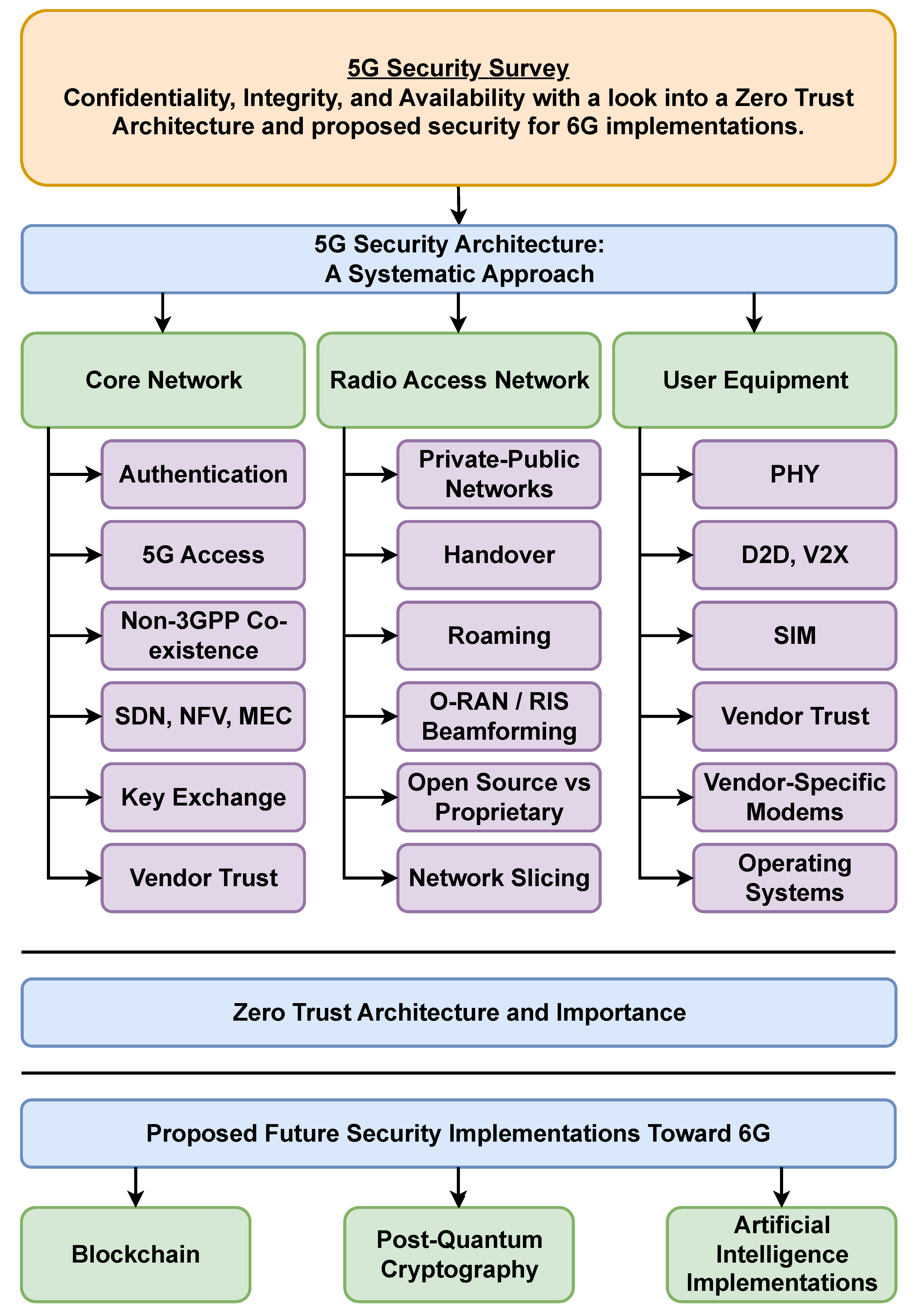
A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas
Abstract
1. Introduction
Scope and Contributions
2. Related Works
2.1. Security Focuses in 5G
- (1)
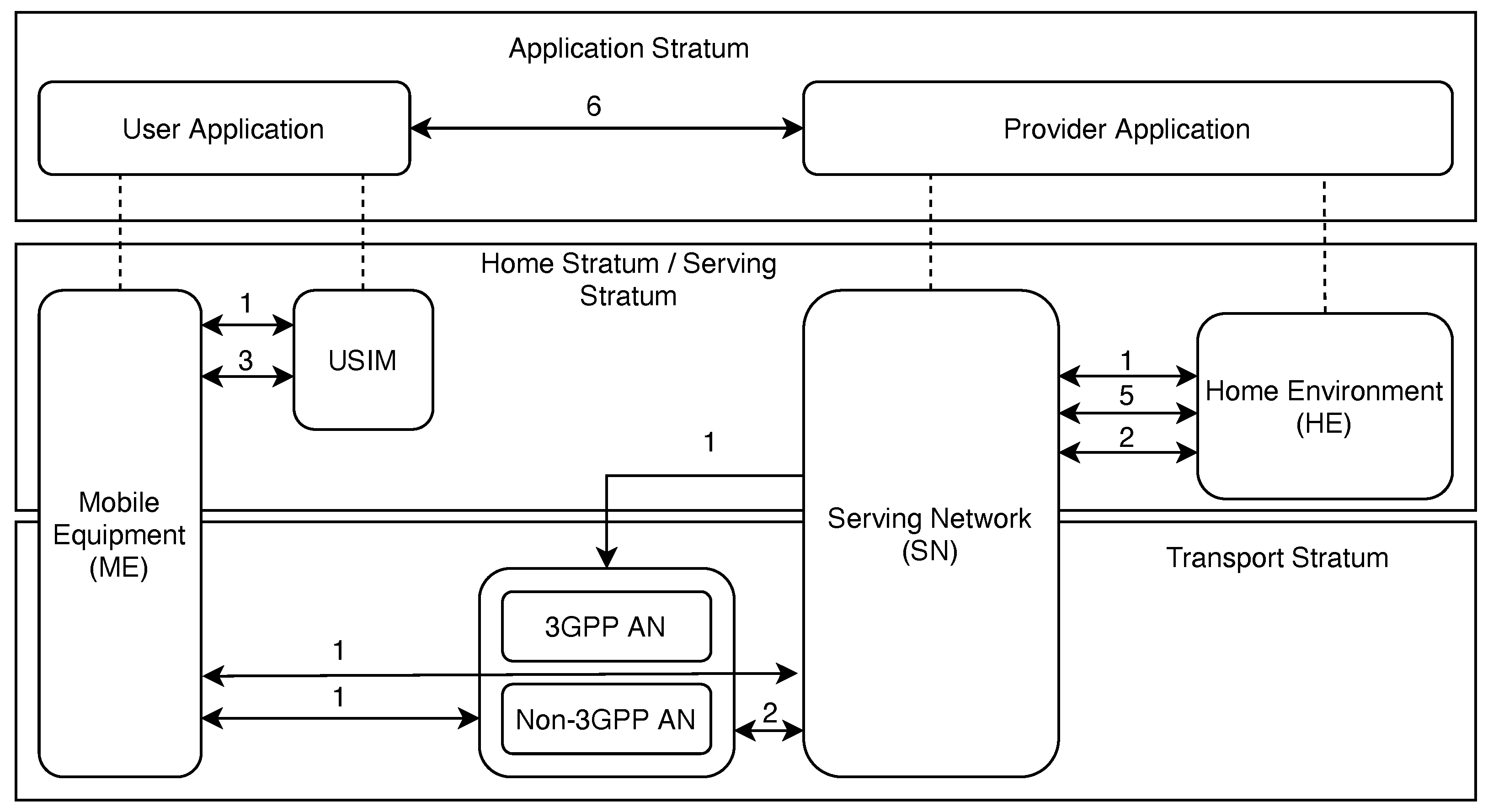
- Network Access Security focuses on UE authentication and secure network services access with a particular focus on attacks against the physical/radio interface. This domain includes both 3GPP and trusted non-3GPP access and the access security between the Serving Network (SN) and Access Network (AN). In the context of this paper, sections covering authentication, 5G access, RAN, and UE physical layer security will review the current state of research in each of these areas. These sections will outline current research enhancements, vulnerabilities, and future research directions to align with the TS 33.501 standard.
- (2)
- Network Domain Security encompasses security for network nodes that enables the secure exchange of signaling data and user plane data. Sections covering the topics of non-3GPP co-existence, SDN, NFV, and MEC will discuss research in this domain later in this paper.
- (3)
- User Domain Security contains the security features that secure the user’s access to mobile equipment. Discussed later are general resources and security measures listed by the National Institute of Science and Technology (NIST) on identifying areas of concern for user security at the device end.
- (4)
- Application Domain Security entails security for the user domain to the application provider domain in order to be able to exchange messages securely. Application domain security is not within the scope of TS 33.501, but this paper will discuss blockchain technology and post-quantum cryptography for applications specific to 5G networks.
- (5)
- Service-Based Architecture (SBA) Domain Security is the set of security features that enables network functions to securely communicate within the serving network domain and with other network domains. Such features include network function registration, discovery, and authorization security aspects as well as the protection for the service-based interfaces. SBA domain security is a new security feature compared to TS 33.401 [3]. These security features will be discussed in the SBA section with specific subsections corresponding to the various network functions in a 5G system.
- (6)
- Visibility and Configurability of Security spans the set of features that inform the user whether a security feature is in operation. Visibility and configurability are mentioned within this survey in the sections discussing the user equipment, the Core Network, and O-RAN (Open-RAN).
2.2. 5G Security Research
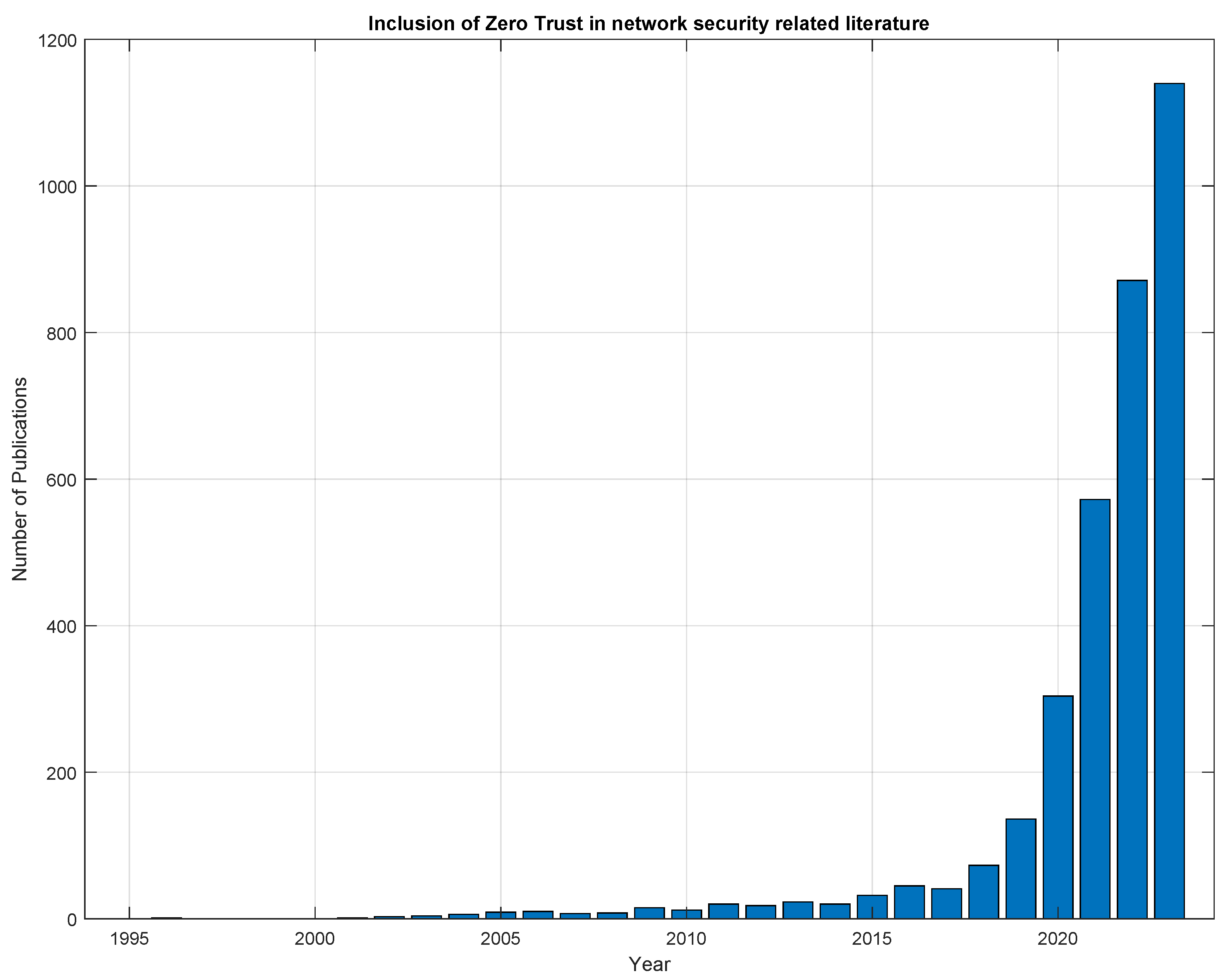
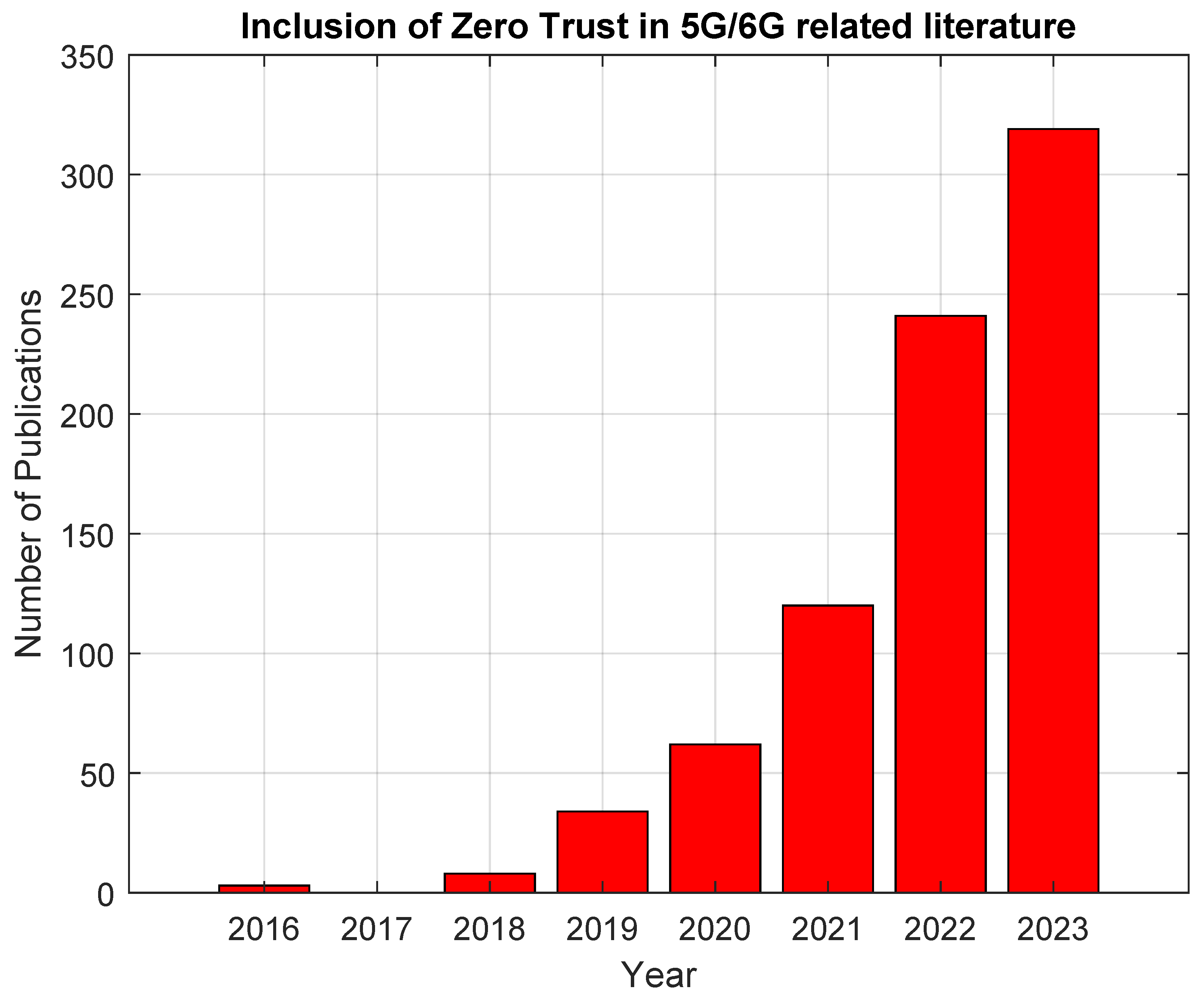
2.3. Zero Trust Importance
3. 5G Security Architecture: A Systematic Approach
3.1. Core Network
3.1.1. Authentication
- Mutual authentication (implicit) between UE and SN, and UE and HN.
- SN is authorized by HN.
- Confidentiality for (Key [from] Security Anchor Function) even if the attacker learns session keys established in other sessions (previous or consequent).
- Anonymity: SUPI (Subscription Permanent Identifier) and SQN (Sequence Number) shall remain secret in the presence of a passive attacker in order to guarantee activity privacy.
- Unlinkability (user location confidentiality and user untraceability) against passive adversaries. An attacker cannot deduce the presence of a subscriber in a certain area or whether different services are delivered to the same user by eavesdropping on the radio access link.
3.1.2. Key Exchange
- The UE establishes a new PDU session or modifies an existing session.
- The UE is handed over to a new base station or RAN cell.
- The UE moves to a different serving network.
- The UE performs a registration or de-registration from the network.
- The UE requests a key change, or the network requests a key change, put in place by the operator’s policy.
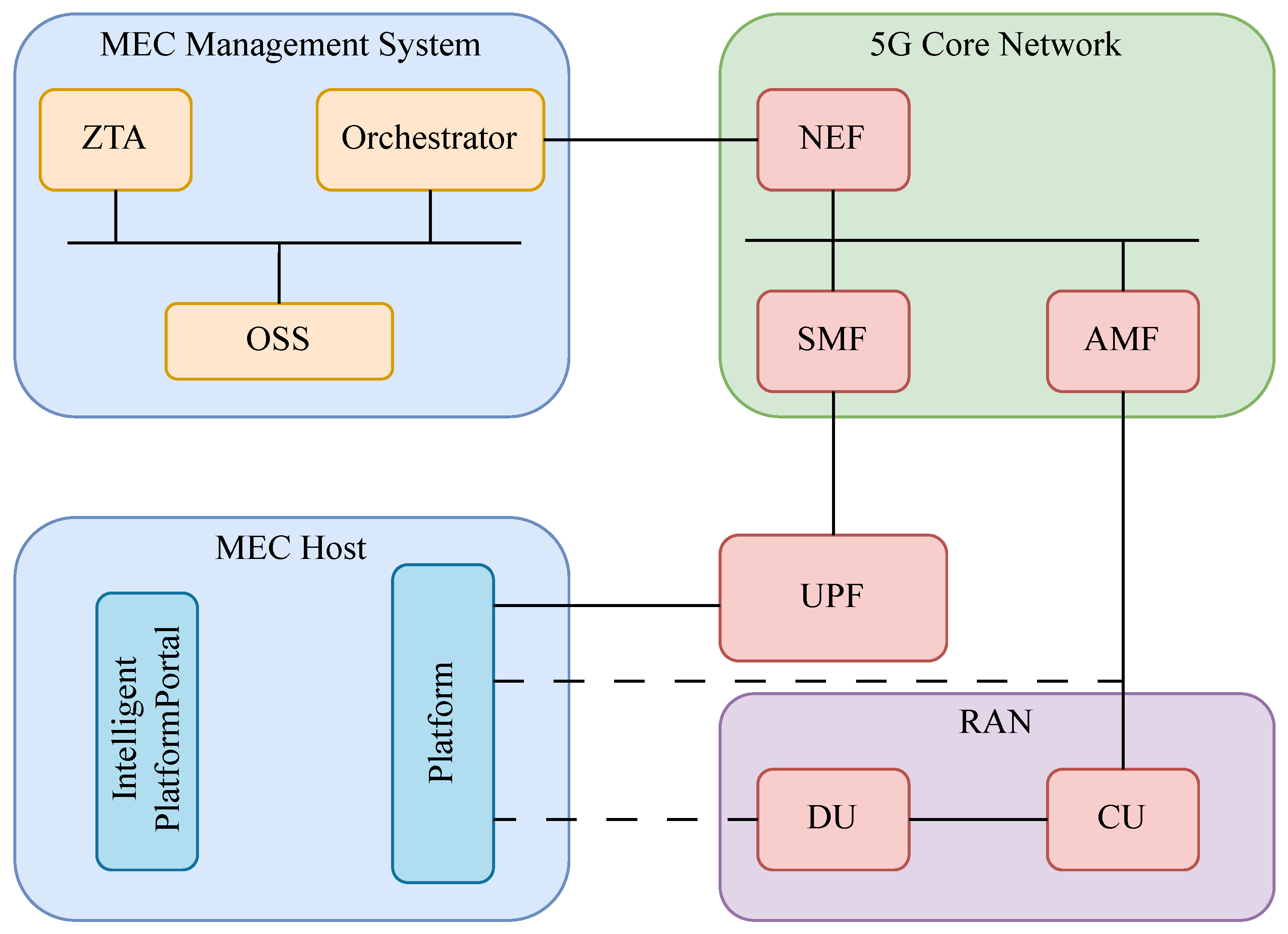
3.1.3. SDN, NFV, MEC
3.1.4. Vendor Trust
3.2. Radio Access Network
3.2.1. Non-Public Networks
3.2.2. Handover
3.2.3. Roaming
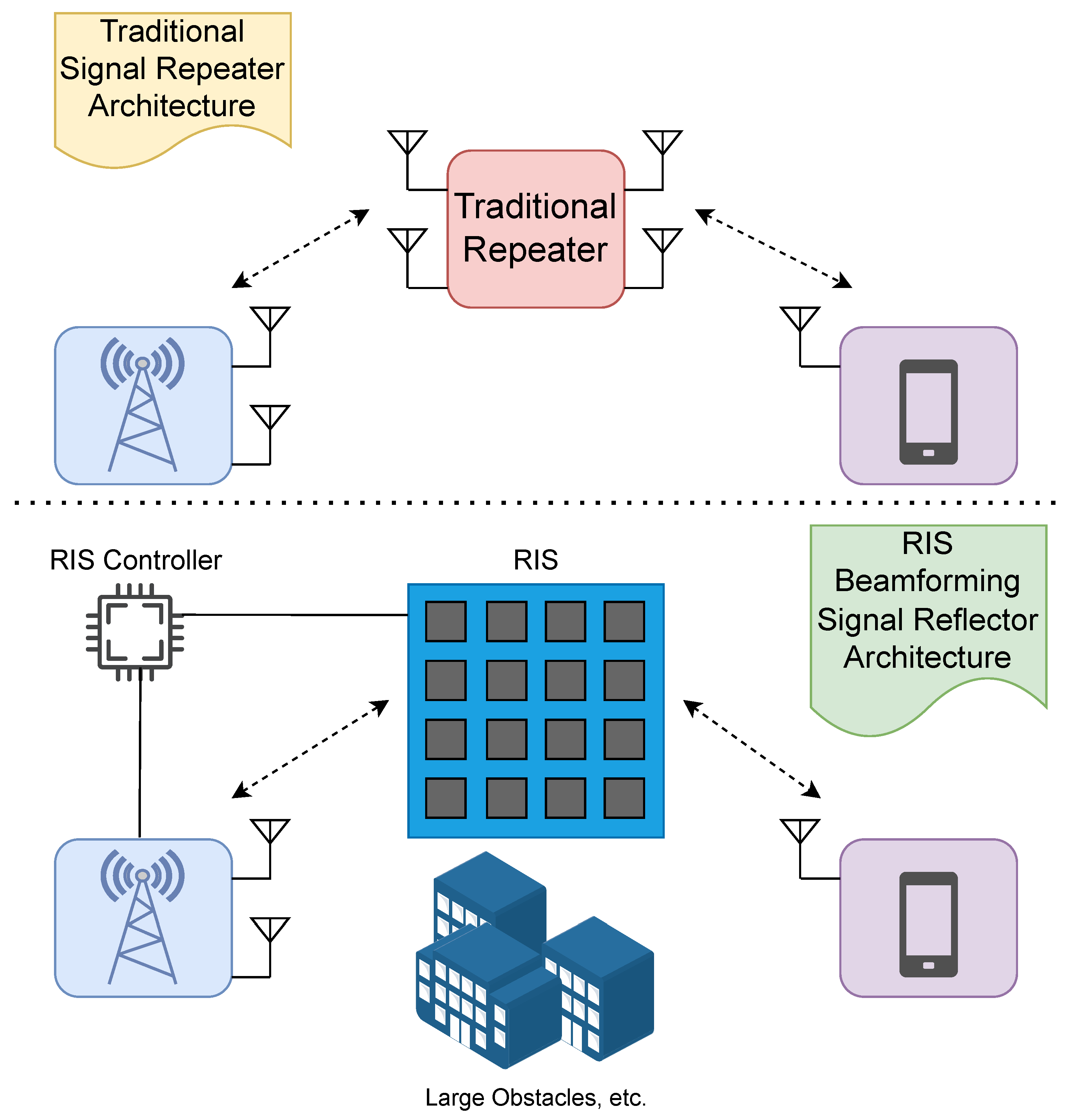
3.2.4. Reconfigurable Intelligent Surfaces (RIS) and RIS-Aided Beamforming
3.2.5. O-RAN
3.2.6. Network Slicing
- Performance: Every slice is designed to meet specific service requirements. In order to protect the performance of one slice compared to other concerns on the network, there must be mechanisms in place to ensure that requirements are met as best as possible under changing network conditions while ensuring that security is not sacrificed in the process and without impeding the operations of other slices.
- Security and Privacy: Faults or attacks impacting one slice must not impact another slice. Every slice must, therefore, provide its own independent security functions that prohibit unauthorized read or write access to configuration/management/accounting information.
- Management: Each slice is seen as a separate network, and to achieve isolation, consistent policies and mechanisms need to be defined at the virtualization layer. The policies describe how different manageable entities must be separated from each other while the mechanisms within the system execute the protocols and enforce the defined policies. The author states that the interplay of both virtualization and orchestration is necessary.
- Mutual authentication
- Implemented between the management service consumer (the entity using or consuming the management services) and the management service producer (the entity providing the management services).
- Transport Layer Security (TLS) is used to secure the communications
- Designed to prevent unauthorized actions at the exposed management interfaces
- Protection of management
- Interactions between the management service consumer and producer are secured via TLS.
- TLS includes protections such as:
- –
- Confidentiality Protection: Keeping the message exchanges confidential and encrypted;
- –
- Integrity Protection: Awareness that the data have not been changed or tampered with;
- –
- Replay Protection: Preventing the unauthorized replaying of previously captured messages to commit unauthorized actions.
- Authorization of management
- Management service consumers are authorized by the management service producer by way of an OAuth (Open Authorization) [77] mechanism.
- Operators’ local policies are taken into account during authorization.
- Only specific authorized services are granted to the consumer.
3.2.7. Massive MIMO
3.3. User Equipment
3.3.1. PHY Security
3.3.2. D2D, V2X
- Authentication: Securing D2D communication requires authentication as one of the main aspects when connecting to the 5G IoT network. All networks need to have mechanisms in place to identify and verify users.
- Data Confidentiality and Integrity: The use of hash functions and message authentication algorithms along with encrypted messages are vital to the confidentiality and integrity of the network. Prevalent concerns over these aspects stem from the number of eavesdropping, replay, and modification attacks that can occur if data are not secured.
- Anonymity: The aspect of anonymity in a network is necessary so the identity of users is concealed and unknown to attackers. Anonymity prevents attackers from targeting specific users on the network. In the case of V2X, anonymity is paramount because when this principle is violated, an attacker could pinpoint a specific car, track its movement, and cause harm to an individual or a group of people.
- Efficiency: As IoT devices have limited resources, it is important that they can request and obtain information on demand and without delay, as they are resource-constrained. The economical and efficient operation of communication systems is vital to the swift operations necessary in an IoT environment.
3.3.3. SIM, Modems, Operating Systems
- Identify and defend against network-based attacks, phishing scams, and mobile malware installation.
- Force users to implement a password on devices.
- Enable the selective device wipe feature for corporate data and applications to safeguard sensitive data.
- Safeguard organizational data integrity by limiting an employee’s capability to copy and paste, take screen captures, or save corporate data in unauthorized locations.
- Understand the potential hazards associated with the Bring-Your-Own-Device (BYOD) strategies and take corrective measures to address threats, such as risks resulting from rooted or jailbroken devices.
- Grant users the ability to reach secured business assets, such as knowledge bases, internal wikis, and application data.
- Ensure executing code is genuine while maintaining the integrity of the runtime state and safeguarding the confidentiality of persistent memory data.
- Secure data from eavesdropping during its transmission across a network.
- Evaluate and verify the security of mobile applications utilized for work-related tasks.
- Facilitate quick deployment and evaluation of BYOD solutions by providing detailed how-to guides covering initial setup and configuration for each component in the system.
4. Zero Trust Architecture (ZTA)
4.1. Zero Trust Applications in 5G
4.2. Risks and Limitations of ZTA
5. Proposed Future Security Mechanisms
5.1. Blockchain
5.1.1. Blockchain for Ultra-Dense Networks
5.1.2. Blockchain for Mobile Edge Computing
5.1.3. Blockchain Uses in 6G
- Intelligent Resource Management;
- Elevated Security Features;
- Industrial Applications;
- Smart Healthcare;
- Decentralized 6G Communications;
- Authentication, Availability, Integrity.
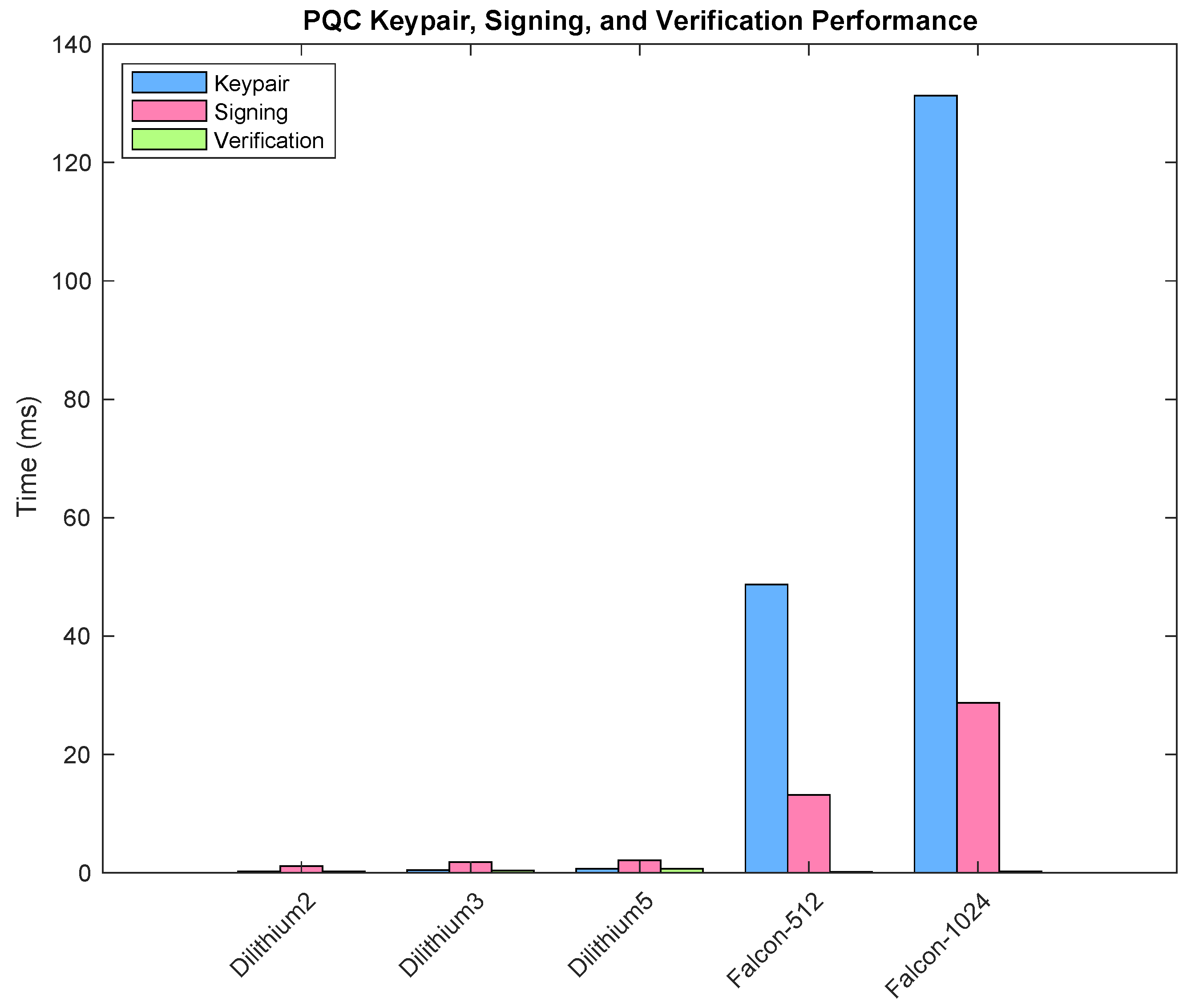
5.2. Post-Quantum Cryptography
5.2.1. Possible Post-Quantum Ciphers
5.2.2. Post-Quantum Cryptography in 5G and 6G
5.3. Artificial Intelligence for 6G
5.3.1. RAN Intelligent Controller
5.3.2. Proposed Security Features
5.3.3. Risks of AI in 6G Security
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| 3GPP | 3rd Generation Partnership Project |
| 5G | 5th Generation |
| CN | Core Network |
| RAN | Radio Access Network |
| UE | User Equipment |
| PQC | Post-Quantum Cryptography |
| IoT | Internet of Things |
| ZTA | Zero Trust Architecture |
| gNB | gNodeB |
| SDN | Software-Defined Network |
| NFV | Network Function Virtualization |
| MEC | Mobile Edge Computing |
| TS | Technical Standard |
| AKA | Authentication and Key Agreement |
| SN | Serving Network |
| AN | Access Network |
| AUSF | Authentication Server Function |
| SEAF | Security Anchor Function |
| NIST | National Institute of Science and Technology |
| SBA | Service Based Architecture |
| O-RAN | Open Radio Access Network |
| CDM | Continuous Diagnostics and Mitigation |
| ICAM | Identity, Credential, and Access Management |
| MNO | Mobile Network Operator |
| EAP | Extensible Authentication Protocols |
| PFS | Perfect Forward Security |
| DH | Diffie–Hellman |
| USIM | Universal Subscriber Identity Module |
| UDM | Unified Data Management |
| SUPI | Subscription Permanent Identifier |
| SUCI | Subscriber Concealed Identifier |
| DOS | Denial of Service |
| MA | Mutual Authentication |
| ASIC | Application-Specific Integrated Circuits |
| FPGA | Field-Programmable Gate Array |
| SMC | Security Mode Control |
| RRC | Radio Resource Control |
| PUF | Physical Unclonable Function |
| NPN | Non-Public Networks |
| TSN | Time-Sensitive Networking |
| NR | New Radio |
| LTE | Long-Term Evolution |
| VANET | Vehicular Ad Hoc Network |
| WLANs | Wireless Local Area Networks |
| HetNet | Heterogeneous Network |
| EPC | Evolved Packet Core |
| UMTS | Universal Mobile Telecommunications System |
| O-vRAN | Open Virtualized Radio Access Network |
| CVE | Common Vulnerabilities and Exposures |
| QoS | Quality of Service |
| TLS | Transport Layer Security |
| RIS | Reconfigurable Intelligent Surface |
| IRIS | Illegal Reconfigurable Intelligent Surface |
| OAuth | Open Authentication |
| NAS | Non-Access Stratum |
| AS | Access Stratum |
| MIMO | Multiple Input Multiple Output |
| RB | Radio Bearer |
| NOMA | Non-Orthogonal Multiple Access |
| PHY | Physical Layer |
| PLS | Physical Layer Security |
| SNR | Signal-to-Noise Ratio |
| D2D | Device to Device |
| V2X | Vehicle to Everything |
| BYOD | Bring Your Own Device |
| i-ZTA | Intelligent Zero Trust Architecture |
| SelfDN | Self-Driving Network |
| MEP | Mobile Edge Computing Platform |
| UPF | User Plane Function |
| UDN | Ultra Dense Network |
| AP | Access Point |
| ECC | Elliptic Curve Cryptography |
| XMSS | eXtended Merkle Signature Scheme |
| FIPS | Federal Information Processing Standards |
| CRYSTALS | Cryptographic Suite for Algebraic Lattices |
| CA | Certificate Authority |
| QoE | Quality of Experience |
| RIC | RAN Intelligent Controller |
| VNF | Virtualized Network Functions |
| THz | Terahertz |
| NTN | Non-Terrestrial Networks |
References
- Vintilă, C.E.; Patriciu, V.V.; Bica, I. Security analysis of LTE access network. In Proceedings of the 10th International Conference on Network, Valencia, Spain, 9–13 May 2011; pp. 29–34. [Google Scholar]
- TS 33.501; Security Architecture and Procedures for 5G System. 3GPP: Valbonne, France, 2023. Available online: https://www.3gpp.org/ftp/Specs/archive/33_series/33.501/ (accessed on 10 August 2023).
- TS 33.401; Technical Specification Group Services and System Aspects; 3GPP System Architecture Evoltuion (SAE); Security Architecture, Release 17, V17.4.0. 3rd Generation Partnership Project: Valbonne, France, 2023.
- Dutta, A.; Hammad, E. 5G Security Challenges and Opportunities: A System Approach. In Proceedings of the 2020 IEEE 3rd 5G World Forum (5GWF), Bangalore, India, 10–12 September 2020; pp. 109–114. [Google Scholar] [CrossRef]
- Cao, J.; Ma, M.; Li, H.; Ma, R.; Sun, Y.; Yu, P.; Xiong, L. A Survey on Security Aspects for 3GPP 5G Networks. IEEE Commun. Surv. Tutor. 2020, 22, 170–195. [Google Scholar] [CrossRef]
- de Castro Nunes Borges, V.O.; Rosa, R.L. General Aspects of Information Security in 5G Networks: Survey. Available online: https://infocomp.dcc.ufla.br/index.php/infocomp/article/view/3072 (accessed on 16 February 2024).
- Sachdeva, T.; Kumar, S.; Diwakar, M.; Singh, P.; Pandey, N.K.; Choudhary, S. Comparative Analysis of 5G Security Mechanisms. In Proceedings of the 2023 6th International Conference on Information Systems and Computer Networks (ISCON), Mathura, India, 3–4 March 2023; pp. 1–4. [Google Scholar] [CrossRef]
- Zhang, S.; Wang, Y.; Zhou, W. Towards secure 5G networks: A Survey. Comput. Netw. 2019, 162, 106871. [Google Scholar] [CrossRef]
- Tashtoush, Y.; Darweesh, D.; Karajeh, O.; Darwish, O.; Maabreh, M.; Swedat, S.; Koraysh, R.; Almousa, O.; Alsaedi, N. Survey on authentication and security protocols and schemes over 5G networks. Int. J. Distrib. Sens. Netw. 2022, 18, 15501329221126609. [Google Scholar] [CrossRef]
- Ounza, J.E. A taxonomical survey of 5G and 6G security and privacy issues. Glob. J. Eng. Technol. Adv. 2023, 14, 042–060. [Google Scholar] [CrossRef]
- Ramezanpour, K.; Jagannath, J.; Jagannath, A. Security and privacy vulnerabilities of 5G/6G and WiFi 6: Survey and research directions from a coexistence perspective. Comput. Netw. 2023, 221, 109515. [Google Scholar] [CrossRef]
- Park, J.H.; Rathore, S.; Singh, S.K.; Salim, M.M.; Azzaoui, A.; Kim, T.W.; Pan, Y.; Park, J.H. A comprehensive survey on core technologies and services for 5G security: Taxonomies, issues, and solutions. Hum.-Centric Comput. Inf. Sci. 2021, 11. [Google Scholar]
- Stafford, V. Zero trust architecture. Nist Spec. Publ. 2020, 800, 207. [Google Scholar]
- Ramezanpour, K.; Jagannath, J. Intelligent zero trust architecture for 5G/6G networks: Principles, challenges, and the role of machine learning in the context of O-RAN. Comput. Netw. 2022, 217, 109358. [Google Scholar] [CrossRef]
- Bhardwaj, A. 5G for Military Communications. Procedia Comput. Sci. 2020, 171, 2665–2674. [Google Scholar] [CrossRef]
- Marsh, S.P. Formalising Trust as a Computational Concept. Available online: https://www.cs.stir.ac.uk/~kjt/techreps/pdf/TR133.pdf (accessed on 16 February 2024).
- Sultan, A. 5G System Overview; 3GPP: Valbonne, France, 2022. [Google Scholar]
- Khan, R.; Kumar, P.; Jayakody, D.N.K.; Liyanage, M. A Survey on Security and Privacy of 5G Technologies: Potential Solutions, Recent Advancements, and Future Directions. IEEE Commun. Surv. Tutor. 2020, 22, 196–248. [Google Scholar] [CrossRef]
- Prasad, A.R.; Zugenmaier, A.; Escott, A.; Soveri, M.C. 3GPP 5G Security; 3GPP: Valbonne, France, 2018. [Google Scholar]
- Ben Henda, N.; Wifvesson, M.; Jost, C. An Overview of the 3GPP 5G Security Standard-Ericsson. Available online: https://www.ericsson.com/en/blog/2019/7/3gpp-5g-security-overview (accessed on 16 February 2024).
- TS 33.501; Technical Specification Group Services and System Aspects; Security Architecture and Procedures for 5G System Release 18, V18.2.0. 3rd Generation Partnership Project: Valbonne, France, 2023.
- Munilla, J.; Burmester, M.; Barco, R. An enhanced symmetric-key based 5G-AKA protocol. Comput. Netw. 2021, 198, 108373. [Google Scholar] [CrossRef]
- Koutsos, A. The 5G-AKA authentication protocol privacy. In Proceedings of the 2019 IEEE European Symposium on Security and Privacy (EuroS&P), Stockholm, Sweden, 17–19 June 2019; pp. 464–479. [Google Scholar]
- Basin, D.; Dreier, J.; Hirschi, L.; Radomirovic, S.; Sasse, R.; Stettler, V. A Formal Analysis of 5G Authentication. In Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security CCS ’18, New York, NY, USA, 15–19 October 2018; pp. 1383–1396. [Google Scholar] [CrossRef]
- Khan, H.; Martin, K.M. A survey of subscription privacy on the 5G radio interface-the past, present and future. J. Inf. Secur. Appl. 2020, 53, 102537. [Google Scholar] [CrossRef]
- Edris, E.K.K.; Aiash, M.; Loo, J.K.K. Formal verification and analysis of primary authentication based on 5G-AKA protocol. In Proceedings of the 2020 Seventh International Conference on Software Defined Systems (SDS), Paris, France, 20–23 April 2020; pp. 256–261. [Google Scholar]
- Nair, S. Authentication and Key Management for Applications (AKMA) in 5G; 3GPP: Valbonne, France, 2022. [Google Scholar]
- Vidhani, S.M.; Vidhate, A.V. Security Challenges in 5G Network: A technical features survey and analysis. In Proceedings of the 2022 5th International Conference on Advances in Science and Technology (ICAST), Mumbai, India, 2–3 December 2022; pp. 592–597. [Google Scholar] [CrossRef]
- Ji, X.; Huang, K.; Jin, L.; Tang, H.; Liu, C.; Zhong, Z.; You, W.; Xu, X.; Zhao, H.; Wu, J.; et al. Overview of 5G security technology. Sci. China Inf. Sci. 2018, 61, 081301. [Google Scholar] [CrossRef]
- Scott-Hayward, S.; O’Callaghan, G.; Sezer, S. SDN security: A survey. In Proceedings of the 2013 IEEE SDN For Future Networks and Services (SDN4FNS), Trento, Italy, 11–13 November 2013; pp. 1–7. [Google Scholar]
- Kloeti, R.; Kotronis, V.; Smith, P. OpenFlow: A Security Analysis. April 2013. In Proceedings of the 2013 21st IEEE International Conference on Network Protocols (ICNP), Goettingen, Germany, 7–10 October 2013. [Google Scholar]
- Shin, S.W.; Porras, P.; Yegneswara, V.; Fong, M.; Gu, G.; Tyson, M. Fresco: Modular composable security services for software-defined networks. In Proceedings of the 20th Annual Network & Distributed System Security Symposium, San Diego, CA, USA, 24–27 February 2013. [Google Scholar]
- Salahdine, F.; Han, T.; Zhang, N. Security in 5G and beyond recent advances and future challenges. Secur. Priv. 2023, 6, e271. [Google Scholar] [CrossRef]
- Kazmi, S.H.A.; Qamar, F.; Hassan, R.; Nisar, K.; Chowdhry, B.S. Survey on Joint Paradigm of 5G and SDN Emerging Mobile Technologies: Architecture, Security, Challenges and Research Directions. Wirel. Pers. Commun. 2023, 130, 2753–2800. [Google Scholar] [CrossRef]
- Tang, Q.; Ermis, O.; Nguyen, C.D.; Oliveira, A.D.; Hirtzig, A. A Systematic Analysis of 5G Networks with a Focus on 5G Core Security. IEEE Access 2022, 10, 18298–18319. [Google Scholar] [CrossRef]
- Sahni, I.; Kaur, A. A Systematic Literature Review on 5G Security. arXiv 2022, arXiv:2212.03299. [Google Scholar]
- Choudhary, G.; Kim, J.; Sharma, V. Security of 5G-mobile backhaul networks: A survey. arXiv 2019, arXiv:1906.11427. [Google Scholar]
- Bello, Y.; Hussein, A.R.; Ulema, M.; Koilpillai, J. On Sustained Zero Trust Conceptualization Security for Mobile Core Networks in 5G and Beyond. IEEE Trans. Netw. Serv. Manag. 2022, 19, 1876–1889. [Google Scholar] [CrossRef]
- Hireche, O.; Benzaïd, C.; Taleb, T. Deep data plane programming and AI for zero-trust self-driven networking in beyond 5G. Comput. Netw. 2022, 203, 108668. [Google Scholar] [CrossRef]
- Fang, D.; Qian, Y.; Hu, R.Q. Security Requirement and Standards for 4G and 5G Wireless Systems. Getmobile Mob. Comp. Comm. 2018, 22, 15–20. [Google Scholar] [CrossRef]
- Moreira, C.M.; Kaddoum, G.; Bou-Harb, E. Cross-layer authentication protocol design for ultra-dense 5G HetNets. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–7. [Google Scholar]
- Samonas, S.; Coss, D. The CIA strikes back: Redefining confidentiality, integrity and availability in security. J. Inf. Syst. Secur. 2014, 10. [Google Scholar]
- Kornaros, G.; Tomoutzoglou, O.; Coppola, M. Hardware-assisted security in electronic control units: Secure automotive communications by utilizing one-time-programmable network on chip and firewalls. IEEE Micro 2018, 38, 63–74. [Google Scholar] [CrossRef]
- Salazar, Z.; Nguyen, H.N.; Mallouli, W.; Cavalli, A.R.; Montes de Oca, E. 5Greplay: A 5G Network Traffic Fuzzer-Application to Attack Injection. In Proceedings of the 16th International Conference on Availability, Reliability and Security, ARES ’21, New York, NY, USA, 17–20 August 2021. [Google Scholar] [CrossRef]
- Park, S.; You, I.; Park, H.; Kim, D. Analyzing RRC Replay Attack and Securing Base Station with Practical Method. In Proceedings of the 17th International Conference on Availability, Reliability and Security, ARES ’22, New York, NY, USA, 23–26 August 2022. [Google Scholar] [CrossRef]
- Bordel Sánchez, B.; Alcarria Garrido, R.P. Physical Unclonable Functions based on silicon micro-ring resonators for secure signature delegation in Wireless Sensor Networks. J. Internet Serv. Inf. Secur. 2018, 8, 40–53. [Google Scholar]
- Yousef Alshunaifi, S.; Mishra, S.; Alshehri, M. Cyber-Attack Detection and Mitigation Using SVM for 5G Network. Intell. Autom. Soft Comput. 2022, 31. [Google Scholar] [CrossRef]
- Kim, D. Non-Public Networks (NPN); 3GPP: Valbonne, France, 2022. [Google Scholar]
- TS 22.261; Service Requirements for the 5G System, Release 19, V19.4.0. 3rd Generation Partnership Project: Valbonne, France, 2023.
- Jerichow, A.; Covell, B.; Chandramouli, D.; Rezaki, A.; Lansisalmi, A.; Merkel, J. 3GPP non-public network security. J. ICT Stand. 2020, 57–76. [Google Scholar] [CrossRef]
- Prados-Garzon, J.; Ameigeiras, P.; Ordonez-Lucena, J.; Muñoz, P.; Adamuz-Hinojosa, O.; Camps-Mur, D. 5G non-public networks: Standardization, architectures and challenges. IEEE Access 2021, 9, 153893–153908. [Google Scholar] [CrossRef]
- Trakadas, P.; Sarakis, L.; Giannopoulos, A.; Spantideas, S.; Capsalis, N.; Gkonis, P.; Karkazis, P.; Rigazzi, G.; Antonopoulos, A.; Cambeiro, M.A.; et al. A cost-efficient 5G non-public network architectural approach: Key concepts and enablers, building blocks and potential use cases. Sensors 2021, 21, 5578. [Google Scholar] [CrossRef]
- Andrews, J.G.; Buzzi, S.; Choi, W.; Hanly, S.V.; Lozano, A.; Soong, A.C.; Zhang, J.C. What will 5G be? IEEE J. Sel. Areas Commun. 2014, 32, 1065–1082. [Google Scholar] [CrossRef]
- Ericsson. Ericsson Mobility Report, Mobile Subscriptions Q2 2023; Technical report; Ericsson: Stockholm, Sweden, 2023. [Google Scholar]
- TS 23.502; Technical Specification Group Services and System Aspects; Procedures for the 5G System; Release 18, V18.2.0. 3rd Generation Partnership Project: Valbonne, France, 2023.
- TS 23.837; Location Services (LCS) Architecture for 3GPP System-Wireless Local Area Network (WLAN) Interworking; Release 7. 3rd Generation Partnership Project: Valbonne, France, 2006.
- TS 38.300; NR; NR and NG-RAN Overall Description; Stage-2 Release 17. 3rd Generation Partnership Project: Valbonne, France, 2023.
- Zhao, D.; Yan, Z.; Wang, M.; Zhang, P.; Song, B. Is 5G Handover Secure and Private? A Survey. IEEE Internet Things J. 2021, 8, 12855–12879. [Google Scholar] [CrossRef]
- Reddy Chavva, A.K.; Rao, V.R.R. Reconfigurable Intelligent Surface (RIS) and Factors Influencing Its Role in Future Networks. Available online: https://research.samsung.com/blog/Reconfigurable-Intelligent-Surface-RIS-and-Factors-Influencing-it-s-Role-in-Future-Networks (accessed on 16 February 2024).
- Luo, J.; Wang, F.; Wang, S.; Wang, H.; Wang, D. Reconfigurable intelligent surface: Reflection design against passive eavesdropping. IEEE Trans. Wirel. Commun. 2021, 20, 3350–3364. [Google Scholar] [CrossRef]
- Dong, L.; Wang, H.M.; Bai, J. Active Reconfigurable Intelligent Surface Aided Secure Transmission. IEEE Trans. Veh. Technol. 2022, 71, 2181–2186. [Google Scholar] [CrossRef]
- Zhang, J.; Du, H.; Sun, Q.; Ai, B.; Ng, D.W.K. Physical Layer Security Enhancement with Reconfigurable Intelligent Surface-Aided Networks. IEEE Trans. Inf. Forensics Secur. 2021, 16, 3480–3495. [Google Scholar] [CrossRef]
- Naeem, F.; Ali, M.; Kaddoum, G.; Huang, C.; Yuen, C. Security and Privacy for Reconfigurable Intelligent Surface in 6G: A Review of Prospective Applications and Challenges. IEEE Open J. Commun. Soc. 2023, 4, 1196–1217. [Google Scholar] [CrossRef]
- Lyu, B.; Hoang, D.T.; Gong, S.; Niyato, D.; Kim, D.I. IRS-based wireless jamming attacks: When jammers can attack without power. IEEE Wirel. Commun. Lett. 2020, 9, 1663–1667. [Google Scholar] [CrossRef]
- Networks, G. OpenRAN (O-ran) for 5G Explained. 2020. Available online: https://www.5g-networks.net/5g-technology/openran-o-ran-for-5g-explained/ (accessed on 27 December 2023).
- Hanselman, E. Security Benefits of Open Virtualized RAN. 2020. Available online: https://www.cisco.com/c/dam/en/us/solutions/service-provider/pdfs/5g-network-architecture/white-paper-sp-open-vran-security-benefits.pdf (accessed on 27 December 2023).
- Nokia. 5G Managed Security Survey 2022. 2023. Available online: https://onestore.nokia.com/asset/212741?_ga=2.218954462.611512529.1668533812-1895305122.1668533812 (accessed on 7 February 2024).
- GSMA. 5G Security Issues. 2019. Available online: https://www.gsma.com/get-involved/gsma-membership/wp-content/uploads/2019/11/5G-Research_A4.pdf (accessed on 7 February 2024).
- TrendMicro. Attacks on 5G Infrastructure from User Devices. 2023. Available online: https://www.trendmicro.com/en_us/research/23/i/attacks-on-5g-infrastructure-from-users-devices.html (accessed on 7 February 2024).
- Lawton, G. Open source security: Opportunity or oxymoron? Computer 2002, 35, 18–21. [Google Scholar] [CrossRef]
- Tung, Y.C.; Liou, E.C.; Cheng, C.H.; Lin, T.H.; Chuang, S.M. Closed-Loop Security Management for Developing O-RAN Infrastructure and B5G RIC Applications. In Proceedings of the 2023 26th International Symposium on Wireless Personal Multimedia Communications (WPMC), Tampa, FL, USA, 19–22 November 2023; pp. 278–281. [Google Scholar]
- Zhang, H.; Liu, N.; Chu, X.; Long, K.; Aghvami, A.H.; Leung, V.C.M. Network Slicing Based 5G and Future Mobile Networks: Mobility, Resource Management, and Challenges. IEEE Commun. Mag. 2017, 55, 138–145. [Google Scholar] [CrossRef]
- Campolo, C.; Molinaro, A.; Iera, A.; Menichella, F. 5G Network Slicing for Vehicle-to-Everything Services. IEEE Wirel. Commun. 2017, 24, 38–45. [Google Scholar] [CrossRef]
- Dangi, R.; Jadhav, A.; Choudhary, G.; Dragoni, N.; Mishra, M.K.; Lalwani, P. ML-Based 5G Network Slicing Security: A Comprehensive Survey. Future Internet 2022, 14, 116. [Google Scholar] [CrossRef]
- Ordonez-Lucena, J.; Ameigeiras, P.; Lopez, D.; Ramos-Munoz, J.J.; Lorca, J.; Folgueira, J. Network Slicing for 5G with SDN/NFV: Concepts, Architectures, and Challenges. IEEE Commun. Mag. 2017, 55, 80–87. [Google Scholar] [CrossRef]
- Cano, M. Technologies; 3GPP: Valbonne, France, 2023. [Google Scholar]
- OAuth. OAuth 2.0, an Industry-Standard Protocol for Authorization. 2023. Available online: https://oauth.net/2/ (accessed on 16 February 2024).
- Khan, L.U.; Yaqoob, I.; Tran, N.H.; Han, Z.; Hong, C.S. Network Slicing: Recent Advances, Taxonomy, Requirements, and Open Research Challenges. IEEE Access 2020, 8, 36009–36028. [Google Scholar] [CrossRef]
- Adesina, D.; Hsieh, C.C.; Sagduyu, Y.E.; Qian, L. Adversarial machine learning in wireless communications using RF data: A review. IEEE Commun. Surv. Tutor. 2022, 25, 77–100. [Google Scholar] [CrossRef]
- Grønsund, P.; Gonzalez, A.; Mahmood, K.; Nomeland, K.; Pitter, J.; Dimitriadis, A.; Berg, T.K.; Gelardi, S. 5g service and slice implementation for a military use case. In Proceedings of the 2020 IEEE International Conference on Communications Workshops (ICC Workshops), Dublin, Ireland, 7–11 June 2020; pp. 1–6. [Google Scholar]
- Osseiran, A.; Boccardi, F.; Braun, V.; Kusume, K.; Marsch, P.; Maternia, M.; Queseth, O.; Schellmann, M.; Schotten, H.; Taoka, H.; et al. Scenarios for 5G mobile and wireless communications: The vision of the METIS project. IEEE Commun. Mag. 2014, 52, 26–35. [Google Scholar] [CrossRef]
- Boccardi, F.; Heath, R.W.; Lozano, A.; Marzetta, T.L.; Popovski, P. Five disruptive technology directions for 5G. IEEE Commun. Mag. 2014, 52, 74–80. [Google Scholar] [CrossRef]
- Wang, C.X.; Haider, F.; Gao, X.; You, X.H.; Yang, Y.; Yuan, D.; Aggoune, H.M.; Haas, H.; Fletcher, S.; Hepsaydir, E. Cellular architecture and key technologies for 5G wireless communication networks. IEEE Commun. Mag. 2014, 52, 122–130. [Google Scholar] [CrossRef]
- Chih-Lin, I.; Rowell, C.; Han, S.; Xu, Z.; Li, G.; Pan, Z. Toward green and soft: A 5G perspective. IEEE Commun. Mag. 2014, 52, 66–73. [Google Scholar]
- Ge, X.; Cheng, H.; Guizani, M.; Han, T. 5G wireless backhaul networks: Challenges and research advances. IEEE Netw. 2014, 28, 6–11. [Google Scholar] [CrossRef]
- Yang, S.; Yin, D.; Song, X.; Dong, X.; Manogaran, G.; Mastorakis, G.; Mavromoustakis, C.X.; Batalla, J.M. Security situation assessment for massive MIMO systems for 5G communications. Future Gener. Comput. Syst. 2019, 98, 25–34. [Google Scholar] [CrossRef]
- Schaefer, R.F.; Amarasuriya, G.; Poor, H.V. Physical layer security in massive MIMO systems. In Proceedings of the 2017 51st Asilomar Conference on Signals, Systems, and Computers, Pacific Grove, CA, USA, 29 October–1 November 2017; pp. 3–8. [Google Scholar]
- Kapetanovic, D.; Zheng, G.; Rusek, F. Physical layer security for massive MIMO: An overview on passive eavesdropping and active attacks. IEEE Commun. Mag. 2015, 53, 21–27. [Google Scholar] [CrossRef]
- Xiao, K.; Gong, L.; Kadoch, M. Opportunistic multicast NOMA with security concerns in a 5G massive MIMO system. IEEE Commun. Mag. 2018, 56, 91–95. [Google Scholar] [CrossRef]
- Gao, Y.; Hu, S.; Tang, W.; Li, Y.; Sun, Y.; Huang, D.; Cheng, S.; Li, X. Physical Layer Security in 5G Based Large Scale Social Networks: Opportunities and Challenges. IEEE Access 2018, 6, 26350–26357. [Google Scholar] [CrossRef]
- Ahmed, I.; Khammari, H.; Shahid, A.; Musa, A.; Kim, K.S.; De Poorter, E.; Moerman, I. A Survey on Hybrid Beamforming Techniques in 5G: Architecture and System Model Perspectives. IEEE Commun. Surv. Tutor. 2018, 20, 3060–3097. [Google Scholar] [CrossRef]
- Sun, L.; Du, Q. Physical layer security with its applications in 5G networks: A review. China Commun. 2017, 14, 1–14. [Google Scholar] [CrossRef]
- Sun, L.; Du, Q.; Ren, P.; Wang, Y. Two birds with one stone: Towards secure and interference-free D2D transmissions via constellation rotation. IEEE Trans. Veh. Technol. 2015, 65, 8767–8774. [Google Scholar] [CrossRef]
- Du, Q.; Sun, L.; Ren, P.; Wang, Y. Statistical security model and power adaptation over wireless fading channels. In Proceedings of the 2015 International Conference on Wireless Communications & Signal Processing (WCSP), Nanjing, China, 15–17 October 2015; pp. 1–6. [Google Scholar]
- Li, W.; Du, Q.; Sun, L.; Ren, P.; Wang, Y. Security enhanced via dynamic fountain code design for wireless delivery. In Proceedings of the 2016 IEEE Wireless Communications and Networking Conference, Doha, Qatar, 3–6 April 2016. [Google Scholar]
- MacKay, D.J. Fountain codes. IEE Proc.-Commun. 2005, 152, 1062–1068. [Google Scholar] [CrossRef]
- Seok, B.; Sicato, J.C.S.; Erzhena, T.; Xuan, C.; Pan, Y.; Park, J.H. Secure D2D communication for 5G IoT network based on lightweight cryptography. Appl. Sci. 2019, 10, 217. [Google Scholar] [CrossRef]
- Zhang, A.; Lin, X. Security-aware and privacy-preserving D2D communications in 5G. IEEE Netw. 2017, 31, 70–77. [Google Scholar] [CrossRef]
- Wang, M.; Yan, Z. Security in D2D communications: A review. In Proceedings of the 2015 IEEE Trustcom/BigDataSE/ISPA, Washington, DC, USA, 20–22 August 2015; Volume 1, pp. 1199–1204. [Google Scholar]
- Sun, Y.; Cao, J.; Ma, M.; Li, H.; Niu, B.; Li, F. Privacy-preserving device discovery and authentication scheme for D2D communication in 3GPP 5G HetNet. In Proceedings of the 2019 International Conference on Computing, Networking and Communications (ICNC), Honolulu, HI, USA, 18–21 February 2019; pp. 425–431. [Google Scholar]
- Mars, A.; Abadleh, A.; Adi, W. Operator and manufacturer independent D2D private link for future 5G networks. In Proceedings of the IEEE INFOCOM 2019-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Paris, France, 29 April–2 May 2019; pp. 1–6. [Google Scholar]
- Howell, G.; Boeckl, K.; Grayson, N.R.; Lefkovitz, N.; Ajmo, J.; Craft, R.E.; McGinnis, M.; Sandlin, K.; Slivina, O.; Snyder, J.; et al. Mobile Device Security: Bring Your Own Device (BYOD); National Institute of Standards and Technology: Gaithersburg, MD, USA, 2023. [Google Scholar]
- Kholidy, H.A.; Karam, A.; Sidoran, J.; Rahman, M.A.; Mahmoud, M.; Badr, M.; Mahmud, M.; Sayed, A.F. Toward Zero Trust Security IN 5G Open Architecture Network Slices. In Proceedings of the MILCOM 2022—2022 IEEE Military Communications Conference (MILCOM), Rockville, MD, USA, 28 November–2 December 2022; pp. 577–582. [Google Scholar] [CrossRef]
- Manan, A.; Min, Z.; Mahmoudi, C.; Formicola, V. Extending 5G services with Zero Trust security pillars: A modular approach. In Proceedings of the 2022 IEEE/ACS 19th International Conference on Computer Systems and Applications (AICCSA), Abu Dhabi, United Arab Emirates, 5–8 December 2022; pp. 1–6. [Google Scholar] [CrossRef]
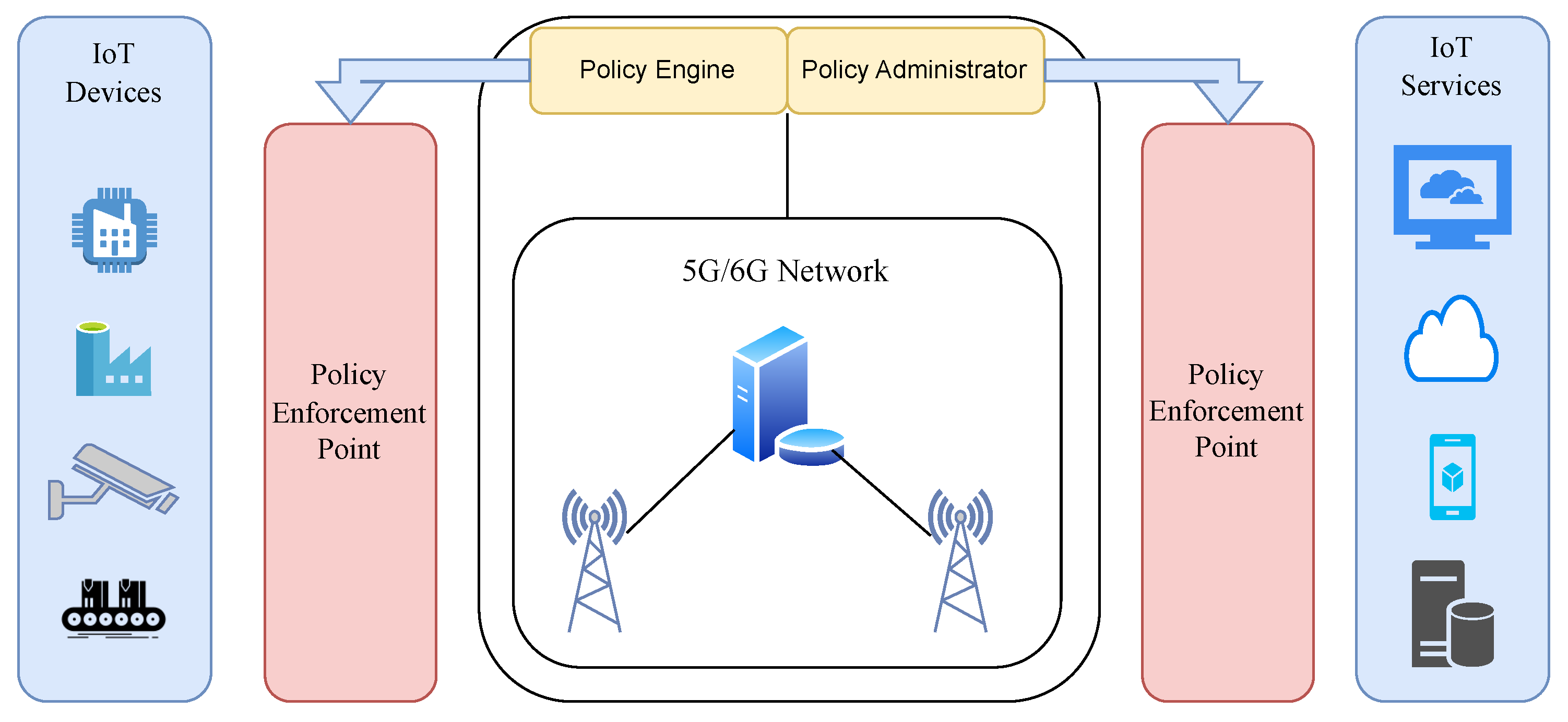
- Li, S.; Iqbal, M.; Saxena, N. Future industry internet of things with zero-trust security. Inf. Syst. Front. 2022, 1–14. [Google Scholar] [CrossRef]
- Malik, A.; Parihar, V.; Bhushan, B.; Chaganti, R.; Bhatia, S.; Astya, P.N. Security Services for Wireless 5G Internet of Things (IoT) Systems. In 5G and Beyond; Bhushan, B., Sharma, S.K., Kumar, R., Priyadarshini, I., Eds.; Springer Nature: Singapore, 2023; pp. 169–195. [Google Scholar] [CrossRef]
- Alipour, M.A.; Ghasemshirazi, S.; Shirvani, G. Enabling a Zero Trust Architecture in a 5G-enabled Smart Grid. arXiv 2022, arXiv:2210.01739. [Google Scholar]
- Feng, Z.; Zhou, P.; Wang, Q.; Qi, W. A Dual-layer Zero Trust Architecture for 5G Industry MEC Applications Access Control. In Proceedings of the 2022 IEEE 5th International Conference on Electronic Information and Communication Technology (ICEICT), Hefei, China, 21–23 August 2022; pp. 100–105. [Google Scholar] [CrossRef]
- Syed, N.F.; Shah, S.W.; Shaghaghi, A.; Anwar, A.; Baig, Z.; Doss, R. Zero Trust Architecture (ZTA): A Comprehensive Survey. IEEE Access 2022, 10, 57143–57179. [Google Scholar] [CrossRef]
- He, Y.; Huang, D.; Chen, L.; Ni, Y.; Ma, X. A survey on zero trust architecture: Challenges and future trends. Wirel. Commun. Mob. Comput. 2022, 2022, 6476274. [Google Scholar] [CrossRef]
- Buck, C.; Olenberger, C.; Schweizer, A.; Völter, F.; Eymann, T. Never trust, always verify: A multivocal literature review on current knowledge and research gaps of zero-trust. Comput. Secur. 2021, 110, 102436. [Google Scholar] [CrossRef]
- Chen, Z.; Chen, S.; Xu, H.; Hu, B. A Security Authentication Scheme of 5G Ultra-Dense Network Based on Block Chain. IEEE Access 2018, 6, 55372–55379. [Google Scholar] [CrossRef]
- Nguyen, D.C.; Pathirana, P.N.; Ding, M.; Seneviratne, A. Blockchain for 5G and beyond networks: A state of the art survey. J. Netw. Comput. Appl. 2020, 166, 102693. [Google Scholar] [CrossRef]
- Wu, H.; Wolter, K.; Jiao, P.; Deng, Y.; Zhao, Y.; Xu, M. EEDTO: An Energy-Efficient Dynamic Task Offloading Algorithm for Blockchain-Enabled IoT-Edge-Cloud Orchestrated Computing. IEEE Internet Things J. 2021, 8, 2163–2176. [Google Scholar] [CrossRef]
- Xu, Y.; Zhang, H.; Ji, H.; Yang, L.; Li, X.; Leung, V.C.M. Transaction Throughput Optimization for Integrated Blockchain and MEC System in IoT. IEEE Trans. Wirel. Commun. 2022, 21, 1022–1036. [Google Scholar] [CrossRef]
- Chen, Y.; Zhang, N.; Zhang, Y.; Chen, X. Dynamic Computation Offloading in Edge Computing for Internet of Things. IEEE Internet Things J. 2019, 6, 4242–4251. [Google Scholar] [CrossRef]
- Guo, S.; Hu, X.; Guo, S.; Qiu, X.; Qi, F. Blockchain Meets Edge Computing: A Distributed and Trusted Authentication System. IEEE Trans. Ind. Inform. 2020, 16, 1972–1983. [Google Scholar] [CrossRef]
- Yang, H.; Liang, Y.; Yuan, J.; Yao, Q.; Yu, A.; Zhang, J. Distributed Blockchain-Based Trusted Multidomain Collaboration for Mobile Edge Computing in 5G and Beyond. IEEE Trans. Ind. Inform. 2020, 16, 7094–7104. [Google Scholar] [CrossRef]
- Hewa, T.; Gür, G.; Kalla, A.; Ylianttila, M.; Bracken, A.; Liyanage, M. The role of blockchain in 6G: Challenges, opportunities and research directions. In Proceedings of the 2020 2nd 6G Wireless Summit (6G SUMMIT), Levi, Finland, 17–20 March 2020; pp. 1–5. [Google Scholar]
- Li, W.; Su, Z.; Li, R.; Zhang, K.; Wang, Y. Blockchain-based data security for artificial intelligence applications in 6G networks. IEEE Netw. 2020, 34, 31–37. [Google Scholar] [CrossRef]
- Kim, H.; Park, J.; Bennis, M.; Kim, S.L. Blockchained on-device federated learning. IEEE Commun. Lett. 2019, 24, 1279–1283. [Google Scholar] [CrossRef]
- Aumasson, J.P. The impact of quantum computing on cryptography. Comput. Fraud. Secur. 2017, 2017, 8–11. [Google Scholar] [CrossRef]
- Clancy, T.C.; McGwier, R.W.; Chen, L. Post-Quantum Cryptography and 5G Security: Tutorial. In Proceedings of the 12th Conference on Security and Privacy in Wireless and Mobile Networks, WiSec ’19, New York, NY, USA, 15–17 May 2019; p. 285. [Google Scholar] [CrossRef]
- Hoffstein, J.; Pipher, J.; Silverman, J.H. NTRU: A ring-based public key cryptosystem. In International Algorithmic Number Theory Symposium; Buhler, J.P., Ed.; Springer: Berlin/Heidelberg, Germany, 1998; pp. 267–288. [Google Scholar]
- Augot, D.; Batina, L.; Bernstein, D.J.; Bos, J.; Buchmann, J.; Castryck, W.; Dunkelman, O.; Güneysu, T.; Gueron, S.; Hülsing, A.; et al. Initial Recommendations of long-Term Secure Post-Quantum Systems (2015). Available online: https://pqcrypto.eu.org/docs/initial-recommendations.pdf (accessed on 12 August 2023).
- National Institute of Standards and Technology. Module-Lattice-Based Key-Encapsulation Mechanism Standard; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2023. [Google Scholar]
- Bos, J.; Ducas, L.; Kiltz, E.; Lepoint, T.; Lyubashevsky, V.; Schanck, J.M.; Schwabe, P.; Seiler, G.; Stehlé, D. CRYSTALS-Kyber: A CCA-secure module-lattice-based KEM. In Proceedings of the 2018 IEEE European Symposium on Security and Privacy (EuroS&P), London, UK, 24–26 April 2018; pp. 353–367. [Google Scholar]
- National Institute of Standards and Technology. Module-Lattice-Based Digital Signature Standard. 2023. Available online: https://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.204.ipd.pdf (accessed on 30 December 2023).
- Ducas, L.; Kiltz, E.; Lepoint, T.; Lyubashevsky, V.; Schwabe, P.; Seiler, G.; Stehlé, D. Crystals-dilithium: A lattice-based digital signature scheme. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2018, 2018, 238–268. [Google Scholar] [CrossRef]
- National Institute of Standards and Technology. Stateless Hash-Based Digital Signature Standard; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2023. [Google Scholar]
- Bernstein, D.J.; Hülsing, A.; Kölbl, S.; Niederhagen, R.; Rijneveld, J.; Schwabe, P. The SPHINCS+ signature framework. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, London, UK, 11–15 November 2019; pp. 2129–2146. [Google Scholar]
- Preuss Mattsson, J.; Thormarker, E.; Smeets, B. Migration of quantum-resistant algorithms to mobile networks. Ericsson Blog 2023. Available online: https://www.ericsson.com/en/blog/2023/2/quantum-resistant-algorithms-mobile-networks (accessed on 30 December 2023).
- Porambage, P.; Gür, G.; Osorio, D.P.M.; Liyanage, M.; Gurtov, A.; Ylianttila, M. The roadmap to 6G security and privacy. IEEE Open J. Commun. Soc. 2021, 2, 1094–1122. [Google Scholar] [CrossRef]
- Sajimon, P.; Jain, K.; Krishnan, P. Analysis of post-quantum cryptography for internet of things. In Proceedings of the 2022 6th International Conference on Intelligent Computing and Control Systems (ICICCS), Madurai, India, 25–27 May 2022; pp. 387–394. [Google Scholar]
- 3GPP. Evolved Universal Terrestrial Radio Access (E-UTRA) and NR; Study on Enhancement for Data Collection for NR and EN-DC (Release 17); 3GPP: Valbonne, France, 2022. [Google Scholar]
- Alwis, C.D.; Kalla, A.; Pham, Q.V.; Kumar, P.; Dev, K.; Hwang, W.J.; Liyanage, M. Survey on 6G Frontiers: Trends, Applications, Requirements, Technologies and Future Research. IEEE Open J. Commun. Soc. 2021, 2, 836–886. [Google Scholar] [CrossRef]
- Siriwardhana, Y.; Porambage, P.; Liyanage, M.; Ylianttila, M. AI and 6G Security: Opportunities and Challenges. In Proceedings of the 2021 Joint European Conference on Networks and Communications & 6G Summit (EuCNC/6G Summit), Porto, Portugal, 8–11 June 2021; pp. 616–621. [Google Scholar] [CrossRef]
- Balasubramanian, B.; Daniels, E.S.; Hiltunen, M.; Jana, R.; Joshi, K.; Sivaraj, R.; Tran, T.X.; Wang, C. RIC: A RAN Intelligent Controller Platform for AI-Enabled Cellular Networks. IEEE Internet Comput. 2021, 25, 7–17. [Google Scholar] [CrossRef]
- Lee, H.; Cha, J.; Kwon, D.; Jeong, M.; Park, I. Hosting AI/ML Workflows on O-RAN RIC Platform. In Proceedings of the 2020 IEEE Globecom Workshops (GC Wkshps), Taipei, Taiwan, 7–11 December 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Yang, H.; Alphones, A.; Xiong, Z.; Niyato, D.; Zhao, J.; Wu, K. Artificial-Intelligence-Enabled Intelligent 6G Networks. IEEE Netw. 2020, 34, 272–280. [Google Scholar] [CrossRef]
- Bárcena, J.L.C.; Ducange, P.; Marcelloni, F.; Nardini, G.; Noferi, A.; Renda, A.; Stea, G.; Virdis, A. Towards Trustworthy AI for QoE prediction in B5G/6G Networks. In Proceedings of the First Int’l Workshop on Artificial Intelligence in Beyond 5G and 6G Wireless Networks (AI6G 2022), Padua, Italy, 21 July 2022. [Google Scholar]
- Kohli, P.; Sharma, S.; Matta, P. Intrusion Detection Techniques For Security and Privacy of 6G Applications. In Proceedings of the 2023 Third International Conference on Secure Cyber Computing and Communication (ICSCCC), Jalandhar, India, 26–28 May 2023; pp. 560–565. [Google Scholar] [CrossRef]
- Saeed, M.M.; Saeed, R.A.; Abdelhaq, M.; Alsaqour, R.; Hasan, M.K.; Mokhtar, R.A. Anomaly detection in 6G networks using machine learning methods. Electronics 2023, 12, 3300. [Google Scholar] [CrossRef]
- Ayub, M.A.; Johnson, W.A.; Talbert, D.A.; Siraj, A. Model Evasion Attack on Intrusion Detection Systems using Adversarial Machine Learning. In Proceedings of the 2020 54th Annual Conference on Information Sciences and Systems (CISS), Princeton, NJ, USA, 18–20 March 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Wang, S.; Ko, R.K.L.; Bai, G.; Dong, N.; Choi, T.; Zhang, Y. Evasion Attack and Defense On Machine Learning Models in Cyber-Physical Systems: A Survey. IEEE Commun. Surv. Tutor. 2023, 1–38. [Google Scholar] [CrossRef]
- Khowaja, S.A.; Khuwaja, P.; Dev, K.; Antonopoulos, A. Spin: Simulated poisoning and inversion network for federated learning-based 6g vehicular networks. In Proceedings of the ICC 2023-IEEE International Conference on Communications, Rome, Italy, 28 May–1 June 2023; pp. 6205–6210. [Google Scholar]
- Renda, A.; Ducange, P.; Gallo, G.; Marcelloni, F. XAI models for quality of experience prediction in wireless networks. In Proceedings of the 2021 IEEE International Conference on Fuzzy Systems (FUZZ-IEEE), Luxembourg, 11–14 July 2021; pp. 1–6. [Google Scholar]



| Zero Trust Architecture Tenets from NIST [13] | |
|---|---|
| Tenet | Explanation |
| (1) “All data sources and computing services are considered resources”. | A network can comprise different classes of devices, which can have different footprints and functions. A personal device can also be seen as a resource if it can access the enterprise-owned network. |
| (2) “All communication is secured regardless of network location”. | Any equipment attempting to obtain access to a network, whether on-site or remote, must be authenticated. Network location alone does not imply trust. Confidentiality and integrity need to be protected. |
| (3) “Access to individual enterprise resources is granted on a per-session basis”. | Prior to accessing an asset, the user will be identified and verified. Only the minimum resources should be given in order to complete a task. Successful authentication and access to one resource does not grant access to other resources on the network without further permissions. |
| (4) “Access to resources is determined by dynamic policy—including the observable state of client identity, application/service, and the requesting asset—and may include other behavioral and environmental attributes”. | It is necessary for an organization to protect resources by defining what resources it has, who its members are, and what access to resources those members need. Requesting asset state can include device characteristics such as software versions installed, network location, time/date of request, previously observed behavior, and installed credentials. Resource access and action permission policies can vary based on the sensitivity of the resource/data. |
| (5) “The enterprise monitors and measures the integrity and security posture of all owned and associated assets”. | No access within the network or remote can be inherently trusted. Devices should be monitored using continuous diagnostics and mitigation (CDM), and patches/fixes should be applied when necessary. Devices that do not match this criteria can be completely rejected from making any connections with the network. |
| (6) “All resource authentication and authorization are dynamic and strictly enforced before access is allowed”. | A ZTA needs to be adaptive and continually reevaluate trust with devices and their open sessions. Identity, Credential, and Access Management (ICAM) and asset management systems are an expectation of the ZTA. Continual monitoring with possible reauthentication and reauthorization occurs throughout user transactions, as defined and enforced by policy (e.g., time-based, new resource requested, resource modification, anomalous subject activity detected) that strives to achieve a balance of security, availability, usability, and cost-efficiency. |
| (7) “The enterprise collects as much information as possible about the current state of assets, network infrastructure, and communications and uses it to improve its security posture”. | Any data on the network that can be captured should be. This allows for the improvement of the policy creation and enforcement. |
| Citation | SDN | NFV | MEC | Network Slicing | User Auth. | Encrypt. | Attack Vectors | HetNets | Vendor/Trust Models | Blockchain | ZTA |
|---|---|---|---|---|---|---|---|---|---|---|---|
| [33] | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X |
| [28] | ✓ | ✓ | ✓ | ✓ | X | X | ✓ | X | X | X | X |
| [34] | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X | X | ✓ | X |
| [12] | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X | X | ✓ | X |
| [4] | ✓ | ✓ | ✓ | ✓ | ✓ | X | ✓ | X | ✓ | X | X |
| [18] | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X |
| [15] | ✓ | ✓ | ✓ | X | ✓ | ✓ | ✓ | ✓ | X | X | X |
| [35] | ✓ | ✓ | X | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X | X |
| [36] | ✓ | X | X | ✓ | X | ✓ | ✓ | X | X | X | X |
| [37] | ✓ | X | X | X | ✓ | ✓ | ✓ | ✓ | ✓ | X | X |
| [14] | ✓ | ✓ | ✓ | X | ✓ | X | ✓ | ✓ | ✓ | X | ✓ |
| [38] | ✓ | ✓ | X | X | ✓ | ✓ | ✓ | X | ✓ | X | ✓ |
| [39] | X | X | X | X | X | X | ✓ | X | ✓ | ✓ | ✓ |
| Backhaul Network Security Considerations [37] | |
|---|---|
| Security Consideration | Explanation |
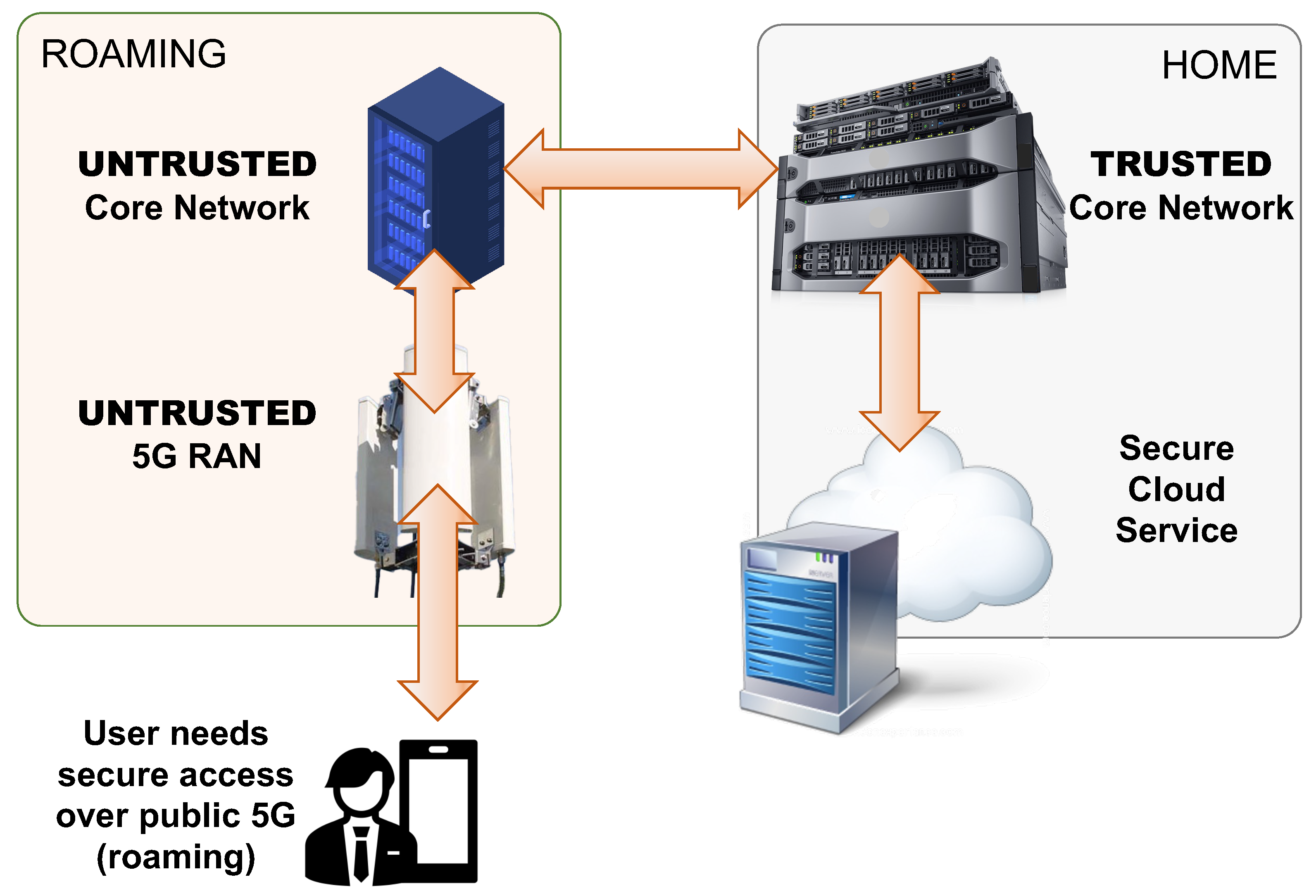
| Confidentiality and Integrity | Confidentiality and integrity are two of the most basic security considerations for any public network. Data integrity is vital to maintaining a trusted connection between two users. If the data are altered in any way or cannot be verified, trust is broken and the network can no longer be considered safe. Figure 6 is a good example of a potential decrease in confidentiality and data integrity with information being passed to an untrusted network link. |
| Mutual Authentication | One way to verify that all components within a network are legitimate is to utilize Mutual Authentication (MA). One example of MA is the 5G-AKA protocol, which authenticates the UE with the CN and vice versa in a quick and efficient manner. Node authentication is discussed in [41], which allows for the verification of different network components. This ensures all devices in the backhaul are authorized and will deny access to rogue actors. |
| Access Control | In order for a user to securely connect to a 5G network, there need to be methods in place to only allow access to legitimate users. This is standard practice for any network, but protecting against illegitimate user access is always a ‘cat and mouse game’ between researchers and hackers. |
| Availability | In any 5G network, availability is paramount, especially for the URLLC slice of 5G, guaranteeing an ultra-reliable and low-latency Quality of Service (QoS). User authentication has a direct impact on the availability of a network. If a large number of illegitimate users are able to gain access to a network, they would not only degrade network integrity but also severely deteriorate availability by consuming resources that are then no longer available to legitimate users of the network. Availability is not only dependent on the resources of the network but also how usable, effective, and efficient the network can be [42]. This can range from how the user accesses the network to provisioned authentication and connection methods and more. |
| Perfect Forward Secrecy | These methods of keeping user data private are crucial when storing information within a core network. The author suggests the use of session keys to allow for future recovery if a private key is exposed. |
| Light-Weight Cryptography Operations | Cryptography is a necessity in 5G networks to allow for more confidentiality and integrity in communications. Network availability can be affected negatively if these algorithms are not efficient and lightweight, however. The use of ASICs (Application-Specific Integrated Circuits) for these algorithms can improve the reliability and availability of the network [43]. Two principal concerns with using an ASIC are forward compatibility and equipment cost. Thus, FPGAs (Field-Programmable Gate Arrays) have emerged as a preferred intermediate solution for hardware-specific designs, since they can be reprogrammed when future standard updates are released. |
| Tamper Resistance | The inner workings of a network need to be tamper-proof and protected against leaking of sensitive information. This requires that no backdoors are incorporated into the network architecture during its design or implementation and that any devices storing secret keys are well guarded and cannot be easily accessed. |
| Defend Against Replay Attacks | The network must be able to reject forged requests to prevent illegitimate users from gaining access. Security Mode Control (SMC) and Radio Resource Control (RRC) replay attacks are common replay attacks that accomplish this. In SMC attacks, a NAS-SMC packet is replayed to impersonate a UE and reduce the security of a UE’s security context [44]. RRC replay attacks utilize a false base station, which receives UE RRC packets, informs the core network of a successful connection, and subsequently disconnects the UE, forcing it to attempt to re-acquire the RRC connection continually. If implemented successfully, this can deny the UE access to the 5G network [45]. For these attacks, the 5G Core needs to be able to identify and prevent these attacks to mitigate false users. |
| Physical Unclonable Function (PUF) | A PUF is a physical identifier hardware algorithm built inside of a semiconductor material [46]. PUFs output a non-reversible random key that can be used for cryptography algorithms, authentication, and signatures [47]. |
| Uncovered Security Challenges Presented in Our Survey | |
|---|---|
| Security Challenge | Proposed Resolution |
| 5G-AKA user privacy and traceability exposure [22] | Encrypt the initial control messages during the 5G-AKA authentication procedure. |
| Compromised USIM leading to data privacy issues [26] | Utilize a Diffie–Hellman key exchange to enable PFS. |
| Key refresh for the UE and serving network | TS 33.501 [2] states that 24 h is the maximum time a key can be valid but does allow for operators to refresh keys on a more frequent basis. |
| Exposure of an NFV hypervisor due to misconfiguration and cross contamination of shared resources [28,29] | Provided clear and succinct steps for configuration of systems and implemented a ZTA with mutual authentication and constant network monitoring. |
| Potential loss of confidentiality when connected to an untrusted core network | Careful consideration of network usage in a roaming scenario, mutual authentication and adopting ZTA. |
| Securing backhaul networks in 5G [37] | The use of mutual authentication for devices on the network, ZTA, PFS, light-weight cryptography, and physical tamper resistance. |
| Network downtime due to specific vendor software problems | Usage of an O-RAN architecture that gives operators more fine-grained control over the security and operation of their network [66]. |
| Verifying security robustness of open source software and O-RAN architecture | Usage of a closed-loop security management system outlined in [71]. |
| Network slicing attacks using adversarial machine learning with the goal of forcing the appearance of a hard-to-find vulnerability [74] | Train AI/ML models with adversarial methods in mind [79]. |
| Eavesdroppers on the physical channel in 5G communications | The usage of beamforming to create a more focused connection between the UE and gNB, achieving weak signal strength outside of the narrow beam region [91]. |
| Passive eavesdroppers on a link with RIS-aided beamforming | Utilize multiplicative random process at the RIS to mitigate the effectiveness of a passive eavesdropper [60]. |
| Illegal addition of RIS-aided beamforming equipment | Enforce strict authentication methods for RIS systems and continuously monitor the radio conditions at the edge of the deployment, possibly through the use of AI/ML. |
| Security measures for resource-constrained IoT devices | A lightweight crypto algorithm presented in [97] to securely connect 5G IoT devices over D2D. |
| Evaluation of trust in a ZTA | Trust evaluation schemes discussed in [103] to support the needs of tactical edge networks in a military setting. |
| Connection and authentication of critical infrastructure over 5G | A novel approach of connecting power grid devices over 5G in a ZTA is discussed in [107]. |
| False base stations attack in ultra-dense networks | Using blockchain technology to verify a cluster of base stations in an ultra-dense network is presented in [112], claiming it is more efficient than normal authentication methods. |
| Maintaining confidentiality in a world with quantum computers | NIST has published three drafts [126,128,130] of post-quantum cryptographic algorithms that are currently not breakable by quantum computers. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Scalise, P.; Boeding, M.; Hempel, M.; Sharif, H.; Delloiacovo, J.; Reed, J. A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas. Future Internet 2024, 16, 67. https://doi.org/10.3390/fi16030067
Scalise P, Boeding M, Hempel M, Sharif H, Delloiacovo J, Reed J. A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas. Future Internet. 2024; 16(3):67. https://doi.org/10.3390/fi16030067
Chicago/Turabian StyleScalise, Paul, Matthew Boeding, Michael Hempel, Hamid Sharif, Joseph Delloiacovo, and John Reed. 2024. "A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas" Future Internet 16, no. 3: 67. https://doi.org/10.3390/fi16030067
APA StyleScalise, P., Boeding, M., Hempel, M., Sharif, H., Delloiacovo, J., & Reed, J. (2024). A Systematic Survey on 5G and 6G Security Considerations, Challenges, Trends, and Research Areas. Future Internet, 16(3), 67. https://doi.org/10.3390/fi16030067








