Non-Cooperative Spectrum Access Strategy Based on Impatient Behavior of Secondary Users in Cognitive Radio Networks
Abstract
:1. Introduction
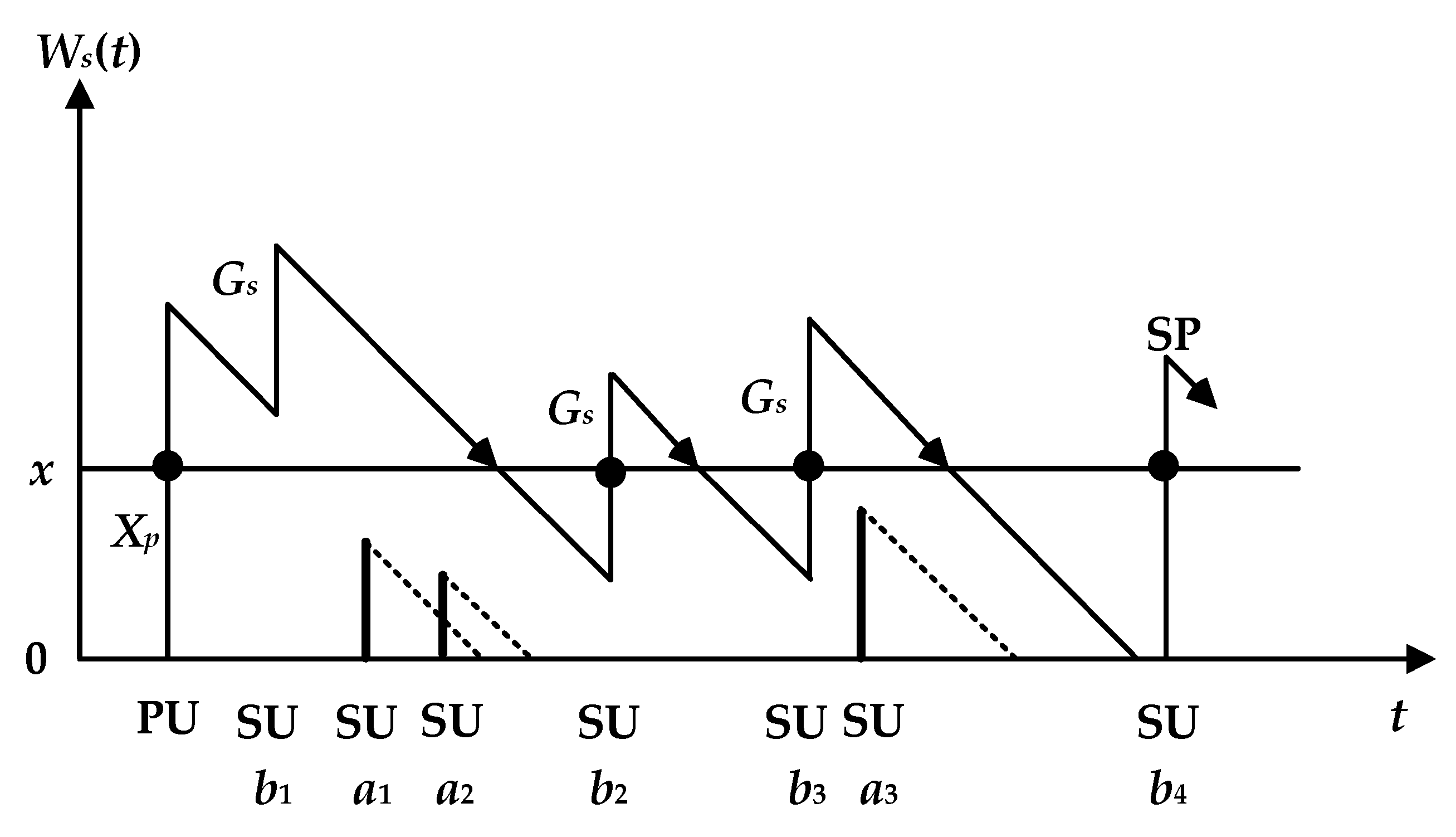
2. System Model and Problem Statement
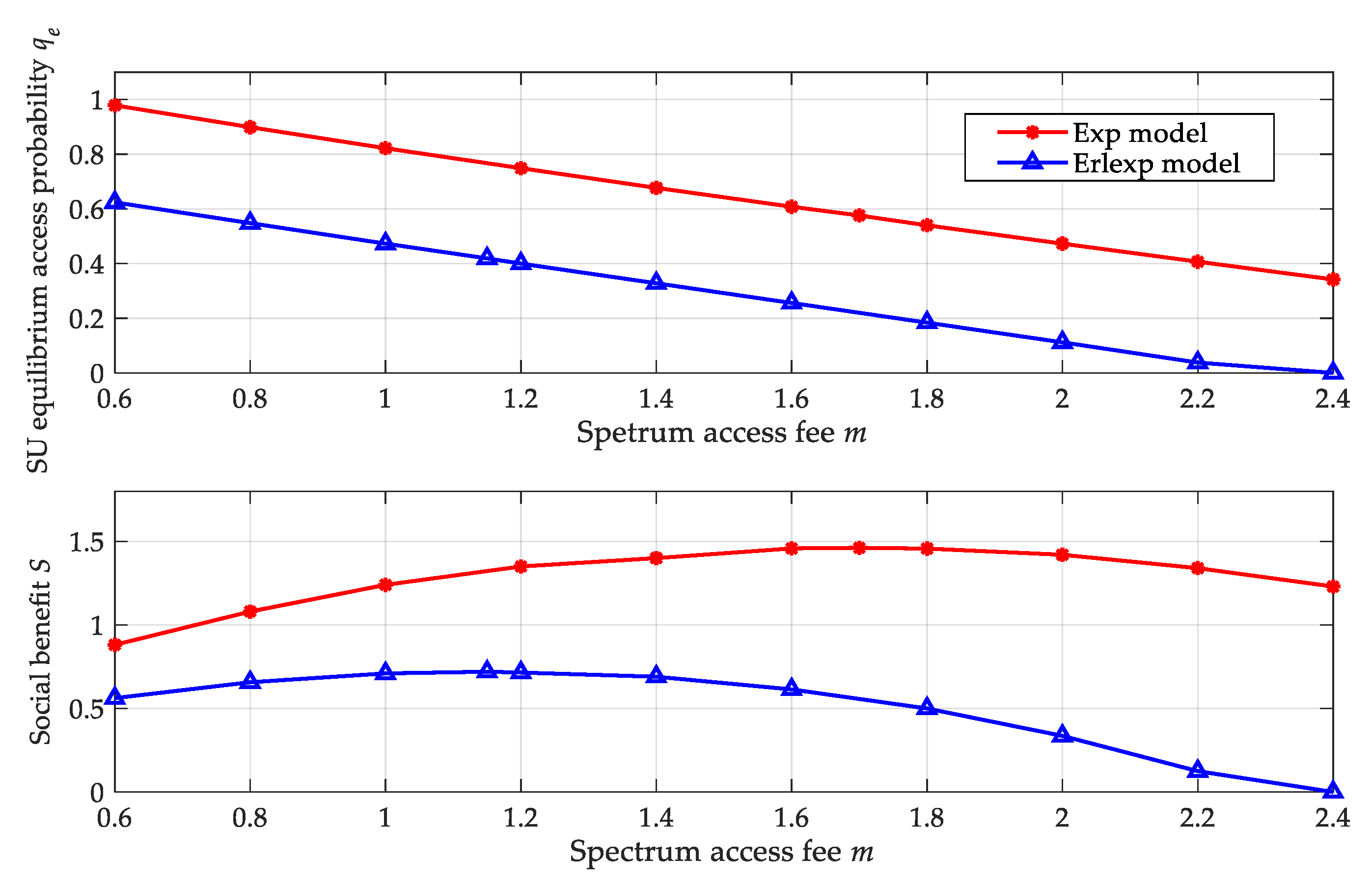
3. Spectrum Access Strategies of SUs
3.1. Individual Equilibrium Strategy
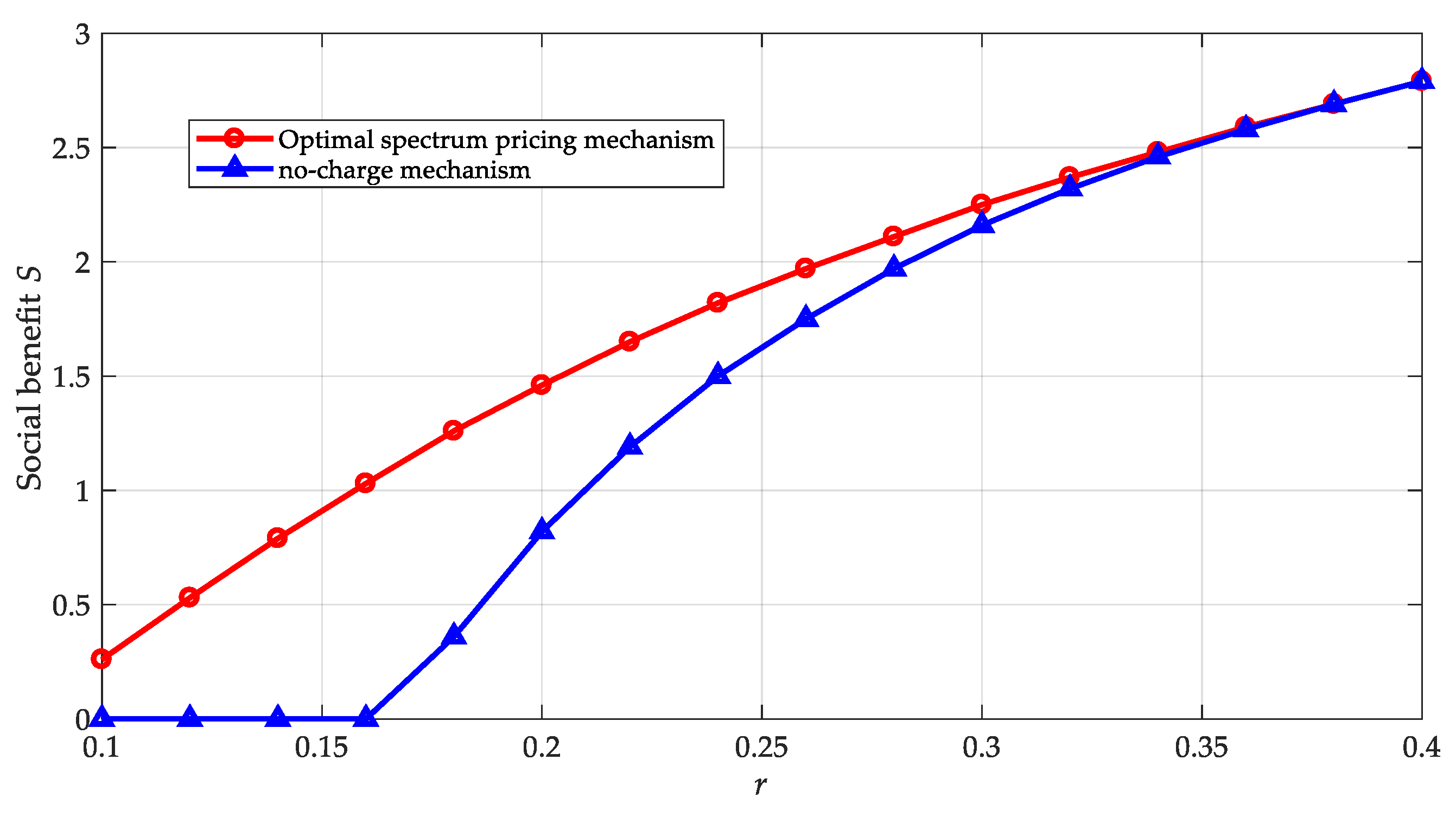
3.2. Socially Optimal Strategy
3.3. Spectrum Pricing
4. Numerical Results
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix
References
- Wang, J.; Gao, Y.; Yin, X.; Li, F.; Kim, H.J. An enhanced PEGASIS algorithm with mobile sink support for wireless sensor networks. Wirel. Commun. Mob. Comput. 2018, 2018, 9472075. [Google Scholar] [CrossRef]
- Lin, Y.; Zhu, X.L.; Zheng, Z.G.; Dou, Z.; Zhou, R.L. The individual identification method of wireless device based on dimensionality reduction and machine learning. J. Supercomput. 2019, 75, 3010–3027. [Google Scholar] [CrossRef]
- Kumar, D.P.; Amgoth, T.; Annavarapu, C.S.R. Machine learning algorithms for wireless sensor networks: A survey. Inform. Fusion 2019, 49, 1–25. [Google Scholar] [CrossRef]
- Wang, J.; Gao, Y.; Liu, W.; Wu, W.B.; Lim, S. An asynchronous clustering and mobile data gathering schema based on timer mechanism in wireless sensor networks. Comput. Mater. Contin. 2019, 58, 711–725. [Google Scholar] [CrossRef]
- Wang, J.; Gu, X.J.; Liu, W.; Sangaiah, A.K.; Kim, H.J. An empower hamilton loop based data collection algorithm with mobile agent for WSNs. Hum-Cent. Comput. Inf. Sci. 2019, 9, 18. [Google Scholar] [CrossRef]
- Park, J.H.; Lee, W.C.; Choi, J.P.; Choi, J.W.; Um, S.B. Applying case-based reasoning to tactical cognitive sensor networks for dynamic frequency allocation. Sensors 2018, 18, 4294. [Google Scholar] [CrossRef] [PubMed]
- Wang, J.; Gao, Y.; Liu, W.; Sangaiah, A.K.; Kim, H.J. An intelligent data gathering schema with data fusion supported for mobile sink in WSNs. Int. J. Distrib. Sens. Netw. 2019, 15. [Google Scholar] [CrossRef]
- Dou, Z.; Si, G.Z.; Lin, Y.; Wang, M.Y. An adaptive resource allocation model with anti-jamming in IoT network. IEEE Access 2019, 7, 93250–93258. [Google Scholar] [CrossRef]
- Zhang, Z.Y.; Guo, X.H.; Lin, Y. Trust management method of D2D communication based on RF fingerprint identification. IEEE Access 2018, 6, 66082–66087. [Google Scholar] [CrossRef]
- Nguyen, T.; Pan, J.; Dao, T. An Improved Flower Pollination Algorithm for Optimizing Layouts of Nodes in Wireless Sensor Network. IEEE Access 2019, 7, 75985–75998. [Google Scholar] [CrossRef]
- Yin, Y.; Xu, Y.; Xu, W.; Min, G.; Pei, Y. Collaborative Service Selection via Ensemble Learning in Mixed Mobile Network Environments. Entropy 2017, 19, 358. [Google Scholar] [CrossRef]
- He, S.; Xie, K.; Xie, K.; Xu, C.; Jin, W. Interference-aware Multi-source Transmission in Multi-radio and Multi-channel Wireless Network. IEEE Syst. J. 2019, 13, 2507–2518. [Google Scholar] [CrossRef]
- He, S.; Xie, K.; Chen, W.; Zhang, D.; Wen, J. Energy-aware Routing for SWIPT in Multi-hop Energy-constrained Wireless Network. IEEE Access 2018, 6, 17996–18008. [Google Scholar] [CrossRef]
- Wang, D.; Song, B.; Chen, D.; Du, X.J. Intelligent cognitive radio in 5G: AI-based hierarchical cognitive cellular networks. IEEE Wirel. Commun. 2019, 26, 54–61. [Google Scholar] [CrossRef]
- Kotobi, K.; Mainwaring, P.B.; Tucker, C.S.; Bilen, S.G. Data-throughput enhancement using data mining-informed cognitive radio. Electronics 2015, 4, 221–238. [Google Scholar] [CrossRef]
- Haykin, S. Cognitive radio: Brain-empowered wireless communications. IEEE J. Sel. Areas Commun. 2005, 23, 201–220. [Google Scholar] [CrossRef]
- Tang, B.; Tu, Y.; Zhang, Z.Y.; Lin, Y. Digital signal modulation classification with data augmentation using generative adversarial nets in cognitive radio networks. IEEE Access 2018, 6, 15713–15722. [Google Scholar] [CrossRef]
- Tu, Y.; Lin, Y.; Wang, J.; Kim, J.U. Semi-supervised learning with generative adversarial networks on digital signal modulation classification. CMC-Comput. Mater. Contin. 2018, 55, 243–254. [Google Scholar]
- Zhang, J.; Jin, X.; Sun, J.; Wang, J.; Sangaiah, A. Spatial and semantic convolutional features for robust visual object tracking. Multimed. Tools Appl. 2018, in press. [Google Scholar] [CrossRef]
- Zhang, J.; Lu, C.; Li, X.; Kim, H.; Wang, J. A full convolutional network based on DenseNet for remote sensing scene classification. Math. Biosci. Eng. 2019, 16, 3345–3367. [Google Scholar] [CrossRef]
- Zhang, J.; Lu, C.; Wang, J.; Wang, L.; Yue, X. Concrete cracks detection based on FCN with dilated convolution. Appl. Sci. 2019, 9, 2686. [Google Scholar] [CrossRef]
- Zhang, J.; Jin, X.; Sun, J.; Wang, J.; Li, K. Dual model learning combined with multiple feature selection for accurate visual tracking. IEEE Access 2019, 7, 43956–43969. [Google Scholar] [CrossRef]
- Yin, Y.; Chen, L.; Xu, Y.; Wan, J.; Mai, Z. QoS prediction for service recommendation with deep feature learning in edge computing environment. Mob. Netw. Appl. 2019. [Google Scholar] [CrossRef]
- Lin, Y.; Wang, C.; Wang, J.X.; Dou, Z. A novel dynamic spectrum access framework based on reinforcement learning for cognitive radio sensor networks. Sensors 2016, 16, 1675. [Google Scholar] [CrossRef] [PubMed]
- Zakariya, A.Y.; Rabia, S.I. Analysis of an interruption-based priority for multi-class secondary users in cognitive radio networks. In Proceedings of the 2016 IEEE International Conference on Communications (ICC), Kuala Lumpur, Malaysia, 22–27 May 2016. [Google Scholar]
- Joo, C.; Shroff, N.B. A novel coupled queueing model to control traffic via QoS-aware collision pricing in cognitive radio networks. In Proceedings of the IEEE INFOCOM 2017—IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017. [Google Scholar]
- Wang, Y.C.; Tang, X.; Wang, T. A unified QoS and security provisioning framework for wiretap cognitive radio networks: A statistical queueing analysis approach. IEEE Trans. Wirel. Commun. 2019, 18, 1548–1565. [Google Scholar] [CrossRef]
- Wang, S.; Maharaj, B.T.; Alfa, A.S. Queueing analysis of performance measures under a new configurable channel allocation in cognitive radio. IEEE Trans. Veh. Technol. 2018, 67, 9571–9582. [Google Scholar] [CrossRef]
- Kosta, A.; Pappas, N.; Ephremides, A.; Angelakis, V. Age of information and throughput in a shared access network with heterogeneous traffic. In Proceedings of the 2018 IEEE Global Communications Conference (GLOBECOM), Abu Dhabi, United Arab Emirates, 9–13 December 2018. [Google Scholar]
- Wang, L.C.; Wang, C.W.; Adachi, F. Load-balancing spectrum decision for cognitive radio networks. IEEE J. Sel. Areas Commun. 2011, 29, 757–769. [Google Scholar] [CrossRef]
- Jagannathan, K.; Menache, I.; Modiano, E.; Zussman, G. Non-cooperative spectrum access - the dedicated vs. free spectrum choice. IEEE J. Sel. Areas Commun. 2012, 30, 2251–2261. [Google Scholar] [CrossRef]
- Zhu, S.; Wang, J.T.; Li, W.W. Optimal service rate in cognitive radio networks with different queue length information. IEEE Access 2018, 6, 51577–51586. [Google Scholar] [CrossRef]
- Wang, J.; Huang, A.P.; Wang, W. Admission control in cognitive radio networks with finite queue and user impatience. IEEE Wirel. Commun. Lett. 2013, 2, 175–178. [Google Scholar] [CrossRef]
- Jin, S.F.; Ge, S.Y.; Yue, W.Y. Performance evaluation for an opportunistic spectrum access mechanism with impatience behavior and imperfect sensing results. In Proceedings of the 2015 Seventh International Conference on U-Biquitous and Future Networks, Sapporo, Japan, 7–10 July 2015. [Google Scholar]
- Li, H.S.; Han, Z. Socially optimal queuing control in cognitive radio networks subject to service interruptions: To queue or not to queue? IEEE Trans. Wirel. Commun. 2011, 10, 1656–1666. [Google Scholar]
- Do, C.T.; Tran, N.H.; Nguyen, M.V.; Hong, C.S.; Lee, S. Social optimization strategy in unobserved queueing systems in cognitive radio networks. IEEE Commun. Lett. 2012, 16, 1944–1947. [Google Scholar] [CrossRef]
- Smith, P.J.; Senanayake, R.; Dmochowski, P.A.; Evans, J.S. Distributed spectrum sensing for cognitive radio networks based on the sphericity test. IEEE Trans. Commun. 2019, 67, 1831–1844. [Google Scholar] [CrossRef]
- Lu, Y.; Duel-Hallen, A. A sensing contribution-based two-layer game for channel selection and spectrum access in cognitive radio Ad-hoc networks. IEEE Trans. Wirel. Commun. 2018, 17, 3631–3640. [Google Scholar] [CrossRef]
- Zhang, Y.; Wang, J.T.; Li, W.W. Optimal pricing strategies in cognitive radio networks with heterogeneous secondary users and retrials. IEEE Access 2019, 7, 3631–3640. [Google Scholar] [CrossRef]
- Stanford, R.E. Reneging phenomena in Single channel queues. Math. Oper. Res. 1979, 4, 162–178. [Google Scholar] [CrossRef]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zeng, Z.; Liu, M.; Wang, J.; Lan, D. Non-Cooperative Spectrum Access Strategy Based on Impatient Behavior of Secondary Users in Cognitive Radio Networks. Electronics 2019, 8, 995. https://doi.org/10.3390/electronics8090995
Zeng Z, Liu M, Wang J, Lan D. Non-Cooperative Spectrum Access Strategy Based on Impatient Behavior of Secondary Users in Cognitive Radio Networks. Electronics. 2019; 8(9):995. https://doi.org/10.3390/electronics8090995
Chicago/Turabian StyleZeng, Zhen, Meng Liu, Jin Wang, and Dongping Lan. 2019. "Non-Cooperative Spectrum Access Strategy Based on Impatient Behavior of Secondary Users in Cognitive Radio Networks" Electronics 8, no. 9: 995. https://doi.org/10.3390/electronics8090995
APA StyleZeng, Z., Liu, M., Wang, J., & Lan, D. (2019). Non-Cooperative Spectrum Access Strategy Based on Impatient Behavior of Secondary Users in Cognitive Radio Networks. Electronics, 8(9), 995. https://doi.org/10.3390/electronics8090995




