1. Introduction
The proliferation of the internet has not only increased connectivity and access to information for people of all ages but also has revolutionized entertainment, offering a vast array of options, including streaming services, online gaming platforms, and social media. Social gaming is significantly popular too, with many games offering a social dimension, allowing players to connect with friends and make new ones in virtual environments [
1]. It has emerged as a particularly significant online phenomenon, enabling players to not only communicate and interact with one another but also participate in games. Social gaming has evolved beyond its mechanics, becoming increasingly popular and sophisticated over the past decade. What began as simply playing games with friends has transformed into a complex form of social life, blurring the lines between the virtual and physical worlds.
Online gaming environments now serve as social networks, allowing people with shared interests to interact and engage with each other. Roblox is one of the largest worldwide social gaming platforms [
2]. It provides an environment where users can create their own games (known as experiences) and play a variety of mini-games. Additionally, players can run Roblox on different devices such as mobile phones, computers, game consoles, and VR helmets. On average, Roblox users spend approximately 2.6 h on the platform each day, exploring around 20 games per month. As of September 2022, Roblox boasted 70.2 million daily active users, with 60% of its users being under 16 [
3].
The number of children using the internet is on the rise [
4]. Studies suggest that five-year-old children spend approximately three hours online each day, with one hour of that time typically spent playing video games [
5]. The primary users of Roblox are children. As of September 2020, Roblox had 36 million daily active users, more than half of whom were under 13 years old. By 2023, this number had grown to 78 million daily users [
6]. According to Perez [
7], Roblox is not just a place for playing games but a virtual space where children can hang out online. Roblox is designed to be an interactive and social environment, allowing players to explore user-generated worlds and interact with others, acting as a recreational space for children.
However, this popularity also makes it a prime target for child predators and cybercriminals seeking to exploit its user base. In 2023, Roblox reported 13,316 instances of child exploitation to the National Center for Missing & Exploited Children, marking a significant increase from 2973 cases in the prior year [
8]. As a result, there is a risk that children may encounter inappropriate and violent content within the platform’s virtual world [
9]. Some of the crimes conducted on the platform include sexual abuse, child abductions, luring children to share explicit pictures for Robux, using Roblox as an initial platform and moving conversations to other platforms, recruitment of children by extremists, and identity theft [
8,
10,
11,
12]. Most of these in-application crimes target unsuspecting users, many of whom are minors [
13,
14]. Today and in the future, identifying and safeguarding vulnerable individuals, particularly children, is a challenging task. As such, forensic investigation of Roblox becomes critical, enabling authorities to uncover and apprehend cyber criminals. By analyzing the digital artifacts left by users on Roblox, it becomes possible to track and address nefarious activities, safeguarding the well-being of its youthful audience.
Despite Roblox’s involvement in various criminal activities and its rapidly growing youth user base, to the best of our knowledge, no research has been conducted on digital forensics investigations of the platform. Consequently, this paper presents a comprehensive forensic examination of Roblox on the Windows operating system, focusing on disk, memory, and network analysis. The range of digital evidence potentially extractable from Roblox includes, but is not limited to, group chats, user information, geolocation, gameplay data, etc. These findings provide a valuable reference for researchers exploring social gaming forensics and for digital forensic analysts aiming to understand the extent of evidence that can be gathered from Roblox. In an era of constantly evolving online threats, the insights gained from Roblox forensics can be instrumental in the pursuit and prosecution of cybercriminals. During our study, we explored the following research questions:
Is it possible to retrieve artifacts from the Roblox application through the digital forensic analysis of the storage, memory, and network?
Do artifacts retrieved during the investigation hold substantial importance for digital forensic analysis?
What personally identifiable information can be retrieved?
What are the similarities and differences between the retrieved artifacts in the three-analysis focus covered in the research?
How can evidence obtained from storage, memory, and network analyses be effectively integrated and cross-referenced?
The rest of the paper is organized as follows.
Section 2 provides some preliminary information on the Roblox application and its architecture.
Section 3 provides information on the related work on the methodology for identifying and retrieving artifacts from social gaming applications. In
Section 4 and
Section 5, we detail the experimental setup and methodology followed in this study. In
Section 6 and
Section 7, we present the results of the examination for all three analysis focuses (storage, RAM, and network) and discuss our results. Lastly, we conclude our work and mention possible directions for future study in
Section 8.
2. Preliminaries
Due to the limited research available on the digital forensic analysis of Roblox, we give a brief overview of the workings and architecture of Roblox in this section.
Roblox is a social gaming platform that allows users to create and play games, socialize, chat, and interact with other users. To begin using Roblox, users must create a free account and provide information such as birthdate, gender, phone number, and email. After setting up the account, users can optionally put links to their other social media accounts, like YouTube, Twitch, and Discord. After setting up the account, users can create their avatars by selecting hairstyles, clothing, and accessories. While many customization options are free, some premium cosmetic enhancements require Robux (Roblox’s in-app currency), which can be purchased. Once users have fully configured their profiles, they can explore and participate in a wide variety of games, known as ’experiences’.
In terms of gaming, users can create their own games or play games created by others. The games available span various genres, catering to the diverse interests of users. As users interact with various games, they can socialize in the process. Roblox’s multiplayer functionality enhances the experience by enabling players to collaborate or compete in games. This interaction is accomplished through the chatting feature (in-game chats or text chats) while playing games.
Roblox offers extensive social media functionalities, including friend requests, direct messaging, group chats, and the creation and joining of public groups. Users can join and create groups of their own and configure information such as the group name, description, and roles. Communication in the groups takes the form of either a “shout” or a “wall post”. Shouts are broadcast messages that can be used to post important updates to the group, while wall posts are used for regular communication in the group.
Architecture of the Application
Roblox is a client–server based social gaming platform composed of multiple interacting components, including the Roblox Player, web-based services, and embedded web rendering technologies. Roblox Player is a native Windows application that integrates browser rendering technologies to display web-based content within its interface.
On Windows systems, Roblox installs two primary components: Roblox Studio (used for game creation) and Roblox Player (used for gameplay). This research focuses on Roblox Player. The executable process RobloxPlayerBeta.exe is responsible for launching and managing gameplay sessions. Roblox Player utilizes Microsoft Edge WebView2 components, including processes such as msedgewebview2.exe and msedge.exe. WebView2 embeds Chromium-based browser functionality inside the native application, enabling Roblox to render HTML, CSS, and JavaScript-based user interfaces. This architecture allows the platform to display account management interfaces, chat modules, in-app purchase pages, and other web-driven features within the desktop application environment.
Disk analysis further confirmed the presence of Chromium-style storage mechanisms, including:
LevelDB-based Local Storage and Session Storage
Chromium Disk Cache structure (index file and data block files)
Web-based JSON artifacts stored within cache directories
Roblox Player incorporates web-rendered components through the Chromium Embedded Framework (CEF) or WebView2.
Roblox is a hybrid native–web application built on a client–server model. The Windows client consists of a native gameplay engine combined with embedded Chromium-based web rendering components. Platform services operate through cloud-hosted HTTPS APIs, while gameplay sessions are hosted on distributed Roblox servers. This architecture results in artifacts spanning disk storage, memory, registry, and encrypted network traffic, all of which are examined in subsequent sections of this study.
5. Methodology
The research employs an experimental methodology to simulate a series of user activities over a span of two hours aimed at generating artifacts. The conducted activities align with typical user behavior and encompass the most prevalent actions on the Roblox application.
Table 4 highlights the user activities simulated for the research.
5.1. Use Case Scenarios
The current research focuses on identifying user-generated data and artifacts from Roblox software (
https://roblox.qq.com/ (accessed on 26 January 2026)). We attempt to define a model that helps analyze a social media gaming platform across various focus areas. The following are the main use cases identified for such a forensics analysis:
- 1.
Analyze local files created by Roblox (Storage forensics): Local files often contain critical evidence of a cyber incident or a crime. A lot of user behavior is persistent in the local files. We examined the various storage mechanisms that Roblox uses to store application data on disk. Analyzing these local application files can help identify artifacts and personally identifiable information that may be relevant to an investigation.
- 2.
Analyze registry changes (Storage forensics): The analysis of registry changes associated with Roblox will be analyzed to provide valuable insights into the platform’s footprint on Windows operating systems. The examination will focus on discerning the specific registry entries modified or created by Roblox. This is instrumental in understanding Roblox’s functionalities and interactions with the underlying operating system.
- 3.
Analyze application processes created (Memory forensics): We analyze the contents of a system’s volatile memory to identify and reconstruct the application processes that were running. This approach allows us to gain insights into the processes initiated by Roblox and the underlying mechanisms it uses to create these processes.
- 4.
Analyze memory dumps (Memory forensics): We capture a memory dump after conducting common user activities on Roblox. These dumps are then analyzed using memory forensics tools such as Volatility, as well as manual analysis using a hex editor to extract critical information, including running processes, open network connections, and user information.
- 5.
Analyze DNS requests from Roblox (Network forensics): For analyzing DNS requests, the methodology focuses on capturing the DNS traffic generated by the software. Network monitoring tools are employed to intercept and log DNS requests made by the application. DNS query patterns, domain resolutions, and response times are then analyzed.
- 6.
Analyze TLS-Based HTTP requests from Roblox (Network forensics): The analysis of TLS-based HTTP requests involves intercepting and capturing encrypted network traffic generated by Roblox. This is achieved by deploying a proxy or utilizing network packet capture tools. The captured traffic is decrypted, and the HTTP requests are extracted for analysis. The methodology focuses on inspecting the content, headers, and metadata of these requests.
- 7.
Analyze non-HTTP requests from Roblox (Network forensics): In situations where the software generates non-HTTP network requests, a similar approach as described for TLS-based HTTP requests can be adopted. The methodology involves capturing and decrypting the network traffic, identifying non-HTTP protocols, and analyzing the payloads. The goal is to understand the nature of these requests, identify their purposes, and assess whether they adhere to the expected behavior of the software.
5.2. Disk Storage Forensics
Storage forensics focuses on the investigation and analysis of storage devices to uncover evidence of digital crimes. The primary goal is to retrieve, examine, and interpret data stored on various types of storage media to support legal investigations. In our research, we investigate the existence of terrestrial artifacts produced by the Roblox application.
To achieve this objective, our experimental approach involves executing the Roblox application in a closely controlled environment, wherein we replicate common user activities. These activities are selected to mimic real-world interactions and behaviors that typically generate application-specific files or data within the disk. This comprised two main stages: application folder analysis and Windows registry analysis.
For the storage analysis, we acquired a bit-for-bit forensic image of the Windows system drive and computed cryptographic hash values (SHA-256) at the time of acquisition. The hash values were verified before examination, and all storage-related analyses in this study were performed on the digital forensic image rather than on the live system. In the pursuit of analyzing the disk, we examined the Roblox installation directory, where we identified numerous files and folders containing a lot of application data. To manually analyze the application data, we used tools such as ChromeCacheView (to analyze and export the cache files) and hex editor (HxD). Roblox is built on the Chromium Embedded Framework (CEF) for its desktop client, as seen by the folder structure of Roblox files during the disk analysis, as shown in
Figure 2. CEF allows Roblox to leverage the capabilities of the Chromium browser within its applications. It also allows Roblox to embed web browser components into the application using WebView. WebView is a component of CEF that allows developers to embed web content (such as HTML pages, CSS styles, and JavaScript code) into their applications. Roblox uses this to display web-based content within the application’s user interface.
Regshot was used to compare snapshots of the Windows registry, allowing us to track changes made to the registry after installing and using the Roblox application. We utilized Regshot to compare created or modified registry entries. We started it off by taking an initial snapshot of the registry’s state before downloading the Roblox app. We then installed and used Roblox and captured a second snapshot to record the updated registry state.
5.3. Memory Forensics
Memory forensics is a specialized area within digital forensics focused on investigating and retrieving digital evidence stored in a computer’s volatile memory, known as RAM. This type of data encompasses a wide array of information, including program data, user-generated content, network-related details, and more [
29]. Due to the wealth of user and system data stored in RAM, memory forensics is integral in uncovering crucial insights. It sheds light on an application’s behavior by revealing the processes it initiates and the data it generates and retains in memory. The forensic examination of memory typically involves two key phases: memory acquisition and subsequent memory analysis.
5.3.1. Memory Acquisition
To acquire a snapshot of the volatile memory of the Windows machine using the tool DumpIt by Magnet Forensics [
30]. One of the advantages of DumpIt is that it is non-intrusive, meaning it acquires memory without altering the state of the system. This is crucial in maintaining the integrity of the data being collected. Additionally, immediately after acquisition, cryptographic hash values (SHA-256) of the memory image were computed and recorded, and these values were verified before any examination.
5.3.2. Memory Analysis
Volatility3 v2.27.0 [
31] is an open-source utility framework for extracting volatile memory artifacts, implemented in Python. When provided with a memory image, Volatility can analyze the volatile memory to extract information on running processes, memory maps (detailed representation of the layout and usage of memory within a system), network connections, file handles, etc. For our experiment, we used Volatility to analyze the memory for residual artifacts from Roblox.
To gain a comprehensive understanding of Roblox’s functionality and the artifacts that can be retrieved, we conducted a memory analysis. Initially, we employed Volatility to examine the RAM, utilizing the ’windows.pstree.Pstree’ plugin to identify all processes running at the time the memory image was captured. The plugin presents processes in a hierarchical tree structure, revealing their parent–child relationships.
We also used the windows.strings.Strings plugin in Volatility. It scans the memory image to extract strings of text stored in various locations within the process address space. The output of this plugin is useful as these strings can include user input, file paths, API function names, and other textual evidence. By examining these strings found in memory, we can retrieve key insights into the activities ongoing at the time the memory dump was taken.
Additionally, we also used a hex editor to analyze the RAM images. Memory images contain a wealth of information, and a hex editor provides a granular view of this data. In our research, we used the HxD hex editor to analyze the memory dump at the binary level, searching for specific strings of information that allowed us to have a targeted approach to uncover evidence. The specific strings that we searched for during the experiment include Roblox, kimkarter (the name of the account user), username, email, and password. The results from these initial searches guided us to additional artifacts. For instance, searching for a user led us to their corresponding user ID. Subsequently, searching for the user ID revealed most of the related artifacts associated with that user.
5.4. Network Forensics
Network forensics is a field within digital forensics, with a primary focus on gathering, analyzing, and interpreting network activities. This entails a systematic investigation of network logs and packet captures aimed at reconstructing events and retrieving artifacts from network traffic [
32,
33].
During the network analysis, Roblox is executed in a controlled environment while its network interactions are closely monitored. DNS requests, HTTP requests, non-HTTP requests (if applicable), and other network traffic are captured and analyzed. We then aggregate and categorize the captured data to establish a network profile. This profile serves as a blueprint for the software’s typical network behavior. The Roblox gaming environment has been abused multiple times by tampering with the requests during gameplay. The software, for this reason, uses anti-tampering techniques that would prevent easy sniffing on the network or processing the network traffic. All network captures used in this study were obtained in this isolated setup, where the Windows node communicated exclusively through the configured Ubuntu gateway and proxies, ensuring that the recorded DNS, HTTP(S), and non-HTTP traffic can be directly attributed to the Roblox client and the scripted activities in
Table 4. This constrained environment reduces background noise and supports a clear mapping between user actions and captured network traces, which is essential when such traces are later considered as digital evidence.
To analyze the network connections originating from the Roblox application, we created an isolated and controlled network environment, as shown in
Figure 1. This is because isolating the network ensures that the evidence related to the forensic analysis remains intact and uncontaminated. Additionally, an isolated environment allows for controlled testing and experimentation. This is crucial for accurately understanding the behavior of Roblox under different user activities.
Due to the anti-tampering mechanisms implemented by Roblox, it was impossible to directly execute Roblox in a virtual environment. Roblox software executed in a virtual machine, or using emulators such as Wine, would just crash immediately upon opening. So, we had to resort to using physical machines for our test setup. In configuring our network setup, we employed a tandem of physical machines (nodes). The first node, operating on a Windows platform, housed the Roblox application, while the second node, a virtual machine running Ubuntu, serves as the dedicated platform for analyzing Roblox traffic. To ensure a controlled and confined networking environment, we created a private network (eth1). Both nodes exist within the confines of the same private network, establishing an environment where communication is restricted to the Windows node interacting exclusively with the Ubuntu node.
In this experimental setup, HTTPS traffic decryption relies on active TLS interception: the Windows machine is configured to trust a root certificate generated by the Fiddler proxy, and all Roblox HTTPS requests are routed through this proxy, which enables inspection of the decrypted HTTP payloads. This configuration assumes that the investigator has administrative control over the client environment and can lawfully install a trusted root certificate and proxy the traffic (for example, in a controlled lab reproduction, an enterprise endpoint monitoring setting, or under an appropriate court order). In many operational investigations, particularly when only passive network capture is feasible and the client cannot be modified, investigators would not be able to decrypt Roblox traffic in this manner and would instead be limited to metadata such as IP addresses, domains, timing information, and TLS handshake parameters, complemented by artifacts from storage and memory or provider-side logs. The decrypted network results presented in this paper should therefore be interpreted as characterizing the structure and content of Roblox’s client–server API interactions under an active interception scenario, rather than as evidence that plaintext application data will always be directly observable in real-world investigations.
As described above, our network analysis relies on active TLS interception. Roblox HTTPS traffic is proxied and decrypted using a trusted root certificate installed on the Windows client. This approach assumes that the investigator has administrative control over the endpoint and the legal authority to modify its trust store and route traffic through an interception proxy. In many operational investigations where only passive capture is feasible and the client cannot be modified, Roblox’s TLS-encrypted traffic would not be directly decryptable, and investigators would be limited to metadata (such as IP addresses, domains, and timing information), complemented by storage and memory artifacts or provider-side logs. Accordingly, the decrypted network results presented in this paper should be interpreted as characterizing Roblox’s client–server API interactions under an active interception scenario, rather than as evidence that plaintext application data will always be observable in real-world cases.
6. Results and Discussion
In the following sections, we outline and explore various Roblox artifacts retrieved from the storage, memory (RAM), and network analysis.
6.1. Storage Forensics
All the artifacts retrieved during disk analysis were extracted from three key storage mechanisms: local storage, session storage, and cache. Local storage and session storage utilize LevelDB data stores, an on-disk key-value storage system. Each LevelDB database occupies a folder in the file system, containing files named “CURRENT”, “LOCK”, “LOG”, “LOG.old”, “MANIFEST-xxxxxx”, “xxxxxx.log”, and “xxxxxx.ldb”, where xxxxxx represents a hexadecimal sequence number indicating the order of file creation (where higher numbers are more recent). The “.log” and “.ldb” files store the actual record data, while the other files contain metadata to facilitate efficient data reading. Initially, data written to a LevelDB database is added to a “.log” file. When a log file reaches a certain size (4 MB by default), its data is converted into a permanent table file (a “.ldb” file), and a new log file is created.
Most of the artifacts during disk storage analysis were retrieved from the cache. Roblox utilizes an implementation of Chromium’s Disk Cache, storing all cache files in a single folder named “Cache”. Chromium’s Disk Cache uses at least five files: one index file (“index”) and four data files (“data_0”, “data_1”, “data_2”, and “data_3”). The index file contains the main hash table used to locate entries in the cache, while the data files, also known as block files, store the actual data. These block files are optimized to store information in fixed-size “blocks”. If the size of a data piece exceeds the maximum block size (16 KB), it is stored in a separate file instead of a standard block file. These separate files, which contain only the data to be saved without special headers, are named in the format “f_xx”, where “xx” is a hexadecimal identifier.
The results of this research are based on user activities performed within the Roblox application, leading to the creation of numerous artifacts across various storage mechanisms. The artifacts highlighted in this section were evaluated for their forensic value. Significant artifacts are listed here, along with the corresponding user activity and the storage mechanism from which they were retrieved, as shown in
Table 3.
6.1.1. Initial Setup
When users create an account in Roblox, they provide a significant amount of personal information, including their birthdate, phone number, gender, and age, all of which can be retrieved. Additional contextual artifacts from the account creation process include geolocation data (indicating where the account is being used) and age verification information. This information is crucial for establishing the user’s identity and tracing their activities. All artifacts retrieved from the initial setup process were found in the cache within JSON files such as “birthdate.json”, “gender.json”, “phone.json”, “verified-age.json”, and “account-country.json”. These files provide key details such as the user’s birthdate, gender, phone number, age verification status, and account country, respectively.
6.1.2. User Profile Configuration
A user profile is a digital representation of the user, composed of various data points. Most artifacts in this category were retrieved from cache files. However, artifacts such as ‘Username’ and ‘User ID’ could also be retrieved from local and storage. Within the cache, there is a JSON file named after each Roblox user’s unique ten-digit user ID. This file includes key information such as a description (a short text section providing information about the user), account creation timestamp, username, and display name, as illustrated in
Figure 3.
In Roblox, users can further customize their accounts by adding social media links and adjusting various account settings, such as privacy and user interaction settings (whoCanMessageMe, whoCanChatWithMe). Artifacts related to these configurations can be found in the cache, specifically in the “promotion-channels.json” and “user-settings.json” files, respectively.
Retrieving these artifacts during a digital forensics investigation can provide significant insights. The ‘description’ section often contains personal information and interests, which can help profile the user. Social media links can connect the Roblox account to the user’s broader online presence, aiding in identifying their real-world identity and social networks. This is crucial for tracing communications or activities across multiple platforms. Additionally, examining account settings can reveal how the user interacts with the platform, including their privacy preferences and security measures, offering clues about potential attempts to hide or secure their activities.
6.1.3. Avatar Creation
An avatar in Roblox is a customizable digital representation of a user within the platform. Each user can personalize their avatar with various features and accessories to reflect their identity or preferences. In this research, artifacts related to the user avatar were also retrieved. These artifacts can serve as a form of identity verification, as users often configure their avatars based on their physical features. Avatar artifacts were retrieved from the cache in the JSON file “currently-wearing.json”, which contains the ‘asset IDs’ of the clothes and accessories the avatar is currently wearing. Additionally, the cache also includes pictures of the avatar.
6.1.4. Creating Friends
Artifacts related to friends in Roblox encompass various data points that offer valuable insights into a user’s social relationships within the platform’s community. These artifacts are crucial for understanding user engagement, social dynamics, and community interactions within Roblox. Friends lists provide a record of users with whom a player has established a social connection. Artifacts related to friends can be retrieved from local storage, session storage, and cache. While we could only retrieve the user ID and username from local and session storage, we were able to retrieve many more artifacts from the cache file “friends.json”. It contains crucial artifacts related to a user’s friends on Roblox.
Some of the key artifacts in each friend entry include details such as their online status (‘isOnline’), indicating whether they are currently active. Additionally, unique identifiers such as ‘id’, along with the friend’s username (‘name’) and display name (‘displayName’), are essential for identification. These artifacts collectively help build a comprehensive profile of the user’s social interactions on Roblox, identifying significant connections. In contrast, during the investigation, we also retrieved information on blocked users from the cache file “get-detailed-blocked-users.json”. This file details the ‘user ID’, ‘name’, and ‘displayName’ of the blocked user.
Additional information on friends can be found in individual user JSON files within the cache, as detailed in
Section 6.1.2. Moreover, crucial artifacts related to friends, including User ID and name, can also be retrieved from both local and session storage.
6.1.5. Creating Groups
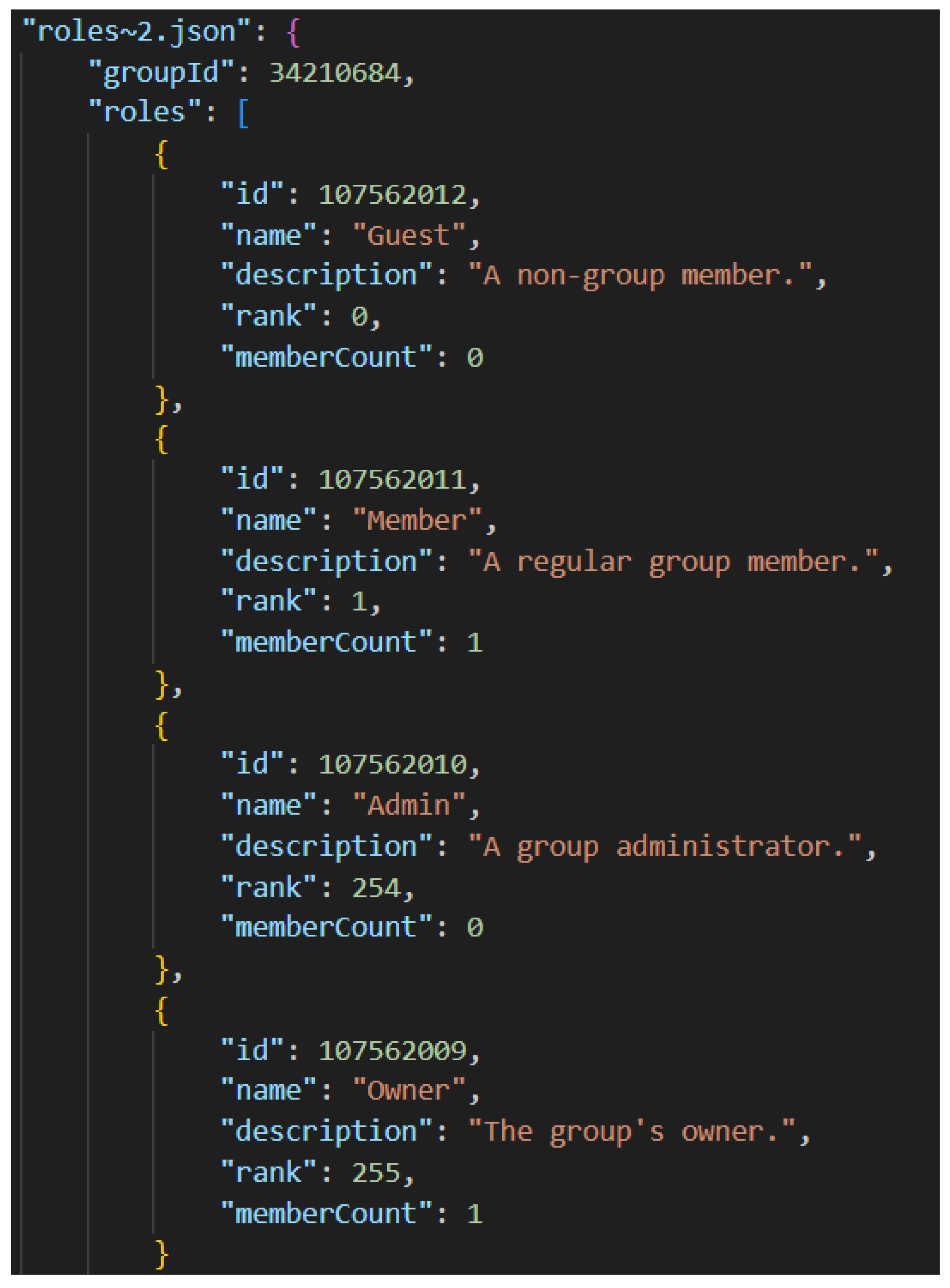
Groups on Roblox are communities that users can join based on shared interests. Group information can reveal which groups a user has joined. During the creation of the group, additional information, such as roles (group owners, administrators, or members), can indicate the level of influence a user has within a group, as well as potentially their involvement in any suspicious activities.
Throughout the research, we retrieved several artifacts related to the user activity of creating groups. As part of the experiment, we created a test group named ‘Roblox digital forensics’. When analyzing the creation of the Roblox group, several key artifacts can be retrieved from JSON files stored in the cache. These artifacts provide a detailed view of the group’s structure, roles, and member interactions, which are crucial for digital forensic investigations.
The cache consists of several JSON files named after the eight-digit group ID itself, such as “34210684.json” as shown in
Figure 4. It contains comprehensive information about the group, such as the group’s name, description (“This is a group for experiments”), and ownership details, highlighting the owner’s user ID, username, and display name. The file also records shout messages (messages broadcast to all members of a group), providing timestamps (Unix Epoch Time) for creation and updates, which are essential for establishing the timeline of communications within the group. Most of these artifacts can be correlated with the screenshot of the group on the Roblox platform, as shown in
Figure 5.
It is important to recognize that each Roblox group has its own group role names and corresponding role IDs. These artifacts can be extracted from the “roles.json” file, as illustrated in
Figure 6. For example, the JSON snippet for group ID 33865601 (Roblox digital forensics) reveals roles such as ‘Guest’, ‘Member’, ‘Admin’, and ‘Owner’, each with a specific role ID and description. Additionally, the cache file also provides the member count for each role, showing how many users occupy each position.
In addition to various roles a group can have, we can also retrieve detailed artifacts about the user’s roles in various groups, listing the groups the user is part of, including key information such as the group ID, group name, description, owner details, and member count.
6.1.6. Socializing (Groups)
One of the most important artifacts that may be retrieved from Roblox is the group chat artifacts. The messages sent in groups can be vital to many digital forensics investigations. They can provide valuable insights into a user’s communication within a group. Following the experiment we conducted, we were able to retrieve wall posts (group messages) from the test group created as shown in
Figure 7 from the cache file “cursor=&limit=50&sortOrder=Desc
.json”. The name of the file indicates that it contains a maximum of 50 entries, listed starting from the most recent, which is significant when establishing a timeline of events or interactions.
The artifacts include detailed information about two wall posts within a group. Each post is identified by a unique ‘id’, the ‘poster’, and the ‘body’. The poster artifacts of each entry reveal information about the user who made the post, including their ‘user ID’, ‘username’, and ‘displayName’. For example, user ‘4155788451’, with the username ‘kimkarter074’, holds the ‘Owner’ role, which has a role ID of ‘107562009’ and a rank of 255. Each post also contains a ‘body’ field, which shows the content of the message and the timestamps for when each post was ‘created’ and ‘updated’. These timestamps are essential for establishing a timeline of interactions and communications within the group. Overall, these artifacts can help investigators understand user interactions and establish a timeline of events.
6.1.7. Game Play
One of the main user activities on Roblox is the creation of a game (also called an experience in Roblox). By analyzing a user’s creations, investigators can potentially identify any suspicious or illegal activities associated with their creations.
Figure 8 depicts a cache file “games.json” that highlights artifacts related to games created by the user.
We were able to retrieve data about the game, including the game’s unique ID, name, and description, from the cache and local storage, as shown in
Figure 8 and
Figure 9, respectively. The artifacts retrieved include information about the creator, specifying their user ID. Additionally, the timestamps for the game’s creation and last update are also recorded, along with the total number of visits to the place. These artifacts are crucial for a digital forensics investigation as they establish the user’s activities in game creation, provide timestamps for the creation and modification of games, and offer insights into the engagement and usage patterns of the games created by the user.
6.1.8. Purchases
In Roblox, players have the option to make in-app purchases to acquire virtual currency, Robux, which is essential for purchasing in-game items, upgrades, and customizations. During the experiment, we bought 400 Robux for
$4.99 using a credit card. We could thus retrieve key artifacts related to this user activity from the cache file “payment-profiles.json” as shown in
Figure 10, such as card network, last 4 digits, and expiry month/year of the credit card used.
Additionally, we can also retrieve artifacts on the purchases made on Roblox from the cache. The cache file is usually named after the product ID. In the illustrated JSON file in
Figure 11, the artifact details a purchase made within Roblox for ‘Roblox Premium 450’ with a monthly subscription duration. The transaction was priced at ‘
$4.99’ USD and is set to renew automatically, with an expiration date of ‘22 May 2024’. Such artifacts are crucial in digital forensic analysis as they contain specific information about the product purchased, its cost, duration, and renewal settings. These details help forensic investigators reconstruct financial activities, verify account usage, and potentially identify patterns of spending or subscription management within the Roblox platform.
6.2. Windows Registry Forensics
In addition to the storage locations discussed earlier, there are other areas where valuable evidence may be concealed, such as the registry. The registry is an important source of artifacts in digital forensics analysis, offering critical insights into system configurations, user activities, and application interactions. Registry modifications provide a detailed record of changes made to a system’s settings and installed software. Through our research, it is evident that Roblox maintains a footprint in the registry. The software installs essential registry components into specific keys within the user hive, as detailed in
Table 5.
Entries such as ‘InstallDate’ can establish timelines of software installations, aiding in reconstructing the sequence of events on a system. Moreover, other registry entries also give critical information such as ‘baseHost’, and ‘version’. These registry entries also include user interface settings ‘FriendlyAppName’, ‘DisplayName (in Unicode)’, and ‘ApplicationCompany’. Overall, these registry creations serve as critical digital footprints, enabling investigators to piece together user activities and software interactions.
6.3. Memory Forensics
Three key processes stood out in relation to Roblox’s operation: ‘msedgewebview2’, ‘msedge.exe’, and ‘RobloxPlayerBeta’, as shown in
Figure 12 and
Figure 13. ‘RobloxPlayerBeta’ is the main executable for the Roblox player, responsible for running the game itself. The ‘msedge’ and ‘msedgewebview’ processes are part of Microsoft Edge WebView, a technology that embeds web content within native applications, using the Chromium engine, the same engine that powers the Microsoft Edge browser to render web pages.
From the pstree plugin results, it was observed that the processes msedgewebview2 and msedge.exe employ a multi-process architecture. In this setup, a main process, often referred to as the master process or entry point, oversees the application’s operations. Beneath this main process, multiple renderer processes efficiently manage distinct tasks. In the following subsections, we present various categories of artifacts retrieved from memory within the Windows operating system. Moreover,
Table 6 provides a comprehensive list of these artifact categories along with each specific artifact discovered.
6.3.1. Initial Setup
Significant personally identifiable information (PII) concerning the account holder can be extracted from the initial setup of the account, making it valuable in the context of a forensic investigation. Among the user account artifacts retrieved from the memory are the geolocation (where the account is created and being used) and the user password. The retrieval of the password, in particular, is crucial as it provides direct access to the user account, enabling investigators to further explore the user’s activities that cannot be retrieved from a digital forensic investigation.
6.3.2. User Profile and Creating Friends
User profile artifacts are essential to digital forensic investigations, providing information about the user on the platform. These artifacts, retrieved from memory, include the username, user ID, and account description. Such information is vital for verifying the identity of the user. Additionally, similar artifacts can be retrieved for all the user’s friends, allowing investigators to map out social connections and interactions.
6.3.3. Chat Messages
A crucial aspect of any social media platform involves the capability to exchange messages. In a forensic context, this information becomes a crucial resource for investigators, enabling them to construct a detailed narrative of communication patterns. Although we could not find any artifacts related to chats from the disk analysis, memory analysis uncovered a set of artifacts linked to chats in the Roblox platform, as shown in
Figure 14. The image provides a glimpse into the artifacts retrieved from the chat logs in Roblox. These artifacts include details such as the request methods, URLs, conversation IDs, and the text message (in plaintext). For instance, the logs reveal that a message was sent in a conversation identified by the ID 19698176631. Additionally, the logs capture interactions with the Roblox chat server, indicated by URLs like ‘
https://chat.roblox.com/v2/update-user-typing-status’ (accessed on 26 January 2026) and ‘
https://chat.roblox.com/v2/send-message’ (accessed on 26 January 2026).
These chat artifacts are significant in digital forensics investigations as they help establish communication patterns by providing message contents. This can be crucial in understanding the context of interactions, identifying participants in a conversation, and reconstructing events.
6.3.4. Creating Groups
Part of the simulated activities for the experiment was to create a public group in Roblox. Groups can be created to serve as designated spaces for specific types of interaction. During our analysis, we could retrieve the group names, group IDs, and ‘shout’ of the group. These artifacts reveal crucial evidence on the communication channels utilized by the user. Furthermore, it may also provide insights into the subject of the communication going on in the channel based on its name.
6.3.5. Game Play
Gameplay is a central activity in Roblox, serving as the primary means through which users engage with the platform. As part of the memory analysis, we were able to uncover artifacts such as ‘GameID’ and ‘name of the game’. These artifacts are crucial for digital forensics investigations because they provide specific identifiers and context for the games that users interact with. The ‘GameID’ helps trace the exact game being played, which can be linked to user activities. The ‘name of the game’ gives context to the type of content the user is engaging with, which can be essential in cases involving inappropriate or illegal activities within the game environment.
6.4. Network Forensics
The network section of Roblox can be analyzed as two different implementations. The first implementation is intercepting HTTPS traffic and analyzing connections being made to the Roblox services, leveraging TLS. The second implementation is intercepting Roblox game traffic outside HTTPS content.
Figure 15 shows a sample HTTPS request issued by Roblox to authenticate the user “mars_cabbage”. The response to the request sets up the .ROBLOSECURITY cookie that contains the authentication token required for subsequent Roblox calls. The cookie is long-lived and is vital to identify and perform actions as a user in Roblox. It allows interacting with any user Roblox HTTPS API. This cookie is important for user security and has been the target for scammers.Based on our analysis, the cookie was not limited to an IP address. We were able to use the cookie from a completely different system where the cookie had not been generated.
The game traffic communication was not interceptable directly. We believe this is because Roblox was communicating over HTTPS API, from the game was using HTTPS cert pinning that would prevent someone malicious from injecting the proxy and intercepting the traffic in between. However, we have noticed communications to the domains such as auth.roblox.com, privatemessages.roblox.com, messages.roblox.com, economy.roblox.com, and titanium.roblox.com in the Wireshark messages. Without the client certificates, it is impossible to decipher the contents of the certificate. Since the objective of the current paper is to investigate the digital forensics of Roblox executed with normal user interactions, analysis of the game traffic specifically tamper-proofed has been considered out of the scope of the current analysis.
6.4.1. Initial Setup
The initial setup occurs over HTTPS and is primarily a browser-based operation. Because of this, it is possible to intercept the TLS traffic between the browser and the Roblox service, provided the TLS certificate is installed as one of the trusted root certificates within the machine. The parameters related to the user account are captured over the network and can be decrypted using man-in-the-middle attacks. The information captured includes parameters about the username, email, client IP address, account settings, blocked and allowed users, and details required to set up the account. Once the email address is accepted by Roblox, subsequent communications to Roblox only include a masked email address with an unmasked domain name (e.g., p******a@gmail.com). The initial login to Roblox also contains the username and password transferred over the TLS protocol, as shown in
Figure 15, which was intercepted, provided a trusted root certificate is added to the computer.
6.4.2. Account Configuration
Upon login, the “.ROBLOSECURITY” cookie, as shown in
Figure 16, can be used to interact with all the Roblox account API for account management operations. The token “.ROBLOSECURITY” acts as the primary authentication token for accessing the API. The format of the cookie, as of June 2024, appears to be a hex-based string of at least 388 bytes long. The common API for account operations includes fetching settings belonging to the user upon submission of the “.ROBLOSECURITY” cookie to the URL “
https://www.roblox.com/my/settings/json”. This returns user-specific details from the API server. Furthermore, the domain “accountsettings.roblox.com” contains APIs that allow users to view the settings related to their Roblox accounts.
6.4.3. Avatar Creation
Avatar creation within Roblox includes communication with the Avatar API located at “avatar.roblox.com”. The avatar rules and avatar settings configured by the user are communicated to this domain. Authentication to this domain includes the same “.ROBLOSECURITY” cookie. The details of the avatar creation are communicated over TLS and were intercepted by a proxy, provided a trusted root certificate is installed on the client.
6.4.4. Creating Friends
The domain friends.roblox.com contains APIs for viewing and managing friends within the Roblox game. Upon logging in, some of the API requests from the browser fetch the friend request count and the list of friends of the user. The list of friends for a user ID can be retrieved using the API “/v1/users/userid/friends”. The cookie “.ROBLOSECURITY” is needed before any list of user friends is retrieved.
6.4.5. Chat Messages
Private messages are retrieved from the domain “privatemessages.roblox.com” using the “.ROBLOSECURITY” cookie. It is possible to send private messages to friends from the browser. This interaction can be captured, including the message contents, using the API at “privatemessages.roblox.com”. However, chat messages with friends during the game cannot be retrieved directly since the interaction happens in the game and not within a browser. Such communications cannot be intercepted because the client outside the browser implements a sort of validation that prevents loading of proxies into the gameplay.
6.4.6. Gameplay
Roblox games implement an active monitoring system that prevents user tampering with some of the internal settings. It is not possible to associate proxies in the game and intercept the communication. Client data is encrypted without exposing any protocol information to the Man-in-the-Middle (MITM) users. Any tampering with the client settings (e.g., running in a virtual machine) crashes the program. This is intended to prevent users of Roblox from cheating within the games.
6.4.7. Purchases
Purchases within Roblox are made through a platform called Robux. Credit card purchases are required to purchase Robux. Roblox uses Stripe as the payment processor. Since the transactions happen over the browser to purchase Robux, the credit card data was captured through MITM, provided again the TLS certificate is installed as a trusted root authority.
7. Discussion
In this research, we conducted digital forensic analysis of Roblox, which covered three distinct focus areas: disk, memory, and network. We retrieved various artifacts related to user activities from each analysis focus. However, as shown in
Table 6, not all artifacts were retrieved from each focus area. For example, while most gameplay artifacts were found in local storage, none were retrieved from session storage, cache, or network analysis, with some artifacts being retrievable from memory. Additionally, user chats were exclusively retrieved through memory analysis.
A limitation of the network analysis is that in-game Roblox traffic could not be decrypted, even when routing traffic through the configured HTTPS interception proxies. This suggests the presence of certificate pinning and anti-tampering mechanisms designed to prevent man-in-the-middle inspection and request manipulation. From a digital forensic perspective, this means that fine-grained in-game interactions cannot be reconstructed directly from network payloads using standard proxy-based interception. However, our results show that many elements of in-game behavior still leave artifacts in storage and memory, and in-game chats can be recovered from memory, while higher-level events such as group creation, chats, and friend networks are reflected in cache and API calls. In operational Roblox investigations, detailed reconstruction of in-game actions will therefore often require combining artifacts from various perspectives.
An important aspect of this study is that the reported artifacts were not only retrieved, but were also validated and cross-referenced across multiple sources. All user activities were scripted as shown in
Table 4, which provided ground-truth values for usernames, user IDs, group identifiers, game identifiers, timestamps, and purchase details. During analysis, artifacts recovered from storage, memory, and network were compared against these recorded actions and, where applicable, against the corresponding views in the Roblox interface (for example, profile and group pages). When the same logical information appeared in more than one location, such as a username observable in cache files, memory strings, and HTTPS API requests, we examined the consistency of these values across sources. In this study, timeline reconstruction was performed with reference to these scripted activities: for each action (e.g., account creation, sending and accepting friend requests, joining and posting in groups, joining games and chatting in-game, and performing purchases), we identified the corresponding artifacts across storage, memory, and network and linked them based on shared identifiers and closely aligned timestamps. The artifacts and event sequences discussed in
Section 6 therefore represent information that is both technically recoverable and consistent with the observed user behavior, which strengthens their reliability and illustrates how multi-source corroboration can be used to support evidentiary robustness.
The storage analysis revealed that the majority of artifacts were retrieved from cache files, as local and session storage have a more limited scope for data storage, storing only certain data points. Memory analysis also provided valuable information; however, a significant challenge was that the artifacts were fragmented throughout the memory dump, requiring keyword searches to locate them. These research findings demonstrate that to thoroughly retrieve artifacts related to all possible user activities, it is crucial to investigate various focus areas. Together, these artifacts enable investigators to build a detailed profile of a user’s actions, interactions, and preferences within the platform.
Considering our research questions outlined in
Section 1, we have found the following:
- 1.
Many crucial user artifacts can be retrieved through the digital forensic analysis of the disk, memory, and network.
- 2.
Artifacts retrieved, such as chats, account credentials, and PII, are crucial to digital forensics investigations because they provide comprehensive insights into user activities and identities.
- 3.
A lot of PII was retrieved, such as email, user ID, credit card information, etc.
- 4.
The retrieved artifacts are similar in that Roblox stores information in a consistent format across different storage types. Differences mainly arise in the type and completeness of the artifacts retrieved from each analysis focus.
- 5.
Since the stored information follows a similar format, evidence from different analysis focuses can be easily integrated and cross-referenced, facilitating a comprehensive digital forensic investigation.
In relation to prior digital forensic analyses of gaming consoles and platforms such as Xbox One, PlayStation 4, Minecraft, Pokémon Go, Nintendo 3DS/Switch, Decentraland, and Discord [
15,
16,
17,
18,
19,
20,
21,
22,
23,
24,
25], the present study both confirms and extends existing methodologies and findings. Similarly to these works, we demonstrate that user identifiers, profile information, gameplay traces, and payment-related artifacts can be recovered from storage and memory and, where TLS interception is feasible, from network traffic. However, our approach differs from most earlier gaming studies, which typically concentrate on a single focus area (e.g., disk or network), by systematically integrating storage, memory, and network perspectives for a single platform and by analyzing how Roblox’s architecture and anti-tampering mechanisms affect the location and accessibility of artifacts.
This research lays the foundation for our future efforts to develop a framework and tool for automating the digital forensic investigation process for Electron-based social media applications, as illustrated in
Figure 17. The proposed framework will begin by identifying and collecting data from various storage locations, including local storage, cache, and memory. It will then incorporate an advanced ETL (Extract, Transform, Load) pipeline specifically designed to handle the complexities of social media data, ensuring efficient standardization and processing across diverse storage formats. Additionally, it will integrate rule-based systems, pattern matching, and natural language processing (NLP) techniques such as Named Entity Recognition (NER), keyword matching, and near-duplicate detection to extract relevant forensic artifacts. Finally, the framework will generate comprehensive reports that present findings through user-based aggregation and timeline visualizations.
8. Conclusions and Future Work
Roblox has become a popular platform for children to engage in online gaming, but this popularity has also attracted various online crimes. In our research, we conducted a comprehensive digital forensics analysis of Roblox on a Windows machine, covering memory, disk, and network to effectively address our research questions. Our findings indicate that a variety of artifacts can be retrieved, many of which include user PII, holding significant forensic value for investigators. We also identified the storage locations of each retrieved artifact, providing essential insights for forensic analysis. Additionally, our results highlight that while many artifacts can be retrieved from the disk, certain crucial artifacts, such as chats and passwords, can only be retrieved through memory and network analysis. Therefore, to obtain a comprehensive dataset of artifacts, a multifaceted digital forensics approach targeting various focal points is necessary.
Our results indicate a gap in the field, a need for a tool that can automate artifact retrieval while maintaining the thoroughness of manual analysis. Our future work aims to address this gap by developing a tool for Electron-based social media applications, capable of parsing through diverse data points (artifacts) and generating comprehensive reports or timelines of activities based on the retrieved artifacts. This initiative is crucial as, despite the availability of artifacts, piecing them together manually to draw conclusions requires substantial labor. By automating this process, we aim to streamline digital forensic investigations and enhance efficiency in uncovering and analyzing digital evidence within Roblox and other social media applications.