Distributed Ledger Technology for eHealth Identity Privacy: State of The Art and Future Perspective
Abstract
1. Introduction
2. Background and Related Work
2.1. Identity and Identity Management
2.2. Distributed Ledger Technology
2.3. Blockchain-Based Identity Management Systems
- A comprehensive review of the identity management models evolution.
- Enumerating the limitation of the centralized identity toward eHealth.
- Identification of healthcare key players, roles, and tasks, as well as eHealth identity scenarios.
- A number of challenges and future works are also discussed.
3. The Evolution of Identity Management Models
3.1. The Evolution and the Stages of Identity Models
3.1.1. Centralized Identity Model
3.1.2. Federated Identity Model
3.1.3. User-Centric Identity Model
3.1.4. Decentralized Identity
3.2. Comparison of Identity Management Models
3.2.1. Comparison Criteria
3.2.2. Discussion
4. eHealth Identity Management Players and Use Cases
4.1. Healthcare Key Players
- Healthcare regulators: including government organizations and healthcare institutions like public health departments and hospitals. In the eHealth system, the regulators aggregate data from the other players in order to develop the eHealth framework and update the care metrics.
- Industry representatives: encompass insurance companies, pharmaceutical firms, and health equipment companies. They operationalize the different elements of the healthcare framework and provide advanced solutions based on a range of data collected from the other players.
- Healthcare providers: can be a physician, a nurse, an ambulance service or any other independent provider. They are responsible for delivering care service and coordinate as care team members. They need access to the facilities and patient information as well as other medical records anytime anywhere to deliver a good quality of service.
- Healthcare consumers: the patients are typically the citizens or people who received treatments and care from the healthcare providers. Patients also may want to access their healthcare records via a personal electronic device or share special information with their care provider.
4.2. Key Players’ Roles and Tasks
4.3. eHealth Identity Scenarios
4.4. The Limitation of Centralized Identity Management Models for ehealth
- Privacy, security, and usability: the healthcare data is sensitive by nature and it needs a maximum of security against data breaches and privacy disclosure when exchanging the data especially after enabling third parties’ medical services to interact with the system.
- Single point of failure: centralizing all the patients’ credentials and all identity decisions in one IdP leads to a single point of failure that it can be possible by human mistake or a hardware damage as well as a natural disaster.
- Single point of access for malicious users: centralizing all the credentials in one IdP will also make the system weak and give hackers an easy way to scam users unless providing trained security professionals to maintain and manage the security of this point or the system which is considered as another challenge.
- The complexity of the ecosystem: the complexity of securing and managing such a centralized ecosystem is considerable and cost-effective, particularly when building trust between the stakeholders, and may it need a special department with an army of engineers and security professionals to make it possible.
5. Decentralized Identity Management Models
5.1. Distributed Ledger Technology for eHealth Identity Management
5.2. Decentralized Identity Models
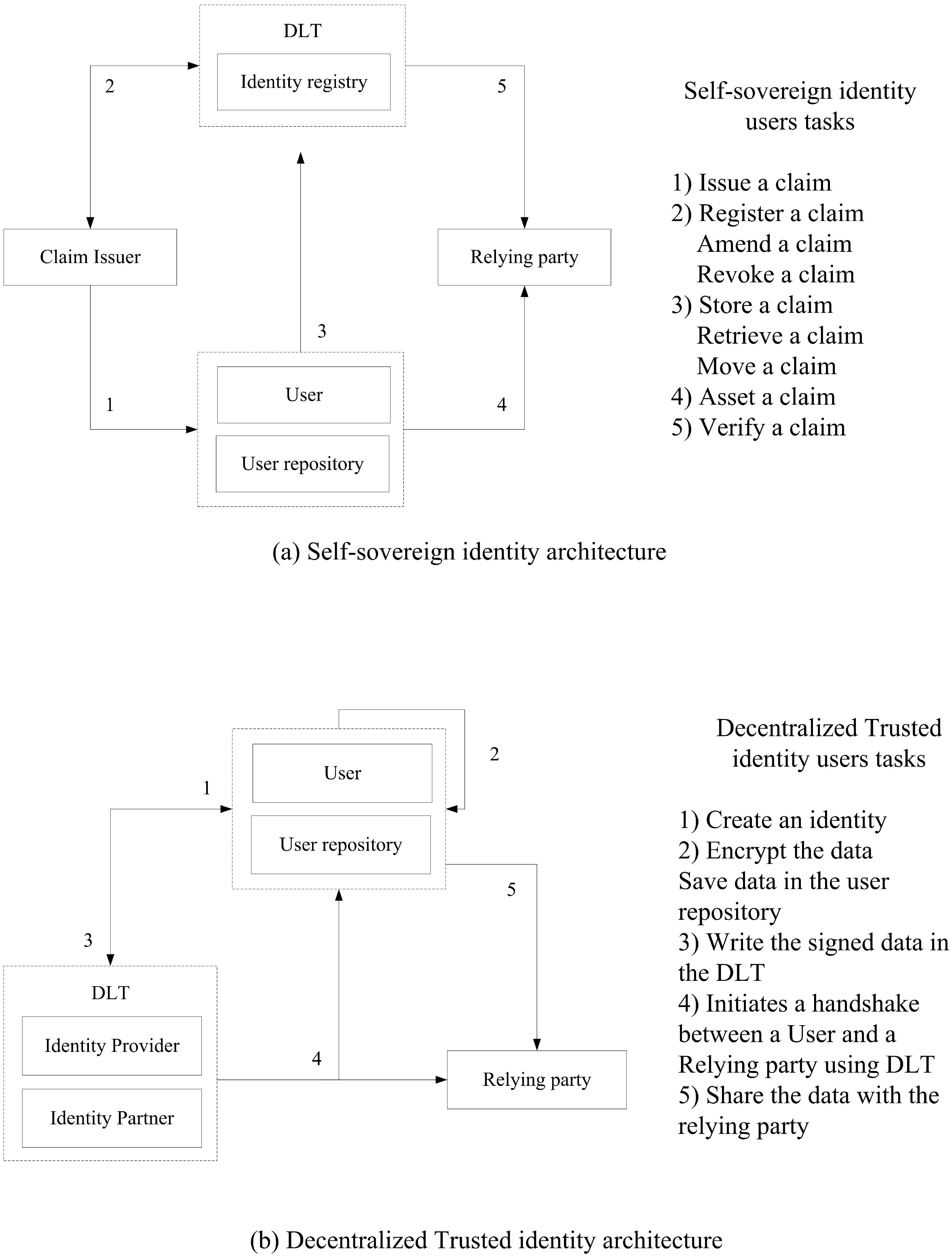
5.2.1. Self-Sovereign Identity
5.2.2. Decentralized Trusted Identity
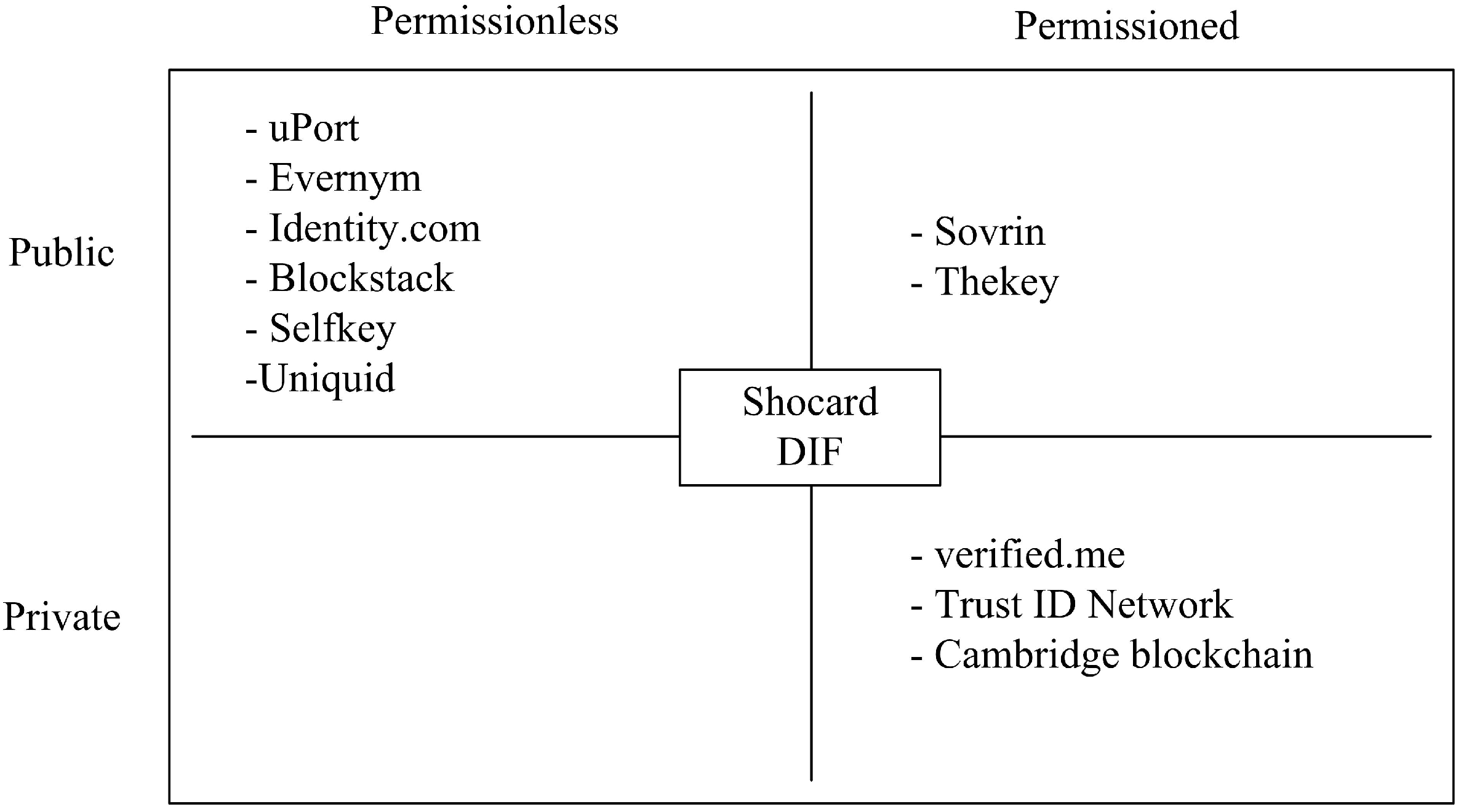
6. Existing Decentralized Solutions
6.1. Public Blockchain Identity Solutions
- uPort is an identity solution settled by ConsenSys Lab [59] and built on the top of Ethereum. The uPort mission is to hand back the control of the digital identity to the user. It uses an interoperable identity layer composed of identity and messaging protocols and it uses also the concept of smart contract and verifiable credentials. The solution infrastructure composed by a mobile app that contains a self-sovereign wallet, an authentication mechanism for the modern web applications and decentralized application, and the developer’s libraries to allow the integration with third party services.
- Sovrin is the solution that claimed to be the decentralized global lifetime public utility for self-sovereign identity [60]. It can be used with any entity including people, organizations, and things. The solution is integrated with Hyperledger Indy which is a blockchain network designed especially for decentralized identity and it’s developed by both Sovrin and Linux foundations.
- Identity.com is an open-source project providing secure access to decentralized identity verification [50]. The ecosystem is composed of Smart contract and blockchain technologies. The solution at first was only designed to support Civic identity system but after that, it becomes a hub for many players as the network grows. The solution has three major components which are smart contracts to leverage the decentralized identity, open-source libraries to allow third-party service to interact with the ecosystem, and open-source application to meet the developer’s needs.
- Evernym is developing a sophisticated identity platform on the top of Sovrin and IOTA [61]. The aim of the Evernym team is to develop the necessary tools and protocols for individuals and enterprises such as identity owner tools, and claim exchange and verification tools to integrate self-severing identity in all industries and ecosystems, and also to leverage SSI identity using different distributed ledger solutions.
- Blockstack is a project built on the top of the Bitcoin network [51] to provide the tools to develop the decentralized application. It’s known as a decentralized identity, discovery and storage platform. The main concept of Blockstack is that computing is performed off-chain and it uses virtual chains to pin the state machines to the network. The identity model in Blockstack known as Onename which is mainly developed to register users and the model is operating on the top of Bitcoin.
- THEKEY is a decentralized ecosystem supporting identity verification using big data and blockchain [52]. THEKEY uses the technology of NEO [62] smart contracts and benefits from the multi-programming language of the NEO network to leverage the identity to various industries. They claim that the second generation of identity verification will be realized by Blockchain-based dynamic multi-dimension identification technology while the project is mainly developed for government purposes.
- SelfKey is an open-source identity system built on the top of Ethereum [53]; consist of three main components which are identity wallet to help the identity owner to access his assets and documents, a marketplace to give user access to various services such as financial, immigration and cryptocurrency, and tokens to power the ecosystem, enable the trust and allow to exchange value.
- Uniquid provides an identity management system for the internet of things and automates access management protocol for the secure machine to machine connections. The solution is to give a device the ability to generate its own identity keypairs using pretty good privacy (PGP) [63] and cryptography principles while making the device able to apply for the needed signature without any centralized authority using blockchain.
6.2. Private and Consortium Blockchain Identity Solutions
- Verified.me: SecureKey and IBM are working together to create the first digital identity using blockchain for Canadian leading banks and financial institutions in Canada [56]. The solution will be built on the top of IBM blockchain service which uses the open-source blockchain Hyperledger fabric of Linux foundation. The solution is in testing face.
- Trust ID Network is the platform of Gemalto firm built for decentralized ID management using R3 Corda private blockchain. The aim of the solution is to put users in control of their identities using a mobile app that employs smart contracts, data models and storage mechanisms for increased security. In addition, the solution provides end-to-end data encryption, a zero-knowledge proof protocol for data minimization, and a UX-optimized identity wallet with biometrics for authentication, and ID document verification.
- Cambridge blockchain LLC initiated a solution for financial institutions to meet the strict data privacy rules by eliminating the redundant identity compliance checks and improving the user experience [58]. The solution encompasses four principles which are the user owns his personal data for better control, distributed identity authorities reached by a marketplace for identity services, transparent and secure solution using cryptography and blockchain technologies, and efficiency for all stockholders.
6.3. Blockchain Hybrid Identity Solutions
- Shocard is one of the earliest enterprise identity blockchain solutions [55]; it can be run on the top of any blockchain network as it has his own core service that contains blockchain API adapter. It provides multi-factor authentication where a user can log in to apps, devices, and cloud services without a need to a password or a username.
- Decentralized Identity Foundation (DIF) is an engineering-driven organization focused on developing the essential foundational standards to establish an open decentralized identity ecosystem for people, organizations, and devices and ensure the interoperability between all participants. The project is still in the early stage development and it encompasses more than 60 diverse global organizations and contributors working together to establish the ecosystem [64].
6.4. Benchmarks for Blockchain-Based Identity Management Systems
7. Challenges and Future Work
- Data standardization: the healthcare organization, government institutes, and insurance companies should consider and give a global format of what identity data should be shared in on or off the distributed ledger and define the size and the format that can be used in the system. A free-form submission of the data to the ledger may be cost-effective and will lead to the creation of unnecessarily large transactions that could harmfully impact the performance of the system. The healthcare policy-makers and different stakeholders should deeply collaborate with companies providing the technology to understand and facilitate the rise of the ecosystem.
- Access permission level: the self-sovereign identity can be implemented on the top of different DLT models, from one hand adopting a public ledger for a global system as it enable broader access may requires proof-of-work calculation which lead to a huge computing power to answer the real-time access for all entities, in the other hand implementing the solution on a private DLT to answer the need of the local healthcare system may requires trust among the participating entities and clear mechanism about reading and writing data to or from the ledger, despite both approaches may have a scalability limitation.
- Scalability limitation: the cost of operating the SSI on a Blockchain technology is not yet known, the famous existing permissionless ledgers like Ethereum and Bitcoin are facing a tradeoff between the transaction volumes and available computing power, for example, Bitcoin can only process around 250,000 transactions daily for around 10 million users, which is not acceptable for the case of real-time identity access. Yet the permissioned ledger can also face a computing power problem due to the poor participation in the network while providing the needed computing power from one side will give it a centralized owner.
- Adoption and incentives for participation: in order to create the promising DLT empower eHealth identity management system, the DLT will need the participation of many individuals to create the network of interconnected computers and provide the needed computing power to process the transaction and maintain the ledger, consequently an incentive approach or a reward system should be designed and tested for healthcare use case and encourage individuals to adopt the proposed approach. Similarly, organizations also should be part of the network and the decentralized system, for this reason, further support is needed to encourage all the stockholders to participate.
- IdM Consensus protocol: the most important element in DLT technology is the consensus protocol, as it provides a controlled and maintained ledger without the need of third parties services. Many consensus protocols are proposed for the case of the cryptocurrencies where for example the order of the event is important to solve the problem of double-spending without an arbitrator. Despite this, identity management may not face the issue of double-spending or an equivalent problem as the IdM paradigm is not transaction-based as currency, for this reason using the existing consensus protocols may not give the performance and the solution needed to support identity management.
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Ammenwerth, E.; Gräber, S.; Herrmann, G.; Bürkle, T.; König, J. Evaluation of health information systems—Problems and challenges. Int. J. Med. Inform. 2003, 71, 125–135. [Google Scholar] [CrossRef]
- Fabian, B.; Ermakova, T.; Junghanns, P. Collaborative and secure sharing of healthcare data in multi-clouds. Inf. Syst. 2015, 48, 132–150. [Google Scholar] [CrossRef]
- Viswanathan, H.; Chen, B.; Pompili, D. Research challenges in computation, communication, and context awareness for ubiquitous healthcare. IEEE Commun. Mag. 2012, 50, 92–99. [Google Scholar] [CrossRef]
- Underwood, S. Blockchain beyond bitcoin. Commun. ACM 2016, 59, 15–17. [Google Scholar] [CrossRef]
- Mühle, A.; Grüner, A.; Gayvoronskaya, T.; Meinel, C. A survey on essential components of a self-sovereign identity. Comput. Sci. Rev. 2018, 30, 80–86. [Google Scholar] [CrossRef]
- Torres, J.; Nogueira, M.; Pujolle, G. A survey on identity management for the future network. IEEE Commun. Surv. Tutor. 2013, 15, 787–802. [Google Scholar] [CrossRef]
- Ning, H.; Liu, X.; Ye, X.; Zhang, J.H.W.; Daneshmand, M. Edge computing based ID and nID combined identification and resolution scheme in IoT. IEEE Internet Things J. 2019. [Google Scholar] [CrossRef]
- Camp, J. Digital identity. IEEE Technol. Soc. Mag. 2004, 23, 34–41. [Google Scholar] [CrossRef]
- Hansen, M.; Berlich, P.; Camenisch, J.; Clauß, S.; Pfitzmann, A.; Waidner, M. Privacy-enhancing identity management. Inf. Secur. Tech. Rep. 2004, 9, 35–44. [Google Scholar] [CrossRef]
- Bertino, E.; Paci, F.; Shang, N. Digital identity protection-concepts and issues. In Proceedings of the 4th International Conference on Availability, Reliability and Security, Fukuoka, Japan, 16–19 March 2009; pp. 69–78. [Google Scholar]
- Ning, H.; Ye, X.; Bouras, M.A.; Wei, D.; Daneshmand, M. General Cyberspace: Cyberspace and Cyber-enabled Spaces. IEEE Internet Things J. 2018. [Google Scholar] [CrossRef]
- Cao, Y.; Yang, L. A survey of identity management technology. In Proceedings of the 2010 IEEE International Conference on Information Theory and Information Security (ICITIS), Beijing, China, 17–19 December 2010; pp. 287–293. [Google Scholar]
- Myllyniemi, A. Identity Management Systems: A Comparison of Current Solutions. TKK T-110.5290 Seminar on Network Security. 2006. Available online: https://pdfs.semanticscholar.org/3043/9b6e5dd36d390a7f2e78b7812a1d39d066ce.pdf (accessed on 15 January 2020).
- Mills, D.C.; Wang, K.; Malone, B.; Ravi, A.; Marquardt, J.; Badev, A.I.; Brezinski, T.; Fahy, L.; Liao, K.; Kargenian, V.; et al. Distributed ledger technology in payments, clearing, and settlement. FEDS Work. Pap. 2016. [Google Scholar] [CrossRef]
- Maull, R.; Godsiff, P.; Mulligan, C.; Brown, A.; Kewell, B. Distributed ledger technology: Applications and implications. Strateg. Chang. 2017, 26, 481–489. [Google Scholar] [CrossRef]
- Anjum, A.; Sporny, M.; Sill, A. Blockchain standards for compliance and trust. IEEE Cloud Comput. 2017, 4, 84–90. [Google Scholar] [CrossRef]
- Xu, X.; Weber, I.; Staples, M.; Zhu, L.; Bosch, J.; Bass, L.; Pautasso, C.; Rimba, P. A taxonomy of blockchain-based systems for architecture design. In Proceedings of the2017 IEEE International Conference on Software Architecture (ICSA), Gothenburg, Sweden, 3–7 April 2017; pp. 243–252. [Google Scholar]
- Lin, I.C.; Liao, T.C. A survey of blockchain security issues and challenges. IJ Netw. Secur. 2017, 19, 653–659. [Google Scholar]
- Andreev, R.; Andreeva, P.; Krotov, L.; Krotova, E. Review of blockchain technology: Types of blockchain and their application. Intellekt. Sist. Proizv. 2018, 16, 11–14. [Google Scholar] [CrossRef]
- Deshpande, A.; Stewart, K.; Lepetit, L.; Gunashekar, S. Distributed Ledger Technologies/Blockchain: Challenges, Opportunities and the Prospects for Standards; Overview Report; The British Standards Institution (BSI): London, UK, 2017. [Google Scholar]
- Kshetri, N. Can blockchain strengthen the internet of things? IT Prof. 2017, 19, 68–72. [Google Scholar] [CrossRef]
- Lin, C.; He, D.; Huang, X.; Khan, M.K.; Choo, K.K.R. A new transitively closed undirected graph authentication scheme for blockchain-based identity management systems. IEEE Access 2018, 6, 28203–28212. [Google Scholar] [CrossRef]
- Lee, J.H. BIDaaS: Blockchain based ID as a service. IEEE Access 2017, 6, 2274–2278. [Google Scholar] [CrossRef]
- Alsayed Kassem, J.; Sayeed, S.; Marco-Gisbert, H.; Pervez, Z.; Dahal, K. DNS-IdM: A blockchain identity management system to secure personal data sharing in a network. Appl. Sci. 2019, 9, 2953. [Google Scholar] [CrossRef]
- Lim, S.Y.; Fotsing, P.T.; Almasri, A.; Musa, O.; Kiah, M.L.M.; Ang, T.F.; Ismail, R. Blockchain technology the identity management and authentication service disruptor: A survey. Int. J. Adv. Sci. Eng. Inf. Technol. 2018, 8, 1735–1745. [Google Scholar] [CrossRef]
- Zhu, X.; Badr, Y. A Survey on Blockchain-based Identity Management Systems for the Internet of Things. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018; pp. 1568–1573. [Google Scholar]
- Pashalidis, A.; Mitchell, C.J. A taxonomy of single sign-on systems. In Proceedings of the Australasian Conference on Information Security and Privacy, Wollongong, Australia, 9–11 July 2003; pp. 249–264. [Google Scholar]
- Jøsang, A.; Fabre, J.; Hay, B.; Dalziel, J.; Pope, S. Trust requirements in identity management. In Proceedings of the 2005 Australasian Workshop on Grid Computing and e-Research; Australian Computer Society, Inc.: Darlinghurst, Australia, 2005; Volume 44, pp. 99–108. [Google Scholar]
- Huang, J.; Nicol, D. A calculus of trust and its application to PKI and identity management. In Proceedings of the 8th Symposium on Identity and Trust on the Internet (IDtrust ’09), Association for Computing Machinery, New York, NY, USA, 14–16 April 2009; pp. 23–37. [Google Scholar]
- Neuman, B.C.; Ts’o, T. Kerberos: An authentication service for computer networks. IEEE Commun. Mag. 1994, 32, 33–38. [Google Scholar] [CrossRef]
- Bhargav-Spantzel, A.; Camenisch, J.; Gross, T.; Sommer, D. User centricity: A taxonomy and open issues. J. Comput. Secur. 2007, 15, 493–527. [Google Scholar] [CrossRef]
- Shim, S.S.; Bhalla, G.; Pendyala, V. Federated identity management. Computer 2005, 38, 120–122. [Google Scholar] [CrossRef]
- Hughes, J.; Maler, E. Security Assertion Markup Language (saml) v2.0 Technical Overview; OASIS SSTC Working Draft sstc-saml-tech-overview-2.0-draft-08; OASIS: Burlington, MA, USA, 2005; pp. 29–38. [Google Scholar]
- Alsaleh, M.; Adams, C. Enhancing consumer privacy in the liberty alliance identity federation and web services frameworks. In Proceedings of the International Workshop on Privacy Enhancing Technologies, Cambridge, UK, 28–30 June 2006; pp. 59–77. [Google Scholar]
- Morgan, R.L.; Cantor, S.; Carmody, S.; Hoehn, W.; Klingenstein, K. Federated security: The shibboleth approach. Educ. Q. 2004, 27, 12–17. [Google Scholar]
- Cameron, K. The Laws of Identity; Microsoft Corp: Redmond, WA, USA, 2005. [Google Scholar]
- Respect Network Corporation. Respect Trust Framework. Available online: https://www.oixnet.org/registry/respect-network/ (accessed on 17 October 2019).
- W3C Group. Decentralized Identifiers (DIDs) v0.11. Available online: https://w3c-ccg.github.io/did-spec/ (accessed on 17 October 2019).
- Christopher, A. The Path to Self-Sovereign Identity. Available online: http://www.lifewithalacrity.com/2016/04/the-path-to-self-soverereign-identity.html (accessed on 22 October 2019).
- Ritz, D.; Althauser, C.; Wilson, K. Connecting Health Information Systems for Better Health-Leveraging. Seattle: Joint Learning Network for Universal Health Coverage. eBook. 2014. Available online: https://jln1.pressbooks.com/ (accessed on 11 January 2020).
- W3C Group. Verifiable Claims Use Cases. Available online: https://www.w3.org/TR/verifiable-claims-use-cases/ (accessed on 17 October 2019).
- Domenech, M.C.; Comunello, E.; Wangham, M.S. Identity management in e-Health: A case study of web of things application using OpenID connect. In Proceedings of the 2014 IEEE 16th International Conference on e-Health Networking, Applications and Services (Healthcom), Natal, Brazil, 15–18 October 2014; pp. 219–224. [Google Scholar]
- Appari, A.; Johnson, M.E. Information security and privacy in healthcare: Current state of research. Int. J. Internet Enterp. Manag. 2010, 6, 279–314. [Google Scholar] [CrossRef]
- Mahmoud, R.; Yousuf, T.; Aloul, F.; Zualkernan, I. Internet of things (IoT) security: Current status, challenges and prospective measures. In Proceedings of the 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 14–16 December 2015; pp. 336–341. [Google Scholar]
- Andersson, T. The medical leadership challenge in healthcare is an identity challenge. Leadersh. Health Serv. 2015, 28, 83–99. [Google Scholar] [CrossRef]
- Zyskind, G.; Nathan, O. Decentralizing privacy: Using blockchain to protect personal data. In Proceedings of the Security and Privacy Workshops (SPW), San Jose, CA, USA, 21–22 May 2015; pp. 180–184. [Google Scholar]
- Dunphy, P.; Petitcolas, F.A. A first look at identity management schemes on the blockchain. arXiv 2018, arXiv:1801.03294. [Google Scholar] [CrossRef]
- Lundkvist, C.; Heck, R.; Torstensson, J.; Mitton, Z.; Sena, M. Uport: A Platform for Self-Sovereign Identity. Available online: http://blockchainlab.com/pdf/uPort_whitepaper_DRAFT20161020.pdf (accessed on 8 October 2019).
- Sovrin Foundation. Sovrin: A Protocol and Token for Self- Sovereign Identity and Decentralized Trust; Whitepaper; Sovrin Foundation: Provo, UT, USA, 2018. [Google Scholar]
- Identity.com Inc. Decentralized Identity Verification Ecosystem. Available online: https://www.identity.com/ (accessed on 11 January 2020).
- Blockstack, Inc. Blockstack. Available online: https://blockstack.org/ (accessed on 15 October 2019).
- Thekey, Inc. Thekey. Available online: https://www.thekey.vip/ (accessed on 15 October 2019).
- Selfkey. SelfKey Identity Ecosystem. Available online: https://selfkey.org/ (accessed on 15 October 2019).
- UniquID Inc. Blockchain Identity and Access Management. Available online: https://uniquid.com/ (accessed on 15 October 2019).
- ShoCard. ShoCard: The Premier Blockchain-Based Mobile Identity Platform. Available online: https://shocard.com/ (accessed on 17 October 2019).
- SecureKey Technologies. Verified.Me. Available online: https://verified.me/ (accessed on 15 October 2019).
- Decentralized Identity Foundation. The Rising Tide of Decentralized Identity—Decentralized Identity Foundation. Available online: https://medium.com/decentralized-identity/the-rising-tide-of-decentralized-identity-2e163e4ec663 (accessed on 15 October 2019).
- Cambridge Blockchain. Identity Compliance Solutions. Available online: https://www.cambridge-blockchain.com/ (accessed on 15 October 2019).
- uPort Inc. uPort.me. Available online: https://www.uport.me/ (accessed on 15 October 2019).
- Sovrin Foundation. Sovrin Identity. Available online: https://sovrin.org/ (accessed on 15 October 2019).
- Evernym, Inc. Evernym. Available online: https://www.evernym.com/ (accessed on 15 October 2019).
- NEO, Inc. NEO Smart Economy. Available online: https://neo.org/ (accessed on 15 October 2019).
- Garfinkel, S. PGP: Pretty Good Privacy; O’Reilly Media, Inc.: Sebastopol, MA, USA, 1995. [Google Scholar]
- DIF. Decentralized identity Foundation. Available online: https://identity.foundation/ (accessed on 15 October 2019).
- Dhamija, R.; Dusseault, L. The seven flaws of identity management: Usability and security challenges. IEEE Secur. Priv. 2008, 6, 24–29. [Google Scholar] [CrossRef]
- Peterson, G. Introduction to identity management risk metrics. IEEE Secur. Priv. 2006, 4, 88–91. [Google Scholar] [CrossRef]
- Geyer, F.; Kinkelin, H.; Leppelsack, H.; Liebald, S.; Scholz, D.; Carle, G.; Schupke, D. Performance perspective on private distributed ledger technologies for industrial networks. In Proceedings of the 2019 International Conference on Networked Systems (NetSys), München, Germany, 18–21 March 2019; pp. 1–8. [Google Scholar]
- Wang, R.; Ye, K.; Xu, C.Z. Performance benchmarking and optimization for blockchain systems: A survey. In Proceedings of the International Conference on Blockchain, Seoul, Korea, 14–17 May 2019; pp. 171–185. [Google Scholar]
- Hileman, G.; Rauchs, M. Global Blockchain Benchmarking Study; Cambridge Centre for Alternative Finance, University of Cambridge: Cambridge, UK, 2017; Volume 122. [Google Scholar]
| Principles | Abstract |
|---|---|
| Autonomy | Is the individual independent from identity vendors? Individuals must be independent of any identity provider or a central governor. |
| Authority | Can the individual have full control of his identity? Individuals must have complete power to manage their identities. |
| Availability | Can an individual have full access to his own data? Individuals must have full permission to gain access to their own data anytime anywhere. |
| Approval | Can the individual voluntary approve the use of his identity? Individuals must voluntary agree and approve requests before using their identity. |
| Confidentiality | Can the individual provide his identity with minimal disclosure of data? Individuals should share only the needed credentials with a minimal disclosure |
| Tenacity | Can the identity live with the individual as long as possible? Individuals identities must be persistent as long as possible |
| Interoperability | Can the individual identity exchange data with any system or service globally? Individual Identities should be universal and widely used by any entities |
| Principles | Centralized Models | Decentralized Models | ||
|---|---|---|---|---|
| Centralized Identity | Federated Identity | User Centric Identity | ||
| Autonomy | No | No | No | Yes |
| Authority | Low | Low | Medium | High |
| Availability | Low | Medium | Medium | High |
| Approval | No | No | Yes | Yes |
| Confidentiality | Low | Low | Medium | High |
| Tenacity | No | No | No | Yes |
| Interoperability | No | Yes | Yes | Yes |
| Key Players | User Roles | Role Definition |
|---|---|---|
| Healthcare regulators | Issuer | Regulators can create claims about the authorized clinics, hospitals, and care providers. |
| Inspector | Regulators can verify the care providers’ certificates and patients’ assurance validity. | |
| Holder | Regulators can control and hold different claim about the other key players. | |
| Industry representatives | Issuer | They can create claims about their own products and services to care providers or consumers. |
| Inspector | They can verify claims coming from healthcare providers and consumers about particular products. | |
| Holder | They can control and hold claims about operations and product selling records. | |
| Healthcare providers | Issuer | Care providers can create claims about healthcare consumers and it can be stored as healthcare records. |
| Inspector | Care providers can inspect and verify claims of their own patients and industry representative. | |
| Holder | Care providers can control and hold claims like working certificate. | |
| Healthcare consumers | Issuer | Consumers can create claims about their own health condition using devices and gadgets. |
| Inspector | Consumers can verify claims coming from care provider for example in a case of telemedicine and remote care. | |
| Holder | Consumers can control and hold claims such as medical records. |
| Name | Scenario | Key Players | Requirements |
|---|---|---|---|
| Healthcare data exchange | Visiting a different health clinic in a different stat after feeling sick when traveling for a vacation or business. The patient will aim to provide only the requested and required information that verifies his identity by delivering an identity credential without disclosing other information like social security number or marital status, besides he wants to revoke the access to his information after a set of time | -Consumers -Regulators | Interoperability is the main aspect to exchange data between different healthcare institutions in different states and countries. |
| Online pharmacy | An online pharmacy may receive a patient prescription from a local clinic. The pharmacy needs to verify the identity of the physician and his ability to write a prescription, as well as the identity of the patient and his insurance coverage before picking up his medication | -Consumers -Care providers -Industry representatives | Automate the essential cases and prevent a manual intervention for better security while providing strong access, authentication, and authorization mechanisms. |
| Payment | A company started an employee assistance program with the aim of providing health insurance and treatment coverage to all employees where the company has branches. This health plan requires access to the employees’ medical records who received a treatment, which will be delivered from the healthcare providers in different locations in order to calculate the budget of the services provided. | -Consumers -Industry representatives -Care providers | Data standard is mandatory for exchanging the information between the key players. |
| Research project | A research project on children is being conducted in a double-blind study and needs access to new data sets for children younger than the age of 13. After authorizing the access to the data, the IRB will review the project and apply research protocols at the medical center where the investigation is located. The research lab asked the principals if they can have access to the data for another 6 months and use the data collected for another study purpose which is not related to the research protocol reviewed in the beginning. | -Consumers -Industry representatives -Regulators | Anonymity is the key feature to share the data of a group of consumers without disclosing their identity. |
| Identity Project | DLT Model | DLT Platform | Identity Model | Launch Date | Open Source | Consensus Algorithm | Industry Target |
|---|---|---|---|---|---|---|---|
| uPort [48] | Public Permissionless | Ethereum | Self-sovereign | January 2017 | Yes | PoW (Ethash) | - |
| Sovrin [49] | Public Permissioned | Hyperledger Indy | Self-sovereign | July 2017 | Yes | Redundant Byzantine Fault Tolerance (RBFT) | - |
| Identity.com [50] | Public Permissionless | Ethereum | Decentralized Trusted Identity | Later | Yes | PoW (Ethash) | - |
| Evernym [49] | Public Permissionless | IOTA | Self-sovereign | Later | Yes | Consensus achieved by Confirmation confidence | Finance, Education, Healthcare, Commerce, Travel |
| Blockstack [51] | Public Permissionless | Bitcoin | Self-sovereign | 2013 | Yes | PoW (Proof-of-Work) | Software |
| Thekey [52] | Public Permissioned | NEO | - | November 2014 | No | Delegated Byzantine Fault Tolerance (dBFT) | Software |
| Selfkey [53] | Public Permissionless | Ethereum | Self-sovereign | 2016 | Yes | PoW (Ethash) | Financial services |
| Uniquid [54] | Public Permissionless | Bitcoin | - | October 2015 | Yes | PoW (Ethash) | IoT |
| ShoCard [55] | Can support all DLT models | - | Decentralized Trusted Identity | May 2015 | No | Not specified | Enterprises, financial institutions, airlines, website and app login |
| Sovrin [49] | Public Permissioned | Hyperledger Indy | Self-sovereign | July 2017 | Yes | Redundant Byzantine Fault Tolerance (RBFT) | - |
| verified.me [56] | Private Permissioned | Hyperledger Fabric | Self-sovereign | Late 2017 | No | Byzantine fault tolerance (BFT) | Banking |
| Trust ID Network | Private Permissioned | R3 Corda | Self-sovereign | September 2018 | No | Consensus over state validity and uniqueness | Banking and financial institutions |
| DIF [57] | Can support all DLT models | - | Self-sovereign | Later | Yes | Not specified | All industries |
| Cambridge blockchain LLC [58] | Private Permissioned | - | Decentralized Trusted Identity | 2015 | No | - | Financial institutions |
| Metrics | Explanation |
|---|---|
| Time spent provisioning and de-provisioning users | Provision and de-provisioning is the core functionality of any identity systems, managing the user accounts from registration to authentication and updates in a short time is a mandatory metric for mature identity management systems. Delays of those operations or failed Logins may lead to a failure of the solution [65]. |
| Unique accounts per user | The more s user creates several accounts the more he is to forget about the credentials. A user may create more than one account for different purpose especially when the process of recovering the username or the password is hard. Single Sign-On (SSO) platforms are mainly to solve this problem [65]. |
| Password reset volume per month | Many companies and applications require changing their password periodically to ensure strong security systems. A mature IdM should answer to the requirement and makes it easy for users to change their password is a fast and secure ways [66]. |
| Number of uncorrelated accounts | Many accounts may not have owners due to changing accounts, upgrading the system, or a user may leave his account open without using it. This situation may lead to a security threat. A mature system my monitor such accounts to reduce the unnecessary risks [66]. |
| Read latency | Reading from the ledger is the most performed action in blockchain networks which is the time between sending the reading request until the replay is received. Improving the reading latency will help to optimize the authentication time [67]. |
| Read throughput | The metric of defining how many reading operations are performed in a period of time. This metric is not really relevant for blockchain network but important for blockchain-based identity solution as most solutions relay to blockchain performance, not to the identity system needed [67]. |
| Transaction latency | Blockchain transactions are time-consuming as the consensus process is used to make the transaction valid across the network. Transaction with long delays may cause a system failure as is not providing a good user experience [68]. |
| Transaction throughput | It’s the rate of valid transaction committed in a set of time. Mainly this metric is performed in every node of the blockchain network to have accurate results and to identify the issues if any. In the blockchain-based identity system transaction throughput is connected to provisioning and de-provisioning operations [68]. |
| Actual production usage | Knowing the real system usage will help to specify the metrics. For instance, in the identity management systems, provisioning and authentication are the most performed operations that it matches in the blockchain the reading and the transaction requests. The more we understand the system the more we easily and accurately identify the metrics and perform evaluations [69]. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bouras, M.A.; Lu, Q.; Zhang, F.; Wan, Y.; Zhang, T.; Ning, H. Distributed Ledger Technology for eHealth Identity Privacy: State of The Art and Future Perspective. Sensors 2020, 20, 483. https://doi.org/10.3390/s20020483
Bouras MA, Lu Q, Zhang F, Wan Y, Zhang T, Ning H. Distributed Ledger Technology for eHealth Identity Privacy: State of The Art and Future Perspective. Sensors. 2020; 20(2):483. https://doi.org/10.3390/s20020483
Chicago/Turabian StyleBouras, Mohammed Amine, Qinghua Lu, Fan Zhang, Yueliang Wan, Tao Zhang, and Huansheng Ning. 2020. "Distributed Ledger Technology for eHealth Identity Privacy: State of The Art and Future Perspective" Sensors 20, no. 2: 483. https://doi.org/10.3390/s20020483
APA StyleBouras, M. A., Lu, Q., Zhang, F., Wan, Y., Zhang, T., & Ning, H. (2020). Distributed Ledger Technology for eHealth Identity Privacy: State of The Art and Future Perspective. Sensors, 20(2), 483. https://doi.org/10.3390/s20020483






