A Process Model for Cooperative Risk Management in Seaports
Abstract
1. Introduction
2. Background and Related Work
2.1. Seaports
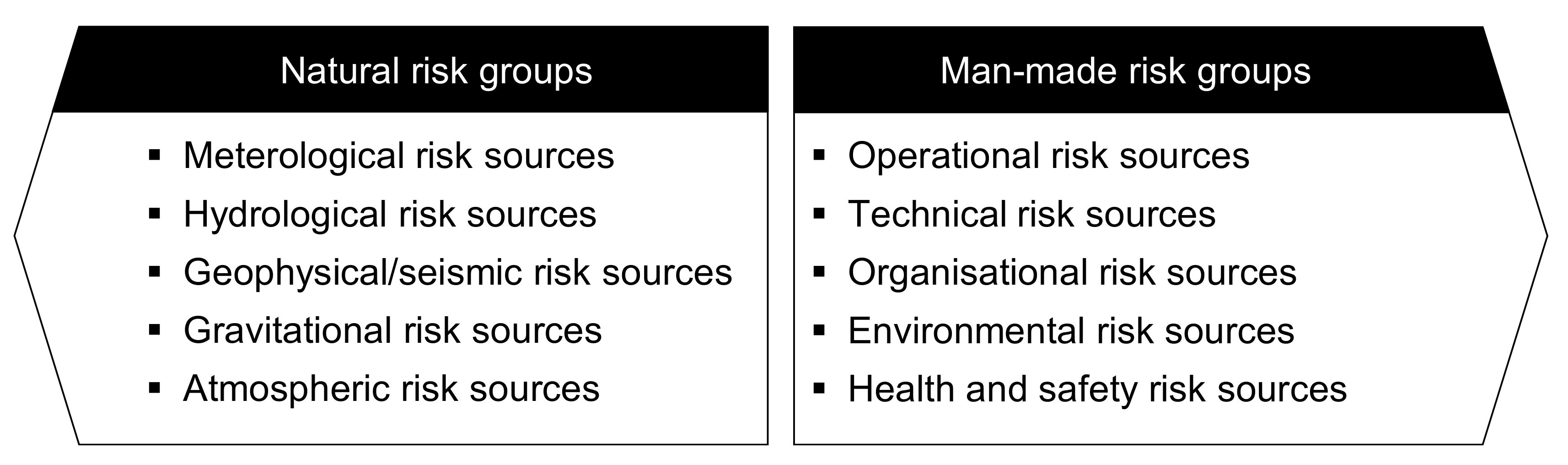
2.2. Risk Management
2.3. Related Work
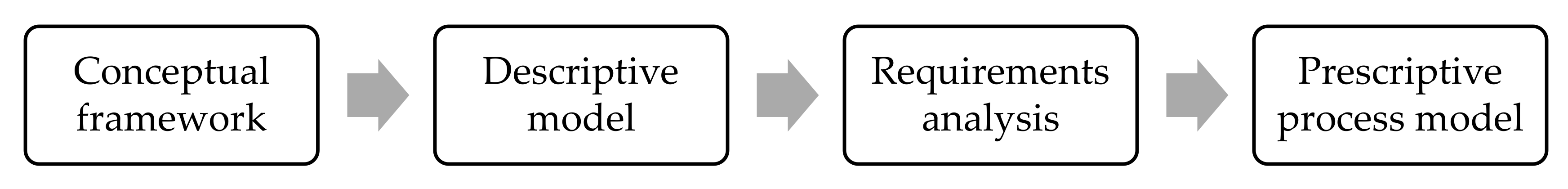
3. Methodology
3.1. Conceptual Framework
3.2. Descriptive Model
3.3. Requirenment Analysis
3.3.1. Focus Groups
3.3.2. Online Survey
3.4. Prescriptive Process Model
4. Requirement Analysis
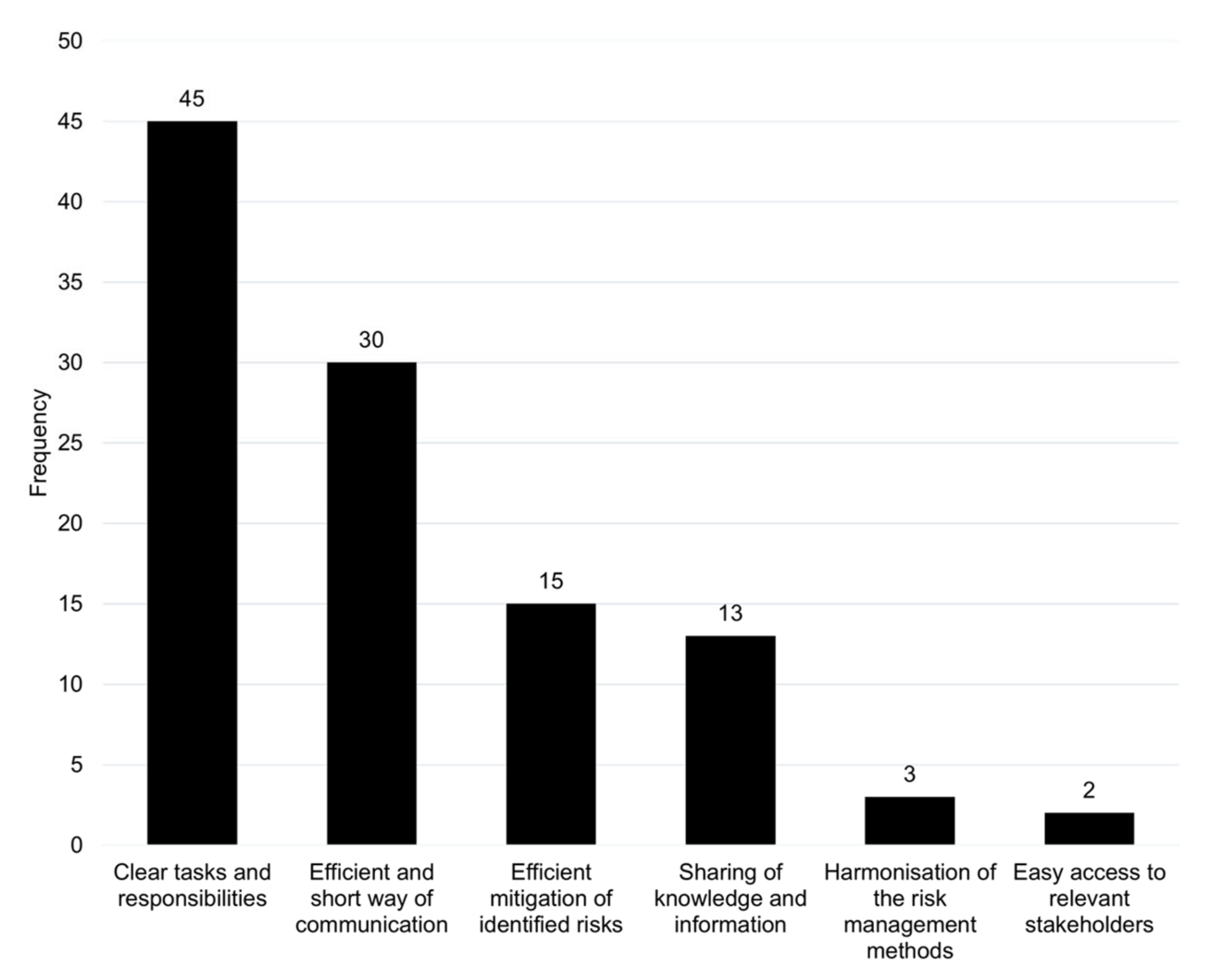
4.1. Opportunities and Benefits of Cooperative Risk Management in Seaports
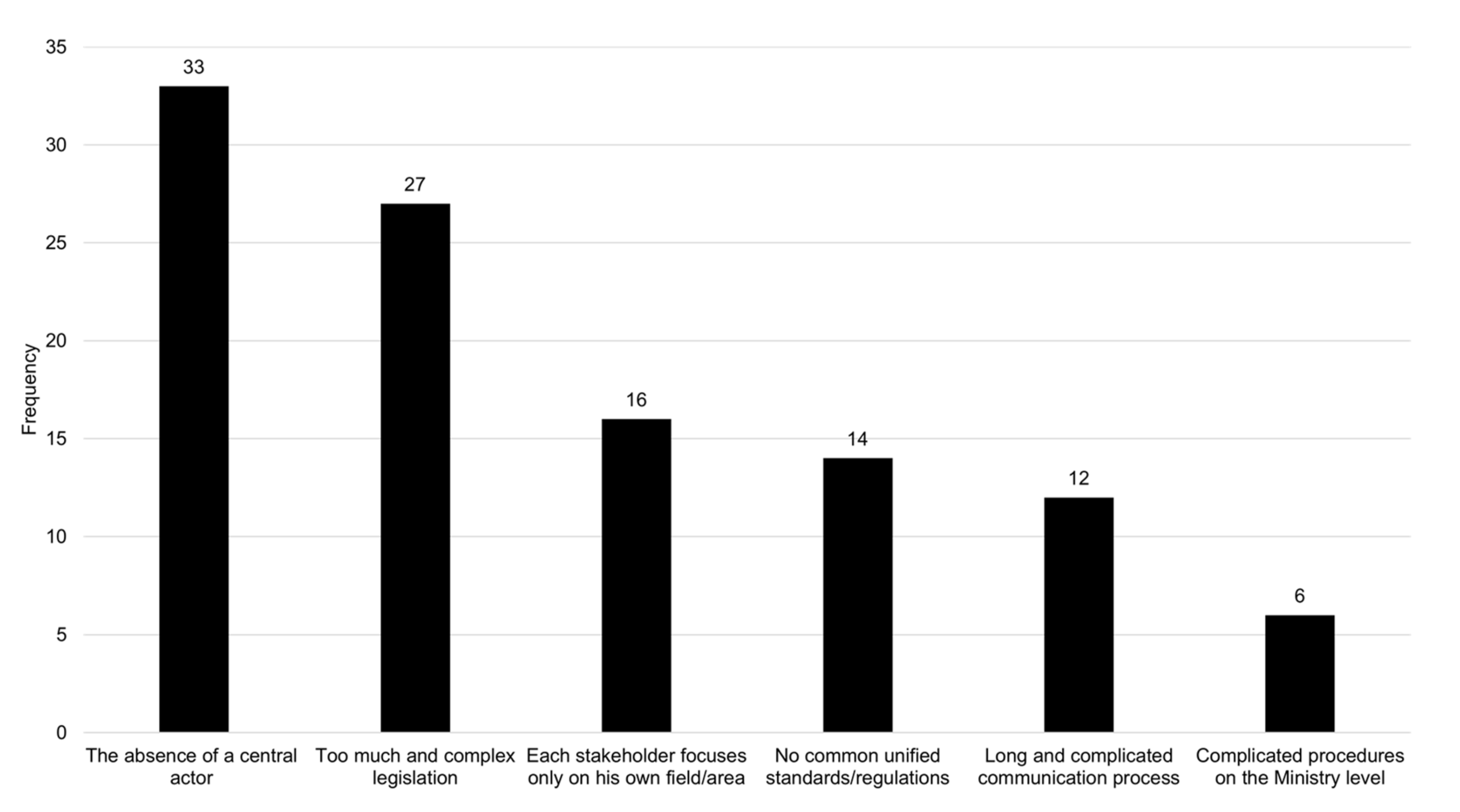
4.2. Barriers and Challenges of Cooperative Risk Management in Seaports
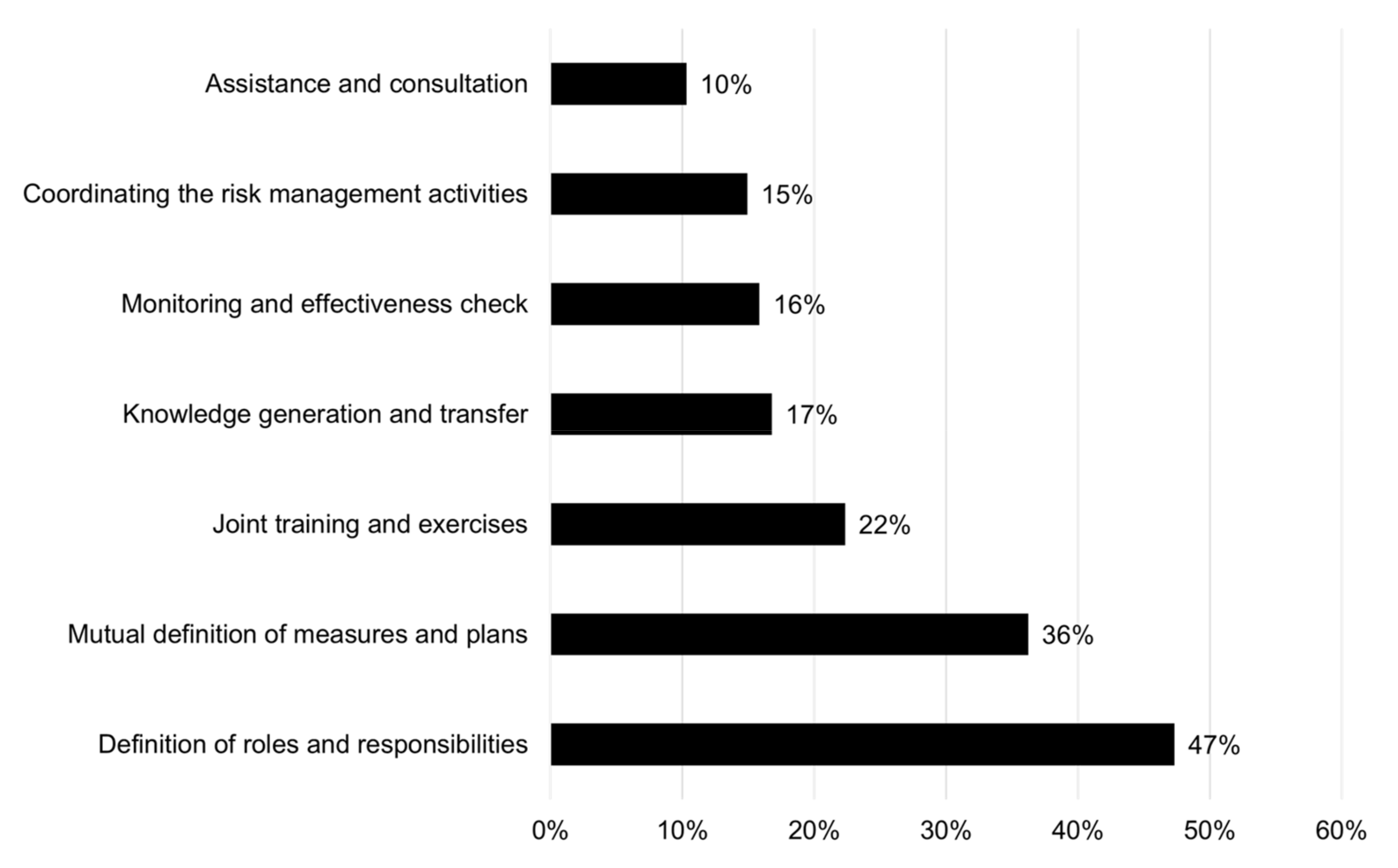
4.3. Requirements of the Prescriptive Process Model for Cooperative Risk Management in Seaports
5. Process Model
5.1. Seaport Type and Structure
5.1.1. Organisational Type
5.1.2. Specialisation Type
5.1.3. Water access Type
5.2. Stakeholder Analysis
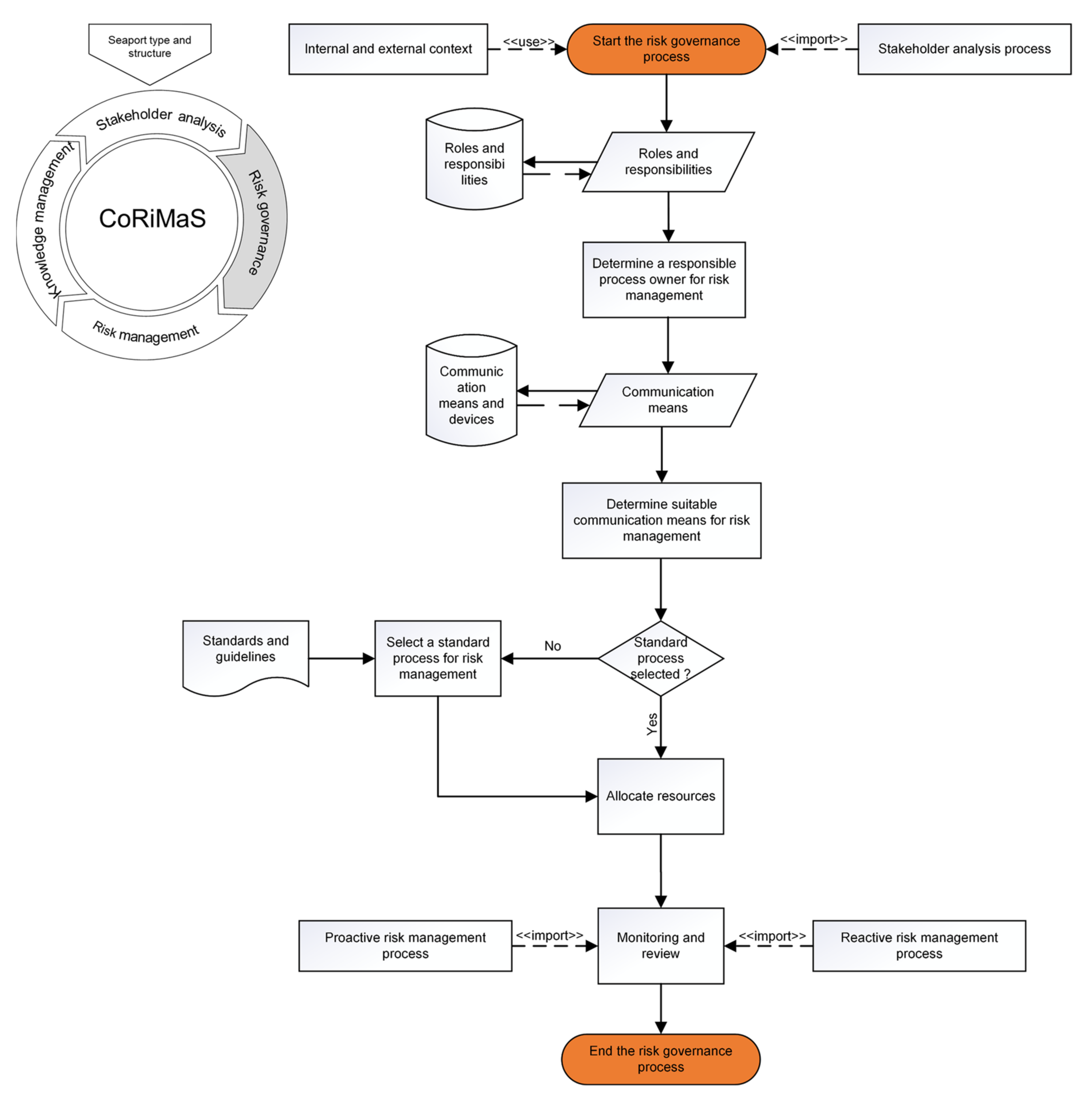
5.3. Risk Governance
5.4. Risk Management
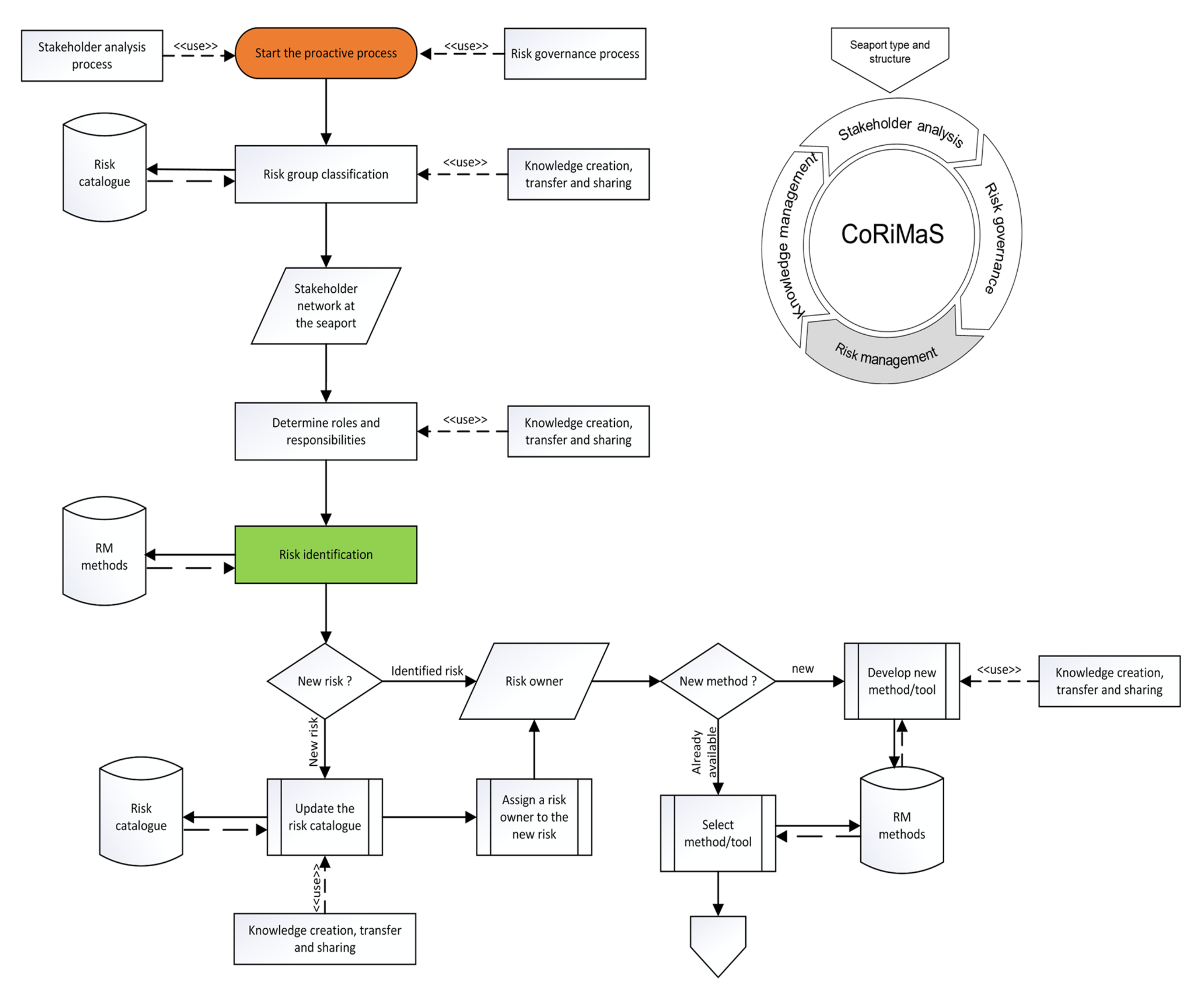
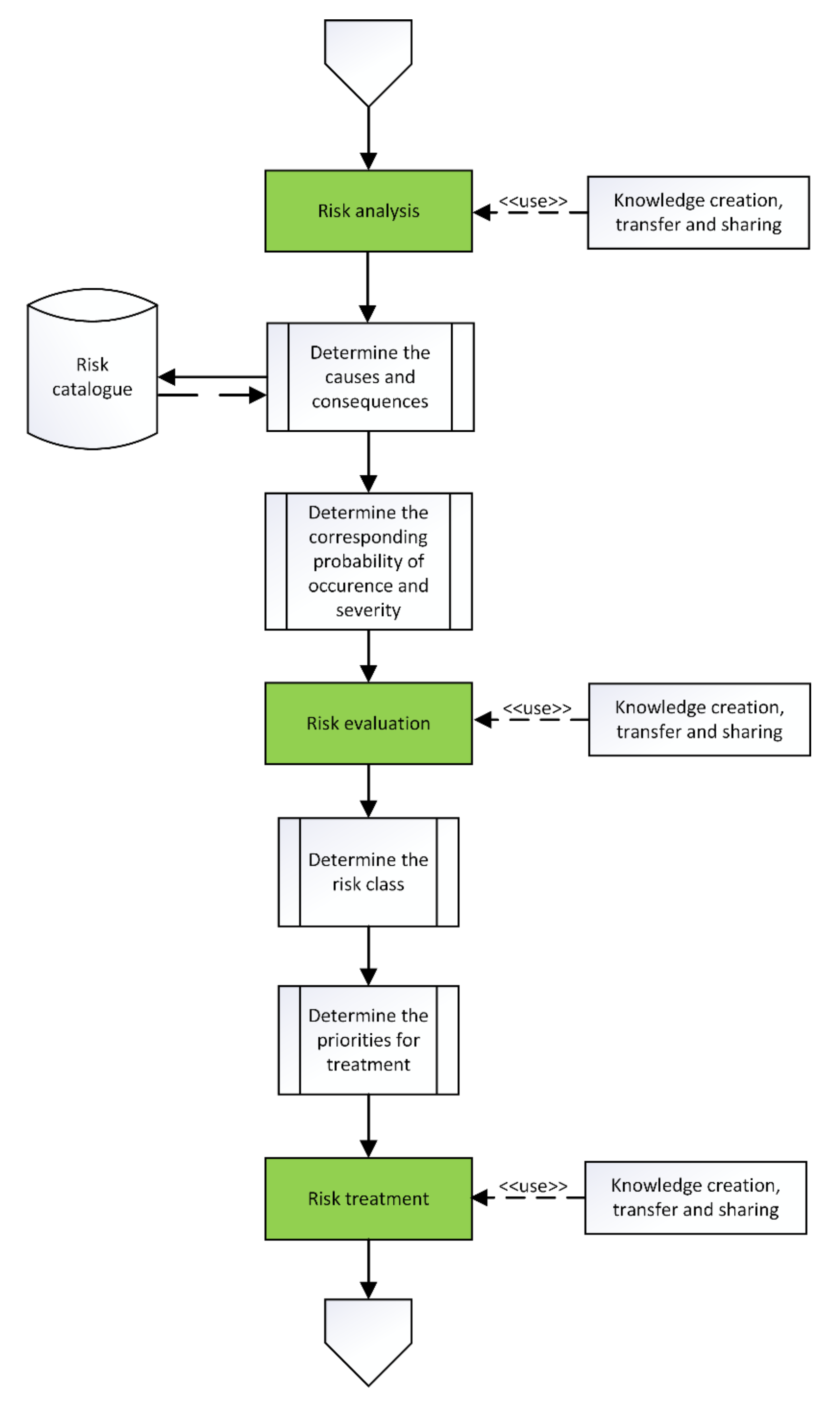
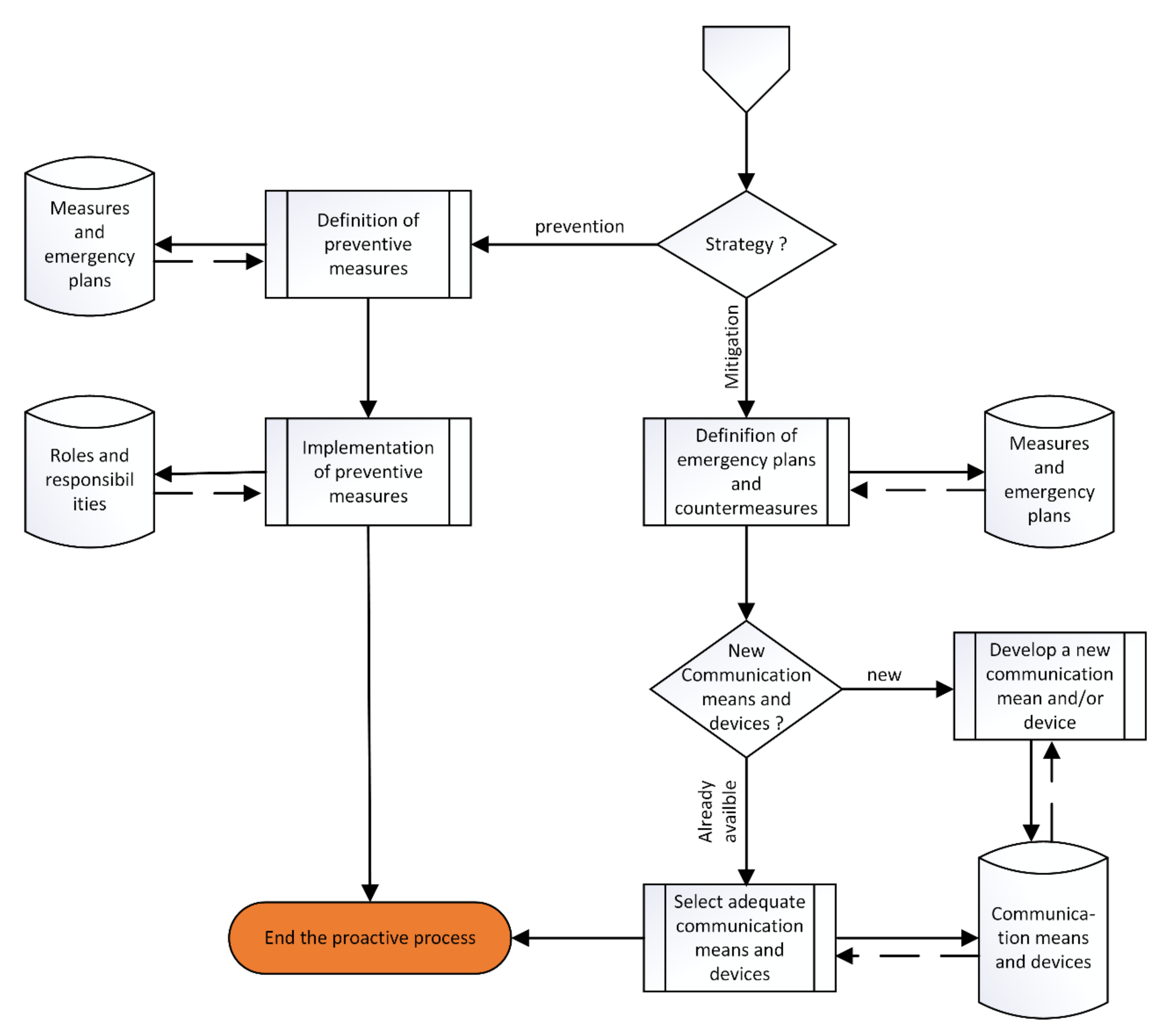
5.4.1. Proactive Process (Prevention)
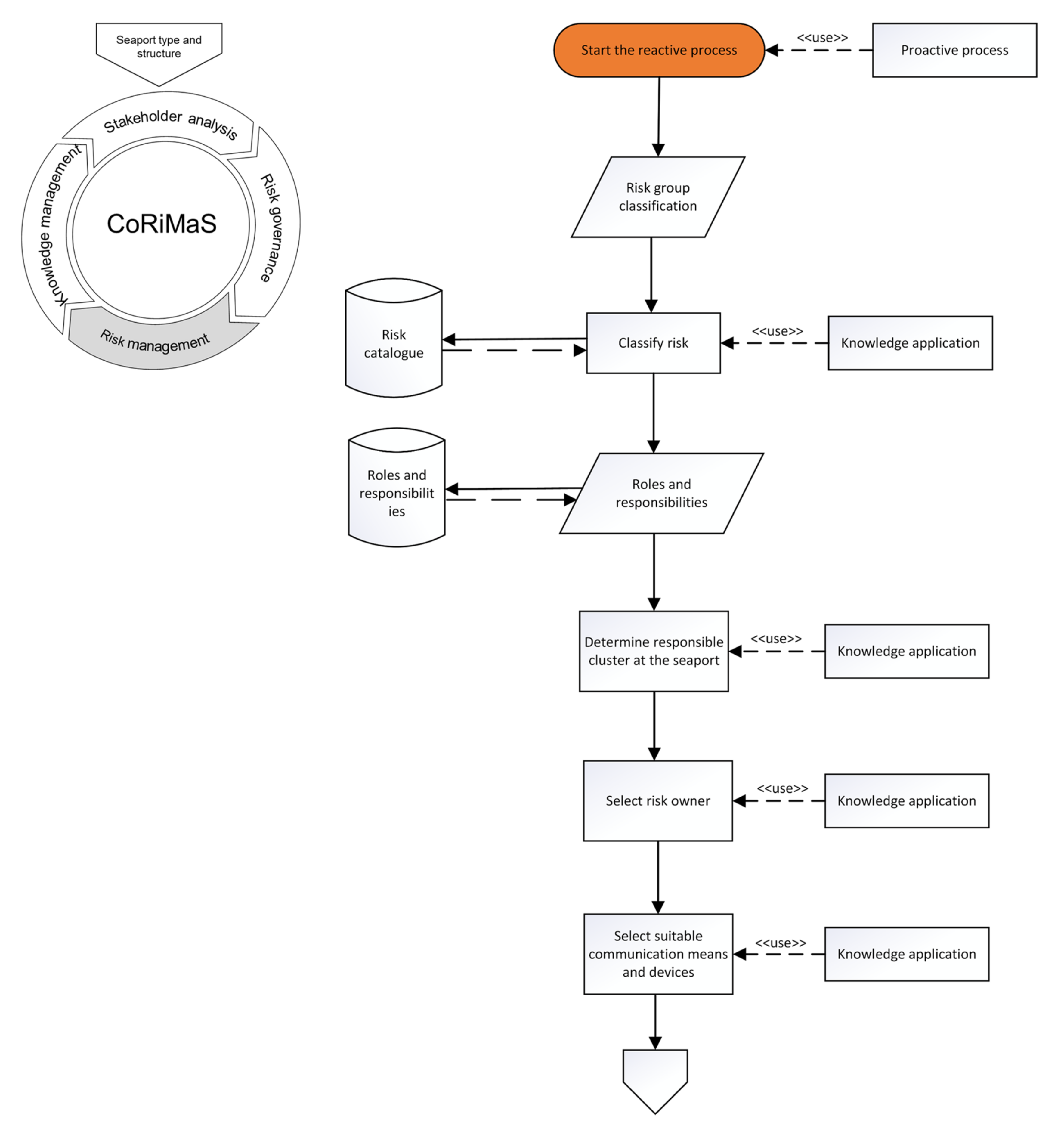
5.4.2. Reactive Process (Response)
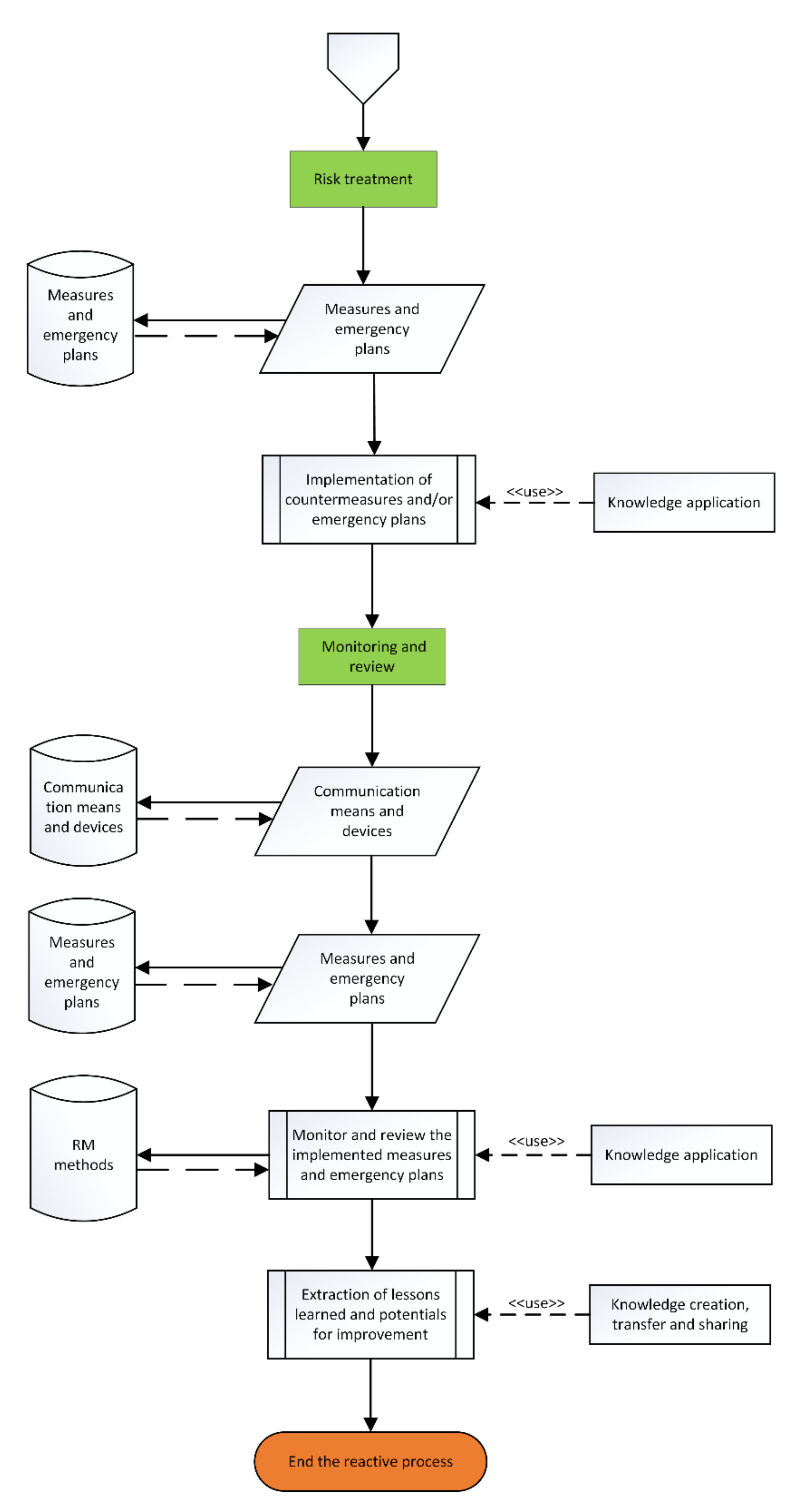
5.4.3. Monitoring and Review
5.4.4. Communication and Consultation
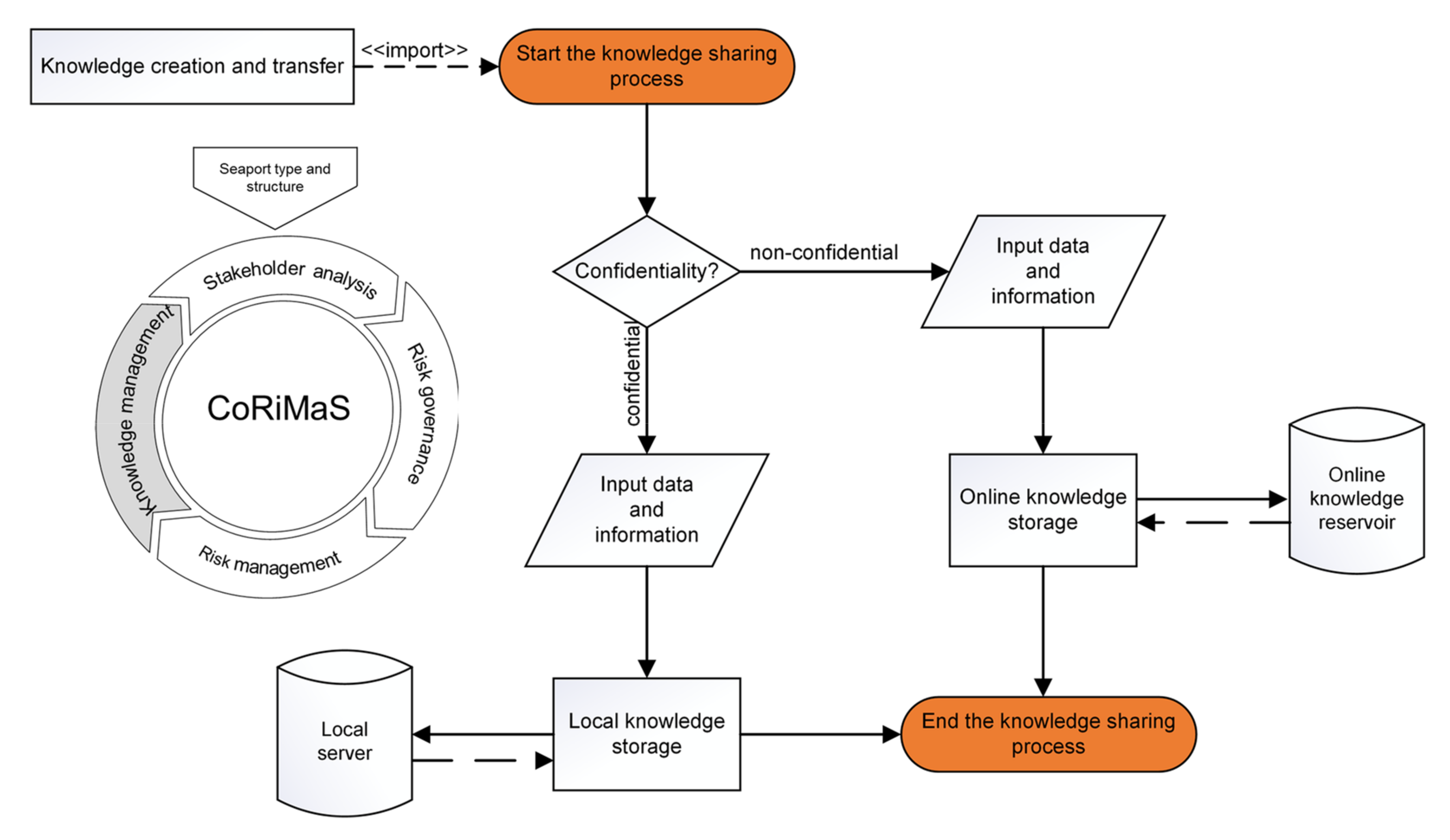
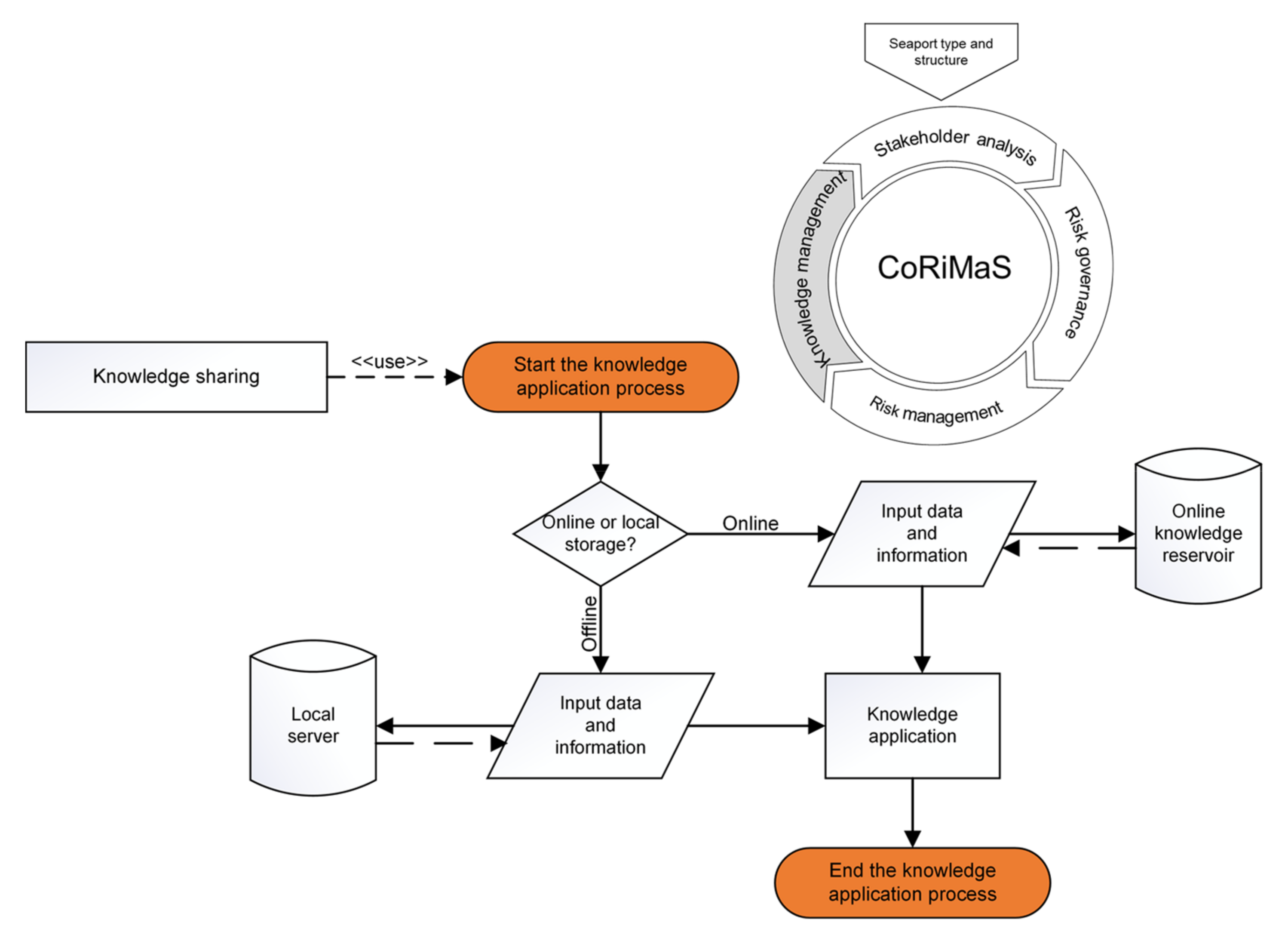
5.5. Knowledge Management
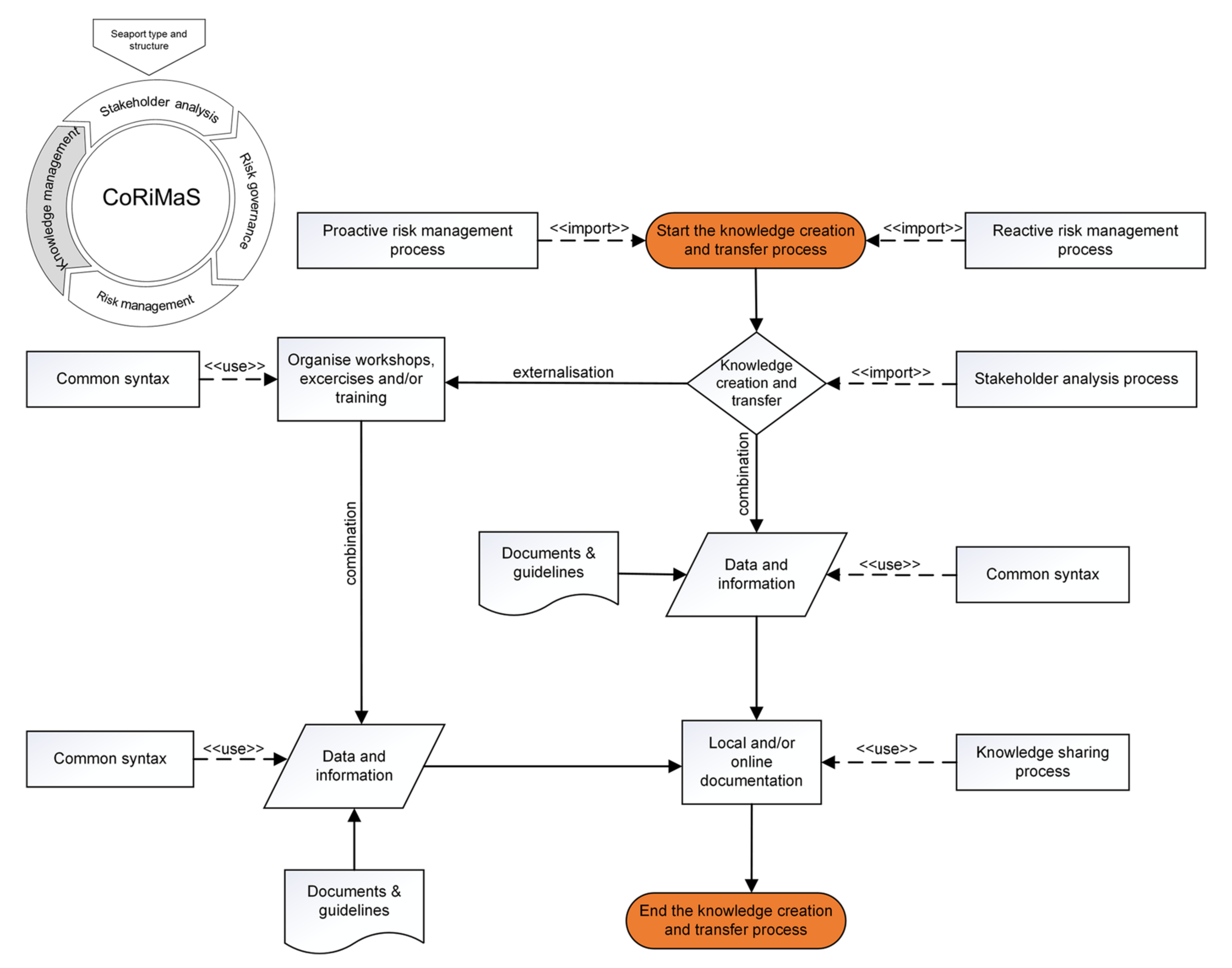
5.5.1. Knowledge Creation and Transfer
5.5.2. Knowledge Sharing and Application
6. Discussion
6.1. Results of the Prescriptive Process Model for Cooperative Risk Management in Seaports
6.2. Implications for Theory and Practice
7. Conclusions, Limitations, and Outlook
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Kersten, W.; Hohrath, P.; Boeger, M.; Singer, C. A supply chain risk management process. Int. J. Logist. Syst. Manag. 2011, 8, 152–166. [Google Scholar] [CrossRef]
- Norrman, A.; Jansson, U. Ericsson’s proactive supply chain risk management approach after a serious sub-supplier accident. Int. J. Phys. Distrib. Logist. Manag. 2004, 34, 434–456. [Google Scholar] [CrossRef]
- Meersman, H. Port Infrastructure Finance; Taylor and Francis: Hoboken, NJ, USA, 2014. [Google Scholar]
- Nagi, A.; Schroeder, M.; Kersten, W. Risk Management in Seaports: A Community Analysis at the Port of Hamburg. Sustainability 2021, 13, 8035. [Google Scholar] [CrossRef]
- Pileggi, S.F.; Indorf, M.; Nagi, A.; Kersten, W. CoRiMaS—An Ontological Approach to Cooperative Risk Management in Seaports. Sustainability 2020, 12, 4767. [Google Scholar] [CrossRef]
- Vis, I.F.; de Koster, R. Transshipment of containers at a container terminal: An overview. Eur. J. Oper. Res. 2003, 147, 1–16. [Google Scholar] [CrossRef]
- John, A.; Yang, Z.; Riahi, R.; Wang, J. A risk assessment approach to improve the resilience of a seaport system using Bayesian networks. Ocean Eng. 2016, 111, 136–147. [Google Scholar] [CrossRef]
- EMSA. Annual Overview of Marine Casualties and Incidents. 2018. Available online: http://www.emsa.europa.eu/newsroom/latest-news/item/3406-annual-overview-of-marine-casualties-and-incidents-2018.html (accessed on 28 July 2021).
- Homayouni, S.M.; Fontes, D.B. Metaheuristics for Maritime Operations; John Wiley & Sons: Hoboken, NJ, USA, 2018. [Google Scholar]
- Benson, D.; Whitehead, G. Transport and Distribution: Made Simple; Elsevier: Amsterdam, The Netherlands, 2013. [Google Scholar]
- Nagi, A.; Indorf, M.; Singer-Neumann, C.; Ojala, L. Current State of Risk Assessment in Seaports: An Empirical Study. In Logistik im Wandel der Zeit–Von der Produktionssteuerung zu Vernetzten Supply Chains; Schröder, M., Wegner, K., Eds.; Springer Fachmedien Wiesbaden: Wiesbaden, Germany, 2019; pp. 79–101. [Google Scholar]
- Notteboom, T. Current Issues in Shipping, Ports and Logistics; University Press Antwerp: Antwerp, Belgium, 2011. [Google Scholar]
- Van Hooydonk, E. Soft Values of Seaports: A Strategy for the Restoration of Public Support for Seaports; Garant: Antwerp-Apeldoorn, The Netherlands, 2007. [Google Scholar]
- Molland, A.F. (Ed.) The Maritime Engineering Reference Book: A Guide to Ship Design, Construction and Operation; Butterworth-Heinemann: Oxford, UK, 2008. [Google Scholar]
- Hinkelman, E.G.; Shippey, K.C.; Putzi, S. Dictionary of International Trade: Handbook of the Global Trade Community Includes 21 Key Appendices; World Trade Press: Petaluma, CA, USA, 2005. [Google Scholar]
- Jaja, C.Y. Freight Traffic at Nigerian Seaports: Problems and Prospects. Soc. Sci. 2011, 6, 250–258. [Google Scholar] [CrossRef]
- Agerschou, H. Planning and Design of Ports and Marine Terminals, 2nd ed.; Telford: London, UK, 2004. [Google Scholar]
- Stopford, M. Maritime Economics, 3rd ed.; Routledge: London, UK, 2008. [Google Scholar]
- Maloni, M.J.; Jackson, E.C. Stakeholder Contributions to Container Port Capacity: A Survey of Port Authorities. J. Transp. Res. Forum. 2010, 46. [Google Scholar] [CrossRef]
- Dooms, M.; Macharis, C.; Verbeke, A. Proactive stakeholder management in the port planning process: Empirical evidence from the Port of Brussels. In Proactive Stakeholder Management in the Port Planning Process: Empirical Evidence from the Port of Brussels; European Regional Science Association (ERSA): Louvain-la-Neuve, Belgium, 2004. [Google Scholar]
- Wagner, N. Identification of the most important sustainability topics in seaports. Logist. Transp. 2017, 34, 79–88. [Google Scholar]
- Norrman, A.; Lindroth, R. Supply chain risk management: Purchasers’ vs planners’ views on sharing capacity investment risks in the telecom industry. In Proceedings of the 11th International Annual IPSERA Conference, Enschede, The Netherlands, 25–27 March 2002; pp. 577–595. [Google Scholar]
- Parra, N.M.; Nagi, A.; Kersten, W. Risk Assessment Methods in Seaports: A Literature Review; Publications of the HAZARD Project; University of Turku: Turku, Finland, 2018. [Google Scholar]
- Kaundinya, I.; Nisancioglu, S.; Kammerer, H.; Oliva, R. All-hazard Guide for Transport Infrastructure. Transp. Res. Procedia 2016, 14, 1325–1334. [Google Scholar] [CrossRef][Green Version]
- Schmidt, J.; Matcham, I.; Reese, S.; King, A.; Bell, R.; Henderson, R.; Smart, G.; Cousins, J.; Smith, W.; Heron, D. Quantitative multi-risk analysis for natural hazards: A framework for multi-risk modelling. Nat. Hazards 2011, 58, 1169–1192. [Google Scholar] [CrossRef]
- Aven, T. Risk assessment and risk management: Review of recent advances on their foundation. Eur. J. Oper. Res. 2016, 253, 1–13. [Google Scholar] [CrossRef]
- Peltier, T.R. Information Security Risk Analysis; CRC Press: Hoboken, NJ, USA, 2005. [Google Scholar]
- ISO 31000:2018; Risk Management-Guidelines. International Organisation for Standardisation: Geneva, Switzerland, 2018.
- Barafort, B.; Mesquida, A.-L.; Mas, A. Developing an Integrated Risk Management Process Model for IT Settings in an ISO Multi-standards Context. In Software Process Improvement and Capability Determination; Mas, A., Mesquida, A., O’Connor, R.V., Rout, T., Dorling, A., Eds.; Springer International Publishing: Cham, Switzerland, 2017; pp. 322–336. [Google Scholar]
- Ilvonen, I.; Jussila, J.J.; Kärkkäinen, H. Towards a Business-Driven Process Model for Knowledge Security Risk Management. Int. J. Knowl. Manag. 2015, 11, 1–18. [Google Scholar] [CrossRef]
- Kajko-Mattsson, M.; Sjokvist, K.; Krogdahl, D. Outlining a Distributed Risk Management Process Model. Int. J. Inf. Process. Manag. 2011, 2, 22–32. [Google Scholar] [CrossRef]
- Caballini, C.; Sacone, S.; Saeednia, M. Cooperation among truck carriers in seaport containerized transportation. Transp. Res. Part E Logist. Transp. Rev. 2016, 93, 38–56. [Google Scholar] [CrossRef]
- Lanne, M.M.; Sarsama, J. Collaboration oriented approach for managing safety and security risks in organizations. In Proceedings of the 2008 IEEE International Conference on Industrial Engineering and Engineering Management, Singapore, 8–11 December 2008; pp. 1341–1345. [Google Scholar]
- Li, J.; Li, M.; Wu, D.; Song, H. An integrated risk measurement and optimization model for trustworthy software process management. Inf. Sci. 2012, 191, 47–60. [Google Scholar] [CrossRef]
- Wong, A.; Kozan, E. Optimization of container process at seaport terminals. J. Oper. Res. Soc. 2010, 61, 658–665. [Google Scholar] [CrossRef]
- Nagi, A.; Schröder, M.; Kersten, W. A Conceptual Framework for Cooperative Risk Management in Seaports. Int. J. Risk Assess. Manag. 2022, in press. [Google Scholar]
- Leshem, S.; Trafford, V. Overlooking the conceptual framework. Innov. Educ. Teach. Int. 2007, 44, 93–105. [Google Scholar] [CrossRef]
- Münch, J. Software Process Definition and Management, 1st ed.; Springer: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Henderson, J.C.; Venkatraman, N. Strategic Alignment: A Model for Organizational Transformation via Information Technology. In Information Technology and the Corporation of the 1990s: Research Studies; Allen, J.A., Scott Morto, M.S., Eds.; Oxford University Press: Oxford, UK, 1994. [Google Scholar]
- Gruber, T.R. A translation approach to portable ontology specifications. Knowl. Acquis. 1993, 5, 199–220. [Google Scholar] [CrossRef]
- Kitzinger, J. Qualitative research. Introducing focus groups. BMJ 1995, 311, 299–302. [Google Scholar] [CrossRef]
- Daivadanam, M.; Wahlström, R.; Ravindran, T.K.S.; Thankappan, K.R.; Ramanathan, M. Conceptual model for dietary behaviour change at household level: A ‘best-fit’ qualitative study using primary data. BMC Public Health 2014, 14, 574. [Google Scholar] [CrossRef] [PubMed]
- Psotka, J. (Ed.) Intelligent Tutoring Systems: Lessons Learned; Lawrence Erlbaum: Hillsdale, NJ, USA, 1988. [Google Scholar]
- Gelinas, U.J.; Dull, R.B. Accounting Information Systems, 8th ed.; South-Western Thomson Learning: Mason, OH, USA, 2010. [Google Scholar]
- Rumbaugh, J.; Jacobson, I.; Booch, G. The Unified Modeling Language Reference Manual; Addison–Wesely: Boston, MA, USA, 1999. [Google Scholar]
- Humphreys, M.; Stokenberga, A.; Dappe, M.H.; Limi, A.; Hartmann, O. Port Development and Competition in East and Southern Africa: Prospects and Challenges; World Bank Group: Washington, DC, USA, 2019. [Google Scholar]
- De Jong, F.; Rodemann, H. Port Economy in a Nutshell; InterRoJo Publications: Barendrecht, The Netherlands, 2020. [Google Scholar]
- European Commission. The EU Floods Directive. 2019. Available online: https://ec.europa.eu/environment/water/flood_risk/ (accessed on 14 July 2021).
- IRGC. IRGC Guidelines for Emerging Risk Governance. 2015. Available online: https://infoscience.epfl.ch/record/228053/files/Guidelines%20for%20Emerging%20Risk%20Governance.pdf (accessed on 13 July 2021).
- Van Asselt, M.B.; Renn, O. Risk governance. J. Risk Res. 2011, 14, 431–449. [Google Scholar] [CrossRef]
- ISO 9004:2018; Quality Management-Quality of an Organisation: Guidance to Achieve Sustained Success. International Organisation for Standardisation: Geneva, Switzerland, 2018.
- Sáenz, M.J.; Revilla, E.; Acero, B. Aligning supply chain design for boosting resilience. Bus. Horiz. 2018, 61, 443–452. [Google Scholar] [CrossRef]
- Smallman, C. Risk and organizational behaviour: A research model. Disaster Prev. Manag. Int. J. 1996, 5, 12–26. [Google Scholar] [CrossRef]
- Dyer, J.H.; Singh, H. The Relational View: Cooperative Strategy and Sources of Interorganizational Competitive Advantage. Acad. Manag. Rev. 1998, 23, 660–679. [Google Scholar] [CrossRef]



| Papers/Scope | Risk Management | Process Model | Seaport | Cooperation |
|---|---|---|---|---|
| Barafort et al., 2017 [29] |  |  |  |  |
| Caballini et al., 2016 [32] |  |  |  |  |
| Ilvonen et al., 2015 [30] |  |  |  |  |
| Lanne and Sarsama, 2008 [33] |  |  |  |  |
| Li et al., 2012 [34] |  |  |  |  |
| Kajko-Mattsson et al., 2017 [31] |  |  |  |  |
| Nagi et al., 2021 [4] |  |  |  |  |
| Pileggi et al., 2020 [5] |  |  |  |  |
| Wong and Kozan, 2010 [35] |  |  |  |  |
| This work |  |  |  |  |
 : fully fulfilled—
: fully fulfilled— : partially fulfilled—
: partially fulfilled— : not fulfilled.
: not fulfilled.| Symbol | Description |
|---|---|
 | Start/End of a process. |
 | Process. |
 | Subprocess. |
 | Decision that has two outputs. |
 | Input/output. |
 | Document. |
 | Database. |
 | Off-page connector. |
 | Direct logic flow from one element to another element. |
 | Dependency flow that presents the relationship between two elements. |
 | Return value from a database. |
| Dependency | Function | Keyword |
|---|---|---|
| usage | Statement that one element requires the presence of another element for its correct functioning. | <<use>> |
| Import | Permission of an element/process to access the content of another element/process. | <<import>> |
| # | Opportunities and Benefits | # | Opportunities and Benefits |
|---|---|---|---|
| 1 | Efficient and short way of communication. | 4 | Sharing knowledge and information. |
| 2 | Clear tasks and responsibilities. | 5 | Harmonisation of the RM methods. |
| 3 | Easy access to relevant stakeholders. | 6 | Efficient mitigation of identified risks. |
| # | Barriers and Challenges | # | Barriers and Challenges |
|---|---|---|---|
| 1 | The absence of a central actor who can control and manage the process of RM. | 4 | There are no common unified standards/regulations used by all stakeholders at the seaport. |
| 2 | Long and complicated communication process. | 5 | Each stakeholder focuses only on his own field/area. |
| 3 | Too much and complex legislation. | 6 | Complicated procedures at the Ministry level. |
| # | Requirements for the Model | # | Requirements for the Model |
|---|---|---|---|
| 1 | A model that provides a common view of the RM process. | 4 | A list of risks that could occur at seaports. |
| 2 | Inclusion of reactive risk management for incident notifications. | 5 | A database with all relevant institutions. |
| 3 | Adequate methods for the identification and assessment of risks. | 6 | A communication approach that allows for interaction with other stakeholders. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nagi, A.; Kersten, W. A Process Model for Cooperative Risk Management in Seaports. Sustainability 2022, 14, 1662. https://doi.org/10.3390/su14031662
Nagi A, Kersten W. A Process Model for Cooperative Risk Management in Seaports. Sustainability. 2022; 14(3):1662. https://doi.org/10.3390/su14031662
Chicago/Turabian StyleNagi, Ayman, and Wolfgang Kersten. 2022. "A Process Model for Cooperative Risk Management in Seaports" Sustainability 14, no. 3: 1662. https://doi.org/10.3390/su14031662
APA StyleNagi, A., & Kersten, W. (2022). A Process Model for Cooperative Risk Management in Seaports. Sustainability, 14(3), 1662. https://doi.org/10.3390/su14031662