Detecting Visualized Malicious Code Through Low-Redundancy Convolution
Abstract
1. Introduction
- (1)
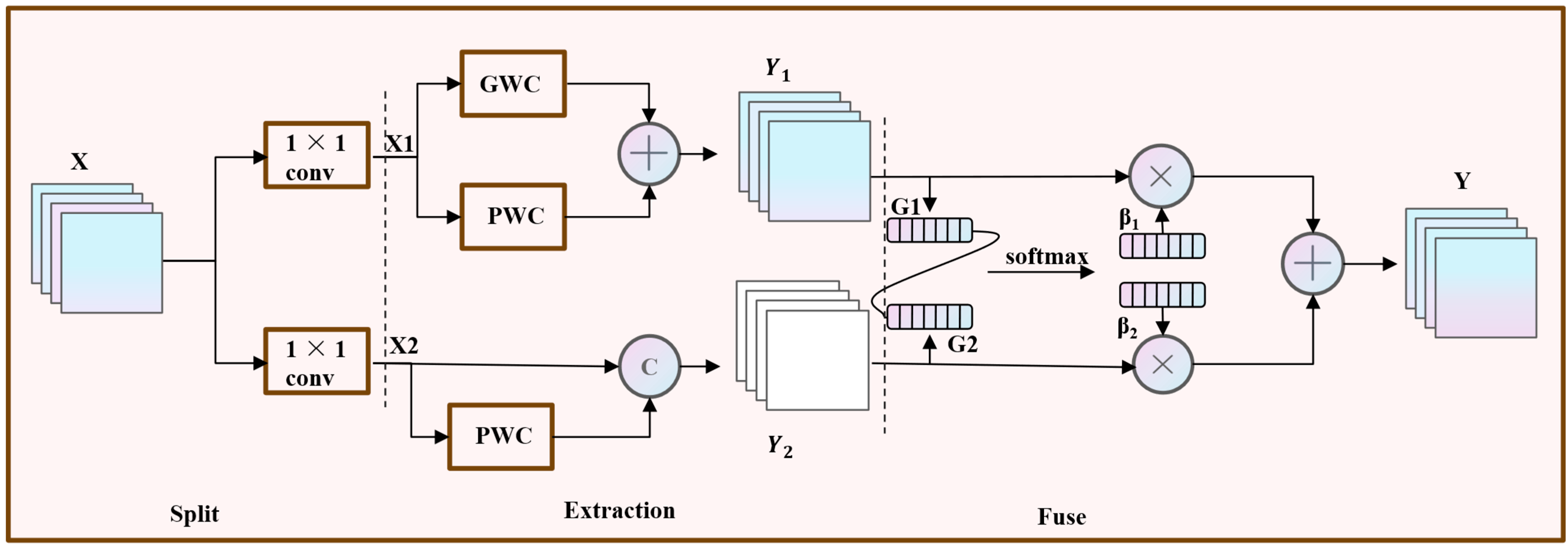
- We propose a novel Low-Redundancy Convolution (LR-Conv) module, specifically designed to address the inherent data characteristics of visualized malware. This module is the first, to our knowledge, to synergistically reduce both spatial redundancy through a Group-Normalization-based gating and reconstruction mechanism, and channel redundancy via an efficient split–transform–fuse strategy. This dual-reduction approach allows for more discriminative feature learning with greater parameter efficiency.
- (2)
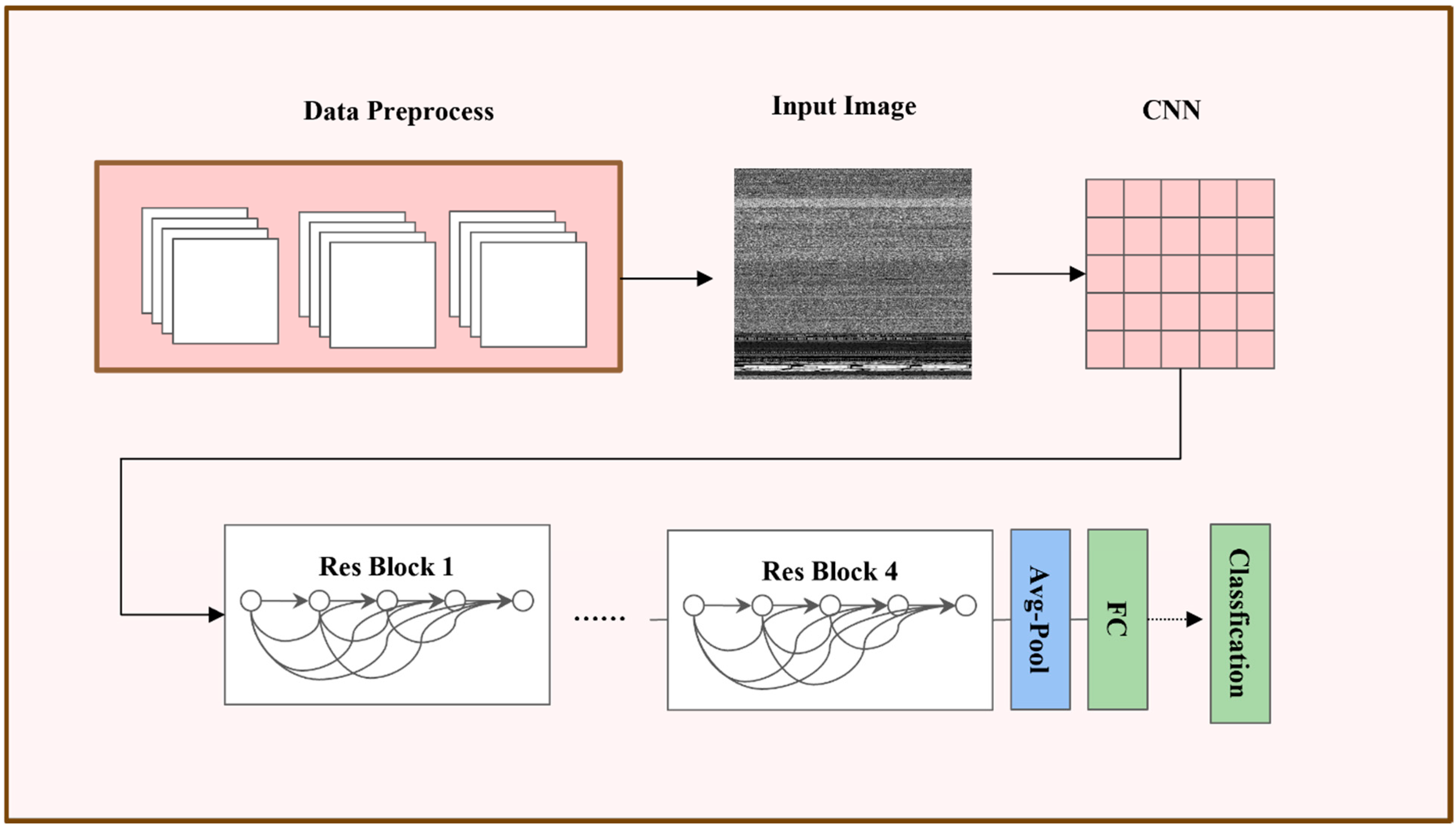
- We design and implement LR-MalConv, a new and efficient deep learning framework for malware detection. By seamlessly integrating the proposed LR-Conv module into a residual network backbone, the framework gains enhanced feature extraction capabilities while significantly reducing the parameter count and computational complexity compared to the standard ResNet architecture.
- (3)
- We conduct extensive experiments on the benchmark Malimg dataset and a newly constructed dataset. Our results demonstrate that LR-MalConv reaches an accuracy of 99.52% on Malimg.
2. Methods
2.1. Model Structure
2.2. Low-Redundancy Convolution
2.2.1. Spatial Redundancy Reduction
2.2.2. Channel Redundancy Reduction
3. Experiments
3.1. Dataset Introduction
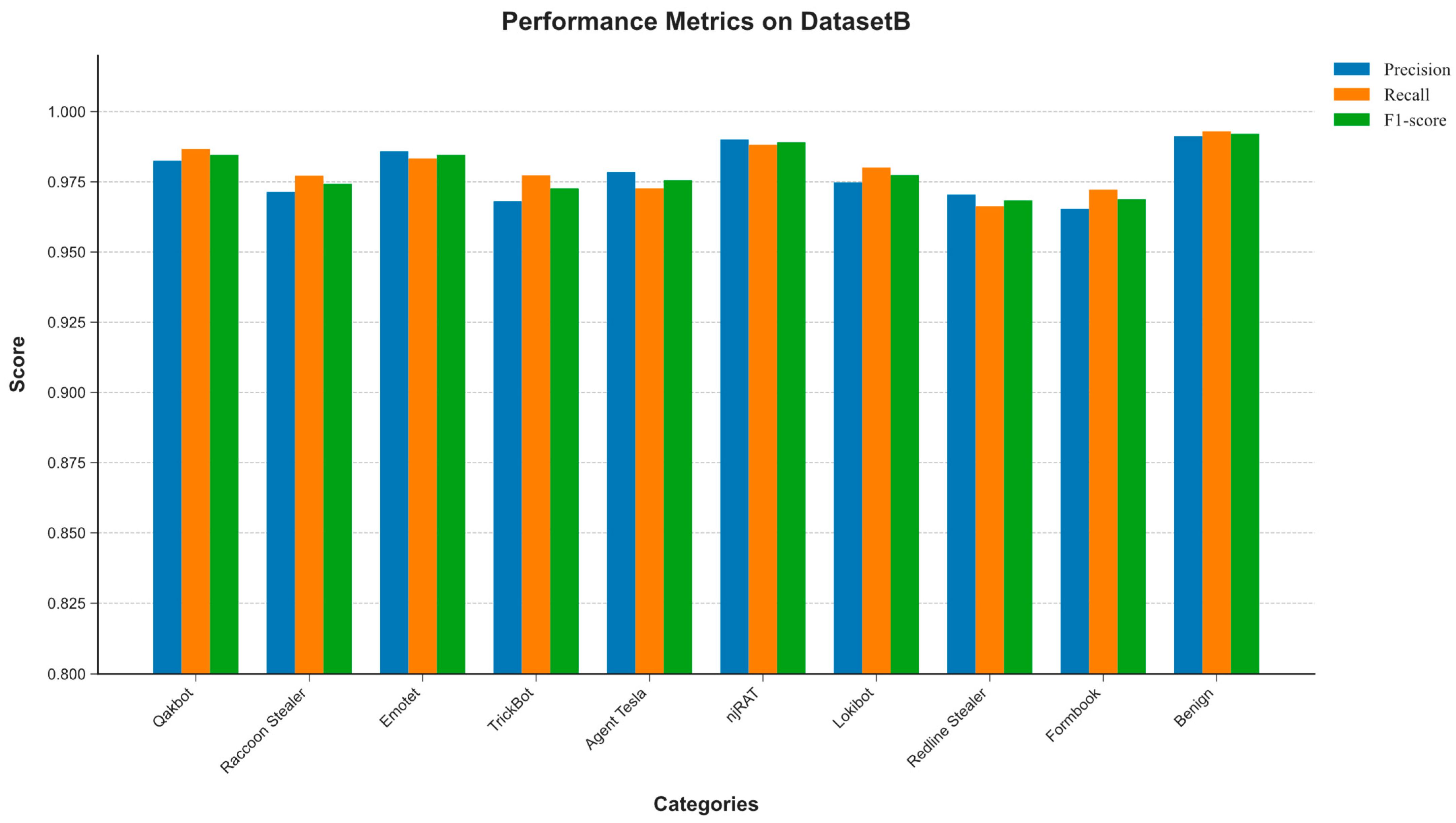
3.2. Result
3.3. Experimental Evaluation
3.4. Ablation Study of the LR-Conv Module
4. Conclusions
5. Limitation and Future Work
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| Conv | Convolution |
| LR | Low-Redundancy |
References
- Rieck, K.; Trinius, P.; Willems, C.; Holz, T. Automatic analysis of malware behavior using machine learning. J. Comput. Secur. 2011, 19, 639–668. [Google Scholar] [CrossRef]
- Amoroso, E. Recent progress in software security. IEEE Softw. 2018, 35, 11–13. [Google Scholar] [CrossRef]
- Santos, I.; Penya, Y.K.; Devesa, J.; Bringas, P.G. N-grams-based file signatures for malware detection. In Proceedings of the 11th International Conference on Enterprise Information Systems, Milan, Italy, 6–10 May 2009; Volume 9, pp. 317–320. [Google Scholar]
- Van Impe, K. Signature-Based Detection with YARA. 2015. Available online: https://securityintelligence.com/signature-based-detection-with-yara/ (accessed on 24 May 2023).
- Drew, J.; Moore, T.; Hahsler, M. Polymorphic malware detection using sequence classification methods. In Proceedings of the 2016 IEEE Security and Privacy Workshops (SPW), San Jose, CA, USA, 22–26 May 2016; pp. 81–87. [Google Scholar]
- Agrawal, R.; Stokes, J.W.; Marinescu, M.; Selvaraj, K. Neural sequential malware detection with parameters. In Proceedings of the ICASSP 2018—2018 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Calgary, AB, Canada, 15–20 April 2018; pp. 2656–2660. [Google Scholar]
- Ki, Y.; Kim, E.; Kim, H.K. A novel approach to detect malware based on API call sequence analysis. Int. J. Distrib. Sensor Netw. 2015, 11, 659101. [Google Scholar] [CrossRef]
- Qiao, Y.; Yang, Y.; Ji, L.; He, J. Analyzing malware by abstracting the frequent itemsets in API call sequences. In Proceedings of the 2013 12th IEEE International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Melbourne, VIC, Australia, 16–18 July 2013; pp. 265–270. [Google Scholar]
- Zhang, Z.; Qi, P.; Wang, W. Dynamic malware analysis with feature engineering and feature learning. Proc. AAAI Conf. Artif. Intell. 2020, 34, 1210–1217. [Google Scholar] [CrossRef]
- Liang, R.; Chen, J.; Wu, C.; He, K.; Wu, Y.; Cao, R.; Du, R.; Zhao, Z.; Liu, Y. VULSEYE: Detect Smart Contract Vulnerabilities via Stateful Directed Graybox Fuzzing. arXiv 2024, arXiv:2408.10116. [Google Scholar] [CrossRef]
- Nataraj, L.; Karthikeyan, S.; Jacob, G.; Manjunath, B.S. Malware images: Visualization and automatic classification. In Proceedings of the 8th International Symposium on Visualization for Cyber Security, Pittsburgh, PA, USA, 20 July 2011; pp. 1–7. [Google Scholar]
- Lecun, Y.; Bottou, L.; Bengio, Y.; Haffner, P. Gradient-Based Learning Applied to Document Recognition. Proc. IEEE 1998, 86, 2278–2324. [Google Scholar] [CrossRef]
- Liu, L.; Wang, B. Malware classification using gray-scale images and ensemble learning. In Proceedings of the 2016 3rd International Conference on Systems and Informatics (ICSAI), Shanghai, China, 19–21 November 2016; pp. 1018–1022. [Google Scholar]
- Vasan, D.; Alazab, M.; Wassan, S.; Safaei, B.; Zheng, Q. Image-Based malware classification using ensemble of CNN architectures (IMCEC). Comput. Secur. 2020, 92, 101748. [Google Scholar] [CrossRef]
- Naeem, H.; Ullah, F.; Naeem, M.R.; Khalid, S.; Vasan, D.; Jabbar, S.; Saeed, S. Malware detection in industrial internet of things based on hybrid image visualization and deep learning model. Ad Hoc Netw. 2020, 105, 102154. [Google Scholar] [CrossRef]
- Wang, X.; Girshick, R.; Gupta, A.; He, K. Non-local Neural Networks. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition (CVPR), Salt Lake City, UT, USA, 18–23 June 2018; pp. 7794–7803. [Google Scholar]
- Hu, J.; Shen, L.; Sun, G. Squeeze-and-Excitation Networks. In Proceedings of the IEEE Conference on Computer vision and pattern recognition (CVPR), Salt Lake City, UT, USA, 18–23 June 2018; pp. 7132–7141. [Google Scholar]
- Krizhevsky, A.; Sutskever, I.; Hinton, G.E. ImageNet Classification with Deep Convolutional Neural Networks. In Advances in Neural Information Processing Systems 25; Pereira, F., Burges, C.J.C., Bottou, L., Weinberger, K.Q., Eds.; Curran Associates, Inc.: New York, NY, USA, 2012; pp. 1097–1105. [Google Scholar]
- Chollet, F. Xception: Deep Learning with Depthwise Separable Convolutions. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition (CVPR), Honolulu, HI, USA, 21–26 July 2017; pp. 1251–1258. [Google Scholar]
- Vaswani, A.; Shazeer, N.; Parmar, N.; Uszkoreit, J.; Jones, L.; Gomez, A.N.; Kaiser, Ł.; Polosukhin, I. Attention Is All You Need. In Advances in Neural Information Processing Systems 30; Guyon, I., Luxburg, U.V., Bengio, S., Wallach, H., Fergus, R., Vishwanathan, S., Garnett, R., Eds.; Curran Associates, Inc.: New York, NY, USA, 2017; pp. 5998–6008. [Google Scholar]
- He, K.; Zhang, X.; Ren, S.; Sun, J. Deep Residual Learning for Image Recognition. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition (CVPR), Las Vegas, NV, USA, 27–30 June 2016; pp. 770–778. [Google Scholar]
- Wu, Y.; He, K. Group Normalization. In Proceedings of the European Conference on Computer Vision (ECCV), Munich, Germany, 8–14 September 2018; pp. 3–19. [Google Scholar]
- Available online: https://virusshare.com/ (accessed on 24 October 2023).
- Sandler, M.; Howard, A.; Zhu, M.; Zhmoginov, A.; Chen, L.C. MobileNetV2: Inverted Residuals and Linear Bottlenecks. In Proceedings of the 2018 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR), Salt Lake City, UT, USA, 18–23 June 2018; pp. 4510–4519. [Google Scholar]
- Ma, N.; Zhang, X.; Zeng, H.T.; Sun, J. ShuffleNet V2: Practical Guidelines for Efficient CNN Architecture Design. In Proceedings of the 15th European Conference on Computer Vision (ECCV), Munich, Germany, 8–14 September 2018; Springer: Cham, Switzerland, 2018; pp. 122–138. [Google Scholar]
- Makandar, A.; Patrot, A. Malware class recognition using image processing techniques. In Proceedings of the 2017 International Conference on Data Management, Analytics and Innovation (ICDMAI), Pune, India, 24–26 February 2017; pp. 76–80. [Google Scholar]
- Hemalatha, J.; Roseline, S.A.; Geetha, S.; Kadry, S.; Damaševičius, R. An efficient densenet-based deep learning model for malware detection. Entropy 2021, 23, 344. [Google Scholar] [CrossRef] [PubMed]
- Vasan, D.; Alazab, M.; Wassan, S.; Naeem, H.; Safaei, B.; Zheng, Q. IMCFN: Image-based malware classification using fine-tuned convolutional neural network architecture. Comput. Netw. 2020, 171, 107138. [Google Scholar] [CrossRef]
- Ahmed, I.; Anisetti, M.; Ahmad, A.; Jeon, G. A Multilayer Deep Learning Approach for Malware Classification in 5G-Enabled IIoT. IEEE Trans. Ind. Inform. 2022, 19, 1495–1503. [Google Scholar] [CrossRef]
- Shaukat, K.; Luo, S.; Varadharajan, V. A novel deep learning-based approach for malware detection. Eng. Appl. Artif. Intell. 2023, 122, 106030. [Google Scholar] [CrossRef]
- Wu, C.; Chen, J.; Zhu, S.; Feng, W.; He, K.; Du, R.; Xiang, Y. WAFBooster: Automatic Boosting of WAF Security Against Mutated Malicious Payloads. IEEE Trans. Dependable Secur. Comput. 2025, 22, 1118–1131. [Google Scholar] [CrossRef]






| Model | Flops | Parameter | Acc (%) | Dataset |
|---|---|---|---|---|
| MobileNetV2 | 598.02 M | 2.26 M | 94.30 | DatasetB |
| ShuffleNetV2 | 281.77 M | 1.28 M | 95.34 | DatasetB |
| ResNet-18 | 3.48 G | 11.18 M | 93.44 | DatasetB |
| proposed | 2 G | 6.18 M | 97.93 | DatasetB |
| MobileNetV2 | 598.02 M | 2.26 M | 98.97 | DatasetA |
| ShuffleNetV2 | 281.77 M | 1.28 M | 99.13 | DatasetA |
| ResNet-18 | 3.48 G | 11.18 M | 97.83 | DatasetA |
| Proposed | 2 G | 6.18 M | 99.52 | DatasetA |
| Model | Accuracy (%) | Precision (%) | Recall (%) | F1-Score (%) | Source |
|---|---|---|---|---|---|
| GIST + SVM [26] | 98.88 | Cited | |||
| DenseNet [27] | 98.23 | 97.78 | 97.92 | 97.85 | Re |
| ResNet-50 [28] | 97.96 | 97.00 | 97.96 | 97.41 | Re |
| Ml-CNN [29] | 97 | Cited | |||
| Vgg16 + svm [30] | 99.06 | 98.47 | 98.52 | 98.49 | Re |
| Proposed | 99.52 | 98.89 | 98.74 | 98.80 |
| Model | Accuracy (%) | Precision (%) | Recall (%) | F1-Score (%) |
|---|---|---|---|---|
| Resnet-18 | 98.00 | 97.03 | 98.00 | 97.48 |
| Res_sr | 98.28 | 97.30 | 98.27 | 97.75 |
| Res_cr | 99.25 | 99.29 | 99.25 | 99.24 |
| Proposed | 99.52 | 98.89 | 98.74 | 98.80 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, X.; Liu, J.; Ren, Y.; Chen, J. Detecting Visualized Malicious Code Through Low-Redundancy Convolution. Computers 2025, 14, 470. https://doi.org/10.3390/computers14110470
Liu X, Liu J, Ren Y, Chen J. Detecting Visualized Malicious Code Through Low-Redundancy Convolution. Computers. 2025; 14(11):470. https://doi.org/10.3390/computers14110470
Chicago/Turabian StyleLiu, Xiao, Jiawang Liu, Yingying Ren, and Jining Chen. 2025. "Detecting Visualized Malicious Code Through Low-Redundancy Convolution" Computers 14, no. 11: 470. https://doi.org/10.3390/computers14110470
APA StyleLiu, X., Liu, J., Ren, Y., & Chen, J. (2025). Detecting Visualized Malicious Code Through Low-Redundancy Convolution. Computers, 14(11), 470. https://doi.org/10.3390/computers14110470





