1. Introduction
As the demand for wireless communication services increases, there is an increasing scarcity of spectrum resources [
1,
2]. Meanwhile, the utilization rate of authorized spectrum resources has been found to be extremely low [
3]. To address this contradiction, cognitive radio technology [
4] has emerged. Cognitive radio, first proposed in [
5], is a promising technology to exploit the under-utilized spectrum in an opportunistic manner [
6,
7,
8,
9]. This technique allows cognitive users (CUs) to access the network using an idle authorized spectrum, thereby improving the utilization of spectrum resources. Cognitive radio uses spectrum sensing as the core technology to detect whether authorized users utilize spectrum resources, thereby enabling unauthorized users to opportunistically use free bands to transmit signals. Therefore, this technology effectively improves the utilization rate of spectrum resources and has been attracting wide attention.
Common single-node spectrum sensing algorithms include energy detection (ED) [
10,
11,
12,
13,
14,
15,
16], matching filters [
17,
18,
19,
20], cyclic stationary detection [
21,
22,
23], and compressive spectrum sensing [
24,
25], and they have different requirements, advantages, and disadvantages. The ED algorithm has low complexity, is based on a simple principle, and is easy to implement. Unlike other methods, ED does not need any prior information regarding the signal, and is robust to unknown multi-path fading. However, it is vulnerable to noise uncertainty [
26,
27,
28,
29]. Moreover, accurate noise power is difficult to obtain in practice, which greatly affects the accuracy of threshold estimation and detection performance. Furthermore, when the SNR is low to a certain value, the performance of the ED will deteriorate sharply, i.e., the SNR wall effect. Under Gaussian white noise, although the matching filtering algorithm is proven to be the optimal spectrum sensing algorithm without multi-path propagation, it requires fully known prior information of the primary user (PU), which is generally unrealistic in practical environments [
17,
19,
20]. Cyclic stationary detection requires the PU to have the characteristics of cyclic stationary and to not be universal. Furthermore, for some existing algorithms, it is assumed that the channel state information is known or the channel is flat fading. However, real wireless channels tend to have multi-path propagation, implying that the channel is non-flat fading, which will severely deteriorate the performance of these algorithms. In particular, multi-path propagation destroys cyclic stationary and sharply declines the performance of the cyclic stationary algorithms. Compressed-sensing-technology-based spectrum sensing has great advantages to apply to the broadband environment because the spectrum is usually sparse in real life. However, sparsity is usually unknown, so it is necessary to choose a larger number of samples for measurement, which leads to a decrease of the detection performance of the algorithm.
To overcome these shortcomings of the single-point algorithm, many scholars have proposed to transform the single-point signal to a similar multi-point reception form through the sliding window technique and, subsequently, establish spectrum sensing algorithms by using the relevant characteristics of the covariance matrix. Therefore, the detection performance is improved. Examples of these methods are the maximum–minimum eigenvalue (MME) method [
30,
31], the covariance absolute value (CAV) method [
32,
33,
34,
35], the eigenvalue moment ratio (EMR) method [
36], and the mixture detection (MD) method [
37]. All these methods use the correlation of received data for data accumulation, which improves detection performance to a certain extent. However, not only is determining the optimal sliding window length a challenge, but the algorithms are computationally complex. In particular, the MD method requires the determinant of the covariance matrix to be calculated, which increases the computational load considerably. Therefore, there is an urgent need to develop a simple spectrum sensing algorithm with good detection performance.
Besides spectrum sensing technology, multiple access technology [
38,
39,
40] is also widely used in cognitive radio to improve spectrum efficiency. This technology allows a CU to transmit over the same time-frequency slot of a PU, which leads to high spectrum efficiency. However, the tempting incentive of the multiple access technology is at the price of multi-signal interference and an increase in the computational complexity of the primary receiver. Compared to multiple access technology, spectrum sensing technology improves the spectrum efficiency without the influence of PU. Consequently, we focus on spectrum sensing technology.
In this paper, we propose two spectrum sensing algorithms based on the analysis of the characteristics of a frequency-selective fading channel. The main contributions are as follows. First, we construct a test statistic on the basis of the strong correlation between the received signal and its corresponding delay version as well as the independence of the noise at different times. The analysis shows that the proposed algorithms implement the correlation accumulation without requiring the prior information of the PU, and that they have similar properties to the matched filter method. Thus, the proposed algorithms improve the detection probability. Second, when the received data are divided into real and complex numbers, we provide the probability distribution of the test statistics of the proposed algorithms by theoretical analysis in the case of absent signals. On the basis of this probability distribution, the false alarm probability of the proposed algorithm can be obtained, and the detection threshold corresponding to the required false alarm probability can be determined. Third, we compare the computational complexity of the proposed algorithm with that of ED, MME, CAV, EMR, and MD. The results show that the computational complexity of the proposed algorithm is similar to that of ED and much lower than that of MME, CAV, EMR, and MD. Finally, the simulation results confirm the effectiveness of the proposed algorithm and the accuracy of the theoretical analysis.
The remainder of the paper is organized as follows. The system model is introduced in
Section 2.
Section 3 describes the proposed algorithms, including the design of the two proposed test statistics, the theoretical analysis, and the determination of the thresholds of the proposed algorithm. This section also discusses the comparison of the complexities of some related algorithms. The simulation results and discussion are presented in
Section 4. Finally,
Section 5 concludes the paper.
The notations used in this paper are as follows: boldface capital and small letters denote matrices and vectors, respectively; the superscripts and stand for transpose and complex conjugate, respectively; denotes the absolute value of a variable or the magnitude of a complex number; and represents the expectation operation.
2. System Model
Consider a spectrum sensing system with one PU and one CU. Assume that there is multi-path propagation between the two users, that is, the channel is frequency-selective fading. In the case of the presence and absence of the PU represented by
and
, the received signal of CU at time
is respectively given by
where
is the independent and identically distributed (i.i.d.) Gaussian white noise independent of the transmission signals with mean zero and variance
. Moreover, if the noise is complex, its real part and imaginary part are independent of each other. Further,
,
is the received signal, which experiences multi-path propagation without considering the effect of noise,
is the impulse response with order
, and
is the signal transmitted by the PU. The signal-to-noise ratio (SNR) is defined as
, and, usually, a low SNR is required for spectrum sensing. Without loss of generality, assume that
meets the following statistical characteristics:
Let us consider
consecutive receiving data samples and define the receiving data vector as
Our goal is to construct the test statistic
T =
f(
x) and determine the detection threshold
and then compare them to determine whether a signal is present or not in the received data, i.e.,
3. Proposed Algorithm
In spectrum sensing, we mainly focus on two performance indicators: the detection probability and the false alarm probability . In the construction of the test statistic, we should consider the effect of the test statistic on both these probabilities. Therefore, irrespective of whether the PU is present or not, the test statistic should have high distinguishability. In other words, the test statistic should meet the following requirements: (1) the difference between the means of the test statistics when the PU signal is present and absent is larger, and (2) the variance of the test statistics is small when the PU signal is either present or not.
3.1. Spectrum Sensing Algorithm Based on Blind Matched Filtering
According to Equation (1), if no PU signal exists, the received data (pure noise) at times
and
are uncorrelated. By contrast, if the PU signal exists, the received data at
and
are correlated. Because they are all related to the received signals
, we can construct the test statistic according to the autocorrelation of the received data from the adjacent times. When there is no PU signal, the autocorrelation of
and
is defined as
According to Equation (5), because the noises at adjacent times are uncorrelated,
is equal to zero. When the PU is present, the autocorrelation of
and
is defined as
Owing to the multi-path effect, the samples at adjacent times have the components of the transmitted signals simultaneously [
41]. Thus, the correlation is relatively high, and
is larger. Combining Equations (5) and (6), statistics
and
are observed to have a significant difference when the PU signal is present and absent. Hence,
can be used as the test statistic for the presence of the PU or not. In addition, the statistic
is similar to the result of matched filtering. As is well known, the output of matched filtering has the largest SNR. Therefore, the proposed algorithm has good detection performance. Without the requirement of the prior information of the PU for the test statistic of
, the proposed algorithm is more robust and has wider application scenarios compared to the non-blind methods. Therefore, the method in which
is used as the test statistic is called blind matched filtering (BMF).
Theoretically,
indicates that no signal is contained in the received data;
indicates that the received data contain a signal. In practice, however, the statistic
can only be calculated with the finite sampling signal. Accordingly, the statistic
can be used as the test statistic
, and it can be approximately calculated as
where
is the number of available samples.
Hence, the spectrum sensing method based on BMF is summarized in Algorithm 1:
| Algorithm 1: The proposed BMF. |
| Step 1: Obtain the observations . |
| Step 2: According to Equation (7), calculate the test statistic . |
| Step 3: Based on and threshold , determine the presence or absence of the PU using the following Formula (8): |
where
is the detection threshold corresponding to the BMF method, which will be discussed in
Section 3.3.
3.2. Spectrum Sensing Algorithm Based on Improved Blind Matched Filtering
BMF considers the case of autocorrelation with unit delay as a test statistic. In fact, the autocorrelation of other adjacent signal samples has similar properties. When the PU is absent, the autocorrelation of
and
is
When the PU is present, the autocorrelation of
and
is
According to Equations (9) and (10),
(
) have the following properties: (1)
indicates that the PU signal does not exist, and (2)
indicates that the PU signal exists. Based on the above analysis, we construct a similar test statistic as follows:
Compared to
, because the test statistic
uses the more correlated information, the detection performance of the test statistic
is better than that of
, which will be proved by the simulation. The method corresponding to this test statistic is called improved BMF (IBMF). Similarly, the test statistic
can be calculated as
Then, the actual test statistic becomes
Hence, the spectrum sensing method based on IBMF is summarized in Algorithm 2:
| Algorithm 2: The proposed IBMF. |
| Step 1: Obtain the observations |
| Step 2: According to Equation (12), calculate (). |
| Step 3: According to Equation (13), the test statistic is calculated. |
| Step 4: Determine whether there is a PU according to the following Formula (14): |
where
is the detection threshold corresponding to the IBMF method. This will be discussed in
Section 3.4.
3.3. Theoretical Analysis and Threshold Determination of the BMF Method
The two performance indexes of spectrum sensing are false alarm probability
and detection probability
. Obviously,
should be large and
should be small for a good detection algorithm. However, these are contradictory indicators that need to be compromised. The requirements of
and
depend on the application. Detection threshold
is a core parameter of spectrum sensing, and it can balance the two probabilities. According to Equation (8), the smaller the detection threshold, the higher the detection probability and the false alarm probability. In the absence of the PU signal,
will simplify to
where notation
stands for round down. Because
is i.i.d., all the terms in
(the odd terms in
) are i.i.d. When the sample number
is large,
satisfies the Gaussian distribution according to the central limit theorem (CLT). Similarly,
(the even term in
) also satisfies the Gaussian distribution. Moreover, because the linear combination of the Gaussian distribution still satisfies the Gaussian distribution,
satisfies the Gaussian distribution. Its mean and variance are, respectively,
and
To calculate the false alarm probability,
must be considered a real number or a complex number. First, when
is a real number, the false alarm probability is
where
. Generally, we determine the detection threshold by a given false alarm probability. Accordingly, the detection threshold
can be calculated as
Second, when
is a complex number, because the real and imaginary parts of
are i.i.d. and
is independent of
, the real part
and imaginary part
of
are i.i.d., and their probability densities can be written, respectively, as
and
Accordingly, the probability density function of
is
Equation (22) indicates that
satisfies the Rayleigh distribution, and its complementary cumulative distribution function is:
Therefore, when
is a complex number, the false alarm probability is
Given the false alarm probability
, the corresponding detection threshold is
3.4. Theoretical Analysis and Threshold Determination of the IBMF Method
Similarly to
, all the
terms in
are i.i.d. Consequently,
also satisfies the Gaussian distribution when
is sufficiently large, and its mean is
Because
are i.i.d.,
can simply be calculated by multiplying
by
, i.e.,
Next, to calculate the false alarm probability of the IBMF, we need to consider the cases where
is a real number and a complex number. First, when
is a real number, according to the above analysis, we can obtain
. Thus, we have
When the sum of the multiple random variables that are i.i.d is calculated, the sum can be approximated by its mathematical expectation by referring to [
34]. According to this conclusion, the false alarm probability can be expressed as
Accordingly, when the false alarm probability is
, the corresponding detection threshold is
Similar to the derivation of
, when
is a complex number,
satisfies the Rayleigh distribution, and its probability density and complementary cumulative distribution function are, respectively,
and
From the probability density function of
, we can obtain the mathematical expectation as follows:
To sum up, when the received data are complex, the false alarm probability is
Similarly to (29), the false alarm probability can be approximated as
by referring to [
34].
Correspondingly, given the false alarm probability, the detection threshold is
It is worth noting that the detection threshold is only related to noise, which is highly susceptible to noise measurement uncertainty. Consequently, this may be a limit of the application of the proposed algorithm. To overcome this problem, it is better to reduce the uncertainty of noise with enough samples.
3.5. Computational Complexity Analysis of ED, MME, CAV, EMR, MD, BMF, and IBMF
To simplify the following computational complexity analysis, we ignore the addition and subtraction operations. Suppose the number of samples is . Then, the computational complexity of ED, MME, CAV, EMR, MD, BMF, and IBMF is analyzed as follows.
First, the ED method requires calculating the square of the modulus of each sample, and it takes approximately multiplications. Similarly, BMF approximately requires multiplications. In IBMF, calculating takes multiplications, and the IBMF method requires about multiplications. Note that the case of generally holds. Thus, the BMF and IBMF methods require approximately and multiplications, respectively.
Second, the computational load of MME mainly includes the calculation of the covariance and eigenvalues. Consider a case where the smoothing factor is set to . The calculation of the covariance needs approximately multiplications and that of the eigenvalue needs approximately multiplications. Thus, MME requires a total of multiplications. If a computational complexity of a lower order than is neglected, the computational complexity of MME is approximately . Again, without considering a computational complexity lower than the order of , the computational complexity of CAV is approximately multiplications. Similarly, the computational load of EMR is mainly concentrated in the calculation of the sample covariance matrix. Consequently, the computational complexity of EMR is also approximately . For MD, the sample covariance matrix and noise covariance matrix are required to be calculated, and the computational complexity of MD is approximately . Here, is the number of noise samples.
The computational complexity of ED, MME, CAV, BMF, IBMF, EMR, and MD is summarized in
Table 1.
As
Table 1 shows, ED has the lowest computational complexity. However, ED accumulates the power of both the noise and the signal, and the accuracy of the noise power greatly affects detection performance. It has been verified that the detection performance of the ED algorithm decreases sharply under the condition of inaccurate noise power [
26,
27,
28,
29]. The other methods make use of the correlation of non-zero time delay. Because the correlation of noise under non-zero delay is zero, the detection performance is less dependent on the accuracy of noise power. Therefore, comparison of the other four methods is more referential. Meanwhile, the table also indicates that the computational complexity of BMF and IBMF is considerably lower than that of MME, CAV, EMR, and MD because the BMF and IBMF do not require calculating the correlation matrix.
4. Simulation Results and Discussion
In this section, we compare the ED, MME, CAV, EMR, MD, BMF, and IBMF algorithms and prove the effectiveness of the proposed algorithm under multi-path fading channels. Cases in which the received signals are real and the numbers are complex numbers are considered. The parameters in the simulations are set as follows: the channels order is 12, and their real and imaginary parts are evenly distributed in the interval [0, 1]. When the received signal is a real number, the transmitted signal is a BPSK signal that takes a value from set . When the received signal is a complex number, the transmitted signal is a 4QAM signal that takes a value from set . The smoothing factor of the MME and CAV algorithms is 12, and the maximum delay of IBMF is set to 11. In addition, the receiver operating characteristic (ROC) and the detection probability are used to measure the performance of all the related algorithms. It is worth noting that in the simulation, the detection threshold is obtained by a Monte Carlo experiment, and we use the true value of the noise power.
First, we consider a case where the received signal is a real number.
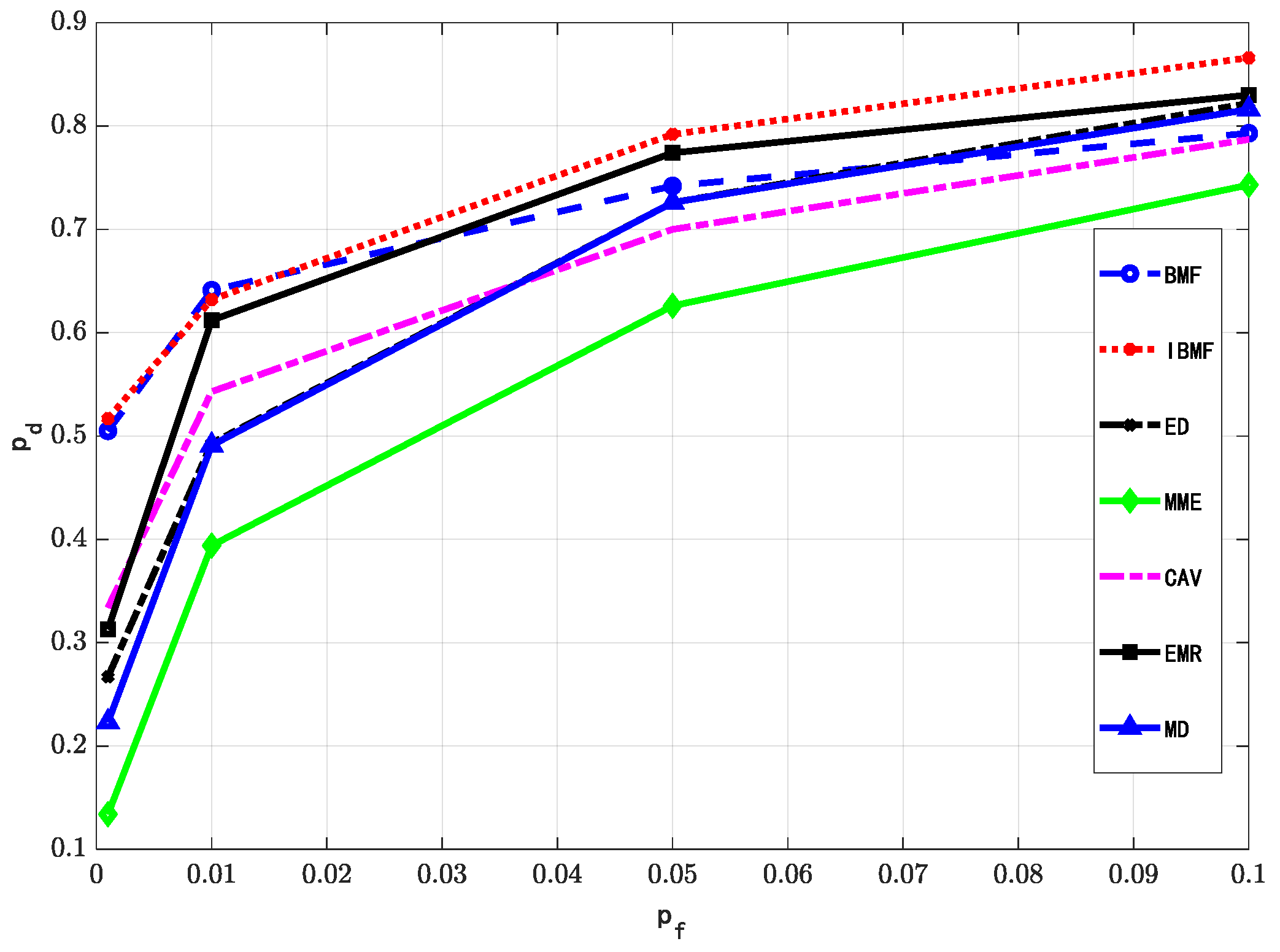
Figure 1 indicates that the performance of the BMF algorithm is not the best compared to other algorithms, while the IBMF algorithm, which is the improved version of the BMF, has the best detection performance compared to the other methods. This result can be explained by the following two aspects: (1) Unlike ED, MME, EMR, MD, and CAV, IBMF uses the correlation of received signals and the uncorrelation of the noise at different time delays, accumulating the signal component and weakening the noise component. Thus, detection performance is improved. (2) Unlike BMF, which simply uses a single delay to perform correlation accumulation, IBMF uses multiple delays to realize correlation accumulation. Therefore, the robustness of IBMF is improved. It is also worth noting that the poor performance of CAV and MME arises from two aspects: (1) The accuracy of covariance directly affects the performance of CAV and MME. However, the sample number is not sufficiently large, which leads to an inaccurate covariance matrix. (2) The
is too low, which adversely affects the estimation of the covariance matrix and consequently affects the performance of CAV and MME.
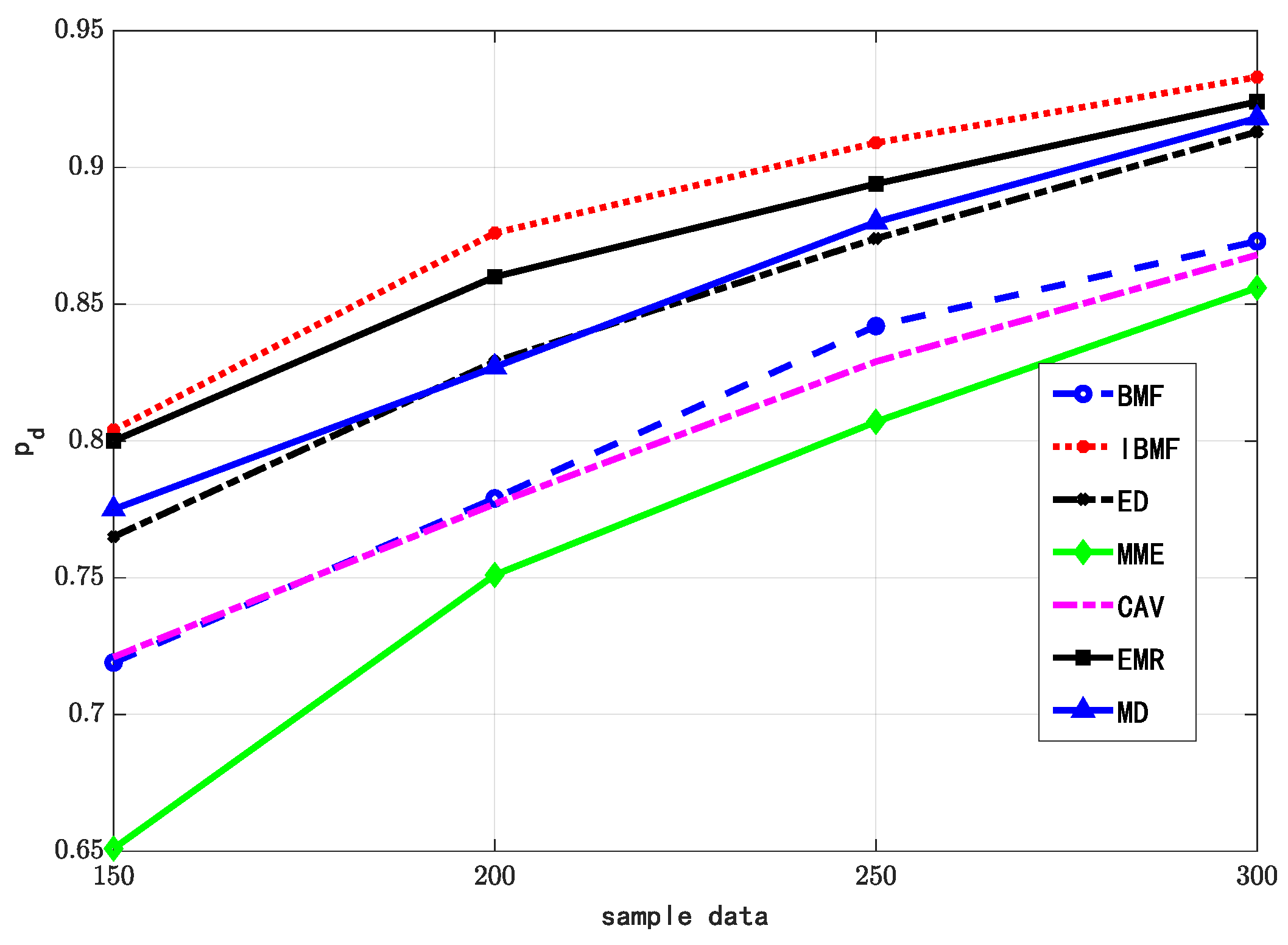
Figure 2 indicates that the proposed IBMF algorithm provides the highest detection probability under the same SNR. This result is consistent with that of the optimal ROC. Thus, the proposed algorithm can be applied to lower SNR scenarios compared to other algorithms.
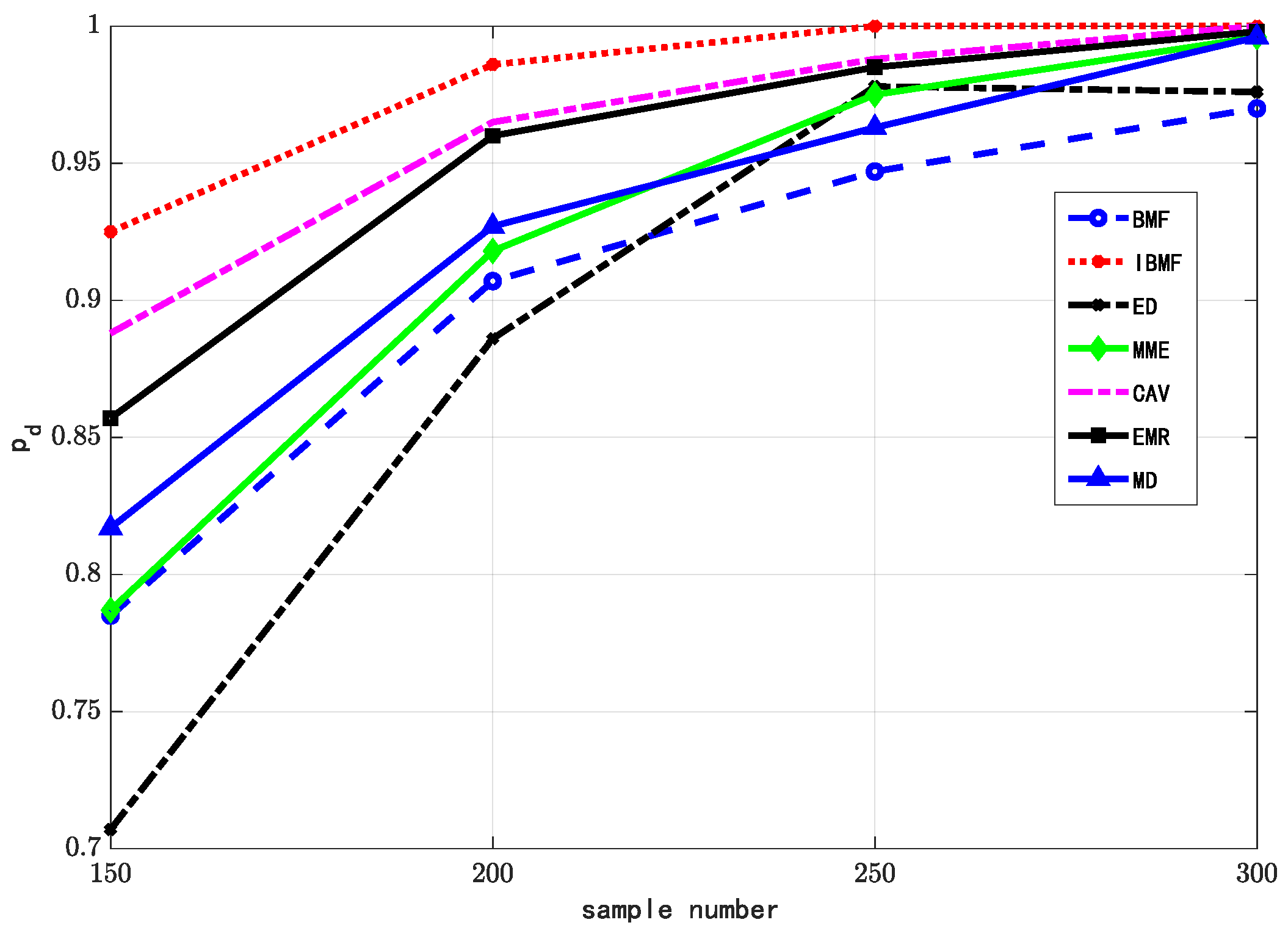
Figure 3 compares the detection probabilities of various methods in different sample sizes. The proposed IBMF algorithm is consistently superior to other algorithms in the same number of samples, while the BMF algorithm is superior to the MME algorithm and slightly better than the CAV algorithm. The results confirm that the IBMF algorithm can achieve higher detection performance under fewer samples; therefore, it can improve the detection efficiency and ensure system reliability.
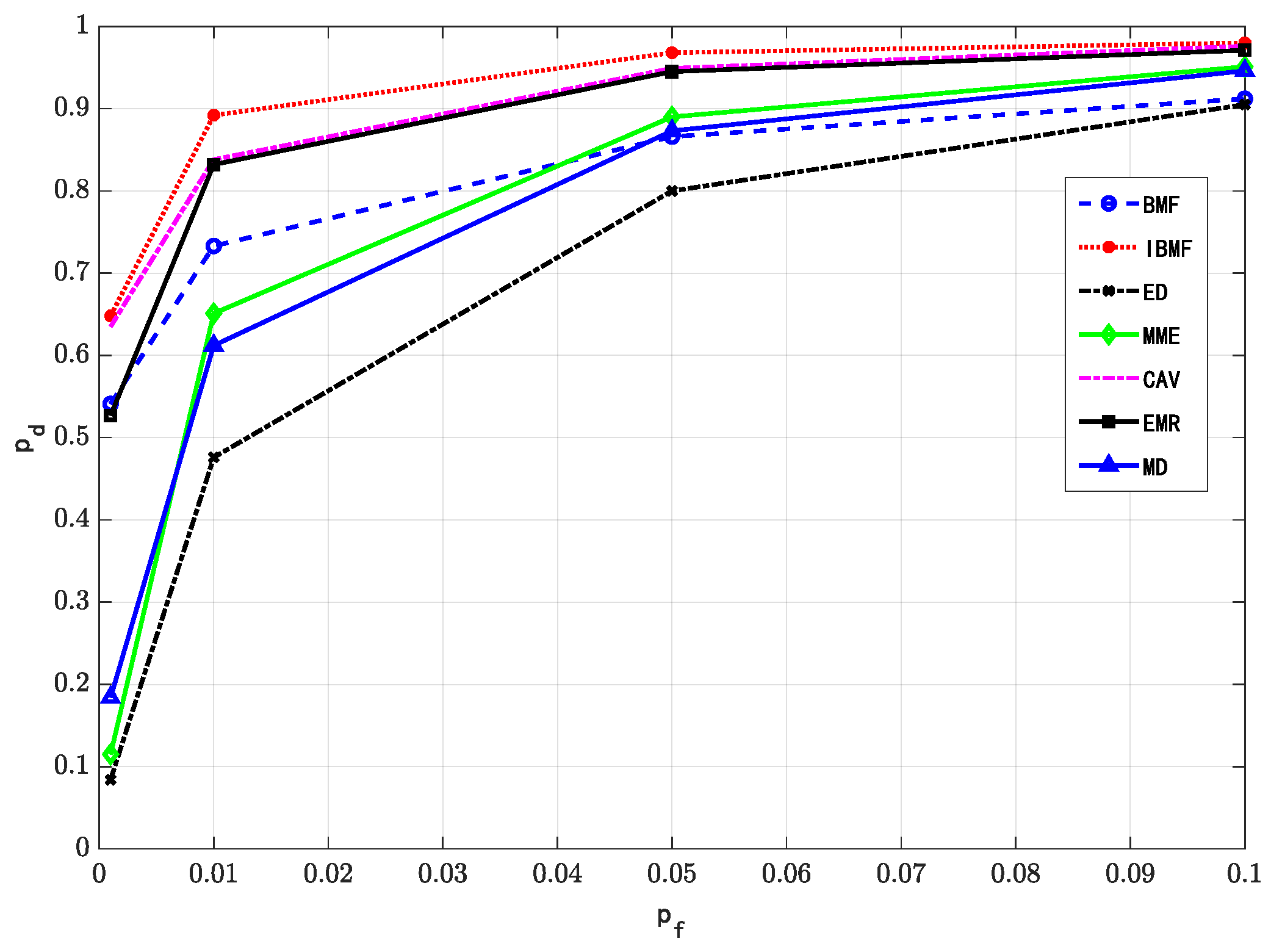
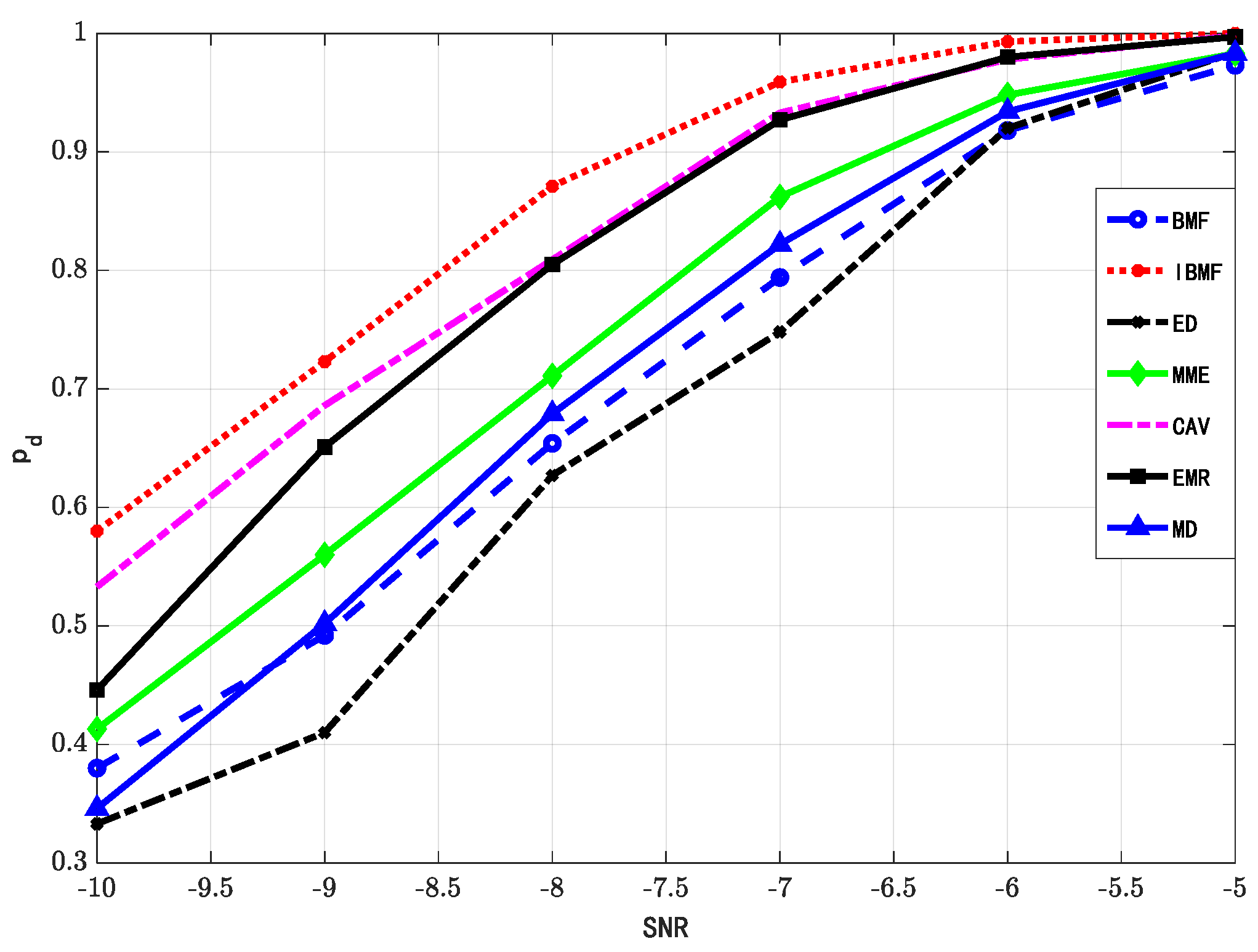
The above three experiments illustrate the effectiveness of the proposed algorithm in the case of a real received signal. Next, we compare the performance of the different algorithms in the case of a complex received signal.
Figure 4,
Figure 5 and
Figure 6 describe the ROCs of various algorithms and the changing trend of the detection probability with SNR as well as the number of samples, respectively. Although the performance of the BMF is not very good, the figures indicate that IBMF shows the best detection performance among all compared algorithms. The reasons are the same as in the case of the real received signal. Horizontal comparison shows that the performance of each algorithm in the case of the complex received signal is better than in the case of the real received signal. This is because in the case of the complex received signal, the data are divided into real and imaginary parts under the same conditions, and the statistical results of the data are more accurate to a certain extent. In addition, in the case of complex received signals, the ED algorithm performed the worst because the other algorithms accumulate signal energy and reduce the accumulation of noise. In the case of separating the data into the real and imaginary parts, the above-mentioned effect is more significant and, therefore, detection performance will be further improved.