Critical Infrastructure Surveillance Using Secure Wireless Sensor Networks
Abstract
:1. Introduction
2. Requirement Analysis
3. Network Design and Architecture
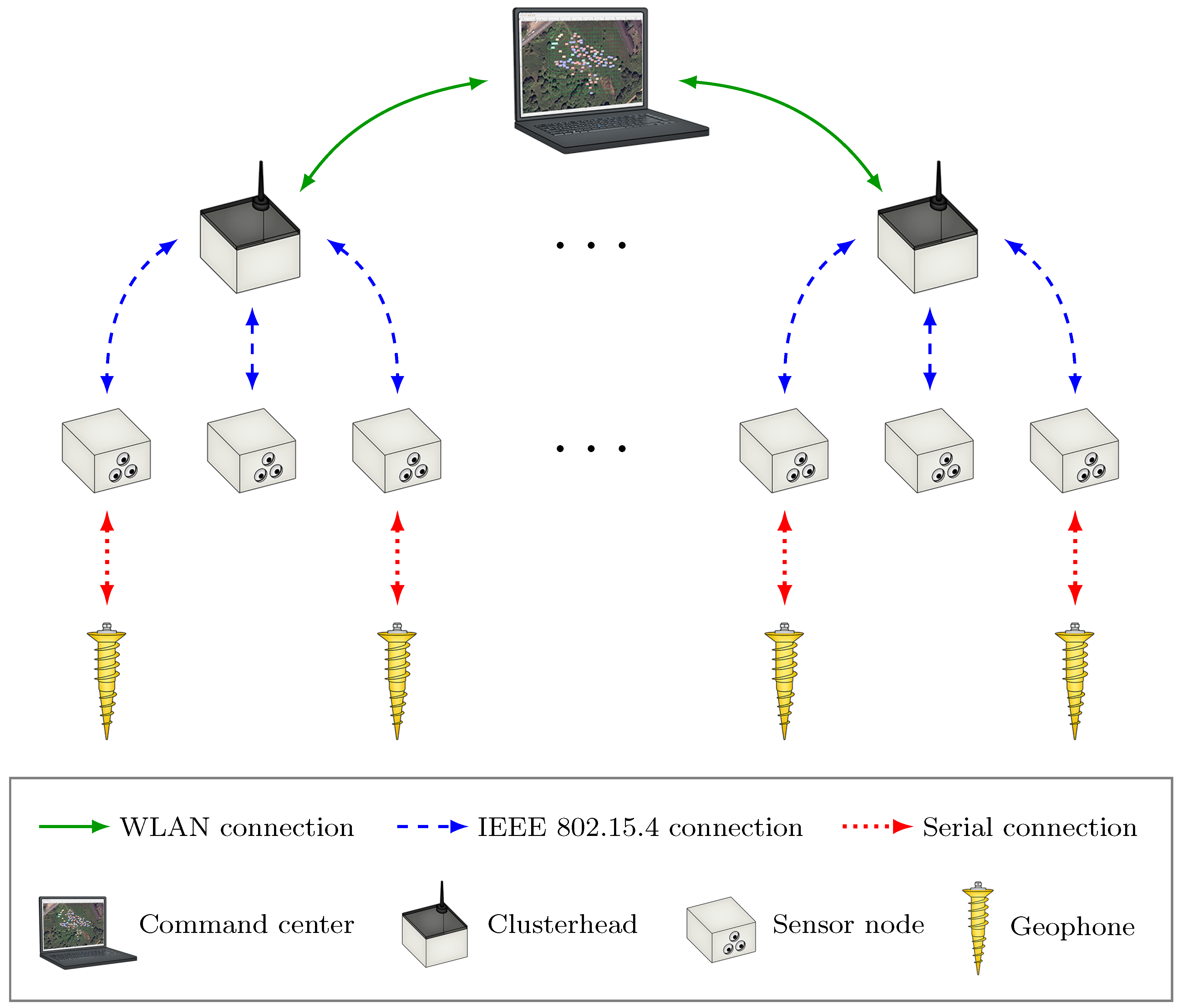
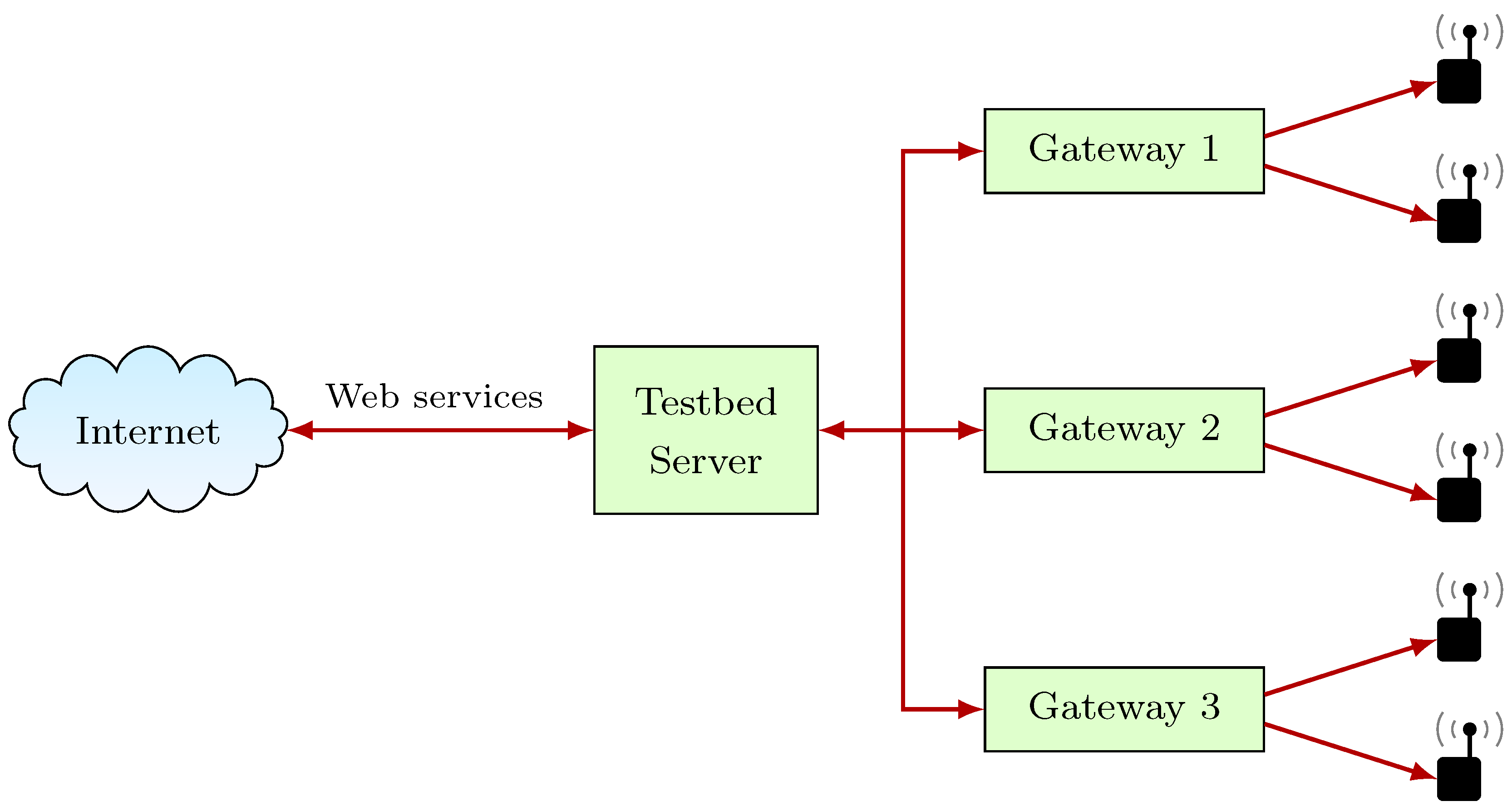
3.1. Network Overview
| Sensor Type | Number of Nodes Equipped | Node Type Equipped |
|---|---|---|
| AMR | 90 | Sensor nodes |
| Accelerometer | 90 | Sensor nodes |
| Single-PIR | 45 | Sensor nodes |
| Multi-PIR | 45 | Sensor nodes |
| Longrange-PIR | 10 | Sensor nodes |
| Geophone | 50 | Sensor nodes |
| GPS | 10 | Clusterheads |
3.2. Hardware
3.2.1. Command Center
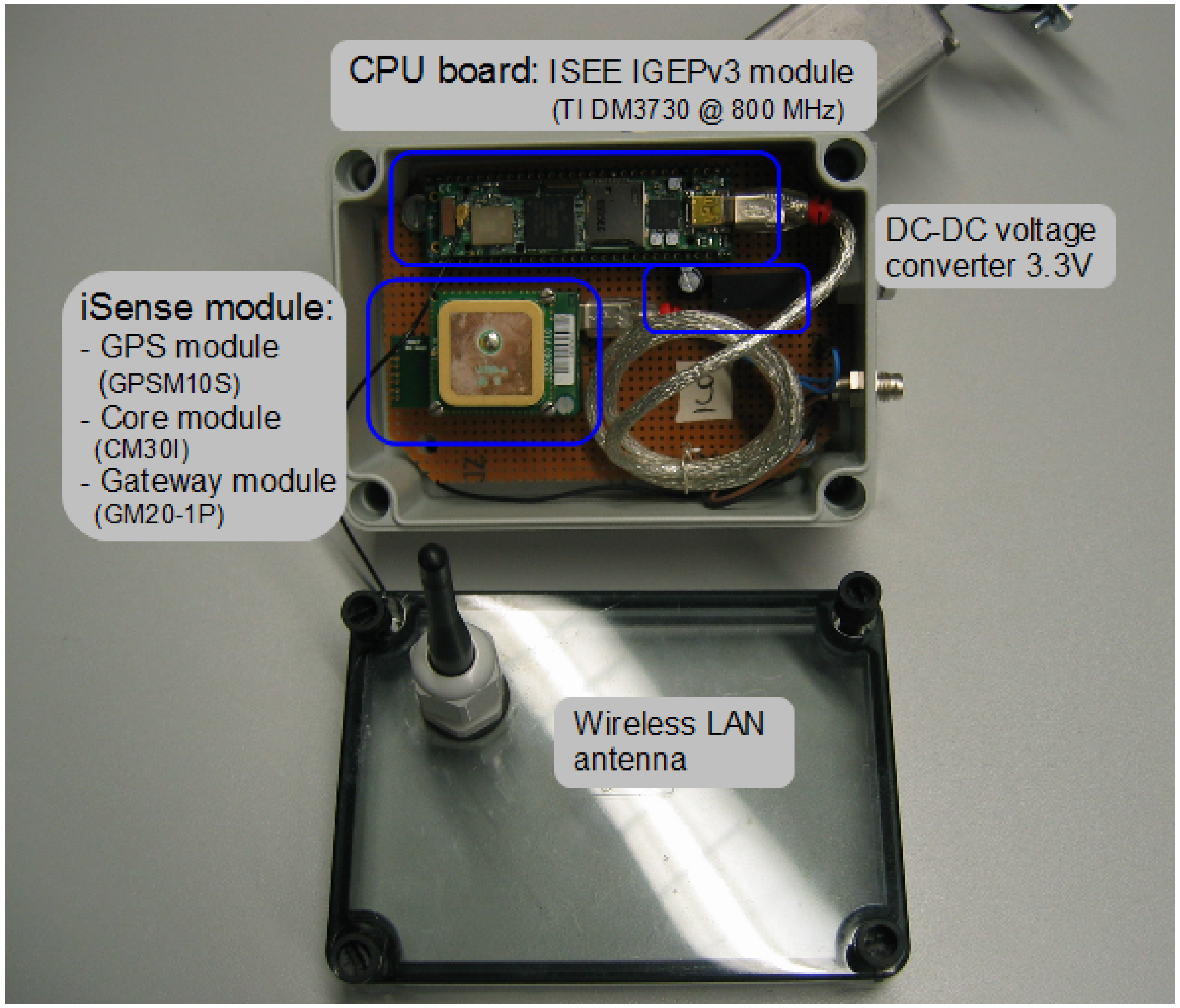
3.2.2. Clusterheads
3.2.3. Sensor Nodes
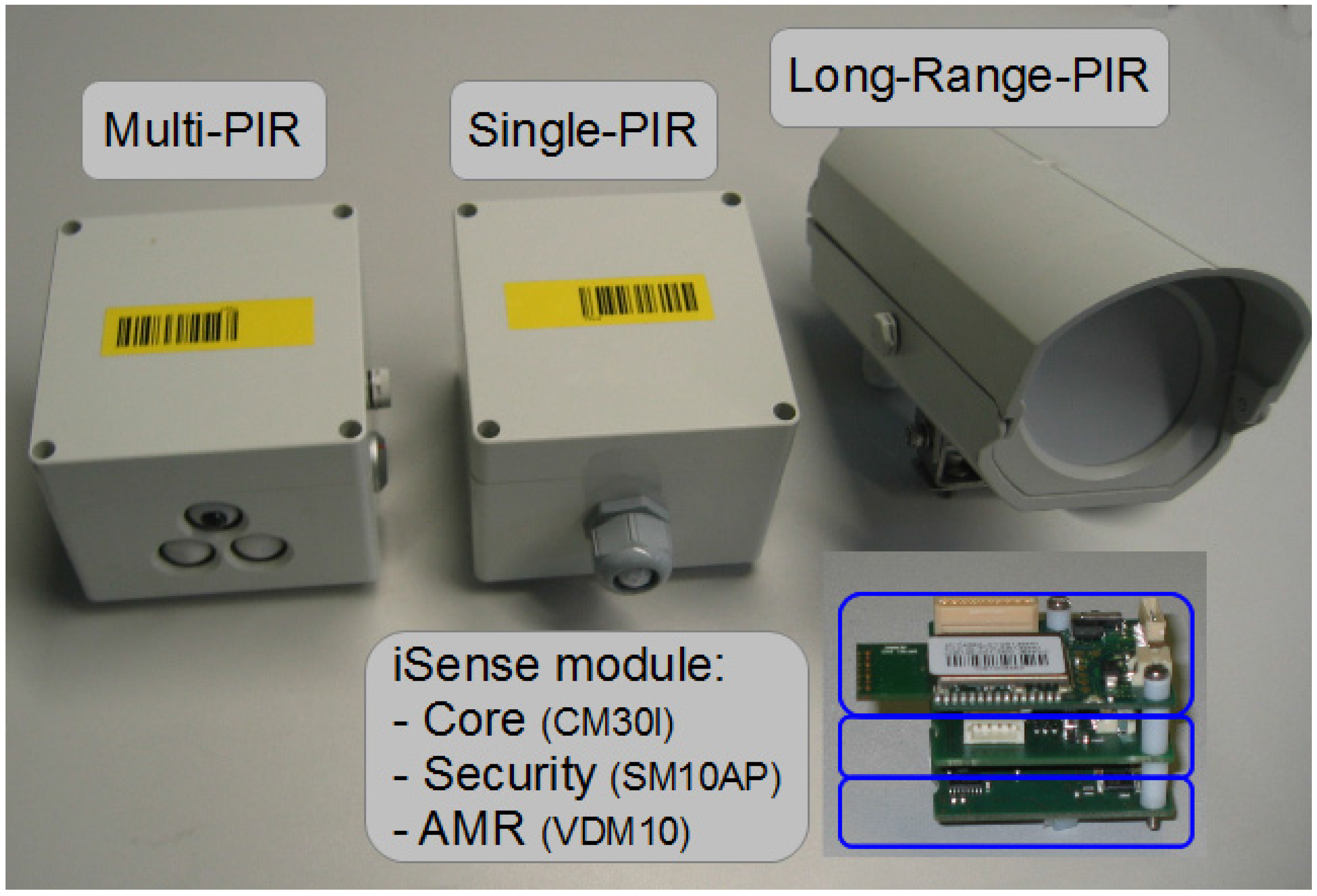
3.2.4. Sensors
3.3. Software
- The hierarchical communication structure.
- The security concept for providing communication security and functional safety (guaranteeing the detection of malfunctions in the sensor or node hardware).
- The detection algorithm. This uses data gathered by the sensor nodes and relates between the sensor clusters to derive a trespasser’s position and current direction of movement.
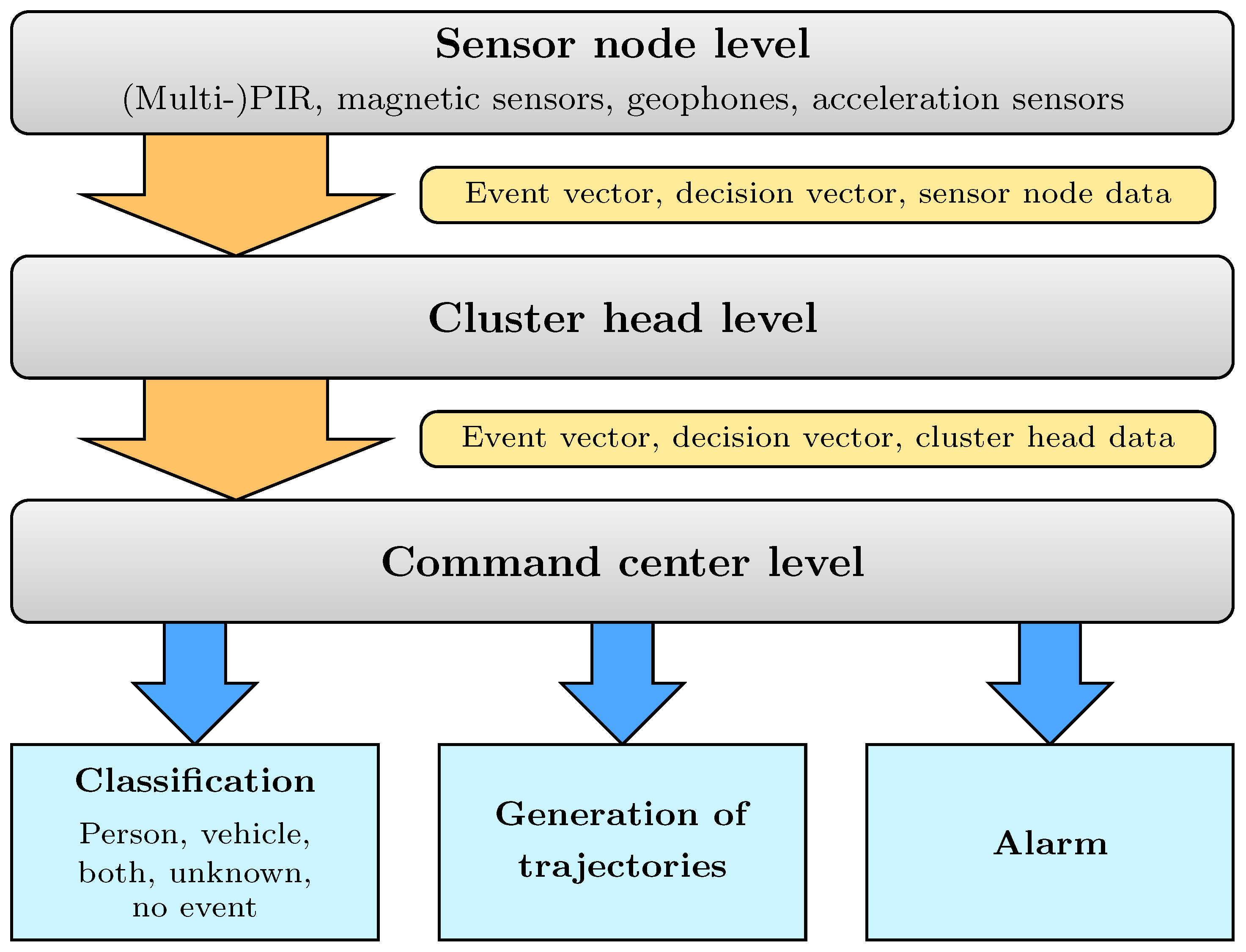
3.3.1. Hierarchical Communication Structure
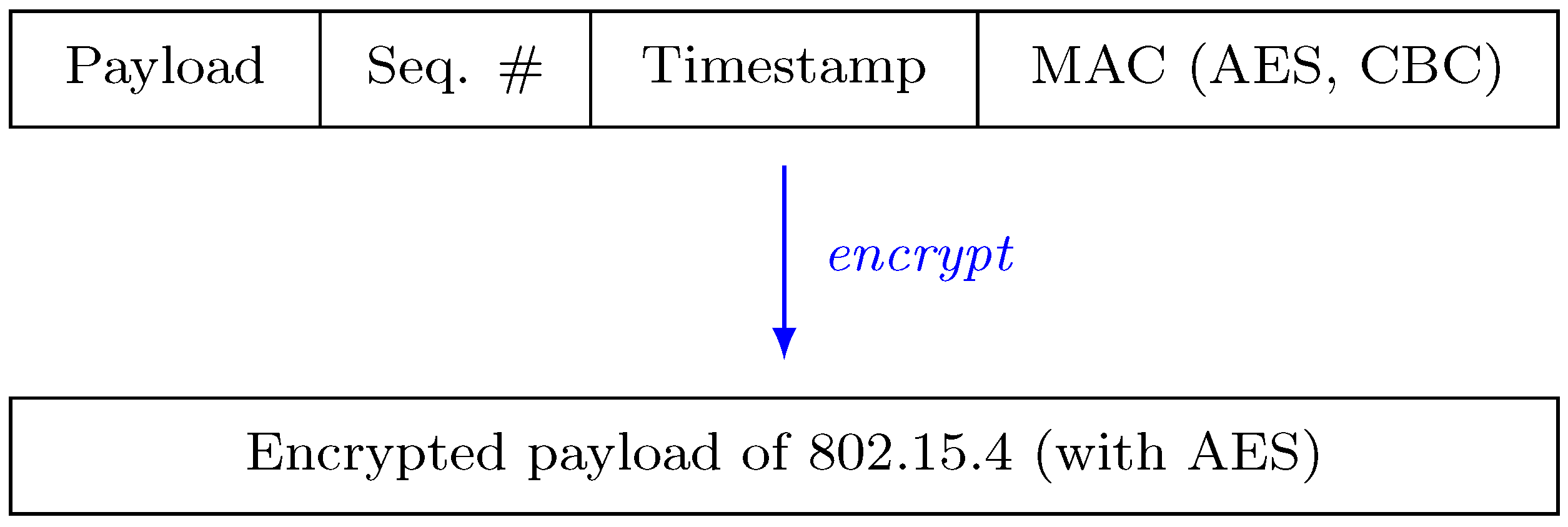
3.3.2. Security
Communication Security
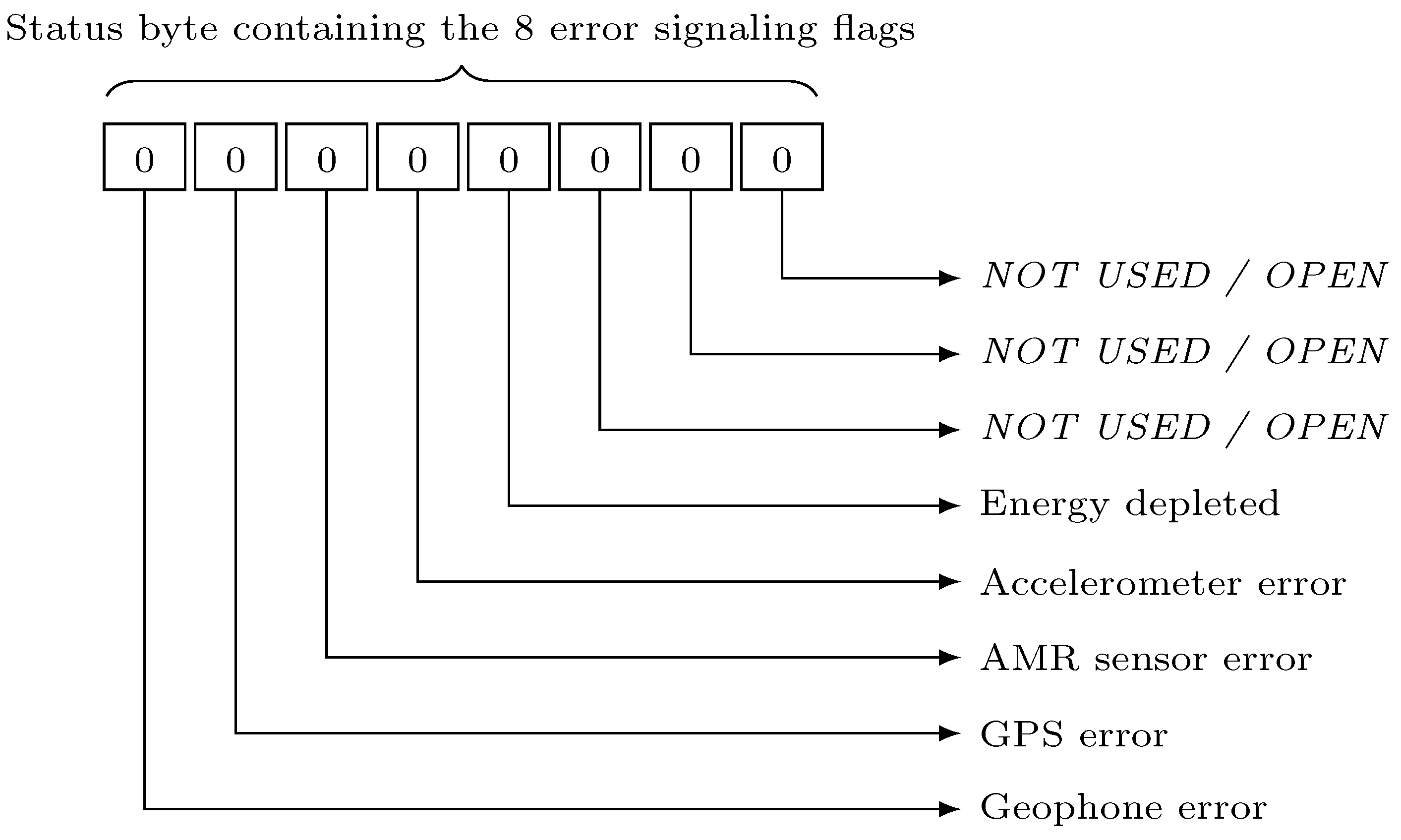
Functional Safety
| Code 1 Pseudocode of Checkerboard RAM test |
| i, j, k, n |
| while i is odd and j is even do |
| write in cell[i] |
| write in cell[j] |
| end while |
| pause( ms) |
| for k to do |
| if ) then |
| FAILURE |
| else |
| complement(cell[k]) |
| complement(cell[n k]) |
| end if |
| end for |
| ms) |
| for k to do |
| if not_equal(sum[k], ) then |
| FAILURE |
| end if |
| end for |
| PASS |
| Code 2 Pseudocode of Fletcher’s checksum |
| i, sum1, sum2 |
| flash[image_length] |
| for i from do |
| end for |
| flash[image_length] check1 |
| flash[image_length ] check2 |
- GPS module: The GPS module is checked each time it is activated for time synchronization purposes. After its activation, the GPS module receives a timing signal after a defined amount of time (one tick each second). If the timing signal is not received in this timeframe, a time-out event occurred. This leads to an error of the GPS module, that is reported by an error flag to the command center c. If the next timing signal is received correctly in time, the error flag is cleared again.
- AMR sensor: Before each use of the AMR sensor inside of the vehicle detection module, it has to fulfill a calibration self-test mechanism. This test works by actively compensating the earth’s magnetic field by sending current through coils. The test routine uses the calibration to find errors in the sensor, which can be found by comparing the current to a reference value. If the difference exceeds a predefined value, an error is reported by setting an error flag. The error flag can be removed again if a following calibration returns an acceptable value.
- Acceleration sensor/accelerometer: The acceleration sensor located on the security module of the node is a key element in the tamper resistance concept of the sensor nodes. The test for this sensor is periodically triggered and uses an internal self-test algorithm of the security module. The test uses the apparent gravity to measure if the acceleration sensor is working correctly. If the self-test fails, which is the case if the difference of the current test result and the reference value stored in the test-algorithm exceeds a certain threshold, the error is reported by an error flag that is sent to the clusterhead. Again, if the test is completed successfully afterwards, the error flag is revoked.
- Geophones: The test routine of the geophones could not be built upon an internal test routine. Therefore, the testing mechanism can only verify if a geophone, which is connected to a sensor node, is able to receive and send messages. This is done by sending a wake-up message to the geophone. If the device is answering that message with an verification message in a certain amount of time, it thereby confirms to be working in unimpaired condition. Again, if either the verification message is not received by the sensor node in time or not at all, an error flag is set. It is revoked the next time a verification message is received within the expected time.
- PIR sensors: Due to the nature of the PIR sensor, there is no self-testing procedure available, due to the lack of an reference value. The only malfunction of a PIR sensor which can be detected is the case when it is always on, because during normal operation, the sensor automatically deactivates directly after being triggered.
Reporting of and Reaction to Errors
3.3.3. Energy Supply
| Component | Awake Demand | Sleep Demand |
|---|---|---|
| Accelerometer | 650 px μA | 1 px μA |
| Single-PIR sensor | 300 px μA | 0 px μA |
| Multi-PIR sensor | 900 px μA | 0 px μA |
| GPS receiver | 50 px mA | 0 px mA |
| AMR sensor | 40 px mA | 0 px μA |
| Core module | 6 px mA | 40 px μA |
| FM transceiver | 16 px mA | 0 px mA |
| Geophone (GP) | 10 px mA | 5 px mA |
| IGEP module | 600 px mA | 480 px mA |
| Node Type | Awake Demand | Sleep Demand | |
|---|---|---|---|
| Clusterhead | 672 px mA | 480 px mA | |
| Node with | Multi-PIR, no GP | 64 px mA | 41 px μA |
| Multi-PIR, with GP | 74 px mA | 5 px mA | |
| Single-PIR, no GP | 63 px mA | 41 px μA | |
| Single-PIR, with GP | 73 px mA | 5 px mA | |
3.4. Secure Detection, Localization and Classification Algorithms
- Sensor node: Located a the lowest level, sensor nodes are responsible for the acquisition of sensor data, with the equipped PIR sensors, magnetic sensors, Geophones and accelerometers. For PIR sensors this is a cone of a specific length whereas for all other sensors, this is a radial symmetric area around the sensor node with a certain radius. After the WSN is started, the detection algorithm first remains in a waiting state, until a significant amount of sensor events are registered, which indicates an object entering the area. If the amount of events remains low, it is assumed that these are caused by random noise or other sources, like wind. Additionally, it is required that there is a local accumulation of events. The amount of random noise depends on the sensor type as well as on other factors like the position of the sensor, the time of the day and the weather conditions. If the sensor data satisfies these conditions, it is inferred that an object is inside the surveillance area and an initial position is determined. Each sensor event suggests possible locations of the object.
- Clusterheads: The event data from neighboring sensor nodes is further processed at clusterheads. As each sensor node suggests a possible position for a object, at the clusterhead, The current position of the object is then determined by averaging the suggested positions of the sensor events while factoring in the previous position of the object. Afterwards, only sensor events in a vicinity of the current position of the detected object are considered, until the object leaves the surveillance area.
- Command center: As the control center of WSNs, command center classifies different objects (person, person carrying metal object, car or unknown) by an analysis of the AMR and geophone events. Magnetic sensor events in the vicinity of the object suggest a car or a motorbike, and geophone events indicate footsteps, but there need to be an accumulation of these events, which exceeds the noise level. Table 4 shows the classification matrix of events detected by different sensor types. For clarification, an example is given here: Assuming a Single-PIR event is triggered, at first, an entity is detected to be present in the WSN’s vicinity, however a classification is not yet possible, therefore it is marked as "unknown". However, if the entity also triggers an AMR event, yet no geophone event, it is classified as a vehicle. Experiments show that the AMR sensors are surprisingly affected by wind (possibly due to movement of cables or the sensor node itself). An object in the surveillance area is considered to have left this area if the last known position is near the border of the area and further sensor events are below the detection level for some time.
| Component | Event Detected | |
|---|---|---|
| Yes | No | |
| Single-PIR | Person/vehicle | — |
| Multi-PIR | Person/vehicle | — |
| Long Range-PIR | Person/vehicle | — |
| AMR sensor | Vehicle | — |
| Geophone (GP) | Person | — |
4. Sensor Evaluation
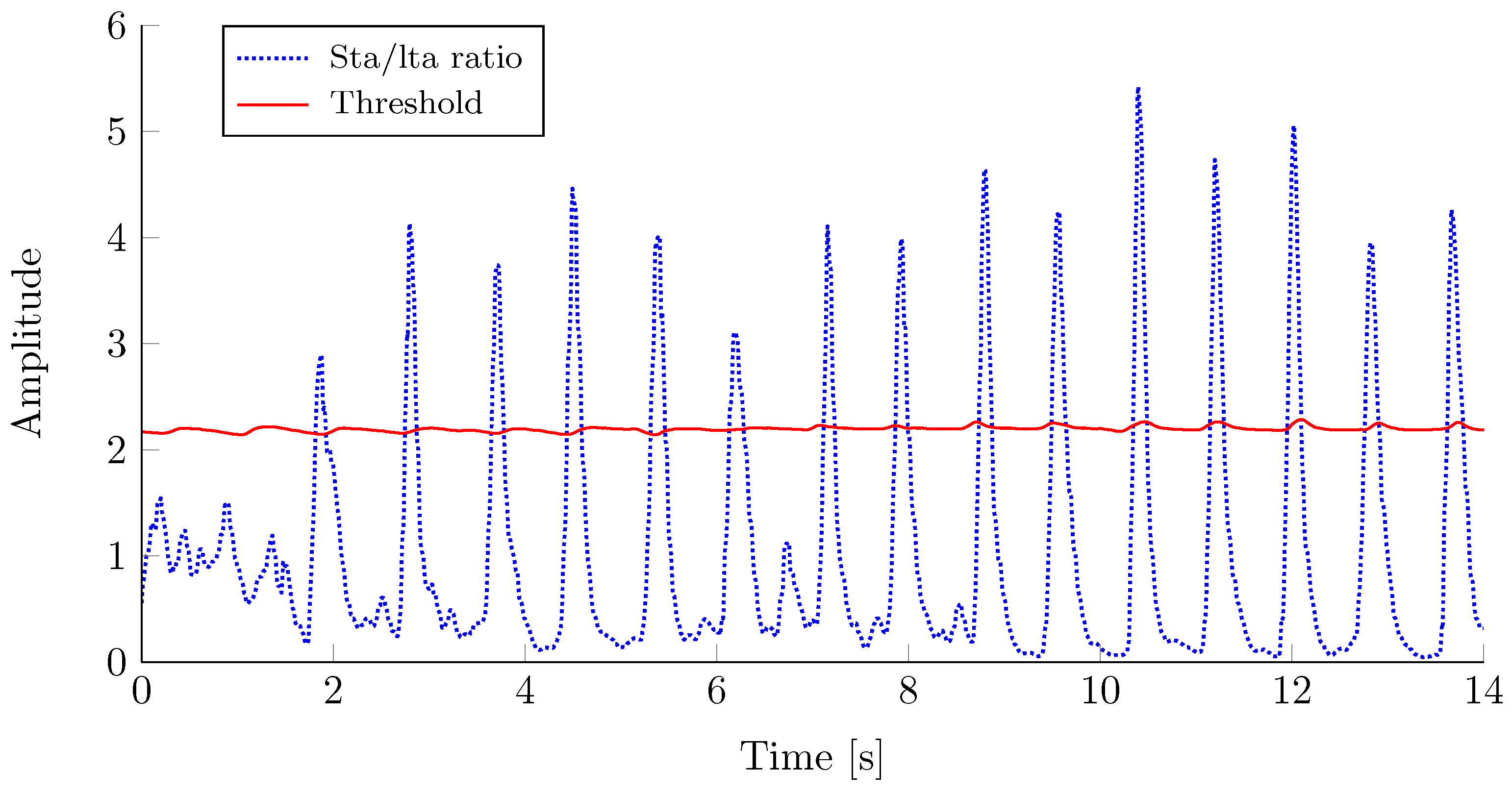
4.1. Geophones
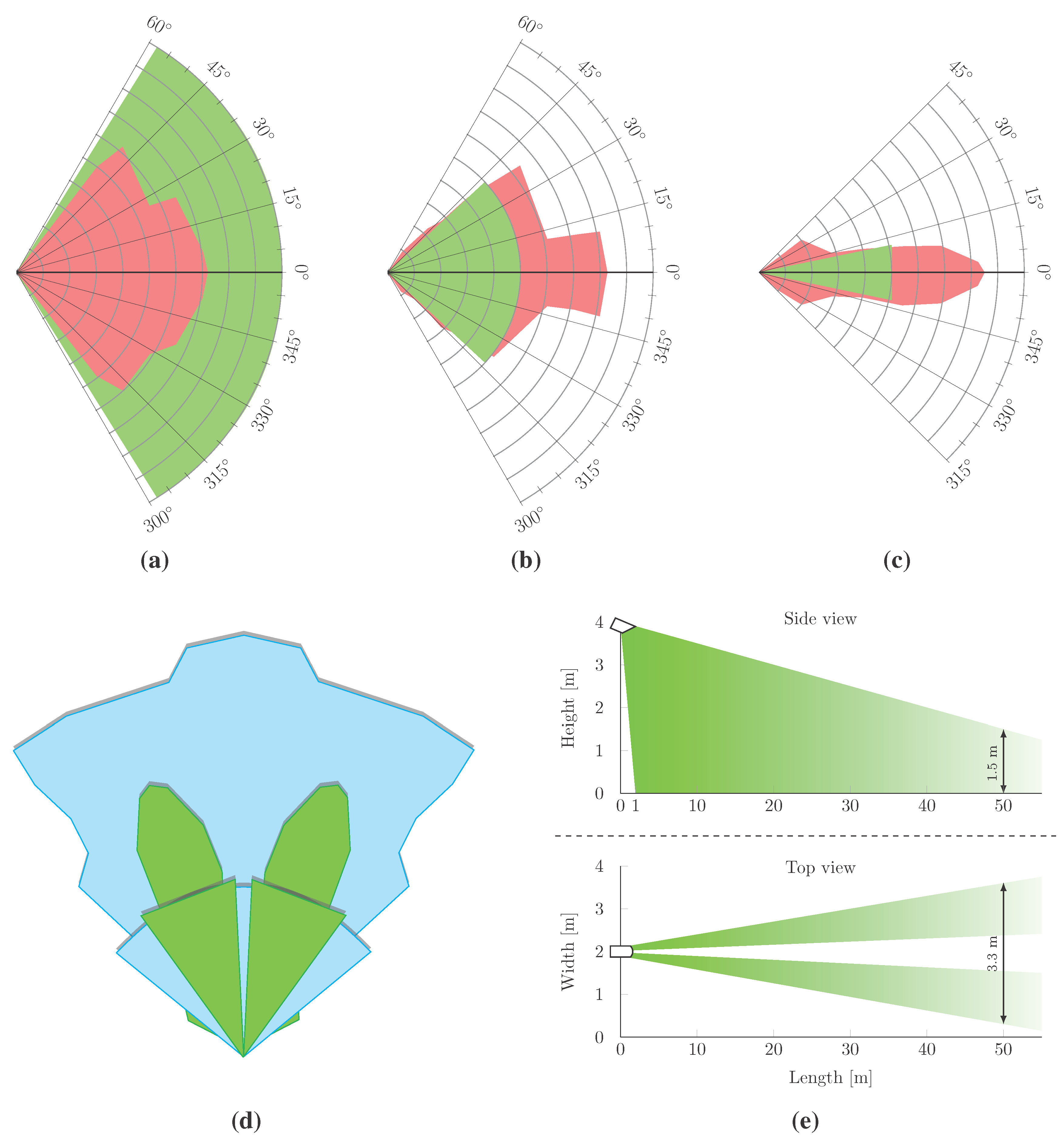
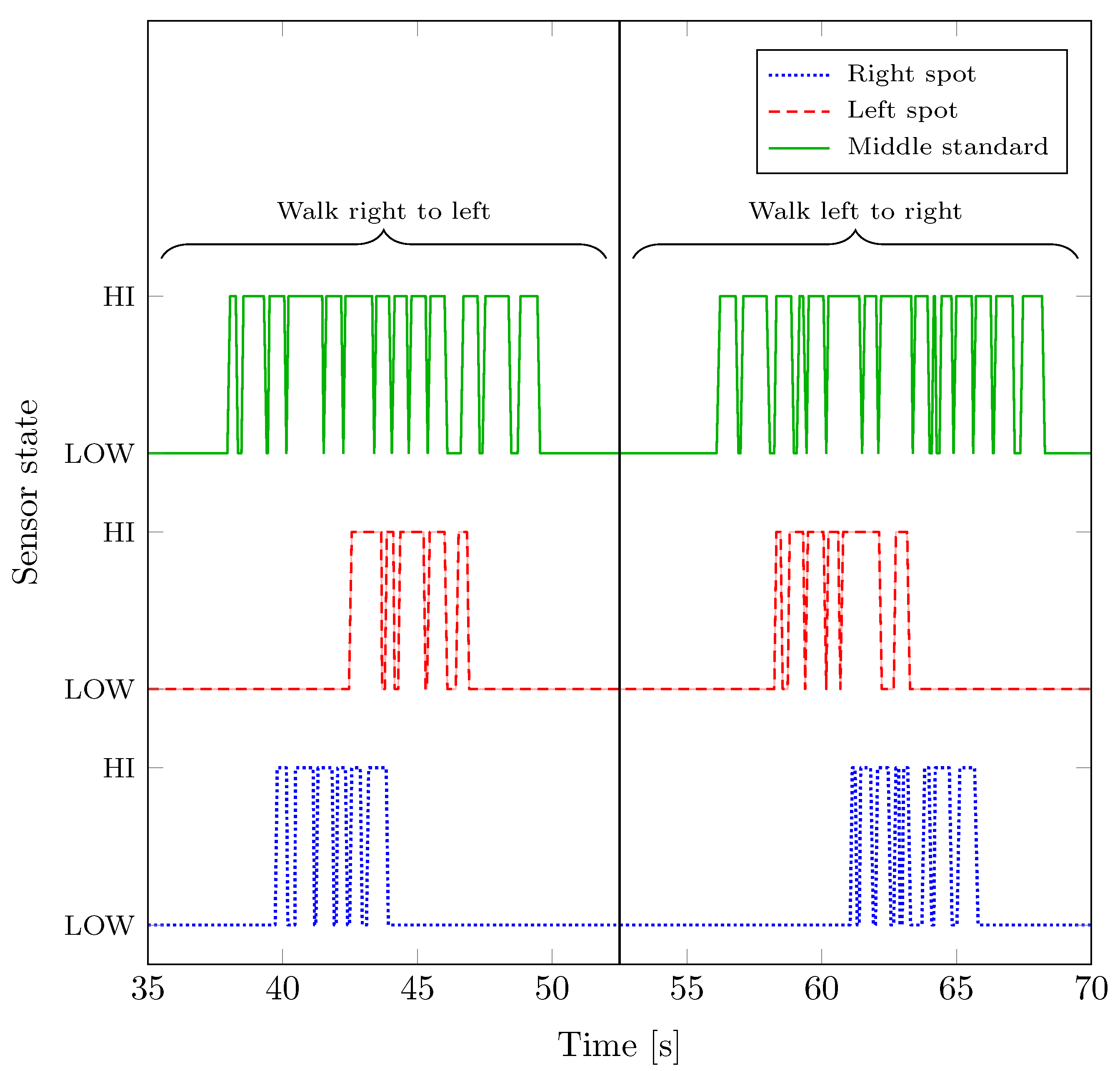
4.2. PIR Sensors
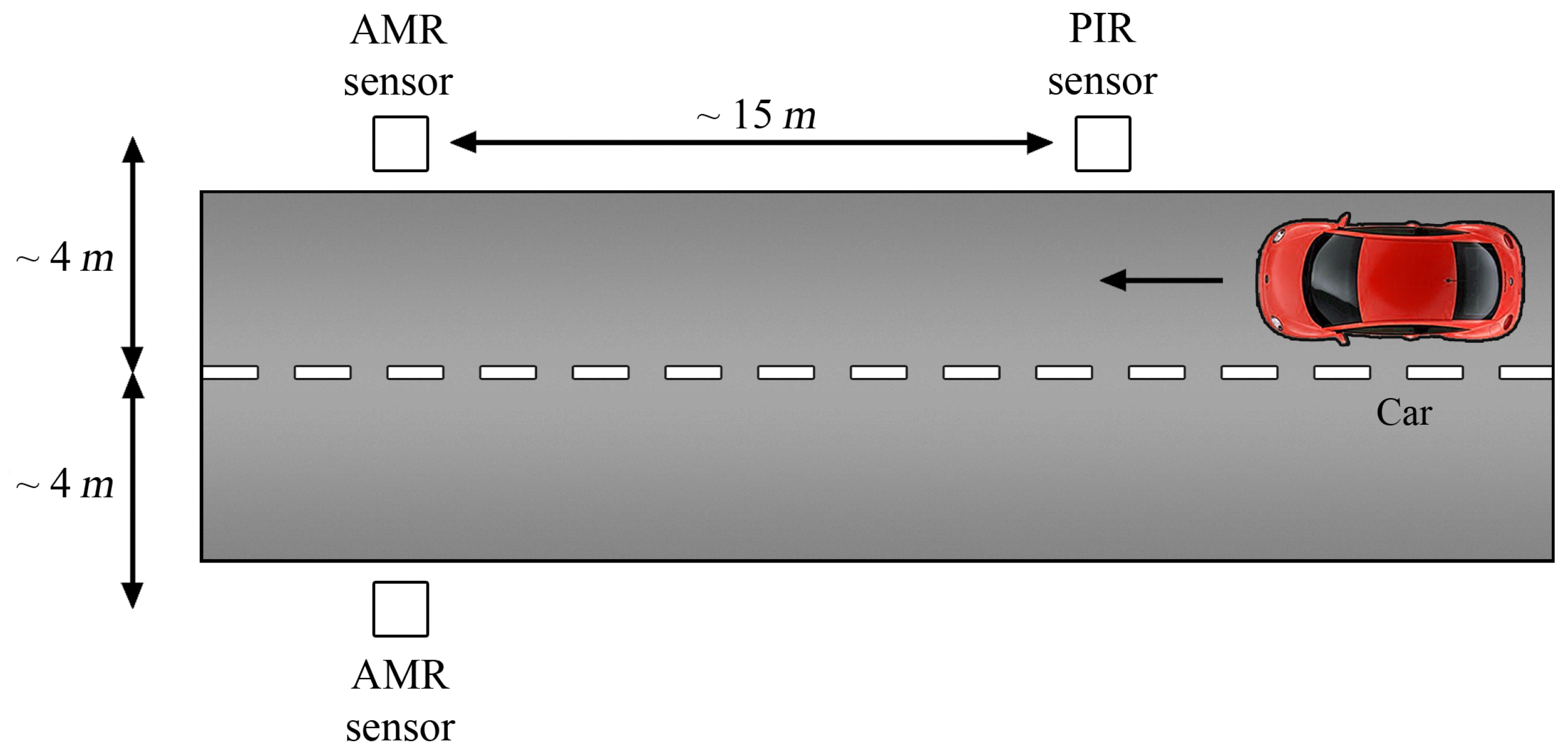
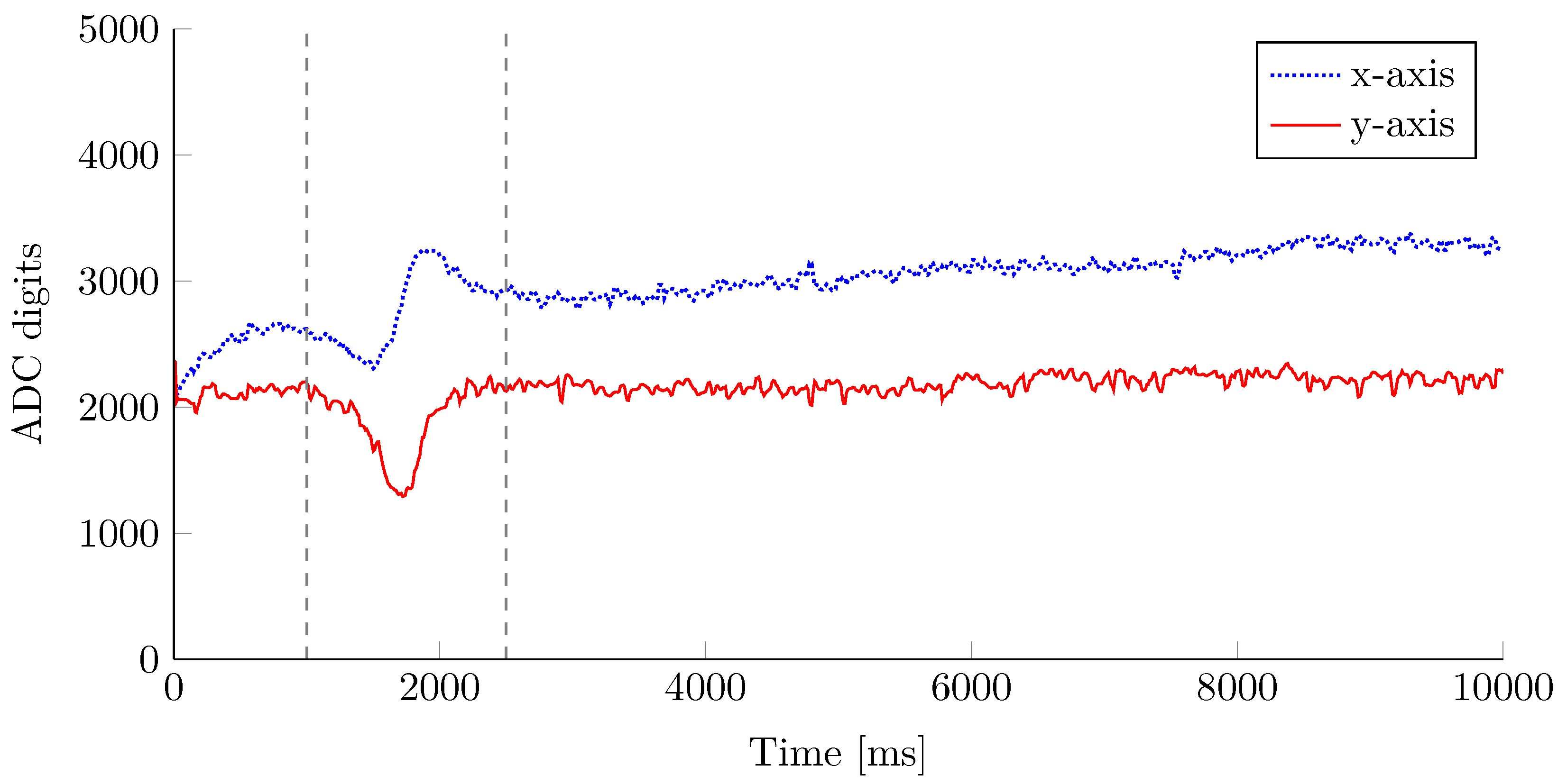
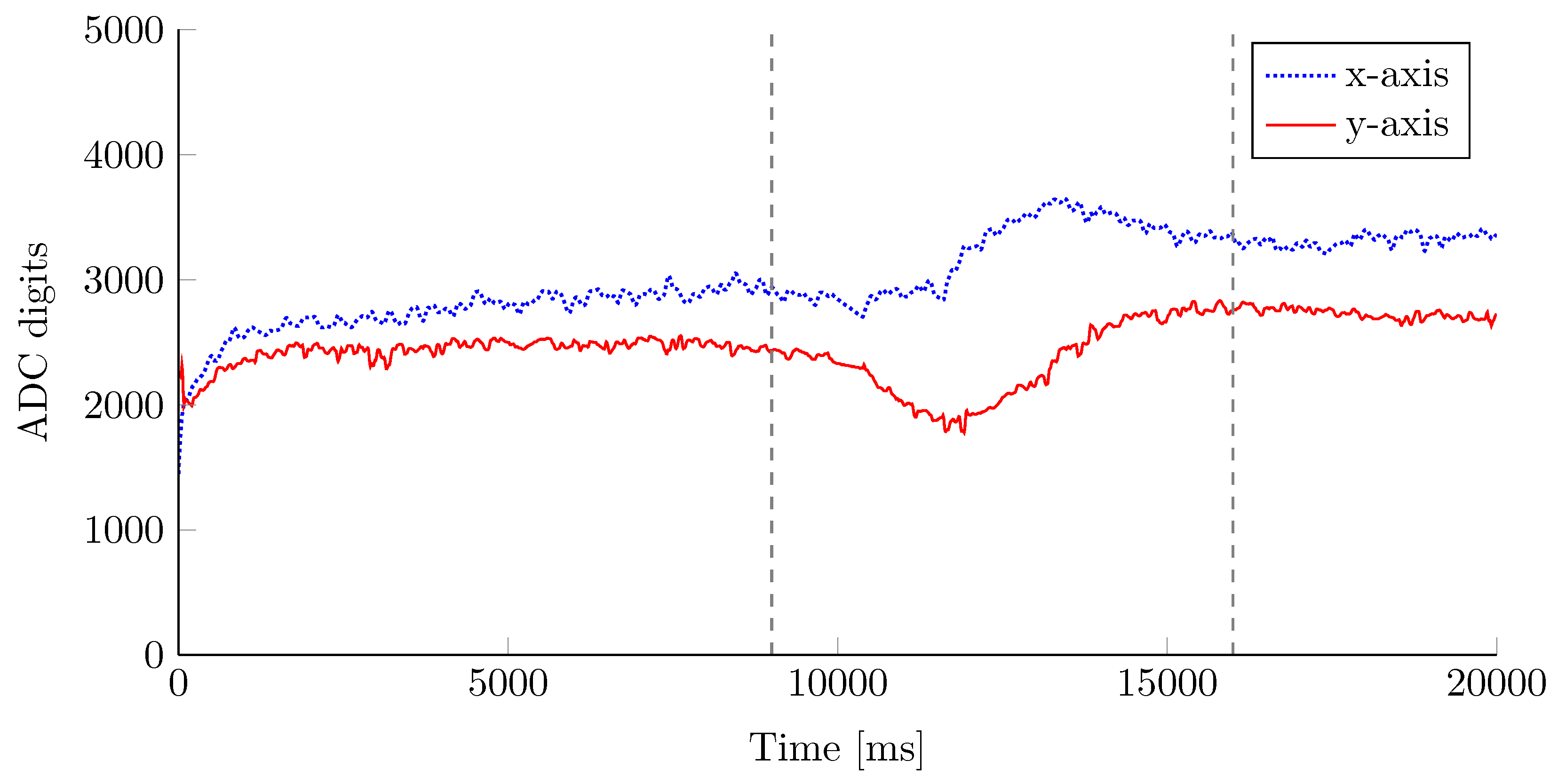
4.3. AMR Sensors
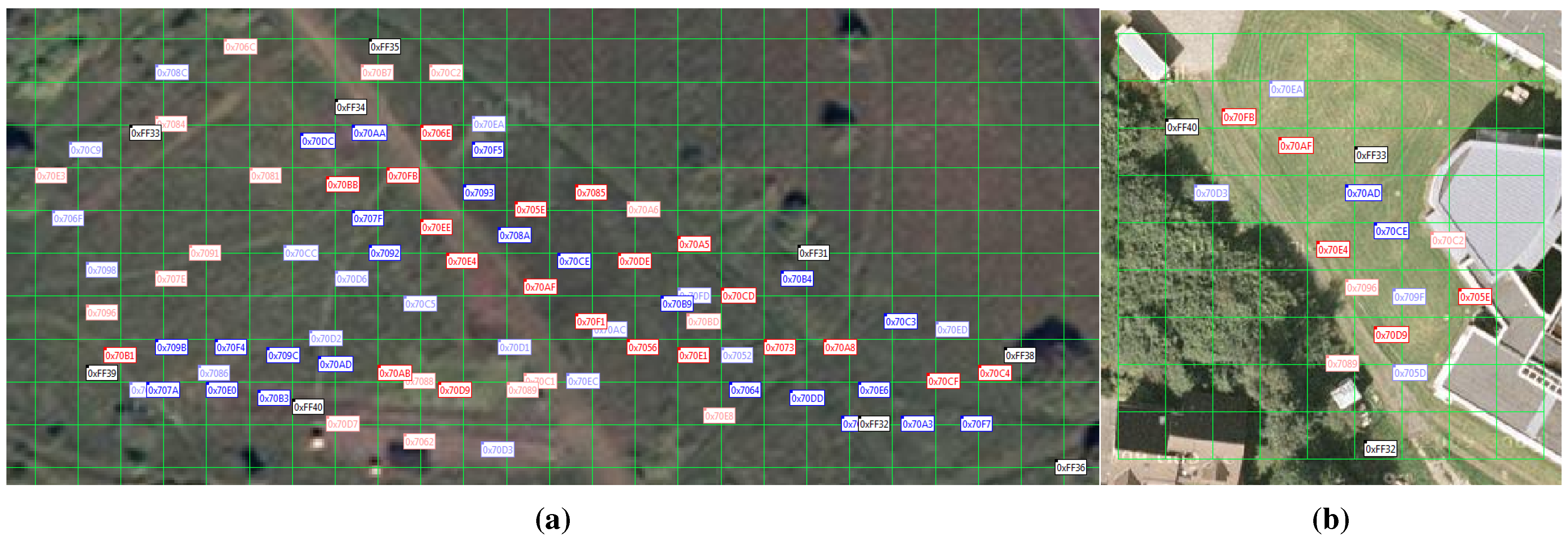
5. Network Implementation and Assessment
5.1. Laboratory Tests
5.1.1. Functional Safety
| # | Function | Action Performed | Time |
|---|---|---|---|
| 1 | AMR | Removal of module | Before start |
| 2 | AMR | Removal of module | During operation |
| 3 | Acceleration | Removal of module | Before start |
| 4 | Acceleration | Removal of module | During operation |
| 5 | Geophone | Disconnection of cable | Before start |
| 6 | Energy supply | Battery draining | During operation |
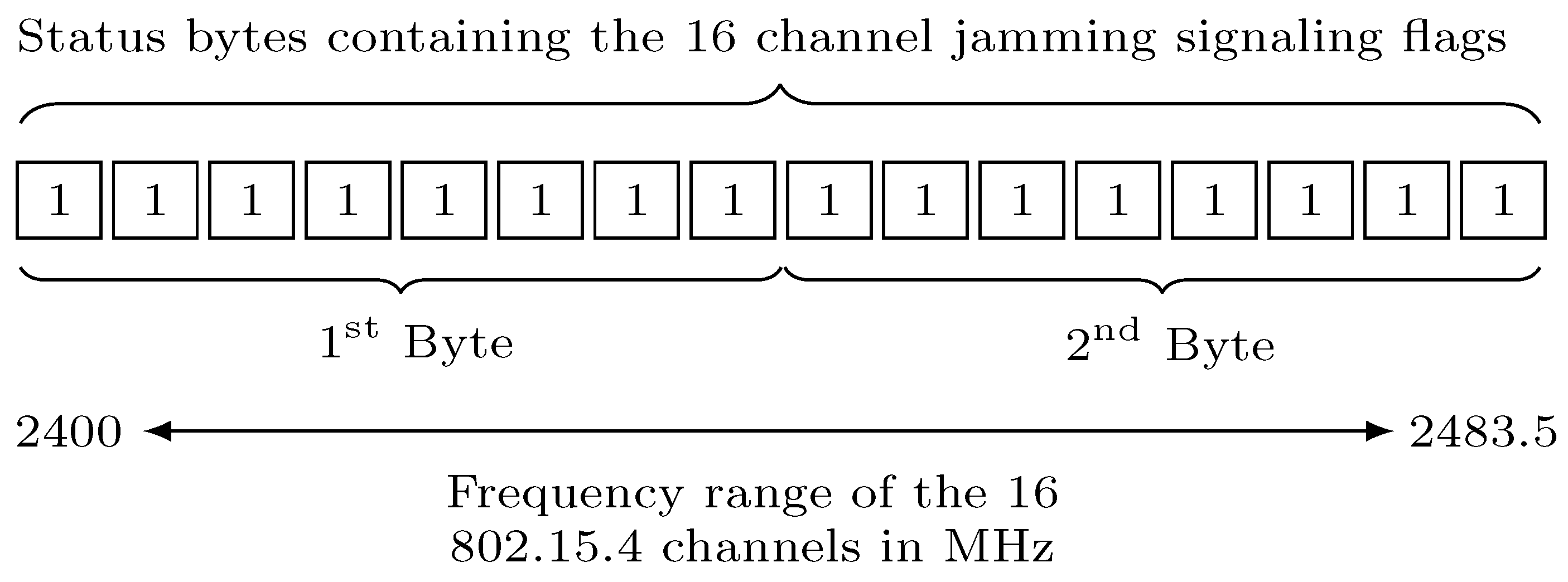
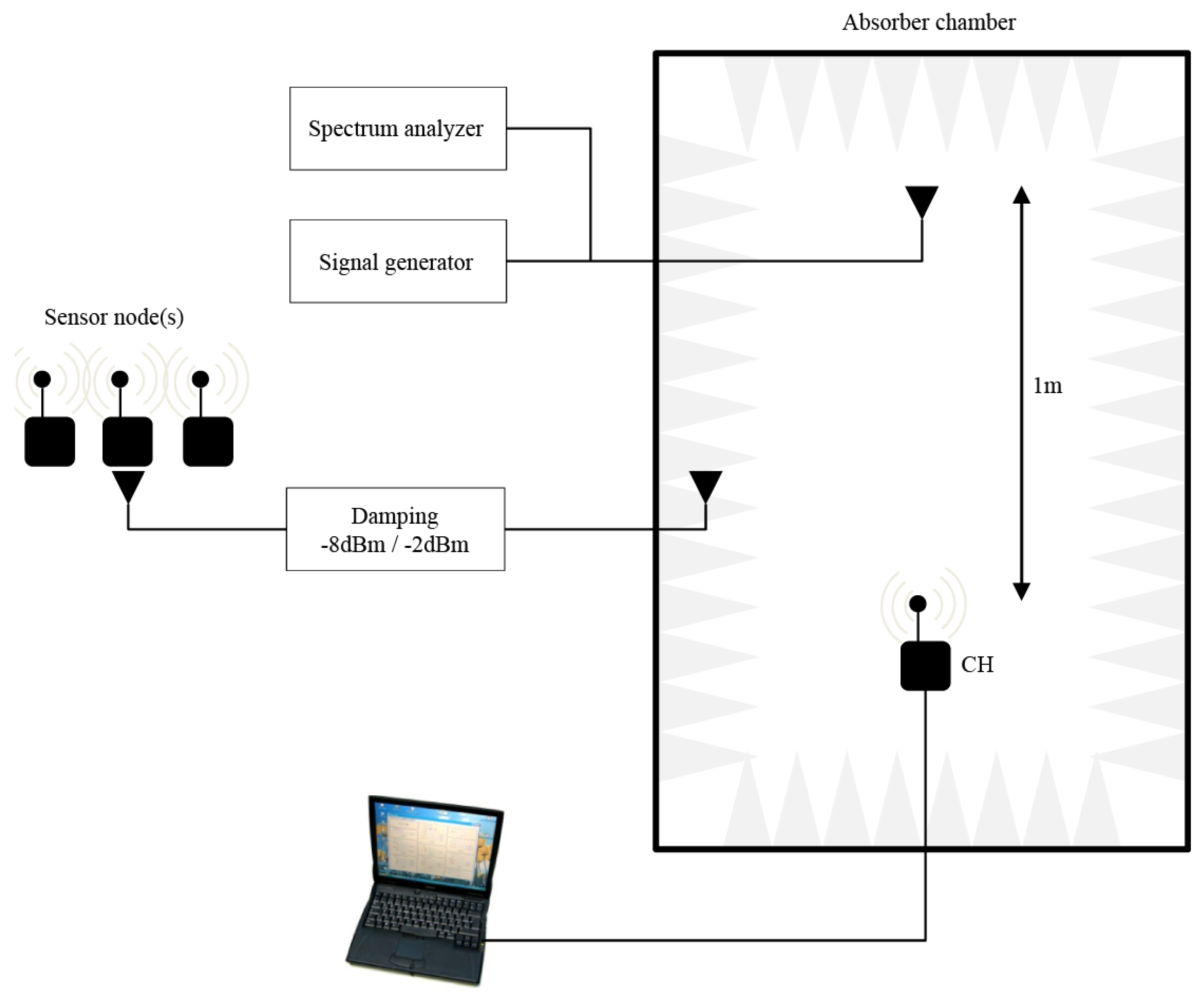
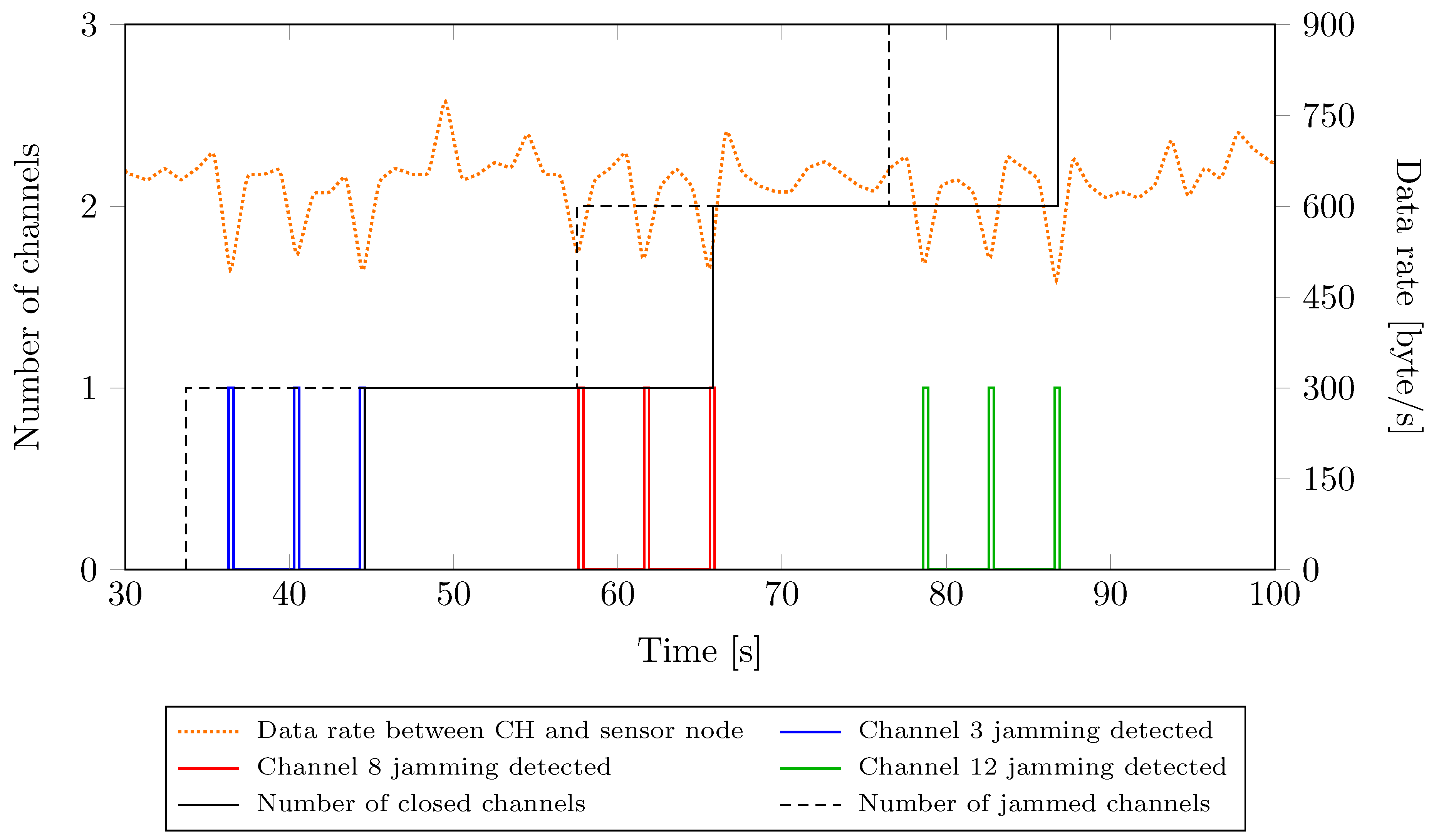
5.1.2. Adaptive Frequency Hopping and Communication Robustness

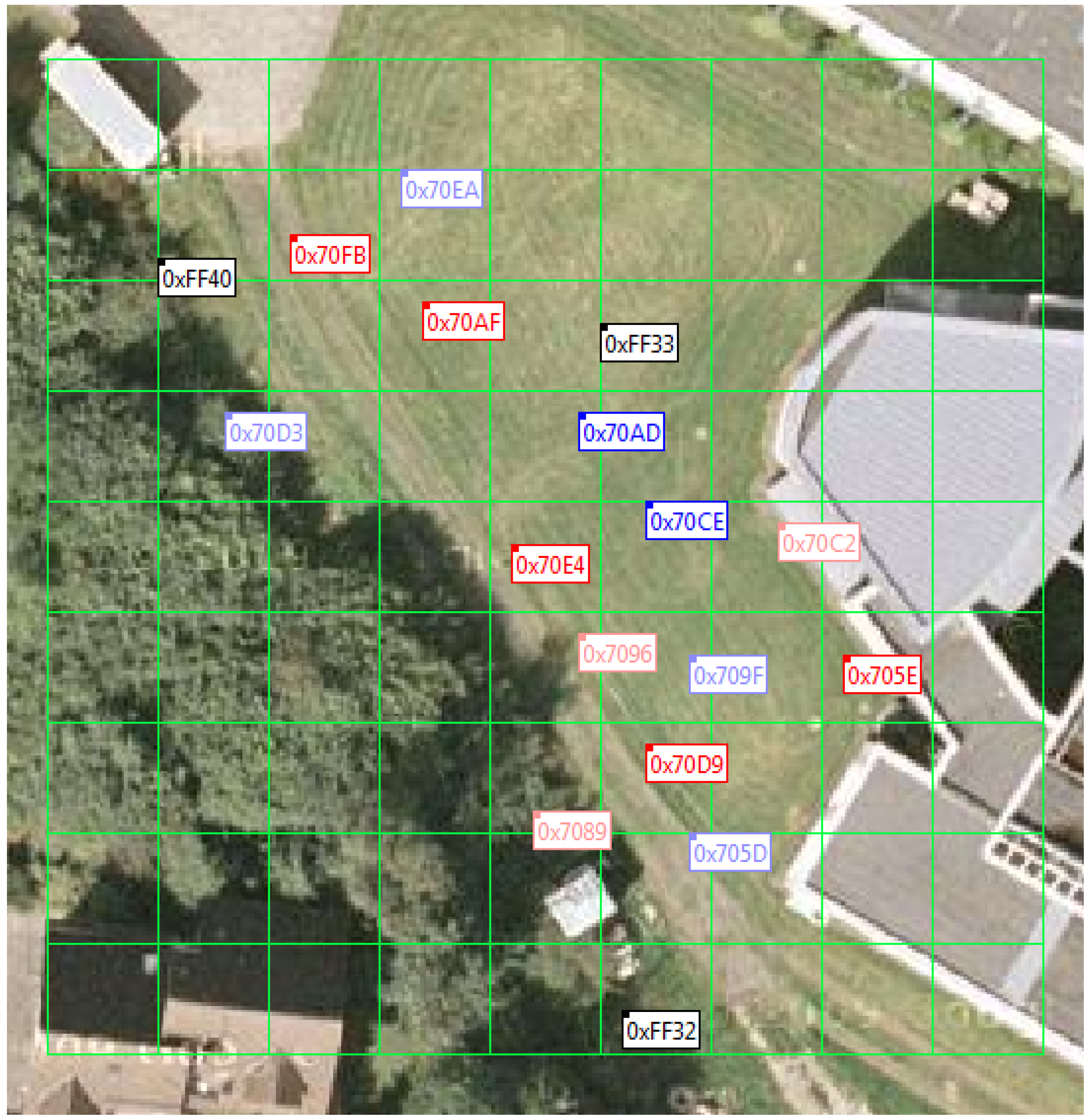
5.2. Field Trial
6. Results
6.1. Laboratory Tests
6.1.1. Adaptive Frequency Hopping and Communication Robustness
6.1.2. Functional Safety
| Code 3 Log of the test #4 |
| Code 4 Log of the test #2 |
| Symbol | Meaning | Symbol | Meaning |
 | Geophon event |  | AMR event |
 | Longrange-PIR event |  | Multi-PIR event |
 | Accelerometer event |  | Single-PIR event |
 | Node communication issue |  | Node failure |
 | Energy drain alert | ||
| Color | Classification | Color | Classification |
 | Human |  | Vehicle |
 | Human with metal object |  | Unknown |
6.2. Field Trial

| Detection Test Scenarios | |||||
| Test # | Distance to Sensor Nodes | Terrain | Type of Trespasser | Employed # of Clusters | Penetration |
| 1 | Short grass | Person | 1 | Yes, shortest path | |
| 2 | High grass | Person | 1 | Yes, shortest path | |
| 3 | Stony ground | Person | 1 | Yes, shortest path | |
| 4 | Short grass | Person | 1 | Yes, shortest path | |
| 5 | High grass | Person | 1 | Yes, shortest path | |
| 6 | Stony ground | Person | 1 | Yes, shortest path | |
| 7 | Short grass | Person | 1 | Yes, shortest path | |
| 8 | High grass | Person | 1 | Yes, shortest path | |
| 9 | Stony ground | Person | 1 | Yes, shortest path | |
| 10 | Variable | Short grass | Person carrying metal object | Arbitrary | No |
| 11 | Variable | Short grass | Person carrying metal object | Arbitrary | Yes |
| 12 | Variable | Stony ground | Car | Arbitrary | No |
| 13 | Variable | Stony ground | Car | Arbitrary | Yes, |
| 14 | Variable | Stony ground | Car | Arbitrary | Yes, |
| 15 | Variable | Stony ground | Person | Arbitrary | Yes, running |
| 16 | Variable | Short grass | Person | Arbitrary | Yes, duck gait |
| 17 | Variable | Short grass | Person | Arbitrary | Yes, creeping |
| 18 | Variable | Short grass | Person | 1 | Yes, zigzag pattern |
| 19 | Variable | Short grass | Person | 2 | Yes, zigzag pattern |
| 20 | Variable | Short grass | Person | 1 | No |
| 21 | Variable | Short grass | Person | 2 | No |
| 22 | Variable | Stony ground | Bicycle | Arbitrary | Yes |
| 23 | Variable | Stony ground | Motorcycle | Arbitrary | Yes, slow |
| 24 | Variable | Stony ground | Motorcycle | Arbitrary | Yes, fast |
| 25 | Variable | Stony road | Person | 1 | Yes, shortest path |
| 26 | Variable | Stony road | Person | 2 | Yes, running |
| 27 | Variable | Stony road | Car | Arbitrary | Yes, slow |
| 28 | Variable | Short grass | Parson | Arbitrary | Yes, shortest path |
| 29 | Variable | Short grass | Person | Arbitrary | No, U pattern |
| Security Test Scenarios | |||||
| Test # | Terrain | Action Performed | Type of Trespasser | ||
| 30 | Short grass | Shaking of a sensor node | Person | ||
| 31 | Short grass | Removal of a sensor node out of the test field | Person | ||
| 32 | Short grass | Reactivation of a sensor node in the test field | Person | ||
| 33 | Short grass | Measurement of the energy consumption of a cluster | — | ||
7. Related Work
8. Conclusions and Future Work
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Estrin, D.; Govindan, R.; Heidemann, J.; Kumar, S. Next Century Challenges: Scalable Coordination in Sensor Networks. In Proceedings of the 5th Annual ACM/IEEE International Conference on Mobile Computing and Networking (MobiCom 99), Seattle, WA, USA, 15–19 August 1999.
- Asada, G.; Dong, M.; Lin, T.S.; Newberg, F.; Pottie, G.; Kaiser, W.J.; Marcy, H.O. Wireless integrated network sensors: Low power systems on a chip. In Proceedings of the 24th IEEE European Solid State Circuits Conference (ESSCIRC 98), The Hague, The Netherlands, 22–24 September 1998.
- SpyGlass, a Modular and Extensible Visualization Framework for Wirelesssensor Networks. Institute of Telematics, University of Lübeck: Lübeck, Germany, 2006; Available online: https://github.com/itm/spyglass (accessed on 23 October 2015).
- coalesenses GmbH. iSense Core Module 3 Data Sheet. 2010. Available online: http://www.coalesenses.com/download/data_sheets/DS_CM30X_1v3.pdf (accessed on 23 October 2015).
- coalesenses GmbH. Gateway Module Data Sheet. 2010. Available online: http://www.coalesenses.com/download/gateway_module_data_sheet_1v2.pdf (accessed on 23 October 2015).
- coalesenses GmbH. GPS Module Product Brief. 2010. Available online: http://www.coalesenses.com/download/product_briefs/ProductBriefGpsModule.pdf (accessed on 23 October 2015).
- Buschmann, C.; Pfisterer, D. iSense: A Modular Hardware and Software Platform for Wireless Sensor Networks. In Technical Report, 6. Fachgespräch Drahtlose Sensornetze der GI/ITG-Fachgruppe Kommunikation und Verteilte Systeme; RWTH Aachen: Aachen, Germany, 2007. [Google Scholar]
- NXP Laboratories UK. Data Sheet: JN5148-001 IEEE802.15.4 Wireless Microcontroller. 2010. Available online: http://www.jennic.com/files/product_briefs/JN-DS-JN5148-1v6.pdf (accessed on 23 October 2015).
- IEEE-SA Standards Board. IEEE Standard for Information Technology—Telecommunications and Information Exchange between Systems—Local and Metropolitan area Networks Specific Requirements-Part 15.4: Wireless Medium Access Control (MAC) and Physical Layer (PHY) Specifications for Low-Rate Wireless Personal Area Networks (LR-WPANs); Technical Report; IEEE Computer Society: New York, NY, USA, 8 September 2006. [Google Scholar]
- The Federal Information Processing and Announcing. Announcing the Advanced Encryption Standard (AES); FIPS 197; Federal Information Processing and Announcing: Gaithersburg, MD, USA, 26 November 2001.
- SIEMENS. IS392, IS392H Outdoor Passive Infrared Detector. 2005. Available online: http://www.ntcbpl.ru/pdfinfo/Data-sheetIS392en.pdf (accessed on 23 October 2015).
- Panasonic. MP Motion Sensor (AMN1,2,4). 2004. Available online: http://datasheet.octopart.com/AMN34111-Panasonic-datasheet-110118.pdf (accessed on 23 October 2015).
- Input/Output, Inc. SM-24 Geophone Element. 2006. Available online: http://cdn.sparkfun.com/datasheets/Sensors/Accelerometers/SM-24%20Brochure.pdf (accessed on 23 October 2015).
- coalesenses GmbH. Vehicle Detection Module Data Sheet. 2010. Available online: http://www.coalesenses.com/download/product_briefs/ProductBriefVehicleDetectionModule.pdf (accessed on 23 October 2015).
- Coulson, G.; Porter, B.; Chatzigiannakis, I.; Koninis, C.; Fischer, S.; Pfisterer, D.; Bimschas, D.; Braun, T.; Hurni, P.; Anwander, M.; et al. Flexible experimentation in wireless sensor networks. Commun. ACM 2012, 55, 82–90. [Google Scholar] [CrossRef]
- Mpitziopoulos, A.; Gavalas, D.; Konstantopoulos, C.; Pantziou, G. A survey on jamming attacks and countermenasures in WSNs. IEEE Commun. Surv. Tutor. 2009, 11, 42–56. [Google Scholar] [CrossRef]
- Whiting, D.; Housley, R.; Ferguson, N. Counter with CBC-MAC (CCM). 2003. Available online: http://tools.ietf.org/html/rfc3610 (accessed on 23 October 2015).
- Lashkari, A.H.; Danesh, M.M.S.; Samadi, B. A survey on wireless security protocols (WEP, WPA and WPA2/802.11i). In Proceedings of the 2nd IEEE International Conference on Computer Science and Information Technology (ICCSIT 2009), Beijing, China, 8–11 August 2009; pp. 48–52.
- Fletcher, J.G. An arithmetic checksum for serial transmissions. IEEE Trans. Commun. 1982, 30, 247–252. [Google Scholar] [CrossRef]
- Havskov, J. Instrumentation in Earthquake Seismology (Modern Approaches in Geophysics); Springer Science + Business Media B.V.: Dordrecht, The Netherlands, 2004. [Google Scholar]
- Practices for Securing Critical Information Assets; Critical Infrastructure Assurance Office: Gaithersburg, MD, USA, 2000.
- Intanagonwiwat, C.; Govindan, R.; Estrin, D. Directed diffusion: A scalable and robust communication paradigm for sensor networks. In Proceedings of the 6th Annual ACM/IEEE International Conference on Mobile Computing and Networking (MobiCom 00), Boston, MA, USA, 6–11 August 2000; pp. 56–67.
- Akyildiz, I.F.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar] [CrossRef]
- The SmartSantander Consortium. SmartSantander. 2010. Available online: http://www.smartsantander.eu/ (accessed on 23.10.2015).
- Roman, R.; Zhou, J.; Lopez, J. On the security of wireless sensor networks. In Proceedings of the International Conference on Computational Science and Its Applications—ICCSA 2005, Suntec City, Singapore, 9–12 May 2005; pp. 681–690.
- Perrig, A.; Stankovic, J.; Wagner, D. Security in Wireless Sensor Networks. Commun. ACM 2004, 47, 53–57. [Google Scholar] [CrossRef]
- Bonitz, F.; Ghobadi, S.E.; Hartmann, K.; Hauff, H.; Herrmann, R.; Kargel, C.; Löpprich, O.E.; Heckmann, D.; Maisch, M.M.; Seidl, A.; et al. Personen- und Objektdetektion mit mobilen Sensoren—Abschlussbericht zum Archbeitspacket 3 (Teil B)—Bericht zum Meilenstein 5; Internal End Report; University of Passau: Passau, Germany, 2010. [Google Scholar]
- Koch, M.; Hubert, C. Personen- und Objekterkennung Basierend auf Trittschall (POT); Internal Technical Report; University of Passau: Passau, Germany, 2011. [Google Scholar]
- Rothenpieler, P.; Krüger, D.; Pfisterer, D.; Fischer, S.; Dudek, D.; Haas, C.; Zitterbart, M. Flegsens—Secure area monitoring using wireless sensor networks. In Proceedings of the 4th Safety and Security Systems in Europe, Micro Materials Center Berlin at Fraunhofer Institute IZM and Fraunhofer ENAS, Potsdam, Germany, 4–5 June 2009.
- Arora, A.; Dutta, P.; Bapat, S.; Kulathumani, V.; Zhang, H.; Naik, V.; Mirral, V.; Cao, H.; Demirbas, M.; Gouda, M. A line in the sand: A wireless sensor network for target detection, claffisication, and tracking. Comput. Netw. 2004, 46, 605–634. [Google Scholar] [CrossRef]
- Sun, Z.; Wang, P.; Vuran, M.C.; Al-Rodhaan, M.A.; Al-Dhelaan, A.M.; Akyildiz, I.F. BorderSense: Border patrol through advanced wireless sensor networks. Ad Hoc Netw. 2011, 9, 468–477. [Google Scholar] [CrossRef]
- Felemban, E. Advanced Border Intrusion Detection and Surveillance Using Wireless Sensor Network Technology. Int. J. Commun. Netw. Syst. Sci. 2013, 6, 251–259. [Google Scholar] [CrossRef]
- Langmann, B.; Niedermeier, M.; de Meer, H.; Buschmann, C.; Koch, M.; Pfisterer, D.; Fischer, S.; Hartmann, K. MOVEDETECT—Secure detection, localization and classification in wireless sensor networks. In Internet of Things, Smart Spaces, and Next Generation Networking; Balandin, S., Andreev, S., Koucheryavy, Y., Eds.; Springer Berlin Heidelberg: St. Petersburg, Russia, 2013; Volume 8121, pp. 284–297. [Google Scholar]
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Niedermeier, M.; He, X.; De Meer, H.; Buschmann, C.; Hartmann, K.; Langmann, B.; Koch, M.; Fischer, S.; Pfisterer, D. Critical Infrastructure Surveillance Using Secure Wireless Sensor Networks. J. Sens. Actuator Netw. 2015, 4, 336-370. https://doi.org/10.3390/jsan4040336
Niedermeier M, He X, De Meer H, Buschmann C, Hartmann K, Langmann B, Koch M, Fischer S, Pfisterer D. Critical Infrastructure Surveillance Using Secure Wireless Sensor Networks. Journal of Sensor and Actuator Networks. 2015; 4(4):336-370. https://doi.org/10.3390/jsan4040336
Chicago/Turabian StyleNiedermeier, Michael, Xiaobing He, Hermann De Meer, Carsten Buschmann, Klaus Hartmann, Benjamin Langmann, Michael Koch, Stefan Fischer, and Dennis Pfisterer. 2015. "Critical Infrastructure Surveillance Using Secure Wireless Sensor Networks" Journal of Sensor and Actuator Networks 4, no. 4: 336-370. https://doi.org/10.3390/jsan4040336
APA StyleNiedermeier, M., He, X., De Meer, H., Buschmann, C., Hartmann, K., Langmann, B., Koch, M., Fischer, S., & Pfisterer, D. (2015). Critical Infrastructure Surveillance Using Secure Wireless Sensor Networks. Journal of Sensor and Actuator Networks, 4(4), 336-370. https://doi.org/10.3390/jsan4040336







