As APT attack alerts are critical to be correlated generating the APT attack scenarios, we focus on deploying the Alert Instance Correlation module on cloud data center to accomplish APT attack scenarios reconstruction. The APT attack usually performs through a few steps with characteristics of persistent, targeted and aiming at the specific object. The final mission of APT is obtaining confidential data in the IoT systems. To achieve this goal, the attack process usually contains complex multistep. Alert instances which are extracted in edge servers and cloud data center belong to different APT attack step,
Table 4 summarizes the matchup between APT attack scenario steps and alert instances.
The first step (Intelligence Gathering) contains some passive process and the corresponding alerts are not readily be detected by network traffic sensors. The fourth step (Lateral Movement) is internal traffic within the edge devices while the APT alerts are detected from the inbound and outbound traffic. Based by the above facts, we only correlate the APT alert instances generated in Step 2, Step 3, Step 5 and Step 6 of an APT attack scenario.
The AICM outputs two kinds of correlated alert instance clusters:
and
. The
will be generated when AICM has correlated a full APT attack scenario during the correlation duration, which has every step of an APT attack scenario. To be more specific, the
include four alert instances, which generated within different step of a full APT attack scenario. We can correlate 9 alert instance cluster patterns based on
Table 4 and the APT attack life cycle. These alert instance cluster patterns can be formalized represented as:
The
will be produced when AICM has correlated two or three rather than all steps of an APT attack scenario during the correlation duration. In this fractional correlated alert cluster, one or two step alert instances are missing. To be more specific, the
includes two types of alert clusters: sub_steps_correlated_two_steps_alert_cluster and sub_steps_correlated_three_steps_ alert_cluster. We can correlate 64 alert instance cluster patterns based on
Table 4 and the APT attack life cycle. These alert instance cluster patterns can be formalized represented as:
4.2.2. Alert Instance Cluster (AIC)
The alert instance cluster module (AIC) allocates the most similar alert instances into a certain cluster. An APT full steps scenario or sub-steps scenario can present an alert instance cluster. Each alert instance presents a disparate attack step. The AIC module gets the AIF products as input and stores the alert instances during a correlation duration. The AIC module tests the possibility of clustering as soon as a new alert instance arrives based on the APT attack scenario characteristics, so as to it is restricted by the following two rules:
Rule 1. Alert instances, which belong to the same APT attack step, should not be allocated into the same cluster.
Rule 2. APT attack alert instances should trigger within the correlation duration and alert instances order should in accord to the APT attack life cycle.
Formally,
and
stand for the trigger time of four alert instances respectively, which belong to four attack steps of the APT scenario. They only if comply with the following criteria that can be clustered into one cluster:
All the generated alert instance clusters are presented as a directed graph and scattered alert instances are linked by directed edges based on the similarity. Then the clusters will be consumed by the correlation indexing module. Each cluster is consisted of maximum of four ordered alert instances and recorded in an instance_cluster_dataset (ICD) which is deployed on the cloud data center.
When a new alert instance arrives in AIC module, we firstly check it belongs to which APT attack step. Based on the different alert instance type, AIC chooses different operation options. We have the conclusion: Point of entry (P) which is the second step of an APT attack scenario is the first detectable attack step. When AIC gets an alert instance it generates a new cluster and allocates at instance_1, which is recorded in ICD.
When AIC gets an alert instance
(namely: Domain_flux_instance or Ip_instance or Ssl_instance) AIC inquires the similarity degrees
between
and
from the cyber situation ontology construction module.
are the instances which are already recorded in ICD in the order
instance_1 of the existing clusters. The
and
are different sub-classes of class alert, then
and
can be treated as
. Therefore, it is feasible to calculate the value of
. AIC adds the
to the order
instance_2 of cluster which not only has the largest value of
but also meet the flowing two conditions in Equations (9) and (10). Then we can get the correlated instance of
:
, and send the
back to the cyber situation ontology construction module for later instance similarity degree calculation. If there are no suitable alert instances
to be chosen, AIC will generate a new cluster and allocate
to
instance_2 and store it in ICD.
When AIC get an alert instance
(namely: Scan_instance) AIC inquires the similarity degrees
between
and
from the cyber situation ontology construction module.
are the instances which are already stored in ICD at the order instance_2 of the existing clusters. AIC adds the
to the order instance_3 of cluster which not only has the largest value of
but also meets the flowing two conditions in Equations (11) and (12). If the chosen
is the first instance of the cluster, the above two conditions should be changed by Equations (13) and (14). Then we can get the correlated instance of
:
, and send the
back to the cyber situation ontology construction module for later instance similarity degree calculation. If there are no suitable alert instances
to be chosen, AIC will generate a new cluster and allocate
to instance_3 and store it in ICD.
When AIC get an alert instance
(namely: Tor_intance) AIC inquires the similarity degrees
between
and
from the cyber situation ontology construction module.
are the instances which are already stored in ICD at the order
instance_3 of each existing cluster. AIC adds the
to the order
instance_4 of cluster which not only has the largest value of
but also meet the flowing two conditions in Equations (15) and (16). If the chosen
is the first instance of the cluster the above two conditions should be changed by Equations (17) and (18). If the chosen
is the second instance of the cluster the above two conditions should be changed by Equations (19) and (20). Then we can get the correlated instance of
:
, and send the
back to the cyber situation ontology construction module for later instance similarity degree calculation. If there are no suitable alert instances
to be chosen, it means the
has no relationships with any clusters in the ICD, AIC will discard the
.
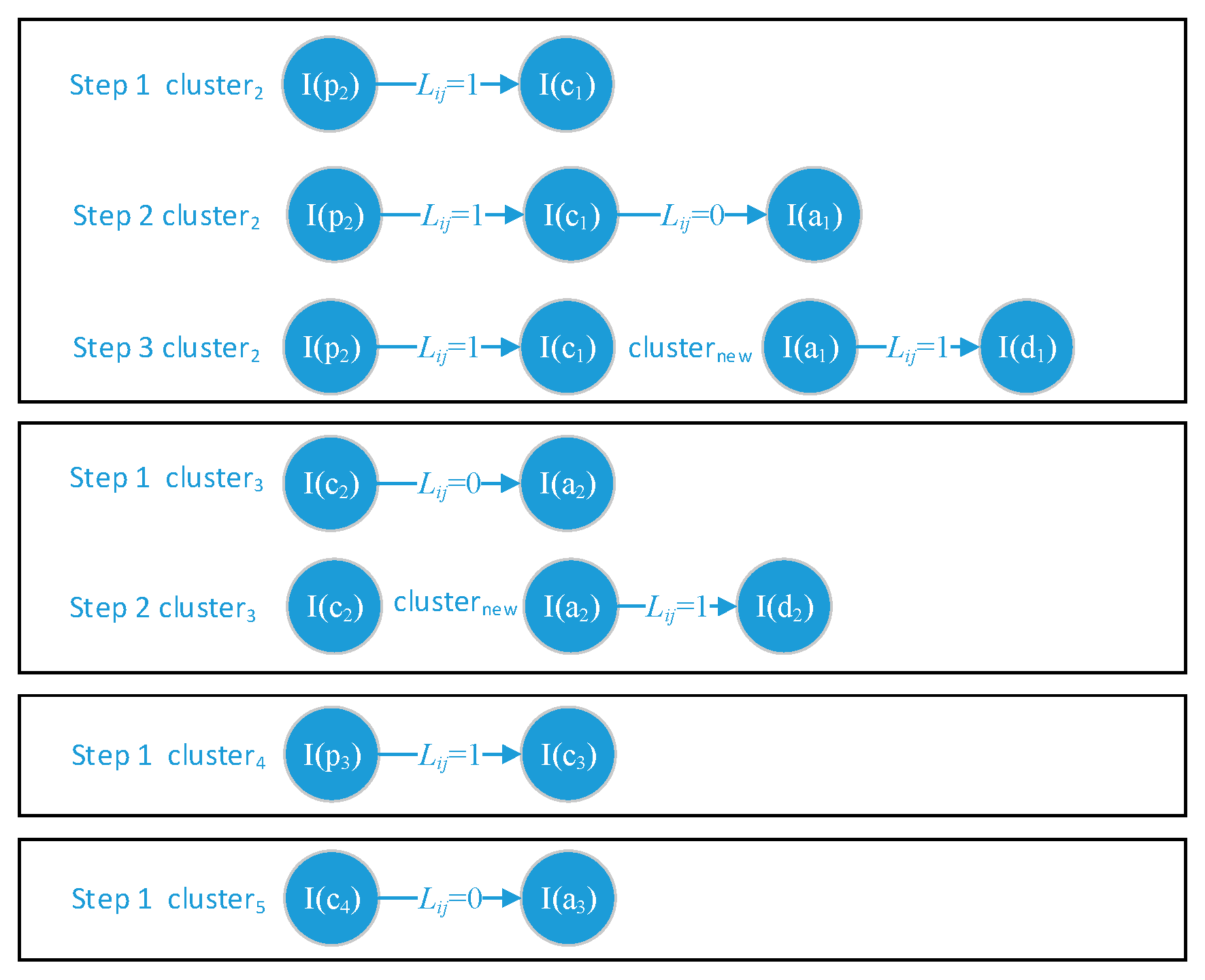
In general, we correlate the alert instance to the most similar prior-step alert instance. A correlation example is shown in
Figure 4.
4.2.3. APT Attack Scenario (AAS)
APT attack scenario (AAS) module confirms the alert instances which belonging to the same alert instance cluster whether or not can construct a full or sectional APT attack scenario in the IoT system based on edge computing architecture. As we knew each ATP alert instance cluster is constructed incrementally, it has the opportunity that later received alert instance reforms the previously correlated alert instances. To address this problem, we add a parameter
on the correlated links between every two alert instances which belong to the same cluster. The parameter
consists of two values: 1 or 0. When alert instance_i and instance_j have identical
Victim_HostIP the
will be set as 1; otherwise, the
will be set as 0. The ASS will face four states of
during the correlation. The four states and corresponding operations are shown in
Figure 5, and we describe them as follows:
: APT alert instances can belong to a certain AAS.
: The latest two alert instances are much more similar than the prior two alert instances. Then the first link should be disconnected and construct a new instance cluster contains the latest two alert instances waiting for the coming correlation.
No evidence can trigger the disconnection, just waiting for the coming instances.
No evidence can trigger the disconnection, just waiting for the coming instances.
We also introduce a parameter
LinkNum to check the clustered APT alert instances and discard the uncorrelated alert instances.
LinkNum can be formulated as follows:
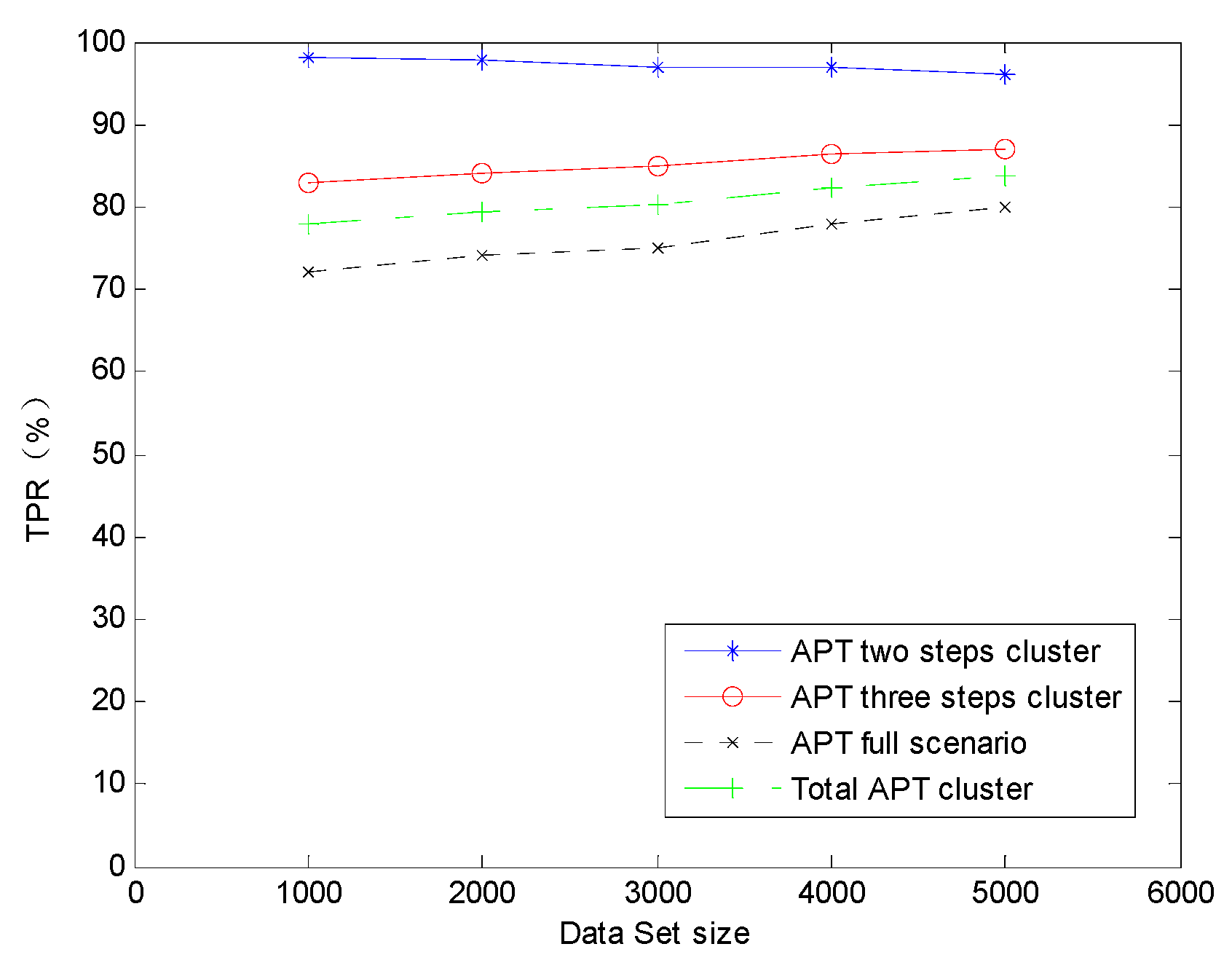
. APT alert instances in the cluster have no effect and cause with each other; they cannot construct an APT attack scenario.
. APT alert instances in the cluster can generate a correlation between two alert instances and they can construct a with two steps.
. APT alert instances in the cluster can generate correlations between three alert instances and they can construct a with three steps.
. APT alert instances in the cluster can generate a correlation between four alert instances. They can construct a
and be presented as an APT attack scenario.
The vectors are the sectional output of cyber situation comprehension to be used in future cyber situation projection. In the condition that alert instance is absent, the value of and can be set as 0. Meanwhile, the LICM modules which are deployed on edge servers can get the attribute Victim_HostIp from the AIC module which is deployed on cloud data center to determine the correlation range of logs which are generated in edge devices.