An Automatic User Activity Analysis Method for Discovering Latent Requirements: Usability Issue Detection on Mobile Applications
Abstract
1. Introduction
2. Related Work
2.1. Usability Testing Method for Mobile Applications
2.2. Self-Adaptive Software Framework
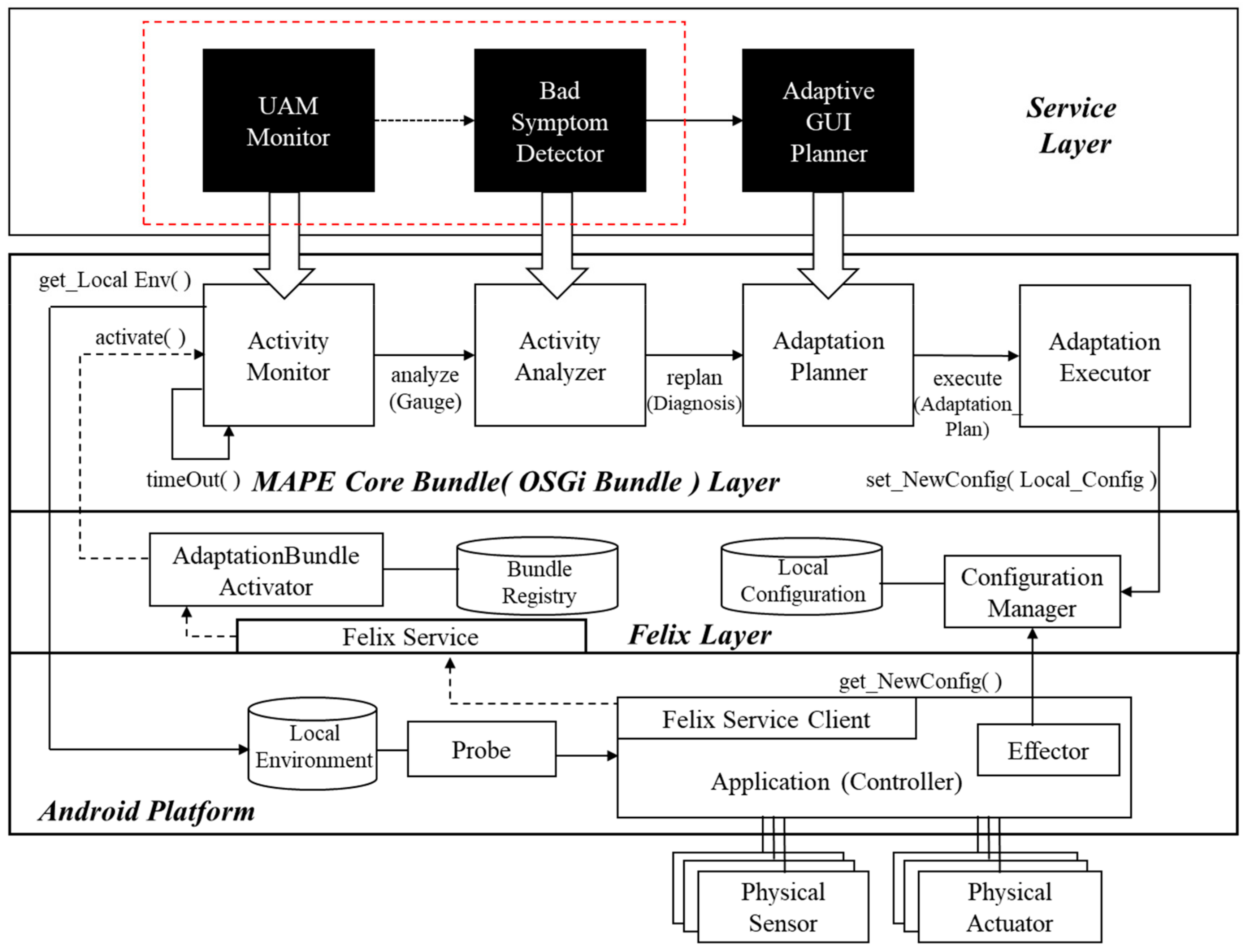
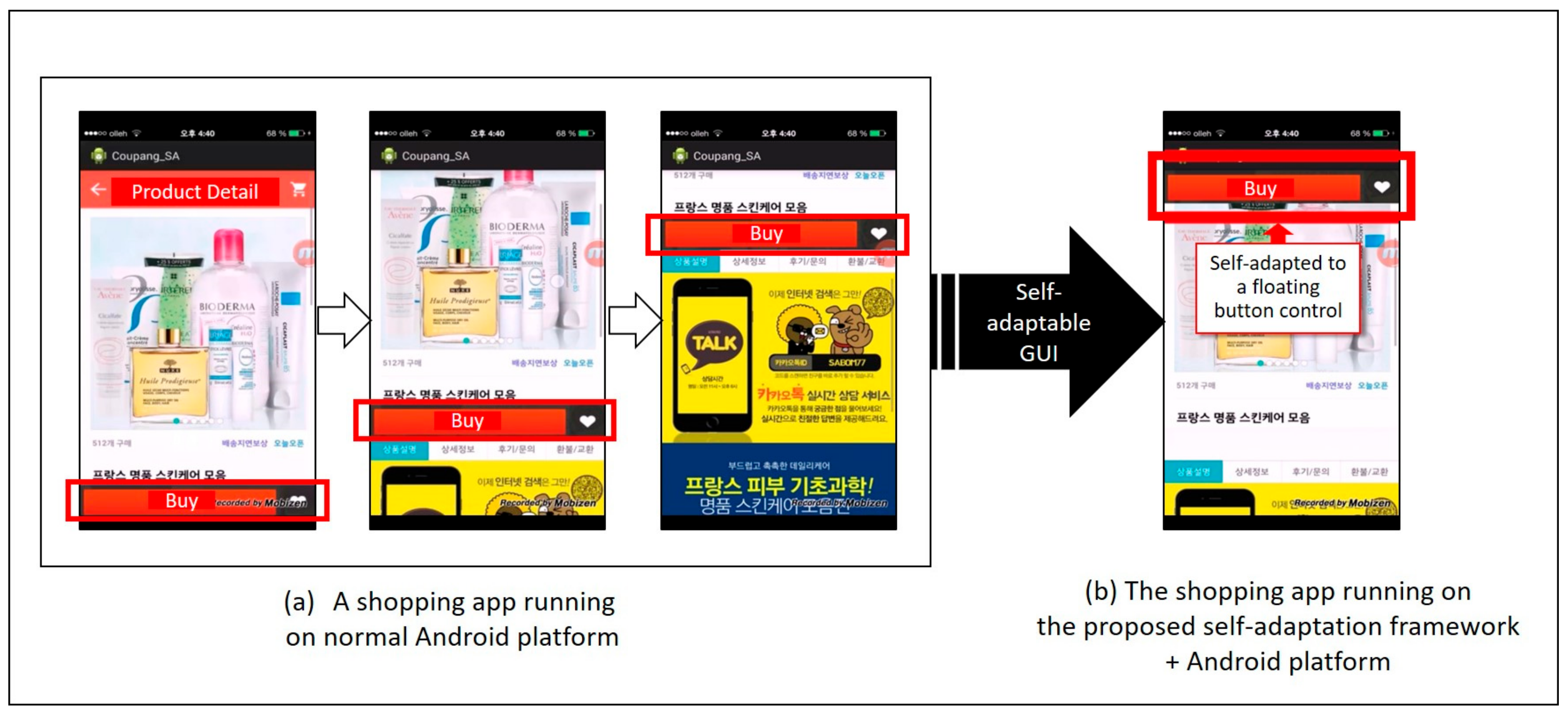
3. A Self-Adaptive Framework for Automatic User Activity Analysis
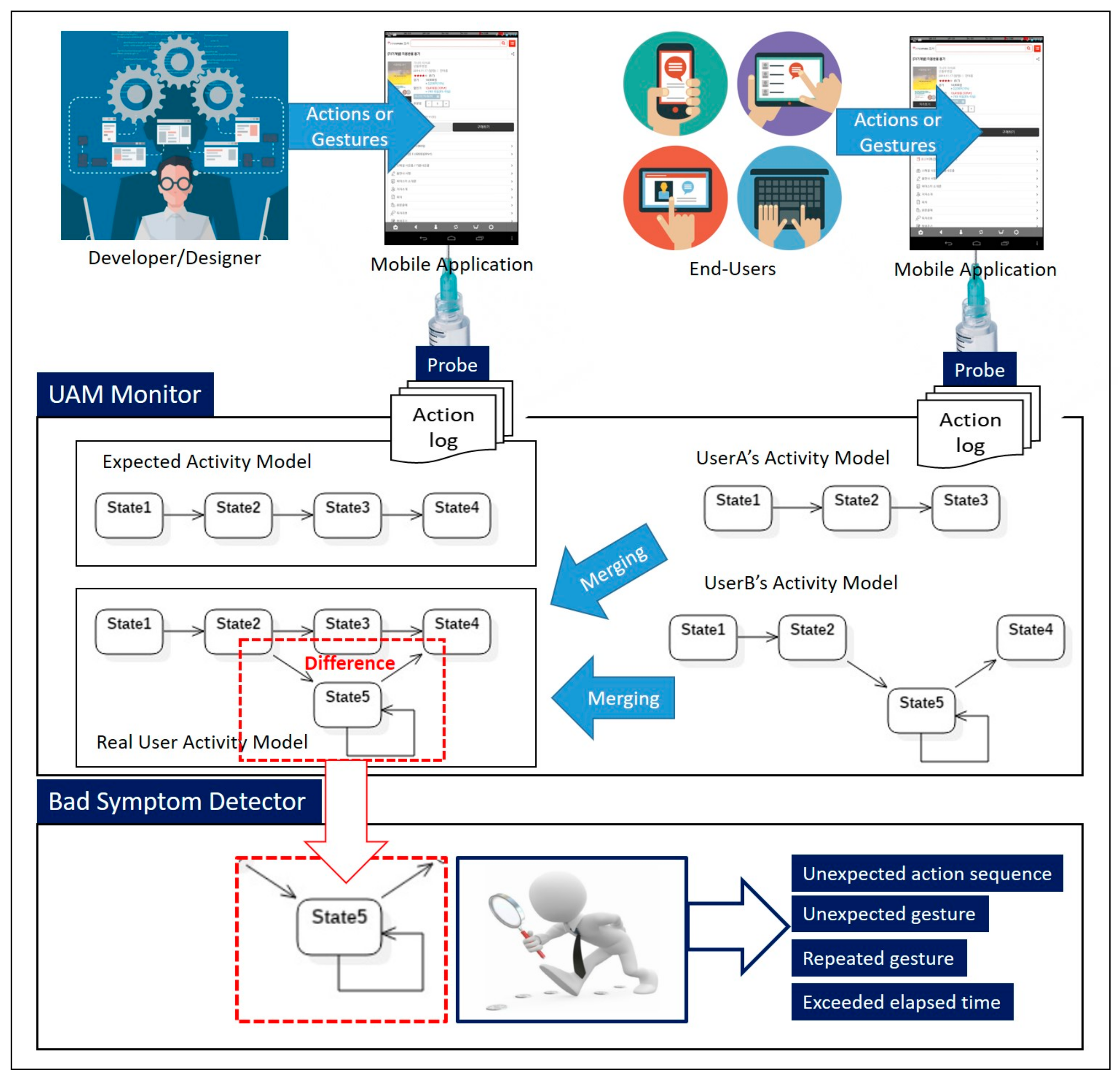
4. An Overview of the Automatic User Activity Analysis Method
5. An Automatic User Activity Analysis Process with a Case Study for Usability Issue Detection in a Mobile Application
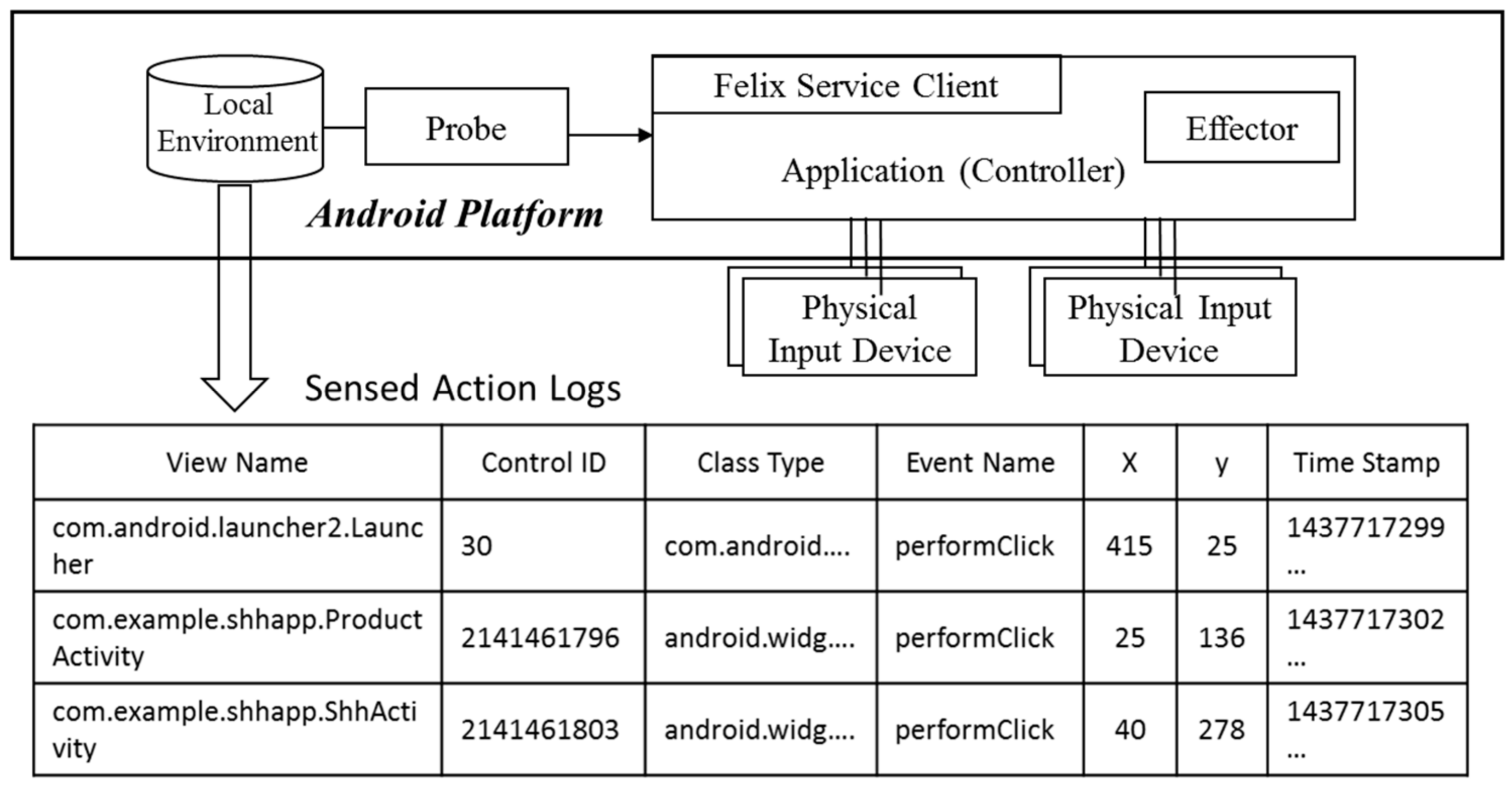
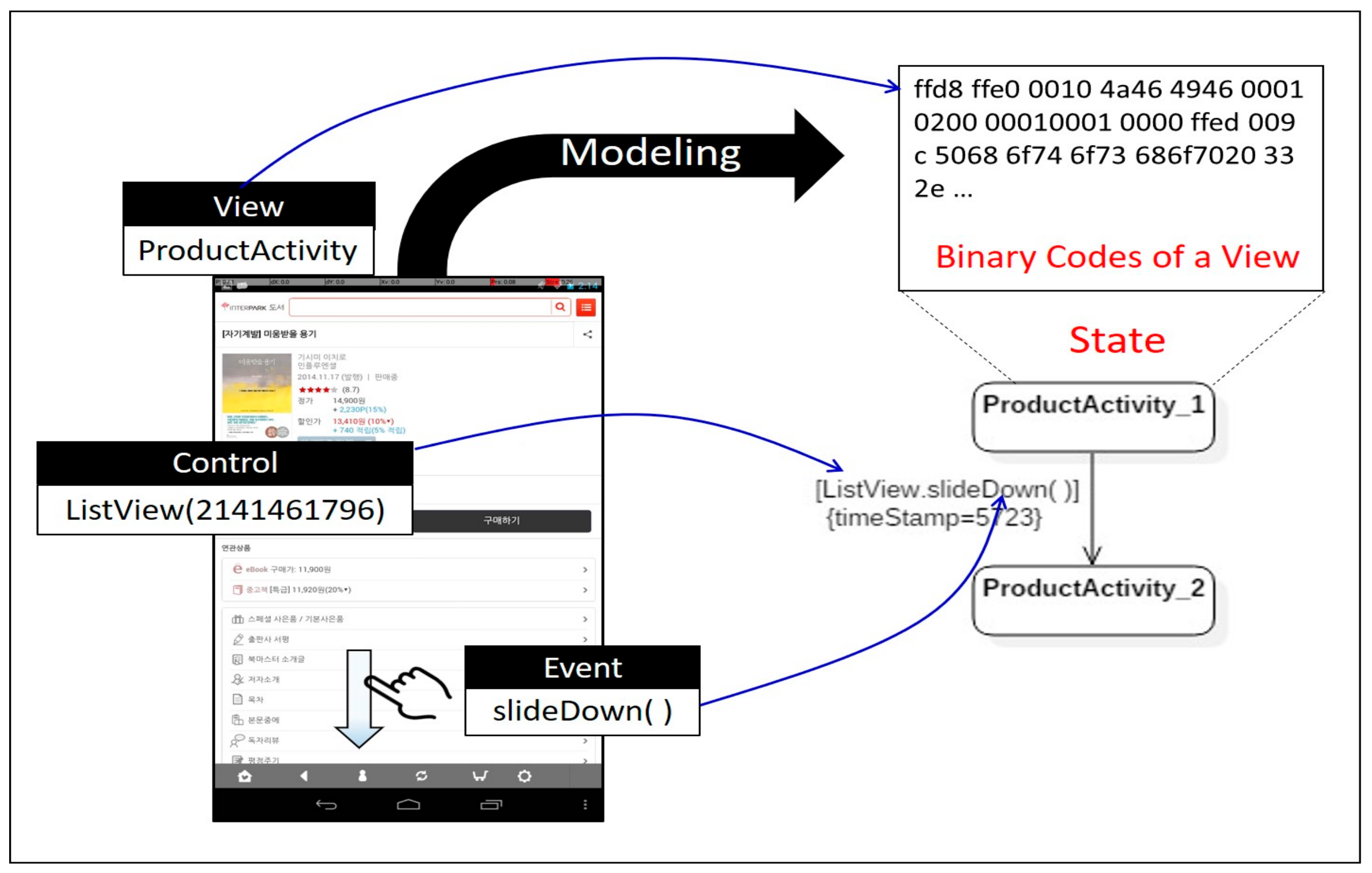
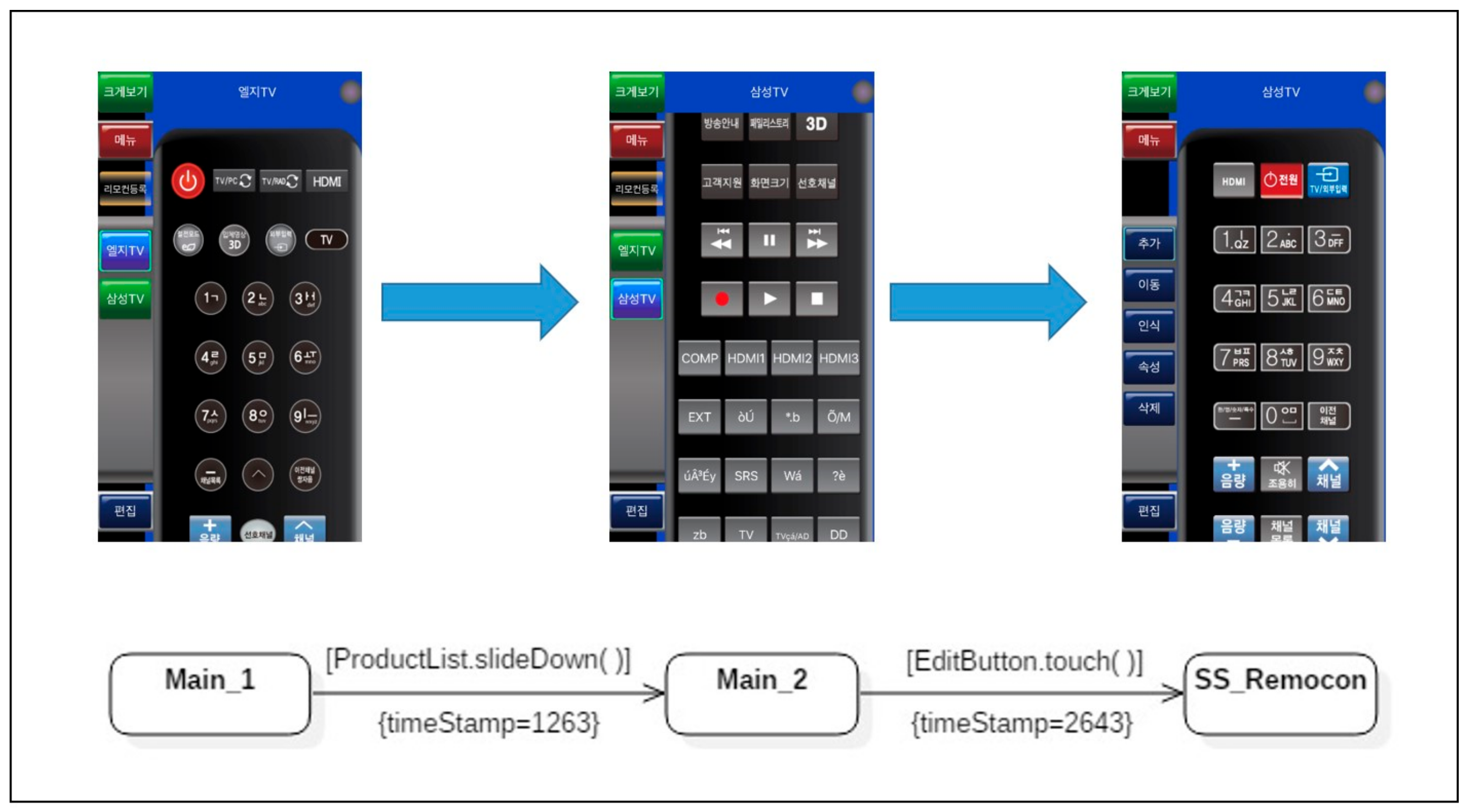
5.1. Generate Activity Model Using Automated Finite-State Machine
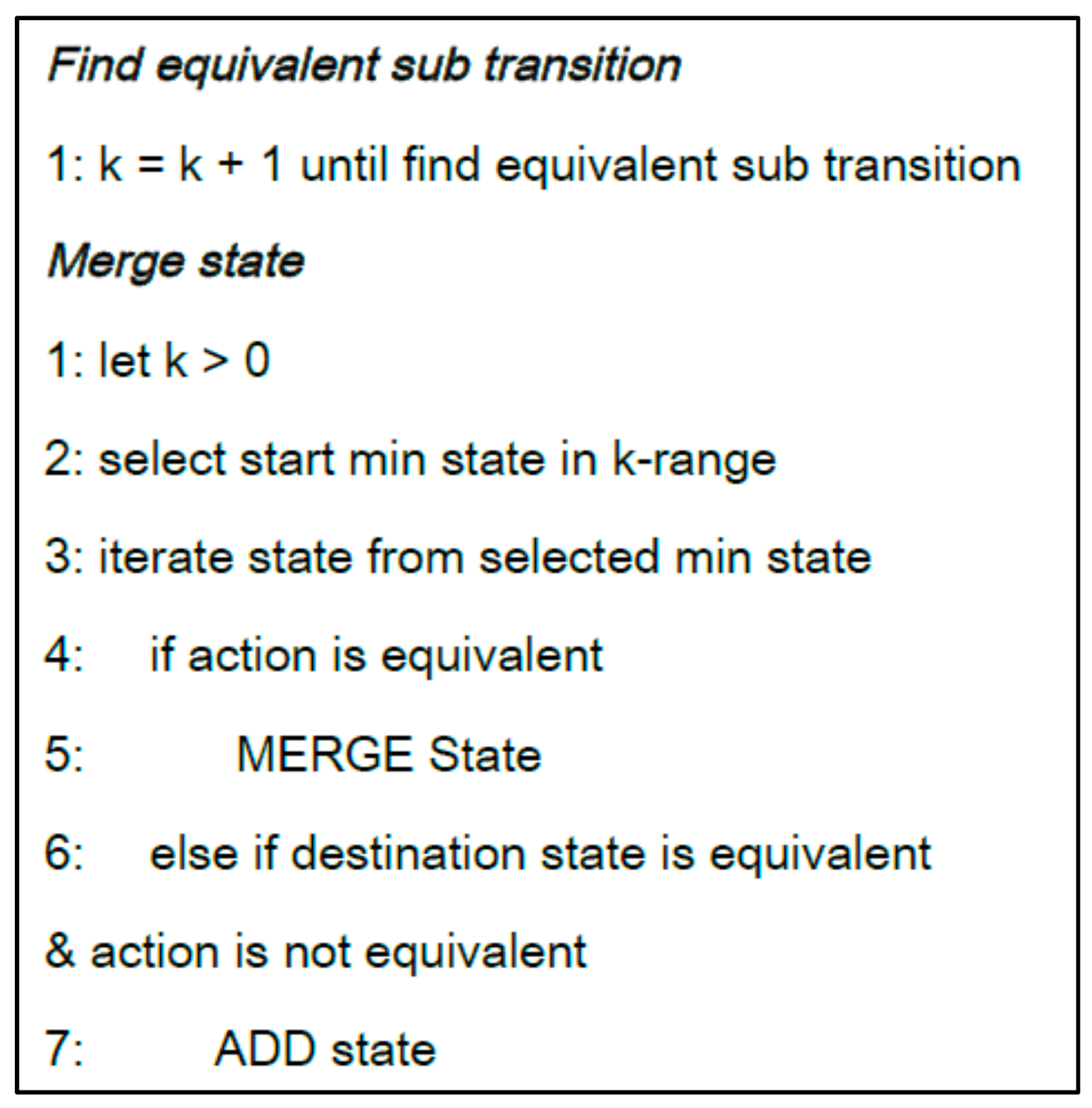
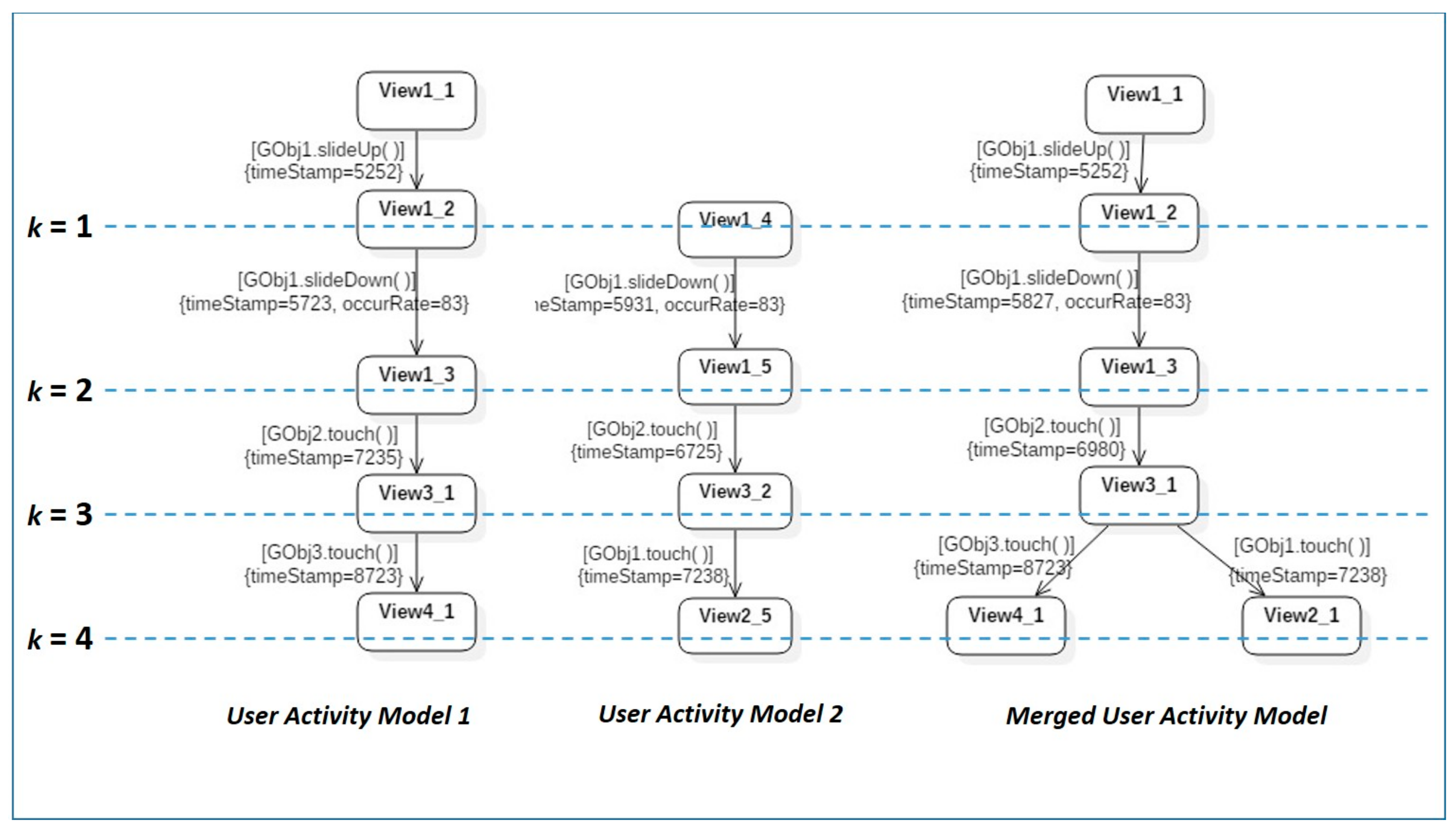
5.2. Merge Multiple User Activity Models into a Representative Real User Activity Model
5.3. Analyze Differences between Expected Activity Model and Merged Real User Activity Model
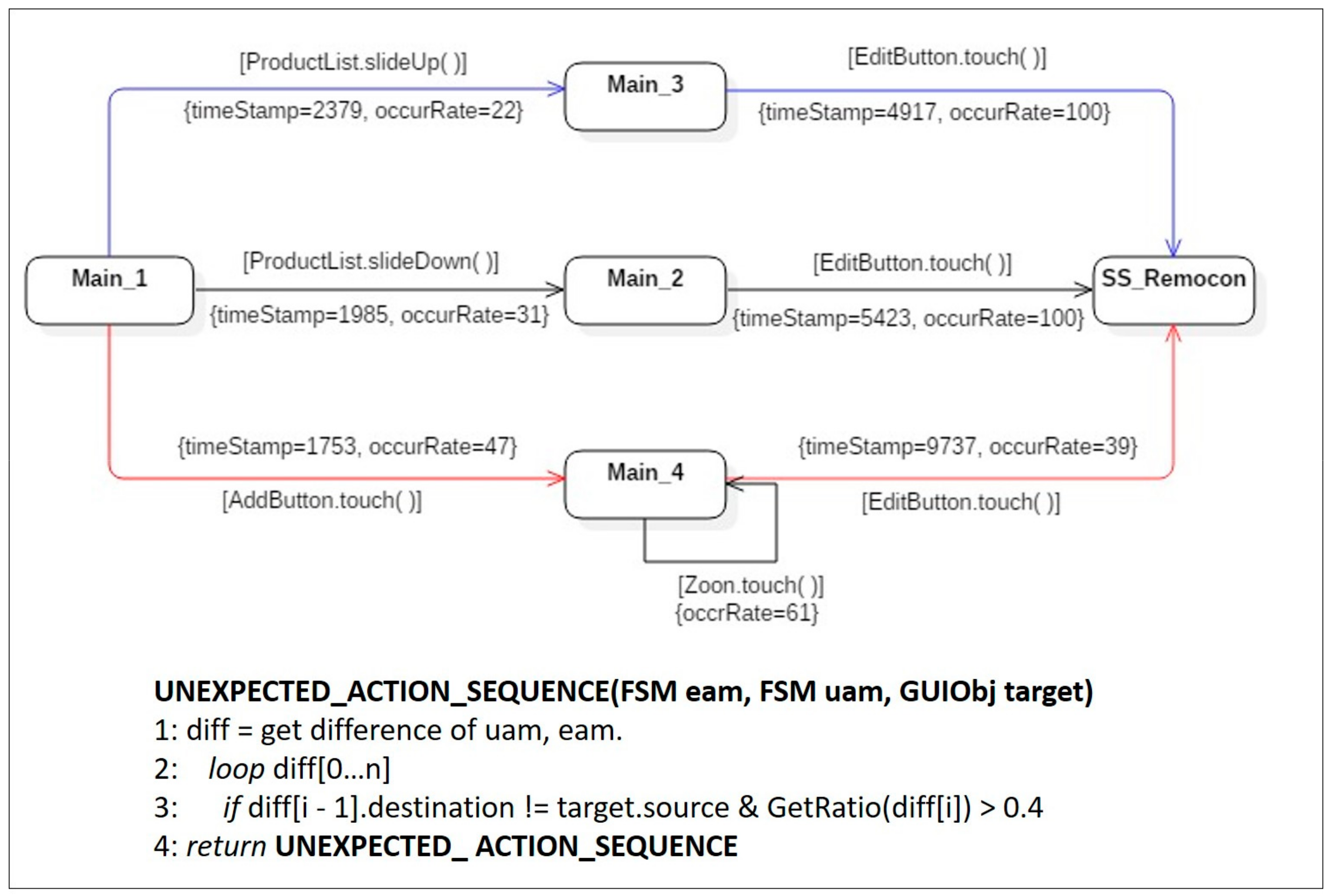
- Symptom type 1: Unexpected action sequence.
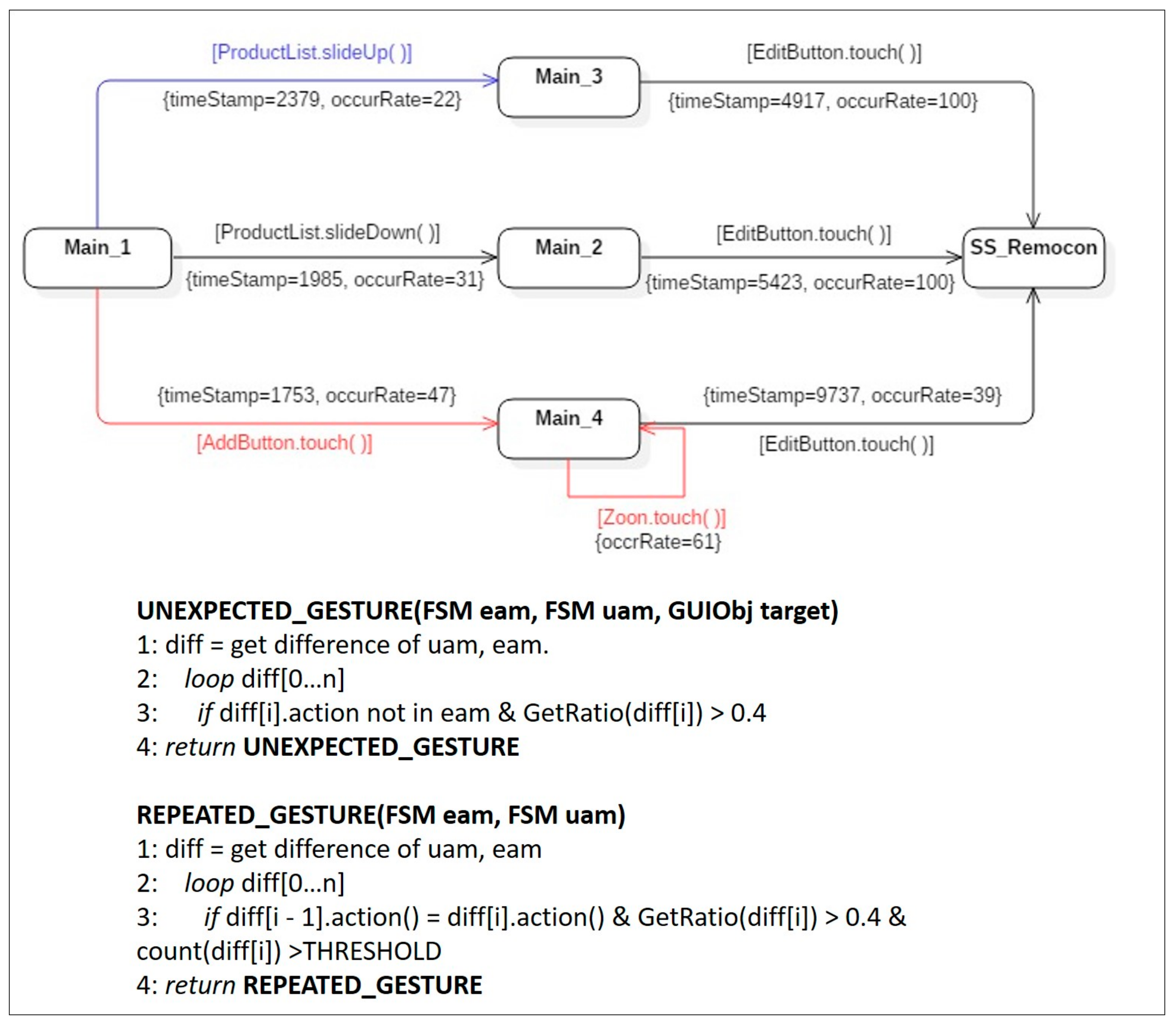
- Symptom type 2: Unexpected gesture.
- Symptom type 3: Repeated gesture.
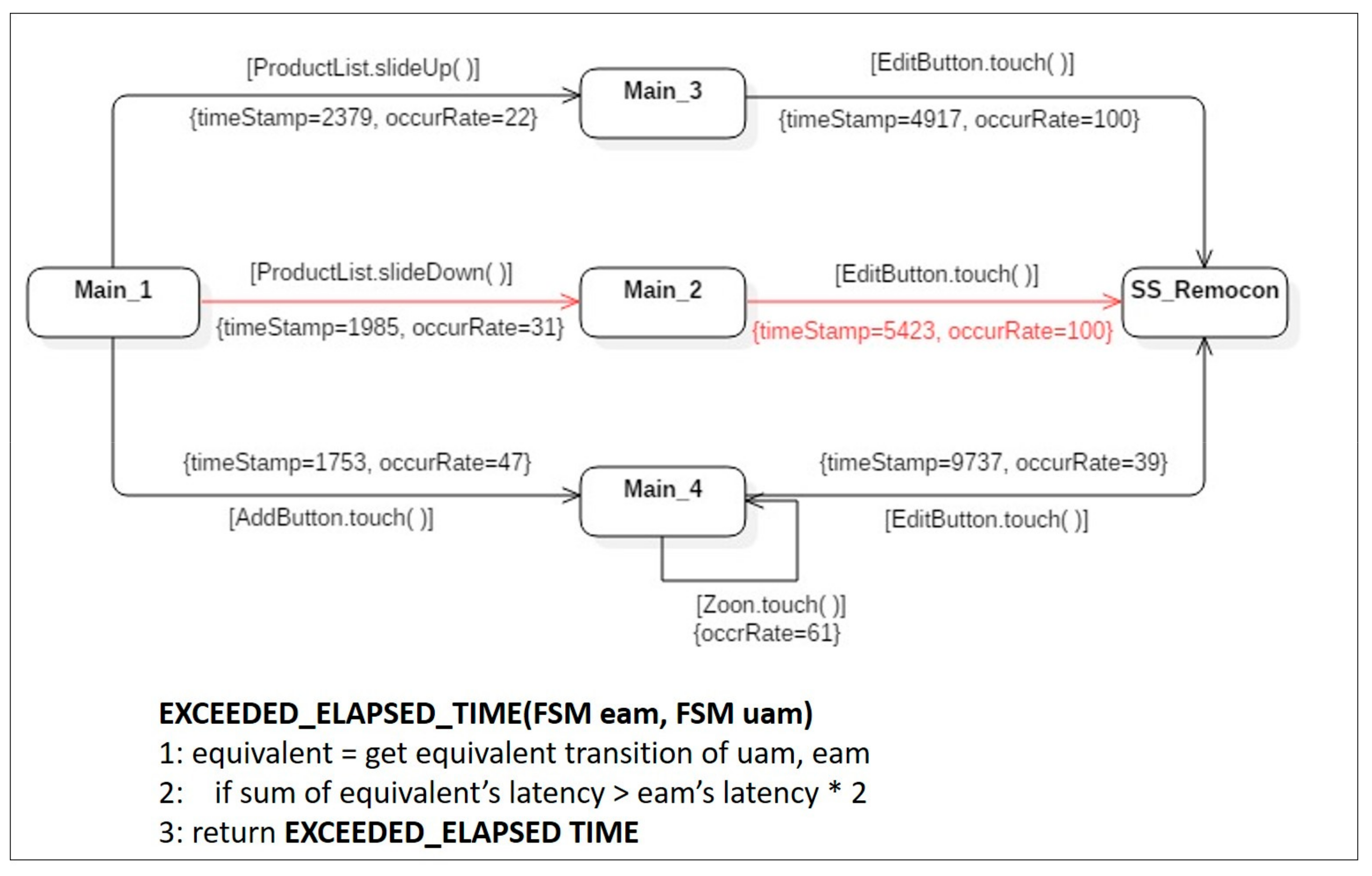
- Symptom type 4: Exceeded elapsed time.
6. Evaluation
- True Positive (TP): The number of cases where automatically detected symptoms coincide with the usability-related issues posed by actual developers.
- False Positive (FP): The number of cases where automatically detected symptoms were not mentioned in the report of usability-related issues posed by actual developers.
7. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Ahmed, A.; Ahmed, E. A Survey on Mobile Edge Computing. In Proceedings of the 10th International Conference on Intelligent Systems and Control (ISCO 2016), Coimbatore, India, 7–8 January 2016. [Google Scholar]
- Frank, H.; Fuhrmann, W.; Ghita, B. Mobile Edge Computing: Requirements for Powerful Mobile Near Real-Time Applications. In Proceedings of the 11th International Network Conference (INC 2016), Frankfurt am Main, Germany, 19–21 July 2016. [Google Scholar]
- Bordel, B.; Alcarria, R.; Robles, T.; Martín, D. Cyber–physical systems: Extending pervasive sensing from control theory to the Internet of Things. Pervasive Mob. Comput. 2017, 40, 156–184. [Google Scholar] [CrossRef]
- Kephart, J.O.; Chess, D.M. The vision of autonomic computing. Computing 2003, 36, 41–50. [Google Scholar] [CrossRef]
- Ma, K.W.; Park, S.; Park, S. Automatic detection of usability issues on mobile applications. KIPS Trans. Softw. Data Eng. 2016, 5, 319–326. [Google Scholar] [CrossRef]
- Park, S.; Park, S.; Park, Y.B. An Architecture framework for orchestrating context-aware it ecosystems: A case study for quantitative evaluation. Sensors 2018, 18, 562. [Google Scholar] [CrossRef] [PubMed]
- Harrison, R.; Flood, D.; Duce, D. Usability of mobile applications: Literature review and rationale for a new usability model. J. Interact. Sci. 2013, 1, 1–16. [Google Scholar] [CrossRef]
- Dolstra, E.; Vliegendhart, R.; Pouwelse, J. Crowdsourcing GUI Tests. In Proceedings of the 2013 IEEE Sixth International Conference on Software Testing, Verification and Validation, Luxembourg, 18–22 March 2013. [Google Scholar]
- Gómez, R.; Caballero, D.; Sevillano, J. Heuristic evaluation on mobile interfaces: A new checklist. Sci. World J. 2014, 2014, 178–188. [Google Scholar] [CrossRef]
- Hussain, A.; Ferneley, E. Usability Metric for Mobile Application: A Goal Question Metric (GQM) Approach. In Proceedings of the 10th International Conference on Information Integration and Web-Based Applications and Services (iiWAS ’08), Linz, Austria, 24–26 November 2008. [Google Scholar]
- Munson, W.A.; Gardner, M.B. Standardizing auditory tests. J. Acoust. Soc. Am. 1950, 22, 675. [Google Scholar] [CrossRef]
- Zen, M. Metric-based Evaluation of Graphical User Interfaces: Model, Method, and Software Support. In Proceedings of the 5th ACM SIGCHI Symposium on Engineering Interactive Computing Systems, London, UK, 24–27 June 2013. [Google Scholar]
- Abrahao, S.; Insfran, E. Early Usability Evaluation in Model Driven Architecture Environments. In Proceedings of the 2006 Sixth International Conference on Quality Software (QSIC06), Beijing, China, 27–28 October 2006. [Google Scholar]
- Kronbauer, A.H.; Santos, C.A.S.; Vieira, V. Smartphone Applications Usability Evaluation: A Hybrid Model and Its Implementation. In Proceedings of the 2012 Human-Centered Software Engineering (HCSE 2012), Toulouse, France, 29–31 October 2012. [Google Scholar]
- Bastien, J.M.C. Usability testing: A review of some methodological and technical aspects of the method. Comput. Res. Repos. 2010, 79, 18–23. [Google Scholar] [CrossRef] [PubMed]
- West, R.; Lehman, K. Automated summative usability studies: An empirical evaluation. In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems (CHI ’06), Montreal, QC, Canada, 22–27 April 2006. [Google Scholar]
- Waterson, S.; Landay, J.A. In the lab and out in the wild: Remote web usability testing for mobile devices. In Proceedings of the Extended Abstracts on Human Factors in Computing Systems (CHI EA’02), Minneapolis, MN, USA, 20–25 April 2002. [Google Scholar]
- Ma, X.; Yan, B.; Chen, G.; Zhang, C.; Huang, K.; Drury, J. A Toolkit for usability testing of mobile applications. In Proceedings of the International Conference on Mobile Computing, Applications, and Services (MobiCASE 2011), Los Angeles, CA, USA, 24–27 October 2011. [Google Scholar]
- Garlan, D.; Cheng, S.W.; Huang, A.C.; Schmerl, B.; Steenkiste, P. Rainbow: Architecture-based self-adaptation with reusable infrastructure. IEEE Comput. 2004, 37, 46–54. [Google Scholar] [CrossRef]
- Hallsteinsen, S.; Geihs, K.; Paspallis, N.; Eliassen, F.; Horn, G.; Lorenzo, J.; Mamelli, A.; Papadopoulos, G.A. A development framework and methodology for self-adapting applications in ubiquitous computing environments. J. Syst. Softw. 2012, 85, 2840–2859. [Google Scholar] [CrossRef]
- Al-Zinati, M.; Araujo, F.; Kuiper, D.; Valente, J.; Wenkstern, R.Z. DIVAs 4.0: A multi-agent based simulation framework. In Proceedings of the IEEE/ACM 17th International Symposium on Distributed Simulation and Real Time Applications, Delft, The Netherlands, 30 October–1 November 2013. [Google Scholar]
- OSGi Specifications. Available online: http://www.osgi.org/Specifications/HomePage (accessed on 30 June 2018).
- Monkeyrunner. Available online: https://developer.android.com/studio/test/monkeyrunner/ (accessed on 30 June 2018).
- Hierarchy Viewer. Available online: http://android.xsoftlab.net/tools/help/hierarchy-viewer.html (accessed on 30 June 2018).
- Mariani, L.; Pastore, F.; Pezze, M. Dynamic analysis for diagnosing integration faults in software engineering. IEEE Trans. 2011, 37, 486–508. [Google Scholar] [CrossRef]
- Zhang, Y.; Zhao, X.; Zhou, Y.; Wang, Y.; Hou, X. The improvement of Gk-tail algorithm of software behavior modeling. In Proceedings of the International Conference on Computer Science and Application Engineering (CSAE 2017), Shanghai, China, 21–23 October 2017. [Google Scholar]
- Nielson, J. Why You Only Need to Test with 5 Users. Available online: http://www.nngroup.com/articles/why-you- only-need-to-test-with-5-users/ (accessed on 30 June 2018).
- O’Brien, R.G. A general ANOVA method for robust tests of additive models for variances. J. Am. Stat. Associ. 1979, 74, 877–880. [Google Scholar] [CrossRef]
- Memon, A.M. A Comprehensive Framework For Testing Graphical User Interfaces. Ph.D. Thesis, University of Pittsburgh, Pittsburgh, PA, USA, 2001. [Google Scholar]
| App Name | Round 1 | Round 2 | ||||
|---|---|---|---|---|---|---|
| TP | FP | Precision | TP | FP | Precision | |
| IMSI | 9 | 3 | 0.75 | 6 | 2 | 0.75 |
| News-android | 18 | 8 | 0.69 | 10 | 3 | 0.77 |
| MyRemocon | 8 | 4 | 0.66 | 5 | 2 | 0.71 |
| open-key | 5 | 2 | 0.71 | 2 | 1 | 0.67 |
| Shhapp | 4 | 2 | 0.67 | 2 | 0 | 1.00 |
| Average | 8.80 | 3.80 | 0.70 | 5.00 | 1.60 | 0.78 |
| IMSI #59 | News-Android #23 | MyRemocon #157 | Open-Key #54 | Shhapp #47 | Average | |
|---|---|---|---|---|---|---|
| (a) | ||||||
| Success rate before resolving | 61% | 68% | 37% | 71% | 54% | 58% |
| Success rate after resolving | 84% | 74% | 86% | 88% | 66% | 80% |
| Changes in success rates | +23% | +6% | +49% | +17% | +12% | +21% |
| (b) | ||||||
| Time taken before resolution | 4975 ms | 5941 ms | 7378 ms | 3259 ms | 4074 ms | 5125.4 ms |
| Time taken after resolution | 3157 ms | 5324 ms | 5349 ms | 3117 ms | 3268 ms | 4043 ms |
| Changes in time taken | −1818 ms | −617 ms | −2029 ms | −142 ms | −806 ms | −1082.4 ms |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Park, S.; Park, S.; Ma, K. An Automatic User Activity Analysis Method for Discovering Latent Requirements: Usability Issue Detection on Mobile Applications. Sensors 2018, 18, 2963. https://doi.org/10.3390/s18092963
Park S, Park S, Ma K. An Automatic User Activity Analysis Method for Discovering Latent Requirements: Usability Issue Detection on Mobile Applications. Sensors. 2018; 18(9):2963. https://doi.org/10.3390/s18092963
Chicago/Turabian StylePark, Soojin, Sungyong Park, and Kyeongwook Ma. 2018. "An Automatic User Activity Analysis Method for Discovering Latent Requirements: Usability Issue Detection on Mobile Applications" Sensors 18, no. 9: 2963. https://doi.org/10.3390/s18092963
APA StylePark, S., Park, S., & Ma, K. (2018). An Automatic User Activity Analysis Method for Discovering Latent Requirements: Usability Issue Detection on Mobile Applications. Sensors, 18(9), 2963. https://doi.org/10.3390/s18092963






