ARIES: A Novel Multivariate Intrusion Detection System for Smart Grid
Abstract
1. Introduction
2. Related Work and Contributions
2.1. Related Work
2.2. Contributions
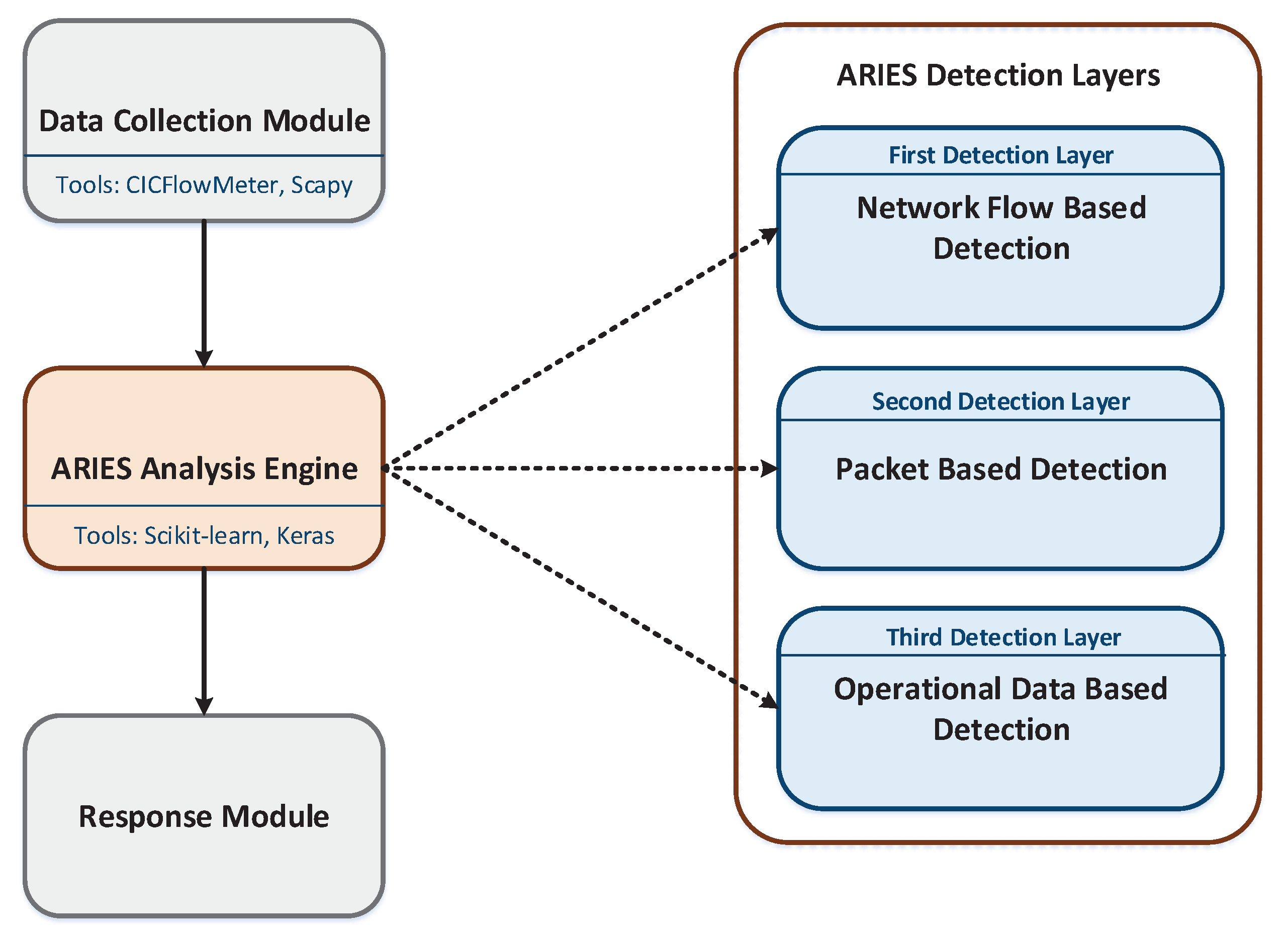
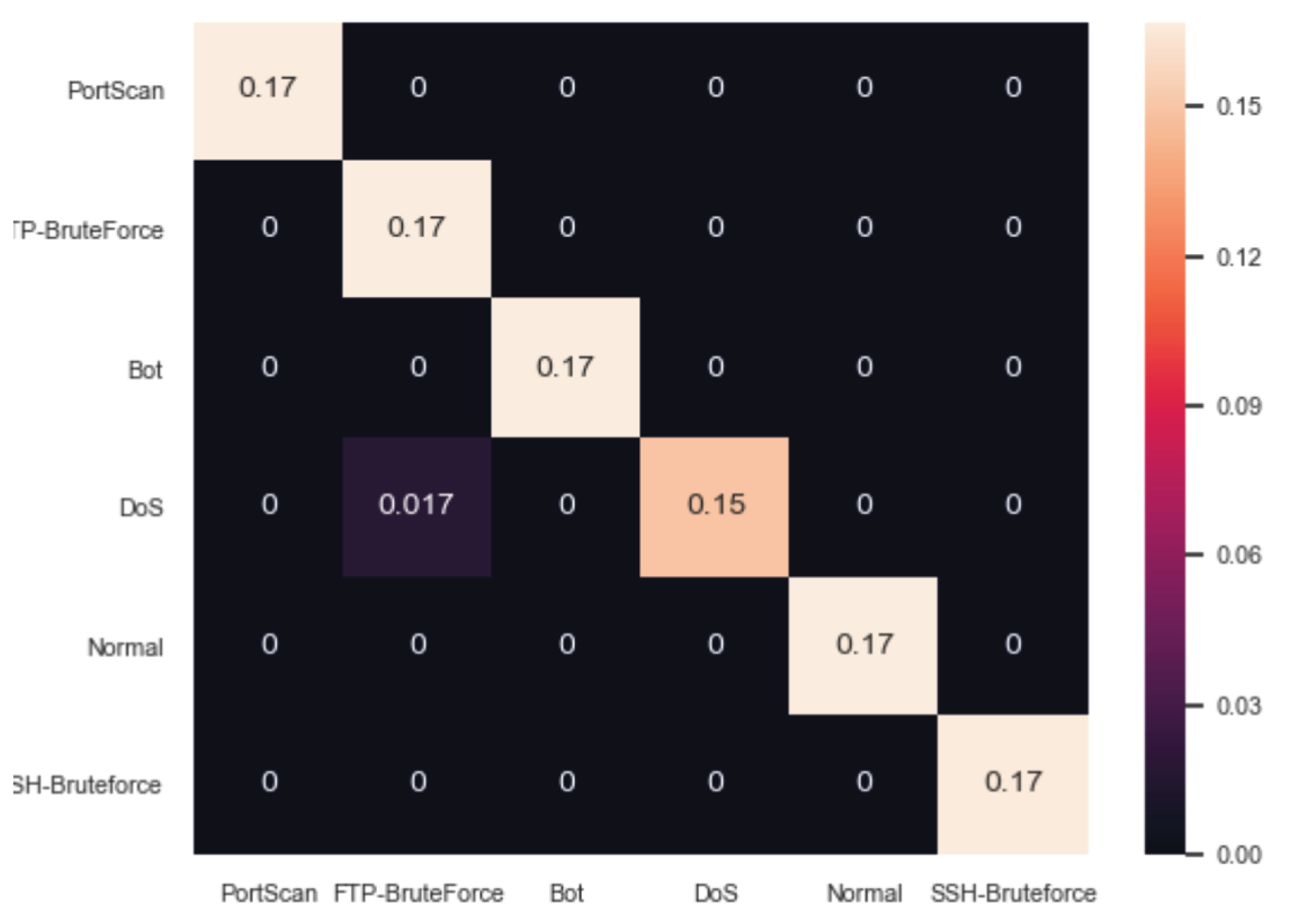
- Providing ARIES, a three detection layer IDS system for SG: The proposed IDS consists of three detection layers: (a) network flow-based detection, (b) packet-based detection, and (c) operational data-based detection. The first layer focuses on network flow statistic features and can detect (a) DoS attacks, (b) SSH brute force attacks, (c) FTP brute force attacks, (d) port scanning attacks and (e) bots. The second layer is devoted to the Modbus/TCP packets by analysing their attributes. Thus, Modbus/TCP-related attacks, such as unauthorised Modbus commands and function code enumeration can be recognised. Finally, the last layer detects anomalies upon operational data that can originate either via an electricity-related disturbance or a cybersecurity policy violation.
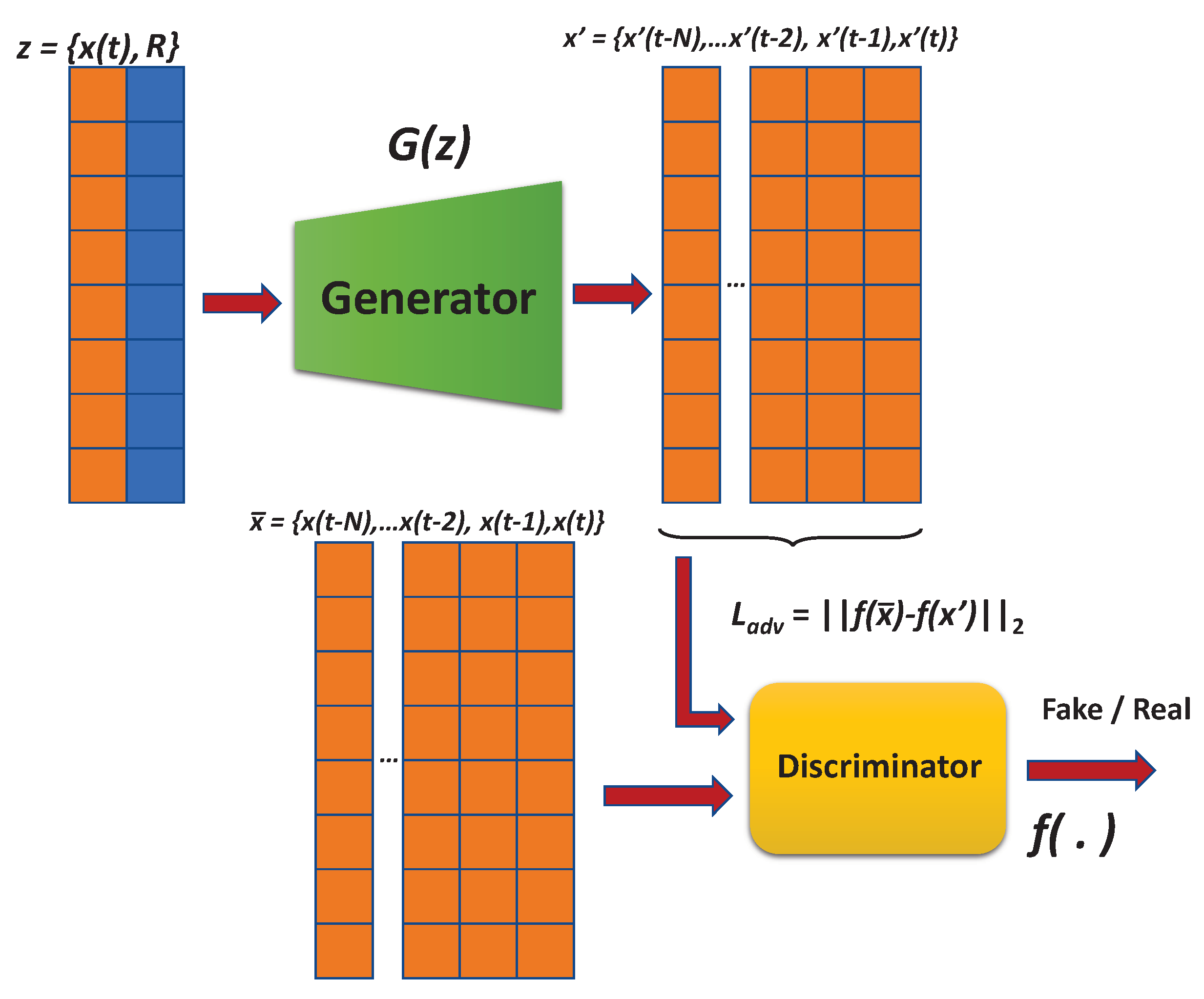
- ARIES GAN: The main novelty of this paper is the development of a GAN network with novel error minimization functions, considering the reconstruction difference. Furthermore, a novel reformed conditional input was suggested, consisting of random noise and the signal features at any given time instance. Based on the evaluation results, the proposed GAN network overcomes the efficacy of other ML methods.
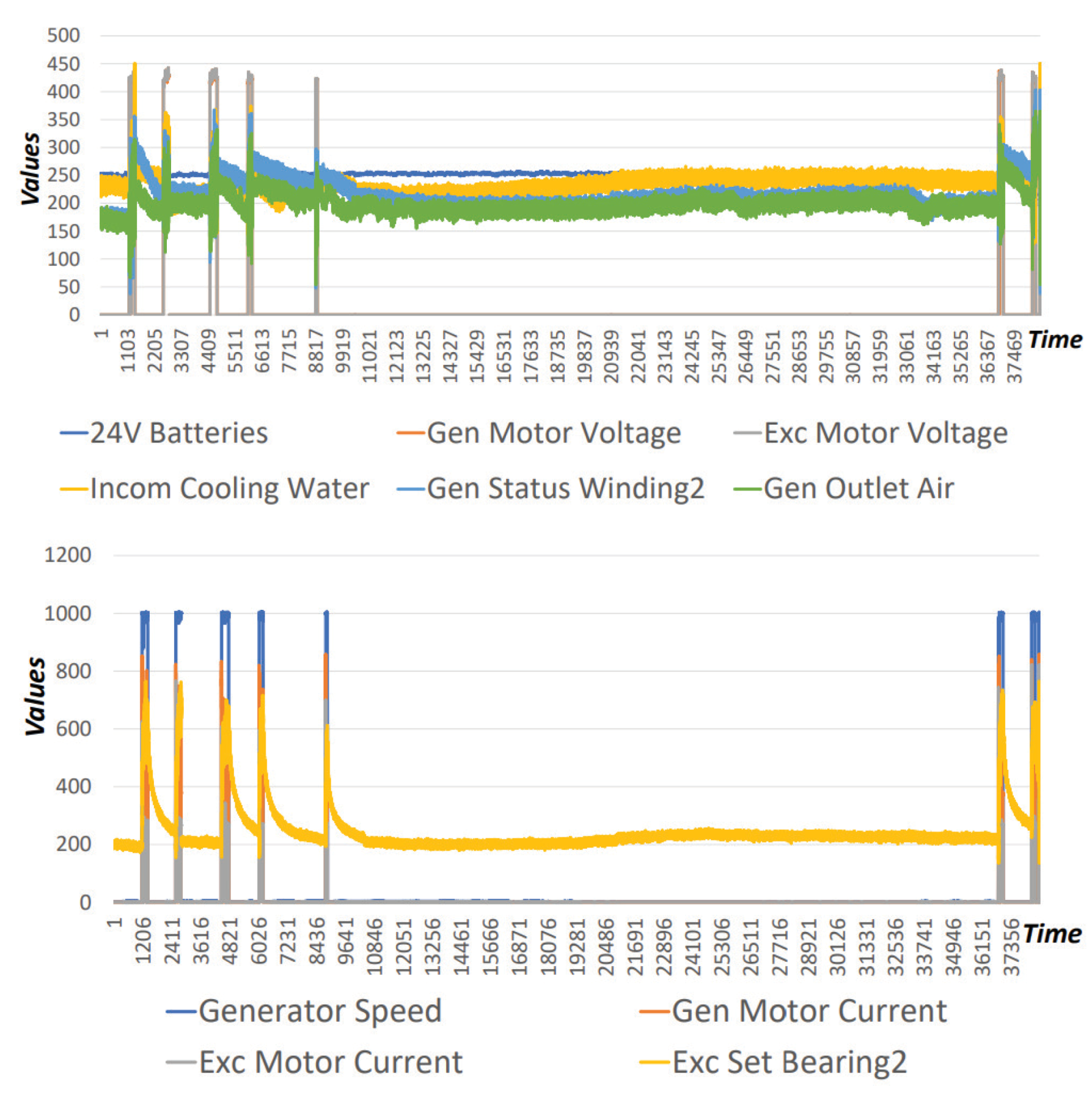
- Development and Evaluation based on Real Data: In contrast to similar works that use ML techniques, the proposed IDS was developed and evaluated utilising real normal data coming from a power plant in Greece. Thus, the ARIES applicability and validity was evaluated under real operational conditions, ensuring the detection performance.
- Evaluating a plethora of ML/DL methods: Multiple ML/DL methods were evaluated for each detection layer in terms of Accuracy, True Positive Rate (TPR), FPR and the F1 score. Each detection layer adopts the ML/DL model originating from the method with the highest F1 score.
3. ARIES Architecture
3.1. Data Collection Module
3.2. ARIES Analysis Engine
3.3. Response Module
4. ARIES GAN
5. Evaluation Analysis
5.1. Evaluation Environment
5.2. Datasets
- Flow Duration: Identifies the duration of a network flow in microseconds.
- TotLen Fwd Pkts: Identifies the total size of packets to the forward direction.
- Fwd Pkt Len Mean: Denotes the average size of the packets to the forward direction.
- Fwd Pkt Len Mean: Denotes the average size of the packets to the forward direction.
- Bwd Pkt Len Std: Indicates the standard deviation size of the packets to the backward direction.
- Flow IAT Std: Implies the standard deviation time between two packets transmitted to the forward direction.
- Bwd Pkts/s: Indicates the number of the packets sent to the backward direction per second.
- Subflow Bwd Pkts: Denotes the average number of packets in a subflow to the backward direction.
- Init Bwd Win Bytes: Identifies the number of bytes transmitted in an initial window to the backward direction.
- Active Mean: Indicates the average time of a network flow, which remained active before becoming idle.
- TCP Len: Indicates the size of the TCP frame.
- Transaction ID: The Transaction ID is used for transaction pairing when multiple Modbus messages are sent during the same TCP connection by a client without waiting for a prior response.
- Protocol ID: The Protocol ID is always equal to zero for Modbus and other values are reserved for possible extensions.
- Len: Indicates the length of the Unit ID, Fcode and the Modbus payload data.
- Unit ID: Unit ID is used for serial bridging to identify a remote server on a non-Transmission Control Protocol/Internet Protocol (TCP/IP) network.
- Fcode: Indicates the Modbus function code. The function codes of Modbus correspond to specific operations that are defined in detail in [54].
- Starting Address: Denotes the starting address of coils or registers where the values will be requested.
- Byte Count: Specifies the size of the response Modbus packets.
5.3. Comparative ML/DL Methods
5.4. Evaluation Results
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| ABOD | Angle-Based Outlier Detection |
| ADM | Anomaly Detection Model |
| AMI | Advanced Metering Infrastructure |
| APTs | Advanced Persistent Threats |
| ARIES | smArt gRid Intrusion dEtection System |
| ARIES GAN | ARIES Generative Adversarial Network |
| BIF | Backward Influence Factor |
| DAG | Directed Acyclic Graph |
| DARPA | Defence Advanced Research Projects Agency |
| DCD | Dynamic Correlation Graph |
| dDCA | deterministic Dendritic Cell Algorithm |
| DDoS | Distributed Denial of Service Attacks |
| DL | Deep Learning |
| DNN | Deep Neural Network |
| DNP3 | Distributed Network Protocol 3 |
| DoS | Denial of Service |
| FN | False Negatives |
| FP | False Positives |
| FPR | False Positive Rate |
| FTP | File Transfer Protocol |
| GAN | Generative Adversarial Network |
| GOOSE | Generic Object Oriented Substation Events |
| HANs | Home Area Networks |
| ICT | Information and Communication Technology |
| IEC | International Electrotechnical Commission |
| IDM | Intrusion Detection Model |
| IDS | Intrusion Detection System |
| IoT | Internet of Things |
| LDA | Linear Discriminant Analysis |
| LOF | Local Outlier Factor |
| MCD | Minimum Covariance Determinant |
| MiTM | Man-in-The-Middle |
| ML | Machine Learning |
| MMS | Manufacturing Message Specification |
| MTU | Master Terminal Unit |
| NANs | Neighbour Area Networks |
| NIDS | Network Intrusion Detection System |
| OSSIM | Open Source SIEM |
| PCA | Principal Component Analysis |
| pcap | Packet capture |
| PLCs | Programmable Logic Controllers |
| RANs | Residential Area Networks |
| RoC | Receiver Operating Characteristics |
| RTUs | Remote Terminal Units |
| SCADA | Supervisory Control and Data Acquisition |
| SDN | Software-Defined Networking |
| SG | Smart Grid |
| SIEM | Security Information and Event Management System |
| SPAN | Switched Port Analyser |
| SSH | Secure Shell |
| SVM | Support Vector Machine |
| TCP | Transmission Control Protocol |
| TCP/IP | Transmission Control Protocol/ Internet Protocol |
| TN | True Negatives |
| TP | True Positives |
| TPR | True Positive Rate |
| TTP | Techniques and Procedures |
| User | Datagram Protocol |
| WANs | Wide Area Networks |
References
- Farhangi, H. The path of the smart grid. IEEE Power Energy Mag. 2009, 8, 18–28. [Google Scholar] [CrossRef]
- Tan, S.; De, D.; Song, W.; Yang, J.; Das, S.K. Survey of Security Advances in Smart Grid: A Data Driven Approach. IEEE Commun. Surv. Tutor. 2017, 19, 397–422. [Google Scholar] [CrossRef]
- Peng, C.; Sun, H.; Yang, M.; Wang, Y. A Survey on Security Communication and Control for Smart Grids Under Malicious Cyber Attacks. IEEE Trans. Syst. Man Cybern. Syst. 2019, 49, 1554–1569. [Google Scholar] [CrossRef]
- Pliatsios, D.; Sarigiannidis, P.; Lagkas, T.; Sarigiannidis, A.G. A Survey on SCADA Systems: Secure Protocols, Incidents, Threats and Tactics. IEEE Commun. Surv. Tutor. 2020, 22, 1942–1976. [Google Scholar] [CrossRef]
- Grammatikis, P.I.R.; Sarigiannidis, P.G.; Moscholios, I.D. Securing the Internet of Things: Challenges, threats and solutions. Internet Things 2019, 5, 41–70. [Google Scholar] [CrossRef]
- Ghosal, A.; Conti, M. Key Management Systems for Smart Grid Advanced Metering Infrastructure: A Survey. IEEE Commun. Surv. Tutor. 2019, 21, 2831–2848. [Google Scholar] [CrossRef]
- Hassan, M.U.; Rehmani, M.H.; Chen, J. Differential Privacy Techniques for Cyber Physical Systems: A Survey. IEEE Commun. Surv. Tutor. 2020, 22, 746–789. [Google Scholar] [CrossRef]
- Kumar, P.; Lin, Y.; Bai, G.; Paverd, A.; Dong, J.S.; Martin, A. Smart Grid Metering Networks: A Survey on Security, Privacy and Open Research Issues. IEEE Commun. Surv. Tutor. 2019, 21, 2886–2927. [Google Scholar] [CrossRef]
- Cleveland, F. Iec tc57 wg15: Iec 62351 Security Standards for the Power System Information Infrastructure. Available online: https://www.iec.ch/dyn/www/f?p=103:7:0::::FSP_ORG_ID,FSP_LANG_ID:1273,25 (accessed on 2 June 2020).
- Zenati, H.; Foo, C.S.; Lecouat, B.; Manek, G.; Chandrasekhar, V.R. Efficient gan-based anomaly detection. arXiv 2018, arXiv:1802.06222. [Google Scholar]
- Lin, Z.; Shi, Y.; Xue, Z. Idsgan: Generative adversarial networks for attack generation against intrusion detection. arXiv 2018, arXiv:1809.02077. [Google Scholar]
- Bendiab, G.; Grammatikakis, K.P.; Koufos, I.; Kolokotronis, N.; Shiaeles, S. Advanced Metering Infrastructures: Security Risks and Mitigation. In Proceedings of the 15th International Conference on Availability, Reliability and Security (ARES’20), Dublin, Ireland, 25–28 August 2020; Association for Computing Machinery: New York, NY, USA, 2020. [Google Scholar] [CrossRef]
- Radoglou-Grammatikis, P.; Sarigiannidis, P.; Liatifis, T.; Apostolakos, T.; Oikonomou, S. An Overview of the Firewall Systems in the Smart Grid Paradigm. In Proceedings of the 2018 Global Information Infrastructure and Networking Symposium (GIIS), Thessaloniki, Greece, 23–25 October 2018; pp. 1–4. [Google Scholar]
- Rios, E.; Rego, A.; Iturbe, E.; Higuero, M.; Larrucea, X. Continuous Quantitative Risk Management in Smart Grids Using Attack Defense Trees. Sensors 2020, 20, 4404. [Google Scholar] [CrossRef] [PubMed]
- Odelu, V.; Das, A.K.; Wazid, M.; Conti, M. Provably Secure Authenticated Key Agreement Scheme for Smart Grid. IEEE Trans. Smart Grid 2018, 9, 1900–1910. [Google Scholar] [CrossRef]
- Kolokotronis, N.; Shiaeles, S.; Bellini, E.; Charalambous, L.; Kavallieros, D.; Gkotsopoulou, O.; Pavue, C.; Bellini, A.; Sargsyan, G. Cyber-trust: The shield for IoT cyber-attacks. In Resilience and Hybrid Threats; IOS Press: Amsterdam, The Netherlands, 2019; pp. 76–93. [Google Scholar]
- Radoglou-Grammatikis, P.I.; Sarigiannidis, P.G. Securing the Smart Grid: A Comprehensive Compilation of Intrusion Detection and Prevention Systems. IEEE Access 2019, 7, 46595–46620. [Google Scholar] [CrossRef]
- Maziku, H.; Shetty, S.; Nicol, D.M. Security risk assessment for SDN-enabled smart grids. Comput. Commun. 2019, 133, 1–11. [Google Scholar] [CrossRef]
- Igbe, O.; Darwish, I.; Saadawi, T. Deterministic dendritic cell algorithm application to smart grid cyber-attack detection. In Proceedings of the 2017 IEEE 4th International Conference on Cyber Security and Cloud Computing (CSCloud), New York, NY, USA, 26–28 June 2017; pp. 199–204. [Google Scholar]
- Manso, P.; Moura, J.; Serrão, C. SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks. Information 2019, 10, 106. [Google Scholar] [CrossRef]
- Rehmani, M.H.; Davy, A.; Jennings, B.; Assi, C. Software Defined Networks-Based Smart Grid Communication: A Comprehensive Survey. IEEE Commun. Surv. Tutor. 2019, 21, 2637–2670. [Google Scholar] [CrossRef]
- Chaabouni, N.; Mosbah, M.; Zemmari, A.; Sauvignac, C.; Faruki, P. Network Intrusion Detection for IoT Security Based on Learning Techniques. IEEE Commun. Surv. Tutor. 2019, 21, 2671–2701. [Google Scholar] [CrossRef]
- Ujjan, R.M.A.; Pervez, Z.; Dahal, K. Snort Based Collaborative Intrusion Detection System Using Blockchain in SDN. In Proceedings of the 2019 13th International Conference on Software, Knowledge, Information Management and Applications (SKIMA), Island of Ulkulhas, Maldives, 26–28 August 2019; pp. 1–8. [Google Scholar]
- Fontes, R.R.; Afzal, S.; Brito, S.H.; Santos, M.A.; Rothenberg, C.E. Mininet-WiFi: Emulating software-defined wireless networks. In Proceedings of the 2015 11th International Conference on Network and Service Management (CNSM), Barcelona, Spain, 9–13 November 2015; pp. 384–389. [Google Scholar]
- Asadollahi, S.; Goswami, B.; Sameer, M. Ryu controller’s scalability experiment on software defined networks. In Proceedings of the 2018 IEEE International Conference on Current Trends in Advanced Computing (ICCTAC), Beijing, China, 16–18 August 2018; pp. 1–5. [Google Scholar]
- Alsaeedi, M.; Mohamad, M.M.; Al-Roubaiey, A.A. Toward Adaptive and Scalable OpenFlow-SDN Flow Control: A Survey. IEEE Access 2019, 7, 107346–107379. [Google Scholar] [CrossRef]
- Milajerdi, S.M.; Gjomemo, R.; Eshete, B.; Sekar, R.; Venkatakrishnan, V. Holmes: Real-time apt detection through correlation of suspicious information flows. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 19–23 May 2019; pp. 1137–1152. [Google Scholar]
- Alshamrani, A.; Myneni, S.; Chowdhary, A.; Huang, D. A Survey on Advanced Persistent Threats: Techniques, Solutions, Challenges, and Research Opportunities. IEEE Commun. Surv. Tutor. 2019, 21, 1851–1877. [Google Scholar] [CrossRef]
- Chekired, D.A.; Khoukhi, L.; Mouftah, H.T. Fog-Based Distributed Intrusion Detection System Against False Metering Attacks in Smart Grid. In Proceedings of the ICC 2019—2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar]
- Omoniwa, B.; Hussain, R.; Javed, M.A.; Bouk, S.H.; Malik, S.A. Fog/Edge Computing-Based IoT (FECIoT): Architecture, Applications, and Research Issues. IEEE Internet Things J. 2019, 6, 4118–4149. [Google Scholar] [CrossRef]
- Xie, Y.; Feng, D.; Hu, Y.; Li, Y.; Sample, S.; Long, D. Pagoda: A Hybrid Approach to Enable Efficient Real-time Provenance Based Intrusion Detection in Big Data Environments. IEEE Trans. Dependable Secur. Comput. 2018. [Google Scholar] [CrossRef]
- Muniswamy-Reddy, K.K.; Holland, D.A.; Braun, U.; Seltzer, M.I. Provenance-aware storage systems. In Proceedings of the Usenix Annual Technical Conference, General Track, Boston, MA, USA, 30 May–3 June 2006; pp. 43–56. [Google Scholar]
- Gehani, A.; Tariq, D. SPADE: Support for provenance auditing in distributed environments. In Proceedings of the ACM/IFIP/USENIX International Conference on Distributed Systems Platforms and Open Distributed Processing, Montreal, QC, Canada, 3–7 December 2012; pp. 101–120. [Google Scholar]
- Pohly, D.J.; McLaughlin, S.; McDaniel, P.; Butler, K. Hi-Fi: Collecting high-fidelity whole-system provenance. In Proceedings of the 28th Annual Computer Security Applications Conference, Orlando, FL, USA, 3–7 December 2012; pp. 259–268. [Google Scholar]
- Bates, A.; Tian, D.J.; Butler, K.R.; Moyer, T. Trustworthy whole-system provenance for the Linux kernel. In Proceedings of the 24th USENIX Security Symposium (USENIX Security 15), Washington, DC, USA, 12–14 August 2015; pp. 319–334. [Google Scholar]
- Xie, Y.; Feng, D.; Tan, Z.; Zhou, J. Unifying intrusion detection and forensic analysis via provenance awareness. Future Gener. Comput. Syst. 2016, 61, 26–36. [Google Scholar] [CrossRef]
- Albanese, M.; Erbacher, R.F.; Jajodia, S.; Molinaro, C.; Persia, F.; Picariello, A.; Sperlì, G.; Subrahmanian, V. Recognizing unexplained behavior in network traffic. In Network Science and Cybersecurity; Springer: Berlin/Heidelberg, Germany, 2014; pp. 39–62. [Google Scholar]
- Zhang, K.; Luo, S.; Xin, Y.; Zhu, H.; Chen, Y. Online Mining Intrusion Patterns from IDS Alerts. Appl. Sci. 2020, 10, 2983. [Google Scholar] [CrossRef]
- Chakraborty, T.; Jajodia, S.; Katz, J.; Picariello, A.; Sperli, G.; Subrahmanian, V. FORGE: A fake online repository generation engine for cyber deception. IEEE Trans. Dependable Secur. Comput. 2019. [Google Scholar] [CrossRef]
- Meena, G.; Choudhary, R.R. A review paper on IDS classification using KDD 99 and NSL KDD dataset in WEKA. In Proceedings of the 2017 International Conference on Computer, Communications and Electronics (Comptelix), Jaipur, India, 1–2 July 2017; pp. 553–558. [Google Scholar]
- Ring, M.; Wunderlich, S.; Scheuring, D.; Landes, D.; Hotho, A. A survey of network-based intrusion detection data sets. Comput. Secur. 2019, 86, 147–167. [Google Scholar] [CrossRef]
- Lashkari, A.H.; Draper-Gil, G.; Mamun, M.S.I.; Ghorbani, A.A. Characterization of Tor Traffic using Time based Features. In Proceedings of the ICISSP, Porto, Portugal, 19–21 February 2017; pp. 253–262. [Google Scholar]
- Draper-Gil, G.; Lashkari, A.H.; Mamun, M.S.I.; Ghorbani, A.A. Characterization of encrypted and vpn traffic using time-related. In Proceedings of the 2nd International Conference on Information Systems Security and Privacy (ICISSP), Rome, Italy, 19–21 February 2016; pp. 407–414. [Google Scholar]
- Kobayashi, T.H.; Batista, A.B.; Brito, A.M.; Motta Pires, P.S. Using a packet manipulation tool for security analysis of industrial network protocols. In Proceedings of the 2007 IEEE Conference on Emerging Technologies and Factory Automation (EFTA 2007), Patras, Greece, 25–28 September 2007; pp. 744–747. [Google Scholar]
- Suaboot, J.; Fahad, A.; Tari, Z.; Grundy, J.; Mahmood, A.N.; Almalawi, A.; Zomaya, A.Y.; Drira, K. A Taxonomy of Supervised Learning for IDSs in SCADA Environments. ACM Comput. Surv. 2020, 53, 1–37. [Google Scholar] [CrossRef]
- Berman, D.S.; Buczak, A.L.; Chavis, J.S.; Corbett, C.L. A survey of deep learning methods for cyber security. Information 2019, 10, 122. [Google Scholar] [CrossRef]
- Radoglou-Grammatikis, P.; Sarigiannidis, P.; Efstathopoulos, G.; Karypidis, P.A.; Sarigiannidis, A. DIDEROT: An Intrusion Detection and Prevention System for DNP3-Based SCADA Systems. In Proceedings of the 15th International Conference on Availability, Reliability and Security (ARES’20), Dublin, Ireland, 25–28 August 2020; Association for Computing Machinery: New York, NY, USA, 2020. [Google Scholar] [CrossRef]
- Hariri, S.; Kind, M.C.; Brunner, R.J. Extended isolation forest. arXiv 2018, arXiv:1811.02141. [Google Scholar] [CrossRef]
- Coppolino, L.; D’Antonio, S.; Formicola, V.; Romano, L. Integration of a System for Critical Infrastructure Protection with the OSSIM SIEM Platform: A dam case study. In Proceedings of the International Conference on Computer Safety, Reliability, and Security, Naples, Italy, 19–22 September 2011; pp. 199–212. [Google Scholar]
- Zarzosa, S.G. D2.1 In-Depth Analysis of SIEMs Extensibility. Available online: http://disiem-project.eu/wp-content/uploads/2017/03/D2.1.pdf (accessed on 2 June 2020).
- Miano, S.; Bertrone, M.; Risso, F.; Bernal, M.V.; Lu, Y.; Pi, J. Securing Linux with a faster and scalable iptables. ACM Sigcomm Comput. Commun. Rev. 2019, 49, 2–17. [Google Scholar] [CrossRef]
- Sharafaldin, I.; Lashkari, A.H.; Ghorbani, A.A. Toward generating a new intrusion detection dataset and intrusion traffic characterization. In Proceedings of the ICISSP, Madeira, Portugal, 22–24 January 2018; pp. 108–116. [Google Scholar]
- Usman, M.; Jan, M.A.; He, X.; Chen, J. A survey on representation learning efforts in cybersecurity domain. ACM Comput. Surv. 2019, 52, 1–28. [Google Scholar] [CrossRef]
- MODBUS Organization. Modbus Application Protocol Specification V1.1b. Available online: https://modbus.org/docs/Modbus_Application_Protocol_V1_1b.pdf (accessed on 2 June 2020).
- Hosmer, D.W., Jr.; Lemeshow, S.; Sturdivant, R.X. Applied Logistic Regression; John Wiley & Sons: Hoboken, NJ, USA, 2013; Volume 398. [Google Scholar]
- Tharwat, A.; Gaber, T.; Ibrahim, A.; Hassanien, A.E. Linear discriminant analysis: A detailed tutorial. AI Commun. 2017, 30, 169–190. [Google Scholar]
- Radoglou-Grammatikis, P.I.; Sarigiannidis, P.G. An Anomaly-Based Intrusion Detection System for the Smart Grid Based on CART Decision Tree. In Proceedings of the 2018 Global Information Infrastructure and Networking Symposium (GIIS), Thessaloniki, Greece, 23–25 October 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Berrar, D. Bayes’ theorem and naive Bayes classifier. In Encyclopedia of Bioinformatics and Computational Biology: ABC of Bioinformatics; ELSEVIER: Amsterdam, The Netherlands, 2018; Volume 403. [Google Scholar]
- Awad, M.; Khanna, R. Support Vector Machines for Classification. In Efficient Learning Machines: Theories, Concepts, and Applications for Engineers and System Designers; Apress: Berkeley, CA, USA, 2015; pp. 39–66. [Google Scholar] [CrossRef]
- Louppe, G. Understanding Random Forests: From Theory to Practice. Ph.D. Thesis, University of Liège, Liege, Belgium, 2014. [Google Scholar] [CrossRef]
- Radoglou-Grammatikis, P.I.; Sarigiannidis, P.G. Flow anomaly based intrusion detection system for Android mobile devices. In Proceedings of the 2017 6th International Conference on Modern Circuits and Systems Technologies (MOCAST), Thessaloniki, Greece, 4–6 May 2017; pp. 1–4. [Google Scholar]
- Schapire, R.E. Explaining adaboost. In Empirical Inference; Springer: Berlin/Heidelberg, Germany, 2013; pp. 37–52. [Google Scholar]
- Tharwat, A. Linear vs. quadratic discriminant analysis classifier: A tutorial. Int. J. Appl. Pattern Recognit. 2016, 3, 145–180. [Google Scholar] [CrossRef]
- Kriegel, H.P.; Schubert, M.; Zimek, A. Angle-based outlier detection in high-dimensional data. In Proceedings of the 14th ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, Las Vegas, NV, USA, 24–27 August 2008; pp. 444–452. [Google Scholar]
- Fernandes, G., Jr.; Carvalho, L.F.; Rodrigues, J.J.; Proença, M.L., Jr. Network anomaly detection using IP flows with principal component analysis and ant colony optimization. J. Netw. Comput. Appl. 2016, 64, 1–11. [Google Scholar] [CrossRef]
- Hardin, J.; Rocke, D.M. Outlier detection in the multiple cluster setting using the minimum covariance determinant estimator. Comput. Stat. Data Anal. 2004, 44, 625–638. [Google Scholar] [CrossRef]
- Paulauskas, N.; Bagdonas, Ą.F. Local outlier factor use for the network flow anomaly detection. Secur. Commun. Netw. 2015, 8, 4203–4212. [Google Scholar] [CrossRef]



| ML Method | Accuracy | TPR | FPR | F1 |
|---|---|---|---|---|
| Logistic Regression | 0.922 | 0.767 | 0.046 | 0.767 |
| LDA | 0.882 | 0.648 | 0.070 | 0.648 |
| Decision Tree Classifier | 0.994 | 0.982 | 0.003 | 0.982 |
| Naive Bayes | 0.917 | 0.751 | 0.049 | 0.751 |
| SVM RBF | 0.841 | 0.523 | 0.095 | 0.523 |
| SVM Linear | 0.802 | 0.406 | 0.118 | 0.406 |
| Random Forest | 0.990 | 0.970 | 0.005 | 0.970 |
| MLP | 0.909 | 0.728 | 0.054 | 0.728 |
| AdaBoost | 0.846 | 0.538 | 0.092 | 0.538 |
| Quadratic Discriminant Analysis | 0.722 | 0.166 | 0.166 | 0.166 |
| Dense DNN Relu | 0.984 | 0.954 | 0.009 | 0.954 |
| Dense DNN Tanh | 0.965 | 0.897 | 0.020 | 0.897 |
| ML Method | Accuracy | TPR | FPR | F1 |
|---|---|---|---|---|
| ABOD | 0.944 | 1 | 0.101 | 0.942 |
| Isolation Forest | 0.938 | 0.999 | 0.111 | 0.937 |
| PCA | 0.545 | 0 | 0 | 0 |
| LOF | 0.944 | 1 | 0.101 | 0.942 |
| MCD | 0.493 | 0.001 | 0.097 | 0.002 |
| Autoencoder | 0.9514 | 1 | 0.0963 | 0.9533 |
| ML Method | Accuracy | TPR | FPR | F1 |
|---|---|---|---|---|
| ABOD | 0.581 | 0.993 | 0.522 | 0.487 |
| Isolation Forest | 0.917 | 0.751 | 0.049 | 0.751 |
| PCA | 0.745 | 0.978 | 0.312 | 0.606 |
| MCD | 0.733 | 0.210 | 0.135 | 0.240 |
| LOF | 0.733 | 0.210 | 0.135 | 0.240 |
| Autoencoder | 0.746 | 0.978 | 0.311 | 0.607 |
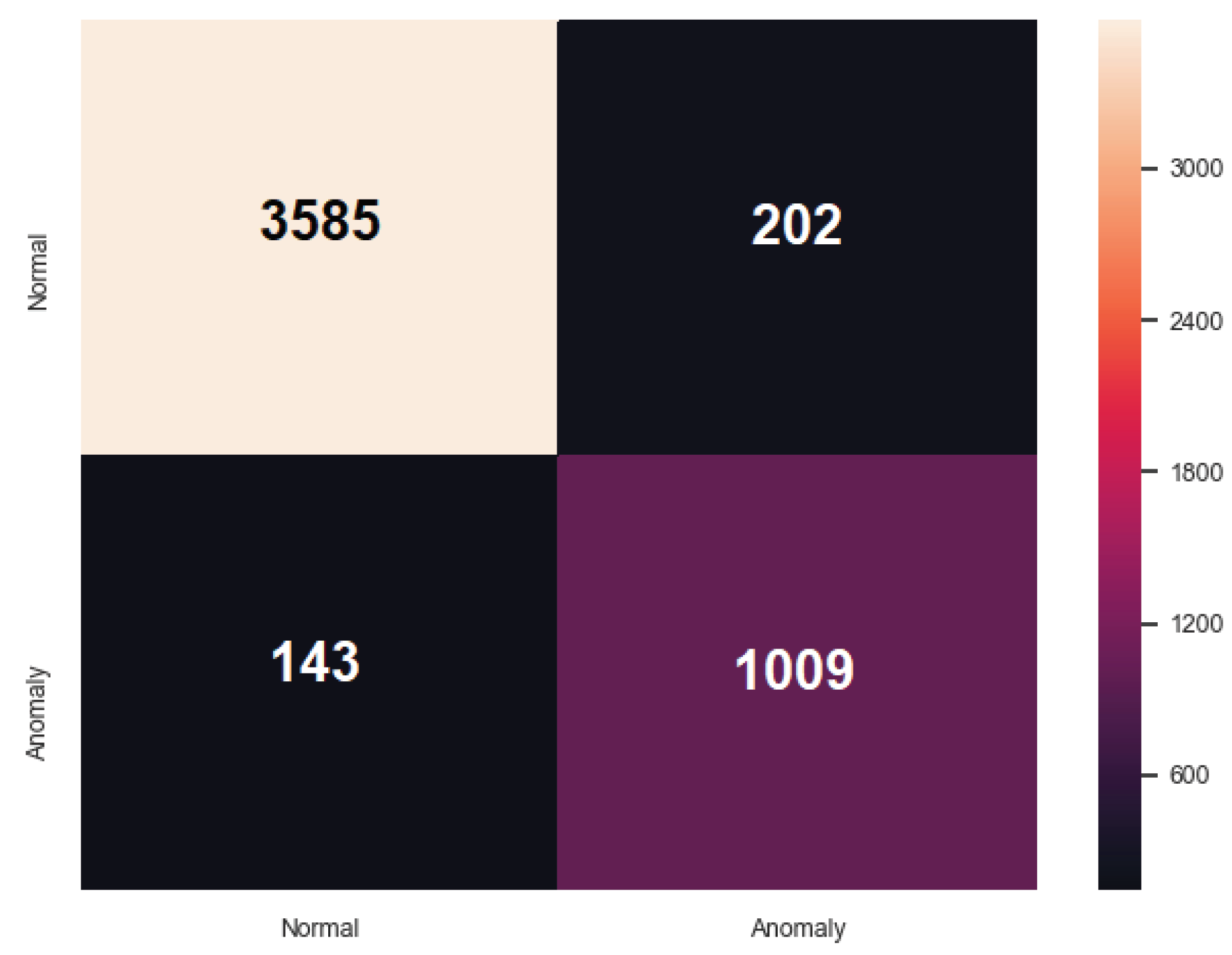
| ML Method | Accuracy | TPR | FPR | F1 |
|---|---|---|---|---|
| ABOD | 0.692 | 0.989 | 0.397 | 0.600 |
| Isolation Forest | 0.813 | 0.960 | 0.231 | 0.705 |
| PCA | 0.851 | 0.982 | 0.187 | 0.755 |
| MCD | 0.715 | 0.299 | 0.158 | 0.329 |
| LOF | 0.829 | 0.992 | 0.220 | 0.730 |
| Autoencoder | 0.851 | 0.982 | 0.188 | 0.755 |
| ARIES GAN | 0.930 | 0.875 | 0.053 | 0.853 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Radoglou Grammatikis, P.; Sarigiannidis, P.; Efstathopoulos, G.; Panaousis, E. ARIES: A Novel Multivariate Intrusion Detection System for Smart Grid. Sensors 2020, 20, 5305. https://doi.org/10.3390/s20185305
Radoglou Grammatikis P, Sarigiannidis P, Efstathopoulos G, Panaousis E. ARIES: A Novel Multivariate Intrusion Detection System for Smart Grid. Sensors. 2020; 20(18):5305. https://doi.org/10.3390/s20185305
Chicago/Turabian StyleRadoglou Grammatikis, Panagiotis, Panagiotis Sarigiannidis, Georgios Efstathopoulos, and Emmanouil Panaousis. 2020. "ARIES: A Novel Multivariate Intrusion Detection System for Smart Grid" Sensors 20, no. 18: 5305. https://doi.org/10.3390/s20185305
APA StyleRadoglou Grammatikis, P., Sarigiannidis, P., Efstathopoulos, G., & Panaousis, E. (2020). ARIES: A Novel Multivariate Intrusion Detection System for Smart Grid. Sensors, 20(18), 5305. https://doi.org/10.3390/s20185305







