Survey on Wireless Technology Trade-Offs for the Industrial Internet of Things
Abstract
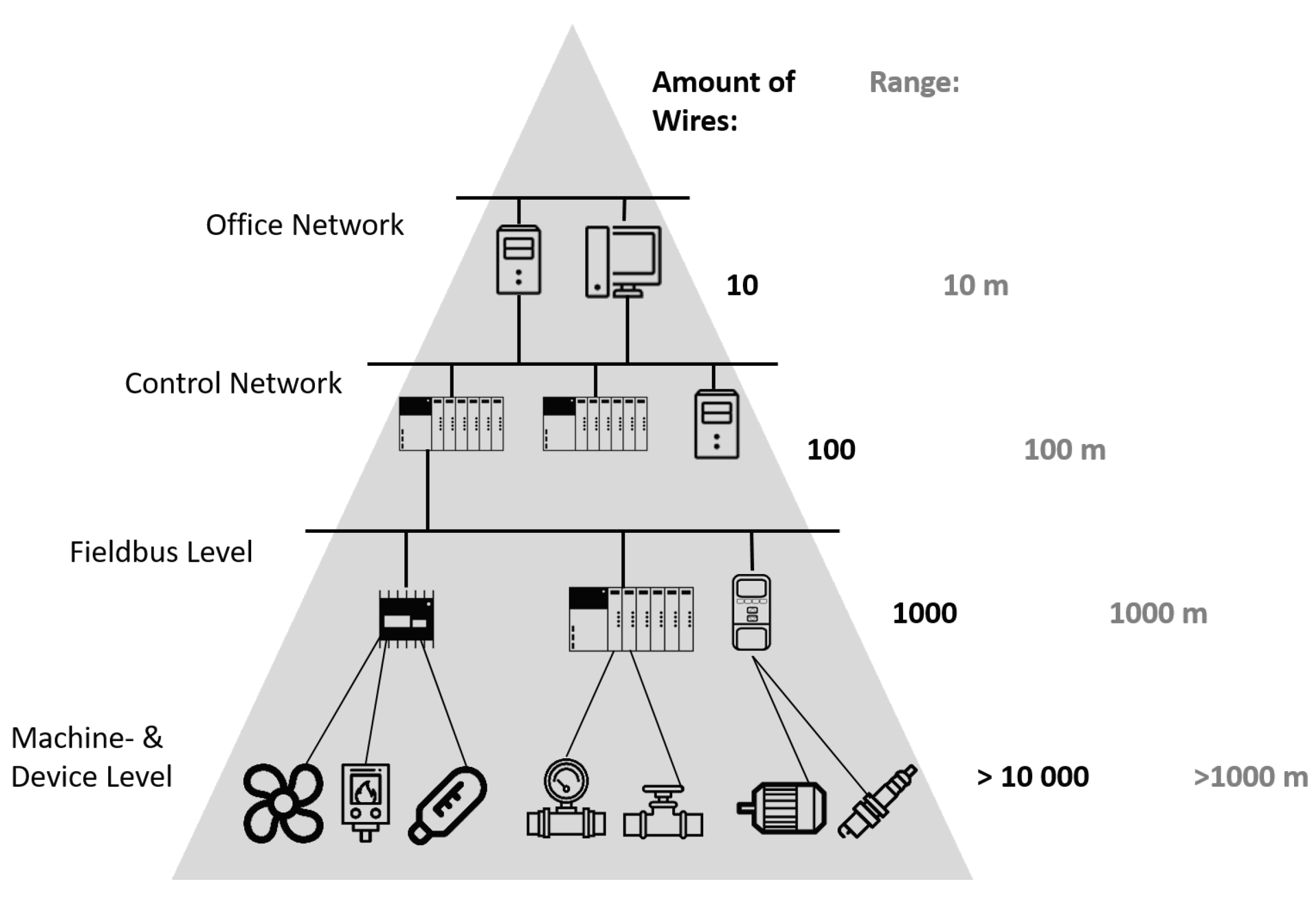
1. Introduction
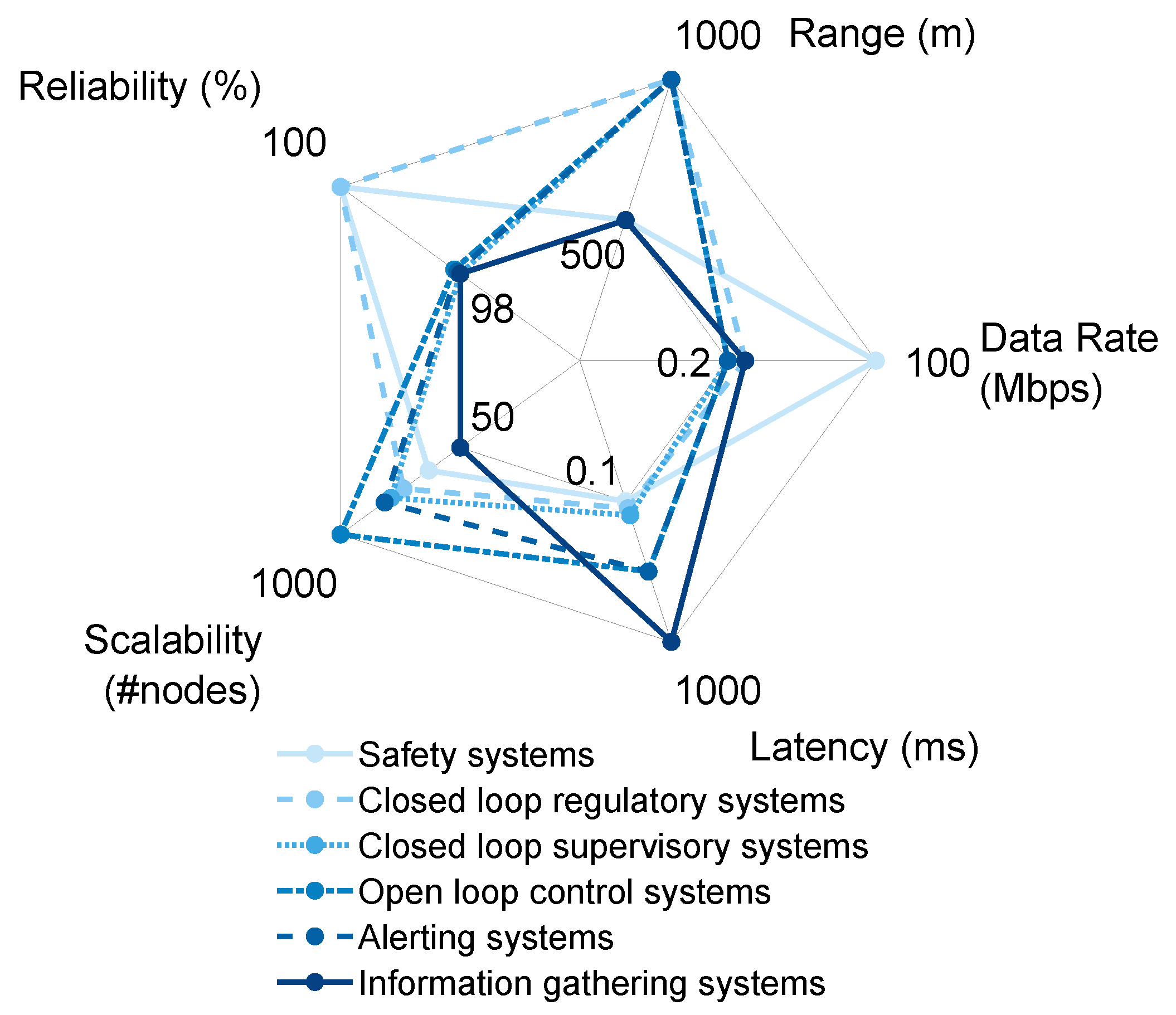
2. Requirements and Challenges
- Safety systems—require immediate actions on events (usually in the order of tens or hundreds of or a few ms).
- Closed loop regulatory systems - control the system via feedback loops operating either periodically or based on events. They may or may not have stricter timing requirements than safety systems.
- Closed loop supervisory systems—similar to regulatory systems with the difference that the feedbacks are usually non-critical and event-based, for example, collecting statistical data and reacting only when a certain trend is observed by issuing a notification or alarm.
- Open loop control systems—where sensors collect data and store it to the central database. An operator (human) analyzes the data and acts upon it if needed.
- Alerting systems—send periodical or event-based alerts indicating different stages, for example, heating up the boiler and alerting every once in a while to indicate the progress.
- Information gathering systems—collect the data (logging) and forward the logs to a server. These systems have no immediate operational consequence.
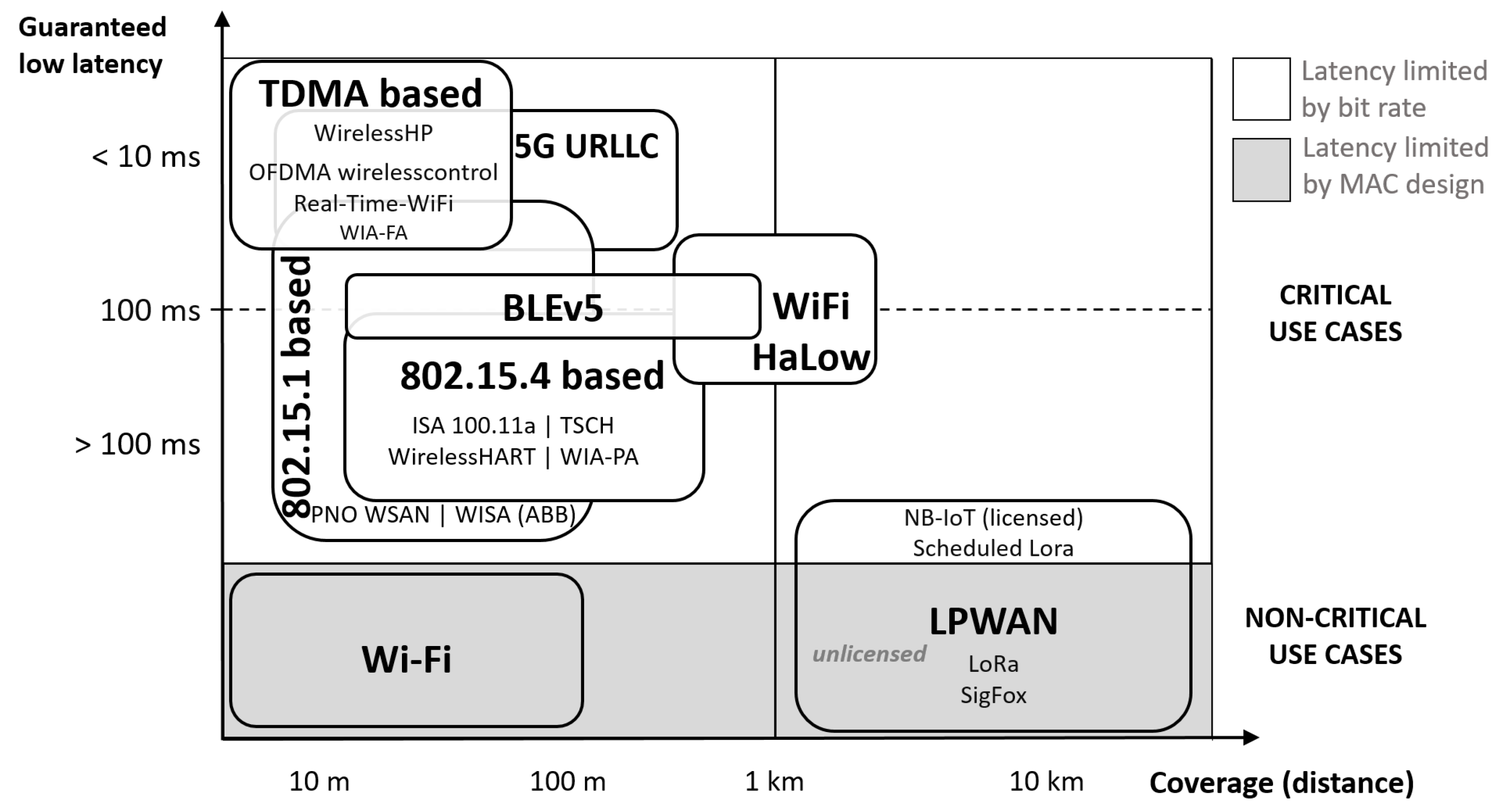
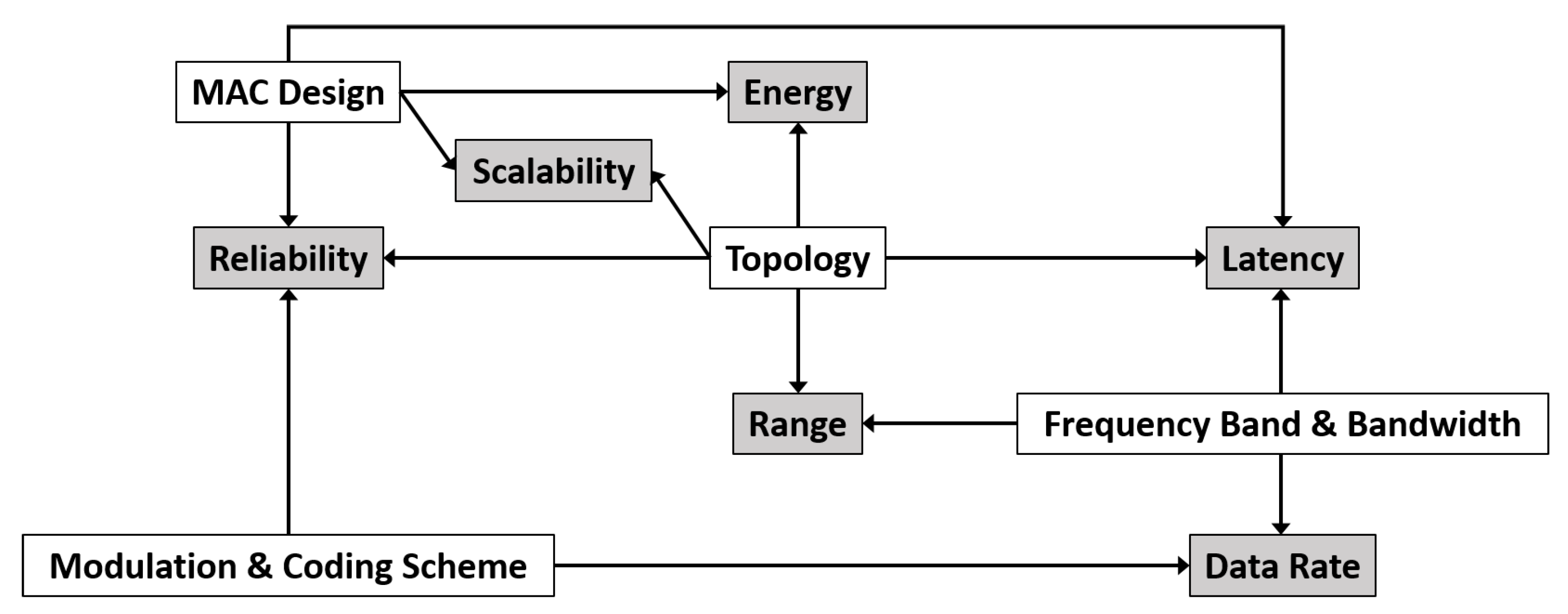
3. Trade-offs in Wireless Network Design
3.1. The Transmission Range
3.2. Latency
3.3. Reliability
3.4. Data Rate
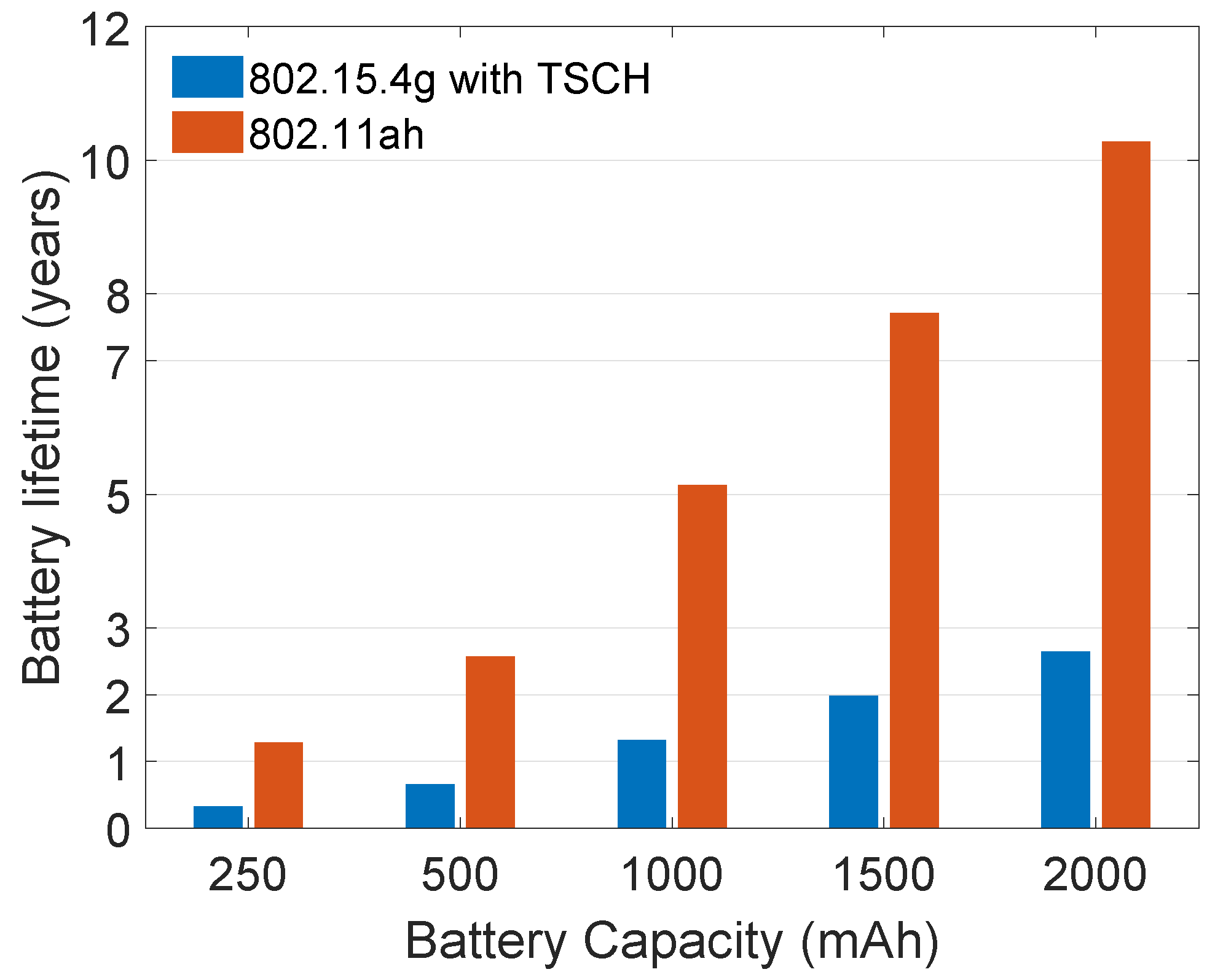
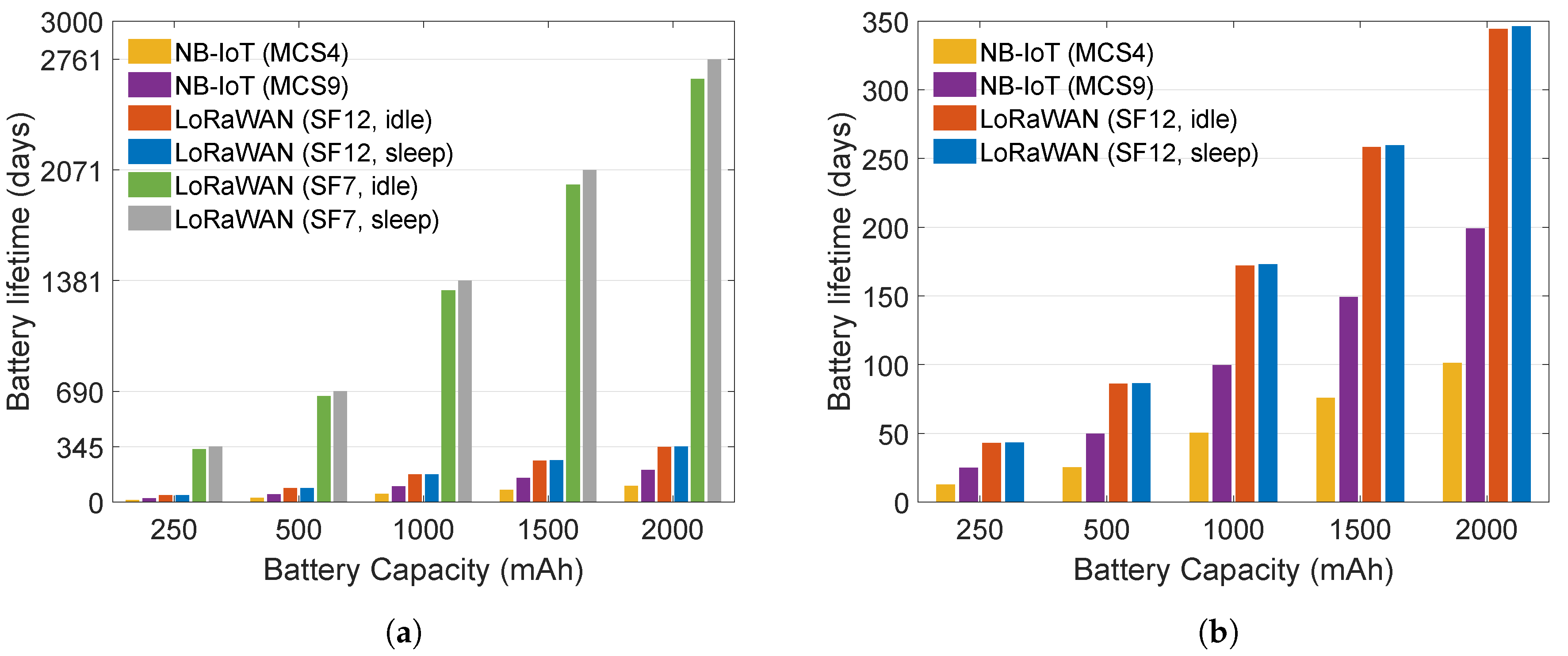
3.5. Energy Consumption
3.6. Scalability
3.7. Spectrum Regulations
4. Wireless Technologies for Industrial Applications
4.1. Long Range Networks
4.1.1. LoRa
- Class A devices have a single ReceiveWindow (RW) scheduled immediately after a corresponding uplink connection,
- Class B devices can schedule additional RWs,
- Class C devices continuously listen and can receive almost anytime.
4.1.2. IEEE 802.11ah/Wi-Fi HaLow
4.1.3. Narrowband-IoT
4.2. Long Range Multi-hop Networks
4.2.1. WirelessHART
4.2.2. ISA100.11a
4.2.3. Bluetooth Low Energy
4.2.4. Time Slotted Channel Hopping
5. Discussions
- spreading factor (and thus data rate): fixed choice or adaptive,
- reliability: ACKs or multiple transmissions of the same packet without downlink ACKs,
- higher layer logic: raw payload or Internet Protocol (IP) compliant stack.
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Willig, A.; Matheus, K.; Wolisz, A. Wireless technology in industrial networks. Proc. IEEE 2005, 93, 1130–1151. [Google Scholar] [CrossRef]
- Luvisotto, M.; Pang, Z.; Dzung, D. High-performance wireless networks for industrial control applications: New targets and feasibility. Proc. IEEE 2019, 107, 1074–1093. [Google Scholar] [CrossRef]
- Weiner, M.; Jorgovanovic, M.; Sahai, A.; Nikolié, B. Design of a low-latency, high-reliability wireless communication system for control applications. In Proceedings of the IEEE International Conference on Communications (ICC), Sydney, Australia, 10–14 June 2014. [Google Scholar] [CrossRef]
- Wei, Y.H.; Leng, Q.; Han, S.; Mok, A.K.; Zhang, W.; Tomizuka, M.; Li, T.; Malone, D.; Leith, D. RT-WiFi: Real-time high speed communication protocol for wireless control systems. ACM SIGBED Rev. 2013, 10, 28. [Google Scholar] [CrossRef]
- Das Neves Valadão, Y.; Künzel, G.; Müller, I.; Pereira, C.E. Industrial Wireless Automation: Overview and Evolution of WIA-PA. IFAC-PapersOnLine 2018, 51, 175–180. [Google Scholar] [CrossRef]
- HART Communications Foundation. HART Field Communication Protocol Specification; HFC_SPEC-12, Revision 6.0; HART Communications Foundation: Austin, TX, USA, 2001. [Google Scholar]
- International Society of Automation (ISA) Standard. Wireless Systems for Industrial Automation: Process Control and Related Applications; ISA-100.11 a-2009; International Society of Automation (ISA) Standard: Research Triangle Park, NC, USA, 2009. [Google Scholar]
- Harada, H.; Mizutani, K.; Fujiwara, J.; Mochizuki, K.; Obata, K.; Okumura, R. IEEE 802.15. 4g based Wi-SUN communication systems. IEICE Trans. Commun. 2017, 100, 1032–1043. [Google Scholar] [CrossRef]
- Hermeto, R.T.; Gallais, A.; Theoleyre, F. Scheduling for IEEE802. 15.4-TSCH and slow channel hopping MAC in low power industrial wireless networks: A survey. Comput. Commun. 2017, 114, 84–105. [Google Scholar] [CrossRef]
- IEC-International Electrotechnical Commission. Industrial Networks: Wireless Communication Network and Communication Profiles; IEC PAS 62601; IEC-International Electrotechnical Commission: Geneva, Switzerland, 2015. [Google Scholar]
- Saelens, M.; Hoebeke, J.; Shahid, A.; De Poorter, E. Impact of EU duty cycle and transmission power limitations for sub-GHz LPWAN SRDs: An overview and future challenges. EURASIP J. Wirel. Commun. Netw. 2019, 2019, 219. [Google Scholar] [CrossRef]
- Åkerberg, J.; Gidlund, M.; Björkman, M. Future research challenges in wireless sensor and actuator networks targeting industrial automation. In Proceedings of the 2011 9th IEEE International Conference on Industrial Informatics (INDIN), Lisbon, Portugal, 26–29 July 2011; pp. 410–415. [Google Scholar]
- Ovsthus, K.; Kristensen, L.M. An industrial perspective on wireless sensor networks–a survey of requirements, protocols, and challenges. IEEE Commun. Surv. Tutor. 2014, 16, 1391–1412. [Google Scholar]
- Frotzscher, A.; Wetzker, U.; Bauer, M.; Rentschler, M.; Beyer, M.; Elspass, S.; Klessig, H. Requirements and current solutions of wireless communication in industrial automation. In Proceedings of the 2014 IEEE International Conference on Communications Workshops (ICC), Sydney, Australia, 10–14 June 2014; pp. 67–72. [Google Scholar]
- Li, X.; Li, D.; Wan, J.; Vasilakos, A.V.; Lai, C.F.; Wang, S. A review of industrial wireless networks in the context of industry 4.0. Wirel. Netw. 2017, 23, 23–41. [Google Scholar] [CrossRef]
- Wollschlaeger, M.; Sauter, T.; Jasperneite, J. The future of industrial communication: Automation networks in the era of the internet of things and industry 4.0. IEEE Ind. Electron. Mag. 2017, 11, 17–27. [Google Scholar] [CrossRef]
- Park, P.; Ergen, S.C.; Fischione, C.; Lu, C.; Johansson, K.H. Wireless network design for control systems: A survey. IEEE Commun. Surv. Tutor. 2018, 20, 978–1013. [Google Scholar] [CrossRef]
- Gunatilaka, D. High Performance Wireless Sensor-Actuator Networks for Industrial Internet of Things. Ph.D. Thesis, Washington University in St. Louis, St. Louis, MO, USA, 2019. [Google Scholar]
- Wang, Q.; Jiang, J. Comparative examination on architecture and protocol of industrial wireless sensor network standards. IEEE Commun. Surv. Tutor. 2016, 18, 2197–2219. [Google Scholar] [CrossRef]
- De Pellegrini, F.; Miorandi, D.; Vitturi, S.; Zanella, A. On the use of wireless networks at low level of factory automation systems. IEEE Trans. Ind. Inf. 2006, 2, 129–143. [Google Scholar] [CrossRef]
- Christin, D.; Mogre, P.S.; Hollick, M. Survey on wireless sensor network technologies for industrial automation: The security and quality of service perspectives. Future Internet 2010, 2, 96–125. [Google Scholar] [CrossRef]
- Lu, C.; Saifullah, A.; Li, B.; Sha, M.; Gonzalez, H.; Gunatilaka, D.; Wu, C.; Nie, L.; Chen, Y. Real-time wireless sensor-actuator networks for industrial cyber-physical systems. Proc. IEEE 2016, 104, 1013–1024. [Google Scholar] [CrossRef]
- Sanchez-Iborra, R.; Cano, M.D. State of the art in LP-WAN solutions for industrial IoT services. Sensors 2016, 16, 708. [Google Scholar] [CrossRef]
- Varghese, A.; Tandur, D. Wireless requirements and challenges in Industry 4.0. In Proceedings of the 2014 International Conference on Contemporary Computing and Informatics (IC3I), Mysore, India, 27–29 November 2014; pp. 634–638. [Google Scholar]
- Zurawski, R. Industrial Communication Technology Handbook; CRC Press: Boca Raton, FL, USA, 2014. [Google Scholar]
- Tindell, K.; Burns, A. Guaranteeing message latencies on control area network (CAN). In Proceedings of the 1st International CAN Conference; 1994. Available online: https://citeseer.ist.psu.edu/viewdoc/download?doi=10.1.1.43.3251&rep=rep1&type=pdf (accessed on 15 January 2020).
- Luvisotto, M.; Tramarin, F.; Vitturi, S. Assessing the impact of full-duplex wireless in real-time industrial networks. In Proceedings of the IECON 2018—44th Annual Conference of the IEEE Industrial Electronics Society, Washington, DC, USA, 21–23 October 2018; pp. 4119–4124. [Google Scholar]
- Vuran, M.C.; Akyildiz, I.F. Error control in wireless sensor networks: A cross layer analysis. IEEE/ACM Trans. Netw. (TON) 2009, 17, 1186–1199. [Google Scholar] [CrossRef]
- Bor, M.C.; Roedig, U.; Voigt, T.; Alonso, J.M. Do LoRa low-power wide-area networks scale? In Proceedings of the 19th ACM International Conference on Modeling, Analysis and Simulation of Wireless and Mobile Systems, Malta, 13–17 November 2016; pp. 59–67. [Google Scholar]
- Aref, M.; Sikora, A. Free space range measurements with Semtech LoRa™ technology. In Proceedings of the 2014 2nd International Symposium on Wireless Systems within the Conferences on Intelligent Data Acquisition and Advanced Computing Systems, Offenburg, Germany, 11–12 September 2014; pp. 19–23. [Google Scholar]
- Van den Abeele, F.; Haxhibeqiri, J.; Moerman, I.; Hoebeke, J. Scalability analysis of large-scale LoRaWAN networks in ns-3. IEEE Internet Things J. 2017, 4, 2186–2198. [Google Scholar] [CrossRef]
- Haxhibeqiri, J.; De Poorter, E.; Moerman, I.; Hoebeke, J. A survey of lorawan for iot: From technology to application. Sensors 2018, 18, 3995. [Google Scholar] [CrossRef]
- Rizzi, M.; Ferrari, P.; Flammini, A.; Sisinni, E.; Gidlund, M. Using LoRa for industrial wireless networks. In Proceedings of the 2017 IEEE 13th International Workshop on Factory Communication Systems (WFCS), Trondheim, Norway, 31 May–2 June 2017; pp. 1–4. [Google Scholar]
- Pötsch, A.; Hammer, F. Towards end-to-end latency of LoRaWAN: Experimental analysis and IIoT applicability. In Proceedings of the 2019 15th IEEE international workshop on factory communication systems (WFCS), Sundsvall, Sweden, 27–29 May 2019; pp. 1–4. [Google Scholar]
- Šljivo, A.; Kerkhove, D.; Tian, L.; Famaey, J.; Munteanu, A.; Moerman, I.; Hoebeke, J.; De Poorter, E. Performance Evaluation of IEEE 802.11ah Networks With High-Throughput Bidirectional Traffic. Sensors 2018, 18, 325. [Google Scholar] [CrossRef]
- Seferagić, A.; Moerman, I.; De Poorter, E.; Hoebeke, J. Evaluating the suitability of IEEE 802.11 ah for low-latency time-critical control loops. IEEE Internet Things J. 2019, 6, 7839–7848. [Google Scholar] [CrossRef]
- Santi, S.; Šljivo, A.; Tian, L.; De Poorter, E.; Hoebeke, J.; Famaey, J. Supporting heterogeneous IoT traffic using the IEEE 802.11 Ah restricted access window. In Proceedings of the 15th ACM Conference on Embedded Network Sensor Systems, Delft, The Netherlands, 6–8 November 2017; p. 32. [Google Scholar]
- Šljivo, A.; Kerkhove, D.; Moerman, I.; De Poorter, E.; Hoebeke, J. Reliability and Scalability Evaluation with TCP/IP of IEEE802. 11ah Networks. In Proceedings of the Workshop on ns3 (WNS3), Porto, Portugal, 13–14 June 2017; pp. 1–4. [Google Scholar]
- Chen, J.; Hu, K.; Wang, Q.; Sun, Y.; Shi, Z.; He, S. Narrowband internet of things: Implementations and applications. IEEE Internet Things J. 2017, 4, 2309–2314. [Google Scholar] [CrossRef]
- Wang, Y.P.E.; Lin, X.; Adhikary, A.; Grovlen, A.; Sui, Y.; Blankenship, Y.; Bergman, J.; Razaghi, H.S. A primer on 3GPP narrowband Internet of Things. IEEE Commun. Mag. 2017, 55, 117–123. [Google Scholar] [CrossRef]
- Basu, S.S.; Sultania, A.K.; Famaey, J.; Hoebeke, J. Experimental Performance Evaluation of NB-IoT. In Proceedings of the International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Barcelona, Spain, 21–23 October 2019. [Google Scholar]
- Martinez, B.; Adelantado, F.; Bartoli, A.; Vilajosana, X. Exploring the Performance Boundaries of NB-IoT. IEEE Internet Things J. 2019, 6, 5702–5712. [Google Scholar] [CrossRef]
- Martinez, B.; Vilajosana, X.; Chraim, F.; Vilajosana, I.; Pister, K.S. When scavengers meet industrial wireless. IEEE Trans. Ind. Electron. 2015, 62, 2994–3003. [Google Scholar] [CrossRef]
- Petersen, S.; Carlsen, S. Performance evaluation of WirelessHART for factory automation. In Proceedings of the 2009 IEEE Conference on Emerging Technologies & Factory Automation, Palma de Mallorca, Spain, 22–25 September 2009; pp. 1–9. [Google Scholar]
- Han, S.; Zhu, X.; Aloysius, K.M.; Nixon, M.; Blevins, T.; Chen, D. Control over WirelessHART network. In Proceedings of the IECON 2010-36th Annual Conference on IEEE Industrial Electronics Society, Glendale, AZ, USA, 7–10 November 2010; pp. 2114–2119. [Google Scholar]
- Åkerberg, J.; Gidlund, M.; Reichenbach, F.; Björkman, M. Measurements on an Industrial Wireless Hart Network Supporting Profisafe: A Case Study. In Proceedings of the International Conference on Emerging Technologies and Factory Automation (ETFA), Toulouse, France, 5–9 September 2011; IEEE: Piscataway, NJ, USA, 2011; pp. 1–8. [Google Scholar]
- Hassan, S.M.; Bingi, K.; Ibrahim, R.; Chein, L.J.; Supramaniam, T. Implementation of flow control over wirelessHART sensor network using wirelessHART adaptors. Indones. J. Electr. Eng. Comput. Sci. 2019, 15, 910–919. [Google Scholar]
- One Wireless Field Device Access Point Specification Release 310 OW03-650-310 Kernel Description. 2018. Available online: https://www.honeywellprocess.com/library/marketing/tech-specs/onewireless-fdap-specification.pdf (accessed on 14 December 2018).
- Jecan, E.; Pop, C.; Padrah, Z.; Ratiu, O.; Puschita, E. A dual-standard solution for industrial Wireless Sensor Network deployment: Experimental testbed and performance evaluation. In Proceedings of the 14th IEEE International Workshop on Factory Communication Systems (WFCS), Imperia, Italy, 13–15 June 2018. [Google Scholar]
- Karvonen, H.; Pomalaza-Ráez, C.; Mikhaylov, K.; Hämäläinen, M.; Iinatti, J. Experimental Performance Evaluation of BLE 4 Versus BLE 5 in Indoors and Outdoors Scenarios; Advances in Body Area Networks, I., Fortino, G., Wang, Z., Eds.; Springer: Cham, Switzerland, 2019; pp. 235–251. [Google Scholar]
- Baert, M.; Rossey, J.; Shahid, A.; Hoebeke, J. The Bluetooth mesh standard: An overview and experimental evaluation. Sensors 2018, 18, 2409. [Google Scholar] [CrossRef]
- Mochizuki, K.; Obata, K.; Mizutani, K.; Harada, H. Development and field experiment of wide area Wi-SUN system based on IEEE 802.15. 4g. In Proceedings of the 2016 IEEE 3rd World Forum on Internet of Things (WF-IoT), Reston, VA, USA, 12–14 December 2016; pp. 76–81. [Google Scholar]
- Cena, G.; Scanzio, S.; Valenzano, A.; Zunino, C. Experimental Analysis and Comparison of Industrial IoT Devices based on TSCH. In Proceedings of the 24th IEEE International Conference on Emerging Technologies and Factory Automation (ETFA), Zaragoza, Spain, 10–13 September 2019. [Google Scholar] [CrossRef]
- ETSI. System Reference document (SRdoc). In Technical characteristics for Low Power Wide Area Networks Chirp Spread Spectrum (LPWAN-CSS) operating in the UHF spectrum below 1 GHz; ETSI TR 103 526 V1.1.1; ETSI: Sophia Antipolis Cedex, France, 2018. [Google Scholar]
- LoRa Alliance. LoRaWAN™ Specification; LoRa Alliance Inc.: Beaverton, OR, USA, 2015; Available online: https://lora-alliance.org/sites/default/files/2018-04/lorawantm_specification_-v1.1.pdf (accessed on 11 October 2017).
- IEEE Standard for Information Technology–Telecommunications and Information Exchange between Systems—Local and Metropolitan Area Networks–Specific Requirements—Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications Amendment 2: Sub 1 GHz License Exempt Operation; IEEE Std 802.11ah-2016 (Amendment to IEEE Std 802.11-2016, as amended by IEEE Std 802.11ai-2016); IEEE: New York, NY, USA, 2017; pp. 1–594. [CrossRef]
- Liu, Y.; Guo, J.; Orlik, P.; Nagai, Y.; Watanabe, K.; Sumi, T. Coexistence of 802.11 ah and 802.15. 4g networks. In Proceedings of the 2018 IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- Haxhibeqiri, J.; Van den Abeele, F.; Moerman, I.; Hoebeke, J. LoRa scalability: A simulation model based on interference measurements. Sensors 2017, 17, 1193. [Google Scholar] [CrossRef]
- Sultania, A.K.; Delgado, C.; Famaey, J. Implementation of NB-IoT Power Saving Schemes in ns-3. In Proceedings of the 2019 Workshop on Next-Generation Wireless with ns-3, Florence, Italy, 21 June 2019; pp. 5–8. [Google Scholar]
- Tian, L.; Šljivo, A.; Santi, S.; De Poorter, E.; Hoebeke, J.; Famaey, J. Extension of the IEEE 802.11 ah ns-3 Simulation Module. In Proceedings of the 10th Workshop on ns-3, Mangalore, India, 13–14 June 2018; pp. 53–60. [Google Scholar]
- Municio, E.; Daneels, G.; Vučinić, M.; Latré, S.; Famaey, J.; Tanaka, Y.; Brun, K.; Muraoka, K.; Vilajosana, X.; Watteyne, T. Simulating 6TiSCH networks. Trans. Emerg. Telecommun. Technol. 2019, 30, e3494. [Google Scholar] [CrossRef]
- Muñoz, J.; Chang, T.; Vilajosana, X.; Watteyne, T. Evaluation of IEEE802. 15.4 g for Environmental Observations. Sensors 2018, 18, 3468. [Google Scholar] [CrossRef]
- Bellekens, B.; Tian, L.; Boer, P.; Weyn, M.; Famaey, J. Outdoor IEEE 802.11 ah range characterization using validated propagation models. In Proceedings of the GLOBECOM 2017—2017 IEEE Global Communications Conference, Singapore, 4–8 December 2017; pp. 1–6. [Google Scholar]
- Ousat, B.; Ghaderi, M. LoRa Network Planning: Gateway Placement and Device Configuration. Proceedings of 2019 IEEE International Congress on Internet of Things (ICIOT), Milan, Italy, 8–13 July 2019; pp. 25–32. [Google Scholar]
- Tian, L.; Khorov, E.; Latré, S.; Famaey, J. Real-Time Station Grouping under Dynamic Traffic for IEEE 802.11ah. Sensors 2017, 17, 1559. [Google Scholar] [CrossRef] [PubMed]
- Khorov, E.; Lyakhov, A.; Krotov, A.; Guschin, A. A survey on IEEE 802.11ah: An enabling networking technology for smart cities. Comput. Commun. 2015, 58, 53–69. [Google Scholar] [CrossRef]
- Shamsi, M. WirelessHART Field Device Installation and Configuration. 2016. Available online: https://www.emerson.com/documents/automation/article-wirelesshart-field-device-installation-configuration-en-38282.pdf (accessed on 8 January 2019).
| Application | Range [m] | Cycle Time |
|---|---|---|
| Building automation | 10–200 | 100 ms—seconds |
| Monitoring and supervision | 100–1000 | seconds—days |
| Process control | 50–500 | 10–1000 ms |
| Factory automation | 10–50 | 0.5–100 ms |
| Automotive | 1–10 | 1–100 ms |
| Interlocking and control | 50–100 | 10–250 ms |
| Power-system protection | 100–10 k | 0.01 –50 ms |
| Event-based control | 10–100 | 1–100 ms |
| LoRa | IEEE 802.11ah | NB-IoT | 802.15.4g TSCH | |
|---|---|---|---|---|
| Band | unlicensed sub-GHz | unlicensed sub-GHz | licensed (LTE band) | unlicensed sub-GHz |
| Bandwidth | 125 kHz/250 kHz | 1/2/4/8/16 MHz | 180 kHz | 200 kHz–1.25 MHz |
| Topology | star-of-stars | star/tree | cellular | star, p2p mesh |
| Deployment | private/operator-based | private | operator-based | private |
| MAC | LoRaWAN | hybrid | LTE based | TSCH |
| EDCA/DCF | OFDMA (DL) & SC-FDMA (UL) | |||
| Retransmissions | yes | yes | yes | yes |
| Reliability mechanisms | orthogonal SFs | FEC, WPA1 (MIC), WPA2 (CCM) | FEC, ARQ | FSK/O-QPSK/OFDM |
| 32-bit MIC | WPA3 (BIP-GMAC-256) | |||
| Range | 15 km | 1 km | 20 km | 1 km |
| Nodes per network | unlimited | 8192 | 52,247 per cell | 6000 |
| Data rate | 250 bps–5.5 kbps/11 kbps/50 kbps | 150 kbps–78 Mbps | <250 kbps | 6.25 kbps–800 kbps |
| Min. cycle time | >1 s | >20 ms | >1.6 s | > 20 ms |
| WirelessHART | ISA100.11a | BLE | 802.15.4e TSCH | |
|---|---|---|---|---|
| Band | 2.4 GHz ISM | 2.4 GHz ISM | 2.4/5 GHz ISM | 2.4 GHz ISM |
| Bandwidth | 200 kHz–1.2 MHz | 2 MHz | 2 MHz | 2 MHz/5 MHz |
| Topology | mesh | star/mesh/star-mesh | p2p/star/mesh | star, tree, mesh |
| Deployment | private | private | private | private |
| MAC | time sync., freq. hopping | TDMA / CSMA/CA (10–12 ms) | TDMA | TSCH |
| TSMP (TDMA, 10ms) | (TDMA/CSMA/CA) | |||
| Retransmissions | yes | yes | yes | yes |
| Reliability mechanisms | ARQ, FHSS | ARQ, FHSS, DSSS | FHSS, 24-bit CRC, | DSSS/OQPSK |
| DSSS, 32-bit MIC | 32-to-128-bit MIC | 32-bit MIC, FEC | ||
| Range | <1.5 km (225 m) | <1.5 km (100 m) | <100 m/<1000 m | <200 m |
| Nodes per network | 30,000/hundreds per AP | unlimited/thousands per GW | unlimited | unlimited |
| Data rate | <250 kbps | <250 kbps | 125 kbps/1 Mbps/2 Mbps | 250 kbps |
| Min. cycle time | 500 ms | 500 ms | 50 ms | 20 ms |
| IEEE 802.15.4g | IEEE 802.11ah | LoRaWAN | NB-IoT | |
|---|---|---|---|---|
| Radio module | Atmel AT86RF215 | SEMTECH SX1272 | uBlox SARA N210 | |
| TX power (dBm) | 14 | 23 | 20 | |
| Power (mA) | 28/62/6.28/0.03 | 11.2/125/0.0015/0.0001 | 46/220/6/0.003 | |
| [RX/TX/idle/sleep] | ||||
| Technology-specific | 113 slots @ 40 ms per frame | 4096 ms beacon interval | no repetitions | RRC: 10 s, DRX: 0 s, |
| parameters | 2-FSK—100 kHz (50 kbps) | MCS 10 —1 MHz (150 kbps) | no ACK | PSM: TI s |
| 0.33% DIO and EB probability | 1 RAW group, 1 slot | no repetitions | ||
| Payload size | 104 bytes | 12 bytes | ||
| Microcontroller | ARM Cortex M3 @ 32 MHz (3.38 mA power consumption) | |||
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Seferagić, A.; Famaey, J.; De Poorter, E.; Hoebeke, J. Survey on Wireless Technology Trade-Offs for the Industrial Internet of Things. Sensors 2020, 20, 488. https://doi.org/10.3390/s20020488
Seferagić A, Famaey J, De Poorter E, Hoebeke J. Survey on Wireless Technology Trade-Offs for the Industrial Internet of Things. Sensors. 2020; 20(2):488. https://doi.org/10.3390/s20020488
Chicago/Turabian StyleSeferagić, Amina, Jeroen Famaey, Eli De Poorter, and Jeroen Hoebeke. 2020. "Survey on Wireless Technology Trade-Offs for the Industrial Internet of Things" Sensors 20, no. 2: 488. https://doi.org/10.3390/s20020488
APA StyleSeferagić, A., Famaey, J., De Poorter, E., & Hoebeke, J. (2020). Survey on Wireless Technology Trade-Offs for the Industrial Internet of Things. Sensors, 20(2), 488. https://doi.org/10.3390/s20020488







