A Survey on Network Optimization Techniques for Blockchain Systems
Abstract
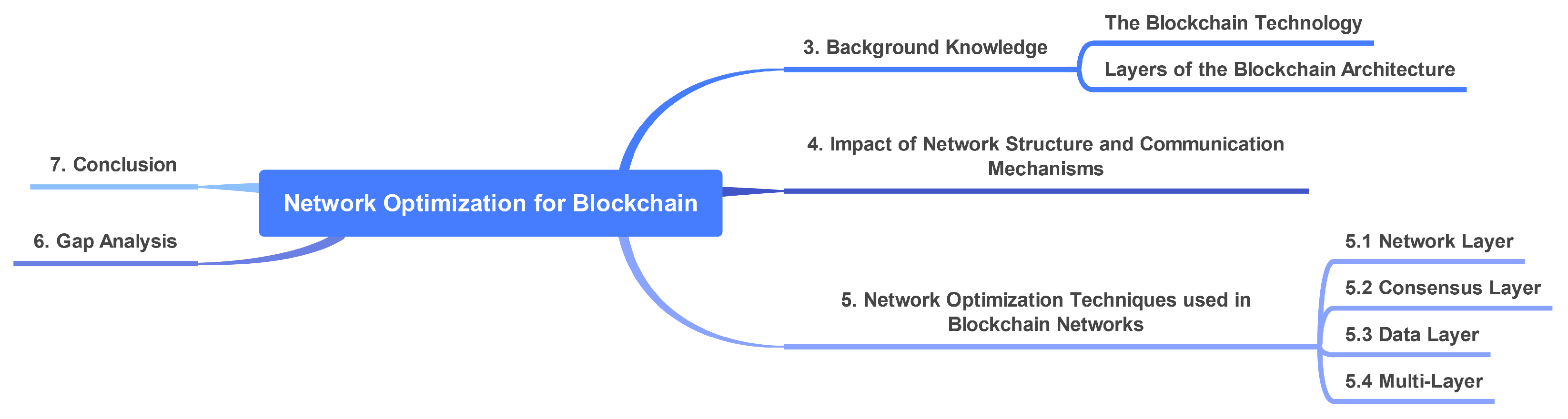
:1. Introduction
- establish the need for network-based optimizations for blockchain
- introduce background knowledge on the blockchain architecture and discuss the layers
- categorize reviewed works based on the blockchain architecture
- discuss network optimization in blockchain, analyze their effectiveness and ability to scale
- finally, we present some open issues and directions for future work
2. Survey Methodology
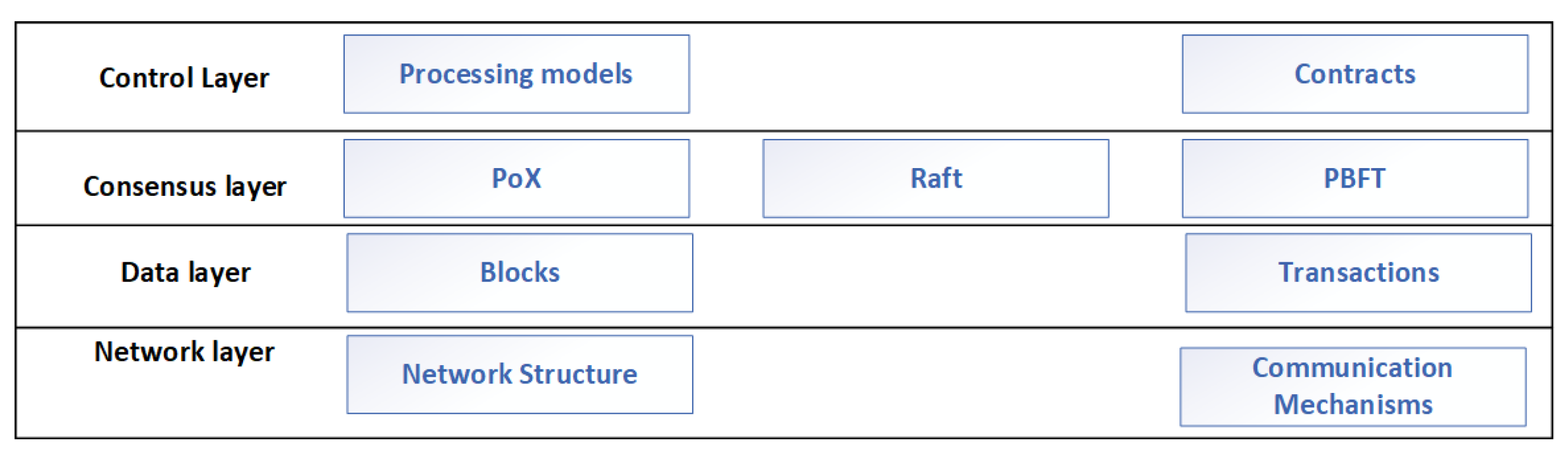
3. Background Knowledge
- Control Layer: The control layer serves as an interface between applications and the ledger. These applications include finance, data storage, voting, securing IoT, logistics and supply chain tracking [10,51]. They interact with the ledger by invoking smart contracts to trigger transactions. Smart contracts are programmable scripts that interact with the ledger by reading or writing data to the ledger when invoked. On-chain and off-chain are the primary processing models at the control layer.
- Consensus Layer: The algorithms blockchain peers use to agree on the validity of blocks and transactions exists at the consensus layer. Peers in public blockchains use Proof of X (X => Work, Stake and many more) algorithms to reach a consensus [53]. All peers in public blockchains are eligible to participate in the consensus process. However, in private blockchains, validating blocks and transactions are performed mainly by different peers with specific roles. In Hyperledger Fabric (HLF), these roles include orderers, endorsers, validators and leaders [31]. New transactions are first sent to peers who can endorse transactions by executing smart contracts. After endorsement, the transaction is sent to the leader node and maintains a connection to the ordering nodes. Next, ordering nodes add the transactions to a block and send them back to the leader node to be broadcasted in the network. Finally, every peer will have to validate the block before committing it to its local ledger.
- Data Layer: The data layer defines the structure of transactions, blocks and the cryptographic mechanisms that link them together. A number of transactions are combined together into a block. The size of a block depends on an explicitly defined size or on a time interval at which blocks must be produced [59].
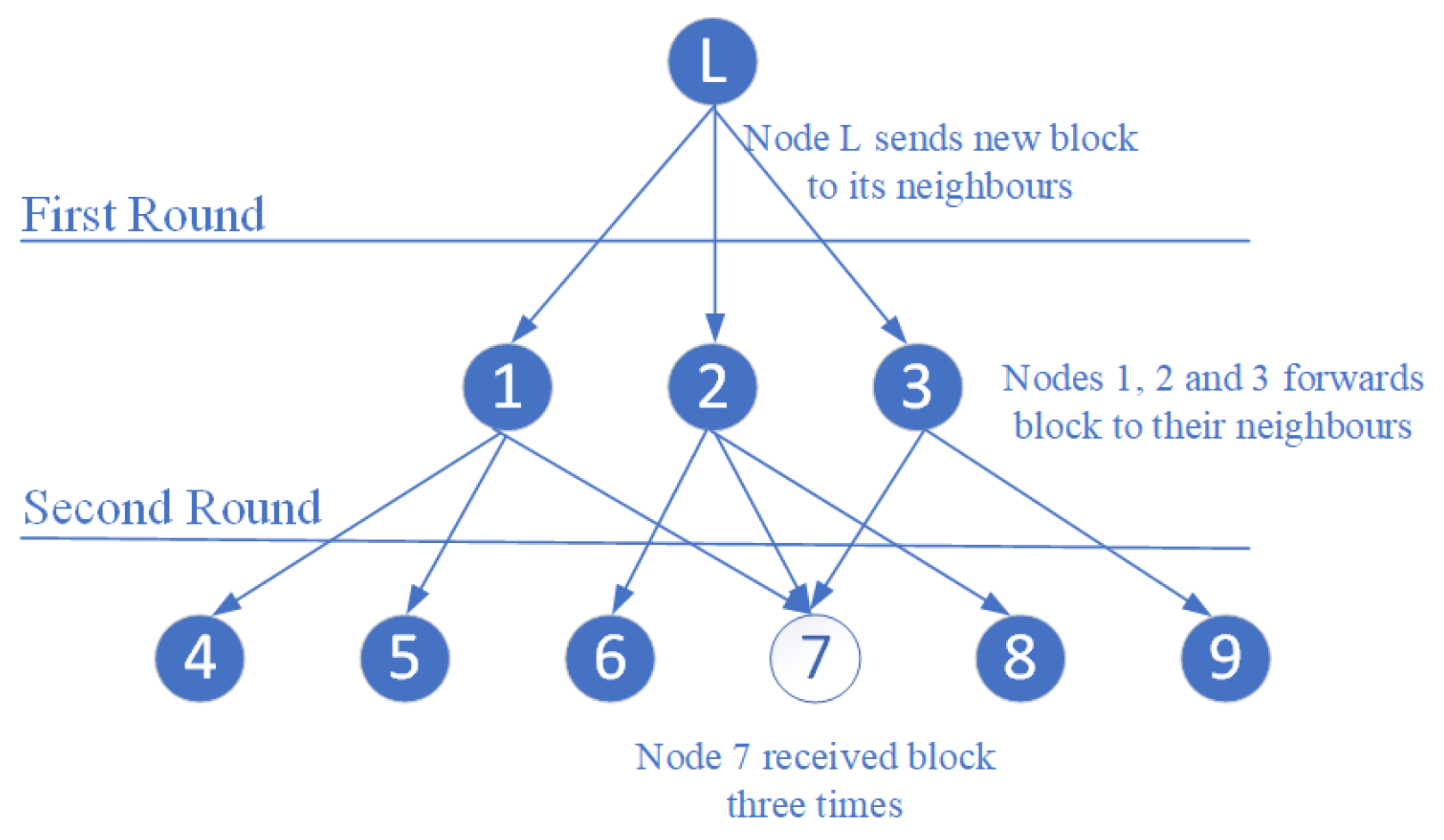
- The Network Layer: The network layer mainly consists of the network structure and the communication mechanisms. The network structure is responsible for establishing and managing the peer-to-peer network structure, while the distribution of transactions or blocks to peers in the network is handled by the communication mechanisms using gossip. Forming the P2P network requires new peers to randomly select some existing peers as their neighbors (to exchange blockchain data). Upon joining the network, a new peer connects to other peers whose addresses are hard-coded into its configurations. Then, the new peer requests the addresses of the existing peer’s neighbors and finally selects some peers randomly as neighbors to gossip with. Peers utilize the gossip protocol in the network to distribute new blocks or transactions [60]. The gossiping dissemination occurs in rounds and is prone to duplicate transmissions. As shown in Figure 4, Node L shares a newly generated block with its neighbours (Peer 1, 2 and 3). Peer 1 also shares with its neighbours (4 5 7), Peer 2 shares with (6 7 8) and Peer 3 then shares it with (7 9). After this round, it can be realized that Node 7 received the block three times.
4. The Impact of Network Structure and Communication Mechanisms on Performance
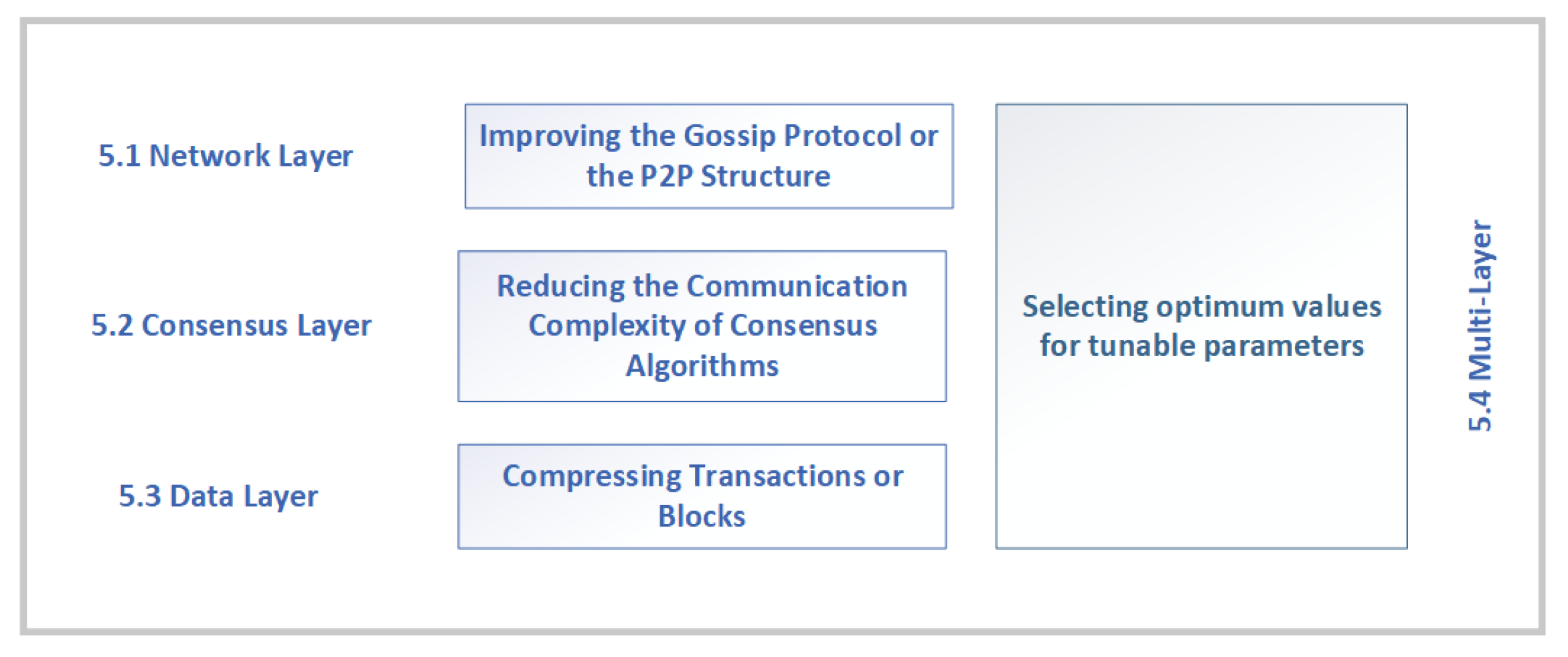
5. Network Optimization Techniques Used in Blockchain Networks
5.1. Network Layer
5.1.1. Gossip Optimization
5.1.2. P2P Topology Optimization
5.2. Consensus Layer
5.2.1. Selective Verification
5.2.2. Communication Complexity
5.2.3. Multi-Leader
5.2.4. Congestion
5.3. Data Layer
5.4. Multi-Layer
6. Gap Analysis
- Some blockchain frameworks allow network administrators to configure block size, interval and other parameters manually. Therefore, to construct an optimum blockchain network with improved transactional throughput, some researchers conducted extensive measurements to determine the impact of parameters on the blockchain’s ability to process transactions. After analyzing the experimental results, guidelines on selecting the best value for each parameter were presented. However, since these guidelines were extracted from a setup consisting of a few nodes, the approach may not suit the blockchain when it scales up with the number of peers. Therefore, researchers could investigate optimization algorithms that will take the network’s size and other relevant parameters as input and automatically determine and apply the optimum value for all the configurable blockchain parameters.
- Deep Reinforcement Learning has been applied to automatically select tunable blockchain parameters, such as consensus algorithm and block size. In principle, a DRL agent persistently interacts with its environment and takes actions that will converge to an optimal state. However, persistently interacting with the blockchain network will impede its normal operation and subsequently bottleneck its transactional throughput. Therefore, future work could research how to achieve a trade-off between maximized performance and minimized interaction.
- Solutions proposed as a better alternative to the random neighbor selection used in current blockchain implementations suggests selecting neighbors based on proximity or latency of communication. Hence, each peer selects neighbors offering the least communication latency during the neighbor selection stage. Furthermore, if many peers consider a specific peer as having low-latency communication, they will all select it. Consequently, it will lead to that peer having too many neighbors and, consequently, overloading it. Therefore, further research could examine neighbor selection strategies and limit the number of neighbors based on network size, a peer’s computing and network resources.
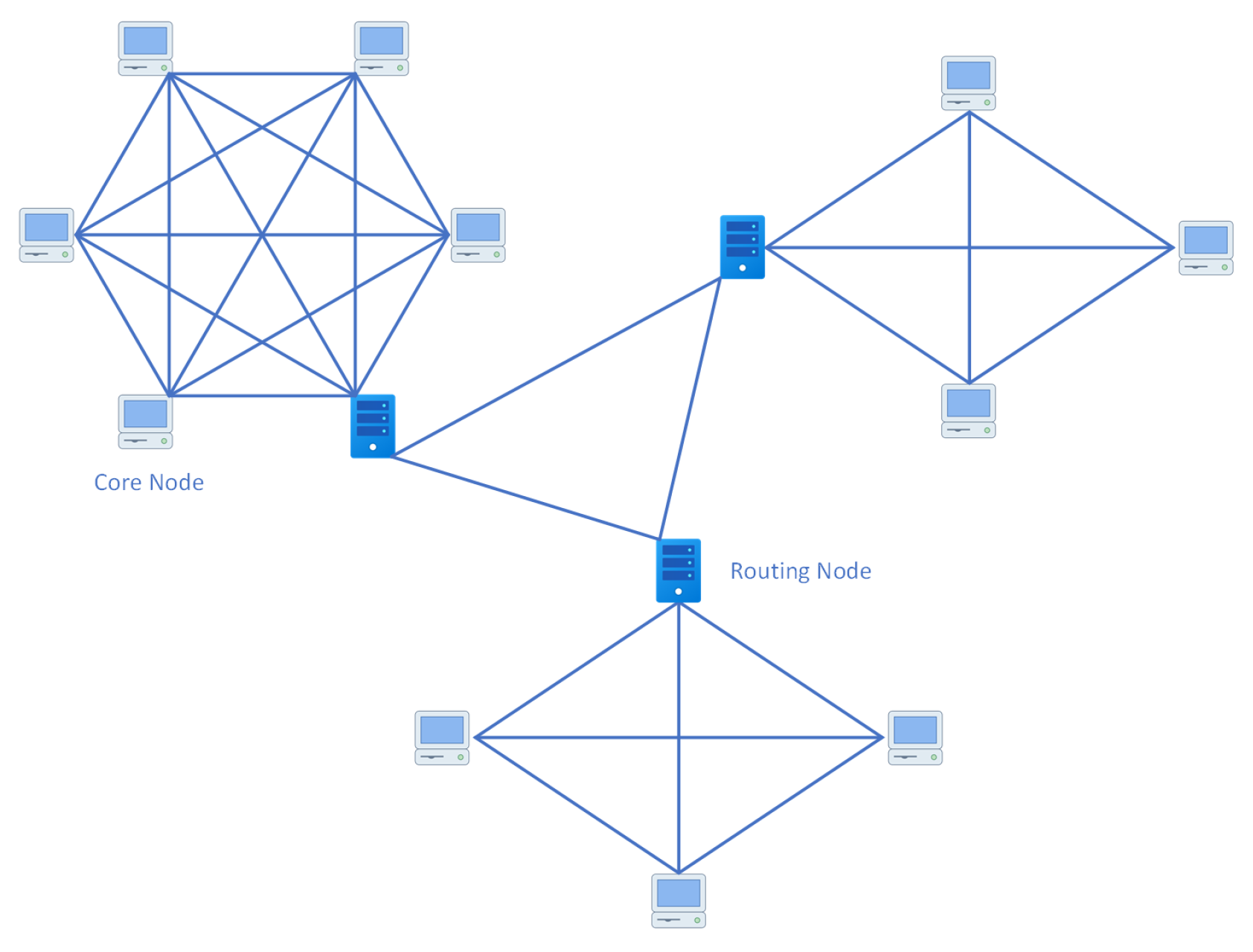
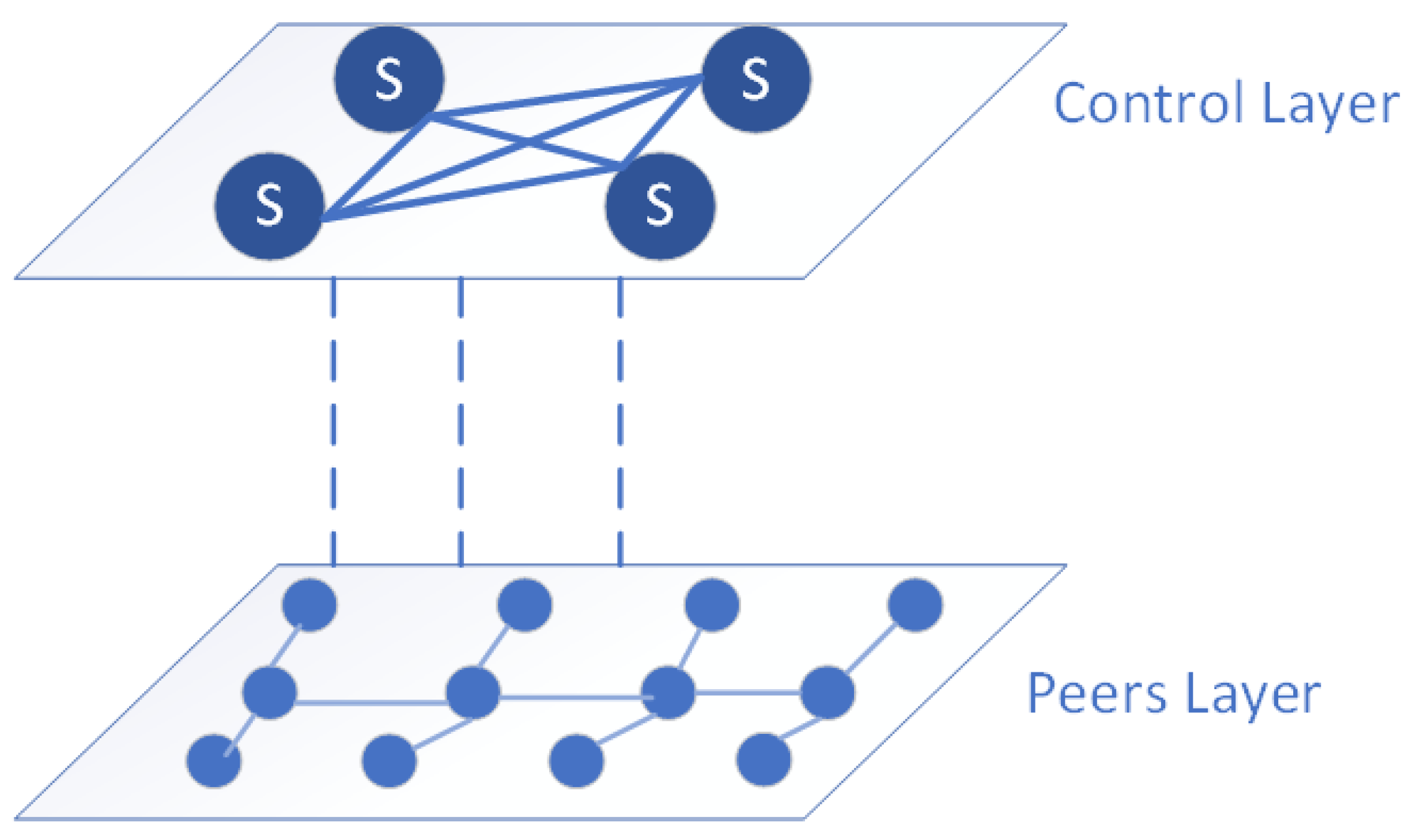
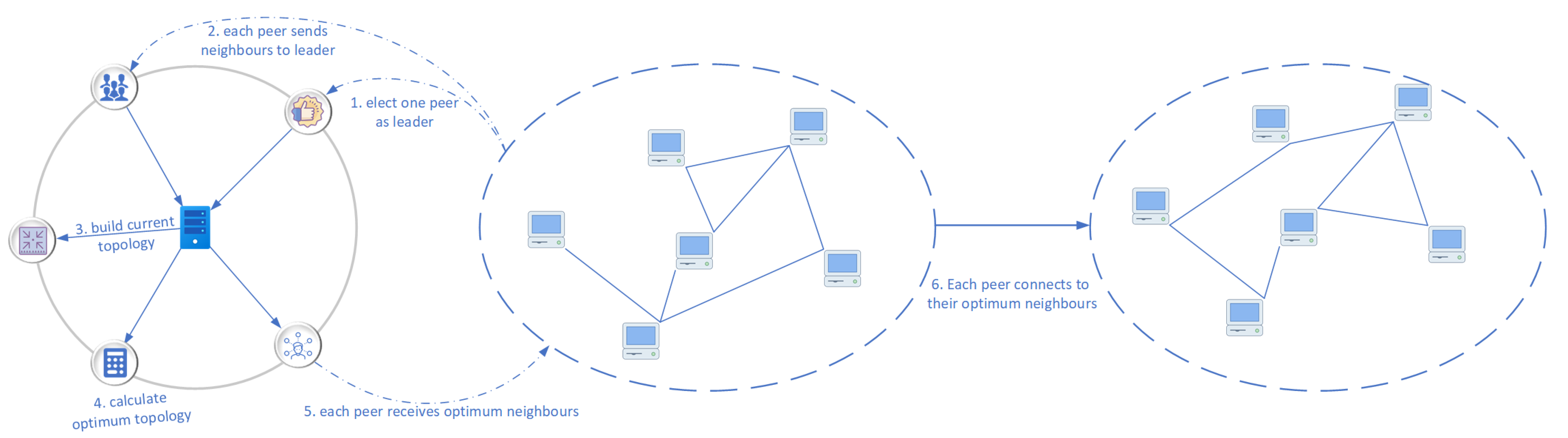
- Blockchain is a distributed technology, hence its P2P network management is also distributed, thus, all peers are responsible for setting up and managing the P2P network. However, this approach has significant network management overhead and does not easily lend itself to a dynamic reconfiguration. Therefore, to make P2P management more flexible and minimize its management overhead, researchers could consider developing intelligent semi-distributed techniques [84] to manage the P2P of blockchain networks. Thus, some peers in the blockchain are assigned special responsibilities. For example, they are tasked with calculating the optimum P2P topology and selecting suitable neighbors for every peer in the network.
- Using semi-distributed strategies for P2P network management will be computationally intensive when the blockchain peers increases. Hence when only a single peer is tasked with the P2P topology calculation, it would require more time to achieve the optimum topology. This would affect the real-time requirements of the network. Therefore, future research could investigate the optimum number of peers required for a network of a given size and share P2P topology calculation and management across the selected peers.
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| RNS | Random Neighbor Selection |
| P2P | Peer-to-Peer |
| IoT | Internet of Things |
| IIoT | Industrial IoT |
| QoS | Quality of Service |
| HLF | Hyperledger Fabric |
| SDN | Software Defined Networking |
| DHT | Distributed Hash Tables |
| INV | Inventory |
| MST | Minimum Spanning Tree |
| PBFT | Practical Byzantine Fault Tolerance |
| DRL | Deep Reinforcement Learning |
References
- Sethi, P.; Sarangi, S.R. Internet of Things: Architectures, Protocols, and Applications. J. Electr. Comput. Eng. 2017, 2017, 1–25. [Google Scholar] [CrossRef] [Green Version]
- Sethi, R.; Bhushan, B.; Sharma, N.; Kumar, R.; Kaushik, I. Applicability of Industrial IoT in Diversified Sectors: Evolution, Applications and Challenges; Springer: Singapore, 2021; pp. 45–67. [Google Scholar] [CrossRef]
- Huo, R.; Zeng, S.; Wang, Z.; Shang, J.; Chen, W.; Huang, T.; Wang, S.; Yu, F.R.; Liu, Y. A Comprehensive Survey on Blockchain in Industrial Internet of Things: Motivations, Research Progresses, and Future Challenges. IEEE Commun. Surv. Tutor. 2022, 1, 88–122. [Google Scholar] [CrossRef]
- Sirojan, T.; Phung, T.; Ambikairajah, E. Enabling Deep Learning on Embedded Systems for IoT Sensor Data Analytics: Opportunities and Challenges. In Proceedings of the 2018 IEEE International Conference on Information and Automation for Sustainability (ICIAfS), Colombo, Sri Lanka, 21–22 December 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Research, P. MCU Market, Microcontroller Market Size, Share, Growth, Forecast 2030. 2022. Available online: https://www.precedenceresearch.com/microcontroller-mcu-market (accessed on 31 May 2022).
- Singh, D.; Sandhu, A.; Thakur, A.; Priyank, N. An Overview of IoT Hardware Development Platforms. Int. J. Emerg. Technol. 2020, 11, 155–163. [Google Scholar]
- Tewari, N.; Deepak, N.; Joshi, M.; Bhatt, J.S. Comparative Study of IoT Development Boards in 2021: Choosing right Hardware for IoT Projects. In Proceedings of the 2021 2nd International Conference on Intelligent Engineering and Management (ICIEM), London, UK, 28–30 April 2021; pp. 357–361. [Google Scholar] [CrossRef]
- Bouachir, O.; Aloqaily, M.; Tseng, L.; Boukerche, A. Blockchain and Fog Computining for Cyberphysical Systems: The Case of Smart Industry. Computer 2020, 53, 36–45. [Google Scholar] [CrossRef]
- Uddin, M.; Stranieri, A.; Gondal, I.; Balasubramanian, V. A Survey on the Adoption of Blockchain in IoT: Challenges and Solutions. Blockchain Res. Appl. 2021, 2, 100006. [Google Scholar] [CrossRef]
- Makridakis, S.; Christodoulou, K. Blockchain: Current Challenges and Future Prospects/Applications. Future Internet 2019, 11, 258. [Google Scholar] [CrossRef] [Green Version]
- Fan, C.; Ghaemi, S.; Khazaei, H.; Musilek, P. Performance Evaluation of Blockchain Systems: A Systematic Survey. IEEE Access 2020, 8, 126927–126950. [Google Scholar] [CrossRef]
- Sagirlar, G.; Carminati, B.; Ferrari, E.; Sheehan, J.D.; Ragnoli, E. Hybrid-IoT: Hybrid Blockchain Architecture for Internet of Things-PoW Sub-Blockchains. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 1007–1016. [Google Scholar] [CrossRef] [Green Version]
- Bach, L.M.; Mihaljevic, B.; Zagar, M. Comparative analysis of blockchain consensus algorithms. In Proceedings of the 2018 41st International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO), Opatija, Croatia, 21–25 May 2018; pp. 1545–1550. [Google Scholar] [CrossRef]
- Li, M.; Qin, Y.; Liu, B.; Chu, X. Enhancing the efficiency and scalability of blockchain through probabilistic verification and clustering. Inf. Process. Manag. 2021, 58, 102650. [Google Scholar] [CrossRef]
- Wang, W.; Hoang, D.T.; Hu, P.; Xiong, Z.; Niyato, D.; Wang, P.; Wen, Y.; Kim, D.I. A Survey on Consensus Mechanisms and Mining Strategy Management in Blockchain Networks. IEEE Access 2019, 7, 22328–22370. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In Proceedings of the 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar] [CrossRef]
- Nguyen, G.T.; Kim, K. A survey about consensus algorithms used in Blockchain. J. Inf. Process. Syst. 2018, 14, 101–128. [Google Scholar] [CrossRef]
- Nartey, C.; Tchao, E.T.; Gadze, J.D.; Yeboah-Akowuah, B.; Nunoo-Mensah, H.; Welte, D.; Sikora, A. Blockchain-IoT peer device storage optimization using an advanced time-variant multi-objective particle swarm optimization algorithm. EURASIP J. Wirel. Commun. Netw. 2022, 2022, 1–27. [Google Scholar] [CrossRef]
- Ding, N.; Zhao, Y. Lightweight Blockchain Based on Storage Resource Optimization for Internet of Vehicles. In Proceedings of the 2021 IEEE International Intelligent Transportation Systems Conference (ITSC), Indianapolis, IN, USA, 19–22 September 2021; pp. 1063–1068. [Google Scholar] [CrossRef]
- Zuo, Y.; Jin, S.; Zhang, S.; Zhang, Y. Blockchain Storage and Computation Offloading for Cooperative Mobile-Edge Computing. IEEE Internet Things J. 2021, 8, 9084–9098. [Google Scholar] [CrossRef]
- Zhou, Q.; Huang, H.; Zheng, Z.; Bian, J. Solutions to Scalability of Blockchain: A Survey. IEEE Access 2020, 8, 16440–16455. [Google Scholar] [CrossRef]
- Yu, B.; Li, X.; Zhao, H. Virtual block group: A scalable blockchain model with partial node storage and distributed hash table. Comput. J. 2021, 63, 1524–1536. [Google Scholar] [CrossRef]
- Qi, X.; Zhang, Z.; Jin, C.; Zhou, A. A reliable storage partition for permissioned blockchain. IEEE Trans. Knowl. Data Eng. 2021, 33, 14–27. [Google Scholar] [CrossRef]
- Xu, M.; Feng, G.; Ren, Y.; Zhang, X. On Cloud Storage Optimization of Blockchain with a Clustering-Based Genetic Algorithm. IEEE Internet Things J. 2020, 7, 8547–8558. [Google Scholar] [CrossRef]
- Mazlan, A.A.; Daud, S.M.; Sam, S.M.; Abas, H.; Rasid, S.Z.A.; Yusof, M.F. Scalability Challenges in Healthcare Blockchain System-A Systematic Review. IEEE Access 2020, 8, 23663–23673. [Google Scholar] [CrossRef]
- Mei, H.; Gao, Z.; Guo, Z.; Zhao, M.; Yang, J. Storage mechanism optimization in blockchain system based on residual number system. IEEE Access 2019, 7, 114539–114546. [Google Scholar] [CrossRef]
- Zeng, Q.; Xie, K.; Li, Y.; Guan, X.; Zhou, C.; Ma, S. Storage Optimization Algorithm for Publication Blockchain. Adv. Intell. Syst. Comput. 2018, 905, 828–835. [Google Scholar] [CrossRef]
- Li, C.; Zhang, J.; Yang, X.; Youlong, L. Lightweight blockchain consensus mechanism and storage optimization for resource-constrained IoT devices. Inf. Process. Manag. 2021, 58, 102602. [Google Scholar] [CrossRef]
- Misic, J.; Misic, V.B.; Chang, X.; Motlagh, S.G.; Ali, M.Z. Block Delivery Time in Bitcoin Distribution Network. In Proceedings of the ICC 2019-2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019. [Google Scholar] [CrossRef]
- Imtiaz, M.A.; Starobinski, D.; Trachtenberg, A.; Younis, N. Churn in the Bitcoin Network. IEEE Trans. Netw. Serv. Manag. 2021, 18, 1598–1615. [Google Scholar] [CrossRef]
- Berendea, N.; Mercier, H.; Onica, E.; Riviere, E. Fair and Efficient Gossip in Hyperledger Fabric. In Proceedings of the 2020 IEEE 40th International Conference on Distributed Computing Systems (ICDCS), Singapore, 29 November–1 December 2020; pp. 190–200. [Google Scholar] [CrossRef]
- Zhang, L.; Xu, H.; Onireti, O.; Imran, M.A.; Cao, B. How Much Communication Resource is Needed to Run a Wireless Blockchain Network? IEEE Netw. 2022, 1, 128–135. [Google Scholar] [CrossRef]
- Municio, E.; Latre, S.; Marquez-Barja, J.M. Extending Network Programmability to the Things Overlay Using Distributed Industrial IoT Protocols. IEEE Trans. Ind. Inform. 2021, 17, 251–259. [Google Scholar] [CrossRef]
- Khan, W.Z.; Rehman, M.H.; Zangoti, H.M.; Afzal, M.K.; Armi, N.; Salah, K. Industrial internet of things: Recent advances, enabling technologies and open challenges. Comput. Electr. Eng. 2020, 81, 106522. [Google Scholar] [CrossRef]
- Smetanin, S.; Ometov, A.; Komarov, M.; Masek, P.; Koucheryavy, Y. Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective. Sensors 2020, 20, 3358. [Google Scholar] [CrossRef]
- Srinidhi, N.N.; Dilip Kumar, S.M.; Venugopal, K.R. Network optimizations in the Internet of Things: A review. Eng. Sci. Technol. Int. J. 2019, 22, 1–21. [Google Scholar] [CrossRef]
- Agnihotri, S.; Ramkumar, K.R. A survey and comparative analysis of the various routing protocols of Internet of Things. Int. J. Pervasive Comput. Commun. 2017, 13, 264–281. [Google Scholar] [CrossRef]
- Tang, F.; Mao, B.; Kawamoto, Y.; Kato, N. Survey on Machine Learning for Intelligent End-to-End Communication Toward 6G: From Network Access, Routing to Traffic Control and Streaming Adaption. IEEE Commun. Surv. Tutor. 2021, 23, 1578–1598. [Google Scholar] [CrossRef]
- Mammeri, Z. Reinforcement learning based routing in networks: Review and classification of approaches. IEEE Access 2019, 7, 55916–55950. [Google Scholar] [CrossRef]
- Mayasari, R.; Syambas, N.R. Machine learning on named data network: A survey routing and forwarding strategy. In Proceedings of the 2020 14th International Conference on Telecommunication Systems, Services, and Applications (TSSA), Bandung, Indonesia, 4–5 November 2020. [Google Scholar] [CrossRef]
- Kumari, P.; Sahana, S.K. QoS-Based ACO Routing Protocols in MANETs: A Review. In Proceedings of the Fourth International Conference on Microelectronics, Computing and Communication Systems, Ranchi, India, 11–12 May 2019; pp. 329–340. [Google Scholar] [CrossRef]
- Kumari, P.; Sahana, S.K. An Efficient Swarm-Based Multicast Routing Technique—Review. Adv. Intell. Syst. Comput. 2019, 711, 123–134. [Google Scholar] [CrossRef]
- Manikannu, J.; Nagarajan, V. A survey of energy efficient routing and optimization techniques in wireless sensor networks. In Proceedings of the 2017 International Conference on Communication and Signal Processing (ICCSP), Chennai, India, 6–8 April 2017; pp. 2075–2080. [Google Scholar] [CrossRef]
- Islam, S.; Muslim, N.; Atwood, J.W. A Survey on Multicasting in Software-Defined Networking. IEEE Commun. Surv. Tutor. 2018, 20, 355–387. [Google Scholar] [CrossRef]
- Cao, B.; Zhang, Z.; Feng, D.; Zhang, S.; Zhang, L.; Peng, M.; Li, Y. Performance analysis and comparison of PoW, PoS and DAG based blockchains. Digit. Commun. Netw. 2020, 6, 480–485. [Google Scholar] [CrossRef]
- Monrat, A.A.; Schelen, O.; Andersson, K. Performance Evaluation of Permissioned Blockchain Platforms. In Proceedings of the 2020 IEEE Asia-Pacific Conference on Computer Science and Data Engineering (CSDE), Gold Coast, Australia, 16–18 December 2020. [Google Scholar] [CrossRef]
- Perez, D.; Xu, J.; Livshits, B. Revisiting Transactional Statistics of High-scalability Blockchains. In Proceedings of the ACM Internet Measurement Conference, Virtual, 27–29 October 2020; Volume 15. [Google Scholar] [CrossRef]
- Wu, Y.; Song, L.; Liu, L.; Li, J.; Li, X.; Zhou, L. Consensus Mechanism of IoT Based on Blockchain Technology. Shock Vib. 2020, 2020, 8846429. [Google Scholar] [CrossRef]
- Fazlali, M.; Eftekhar, S.M.; Dehshibi, M.M.; Malazi, H.T.; Nosrati, M. Raft Consensus Algorithm: An Effective Substitute for Paxos in High Throughput P2P-based Systems. arXiv 2019, arXiv:1911.01231. [Google Scholar]
- Shrimali, B.; Patel, H.B. Blockchain state-of-the-art: Architecture, use cases, consensus, challenges and opportunities. J. King Saud Univ.-Comput. Inf. Sci. 2021; in press. [Google Scholar] [CrossRef]
- Ali Syed, T.; Alzahrani, A.; Jan, S.; Siddiqui, M.S.; Nadeem, A.; Alghamdi, T. A Comparative Analysis of Blockchain Architecture and its Applications: Problems and Recommendations. IEEE Access 2019, 7, 176838–176869. [Google Scholar] [CrossRef]
- Nguyen, T.G.; Phan, T.V.; Hoang, D.T.; Nguyen, T.N.; So-In, C. Federated Deep Reinforcement Learning for Traffic Monitoring in SDN-Based IoT Networks. IEEE Trans. Cogn. Commun. Netw. 2021, 7731, 1–17. [Google Scholar] [CrossRef]
- Monrat, A.A.; Schelén, O.; Andersson, K. A survey of blockchain from the perspectives of applications, challenges, and opportunities. IEEE Access 2019, 7, 117134–117151. [Google Scholar] [CrossRef]
- Sanka, A.I.; Cheung, R.C. A systematic review of blockchain scalability: Issues, solutions, analysis and future research. J. Netw. Comput. Appl. 2021, 195, 103232. [Google Scholar] [CrossRef]
- Alrehaili, A.; Namoun, A. A Comparative Analysis of Scalability Issues within Blockchain-based Solutions in the Internet of Things. Environments 2021, 12, 480–490. [Google Scholar] [CrossRef]
- Xie, J.; Yu, F.R.; Huang, T.; Xie, R.; Liu, J.; Liu, Y. A Survey on the Scalability of Blockchain Systems. IEEE Netw. 2019, 33, 166–173. [Google Scholar] [CrossRef]
- Leible, S.; Schlager, S.; Schubotz, M.; Gipp, B. A Review on Blockchain Technology and Blockchain Projects Fostering Open Science. Front. Blockchain 2019, 2, 16. [Google Scholar] [CrossRef]
- Litke, A.; Anagnostopoulos, D.; Varvarigou, T. Blockchains for Supply Chain Management: Architectural Elements and Challenges Towards a Global Scale Deployment. Logistics 2019, 3, 5. [Google Scholar] [CrossRef] [Green Version]
- Xu, X.; Sun, G.; Luo, L.; Cao, H.; Yu, H.; Vasilakos, A.V. Latency performance modeling and analysis for hyperledger fabric blockchain network. Inf. Process. Manag. 2021, 58, 102436. [Google Scholar] [CrossRef]
- Loizou, N.; Richtarik, P. Revisiting Randomized Gossip Algorithms: General Framework, Convergence Rates and Novel Block and Accelerated Protocols. IEEE Trans. Inf. Theory 2021, 67, 8300–8324. [Google Scholar] [CrossRef]
- Kiffer, L.; Salman, A.; Levin, D.; Mislove, A.; Nita-Rotaru, C. Under the Hood of the Ethereum Gossip Protocol. In International Conference on Financial Cryptography and Data Security; Springer: Berlin/Heidelberg, Germany, 2021; pp. 437–456. ISBN 9783662643303. [Google Scholar] [CrossRef]
- Guggenberger, T.; Sedlmeir, J.; Fridgen, G.; Luckow, A. An In-Depth Investigation of Performance Characteristics of Hyperledger Fabric. arXiv 2021, arXiv:2102.07731. [Google Scholar]
- Nguyen, T.S.L.; Jourjon, G.; Potop-Butucaru, M.; Thai, K.L. Impact of network delays on Hyperledger Fabric. In Proceedings of the IEEE INFOCOM 2019-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Paris, France, 29 April–2 May 2019; pp. 222–227. [Google Scholar] [CrossRef] [Green Version]
- Zhang, Y.H.; Liu, X.F. Traffic Redundancy in Blockchain Systems: The Impact of Logical and Physical Network Structures. In Proceedings of the 2021 IEEE International Symposium on Circuits and Systems (ISCAS), Daegu, Korea, 22–28 May 2021; pp. 1–5. [Google Scholar] [CrossRef]
- Elagin, V.; Spirkina, A.; Levakov, A.; Belozertsev, I. Blockchain Behavioral Traffic Model as a Tool to Influence Service IT Security. Future Internet 2020, 12, 68. [Google Scholar] [CrossRef]
- Rohrer, E.; Tschorsch, F. Blockchain layer zero: Characterizing the bitcoin network through measurements, models, and simulations. In Proceedings of the 2021 IEEE 46th Conference on Local Computer Networks (LCN), Edmonton, AB, Canada, 4–7 October 2021; pp. 9–16. [Google Scholar] [CrossRef]
- Zhang, Y.; Tan, R.; Kong, X.; Tan, Q.; Liu, X. Bitcoin Node Discovery: Large-Scale Empirical Evaluation of Network Churn. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Sun, X., Pan, Z., Bertino, E., Eds.; Springer International Publishing: Cham, Switzerland, 2019; pp. 385–395. [Google Scholar] [CrossRef]
- Kim, A.; Kim, J.; Essaid, M.; Park, S.; Ju, H. Analysis of Compact Block Propagation Delay in Bitcoin Network. In Proceedings of the 2021 22nd Asia-Pacific Network Operations and Management Symposium (APNOMS), Tainan, Taiwan, 8–10 September 2021; pp. 313–318. [Google Scholar] [CrossRef]
- Aoki, Y.; Shudo, K. Proximity Neighbor Selection in Blockchain Networks. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019; pp. 52–58. [Google Scholar] [CrossRef] [Green Version]
- He, X.; Cui, Y.; Jiang, Y. An Improved Gossip Algorithm Based on Semi-Distributed Blockchain Network. In Proceedings of the 2019 International Conference on Cyber-Enabled Distributed Computing and Knowledge Discovery (CyberC), Guilin, China, 17–19 October 2019; pp. 24–27. [Google Scholar] [CrossRef]
- Yu, B.; Li, X.; Zhao, H.; Zhou, T. A scalable blockchain network model with transmission paths and neighbor node subareas. Computing 2021, 1, 1–25. [Google Scholar] [CrossRef]
- Shaleva, A.; Korkhov, V. Evaluation of the Neo P2P Blockchain Network Protocol Efficiency. In Proceedings of the International Conference on Computational Science and Its Applications, Cagliari, Italy, 13–16 September 2021; Springer: Cham, Switzerland, 2021; pp. 56–71, ISBN 9783030869724. [Google Scholar] [CrossRef]
- Shaleva, A.; Korkhov, V. Efficient gossip-based protocol in the neo blockchain network. In Proceedings of the 9th International Conference “Distributed Computing and Grid Technologies in Science and Education”, Dubna, Russia, 5–9 July 2021; Volume 3041, pp. 508–513. [Google Scholar] [CrossRef]
- Danzi, P.; Kalor, A.E.; Stefanovic, C.; Popovski, P. Analysis of the Communication Traffic for Blockchain Synchronization of IoT Devices. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–7. [Google Scholar] [CrossRef] [Green Version]
- Vu, H.; Tewari, H. An Efficient Peer-to-Peer Bitcoin Protocol with Probabilistic Flooding. In Proceedings of the International Conference for Emerging Technologies in Computing, London, UK, 19–20 August 2019; Springer: Cham, Switzerland, 2019; Volume 285, pp. 29–45, ISBN 9783030239428. [Google Scholar] [CrossRef]
- Santiago, C.; Lee, C. Accelerating Message Propagation in Blockchain Networks. In Proceedings of the 2020 International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 21–23 October 2020; pp. 157–160. [Google Scholar] [CrossRef]
- Kan, J.; Zou, L.; Liu, B.; Huang, X. Boost Blockchain Broadcast Propagation with Tree Routing. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Cham, Switzerland, 2018; pp. 77–85. [Google Scholar] [CrossRef] [Green Version]
- Kaneko, Y.; Asaka, T. DHT clustering for load balancing considering blockchain data size. In Proceedings of the 2018 Sixth International Symposium on Computing and Networking Workshops (CANDARW), Takayama, Japan, 27–30 November 2018; pp. 71–74. [Google Scholar] [CrossRef]
- Yang, X.; Shi, L. Ari: A P2P optimization for blockchain systems. In Proceedings of the 2019 17th International Conference on Privacy, Security and Trust (PST), Fredericton, NB, Canada, 26–28 August 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Hao, W.; Zeng, J.; Dai, X.; Xiao, J.; Hua, Q.; Chen, H.; Li, K.C.; Jin, H. BlockP2P: Enabling Fast Blockchain Broadcast with Scalable Peer-to-Peer Network Topology. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Cham, Switzerland, 2019; pp. 223–237. [Google Scholar] [CrossRef]
- Al-Musharaf, A.J.; Al-Alak, S.M.; Al-Mashhadi, H.M. Improving Blockchain Consensus Mechanism via Network Clusters. In Proceedings of the 2021 1st Babylon International Conference on Information Technology and Science (BICITS), Babil, Iraq, 28–29 April 2021; pp. 293–298. [Google Scholar] [CrossRef]
- Huang, J.; Tan, L.; Mao, S.; Yu, K. Blockchain Network Propagation Mechanism Based on P4P Architecture. Secur. Commun. Netw. 2021, 2021, 1–12. [Google Scholar] [CrossRef]
- Deshpande, V.; Badis, H.; George, L. Efficient topology control of blockchain peer to peer network based on SDN paradigm. Peer-to-Peer Netw. Appl. 2021, 15, 267–289. [Google Scholar] [CrossRef]
- Baniata, H.; Anaqreh, A.; Kertesz, A. DONS: Dynamic Optimized Neighbor Selection for smart blockchain networks. Future Gener. Comput. Syst. 2022, 130, 75–90. [Google Scholar] [CrossRef]
- Chen, J.; Qin, Y. Reducing Block Propagation Delay in Blockchain Networks via Guarantee Verification. In Proceedings of the 2021 IEEE 29th International Conference on Network Protocols (ICNP), Dallas, TX, USA, 1–5 November 2021. [Google Scholar] [CrossRef]
- Zhang, M.; Cheng, Y.; Deng, X.; Wang, B.; Xie, J.; Yang, Y.; Zhang, J. Accelerating Transactions Relay in Blockchain Networks via Reputation. In Proceedings of the 2021 IEEE/ACM 29th International Symposium on Quality of Service (IWQOS), Tokyo, Japan, 25–28 June 2021. [Google Scholar] [CrossRef]
- Locher, T. Fast Byzantine Agreement for Permissioned Distributed Ledgers. In Proceedings of the 32nd ACM Symposium on Parallelism in Algorithms and Architectures, Virtual, 15–17 July 2020; pp. 371–382. [Google Scholar] [CrossRef]
- Jiang, Y.; Lian, Z. High performance and scalable byzantine fault tolerance. In Proceedings of the 2019 IEEE 3rd Information Technology, Networking, Electronic and Automation Control Conference (ITNEC), Chengdu, China, 15–17 March 2019; pp. 1195–1202. [Google Scholar] [CrossRef]
- Cao, N.; Jiang, D.; Liu, Y.; Zhou, Y.; Du, H.; Qiao, X.; Xia, Y.; Zhu, D.; Yu, F.; Bi, W. Revisit Raft Consistency Protocol on Private Blockchain System in High Network Latency. In Proceedings of the International Conference on Artificial Intelligence and Security, Dublin, Ireland, 19–23 July 2021; Springer: Cham, Switzerland, 2021; Volume 1423, pp. 571–579, ISBN 9783030786175. [Google Scholar] [CrossRef]
- Jalalzai, M.M.; Busch, C.; Richard, G.G. Consistent BFT Performance for Blockchains. In Proceedings of the 2019 49th Annual IEEE/IFIP International Conference on Dependable Systems and Networks–Supplemental Volume (DSN-S), Portland, OR, USA, 24–27 June 2019; pp. 17–18. [Google Scholar] [CrossRef]
- Casado-Vara, R.; Chamoso, P.; De la Prieta, F.; Prieto, J.; Corchado, J.M. Non-linear adaptive closed-loop control system for improved efficiency in IoT-blockchain management. Inf. Fusion 2019, 49, 227–239. [Google Scholar] [CrossRef]
- Castro, M.; Liskov, B. Practical byzantine fault tolerance and proactive recovery. ACM Trans. Comput. Syst. 2002, 20, 398–461. [Google Scholar] [CrossRef]
- Jalalzai, M.M.; Busch, C. Window Based BFT Blockchain Consensus. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 971–979. [Google Scholar] [CrossRef] [Green Version]
- Lei, K.; Zhang, Q.; Xu, L.; Qi, Z. Reputation-Based Byzantine Fault-Tolerance for Consortium Blockchain. In Proceedings of the 2018 IEEE 24th International Conference on Parallel and Distributed Systems (ICPADS), Singapore, 11–13 December 2018; pp. 604–611. [Google Scholar] [CrossRef]
- Ahn, S.; Kim, T.; Kwon, Y.; Cho, S. Packet aggregation scheme to mitigate the network congestion in blockchain networks. In Proceedings of the 2020 International Conference on Electronics, Information, and Communication (ICEIC), Barcelona, Spain, 19–22 January 2020. [Google Scholar] [CrossRef]
- Jin, M.; Chen, X.; Lin, S.J. Reducing the Bandwidth of Block Propagation in Bitcoin Network With Erasure Coding. IEEE Access 2019, 7, 175606–175613. [Google Scholar] [CrossRef]
- Zhang, L.; Wang, T.; Liew, S.C. Speeding up block propagation in Bitcoin network: Uncoded and coded designs. Comput. Netw. 2022, 206, 108791. [Google Scholar] [CrossRef]
- Cebe, M.; Kaplan, B.; Akkaya, K. A network coding based information spreading approach for permissioned blockchain in IoT settings. In Proceedings of the ACM International Conference Proceeding Series, New York, NY, USA, 5–7 November 2018; pp. 470–475. [Google Scholar] [CrossRef]
- Zhao, C.; Wang, T.; Zhang, S. LightBlock: Reducing Bandwidth Required to Synchronize Blocks in Ethereum Network. In Proceedings of the 2021 International Conference on Communications, Information System and Computer Engineering (CISCE), Beijing, China, 14–16 May 2021; pp. 868–874. [Google Scholar] [CrossRef]
- Hang, L.; Kim, D.H. Optimal blockchain network construction methodology based on analysis of configurable components for enhancing Hyperledger Fabric performance. Blockchain Res. Appl. 2021, 2, 100009. [Google Scholar] [CrossRef]
- Liu, M.; Yu, F.R.; Teng, Y.; Leung, V.C.; Song, M. Performance optimization for blockchain-enabled industrial internet of things (iiot) systems: A deep reinforcement learning approach. IEEE Trans. Ind. Inform. 2019, 15, 3559–3570. [Google Scholar] [CrossRef]
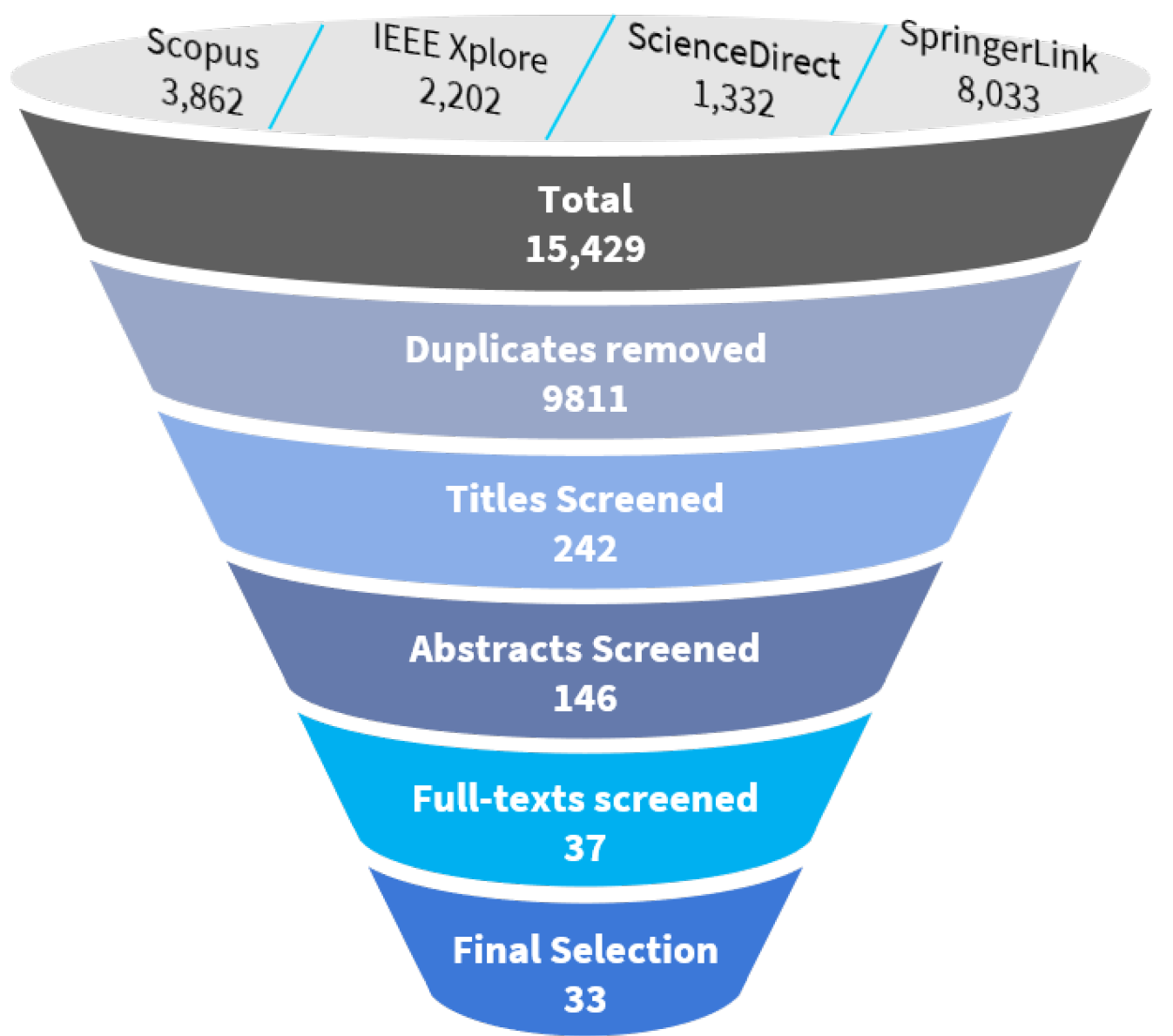
| Query | Keywords | Scopus | IEEE Xplore | Science Direct | Springer Link | Total |
|---|---|---|---|---|---|---|
| Query 1 | “blockchain” AND (iot OR iiot) AND integration | 556 | 262 | 3017 | 5519 | 9354 |
| Query 2 | “blockchain” AND “scalability” | 1913 | 1075 | 6280 | 5224 | 14,492 |
| Query 3 | “blockchain” AND (iot OR iiot) AND (optimization OR optimize) | 363 | 224 | 2746 | 5134 | 8467 |
| Query 4 | “blockchain” AND “gossip” | 50 | 26 | 134 | 478 | 688 |
| Query 5 | “blockchain” AND (peer-to-peer OR p2p OR network OR gossip ) AND (optimization OR optimize) | 992 | 650 | 4583 | 8598 | 14,823 |
| Total | 3874 | 2237 | 16,760 | 24,953 | 47,825 |
| Query | Keywords | Scopus | IEEE Xplore | Science Direct | Springer Link | Total |
|---|---|---|---|---|---|---|
| Query 1 | “blockchain” AND (iot OR iiot) AND integration | 556 | 262 | 300 | 1866 | 2984 |
| Query 2 | “blockchain” AND “scalability” | 1913 | 1049 | 298 | 1986 | 5246 |
| Query 3 | “blockchain” AND (iot OR iiot ) AND (optimization OR optimize) | 363 | 224 | 300 | 1992 | 2879 |
| Query 4 | “blockchain” AND “gossip” | 49 | 26 | 134 | 195 | 404 |
| Query 5 | “blockchain” AND (peer-to-peer OR p2p OR network OR gossip ) AND (optimization OR optimize) | 981 | 641 | 300 | 1994 | 3916 |
| Total | 3862 | 2202 | 1332 | 8033 | 15,429 |
| No. | Criteria |
|---|---|
| 1 | The article is not published in English. |
| 2 | The article uses blockchain to secure IoT applications. |
| 3 | The article uses blockchain to secure a non-blockchain network optimization. |
| 4 | The article presents a sharding-based blockchain optimization. |
| No. | Criteria |
|---|---|
| 1 | The study emphasizes the communication complexity of consensus algorithms. |
| 2 | The paper proposes optimization for protocols used to share transactions or blocks. |
| 3 | The paper presents an optimized neighbor selection or peer-to-peer topology. |
| 4 | The paper proposes compression schemes for blockchain data before transmission. |
| Ref. | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | Blockchain | Study Objectives | Key Findings |
|---|---|---|---|---|---|---|---|---|---|---|---|
| [64] | √ | √ | √ | Bitcoin | Impact of network structure on traffic redundancy | Redundancy increases with number of peers | |||||
| [61] | √ | √ | Ethereum | Investigate P2P network structure, block propagation mechanisms and the evolution of network over time | Peer location determines block delivery latency High churn in P2P network Only a few nodes propagate new blocks | ||||||
| [47] | √ | √ | √ | EOSIO Tezos XRP Ledger | Compare transactional throughput to traffic generated | About 76% of traffic used for consensus | |||||
| [59] | √ | √ | √ | √ | √ | HLF | Study impact of HLF’s parameters on latency | Block generation latency increases with transaction arrival rate Increase in number of peer organizations increases latency | |||
| [32] | √ | √ | √ | √ | Investigate feasibility of a wireless blockchain network | PBFT has the highest communication complexity | |||||
| [66] | √ | √ | √ | √ | Bitcoin | Impact of miner’s geographi-cal distribution | Propagation delay increases with an increase in block size Higher propagation delay leads to higher occurrence of forks | ||||
| [29] | √ | √ | √ | √ | Bitcoin | Impact of P2P structure and gossip on latency | Forking rates reduces with a reduction in block propagation time | ||||
| [67] | √ | √ | Investigate peer communication and dynamicity of peers | The proportion of always-online peers determine variability of topology | |||||||
| [68] | √ | √ | Bitcoin | Causes of delay in bitcoin | Physical network characteristics impact block delivery time Internet usage at peak times reduces delivery | ||||||
| [62] | √ | √ | √ | √ | √ | HLF | Impact of HLF parameters | Transaction latency has linear relationship with network latency Bandwidth requirements of leader node is proportional to number of nodes | |||
| [63] | √ | √ | √ | HLF | Investigate the impact of delay on HLF performance | Network delay causes inconsistencies and block synchronization problems | |||||
| [30] | √ | √ | Bitcoin | Characteristics of Bitcoin’s P2P network | High churn rate Churning leads to increased block propagation time |
| Ref. | PC | PR | BI | CT | DT | HY | DY | LY | BW | Main Contributions | Limitations |
|---|---|---|---|---|---|---|---|---|---|---|---|
| [70] | √ | 33% | Gossip Algorithm with reduced degree of duplication | Results were collected using only nine peers | |||||||
| [71] | 33% | DHT for blockchain P2P Compression scheme to reduce size of transmitted data | |||||||||
| [31] | √ | >100% | 40% | Gossip algorithm with increased speed and reduced bandwidth consumption | Could still be bandwidth inefficient at large scales due to block duplication | ||||||
| [72,73] | Gossip algorithm with increased speed and reduced bandwidth consumption | ||||||||||
| [74] | √ | √ | 88% | Mathematical model to assess impact of wireless connectivity on block synchronization and smart contract execution | |||||||
| [75] | √ | 0.88% | Probability-based gossiping | Excessive and repeated send rate of INV messages can be an overhead | |||||||
| [69] | √ | 12.5% | Neighbor selection algorithm based on proximity | Susceptible to crowding and over reliance on one node | |||||||
| [76] | 75% | Weight-based neighbor selection | |||||||||
| [77] | √ | Tree-based topology for broadcast on the blockhain | No results presented on the effectiveness of the work | ||||||||
| [78] | √ | 7% | DHT P2P Topology | ||||||||
| [79] | √ | Intercrossing-net P2P topology for block broadcast | Overhead due to constant reassembly of blocks | ||||||||
| [80] | √ | √ | Cluster-based P2P topology | Susceptible to crowding and over reliance on one node | |||||||
| [81] | Clustered P2P topology | Susceptible to eclipse attacks | |||||||||
| [82] | √ | Semi-distributed P2P topology management | Susceptible to crowding and over reliance on one node | ||||||||
| [83] | √ | √ | √ | √ | √ | >100% | SDN-inspired topology management. Mathematical modelling of P2P topology | Increase in topology calculation time with increase in the number of peers. | |||
| [84] | √ | √ | >100% | >100% | Semi-distributed topology management | Increase in topology calculation time with network size. Overhead incurred by frequent leader election |
| Ref. | PC | PR | BI | LY | TT | BW | Main Contributions | Limitations |
|---|---|---|---|---|---|---|---|---|
| [14] | 10% | Probabilistic verification algorithm to determine when to validate blocks | Trustworthiness of nodes not checked | |||||
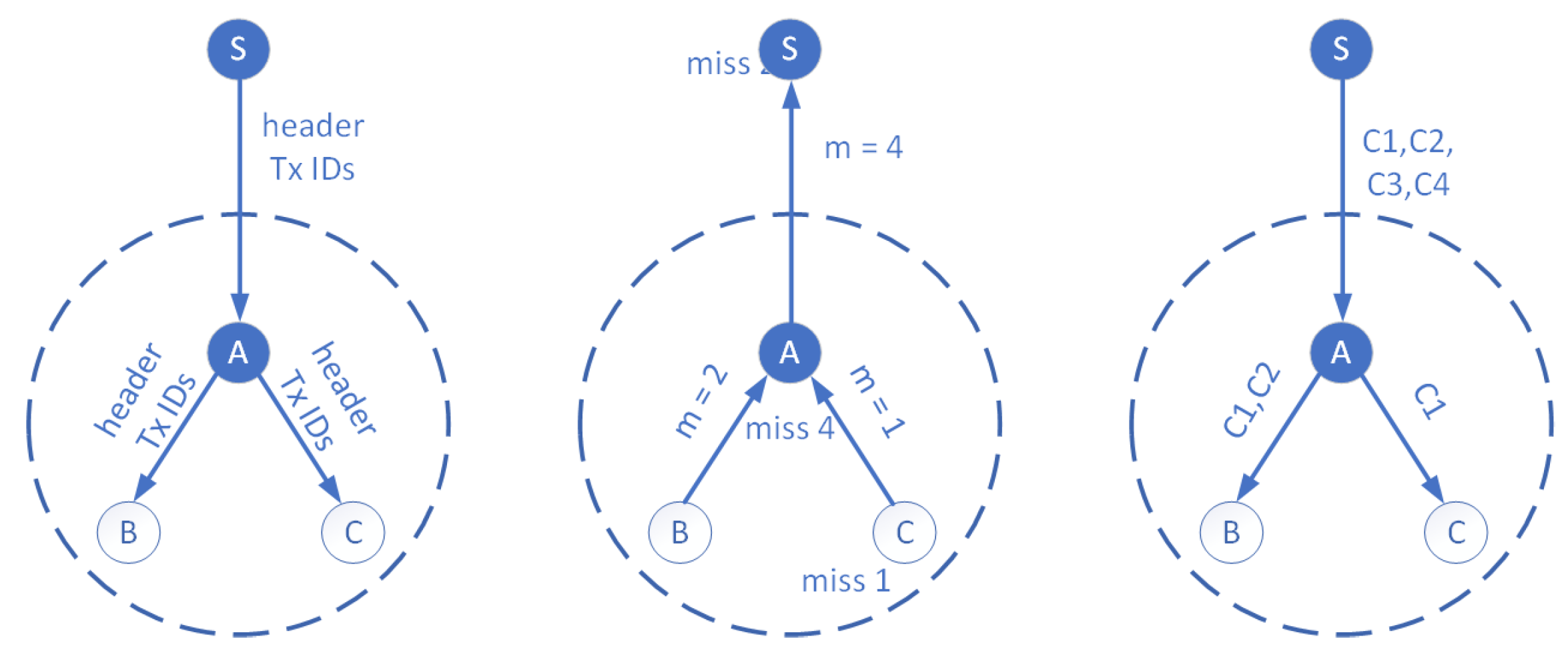
| [85] | √ | >100% | Trust-based verification Guarantor selection algorithm | |||||
| [86] | Reputation-based block verification | |||||||
| [87] | √ | >100% | Byzantine Agreement consensus algorithm with two rounds of communication | Performance degrades with increase in peers. | ||||
| [88] | √ | HSBFT consensus algorithm | No evaluation performed for the technique | |||||
| [89] | √ | 30% | Multi-Raft consensus algorithm | |||||
| [28] | √ | √ | >100% | 68.75% | SPBFT consensus algorithm | Evaluated against a network with a few nodes | ||
| [90] | √ | >100% | Multi-leader PBFT algorithm | |||||
| [91] | √ | √ | A closed-loop algorithm to determine the optimum blocks to mine | Higher occurrences of forking at high scale |
| Ref. | PC | PR | BI | BW | Main Contributions | Limitations |
|---|---|---|---|---|---|---|
| [95] | √ | 1.87% | XOR-based compression of blockchain traffic | Requires peers to have multiple network interfaces | ||
| [96] | √ | 82% | Erasure coding technique to compress transactions before transmission | Only effective when dealing with a few transactions | ||
| [97] | √ | Erasure coding technique to compress compact blocks | ||||
| [98] | √ | √ | >100% | Network coding technique to compress compact blocks | ||
| [99] | √ | A block structure with transactions replaced by their hashes | Requires peers to have a similar transaction pool. Will consume higher bandwidth if dissimilarity is high |
| Ref. | PC | PR | BI | CL | DL | LY | TT | Main Contributions | Limitations |
|---|---|---|---|---|---|---|---|---|---|
| [100] | √ | √ | √ | 36.7% | 20% | Methodology to construct optimum network based on empirical data | May not scale well with peers | ||
| [101] | √ | √ | √ | √ | 11.9% | A DRL algorithm to select optimum values for tunable parameters of the blockchain | Single agent may not scale well with an increase in peers |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Antwi, R.; Gadze, J.D.; Tchao, E.T.; Sikora, A.; Nunoo-Mensah, H.; Agbemenu, A.S.; Obour Agyekum, K.O.-B.; Agyemang, J.O.; Welte, D.; Keelson, E. A Survey on Network Optimization Techniques for Blockchain Systems. Algorithms 2022, 15, 193. https://doi.org/10.3390/a15060193
Antwi R, Gadze JD, Tchao ET, Sikora A, Nunoo-Mensah H, Agbemenu AS, Obour Agyekum KO-B, Agyemang JO, Welte D, Keelson E. A Survey on Network Optimization Techniques for Blockchain Systems. Algorithms. 2022; 15(6):193. https://doi.org/10.3390/a15060193
Chicago/Turabian StyleAntwi, Robert, James Dzisi Gadze, Eric Tutu Tchao, Axel Sikora, Henry Nunoo-Mensah, Andrew Selasi Agbemenu, Kwame Opunie-Boachie Obour Agyekum, Justice Owusu Agyemang, Dominik Welte, and Eliel Keelson. 2022. "A Survey on Network Optimization Techniques for Blockchain Systems" Algorithms 15, no. 6: 193. https://doi.org/10.3390/a15060193
APA StyleAntwi, R., Gadze, J. D., Tchao, E. T., Sikora, A., Nunoo-Mensah, H., Agbemenu, A. S., Obour Agyekum, K. O.-B., Agyemang, J. O., Welte, D., & Keelson, E. (2022). A Survey on Network Optimization Techniques for Blockchain Systems. Algorithms, 15(6), 193. https://doi.org/10.3390/a15060193










