A Lightweight Authentication Scheme for V2G Communications: A PUF-Based Approach Ensuring Cyber/Physical Security and Identity/Location Privacy
Abstract
1. Introduction
1.1. Related Works
1.2. Paper Contributions
- The proposed scheme ensures a good range of privacy. The privacy here consists of data and identity privacy against the external adversary, the location privacy of the EVs, and privacy against internal entities. For example, except for a trusted party like GS, any other internal entities like EVs and CSs have not to know each other’s secrets and private data.
- Proposing an efficient and secure protocol that performs the key agreement and data transmission phases simultaneously.
- Proposing a PUF-based authentication scheme which not only resists against all well-known attacks, such as replay, impersonation, data analysis, data integrity, etc., but is also secure against physical threats.
- The proposed scheme consumes the lowest computational and communication resources in comparison with the state-of-the-art.
2. Preliminary Backgrounds and Assumptions
2.1. Background of PUF
- If we input different challenges to the same PUF, we will obtain different responses with great distances. The concept of distance here can be considered as an appropriate distance metric while the responses are always considered as bit vectors.
- If we input same challenge,, to the same PUF in different situations (n times), we will obtain identical responses with great possibility.
- If we input same challenge, , to different PUF instances , we will obtain different responses with great distances.
2.2. V2G System Model
2.3. Threats Facing V2G System
3. Methodology
3.1. Installation Phase
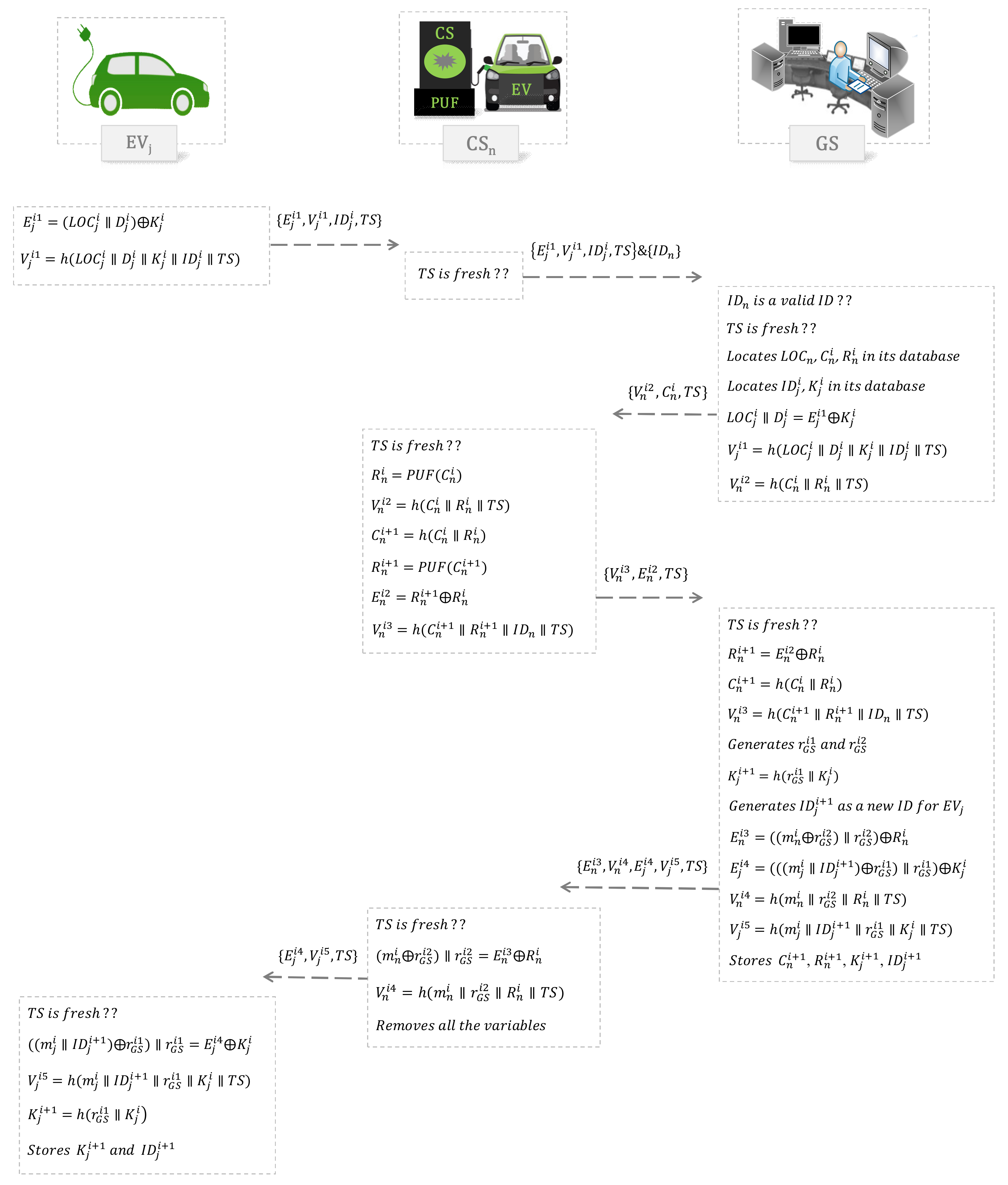
3.2. Authentication Phase
- Decrypts using and i.e., . Now, GS has the new key () to communicates with in the future authentication phase.
- Computes the new challenge as the same of , i.e., .
- Verifies by computing . GS goes to the next step only if the verification is passed.
- Generates two pseudo-random number and .
- Computes the new key for as . GS and will use it for future authentication.
- Generates a pseudo-random number as new ID for named .
- Encrypts the message for using and as .
- Encrypts the message for using and as .
- Computes hash values for and ’s side verification as and , respectively.
- Replaces new parameters i.e. , , , and with the previous ones.
- Sends the packet to .
4. Security Analysis
4.1. Resistance to Eavesdropping and Message Analysis Attack
4.2. Resistance to Message Altering Attack
4.3. Resistance to Impersonation and Message Injection Attack
4.4. Resistance to Replay Attack
4.5. Resistance to DoS Attack
4.6. Resistance to Physical Attack
4.7. User Privacy Protection
5. Performance Evaluation and Comparison
5.1. Communication Overhead
5.2. Computational Cost
5.3. Characteristics Comparison
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Li, F.; Qiao, W.; Sun, H.; Wan, H.; Wang, J.; Xia, Y.; Xu, Z.; Zhang, P. Smart transmission grid: Vision and framework. Renew. Sustain. Energy Rev. 2010, 1, 168–177. [Google Scholar] [CrossRef]
- Challa, S.; Das, A.K.; Gope, P.; Kumar, N.; Wu, F. Design and analysis of authenticated key agreement scheme in cloud-assisted cyber/Physical systems. Future Gener. Comput. Syst. 2020, 108, 1267–1286. [Google Scholar] [CrossRef]
- Vasudev, H.; Das, D.; Vasilakos, A.V. Secure message propagation protocols for IoVs communication components. Comput. Electr. Eng. 2020, 82, 106555. [Google Scholar] [CrossRef]
- Kempton, W.; Tomi’c, J. Vehicle-to-grid power fundamentals: Calculating capacity and net revenue. J. Power Sources 2005, 144, 268–279. [Google Scholar] [CrossRef]
- Park, J.; Kim, H.; Choi, J. Improving TCP performance in vehicle-to-grid (V2G) communication. Electronics 2019, 8, 1206. [Google Scholar] [CrossRef]
- Shen, Y.; Fang, W.; Ye, F.; Kadoch, M. EV charging behavior analysis using hybrid intelligence for 5G smart grid. Electronics 2020, 9, 80. [Google Scholar] [CrossRef]
- Khan, P.; Byun, Y. Smart contract centric inference engine for intelligent electric vehicle transportation system. Sensors 2020, 20, 4252. [Google Scholar] [CrossRef]
- Fazeli, S.S.; Venkatachalam, S.; Chinnam, R.B.; Murat, A. Two-stage stochastic choice modeling approach for electric vehicle charging station network design in urban communities. IEEE Trans. Intell. Transp. Syst. 2020, 1–16. [Google Scholar] [CrossRef]
- Abronzini, U.; Attaianese, C.; D’Arpino, M.; Monaco, M.D.; Tomasso, G. Cost minimization energy control including battery aging for multi-source EV charging station. Electronics 2019, 8, 31. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Kumar, N.; Vasilakos, A.V. Design of secure key management and user authentication scheme for fog computing services. Future Gener. Comput. Syst. 2019, 91, 475–492. [Google Scholar] [CrossRef]
- Kaveh, M.; Mosavi, M.R. A lightweight mutual authentication for smart grid neighborhood area network communications based on physically unclonable function. IEEE Syst. J. 2020, 14, 4535–4544. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Bhat, V.; Vasilakos, A.V. LAM-CIoT: Lightweight authentication mechanism in cloud-based IoT environment. J. Netw. Comput. Appl. 2020, 150, 102496. [Google Scholar] [CrossRef]
- Aghapour, S.; Kaveh, M.; Martín, D.; Mosavi, M.R. An ultra-lightweight and provably secure broadcast authentication protocol for smart grid communications. IEEE Access 2020, 8, 125477–125487. [Google Scholar] [CrossRef]
- Mustafa, M.; Zhang, N.; Fan, Z. Smart electric vehicle charging: Security analysis. In Proceedings of the 2013 IEEE PES Innovative Smart Grid Technologies Conference, Washington, DC, USA, 24–27 February 2013; pp. 1–6. [Google Scholar]
- Guo, H.; Wu, Y.; Ma, M. UBAPV2G: A unique batch authentication protocol for vehicle-to-grid communications. IEEE Trans. Smart Grid 2011, 2, 707–714. [Google Scholar] [CrossRef]
- Liu, H.; Ning, H.; Yang, L. Role-dependent privacy preservation for secure V2G networks in the smart grid. IEEE Trans. Inf. Forensics Secur. 2014, 9, 208–220. [Google Scholar] [CrossRef]
- Yang, Z.; Yu, S.; Liu, C. P2: Privacy-preserving communication and precise reward architecture for V2G networks in smart grid. IEEE Trans. Smart Grid 2011, 2, 697–706. [Google Scholar] [CrossRef]
- Liu, H.; Ning, H.; Zhang, Y.; Yang, L.T. Aggregated-proofs based privacy-preserving authentication for V2G networks in the smart grid. IEEE Trans. Smart Grid 2012, 66, 1722–1733. [Google Scholar] [CrossRef]
- Abdallah, A.; Shen, X. Lightweight authentication and privacy-preserving scheme for V2G connections. IEEE Trans. Veh. Technol. 2017, 3, 2615–2629. [Google Scholar] [CrossRef]
- Saxena, N.; Choi, B.J. Authentication scheme for flexible charging and discharging of mobile vehicles in the V2G networks. IEEE Trans. Inf. Forensics Secur. 2016, 11, 1438–1452. [Google Scholar] [CrossRef]
- He, D.; Chan, S.; Guizani, M. A privacy-friendly and efficient secure communication framework for V2G networks. IET Commun. 2018, 12, 304–309. [Google Scholar] [CrossRef]
- Zhang, Y.; Gjessing, S.; Liu, H.; Ning, H.; Yang, L.T.; Guizani, M. Securing vehicle-to-grid communications in the smart grid. IEEE Wirel. Commun. 2018, 20, 66–73. [Google Scholar] [CrossRef]
- Shen, J.; Zhou, T.; Wei, F.; Sun, X.; Xiang, Y. Privacy-preserving and lightweight key agreement protocol for V2G in the social internet of things. IEEE Internet Things J. 2017, 5, 2526–2536. [Google Scholar] [CrossRef]
- He, D.; Zeadally, S.; Xu, B.; Huang, X. An efficient identity-based conditional privacy-preserving authentication scheme for vehicular ad hoc networks. IEEE Trans. Inf. Forensics Secur. 2015, 10, 2681–2691. [Google Scholar] [CrossRef]
- Liu, Y.; Wang, Y.; Chang, G. Efficient privacy-preserving dual authentication and key agreement scheme for secure V2V communications in an IoV paradigm. IEEE Trans. Intell. Transp. Syst. 2017, 18, 2740–2749. [Google Scholar] [CrossRef]
- Wang, H.; Qin, B.; Wu, Q.; Xu, L.; Domingo-Ferrer, J. TPP: Traceable privacy-preserving communication and precise reward for vehicle-to-grid networks in smart grids. IEEE Trans. Inf. Forensics Secur. 2015, 10, 2340–2351. [Google Scholar] [CrossRef]
- Vijayakumar, P.; Azees, M.; Kannan, A.; Deborah, L.J. Dual authentication and key management techniques for secure data transmission in vehicular ad hoc networks. IEEE Trans. Intell. Transp. Syst. 2016, 17, 1015–1028. [Google Scholar] [CrossRef]
- Tan, H.; Choi, D.; Kim, P.; Pan, S.; Chung, I. Comments on Dual authentication and key management techniques for secure data transmission in vehicular ad hoc networks. IEEE Trans. Intell. Transp. Syst. 2018, 19, 2149–2151. [Google Scholar] [CrossRef]
- Gope, P.; Sikdar, B. An efficient privacy-preserving authentication scheme for energy internet-based vehicle-to-grid communication. IEEE Trans. Smart Grid 2019, 10, 6607–6618. [Google Scholar] [CrossRef]
- Su, Y.; Shen, G.; Zhang, M. A novel privacy-preserving authentication scheme for V2G networks. IEEE Syst. J. 2019, 14, 1963–1971. [Google Scholar] [CrossRef]
- Abbasinezhad-Mood, D.; Ostad-Sharif, A.; Mazinani, S.M.; Nikooghadam, M. Provably-secure escrow-less Chebyshev chaotic map-based key agreement protocol for vehicle to grid connections with privacy protection. IEEE Trans. Ind. Inform. 2020, 2020, 1. [Google Scholar] [CrossRef]
- Gaurang, B.; Naren, N.; Chamola, V.; Sikdar, B.; Kumar, N.; Guizani, M. Lightweight mutual authentication protocol for V2G using physical unclonable function. IEEE Trans. Veh. Technol. 2020, 69, 7234–7246. [Google Scholar]
- Maes, R. Physically unclonable functions: concept and nonstructions. In Physically Unclonable Functions: Constructions, Properties and Applications; Springer: Berlin, Germany, 2012; ISBN 978-3-642-41395-7. [Google Scholar]
- Naveed, M.; Chaing, K.; Sikdar, B. Mutual authentication in IoT systems using physical unclonable functions. IEEE Internet Things J. 2017, 4, 1327–1340. [Google Scholar]
- Gope, P.; Lee, J.; Quek, T.Q. Lightweight and practical anonymous authentication protocol for RFID systems using physically unclonable functions. IEEE Trans. Inf. Forensics Secur. 2018, 13, 2831–2843. [Google Scholar] [CrossRef]
- Delavar, M.; Mirzakuchaki, S.; Mohajeri, J. A ring oscillator-based PUF with enhanced challenge-response pairs. Canadian J. Electr. Comput. Eng. 2016, 39, 174–180. [Google Scholar] [CrossRef]
- Gope, P.; Sikdar, B. Lightweight and privacy-preserving two-factor authentication scheme for IoT devices. IEEE Internet Things J. 2018, 6, 580–589. [Google Scholar] [CrossRef]
- Kaveh, M.; Aghapour, S.; Martin, D.; Mosavi, M.R. A secure lightweight signcryption scheme for smart grid communications using reliable physically unclonable function. In Proceedings of the IEEE International Conference on Environment and Electrical Engineering and IEEE Industrial and Commercial Power Systems Europe, Madrid, Spain, 9–12 June 2020; pp. 1–6. [Google Scholar]
- Gao, Y.; Su, Y.; Xu, L.; Ranasinghe, D.C. Lightweight (reverse) fuzzy extractor with multiple reference PUF responses. IEEE Trans. Inf. Forensics Secur. 2018, 14, 1887–1901. [Google Scholar] [CrossRef]
- Pandey, S.; Deyati, S.; Singh, A.; Chatterjee, A. Noise-resilient SRAM physically unclonable function design for security. In Proceedings of the IEEE 25th Asian Test Symposium (ATS), Hiroshima, Japan, 21–24 November 2016; pp. 55–60. [Google Scholar]
- Jeon, D.; Baek, J.H.; Kim, D.K.; Choi, B.D. Towards zero bit-error-rate physical unclonable function: Mismatch-based vs. physical-based approaches in standard CMOS technology. In Proceedings of the 2015 Euromicro Conference on Digital System Design, Madeira, Portugal, 26–28 August 2015; pp. 407–414. [Google Scholar]
- Chuang, K.H.; Bury, E.; Degraeve, R.; Kaczer, B.; Linten, D.; Verbauwhede, I. A physically unclonable function using soft oxide breakdown featuring 0% native BER and 51.8 Fj/Bit in 40-Nm CMOS. IEEE J. Solid State Circuits 2018, 54, 2765–2776. [Google Scholar] [CrossRef]
- Lu, X.; Hong, L.; Sengupta, K. CMOS optical PUFs using noise-immune process-sensitive photonic crystals incorporating passive variations for robustness. IEEE J. Solid State Circuits 2018, 53, 2709–2721. [Google Scholar] [CrossRef]
- Wang, W.C.; Yona, Y.S.; Diggavi, N.; Gupta, P. Design and analysis of stability-guaranteed PUFs. IEEE Trans. Inf. Forensics Secur. 2017, 13, 978–992. [Google Scholar] [CrossRef]
- Jindal, A.; Kumar, N.; Singh, M. Internet of energy-based demand response management scheme for smart homes and PHEVs using SVM. Future Gener. Comput. Syst. 2018, 108, 1058–1068. [Google Scholar] [CrossRef]
- ArduinoLibs: Cryptographic Library. 2019. Available online: http://rweather.github.io/arduinolibs/crypto.html (accessed on 11 June 2020).
- Herder, C.; Yu, M.D.; Koushanfar, F.; Devadas, S. Physical unclonable functions and applications: A tutorial. In Proceedings of the IEEE, Istanbul, Turkey, 3–5 April 2014; pp. 1126–1141. [Google Scholar]
- Abbasinezhad-Mood, D.; Nikooghadam, M. Efficient design of a novel ECC-based public key scheme for medical data protection by utilization of NanoPi fire. IEEE Trans. Reliab. 2018, 67, 1328–1339. [Google Scholar] [CrossRef]
- Zhu, H.; Zhang, Y.; Xia, Y.; Li, H. Password-authenticated key exchange scheme using chaotic maps towards a new architecture in standard model. IJ Netw. Secur. 2016, 18, 326–334. [Google Scholar]




| Notation | Description | Notation | Description |
|---|---|---|---|
| j-th Electrical Vehicle | location of in i-th authentication | ||
| n-th Charge Station | Timestamp | ||
| Grid Server | Hash of | ||
| Identity of in i-th Authentication | Logical XOR | ||
| Identity of | Concatenation operation | ||
| Byte | Second |
| EV | |||||||||||
| CS |
| Total Cost | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| [29] | 8 | 1 | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | |
| [30] | 2 | 1 | ✘ | 5 | 3 | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | |
| [31] | 7 | ✘ | ✘ | ✘ | ✘ | 4 | ✘ | 2 | ✘ | 1 | ✘ | |
| [32] | ✘ | 2 | 2 | ✘ | ✘ | ✘ | 2 | ✘ | 1 | 1 | 5 | |
| Ours | 3 | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kaveh, M.; Martín, D.; Mosavi, M.R. A Lightweight Authentication Scheme for V2G Communications: A PUF-Based Approach Ensuring Cyber/Physical Security and Identity/Location Privacy. Electronics 2020, 9, 1479. https://doi.org/10.3390/electronics9091479
Kaveh M, Martín D, Mosavi MR. A Lightweight Authentication Scheme for V2G Communications: A PUF-Based Approach Ensuring Cyber/Physical Security and Identity/Location Privacy. Electronics. 2020; 9(9):1479. https://doi.org/10.3390/electronics9091479
Chicago/Turabian StyleKaveh, Masoud, Diego Martín, and Mohammad Reza Mosavi. 2020. "A Lightweight Authentication Scheme for V2G Communications: A PUF-Based Approach Ensuring Cyber/Physical Security and Identity/Location Privacy" Electronics 9, no. 9: 1479. https://doi.org/10.3390/electronics9091479
APA StyleKaveh, M., Martín, D., & Mosavi, M. R. (2020). A Lightweight Authentication Scheme for V2G Communications: A PUF-Based Approach Ensuring Cyber/Physical Security and Identity/Location Privacy. Electronics, 9(9), 1479. https://doi.org/10.3390/electronics9091479







