An IoT Architecture for Continuous Livestock Monitoring Using LoRa LPWAN
Abstract
1. Introduction
2. Related Works
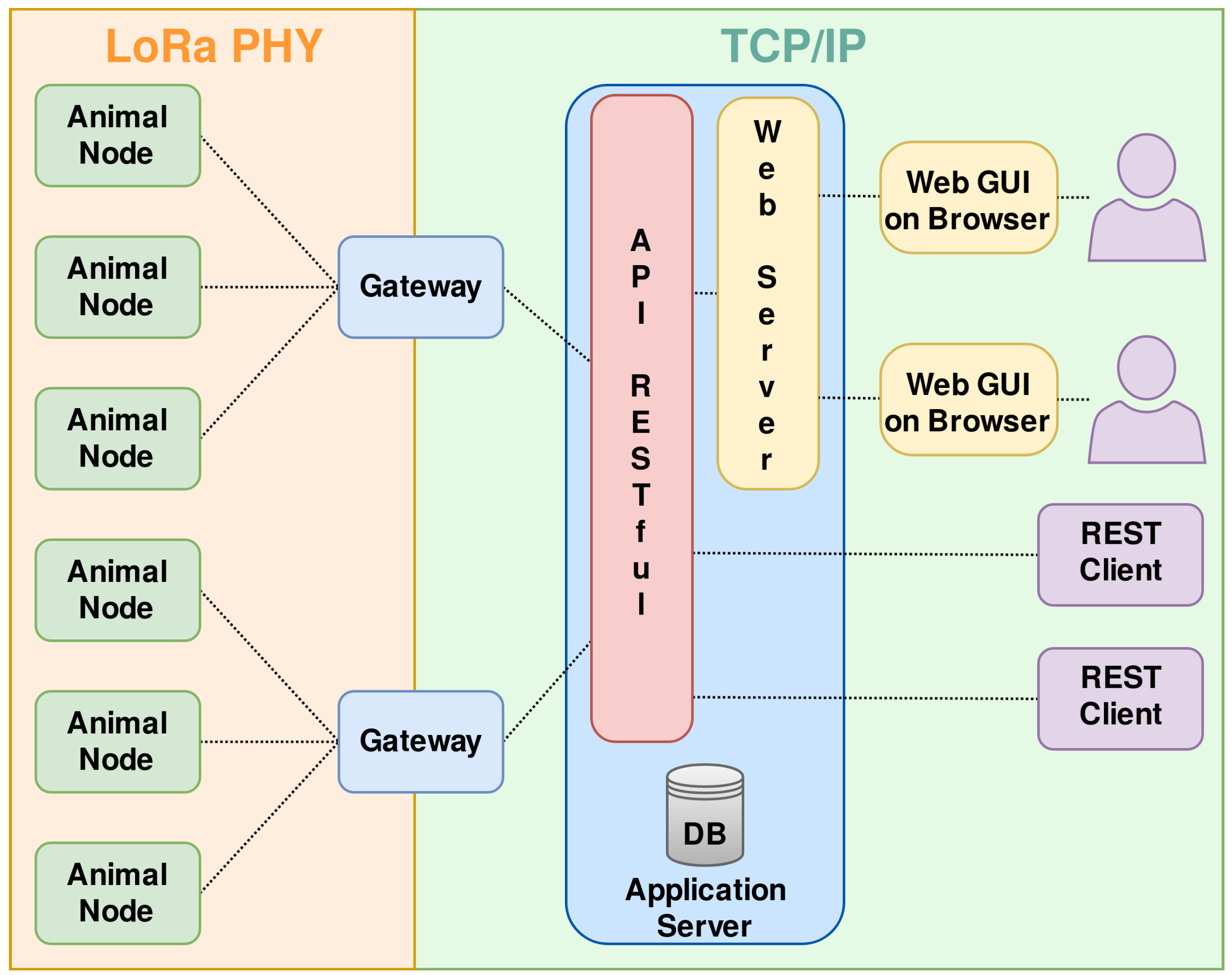
3. System Architecture
3.1. Application Server
3.1.1. API Description
- Data uploading: The sensor data aggregated on the GW are uploaded via a POST request to the HTTP service. The request carries the sensor identifier, the GW identifier, the ED identifier, the data value, and an access token. If the data are successfully uploaded, the service returns HTTP code 200 (OK), to indicate success. Otherwise, HTTP code 203 is returned to indicate a duplicate data insertion, and HTTP code 403 to denote an unauthorized action; other HTTP codes can also be used, following the standard numbering.
- Data downloading: The client can request stored data values over a specified time interval or from some moment in the past up to the current time. The request is done via a POST command and comprises the sensor identifier, the start and stop times of the interval or the time duration in seconds, and an access token. If the command is executed with success, the data are returned in JSON format as an array of couples, where each couple stores the data sample value and the data sample time.
3.1.2. Database Storage
3.2. Gateways
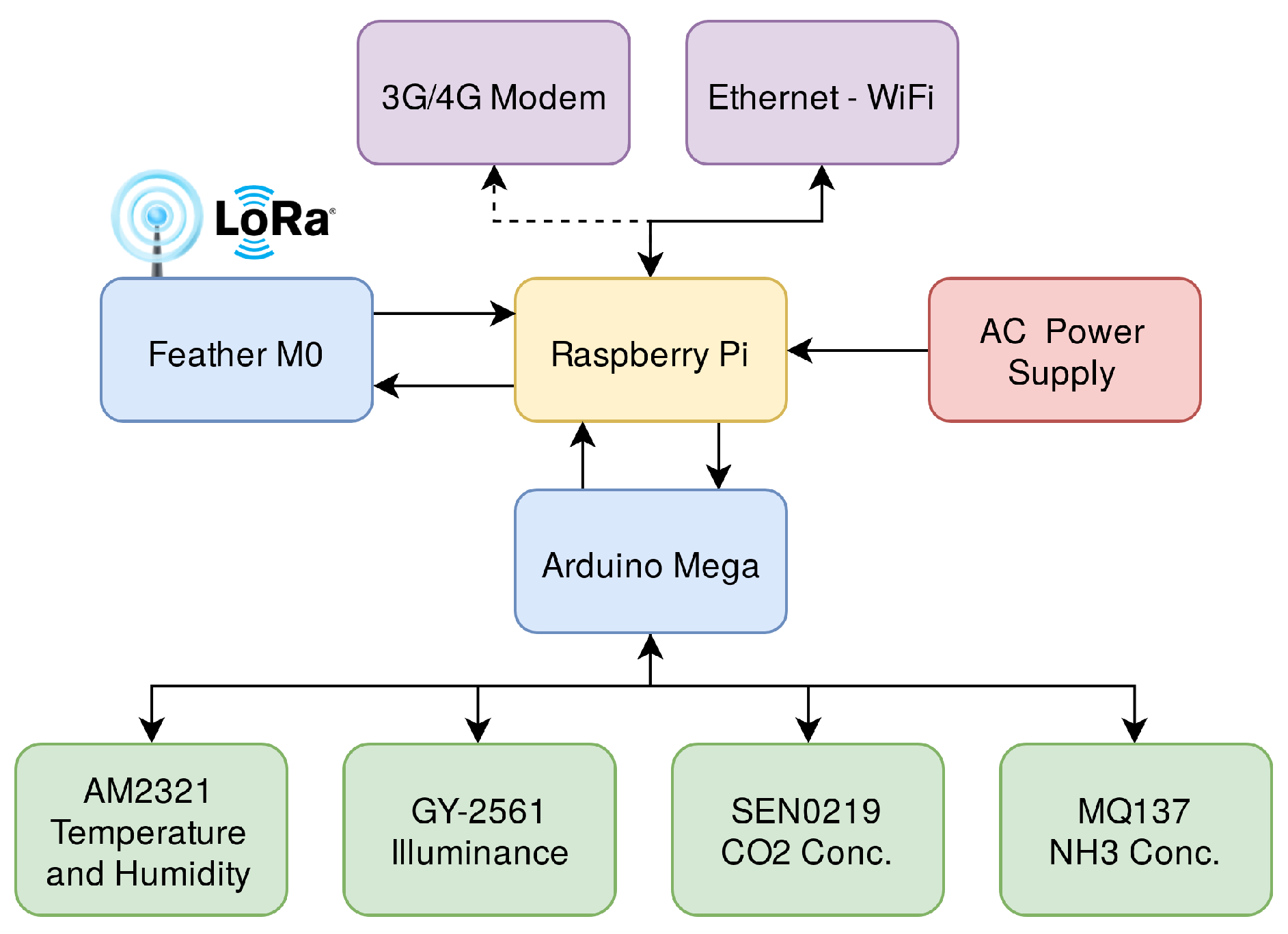
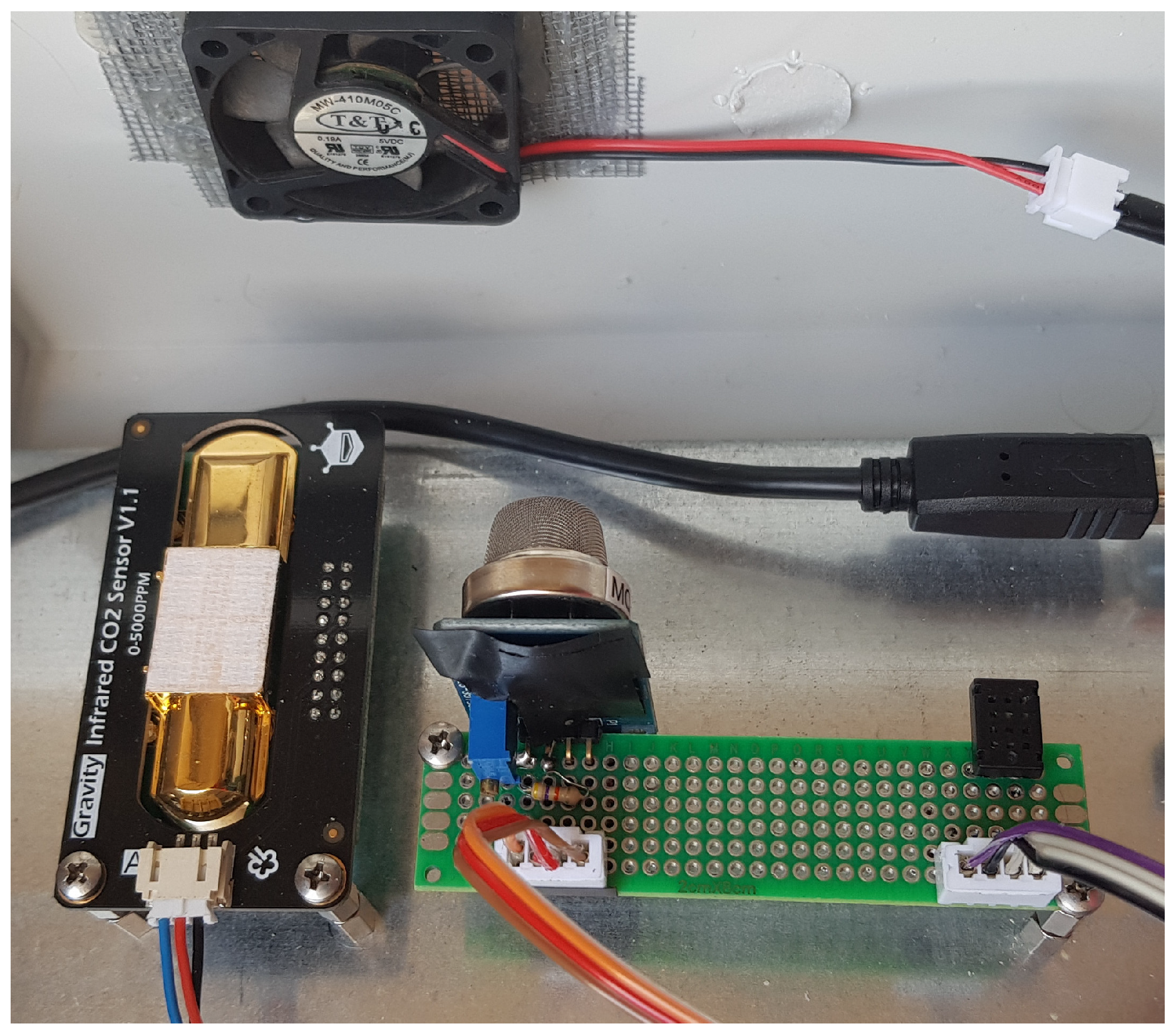
3.2.1. Indoor Version
- Aosong AM2321 [44]: Queried on the I2C bus, records the external temperature with a resolution of 0.1 °C and accuracy of ±0.5 °C in the range from −40 °C to 80 °C, and the relative humidity with a resolution of 0.1 % and accuracy of ±3 %.
- Adafruit TLS2561 (GY-2561) [45]: Queried on the I2C bus, records the illuminance in a range from 0.1 lx to 40000 lx with a dynamically varying resolution.
- DFRobot SEN0219 [46]: Queried on the analog pins, records the concentration with an accuracy of about ±50 ppm in the range from 0 ppm to 5000 ppm;
- Winsen MQ137 [47]: Queried on the analog pins, records the concentration within a range from 5 ppm to 500 ppm.
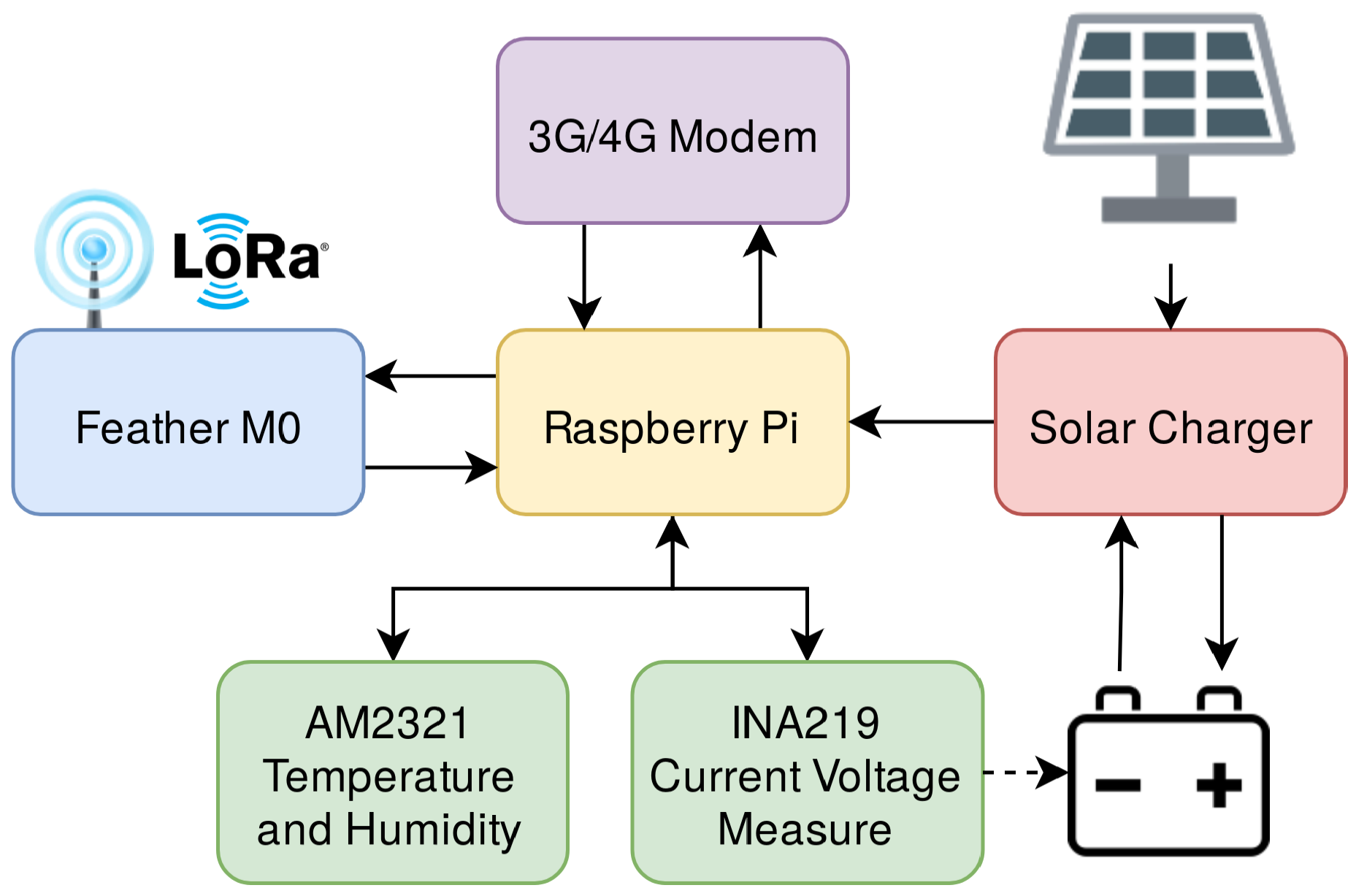
3.2.2. Outdoor Version
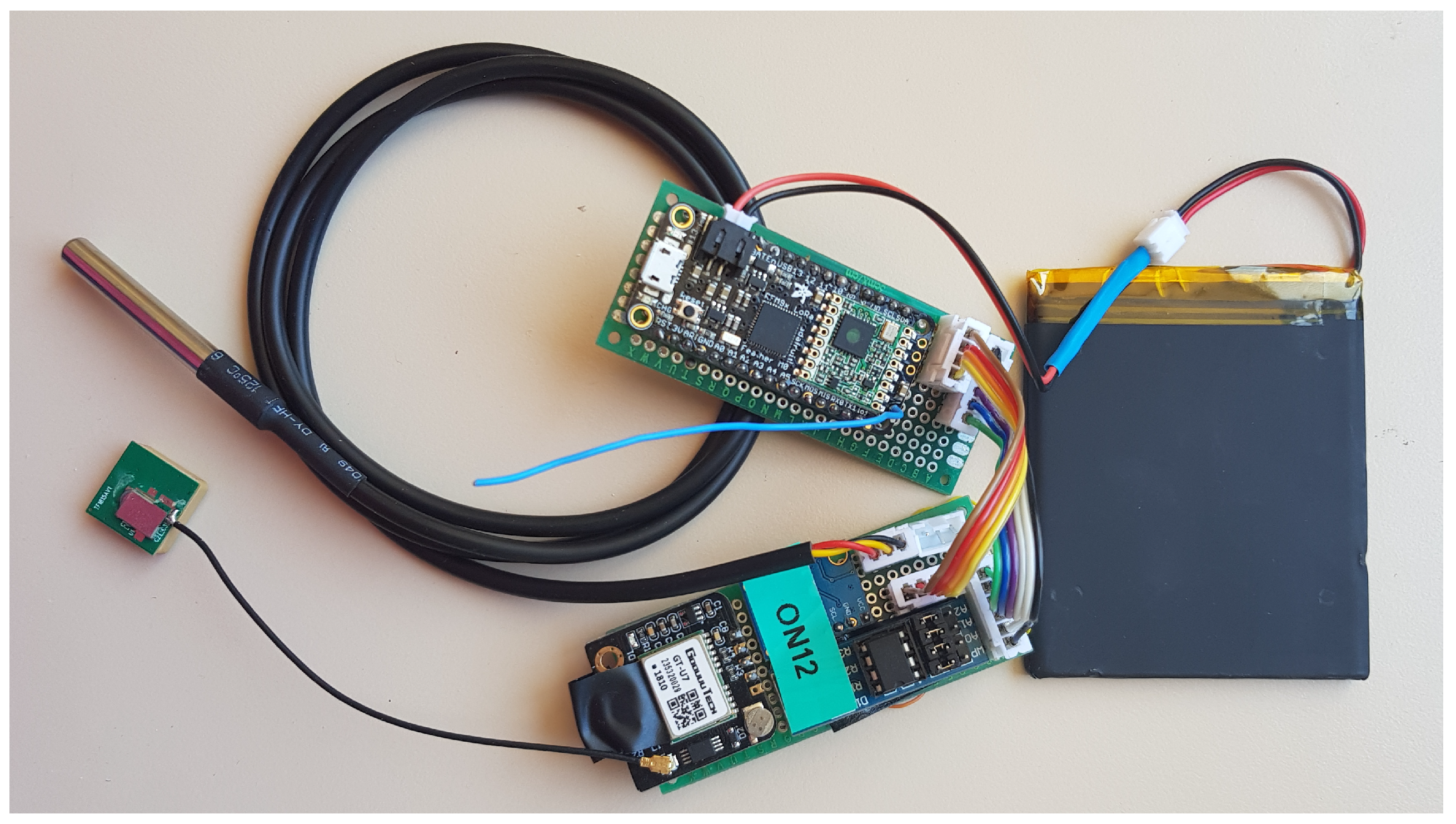
3.3. End Devices
3.3.1. HW Implementation
- u-blox Neo-6m [49]: GNSS receiver for precise geographic positioning that communicates NMEA messages via UART;
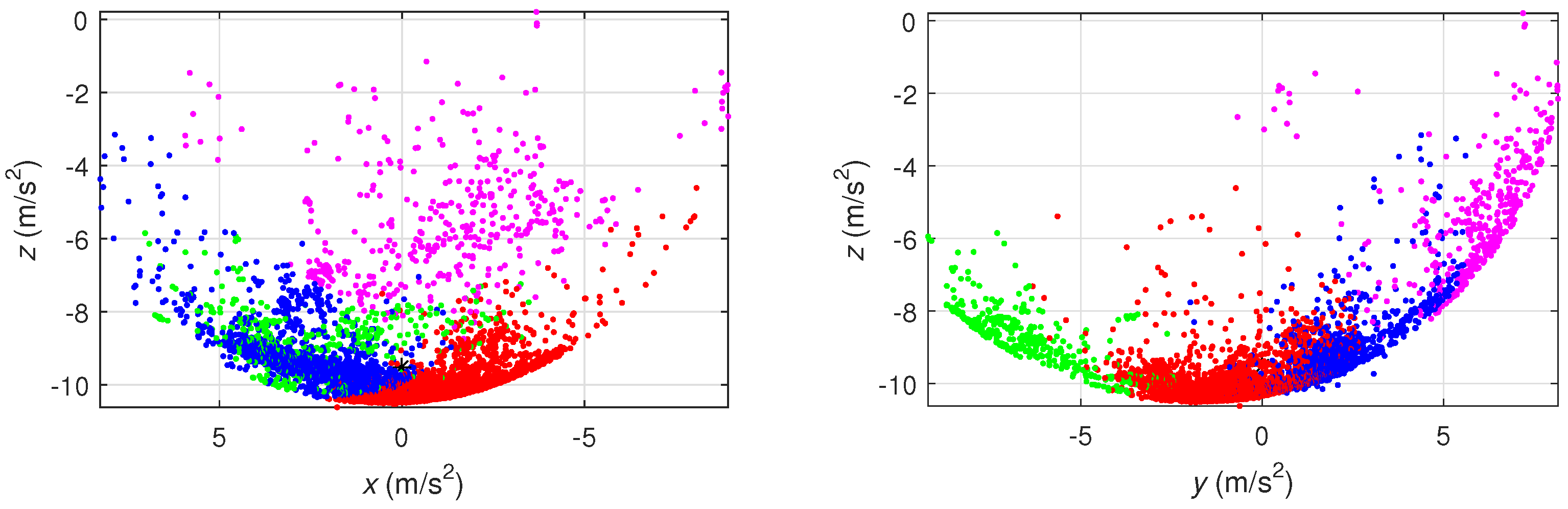
- InvenSense MPU-6050 [50]: Queried on the I2C bus, records accelerations and rotations;
- WINOMO DS18B20 [51]: Queried via a digital pin using One Wire protocol, measures body temperature with an accuracy of ±0.5 °C in the range from −10 °C to 85 °C.
3.3.2. Custom Access Protocol
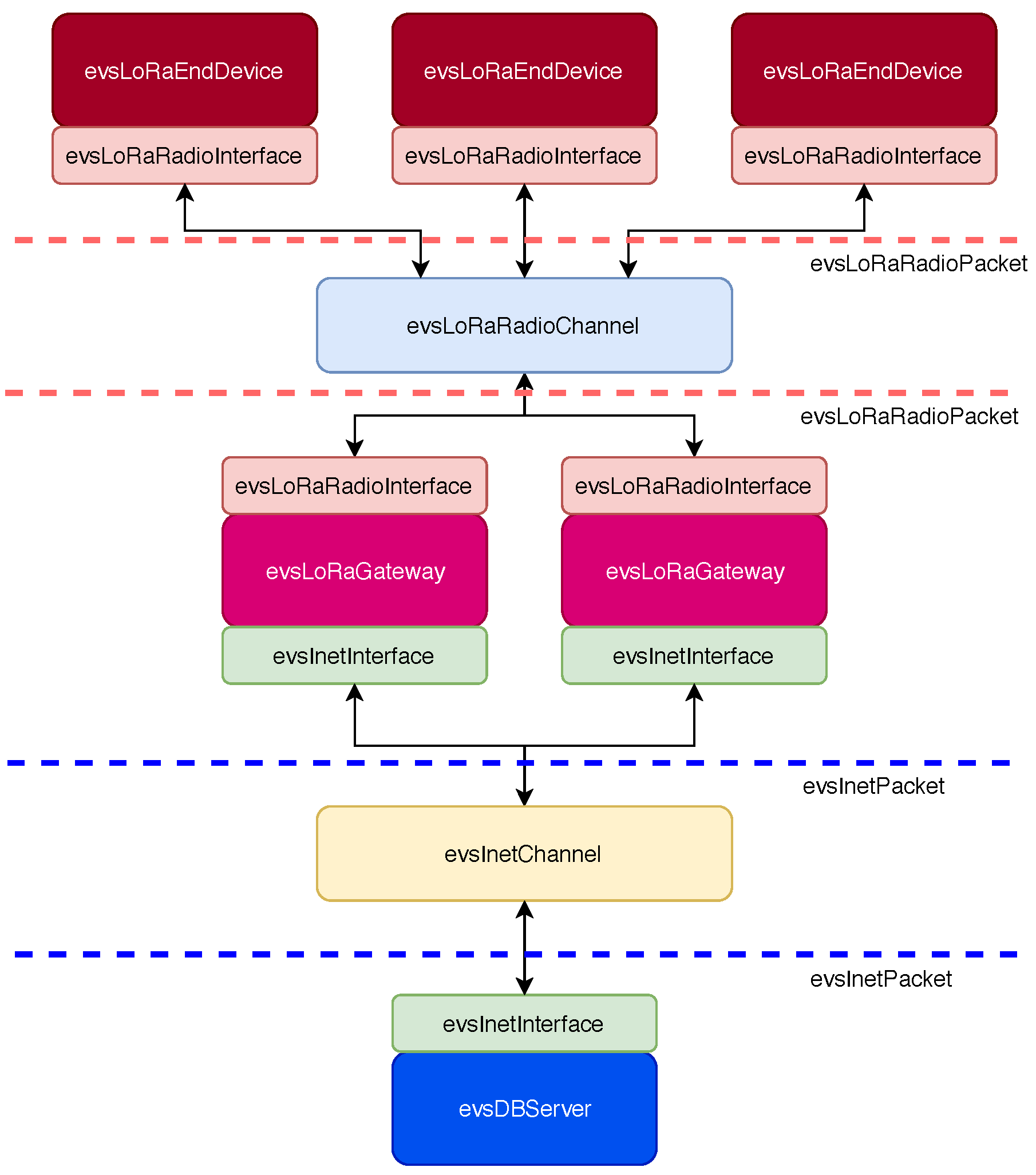
4. PHY/MAC Level Simulator
- evsChannel: This class represents the communication channels, upon which data delivery may take place as a byte packet exchange;
- evsDevice: This class represents the communication devices, characterized as a finite state machine with MAC arbitration policies;
- evsInterface: This class acts as a connector between the communication devices and the communication channels. For instance, a device may act as bridge between different communication channels by incorporating multiple interfaces.
- evsInetChannel: This object represents a generic Internet data channel with reliable packet delivery (e.g., TCP/IP);
- evsRadioChannel: This object represents a generic radio communication channel characterized by attenuation and packet losses;
- evsLoRaEndDevice: This object represents a LoRa ED;
- evsLoRaGateway: This object represents a LoRa gateway;
- evsDBServer: This object represents the server hosting the database;
- evsInetInterface: This object represents the interface towards an Internet communication channel;
- evsLoRaRadioInterface: This object represents the interface towards a radio communication channel.
- evsInetPacket: A data packet delivered through the reliable Internet communication channel;
- evsLoRaRadioPacket: A data packet unreliably delivered through the radio communication channel with the LoRa PHY.
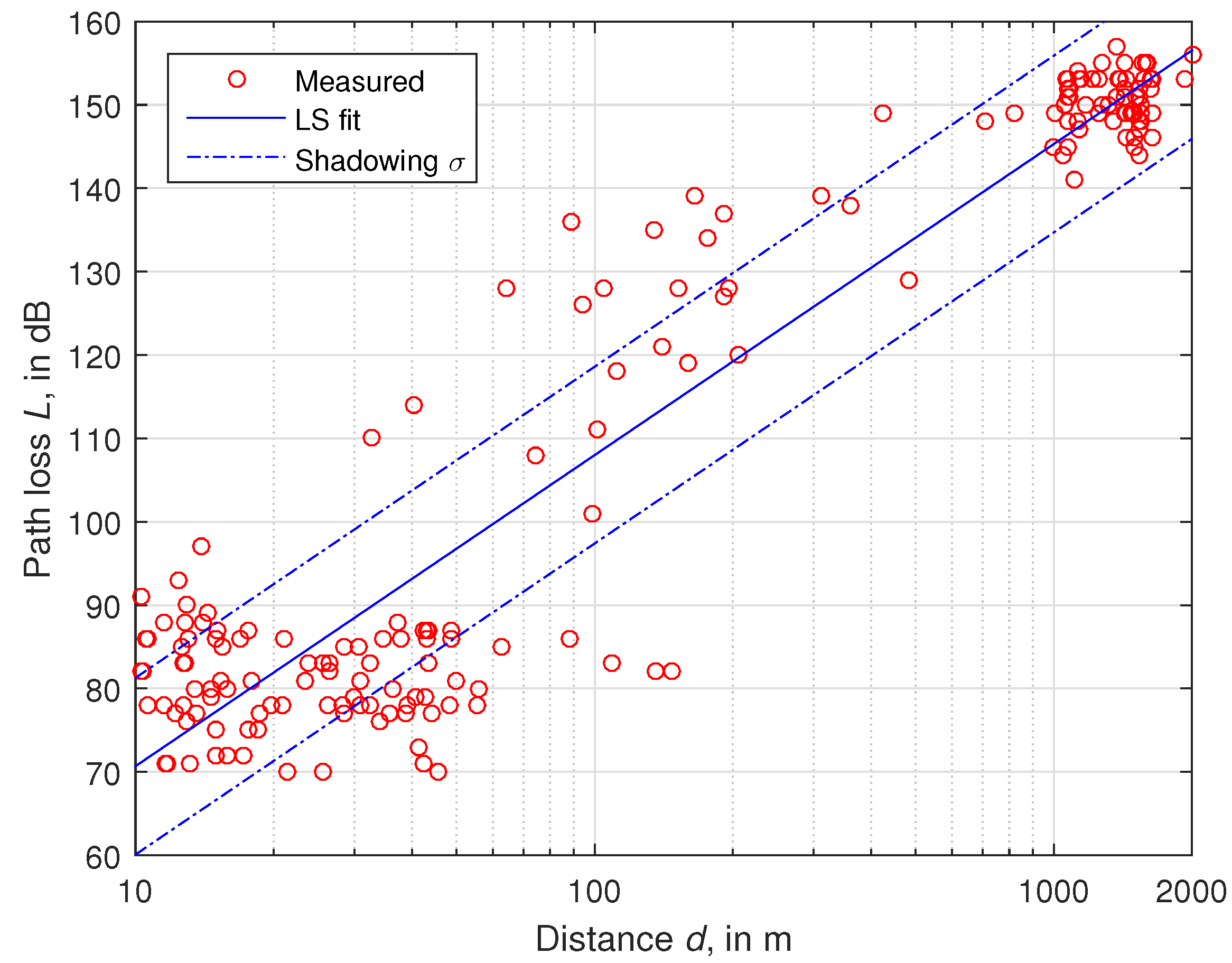
4.1. Physical Layer Model
4.2. MAC and Transport Layer Model
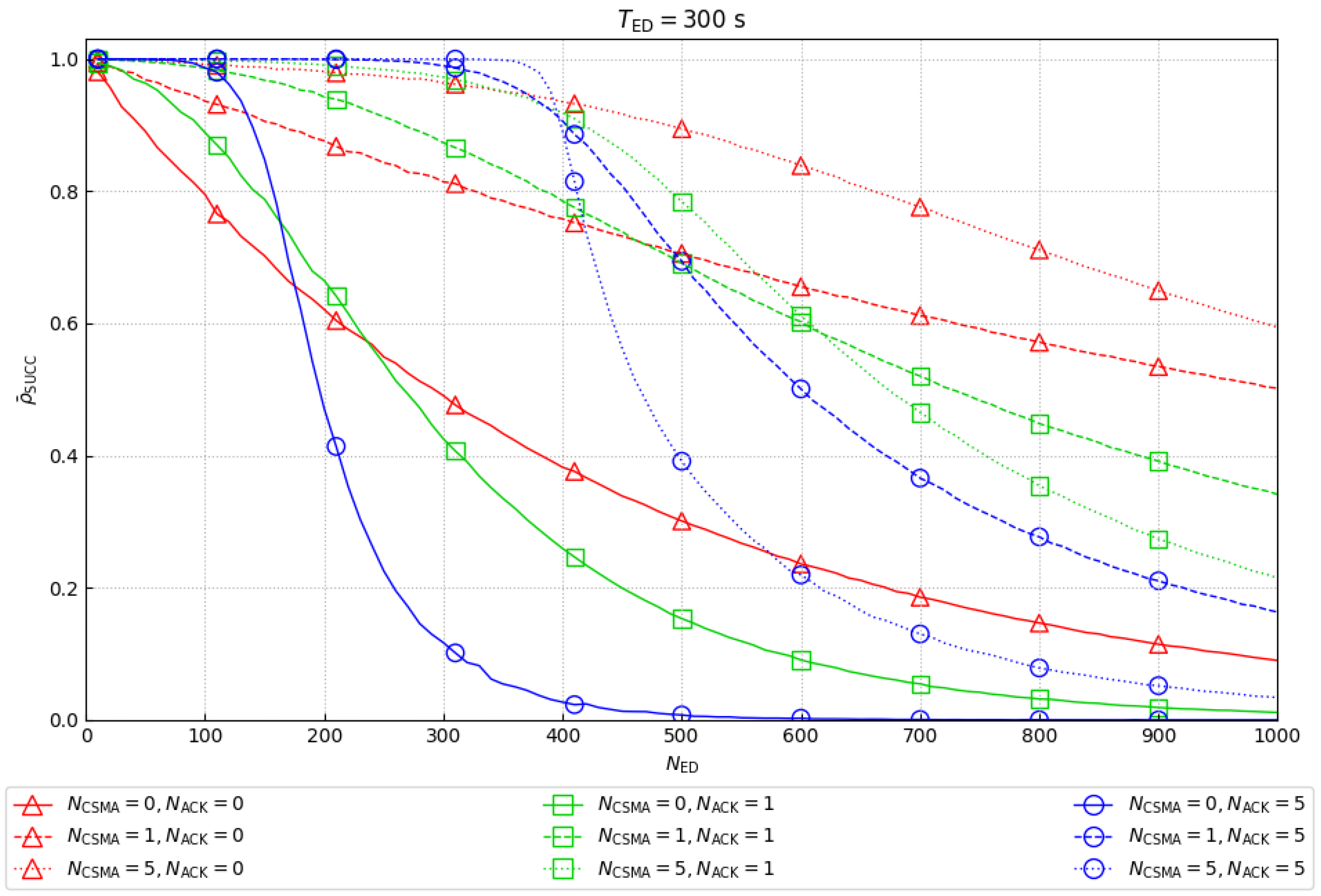
5. Simulation Results
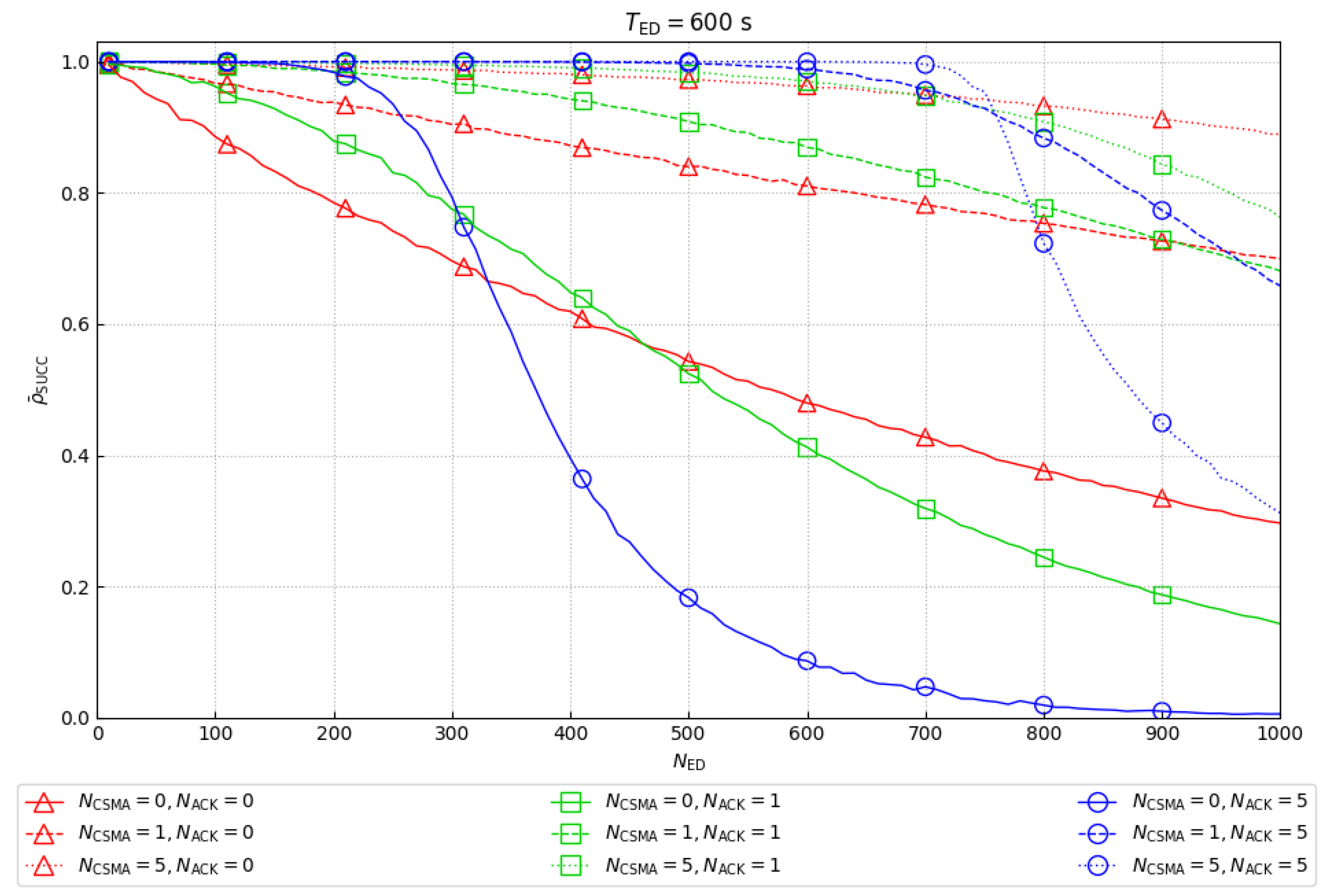
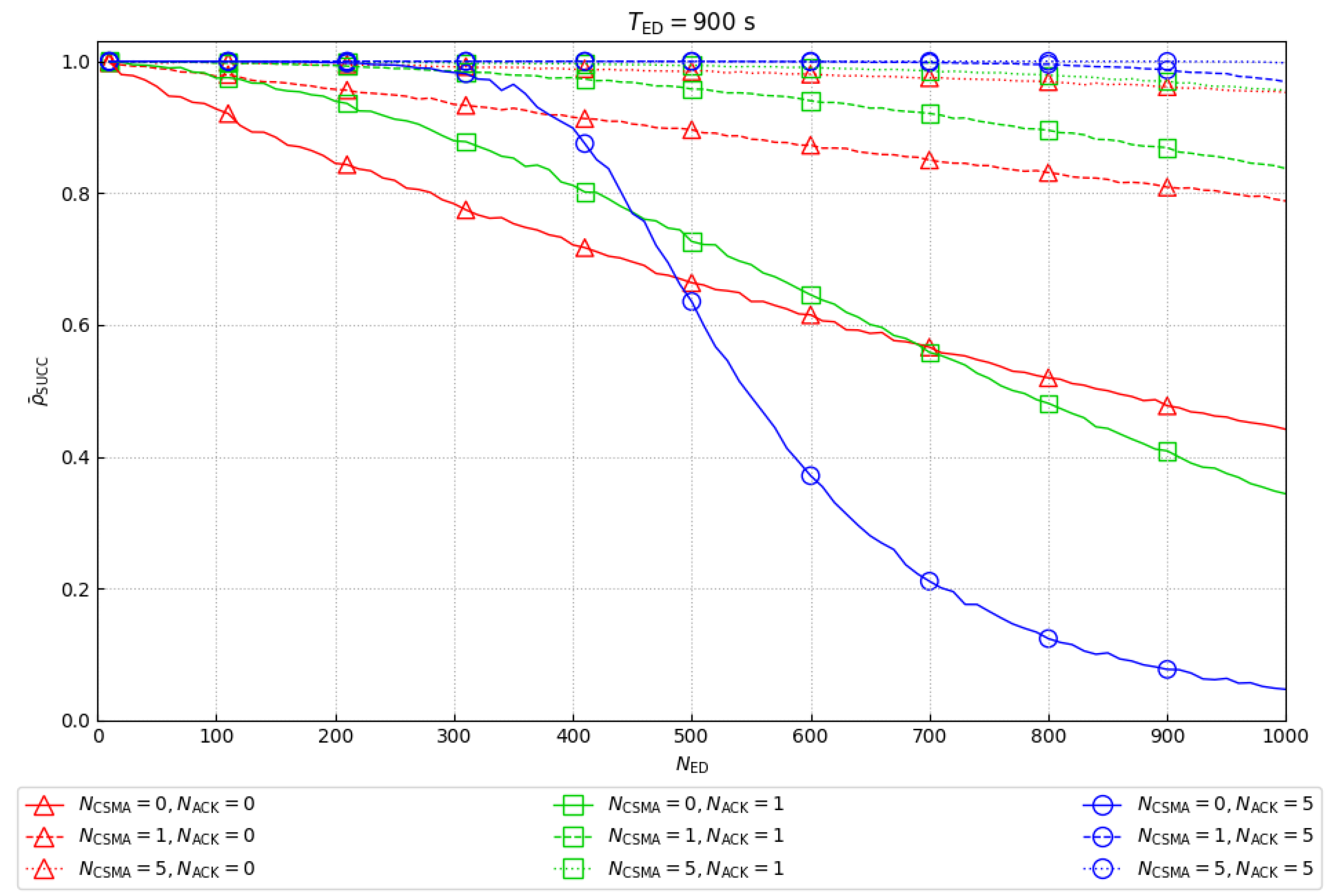
5.1. Global Average Success Rate
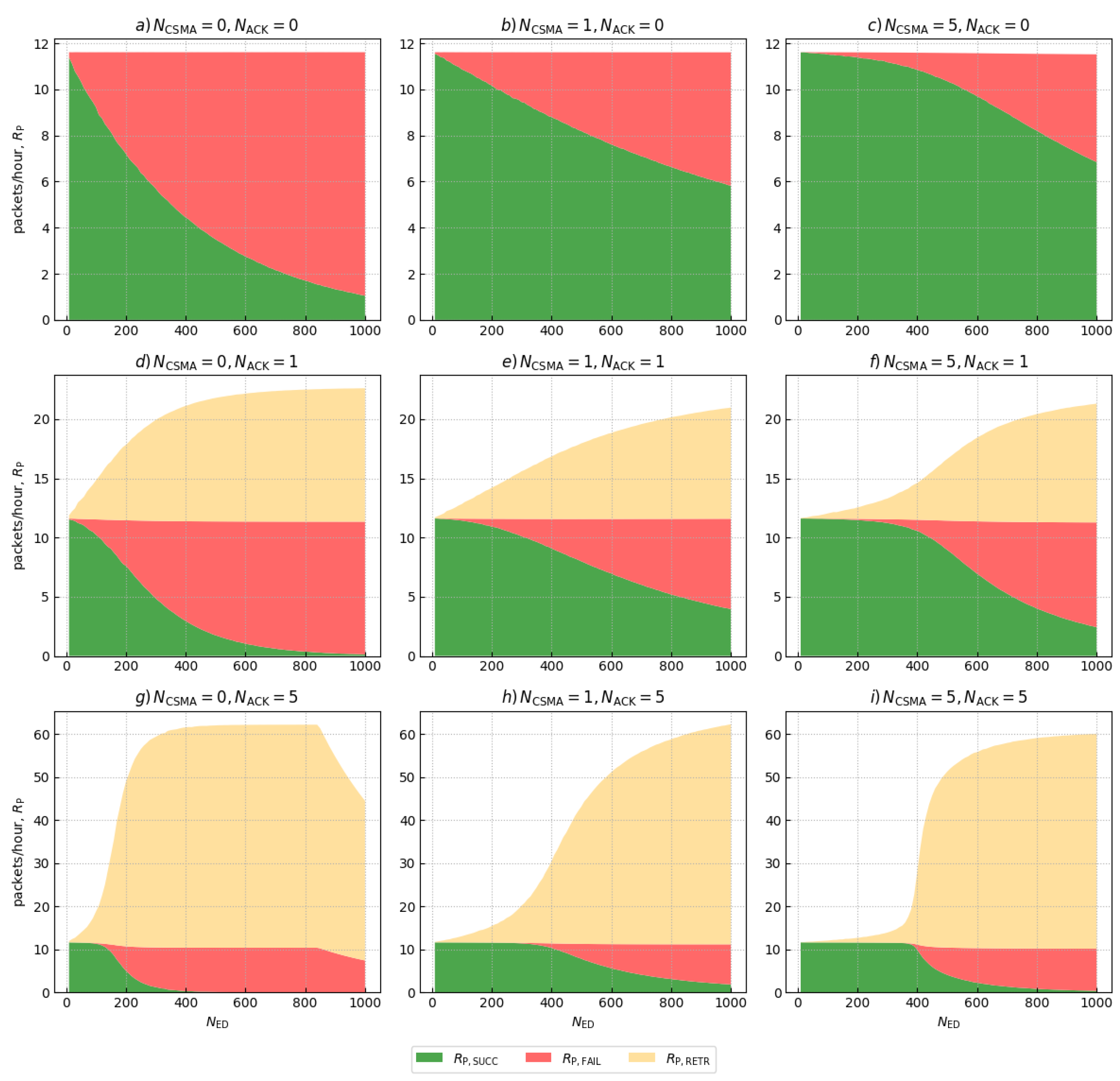
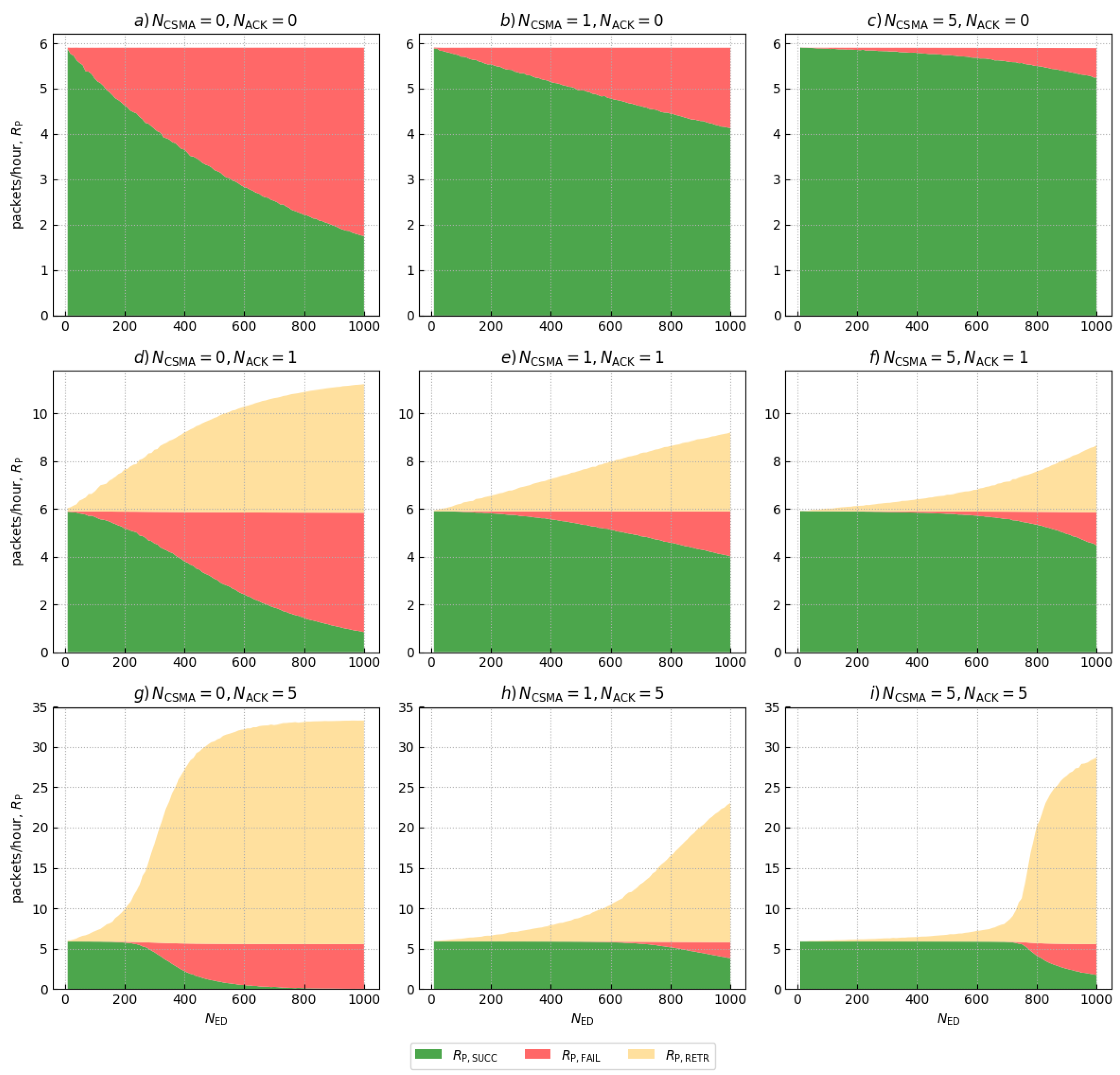
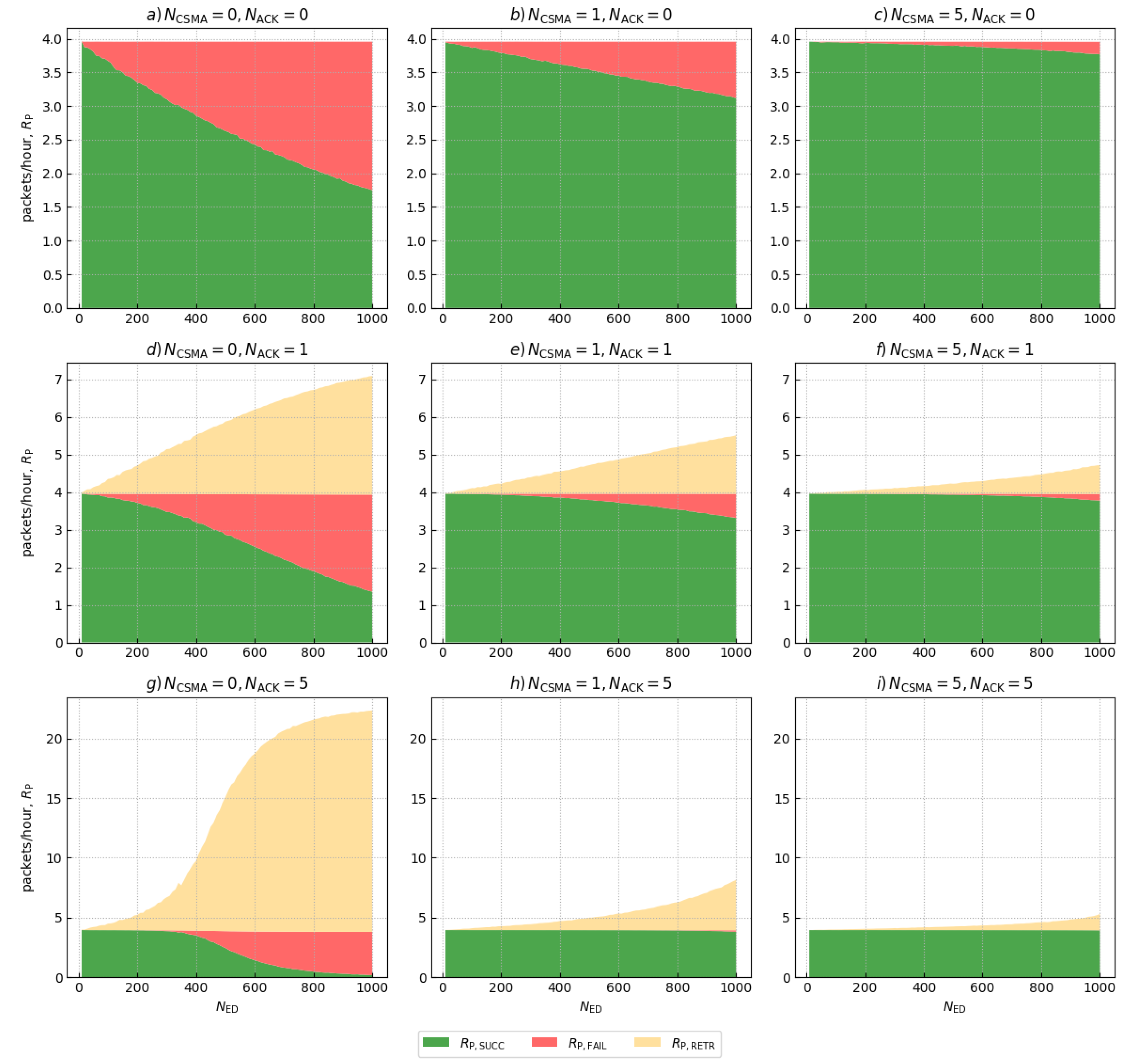
5.2. Traffic Composition
6. Experimental Results
6.1. Range Performance
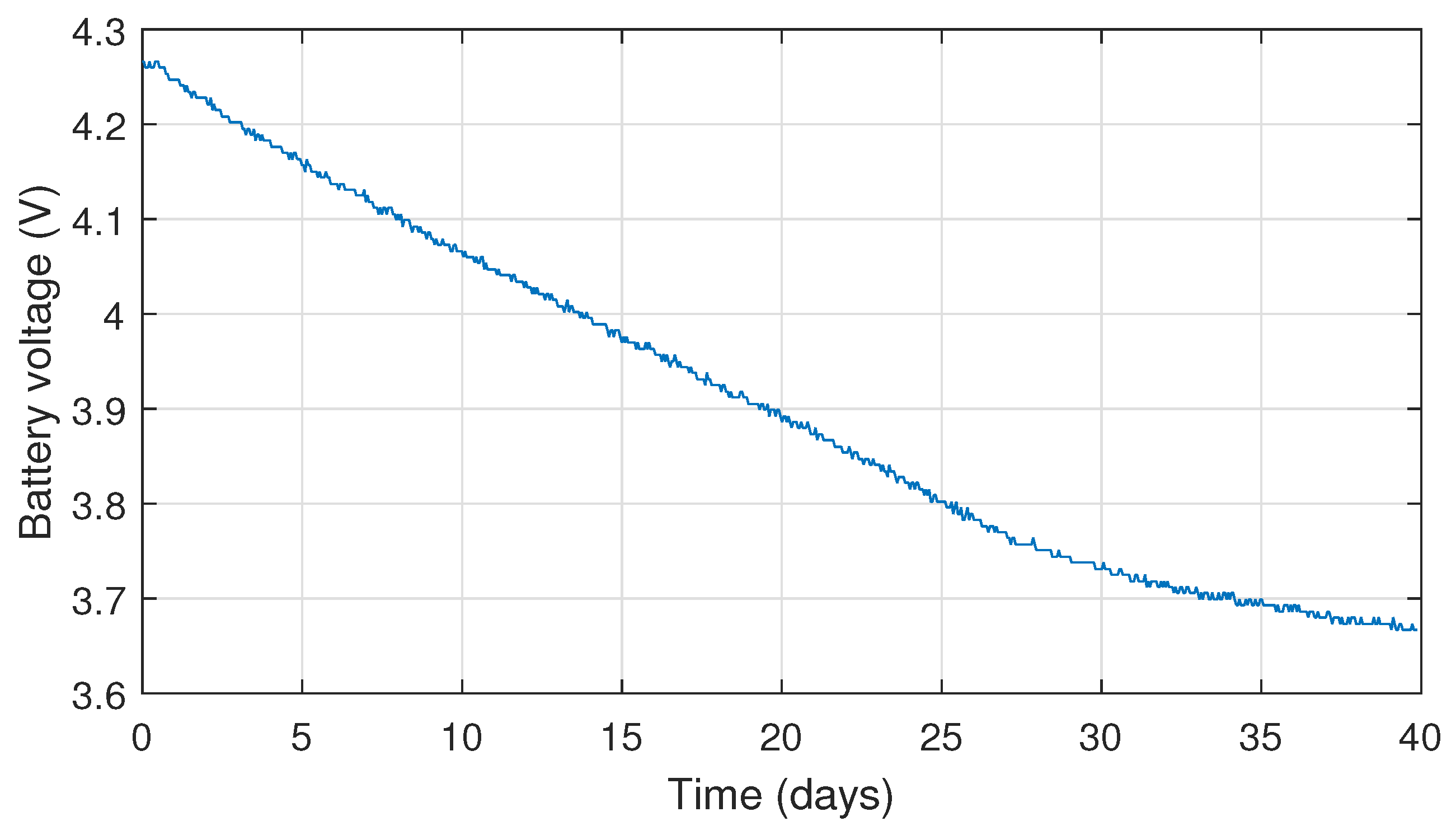
Battery Lifespan of LoRa EDs
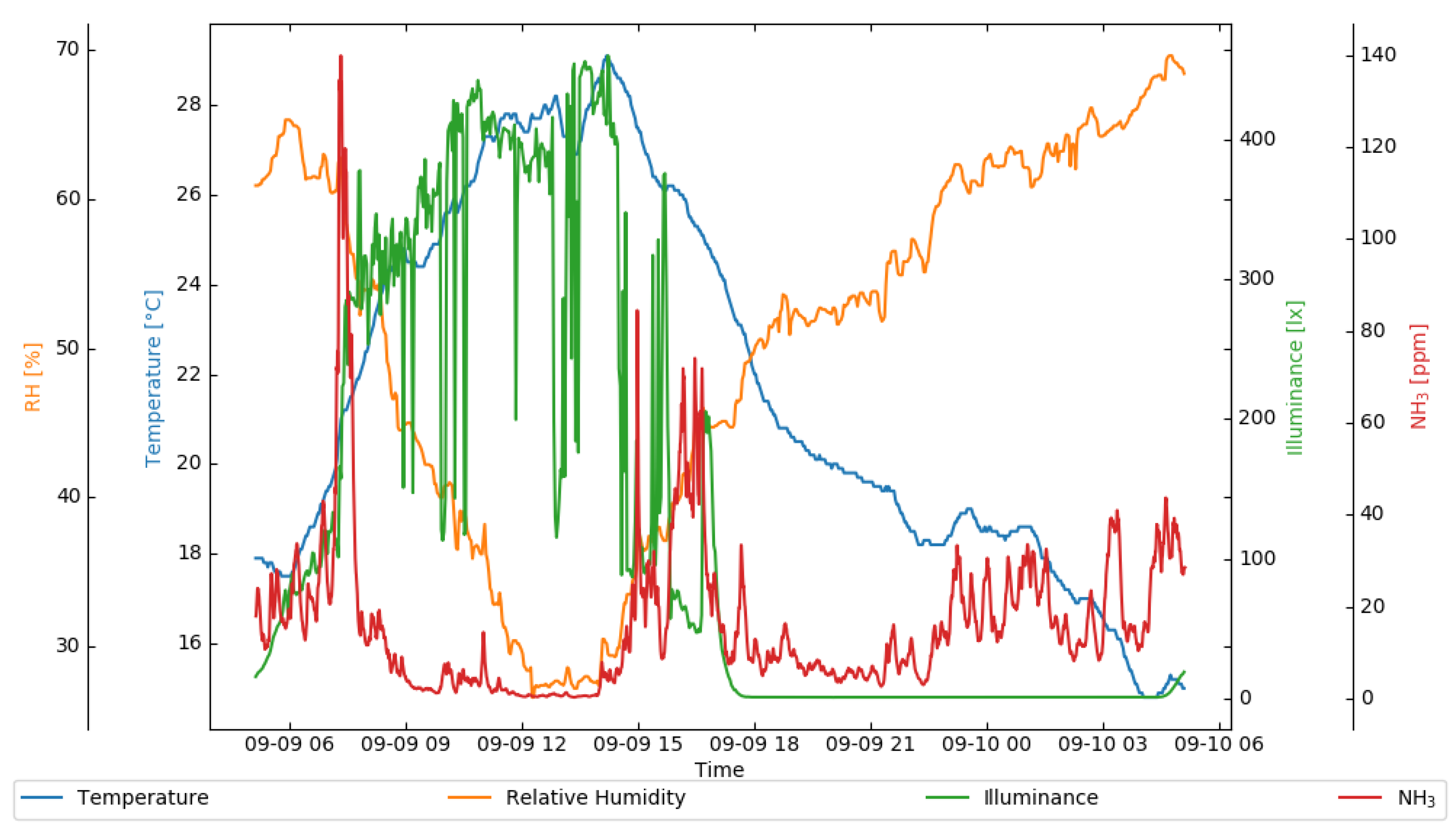
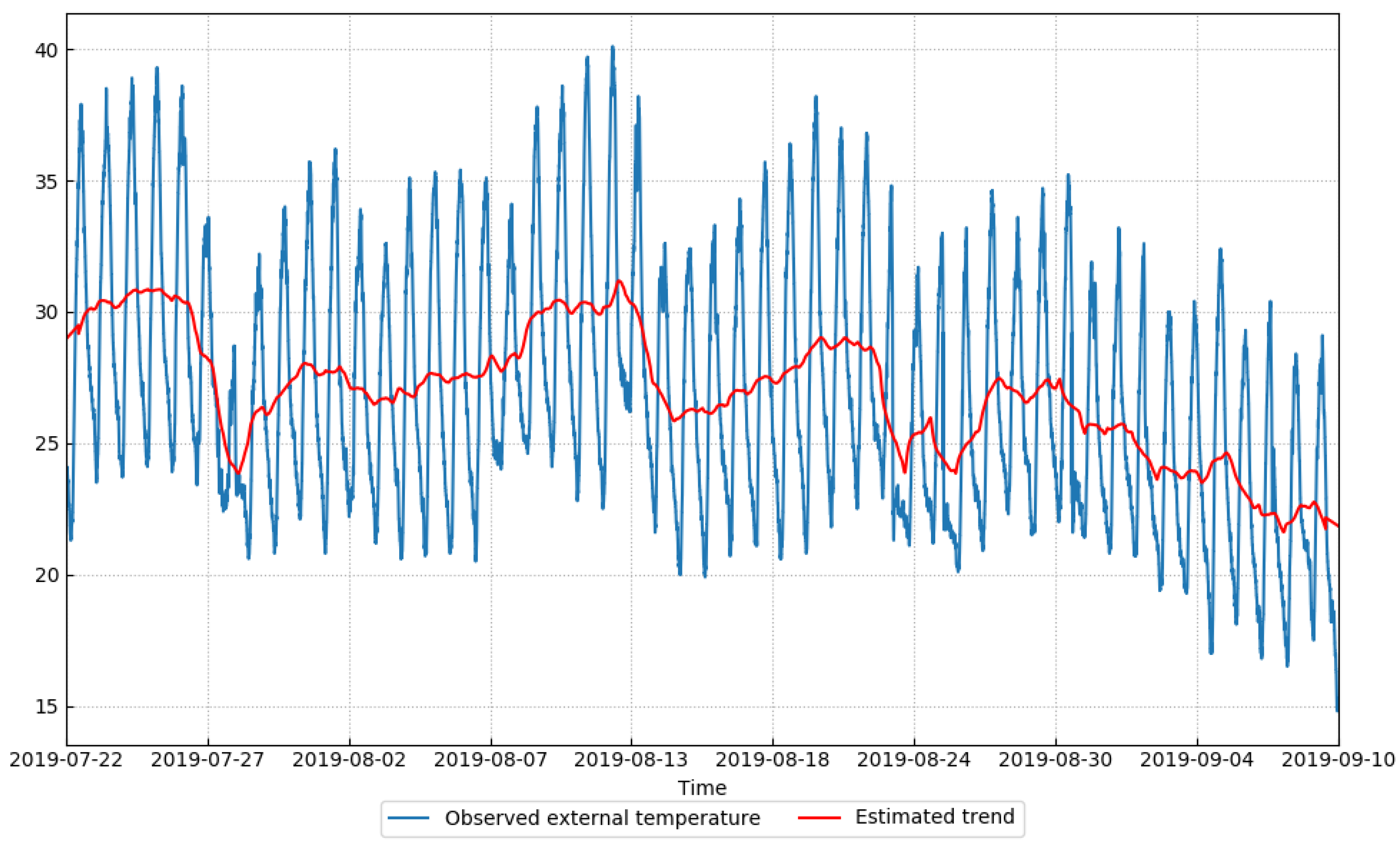
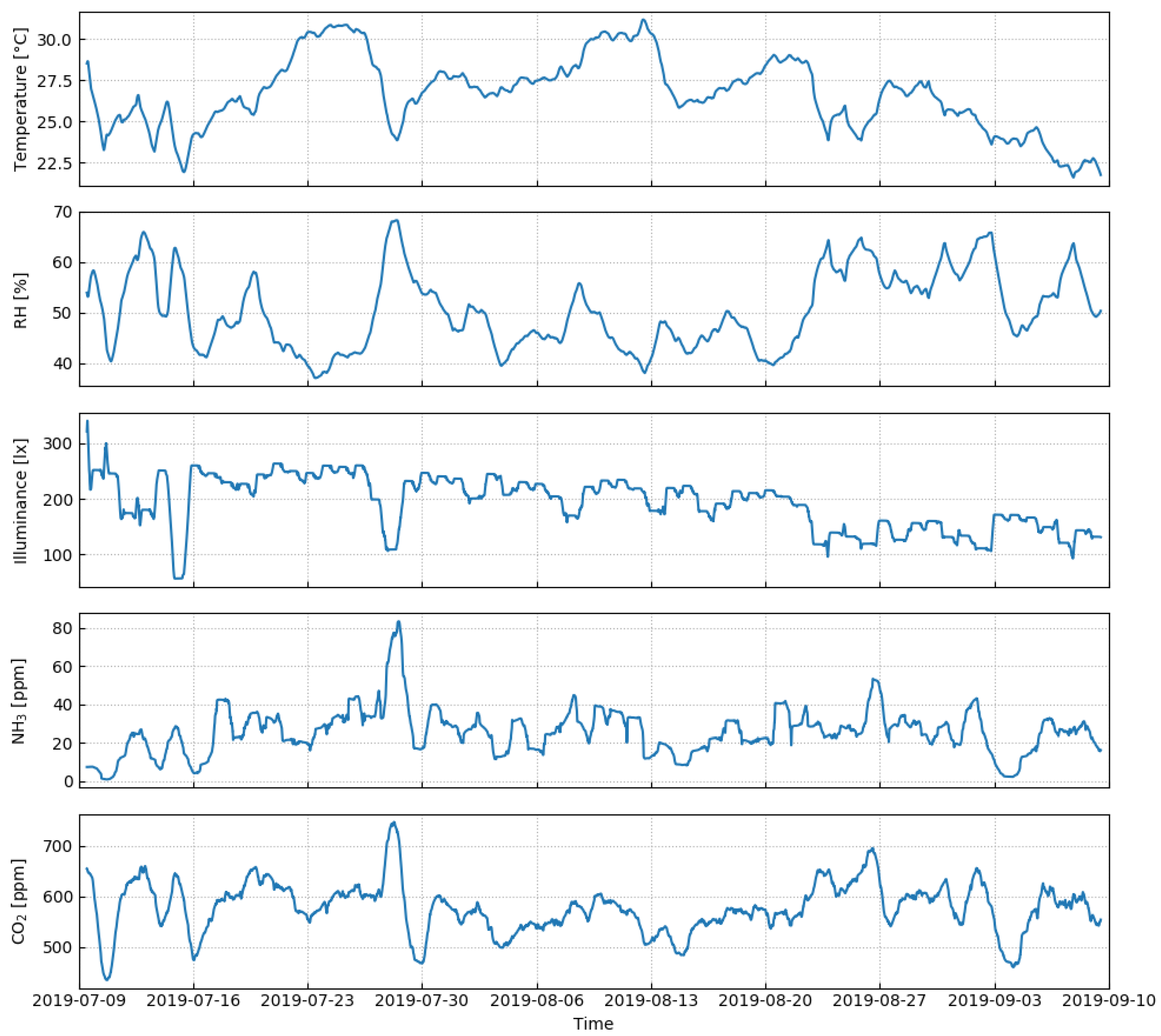
6.2. Exploratory Data Analysis of Sensor Measurements
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Choi, Y.J.; Kang, H.J.; Lee, I.G. Scalable and secure Internet of Things connectivity. Electronics 2019, 8, 752. [Google Scholar] [CrossRef]
- Pasolini, G.; Buratti, C.; Feltrin, L.; Zabini, F.; De Castro, C.; Verdone, R.; Andrisano, O. Smart City pilot projects using LoRa and IEEE802.15.4 technologies. Sensors 2018, 18, 1118. [Google Scholar] [CrossRef] [PubMed]
- Kabalci, Y.; Kabalci, E.; Padmanaban, S.; Holm-Nielsen, J.B.; Blaabjerg, F. Internet of Things applications as energy internet in Smart Grids and Smart Environments. Electronics 2019, 8, 972. [Google Scholar] [CrossRef]
- Sisinni, E.; Carvalho, D.F.; Ferrari, P.; Flammini, A.; Silva, D.R.C.; Da Silva, I.M.D. Enhanced flexible LoRaWAN node for industrial IoT. In Proceedings of the 2018 14th IEEE International Workshop on Factory Communication Systems (WFCS), Imperia, Italy, 13–15 June 2018; pp. 1–4. [Google Scholar] [CrossRef]
- Haxhibeqiri, J.; Karaagac, A.; Van den Abeele, F.; Joseph, W.; Moerman, I.; Hoebeke, J. LoRa indoor coverage and performance in an industrial environment: Case study. In Proceedings of the 2017 22nd IEEE International Conference on Emerging Technologies and Factory Automation (ETFA), Limassol, Cyprus, 12–15 September 2017; pp. 1–8. [Google Scholar] [CrossRef]
- Islam, S.M.R.; Kwak, D.; Kabir, M.H.; Hossain, M.; Kwak, K. The Internet of Things for health care: A comprehensive survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Pereira, C.; Mesquita, J.; Guimarães, D.; Santos, F.; Almeida, L.; Aguiar, A. Open IoT architecture for continuous patient monitoring in emergency wards. Electronics 2019, 8, 1074. [Google Scholar] [CrossRef]
- Kumar, N.M.; Dash, A. The Internet of Things: An opportunity for transportation and logistics. In Proceedings of the International Conference on Inventive Computing and Informatics (ICICI 2017), Coimbatore, India, 23–24 November 2017; pp. 194–197. [Google Scholar]
- Sanchez-Iborra, R.; Liaño, I.G.; Simoes, C.; Couñago, E.; Skarmeta, A.F. Tracking and monitoring system based on LoRa technology for lightweight boats. Electronics 2018, 8, 15. [Google Scholar] [CrossRef]
- Ojha, T.; Misra, S.; Raghuwanshi, N.S. Wireless sensor networks for agriculture: The state-of-the-art in practice and future challenges. Comput. Electron. Agric. 2015, 118, 66–84. [Google Scholar] [CrossRef]
- Jawad, H.M.; Nordin, R.; Gharghan, S.K.; Jawad, A.M.; Ismail, M. Energy-Efficient wireless sensor networks for precision agriculture: A review. Sensors 2017, 17, 1781. [Google Scholar] [CrossRef] [PubMed]
- Yim, D.; Chung, J.; Cho, Y.; Song, H.; Jin, D.; Kim, S.; Ko, S.; Smith, A.; Riegsecker, A. An experimental LoRa performance evaluation in tree farm. In Proceedings of the 2018 IEEE Sensors Applications Symposium (SAS), Seoul, Korea, 12–14 March 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Raza, U.; Kulkarni, P.; Sooriyabandara, M. Low power wide area networks: An overview. IEEE Commun. Surv. Tutor. 2017, 19, 855–873. [Google Scholar] [CrossRef]
- Barker, P.; Hammoudeh, M. A survey on low power network protocols for the Internet of Things and wireless sensor networks. In Proceedings of the International Conference on Future Networks and Distributed Systems, Cambridge, UK, 19–20 July 2017; p. 44. [Google Scholar] [CrossRef]
- Augustin, A.; Yi, J.; Clausen, T.; Townsley, W.M. A study of LoRa: Long range & low power networks for the Internet of Things. Sensors 2016, 16, 1466. [Google Scholar] [CrossRef]
- Semtech. SX1272/3/6/7/8: LoRa Modem Designer’s Guide; Semtech Corporation: Camarillo, CA, USA, 2013. [Google Scholar]
- Baruffa, G.; Rugini, L.; Mecarelli, V.; Germani, L.; Frescura, F. Coded LoRa performance in wireless channels. In Proceedings of the 2019 IEEE International Symposium on Personal, Indoor and Mobile Radio Communications (IEEE PIMRC 2019), Istanbul, Turkey, 8–11 September 2019; pp. 1–6. [Google Scholar]
- Sondrol, T.; Jalaian, B.; Suri, N. Investigating LoRa for the Internet of Battlefield Things: A cyber perspective. In Proceedings of the MILCOM 2018—2018 IEEE Military Communications Conference (MILCOM), Los Angeles, CA, USA, 29–31 October 2018; pp. 749–756. [Google Scholar] [CrossRef]
- de Carvalho Silva, J.; Rodrigues, J.J.P.C.; Alberti, A.M.; Solic, P.; Aquino, A.L.L. LoRaWAN—A low power WAN protocol for Internet of Things: A review and opportunities. In Proceedings of the 2017 2nd International Multidisciplinary Conference on Computer and Energy Science (SpliTech), Split, Croatia, 12–14 July 2017; pp. 1–6. [Google Scholar]
- Adelantado, F.; Vilajosana, X.; Tuset-Peiro, P.; Martinez, B.; Melia-Segui, J.; Watteyne, T. Understanding the limits of LoRaWAN. IEEE Commun. Mag. 2017, 55, 34–40. [Google Scholar] [CrossRef]
- Liu, X.; Huo, C. Research on remote measurement and control system of piggery environment based on LoRa. In Proceedings of the 2017 Chinese Automation Congress (CAC), Jinan, China, 20–22 October 2017; pp. 7016–7019. [Google Scholar] [CrossRef]
- Sharma, B.; Koundal, D. Cattle health monitoring system using wireless sensor network: A survey from innovation perspective. IET Wirel. Sens. Syst. 2018, 8, 143–151. [Google Scholar] [CrossRef]
- Cousin, P.; Dupont, C.; Fatnassi, S.; Pham, C.; Thiare, O.; Wussah, A.; Koffi, S. IoT, an affordable technology to empower Africans addressing needs in Africa. In Proceedings of the 2017 IST-Africa Week Conference (IST-Africa), Windhoek, Namibia, 30 May–2 June 2017; pp. 1–8. [Google Scholar]
- Davcev, D.; Mitreski, K.; Trajkovic, S.; Nikolovski, V.; Koteli, N. IoT agriculture system based on LoRaWAN. In Proceedings of the 2018 14th IEEE International Workshop on Factory Communication Systems (WFCS), Imperia, Italy, 13–15 June 2018; pp. 1–4. [Google Scholar] [CrossRef]
- Li, Q.; Liu, Z.; Xiao, J. A Data collection collar for vital signs of cows on the grassland based on LoRa. In Proceedings of the 2018 IEEE 15th International Conference on e-Business Engineering (ICEBE), Xi’an, China, 12–14 October 2018; pp. 213–217. [Google Scholar] [CrossRef]
- Petäjäjärvi, J.; Mikhaylov, K.; Hämäläinen, M.; Iinatti, J. Evaluation of LoRa LPWAN technology for remote health and wellbeing monitoring. In Proceedings of the 2016 10th International Symposium on Medical Information and Communication Technology (ISMICT), Worcester, MA, USA, 20–23 March 2016; pp. 1–5. [Google Scholar] [CrossRef]
- Sardar, M.S.; Yi, Y.; Xue-fen, W.; Huang, J.; Zhang, J.; Qin, X.; Zhao, Q.; Wang, Y.; Iqbal, M.A. Experimental analysis of LoRa CSS wireless transmission characteristics for forestry monitoring and sensing. In Proceedings of the 2018 International Symposium in Sensing and Instrumentation in IoT Era (ISSI), Shanghai, China, 6–7 September 2018; pp. 01249–01254. [Google Scholar] [CrossRef]
- Magrin, D.; Centenaro, M.; Vangelista, L. Performance evaluation of LoRa networks in a smart city scenario. In Proceedings of the 2017 IEEE International Conference on Communications (ICC), Paris, France, 21–25 May 2017; pp. 1–7. [Google Scholar] [CrossRef]
- Rizzi, M.; Ferrari, P.; Sisinni, E.; Gidlund, M. Using LoRa for industrial wireless networks. In Proceedings of the 2017 IEEE 13th International Workshop on Factory Communication Systems (WFCS), Trondheim, Norway, 31 May–2 June 2017; pp. 1–4. [Google Scholar] [CrossRef]
- Cattle Watch. Available online: http://www.cattle-watch.com/ (accessed on 18 November 2019).
- Sodaq. Available online: https://www.sodaq.com/ (accessed on 18 November 2019).
- SenseHub Beef. Available online: http://www.scr-dairy.com/cow-intelligence/sensehub-beef.html (accessed on 18 November 2019).
- Moocall. Available online: https://www.moocall.com (accessed on 18 November 2019).
- Van den Abeele, F.; Haxhibeqiri, J.; Moerman, I.; Hoebeke, J. Scalability analysis of large-scale LoRaWAN networks in ns-3. IEEE Internet Things J. 2017, 4, 2186–2198. [Google Scholar] [CrossRef]
- Bor, M.C.; Roedig, U.; Voigt, T.; Alonso, J.M. Do LoRa low-power wide-area networks scale? In Proceedings of the 19th ACM International Conference on Modeling, Analysis and Simulation of Wireless and Mobile Systems (MSWiM ’16), Floriana, Malta, 13–17 November 2016; pp. 59–67. [Google Scholar] [CrossRef]
- Dell. DELL PowerEdge R440 Round Rock, Texas, United States. Available online: https://www.dell.com/en-us/work/shop/povw/poweredge-r440 (accessed on 24 November 2019).
- Richardson, L.; Ruby, S. RESTful web services; O’Reilly Media, Inc.: Sebastopol, CA, USA, 2008. [Google Scholar]
- Xu, B.; Xu, L.D.; Cai, H.; Xie, C.; Hu, J.; Bu, F. Ubiquitous data accessing method in IoT-based information system for emergency medical services. IEEE Trans. Ind. Inform. 2014, 10, 1578–1586. [Google Scholar] [CrossRef]
- Baruffa, G.; Femminella, M.; Pergolesi, M.; Reali, G. A Big Data architecture for spectrum monitoring in cognitive radio applications. Ann. Telecommun. 2018, 73, 451–461. [Google Scholar] [CrossRef]
- Adafruit Learning System. Adafruit Feather M0 radio with LoRa radio module. 2019. Available online: https://learn.adafruit.com/adafruit-feather-m0-radio-with-lora-radio-module (accessed on 25 November 2019).
- Fiedler, A.; Müller, H.J. Emissions of ammonia and methane from a livestock building natural cross ventilation. Meteorol. Z. 2011, 20, 59–65. [Google Scholar] [CrossRef]
- Hristov, A.N.; Hanigan, M.; Cole, A.; Todd, R.; McAllister, T.A.; Ndegwa, P.M.; Rotz, A. Review: Ammonia emissions from dairy farms and beef feedlots. Can. J. Anim. Sci. 2011, 91, 1–35. [Google Scholar] [CrossRef]
- Mattachini, G.; Riva, E.; Provolo, G. The lying and standing activity indices of dairy cows in free-stall housing. Appl. Anim. Behav. Sci. 2011, 129, 18–27. [Google Scholar] [CrossRef]
- Aosong. Digital Temperature and Humidity Sensor AM2321 Product Manual; Aosong Guangzhou Electronics Co., Ltd.: Guangzhou, China, 2014. [Google Scholar]
- Adafruit Learning System. TSL2561 Luminosity Sensor. 2018. Available online: https://learn.adafruit.com/tsl2561 (accessed on 25 November 2019).
- DFRobot. Gravity: Analog infrared CO2 sensor for Arduino SKU: SEN0219. 2017. Available online: https://wiki.dfrobot.com/Gravity__Analog_Infrared_CO2_Sensor_For_Arduino_SKU__SEN0219 (accessed on 25 November 2019).
- Winsen. Ammonia Gas Sensor Model: MQ137; Zhengzhou Winsen Electronics Technology Co., Ltd.: Zhengzhou, China, 2015. [Google Scholar]
- Adafruit Learning System. Adafruit INA219 current sensor breakout. 2019. Available online: https://learn.adafruit.com/adafruit-ina219-current-sensor-breakout/ (accessed on 25 November 2019).
- u-blox. NEO-6 u-Blox 6 GPS Modules; u-blox AG: Thalwil, Switzerland, 2011. [Google Scholar]
- InvenSense Inc. MPU-6000 and MPU-6050 Product Specification Revision 3.4; InvenSense Inc.: Sunnyvale, CA, USA, 2013. [Google Scholar]
- Maxim. DS18B20-PAR 1-Wire Parasite-Power Digital Thermometer. Available online: https://www.maximintegrated.com/en/products/sensors/DS18B20-PAR.html (accessed on 25 November 2019).
- Sklar, B. Rayleigh fading channels in mobile digital communication systems. I. Characterization. IEEE Commun. Mag. 1997, 35, 90–100. [Google Scholar] [CrossRef]
- Ortín, J.; Cesana, M.; Redondi, A. How do ALOHA and Listen Before Talk coexist in LoRaWAN? In Proceedings of the 2018 IEEE 29th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), Bologna, Italy, 9–12 September 2018; pp. 1–7. [Google Scholar] [CrossRef]
- Iannello, F.; Simeone, O.; Spagnolini, U. Medium access control protocols for wireless sensor networks with energy harvesting. IEEE Trans. Commun. 2012, 60, 1381–1389. [Google Scholar] [CrossRef]
- Tukey, J.W. Exploratory data analysis; Addison-Wesley Series in Behavioral Science; Addison-Wesley: Reading, MA, USA, 1977. [Google Scholar]
- Seabold, S.; Perktold, J. statsmodels: Econometric and statistical modeling with python. In Proceedings of the 9th Python in Science Conference, Austin, TX, USA, 28 June–3 July 2010. [Google Scholar]
- Waskom, M.; Botvinnik, O.; O’Kane, D.; Hobson, P.; Ostblom, J.; Lukauskas, S.; Gemperline, D.C.; Augspurger, T.; Halchenko, Y.; Cole, J.B.; et al. mwaskom/seaborn: v0.9.0 (July 2018). 2018. Available online: http://seaborn.pydata.org/ (accessed on 25 November 2019). [CrossRef]
- Silverman, B.W. Density Estimation for Statistics and Data Analysis; Routledge: New York, NY, USA, 1998. [Google Scholar]
- Fan, J. Local Polynomial Modelling and Its Applications: Monographs on Statistics and Applied Probability 66; Routledge: New York, NY, USA, 1996. [Google Scholar]



| Device Class | Observed Parameters |
|---|---|
| Indoor GW | Temperature, relative humidity, illuminance, and concentrations |
| Outdoor GW | Temperature, relative humidity |
| ED | GNSS positioning, acceleration, rotation, body temperature |
| Parameter Description | Parameter Value |
|---|---|
| LoRa ED payload size | bytes |
| CW duration | ms |
| Spreading factor | |
| Coding rate | |
| LoRa ED transmission power | dBm |
| LoRa ED antenna gain | dB |
| Radio channel path loss exponent | |
| Radio channel reference path loss | dB |
| Radio channel shadowing std. deviation | dB |
| Additional losses | dB |
| Coverage area size (width and height) | m × 200 m |
| Number of LoRa GWs | |
| Number of database servers | |
| LoRa GW antenna gain | dB |
| Receiver sensitivity | as in (Table 10 of [16], pp. 20–21) |
| Duration of the network activity | 2 days |
| Parameter | Parameter Value |
|---|---|
| Bandwidth | kHz |
| Number of LoRa EDs | from 10 to 1000 |
| Transmission period | s |
| Number of ACK retransmissions | |
| Number of CSMA/CA retransmissions |
| Parameter Name | Parameter Value |
|---|---|
| Bandwidth | kHz |
| Frequency | MHz |
| Spreading factor | |
| Coding rate | |
| Transmission power | dBm |
| GW antenna height | m |
| Parameter Name | Parameter Value |
|---|---|
| LiPo battery voltage | 3.7 V |
| LiPo battery capacity | 2800 mAh |
| Transmission power | dBm |
| Transmission period | s (70 min) |
| Payload size | bytes |
| Board status sampling period | 3600 s |
| Body temperature sampling period | 900 s |
| Accelerometer sampling period | 5 s |
| Description | Current Level | Relative Duration |
|---|---|---|
| LoRa transmission | 23 mA | % |
| Board and sensors sampling | 15 mA | % |
| Sleep | mA | % |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Germani, L.; Mecarelli, V.; Baruffa, G.; Rugini, L.; Frescura, F. An IoT Architecture for Continuous Livestock Monitoring Using LoRa LPWAN. Electronics 2019, 8, 1435. https://doi.org/10.3390/electronics8121435
Germani L, Mecarelli V, Baruffa G, Rugini L, Frescura F. An IoT Architecture for Continuous Livestock Monitoring Using LoRa LPWAN. Electronics. 2019; 8(12):1435. https://doi.org/10.3390/electronics8121435
Chicago/Turabian StyleGermani, Lorenzo, Vanni Mecarelli, Giuseppe Baruffa, Luca Rugini, and Fabrizio Frescura. 2019. "An IoT Architecture for Continuous Livestock Monitoring Using LoRa LPWAN" Electronics 8, no. 12: 1435. https://doi.org/10.3390/electronics8121435
APA StyleGermani, L., Mecarelli, V., Baruffa, G., Rugini, L., & Frescura, F. (2019). An IoT Architecture for Continuous Livestock Monitoring Using LoRa LPWAN. Electronics, 8(12), 1435. https://doi.org/10.3390/electronics8121435





