2.1. Comprehensive Survey of Ad Hoc Routing Protocols
Given the importance of routing protocols to UAV networks, a significant amount of research has emerged over the past decade, including performance evaluation of routing protocols in FANET scenarios and design and optimization of routing protocols tailored for UAV networks. In recent years, a significant number of review papers have emerged to provide a more in-depth analysis of the technical challenges, research advancements, and development trends in FANET routing protocols, aiming to offer a better summary of research in this field [
4,
45,
46,
47,
48,
49,
50,
51,
52]. For example, Arafat et al. provided a comprehensive review of communication strategies for UAV networks, categorizing and surveying them into topology-based, geographical, hierarchical, deterministic, and stochastic frameworks. Subsequently, a qualitative assessment was conducted to compare these protocols based on their core characteristics and efficiency. Then, the routing protocols were compared qualitatively considering their major features and performance. They also discussed the open problems and research directions from the perspective of design and development [
45].
Oubbati et al. provided an extensive overview that examines the structural architecture and design constraints of UAV networks. Their work also details diverse mobility models and routing protocols, as well as specialized simulation platforms. Existing important routing protocols dedicated to UAV networks were classified, described, and compared in detail. Moreover, they depicted future research challenges for UAV networks [
46]. After presenting typical UAV communication network architectures, Lakew et al. provided an extensive overview of current pathfinding schemes tailored for FANETs. Moreover, they highlighted the key characteristics, advantages and disadvantages, and various mobility models employed for performance evaluation of existing MANET routing protocols. Finally, they highlighted existing open problems and research challenges in UAV networks [
4].
Nazib et al. delivered a meticulous review of current routing mechanisms for UAV-assisted vehicular networks. They categorized these protocols into seven distinct groups based on their foundational principles, followed by a qualitative comparison of their design characteristics, operational parameters, and efficiency indicators. Furthermore, the study delved into optimization strategies to offer valuable insights for both the scientific and engineering communities [
47]. Abdulhae et al. presented an extensive overview regarding the cluster-based routing schemes, focusing on their advantages, disadvantages, application domains, supported number of nodes, and possible improvements for serving UAV networks. In addition, several UAV networks using cluster-based routing protocols were analyzed in terms of their topology structure, clustering method, scalability, cluster head selection scheme, reliability, performance metrics, and measurements [
48].
Cao et al. provided a comprehensive overview of computational intelligence (CL)-based networking and collaboration algorithms from six typical aspects including channel access, network routing, cooperative task assignment, cooperative path planning, cooperative search, and cooperative jamming. To help researchers choose appropriate algorithms to satisfy the requirements of different missions, they classified CI-based algorithms into four categories, namely, heuristic behavior search-based algorithms, policy design-based algorithms, policy learning-based algorithms, and hybrid algorithms [
49]. Oubbati et al. discussed the main features of Network Function Virtualization (NFV) and Software-Defined Network (SDN) technologies in FANETS. Moreover, they provided a thorough discussion of the different types, application scenarios, and difficulties associated with UAV-assisted systems. Their study then explored SDN/NFV-enabled aerial platforms, along with several case studies and issues, such as the involvement of UAVs in cellular communications, monitoring, and routing, to name a few [
50].
Mansoor et al. examined several state-of-the-art routing protocols specially designed for UAV networks, including their design principles. Although these protocols address various considerations regarding the development of routing protocols for UAV networks, certain obstacles persist. Therefore, they provided a detailed survey of current routing protocols in UAV networks, as well as a discussion of some open issues [
51]. Al-Emadi et al. meticulously reviewed the latest network architectures and various routing protocols designed for ad hoc networks. These categories comprise the proactive, reactive, and hybrid routing protocols and their enhanced variants deployed in UAV networks. Moreover, they developed a customized network architecture based on clustering with the purpose of dealing with the problems in existing works [
52].
Although these surveys provide a detailed exposition on the technical challenges, research advancements, and development trends of FANET routing protocols, particularly offering in-depth comparisons and analyses of the applicability of various ad hoc routing protocols in FANETs, these comparative analyses are primarily qualitative rather than quantitative. By synthesizing available research focused on evaluating the performance of routing protocols in UAV networks, these surveys analyze the potential and problems of using traditional ad hoc routing protocols in FANET scenarios, starting from the principles of these routing protocols. However, they have not compared the performance of typical routing protocols horizontally through numerical simulation or actual testing, especially the relative performance under different mobility models. Therefore, they cannot provide quantitative guidance for selecting a routing protocol that is suitable for the target scenario.
2.2. Evaluation of Single Routing Protocol Under Single Mobility Model
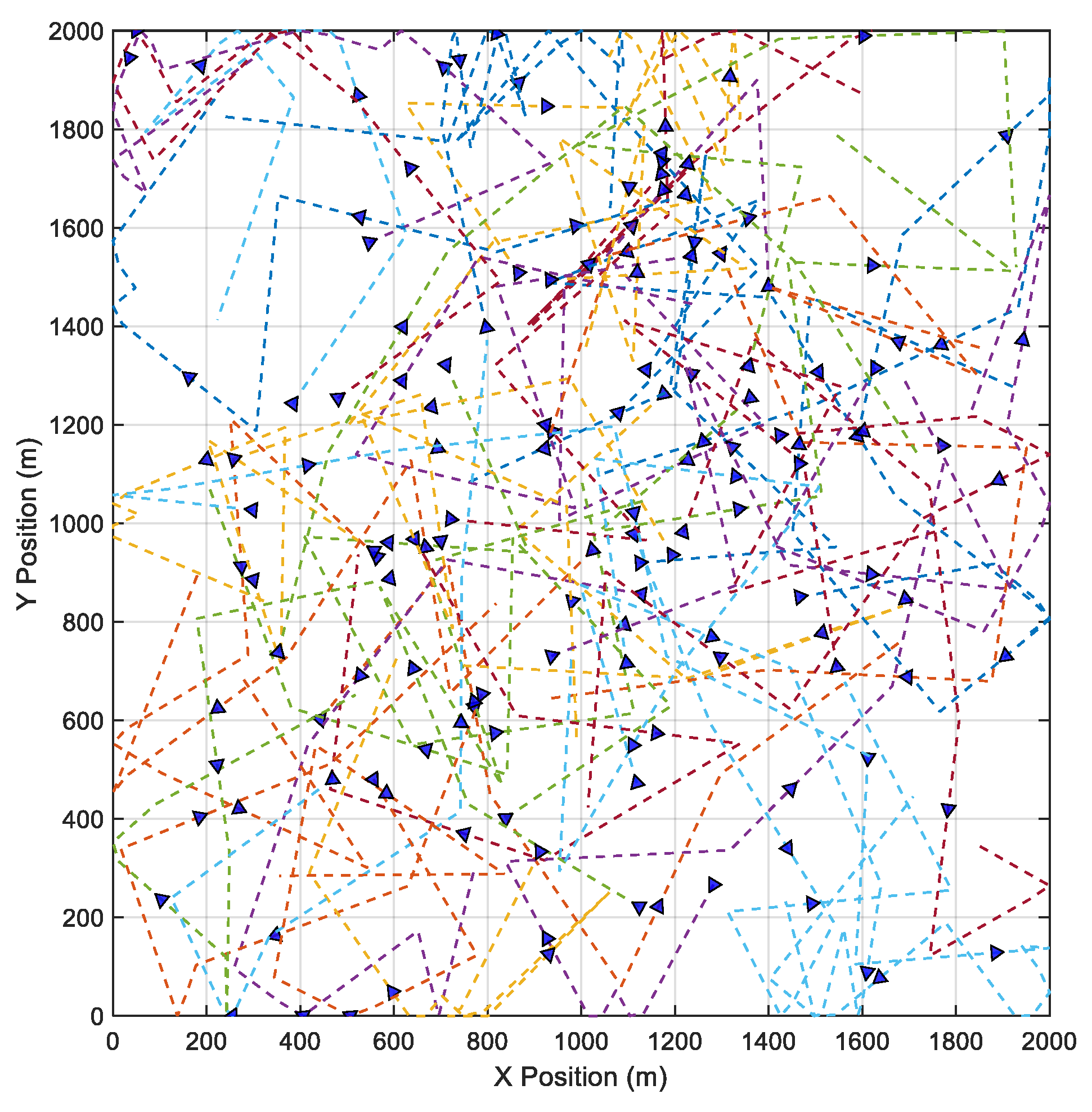
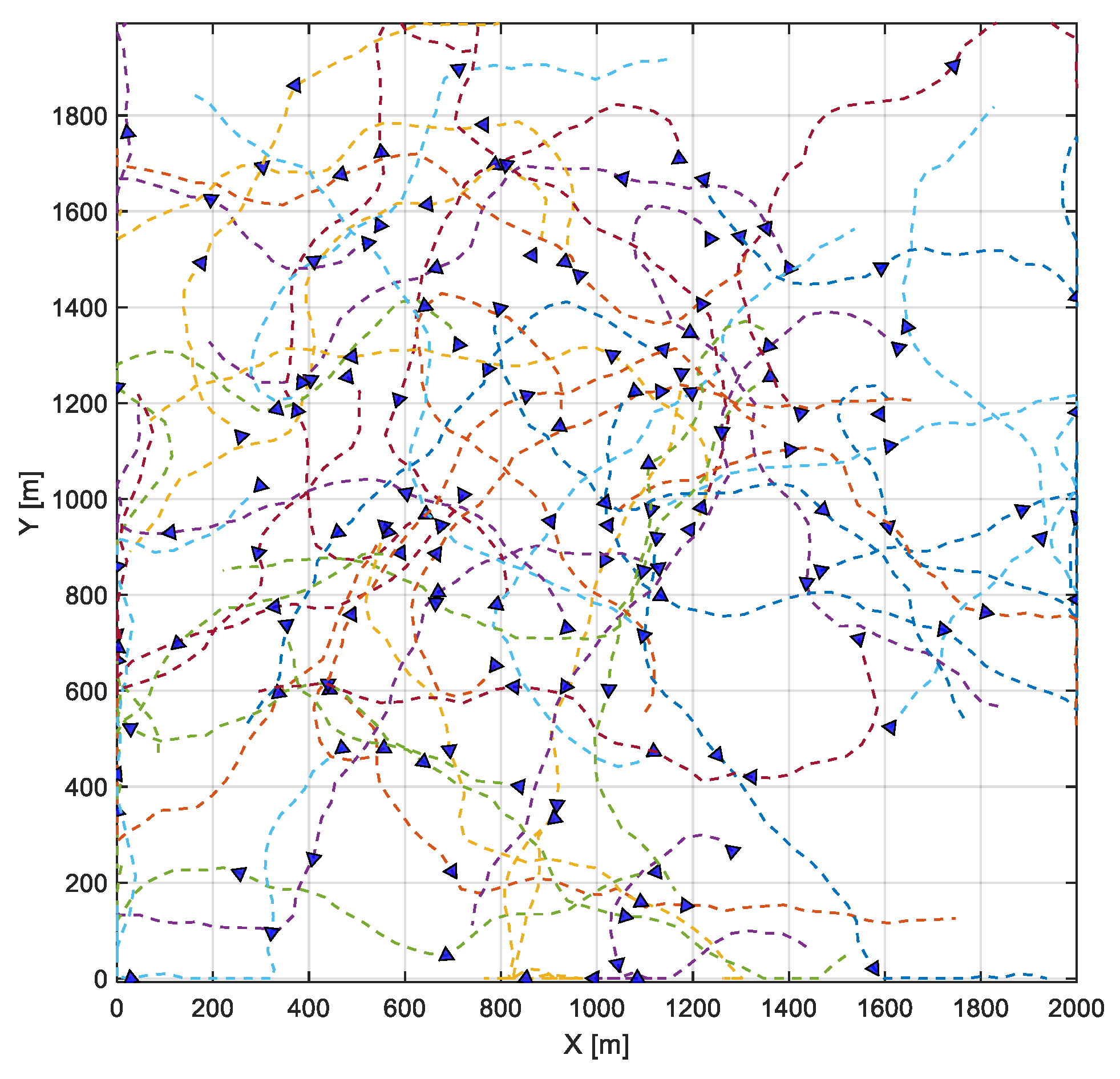
To directly port traditional ad hoc routing protocols to FANETs, it is necessary to evaluate whether the selected protocol is suitable for FANET application scenarios, as FANETs have significantly different node speeds, movement trajectories, and so on compared to traditional networks. Considering the complexity and cost of actual UAV network testing, existing studies mostly use network simulators such as NS [
53], OMNET++ [
54], etc., for the performance assessment of routing protocols. These studies simulate and analyze the performance of the target protocol in specific FANET scenarios by selecting or designing appropriate mobility models while considering the typical speed of UAVs. For example, Huang et al. examined how OLSR performs in NS3 simulations by incorporating the Gauss Markov (GM) mobility model. They also used the position of nodes in 3D space to predict the link duration to improve the construction of the routes between nodes. Experimental outcomes demonstrated that the introduced approach enhances the PDR while minimizing the E2ED [
5].
Gangopadhyay et al. evaluated the performance of OLSR using NS3 under the GM mobility model. They also proposed an enhanced OLSR protocol which uses the position of nodes for efficient MPR selection. The enhanced OLSR protocol addresses the high mobility of nodes and rapid changes in topology. This is accomplished by considering the residual energy and node degree of UAVs and combining the position information of the UAV, which serves to calculate the link expiration time [
6]. Leonov et al. evaluated the packet delivery performance of OLSR in FANET scenarios using the NS2 simulator and the Random Waypoint (RWP) mobility model. By configuring different parameters of OLSR, the change in packet delivery performance and the main factors causing packet loss were analyzed [
7].
Cett et al. evaluated OLSR’s performance across varying scenarios of movement velocity and node concentration using NS2. The metrics for evaluation included mean data throughput, PDR, and average packet latency. They found that the execution of the MPR technique effectively curtails unnecessary data relaying throughout the normal message broadcast. Therefore, the number of unnecessary broadcasts can be decreased [
8]. Wheeb et al. examined the performance of the original and modified OLSR protocols in UAV ad hoc networks for three search and rescue scenarios. The performance metrics of these routing protocols including PDR, latency, energy consumption, and throughput were simulated using NS3. According to the simulation data, it was observed that the modified OLSR outperforms the original one in the considered measures [
9].
Arya et al. developed a complete simulation framework to simulate different network circumstances and situations. A number of performance metrics, such as total packets received, average E2ED, and throughput, served as benchmarks for gauging the efficiency of the AODV routing protocol under the RWP mobility model. The simulation scenarios taken into account different node densities and traffic loads in order to give a comprehensive evaluation of the behavior of the protocol [
10]. Ching et al. evaluated the effectiveness of AODV and analyzed the impacts of mobility speed and node density using NS3. Performance metrics used were PDR, throughput, and average E2ED. Numerical analysis demonstrated that mobility speed and node density affect the operational efficiency of AODV in ad hoc networks [
11].
Prasad et al. evaluated the performance of the AODV protocol under the free space, two-ray ground reflection, and shadowing fading channel models and also under different scenarios. NS3 was used and the mobility model is RWP. It showed that the AODV protocol could construct the routes in the given scenarios with severe fading [
12]. Fiade et al. compared the consequences of blackhole versus flooding intrusions targeting AODV on vehicle networks using several simulators such as SUMO, NS2, and NAM. To measure the quality of service (QoS), throughput, packet loss, and E2ED were monitored. The simulation results demonstrated that peak throughput is achieved in a healthy environment, while a blackhole attack triggers the most severe packet loss. Flooding attacks, conversely, lead to the highest E2ED and residual energy levels [
13].
Menaka et al. analyzed the performance of DSR in FANET scenarios using NS2 under the RWP mobility model. Performance metrics, such as route discovery time, route requests sent, and throughout were employed [
14]. Gumaste et al. analyzed the DSR protocol by extensive simulations in NS2 simulator under the RWP mobility model with various performance metrics such as PDR, E2ED, routing overhead, and throughput under various scenarios. They found that it is possible to observe the operational behavior of routing protocols within network nodes through digital simulation environments [
15].
Table 1 summarizes the protocols as well as the simulators and mobility models used in the aforementioned works. It can be clearly seen that these works evaluated the performance of a specific ad hoc routing protocol in UAV network scenarios with a specific mobility model using simulators. The main objective of these works is to evaluate the availability of a specific routing protocol in UAV network scenarios, without involving mutual comparison between different routing protocols nor considering the way routing protocols are influenced by varying mobility models.
2.3. Evaluation of Multiple Routing Protocols Under Single Mobility Model
Depending on the neighboring node discovery mechanism, path selection algorithm, etc., used, different ad hoc routing protocols are generally optimal for different network application scenarios. To assess the comparative performance of ad hoc routing protocols in UAV-based environments, numerous investigations have evaluated and compared different routing protocols through simulation. For example, Ferronato et al. investigated how the OLSR, AODV, and Zone Routing Protocol (ZRP) perform using NS2 under real urban vehicular scenarios. The results showed that the OLSR protocol obtains the greatest reduction in overhead and the AODV protocol obtains better performance for the transfer rate. Meanwhile, the hybrid protocol ZRP obtains the best results in terms of the reduction in E2ED and increase in PDR [
16]. Tan et al. developed a more realistic simulation environment using OPNET and evaluated and compared the performance of four typical routing protocols, AODV, DSR, OLSR, and GRP. The performance metrics used were network delay, packet received, packet lost, and throughput. The adaptability of routing protocols to specific UAV network settings was confirmed through simulation findings [
17].
Khanh et al. considered in detail the requirements of modern 6G UAV communications and then constructed a highly authentic simulation setup via NS3. This allowed for testing the effectiveness of standard AODV, DSR, and OLSR protocols across latency, PDR, and routing overhead dimensions. Such quantitative findings provide key insights for selecting suitable routing protocols in different 6G UAV scenarios [
18]. Tuli et al. evaluated four specific table-driven routing solutions (DSR, AODV, GRP, and OLSR) using the OPNET simulator. The assessment parameters primarily consisted of throughput, delay, and packet loss rate [
19]. Rani et al. produced a more lifelike simulation context in NS3 to benchmark four classic routing protocols (AODV, DSDV, DSR, and OLSR) through PDR and throughput analysis. The results demonstrate that alternative routing strategies may function effectively in several UAV communication network circumstances [
20].
Hussen et al. analyzed the performance of several ad hoc routing protocols in UAV networks using the OPNET 18.6 software. Four routing protocols were chosen for comparison, including AODV, DSR, GRP, and OLSR [
21]. Singh et al. conducted simulation analysis on AODV, DSDV, and OLSR routing protocols in UAV networks with NS2, in which simulated trajectories of real UAV scenarios were used [
22]. Jorge et al. analyzed the performance of various routing protocols OLSR, DSDV, AODV, DSR, AOMDV, and HWMP through simulations in NS3 based on throughput, PDR, and average delay under different speeds with tests conducted using 25 and 50 UAVs. The results provide insights into the efficiency of these protocols in static and dynamic environments, offering valuable information for the design and optimization of UAV communication networks [
23].
Leonov et al. evaluated the performance of AODV alongside OLSR in ad hoc clusters of mini drones using NS2. The protocols were evaluated with several variables such as the density of UAVs, the mobility of nodes, and the communication range. It was demonstrated that these parameters substantially influence how routing protocols perform. The performance metrics considered in this work were lost packets and PDR [
24]. Zheng et al. evaluated the performance of OLSR, AODV, and BATMAN-ADV using OPNET under real flying trajectories. The simulation results showed that, compared with OLSR and AODV, BATMAN-ADV is more suitable for application in large-scale, high-dynamic, and high-load UAV network scenes [
25]. Diniz et al. carried out experiments in real environments using Raspberry Pi devices to benchmark the operational capabilities of the OLSR, BATMAN-ADV, and Babel protocols. Experimental results demonstrate that OLSR exhibits superior robustness and effectiveness under fluctuating traffic volumes, stemming from its fast route reconfiguration. In high-mobility contexts, Babel outshines others by offering reduced latency, thanks to its nimble topology refresh mechanism. Conversely, despite its efficiency in specific settings, BATMAN-ADV suffers from increased overhead and volatility when subjected to intensive data traffic [
26].
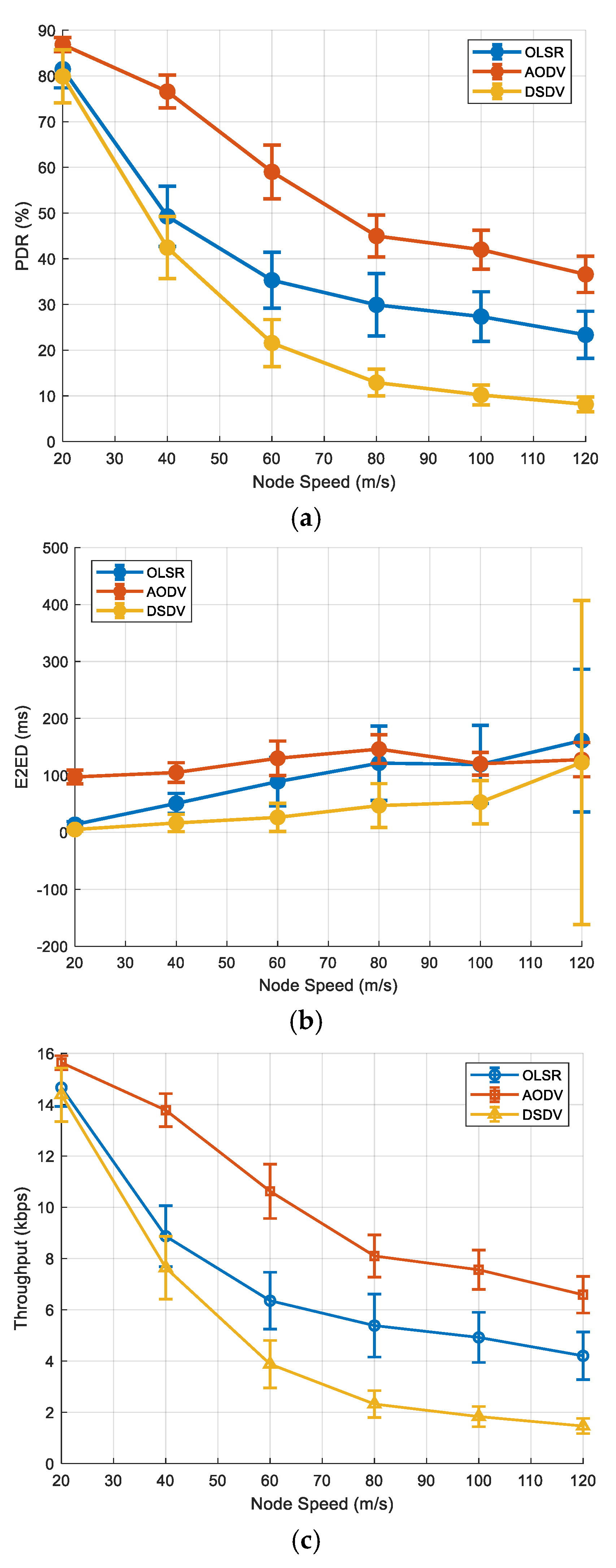
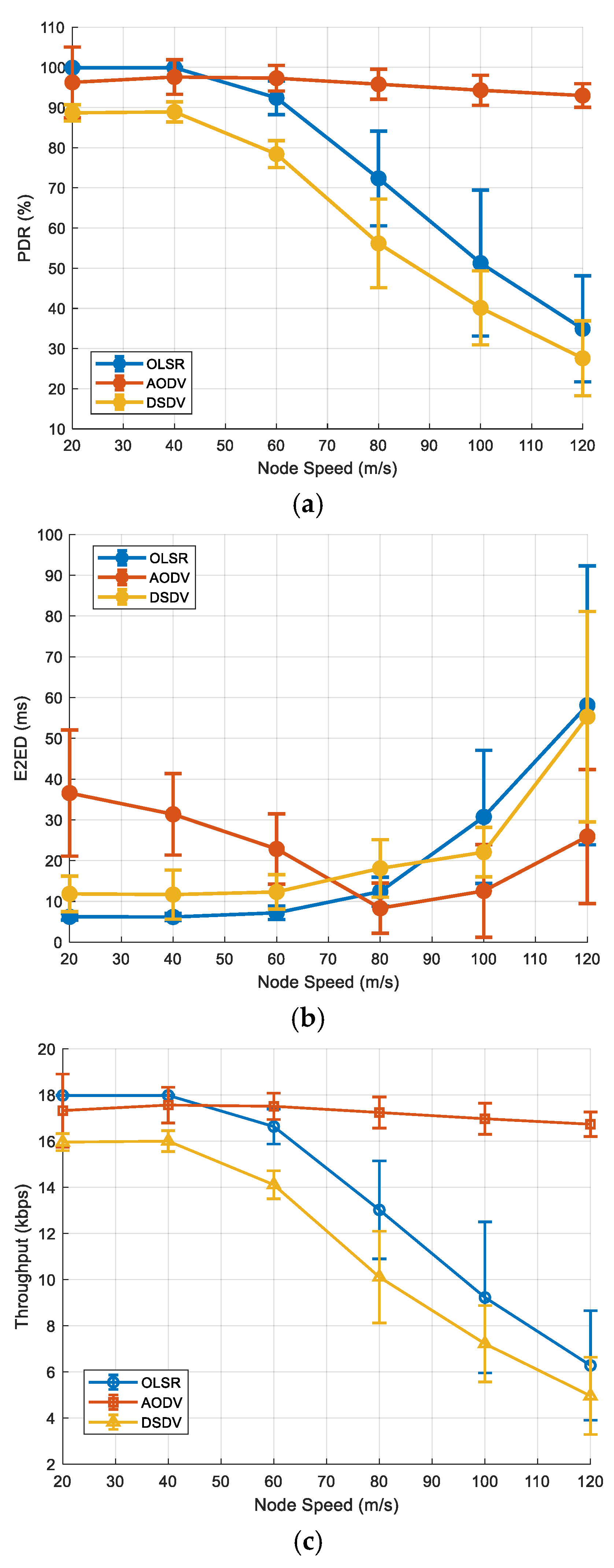
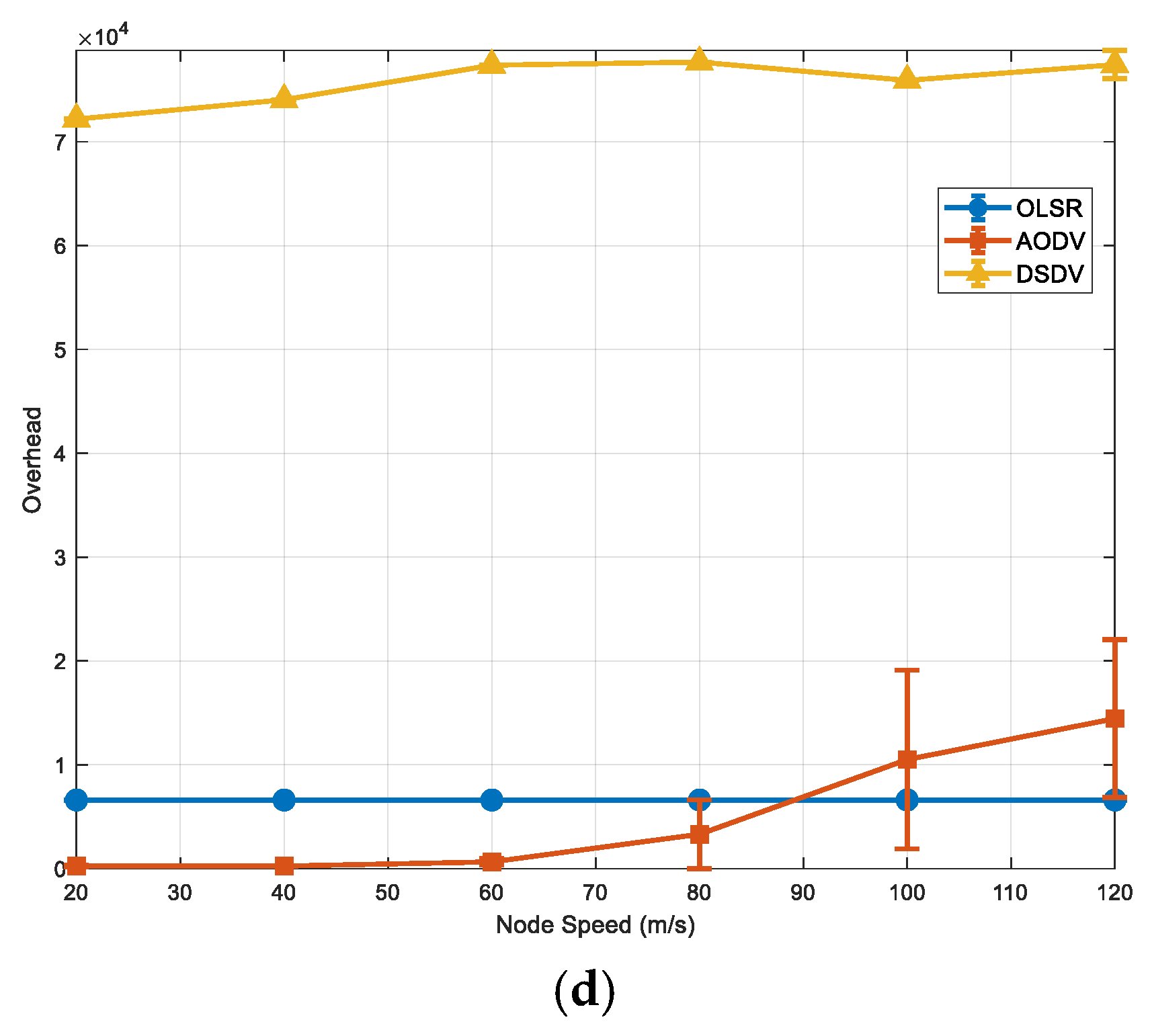
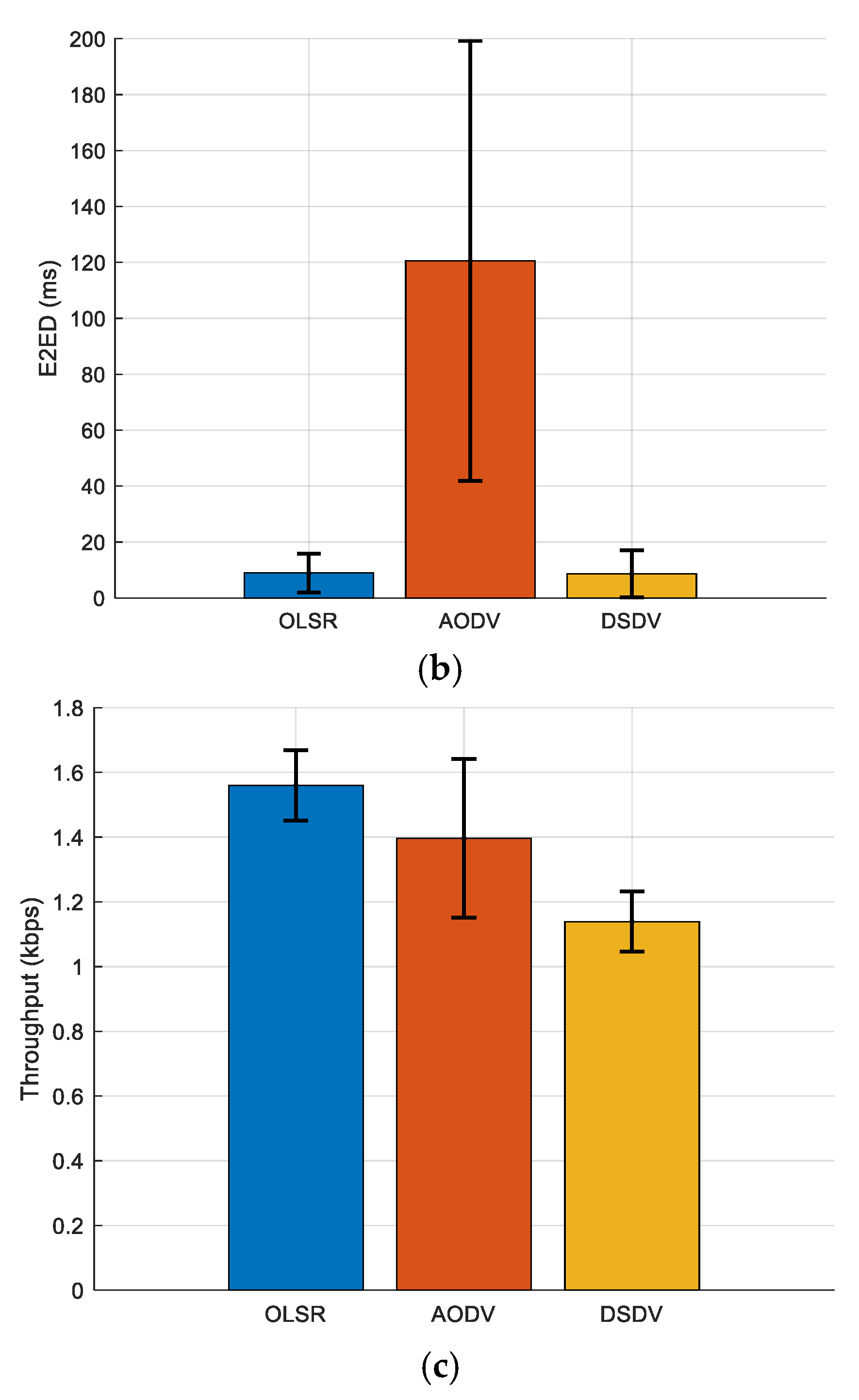
Gupta et al. investigated the AODV, DSDV, and OLSR routing schemes within the NS3 simulation environment, utilizing multiple metrics such as PDR, packet drop rate, throughput, latency, and jitter. The effectiveness of these protocols was evaluated in the presence of varying UAV speeds. It carefully explored how different routing protocols function under varied UAV intensities and speeds [
27]. Gupta et al. examined the performance of AODV, DSDV, OLSR, and DSR through comprehensive simulation for their suitability in FANETs. By fluctuating the velocity and concentration of nodes, the packet reception rate was documented. The NS3-based analysis revealed that AODV demonstrates superior efficiency compared to its counterparts in the aforementioned contexts [
28]. Choudhary et al. evaluated and compared the performance of AODV, OLSR, DSDV, and DSR suitable for UAV-assisted communication networks. Through extensive simulation experiments utilizing NS3, the performance of these protocols was assessed based on network parameters such as delay, throughput, jitter, and packet loss ratio. The results demonstrated that OLSR exhibits optimal routing performance for smaller areas and less nodes. However, DSR performs better when both the network area and the number of nodes increased [
29].
Basu et al. employed different wireless channel models to conduct a comparative study of routing schemes in UAV networks. Specifically, their simulation outputs for Lutz and ITU models were used to benchmark AODV against DSDV, both of which are widely used MANET protocols. The simulator was developed using Matlab (R2022a) and the mobility model used was GM [
30]. Feng et al. investigated the operational efficiency of AODV, DSDV, and OLSR by analyzing metrics such as packet delivery rate, E2ED, and throughput. It was found that all three protocols perform similarly and effectively in low-speed scenarios. In the medium-speed scenario, OLSR performs better than both AODV and DSDV routing protocols. In the high-speed scenario, without considering data delay, AODV performs better than both DSDV and OLSR routing protocols [
31]. Pandey et al. compared the performance of DSR, AODV, OLSR, and ZRP for UAV-enabled telecommunications networks. Actual-world datasets of UAV trajectories were employed in combination with the COMSNET simulator. The data revealed that DSR surpasses AODV and OLSR in terms of latency and packet shipping ratio. However, further evaluation discovered that AODV and OLSR had superior overall performance beneath varying mobility styles [
32].
Ahmed et al. investigated how the AODV, OLSR, and DSDV protocols behave using OMNET++. They found that in a high percentage of tests, AODV surpasses both OLSR and DSDV. The overall throughput, PDR, and E2ED are heavily influenced by the network’s node density. OLSR is well-suited for scenarios necessitating low delay, while DSDV delivered the poorest PDR and throughput [
33]. Kamble et al. investigated OLSR, AODV, and DSDV in terms of PDR, average throughput, E2ED, and delay jitter using NS3. The 2D random walk mobility model was used. From the simulation results, they found that AODV outperforms OLSR and DSDV in FANETs [
34]. Huang et al. evaluated the routing protocols AODV, DSDV, and OLSR using the NS3 simulator and real UAV trajectories. The results showed that DSDV is suitable for simple communication between UAV groups, while AODV is suitable for complex communication between UAV groups [
35].
Table 2 summarizes the protocols as well as the simulators and mobility models used in the aforementioned works. These works clearly demonstrate how diverse routing protocols perform across UAV network settings through the application of various simulators. These evaluations and comparisons used a specific mobility model and did not take into account the impacts of different mobility models on the relative performance of routing protocols, that is, whether the use of different mobility models would affect the judgment of performance differences in routing protocols.
2.4. Evaluation of Single Routing Protocol Under Multiple Mobility Models
Different mobility models use different methods to describe the behavior of mobile nodes. In order to evaluate the impact of mobility models on routing protocol performance, some studies have conducted simulation analysis on the performance of a specific routing protocol under various mobility models. For example, Hameurlaine et al. evaluated the performance of OLSR utilizing NS2 by analyzing how various factors, such as operational area size, mobility models, node speed, and traffic rate, impact the PDR. Several mobility models, including time and random and group-based movements, were employed to simulate realistic UAV behaviors. The findings emphasized the significant impact of area size on OLSR’s performance, providing valuable insights for optimizing FANET deployments and enhancing the reliability and efficiency of these systems in critical applications [
36].
Singh et al. thought that the mobility model plays a very essential role in optimizing the performance of routing protocols in UAV networks. Therefore, they applied the OLSR protocol in FANETs and evaluated it under different mobility models to optimize the performance of OLSR in FANETs. The mobility models used were RWP, Reference Point Group Mobility, Manhattan Grid, and Pursue models [
37]. Bezziane et al. evaluated the performance of GPSR under various mobility models, including GM, Mass Mobility, and RWP mobility models, to uncover their strengths and limitations. The simulation results revealed notable variations in performance indicators, including E2ED, PDR, and loss rate across various mobility models. These findings offer valuable insights for selecting the most suitable mobility model for specific applications, and improving routing protocols, thereby advancing the reliability and effectiveness of FANETs [
38].
By analyzing data packet transmission and node movement, Mowla et al. found that the mobility model plays an important role to enhance network performances. Therefore, five mobility models, including Manhattan Grid, Boundless, Column, Nomadic, and RWP were employed for comparative analysis in FANETs. The performance analysis of different performance metrics (PDR, throughput, packet loss, E2ED, delay jitter, and control overhead) were analyzed using the AODV routing protocol for those models [
39]. Wheeb et al. assessed how OLSR behaves across a variety of stochastic and collective mobility models. The study employed two simulation configurations to examine different motion models. NS3 was used to develop the simulation environments. Findings from the simulation indicate that while RWP yields optimal OLSR efficiency in low-velocity settings, the Nomadic model is more compatible with the OLSR protocol when node speeds increase [
40].
Nurwarsito et al. analyzed the impact of mobility on the performance of OLSR using NS3 with PDR, E2ED, and routing overhead. PDR showed the highest value on GM with 80 nodes. The best E2ED was seen in GM with 20 nodes. The routing overhead was the best under the random walk model with 20 nodes [
41]. Patel et al. characterized the performance of AODV for different mobility scenarios including random movement scenarios, determined movement scenarios, and realistic mobility models. Several parameters such as E2ED, number of received packets, control overhead, PDR, and throughput were evaluated using NS2 [
42].
Essa et al. investigated the performance of the AODV protocol with different transmit powers under several mobility models including RWP, Mass Mobility and Linear mobility. They also examined the sensitivity of network metrics to changes in node count, travel speed, and simulation boundaries. Utilizing the OMNeT++ and INET framework, the researchers analyzed AODV’s PDR, end-to-end delay, and throughput across various MANET scenarios [
43]. Wahanani et al. integrated the Manhattan mobility framework into DSR to compare it with the existing RWP in NS2. The evaluation spanned multiple network scales, varying node speeds, and distinct simulation terrains. Performance metrics used included PDR and average E2ED. The results showed that the performance of DSR will be affected by different mobility models [
44].
Table 3 summarizes the protocols as well as the simulators and mobility models used in the aforementioned works. It can be clearly seen that these works evaluated and compared the performance of a specific routing protocol under several mobility models using simulators. However, they did not take into account the relative performance of different routing protocols under different mobility models. Therefore, it cannot be determined whether the performance differences between different routing protocols under a specific mobility model depend on the mobility model used.