019 16th International Computer Conference on Wavelet Active Media Technology and Information Processing, Chengdu, China, 14–15 December 2019; pp. 365–368. [Google Scholar]
- Juels, A.; Eyal, I.; Naor, O. Blockchains won’t Fix Internet Voting Security could Make it Worse. Available online: https://theconversation.com/blockchains-wont-fix-internet-voting-security-and-could-make-it-worse-104830 (accessed on 3 April 2020).
- Goodman, R.; Halderman, J.A. Internet Voting is Happening Now. Available online: https://slate.com/technology/2020/01/internet-voting-could-destroy-our-elections.html (accessed on 15 July 2020).
- Park, S.; Specter, M.; Narula, N.; Rivest, R.L. Going from Bad to Worse: From Internet Voting to Blockchain Voting. Available online: https://people.csail.mit.edu/rivest/pubs/PSNR20.pdf (accessed on 17 July 2020).
- Bull, C.; Gjøsteen, K.; Nore, H. Faults in Norwegian Internet Voting; TUT Press: Lochau, Austria; Bregenz, Austria, 2018; pp. 166–169. [Google Scholar]
- Pathak, A.; Wasay, A.; Singh, C.; Bhavan, R.; Umale, J. Design and implementation of a secure and robust voting system based on blockchain. Int. J. Adv. Res. Ideas Innov. Technol. 2018, 4, 869–875. [Google Scholar]
- McCorry, P.; Shahandashti, S.F.; Hao, F. A Smart Contract for Boardroom Voting with Maximum Voter Privacy. In Financial Cryptography and Data Security; Kiayias, A., Ed.; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2017; Volume 10322, pp. 357–375. ISBN 978-3-319-70971-0. [Google Scholar]
- Mercer, R. Privacy on the Blockchain: Unique Ring Signatures. arXiv 2016, arXiv:161201188. [Google Scholar]
- Roopak, T.M.; Sumathi, R. Electronic Voting based on Virtual ID of Aadhar using Blockchain Technology. In Proceedings of the 2020 2nd International Conference on Innovative Mechanisms for Industry Applications (ICIMIA), Bangalore, India, 5–7 March 2020; pp. 71–75. [Google Scholar]
- Juno Bella Gracia, S.V.; Raghav, D.; Santhoshkumar, R.; Velprakash, B. Blockchain Based Aadhaar. In Proceedings of the 2019 3rd International Conference on Computing and Communications Technologies (ICCCT), Chennai, India, 21–22 February 2019; pp. 173–177. [Google Scholar]
- Domestic and Overseas Voters Gender Statistics. Available online: http://www.ysk.gov.tr/doc/dosyalar/docs/24Haziran2018/2018CBMV-SecmenCinsiyet.pdf (accessed on 18 August 2019).
- Xu, J.J. Are blockchains immune to all malicious attacks? Financ. Innov. 2016, 2, 25. [Google Scholar] [CrossRef]
- Wang, S.; Wang, C.; Hu, Q. Corking by Forking: Vulnerability Analysis of Blockchain. In Proceedings of the IEEE INFOCOM 2019-IEEE Conference on Computer Communications, Paris, France, 29 April–2 May 2019; pp. 829–837. [Google Scholar]
- Saad, M.; Spaulding, J.; Njilla, L.; Kamhoua, C.; Shetty, S.; Nyang, D.; Mohaisen, A. Exploring the Attack Surface of Blockchain: A Systematic Overview. arXiv 2019, arXiv:190403487. [Google Scholar]
- Ramezan, G.; Leung, C.; Jane Wang, Z. A Strong Adaptive, Strategic Double-Spending Attack on Blockchains. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 1219–1227. [Google Scholar]
- Vegendla, A.; Duc, A.N.; Gao, S.; Sindre, G. A Systematic Mapping Study on Requirements Engineering in Software Ecosystems. J. Inf. Technol. Res. 2018, 11, 49–69. [Google Scholar] [CrossRef]
- Kosar, T.; Bohra, S.; Mernik, M. A Systematic Mapping Study driven by the margin of error. J. Syst. Softw. 2018, 144, 439–449. [Google Scholar] [CrossRef]
- Silva, R.A.; de Souza, S.D.R.S.; de Souza, P.S.L. A systematic review on search based mutation testing. Inf. Softw. Technol. 2017, 81, 19–35. [Google Scholar] [CrossRef]
| Property | Public | Private | Consortium |
|---|---|---|---|
| Management | No Centralized Management | Single organization | Multiple organization |
| Participants | Permissionless | Permissioned | Permissioned |
| Centralized | no | Yes | partial |
| Efficiency | Low | High | High |
| Consensus Determination | All miners | Organization participating | Selected miners |
| Transaction duration | Long | Short | Short |
| Databases | Blockchain | E-Voting | Blockchain Ballot |
|---|---|---|---|
| sciencedirect.com (Future Gen. Comp. Sys, Comp. & Sec., Journal of Network and Comp. App. Procedia Comp. Science) | 317 | 462 | 80 |
| arxiv.org | 1178 | 56 | 7 |
| ieeexplore.ieee.org (conferences and journals) | 3149 | 290 | 24 |
| scitepress.org | 57 | 100 | 5 |
| webofscience.com | 4299 | 740 | 26 |
| springer.com (journal) | 510 | 2123 | 2126 |
| Year | Blockchain |
|---|---|
| 2015 | [26] |
| 2016 | |
| 2017 | [14,38,41,42,43,44,45] |
| 2018 | [11,34,46,47,48,49,50,51,52,53,54,55,56,57,58,59,60,61,62,63,64,65,66,67,68] |
| 2019 | [30,37,69,70,71,72,73,74,75,76,77,78,79,80,81,82,83,84,85,86,87,88,89,90,91,92,93,94,95,96] |
| General | Coin-Based | Privacy | Integrity | Consensus | |
|---|---|---|---|---|---|
| General | [41,52,63,64,68,72,75,81,85,86,94] | [37,83,90,93] | [47,58,73,77] | [44,49,59,79,91] | [54] |
| Coin-Based | [37,83,90,93] | [42,50,62,65,71,74,76] | [26,34,46,48,51] | [22,53,57,60,61,66,80,82,89] | [70,118] |
| Privacy | [47,58,73,77] | [26,34,46,48,51] | [38,46,56,61,84,87,119] | [12] | |
| Integrity | [44,49,59,79,91] | [22,53,57,60,61,66,80,82,89] | [38,46,56,61,84,87,119] | [14,30,67] | [92,95] |
| Consensus | [54] | [70,118] | [12] | [92,95] | [11,22] |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Taş, R.; Tanrıöver, Ö.Ö. A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting. Symmetry 2020, 12, 1328. https://doi.org/10.3390/sym12081328
Taş R, Tanrıöver ÖÖ. A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting. Symmetry. 2020; 12(8):1328. https://doi.org/10.3390/sym12081328
Chicago/Turabian StyleTaş, Ruhi, and Ömer Özgür Tanrıöver. 2020. "A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting" Symmetry 12, no. 8: 1328. https://doi.org/10.3390/sym12081328
APA StyleTaş, R., & Tanrıöver, Ö. Ö. (2020). A Systematic Review of Challenges and Opportunities of Blockchain for E-Voting. Symmetry, 12(8), 1328. https://doi.org/10.3390/sym12081328