A Blockchain-Based Authorization System for Trustworthy Resource Monitoring and Trading in Smart Communities
Abstract
1. Introduction
2. State of the Art
3. System Requirements and Architecture of the Solution
3.1. System Requirements
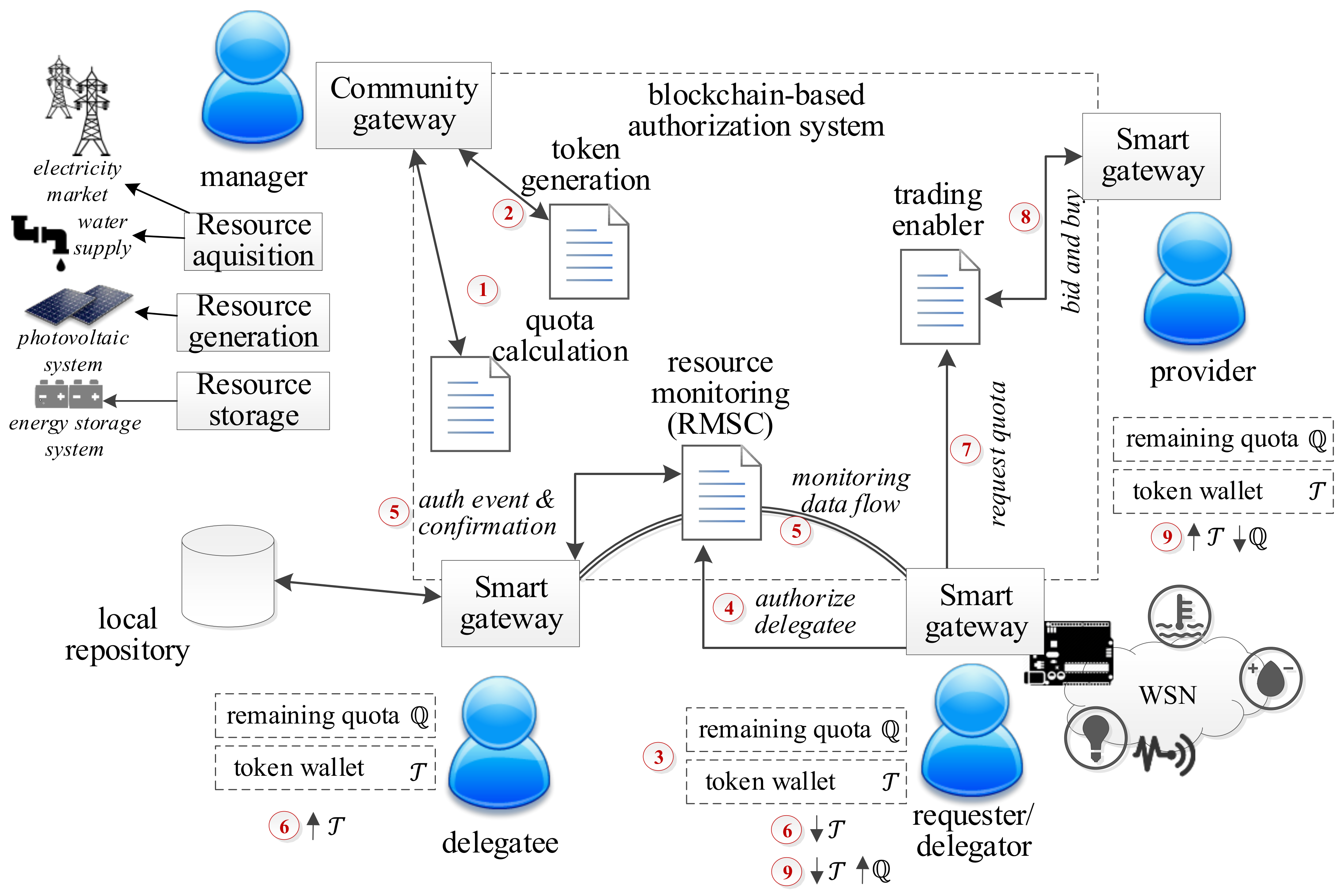
3.2. Architecture of the Solution
4. An Authorization System for Trustworthy Resource Monitoring
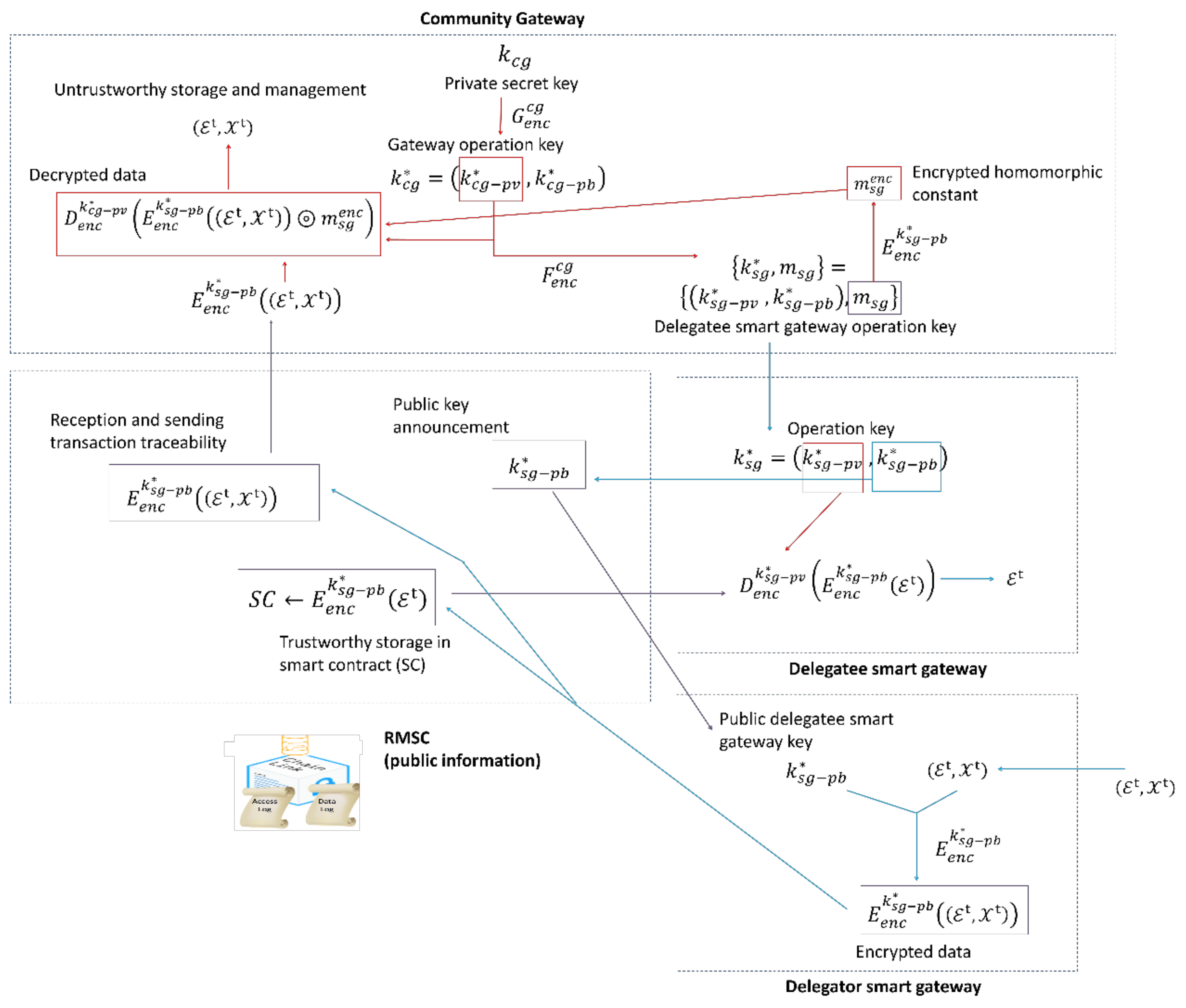
4.1. Trustworthy Secure Monitoring Solution
4.2. Secure Controller Functions Delegation
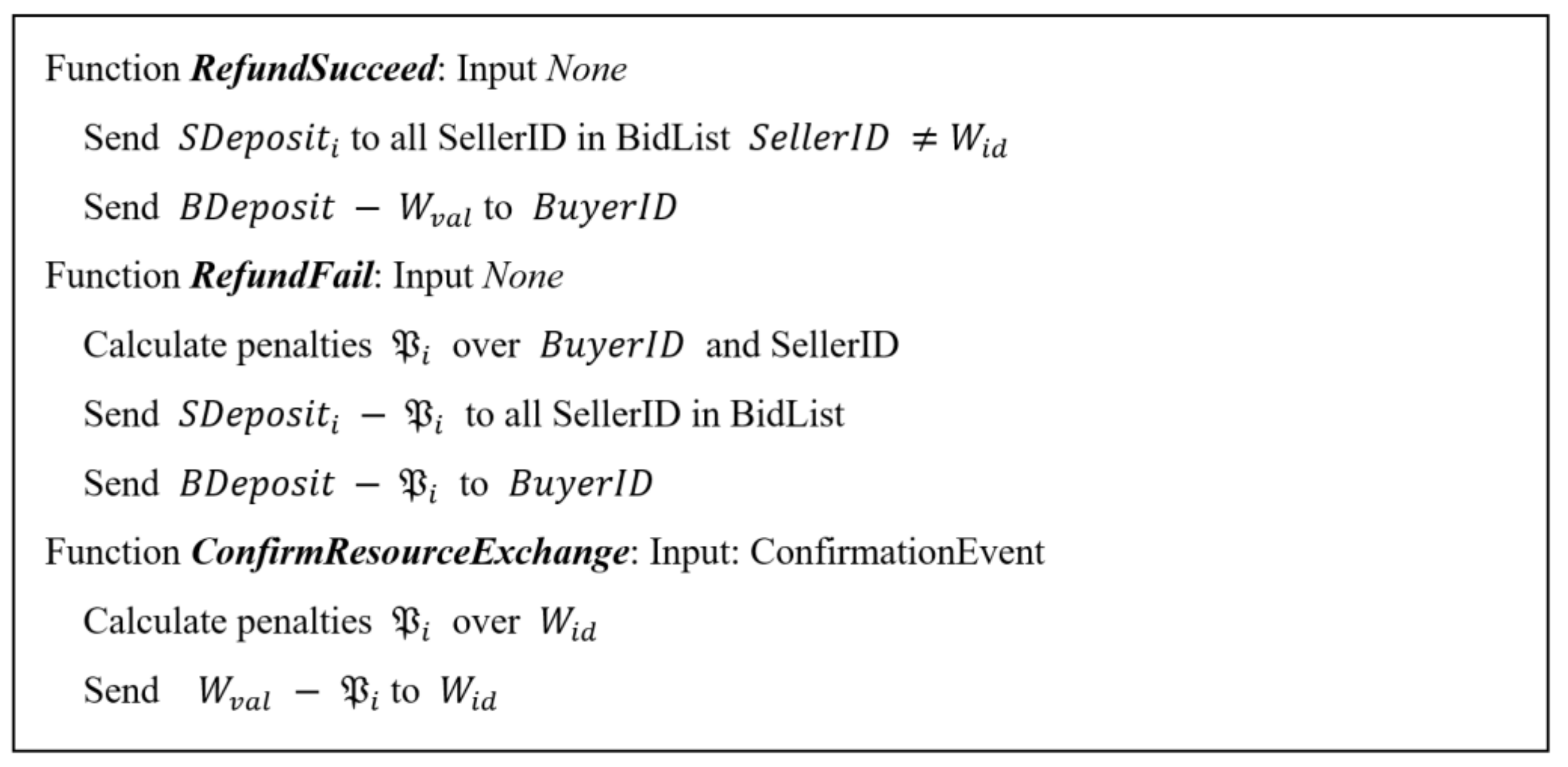
5. Trustworthy Resource Trading Proposal
5.1. Resource Consumption Model
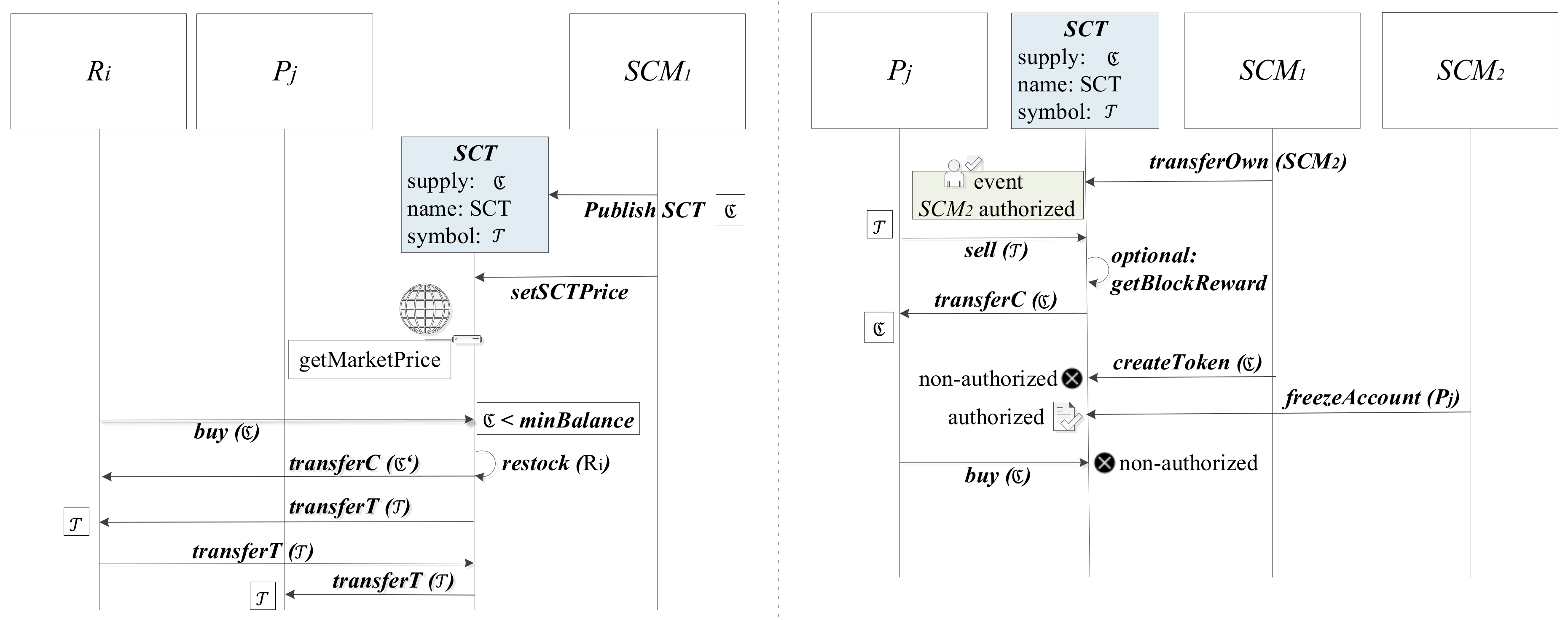
5.2. Smart Community Token Definition and Provision
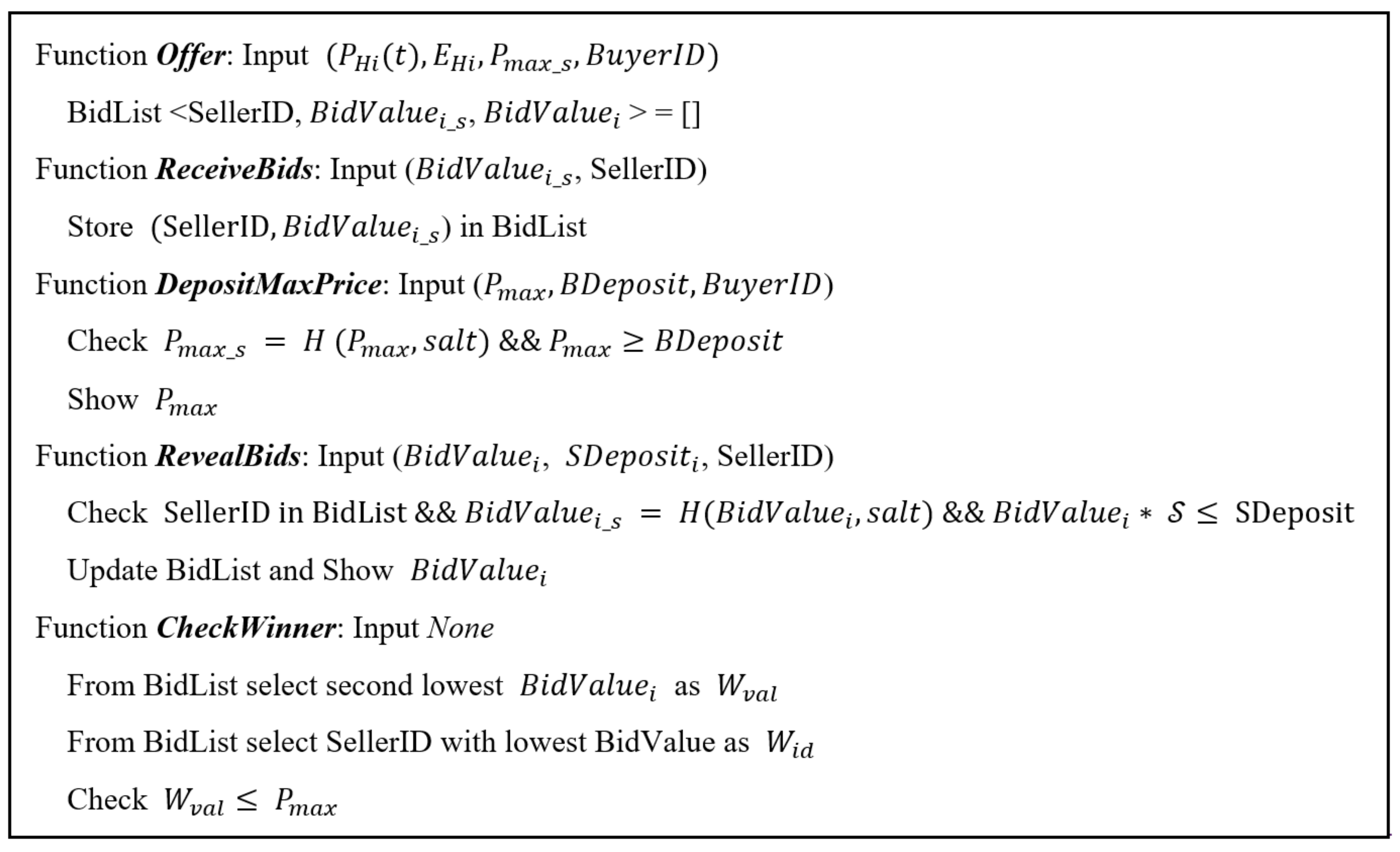
5.3. Resource Trading
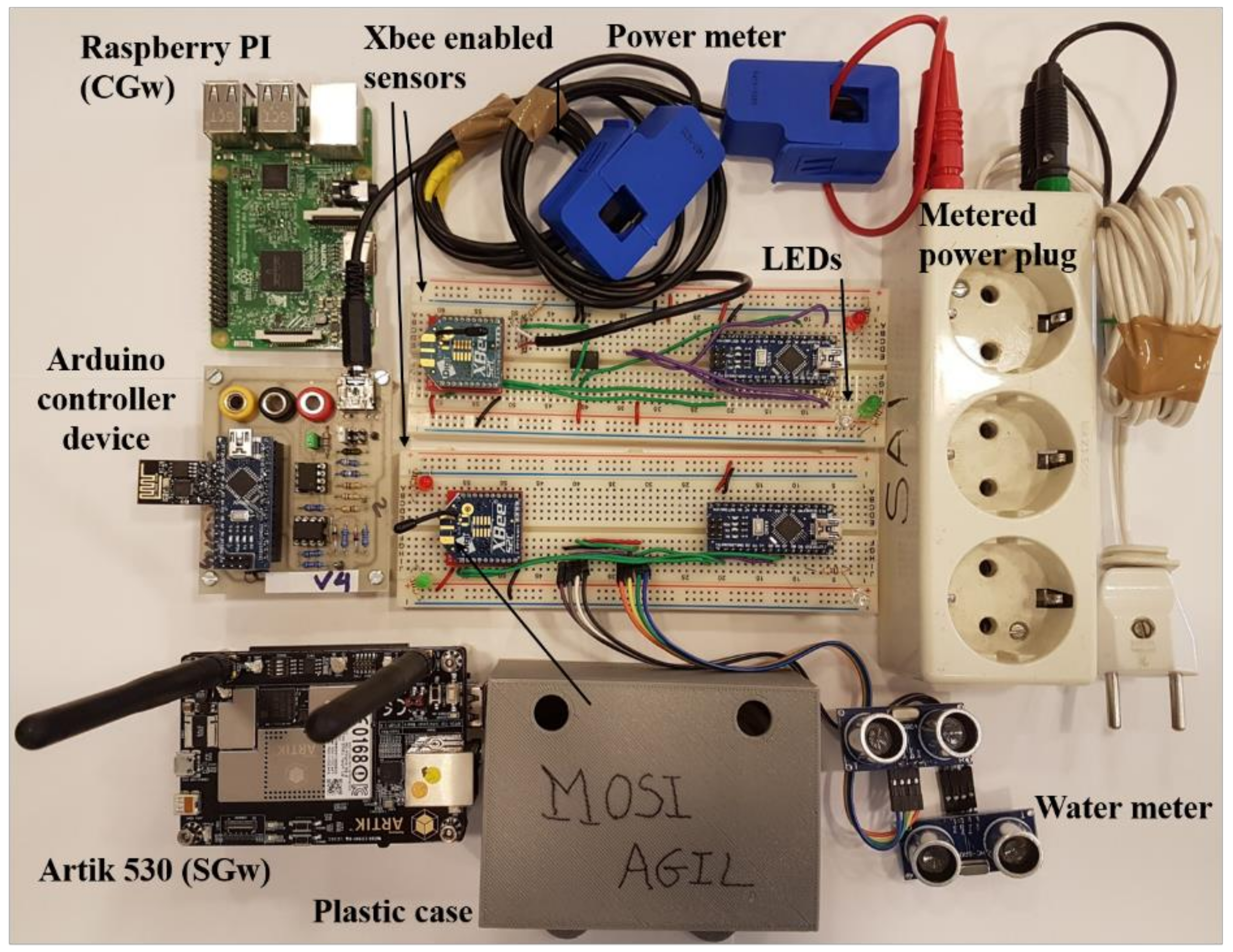
6. System Implementation
6.1. WNS for Resource Monitoring
6.2. Blockchain-Based Authorization and Proof-of-Authority
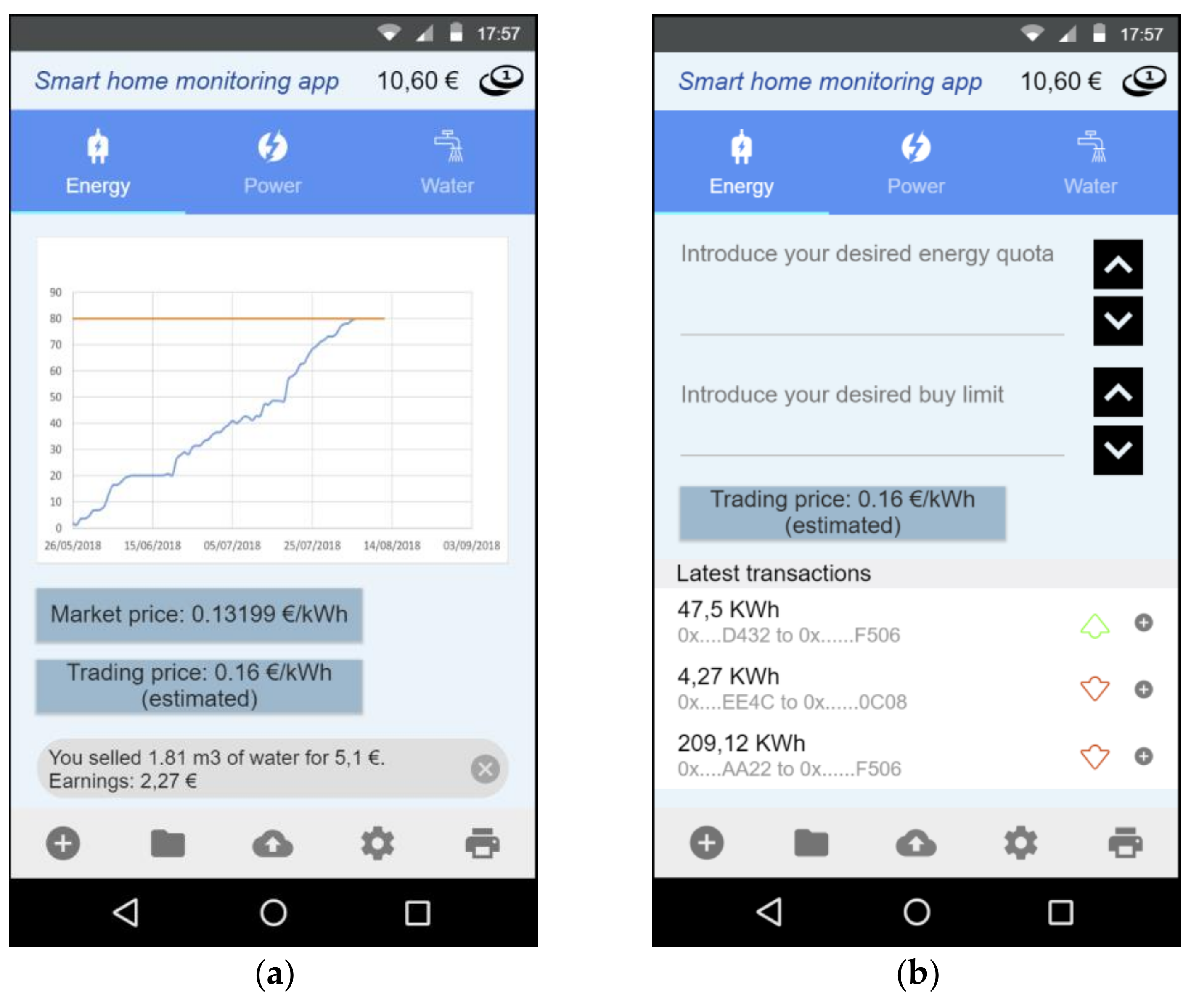
6.3. Notification Management and User Interaction
7. Experiments and Results
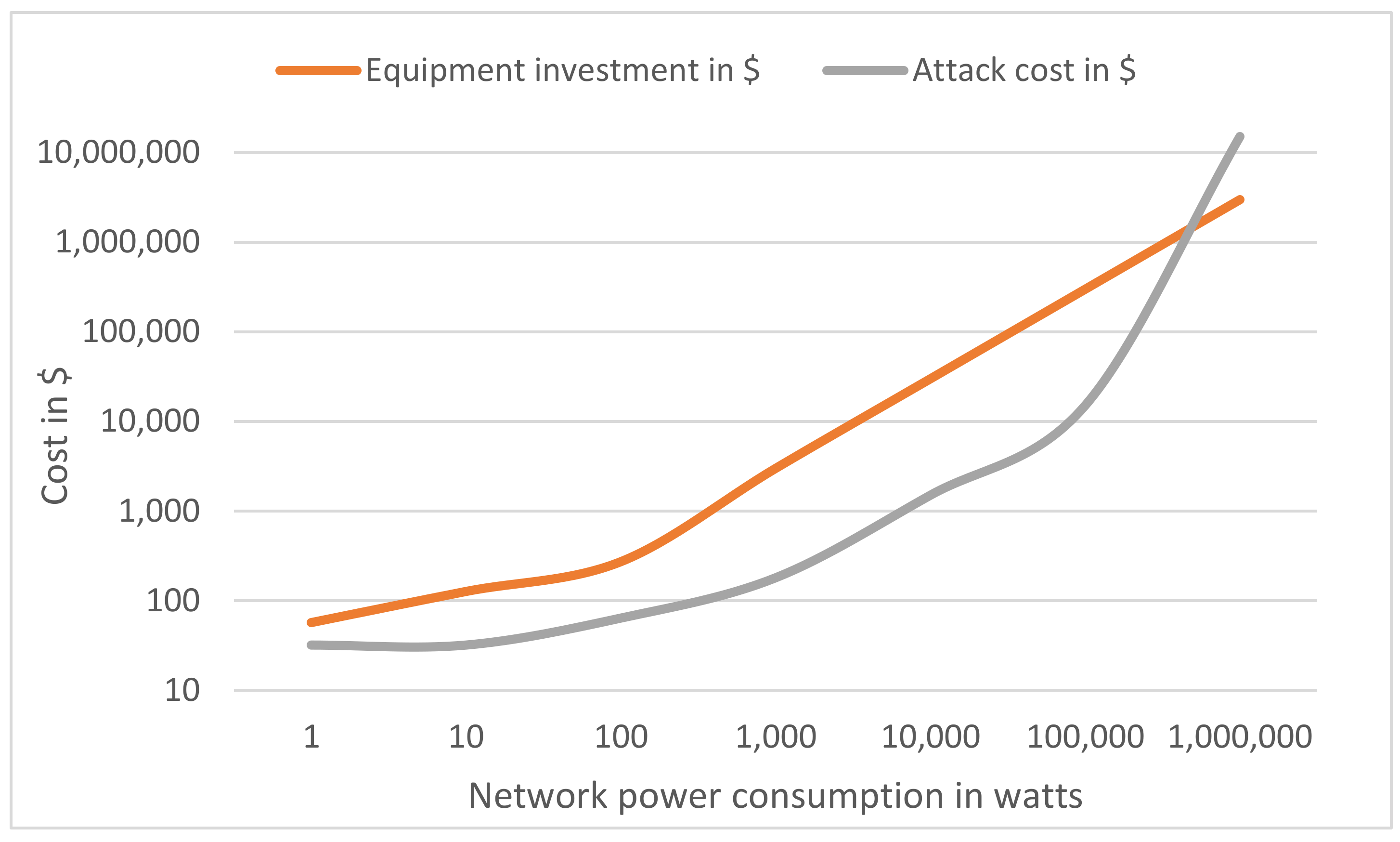
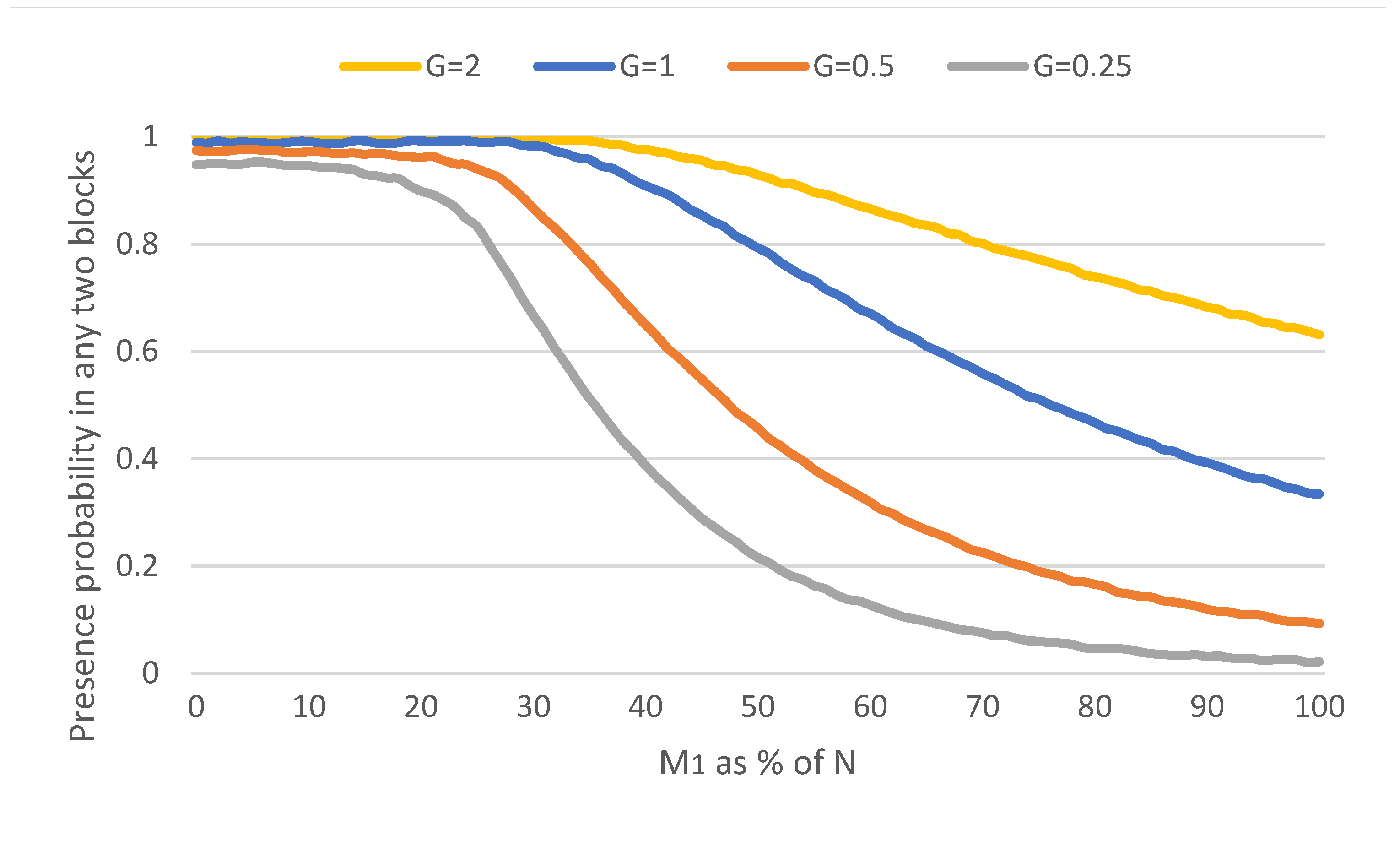
7.1. Proof of Authority Suitability and Security Considerations
7.2. Performance Evaluation for Resource Monitoring
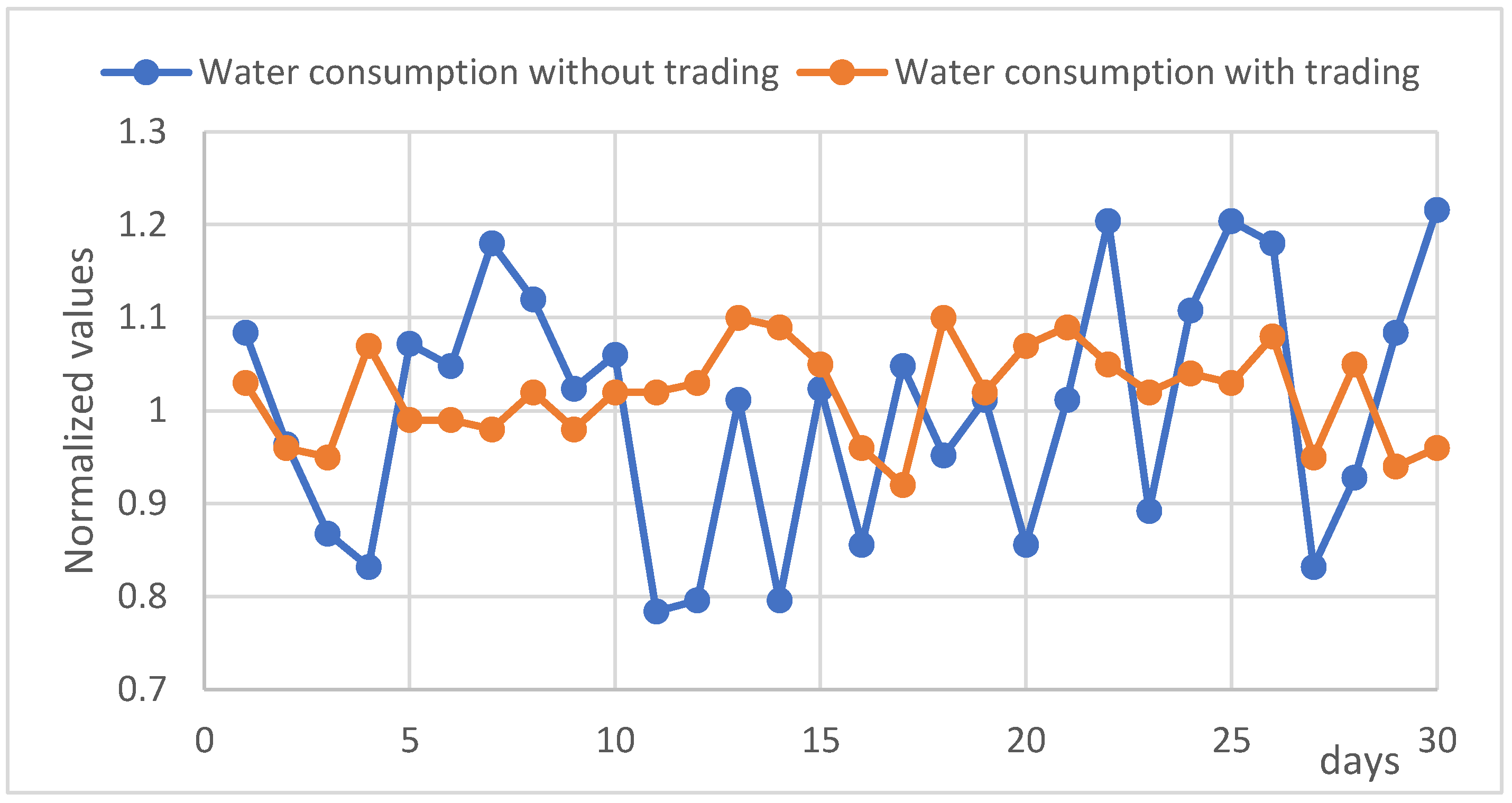
7.3. Validation of Resource Trading
8. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Hahn, A.; Singh, R.; Liu, C.-C.; Chen, S. Smart Contract-Based Campus Demonstration of Decentralized Transactive Energy Auctions. In Proceedings of the 2017 IEEE Power & Energy Society Innovative Smart Grid Technologies Conference (ISGT), Washington, DC, USA, 23–26 April 2017; pp. 1–5. [Google Scholar]
- Ronen, E.; Shamir, A. Extended Functionality Attacks on IoT Devices: The Case of Smart Lights. In Proceedings of the 2016 IEEE European Symposium on Security and Privacy (EuroS&P), Saarbrucken, Germany, 21–24 March 2016; pp. 3–12. [Google Scholar]
- Pilkington, M. Blockchain Technology: Principles and Applications. In Research Handbook on Digital Transformations; Oleros, F.X., Zhegu, M., Eds.; Edward Elgar: Cheltenham, UK, 2015. [Google Scholar]
- Bordel, B.; Alcarria, R.; Martín, D.; Sánchez-Picot, Á. Trust Provision in the Internet of Things Using Transversal Blockchain Networks. Available online: http://autosoftjournal.net/paperShow.php?paper=100000052 (accessed on 18 October 2018).
- Bellido-Outeirino, F.; Flores-Arias, J.; Linan-Reyes, M.; Palacios-Garcia, E.; Luna-Rodriguez, J. Wireless Sensor Network and Stochastic Models for Household Power Management. IEEE Trans. Consum. Electron. 2013, 59, 483–491. [Google Scholar] [CrossRef]
- Zeifman, M. Disaggregation of Home Energy Display Data Using Probabilistic Approach. IEEE Trans. Consum. Electron. 2012, 58, 23–31. [Google Scholar] [CrossRef]
- Kong, S.; Kim, Y.; Ko, R.; Joo, S.-K. Home Appliance Load Disaggregation Using Cepstrum-Smoothing-Based Method. IEEE Trans. Consum. Electron. 2015, 61, 24–30. [Google Scholar] [CrossRef]
- Lee, Y.; Hsiao, W.; Huang, C.; Chou, S.T. An Integrated Cloud-Based Smart Home Management System with Community Hierarchy. IEEE Trans. Consum. Electron. 2016, 62, 1–9. [Google Scholar] [CrossRef]
- Wi, Y.-M.; Lee, J.-U.; Joo, S.-K. Electric Vehicle Charging Method for Smart Homes/Buildings with a Photovoltaic System. IEEE Trans. Consum. Electron. 2013, 59, 323–328. [Google Scholar] [CrossRef]
- Pop, C.; Cioara, T.; Antal, M.; Anghel, I.; Salomie, I.; Bertoncini, M.; Pop, C.; Cioara, T.; Antal, M.; Anghel, I.; et al. Blockchain Based Decentralized Management of Demand Response Programs in Smart Energy Grids. Sensors 2018, 18, 162. [Google Scholar] [CrossRef] [PubMed]
- Khan, A.M.; Büyükşahin, Ü.C.; Freitag, F. Incentive-Based Resource Assignment and Regulation for Collaborative Cloud Services in Community Networks. J. Comput. Syst. Sci. 2015, 81, 1479–1495. [Google Scholar] [CrossRef]
- Lee, J.; Shin, Y.; Lee, I. Energy Trading System of Distributed Resources. In Proceedings of the 2017 International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 18–20 October 2017; pp. 1131–1133. [Google Scholar]
- Abdella, J.; Shuaib, K. Peer to Peer Distributed Energy Trading in Smart Grids: A Survey. Energies 2018, 11, 1560. [Google Scholar] [CrossRef]
- Avital, M. Peer Review: Toward a Blockchain-Enabled Market-Based Ecosystem. Commun. Assoc. Inf. Syst. 2018, 42, 646–653. [Google Scholar] [CrossRef]
- Park, L.; Lee, S.; Chang, H.; Park, L.W.; Lee, S.; Chang, H. A Sustainable Home Energy Prosumer-Chain Methodology with Energy Tags over the Blockchain. Sustainability 2018, 10, 658. [Google Scholar] [CrossRef]
- Davis, N. Blockchain for the Connected Home: Combining Security and Flexibility. Available online: https://labs.comcast.com/blockchain-for-the-connected-home-combining-security-and-flexibility (accessed on 18 October 2018).
- Gatteschi, V.; Lamberti, F.; Demartini, C.; Pranteda, C.; Santamaría, V. Blockchain and Smart Contracts for Insurance: Is the Technology Mature Enough? Future Internet 2018, 10, 20. [Google Scholar] [CrossRef]
- Lee, J. Patch Transporter: Incentivized, Decentralized Software Patch System for WSN and IoT Environments. Sensors 2018, 18, 574. [Google Scholar] [CrossRef] [PubMed]
- Hong, Z.; Wang, Z.; Cai, W.; Leung, V.C.M. Blockchain-Empowered Fair Computational Resource Sharing System in the D2D Network. Future Internet 2017, 9, 85. [Google Scholar] [CrossRef]
- Lin, Y.-P.; Petway, J.R.; Anthony, J.; Mukhtar, H.; Liao, S.-W.; Chou, C.-F.; Ho, Y.-F. Blockchain: The Evolutionary Next Step for ICT E-Agriculture. Environments 2017, 4, 50. [Google Scholar] [CrossRef]
- Dhillon, V.; Metcalf, D.; Hooper, M. Ethereum Tokens: High-Performance Computing. In Blockchain Enabled Applications; Apress: Berkeley, CA, USA, 2017; pp. 79–109. [Google Scholar]
- Park, Y.; Sur, C.; Kim, H.; Rhee, K.-H. A Reliable Incentive Scheme Using Bitcoin on Cooperative Vehicular Ad Hoc Networks. IT Converg. Pract. 2017, 5, 34–41. [Google Scholar]
- Li, L.; Liu, J.; Cheng, L.; Qiu, S.; Wang, W.; Zhang, X.; Zhang, Z. CreditCoin: A Privacy-Preserving Blockchain-Based Incentive Announcement Network for Communications of Smart Vehicles. IEEE Trans. Intell. Transp. Syst. 2018, 19, 2204–2220. [Google Scholar] [CrossRef]
- Bergquist, J.; Laszka, A.; Sturm, M.; Dubey, A. On the Design of Communication and Transaction Anonymity in Blockchain-Based Transactive Microgrids. In Proceedings of the 1st Workshop on Scalable and Resilient Infrastructures for Distributed Ledgers-SERIAL’17, Las Vegas, NV, USA, 11–15 December 2017; ACM Press: New York, NY, USA, 2017; pp. 1–6. [Google Scholar]
- Castellanos, J.A.F.; Coll-Mayor, D.; Notholt, J.A. Cryptocurrency as Guarantees of Origin: Simulating a Green Certificate Market with the Ethereum Blockchain. In Proceedings of the 2017 IEEE International Conference on Smart Energy Grid Engineering (SEGE), Oshawa, ON, Canada, 14–17 August 2017; pp. 367–372. [Google Scholar]
- Bentov, I.; Gabizon, A.; Mizrahi, A. Cryptocurrencies Without Proof of Work; Springer: Berlin/Heidelberg, Germany, 2016; pp. 142–157. [Google Scholar]
- Dhillon, V.; Metcalf, D.; Hooper, M. Recent Developments in Blockchain. In Blockchain Enabled Applications; Apress: Berkeley, CA, USA, 2017; pp. 151–181. [Google Scholar]
- LO3 Energy Homepage. Available online: https://lo3energy.com/ (accessed on 22 August 2018).
- Power Ledger (POWR) Whitepaper. Available online: https://whitepaperdatabase.com/power-ledger-powr-whitepaper/ (accessed on 22 August 2018).
- Grid Singularity Homepage. Available online: https://gridsingularity.com/ (accessed on 22 August 2018).
- Rahulamathavan, Y.; Phan, R.C.-W.; Rajarajan, M.; Misra, S.; Kondoz, A. Privacy-Preserving Blockchain Based IoT Ecosystem Using Attribute-Based Encryption. In Proceedings of the 2017 IEEE International Conference on Advanced Networks and Telecommunications Systems (ANTS), Bhubaneswar, India, 17–20 December 2017; pp. 1–6. [Google Scholar]
- Ateniese, G.; Magri, B.; Venturi, D.; Andrade, E. Redactable Blockchain – or – Rewriting History in Bitcoin and Friends. In Proceedings of the 2017 IEEE European Symposium on Security and Privacy (EuroS&P), Paris, France, 26–28 April 2017; pp. 111–126. [Google Scholar]
- Wang, J.; Li, M.; He, Y.; Li, H.; Xiao, K.; Wang, C. A Blockchain Based Privacy-Preserving Incentive Mechanism in Crowdsensing Applications. IEEE Access 2018, 6, 17545–17556. [Google Scholar] [CrossRef]
- Cha, S.-C.; Tsai, T.-Y.; Peng, W.-C.; Huang, T.-C.; Hsu, T.-Y. Privacy-Aware and Blockchain Connected Gateways for Users to Access Legacy IoT Devices. In Proceedings of the 2017 IEEE 6th Global Conference on Consumer Electronics (GCCE), Nagoya, Japan, 24–27 October 2017; pp. 1–3. [Google Scholar]
- Banerjee, A.; Joshi, K.P. Link before You Share: Managing Privacy Policies through Blockchain. In Proceedings of the 2017 IEEE International Conference on Big Data (Big Data), Boston, MA, USA, 11–14 December 2017; pp. 4438–4447. [Google Scholar]
- Yan, Z.; Zhang, P.; Vasilakos, A.V. A Survey on Trust Management for Internet of Things. J. Netw. Comput. Appl. 2014, 42, 120–134. [Google Scholar] [CrossRef]
- Idelberger, F.; Governatori, G.; Riveret, R.; Sartor, G. Evaluation of Logic-Based Smart Contracts for Blockchain Systems; Springer: Cham, Switzerland, 2016; pp. 167–183. [Google Scholar]
- Stavropoulos, T.G.; Kontopoulos, E.; Bassiliades, N.; Argyriou, J.; Bikakis, A.; Vrakas, D.; Vlahavas, I. Rule-Based Approaches for Energy Savings in an Ambient Intelligence Environment. Pervasive Mob. Comput. 2015, 19, 1–23. [Google Scholar] [CrossRef]
- Bordel, B.; Miguel, C.; Alcarria, R.; Robles, T. A Hardware-Supported Algorithm for Self-Managed and Choreographed Task Execution in Sensor Networks. Sensors 2018, 18, 812. [Google Scholar] [CrossRef] [PubMed]
- Schnorr, C.P.; Jakobsson, M. Security of Signed ElGamal Encryption; Springer: Berlin/Heidelberg, Germany, 2000; pp. 73–89. [Google Scholar]
- Alcarria, R.; Bordel, B.; Martín, D.; De Rivera, D.S. Rule-Based Monitoring and Coordination of Resource Consumption in Smart Communities. IEEE Trans. Consum. Electron. 2017, 63, 191–199. [Google Scholar] [CrossRef]
- Zhang, F.; Cecchetti, E.; Croman, K.; Juels, A.; Shi, E. Town Crier: An Authenticated Data Feed for Smart Contracts. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security-CCS’16, Vienna, Austria, 24–28 October 2016; ACM Press: New York, NY, USA, 2016; pp. 270–282. [Google Scholar]
- Wang, T.; Song, L.; Han, Z.; Cheng, X.; Jiao, B. Power Allocation Using Vickrey Auction and Sequential First-Price Auction Games for Physical Layer Security in Cognitive Relay Networks. In Proceedings of the 2012 IEEE International Conference on Communications (ICC), Ottawa, ON, Canada, 10–15 June 2012; pp. 1683–1687. [Google Scholar]
- Sfichi, Ș. The Evolution of the Processing Power Needed by the Primary Cryptocurrencies and Its Profit. J. Appl. Comput. Sci. Math. 2018, 12, 44–49. [Google Scholar] [CrossRef]
- De Angelis, S.; Aniello, L.; Baldoni, R.; Lombardi, F.; Margheri, A.; Sassone, V. PBFT vs Proof-of-Authority: Applying the CAP Theorem to Permissioned Blockchain. In Italian Conference on Cyber Security; Springer: Berlin/Heidelberg, Germany, 2018; p. 11. [Google Scholar]
- Brewer, E. CAP Twelve Years Later: How the ‘Rules’ Have Changed. Computer (Long. Beach. Calif) 2012, 45, 23–29. [Google Scholar] [CrossRef]
- Per Capita Water Use. Water Questions and Answers. Available online: https://water.usgs.gov/edu/qa-home-percapita.html (accessed on 23 August 2018).

| Parameter | Value | Description |
|---|---|---|
| eip150Block | 2 | EIP150 since block #2: improvements for denial-of-service |
| eip150Hash | 0x0 | needed for fast sync |
| eip155Block | 3 | EIP155 since block #3: preventing replay attacks. |
| eip158Block | 3 | EIP158 since block #3: treating empty accounts as non-existent |
| epoch_lng | 30000 | Number of blocks after resetting pending votes |
| block_period | 10 s | Minimum difference between two consecutive block’s timestamps |
| extra-data | 65 bytes | Extra-data of each block enough to store the miner’s signature |
| nonce | {0xf, 0x0} | Vote on adding a new signer (0xf) or removing a signer (0x0) |
| signer_count | 3 | Number of authorized signers valid at a particular chain instance |
| signer_limit | 2 | Signer signs only one block out of signer_limit consecutive blocks for an in-turn signature |
| difficulty | {1, 2} | Block difficulty for blocks containing in-turn signatures (1) and out-of-turn signatures (2), with slight penalization |
| Attack | PoW | PoA |
|---|---|---|
| Malicious contributor | Malicious miner needs 51% of hashing power for successful attach | Any signer may only mint 1 block out of every K. Damage is limited. Signer can be voted out. |
| Censoring contributor | Miner censoring blocks is penalized and their blocks are rarely included in the chain | Signers censoring blocks with negative votes are limited to 1 block out of N/2 block. |
| Spamming contributor | Spamming transactions requires money to be spent on transaction fees | Signers injecting new vote proposals inside every block they mint is mitigated by placing a limit on the vote window. |
| Concurrent contributors | Concurrent block discovery is rare. In this case best fork is selected for chain continuation. | As at any point in time N-K + 1 miners are allowed to mint. To avoid racing we add a small random “offset” to the time it releases a new block. |
| Parameter | Value | Description |
|---|---|---|
| num_SH | 40 | Number of smart homes available in the smart community. |
| block_period | 10 s | Minimum difference between two consecutive block’s timestamps |
| [0, N] | Length of essential data set for basic quota control. | |
| [0, N] | Length of extended dataset for enhanced management. | |
| N | 10 KB | . |
| L | variable | Number of records of essential data set samples which are simultaneously stored in the blockchain. |
| f(block_period) | Sample generation period. | |
| G | {0.25, 0.5, 1, 2} | Number of samples that will be generated by smart home in the time in which a block is generated. |
| L | Solutions | |||
|---|---|---|---|---|
| Smonitoring | Monitoring | Sdelegation | Delegation | |
| 1 | 3.06 × 105 | 8.44 × 104 | 6.52 × 103 | 1.12 × 103 |
| 101 | 3.45 × 106 | 6.98 × 105 | 6.18 × 104 | 9.22 × 103 |
| 102 | 3.26 × 107 | 6.02 × 106 | 5.95 × 105 | 9.17 × 104 |
| 103 | 3.11 × 108 | 6.37 × 107 | 5.72 × 106 | 9.06 × 105 |
| 104 | 3.15 × 109 | 6.25 × 108 | 5.67 × 107 | 8.87 × 106 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alcarria, R.; Bordel, B.; Robles, T.; Martín, D.; Manso-Callejo, M.-Á. A Blockchain-Based Authorization System for Trustworthy Resource Monitoring and Trading in Smart Communities. Sensors 2018, 18, 3561. https://doi.org/10.3390/s18103561
Alcarria R, Bordel B, Robles T, Martín D, Manso-Callejo M-Á. A Blockchain-Based Authorization System for Trustworthy Resource Monitoring and Trading in Smart Communities. Sensors. 2018; 18(10):3561. https://doi.org/10.3390/s18103561
Chicago/Turabian StyleAlcarria, Ramon, Borja Bordel, Tomás Robles, Diego Martín, and Miguel-Ángel Manso-Callejo. 2018. "A Blockchain-Based Authorization System for Trustworthy Resource Monitoring and Trading in Smart Communities" Sensors 18, no. 10: 3561. https://doi.org/10.3390/s18103561
APA StyleAlcarria, R., Bordel, B., Robles, T., Martín, D., & Manso-Callejo, M.-Á. (2018). A Blockchain-Based Authorization System for Trustworthy Resource Monitoring and Trading in Smart Communities. Sensors, 18(10), 3561. https://doi.org/10.3390/s18103561









