Securing Publisher–Subscriber Smart Grid Infrastructure
Abstract
:1. Introduction
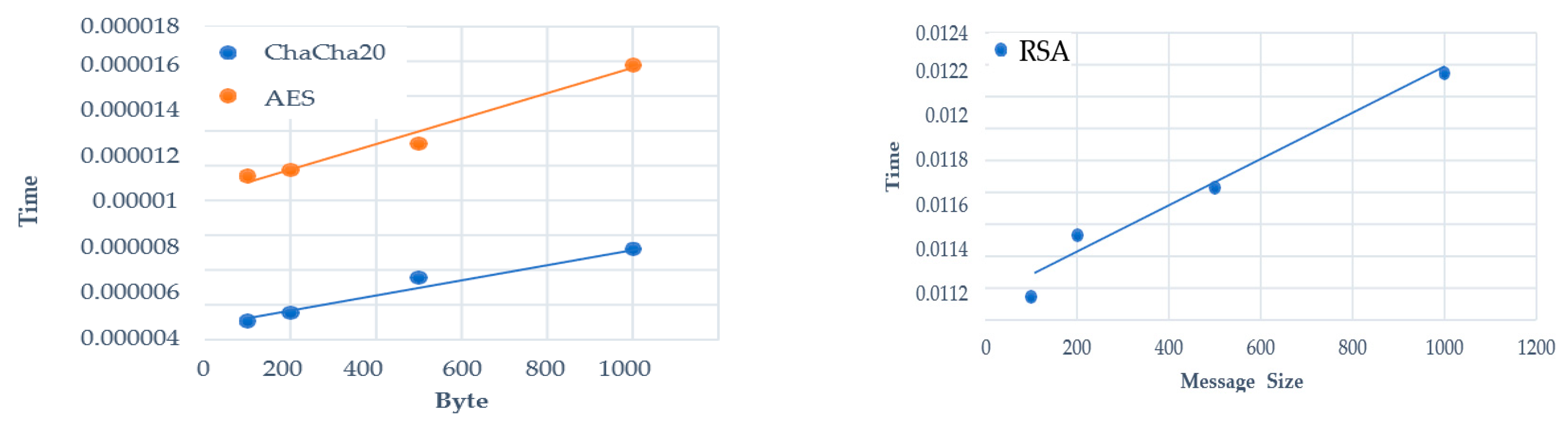
- We develop a tool to investigate and evaluate the performance of our approach that incorporates encryption algorithms with various potential factors such as the size of the messages.
- We implement the encryption algorithms as per IEC61850 to secure GOOSE, SMV, and MMS communication in the substation automation systems.
- We analyze the efficacy of our proposed approach in evaluating it concerning the specific requirements of the protocols in the substation automation systems.
2. Communication and Adversary Models
2.1. Substation Automation Features
2.2. Communication Model
2.3. Adversary Model
2.4. Related Work
3. Proposed Approach
3.1. Approach Idea
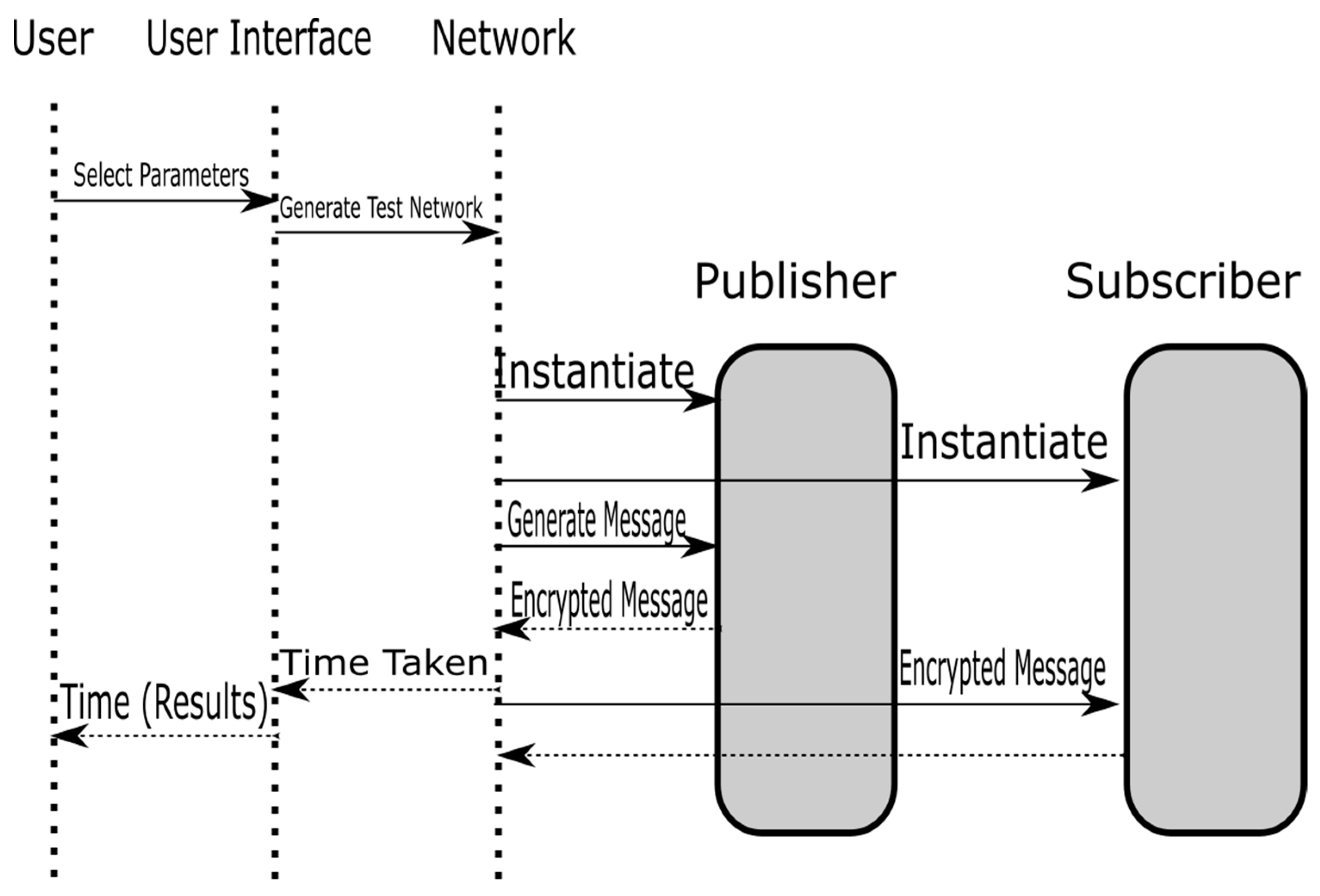
3.2. Proposed Scheme
| Algorithm 1 Proposed Approach |
| Step 1: A publisher creates a message that is later multicasted in the network for its all subscribers of the topic. Step 2: An access control list is created based on all subscribers of the topic. A group key is created to cover all subscribers who could receive a secret key to decipher the message. Step 3: A cipher algorithm is decided to encrypt the message before its transmission over the network. A message is encrypted using a secret key. Step 4: A secret key is transmitted to all subscribers using a group key, i.e., encrypting the secret key using a group key. Step 5: The message is reached to all its subscribers who will have access to this message based on the access list. Step 6: The secret key is extracted using the group key and the message is encrypted by each subscriber. |
3.3. Secret Key Exchange
3.4. Experimental Design
3.5. Implementation: Protecting Communicated Information—Confidentiality
- A non-linear substitution step where each byte is replaced with another according to a lookup table.
- A transposition step where the last three rows of the state are shifted a certain number of steps cyclically.
- A linear mixing operation that operates on the columns of the state, combining the four bytes in each column.
- Round key addition where the subkey is combined with the state.
4. Results and Evaluation
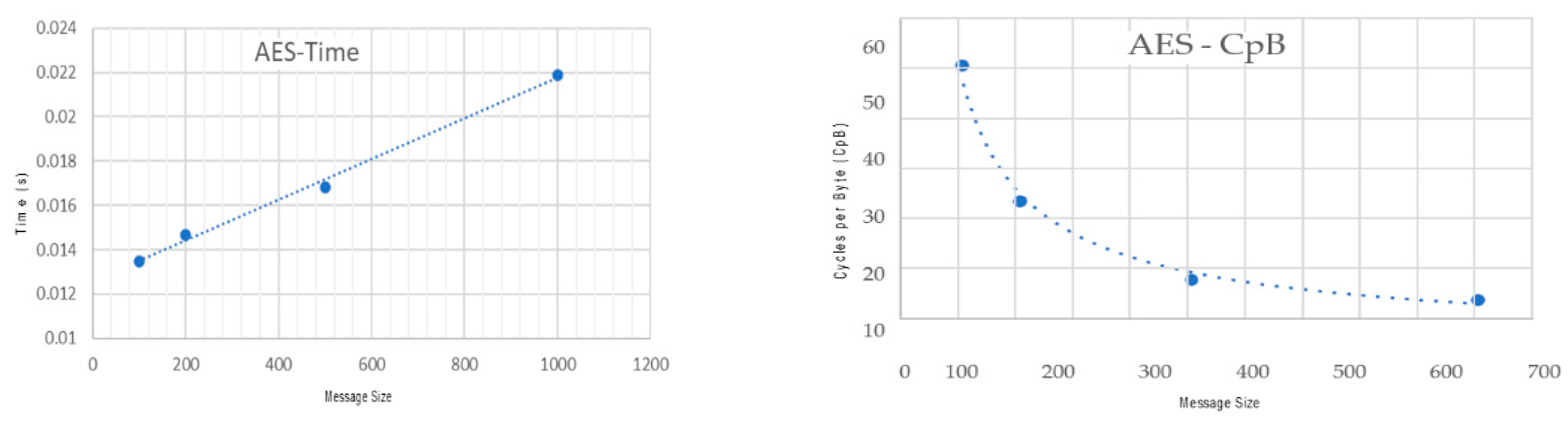
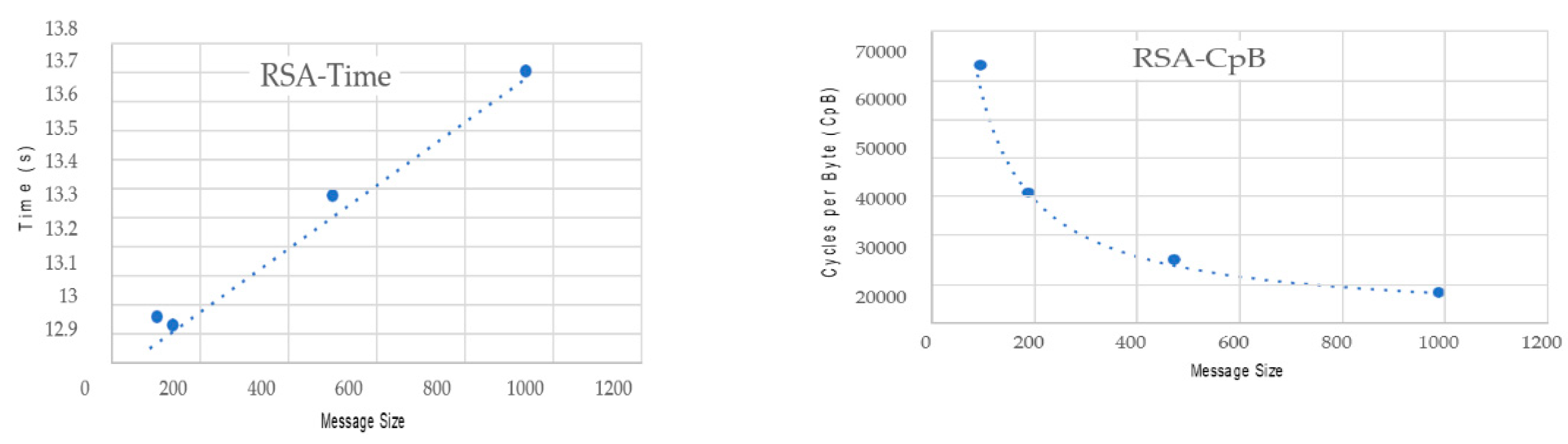
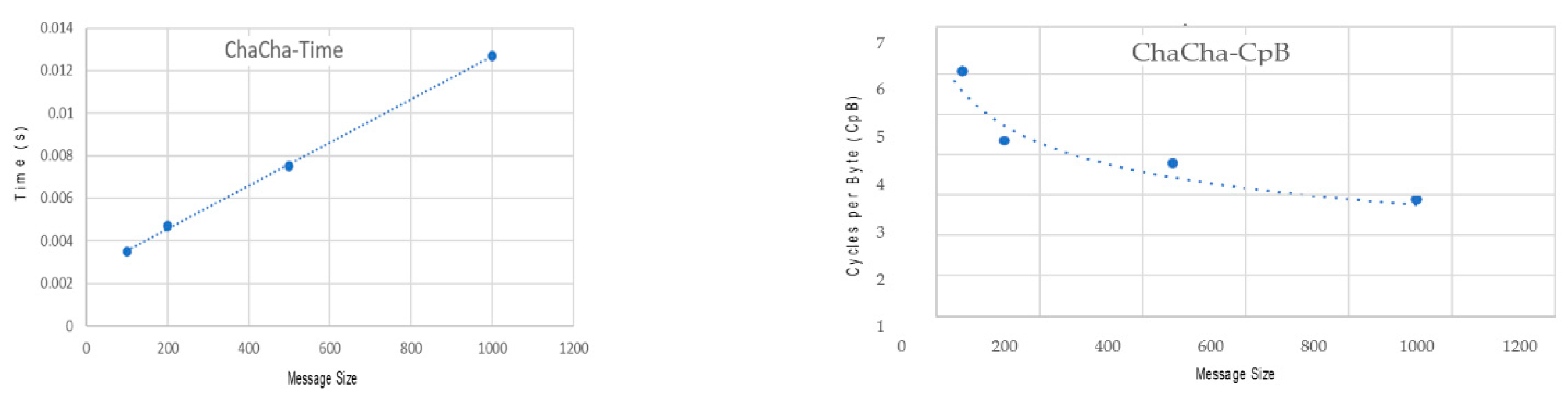
4.1. Results Observation
4.2. Evaluation
4.3. Attack Analysis
4.3.1. What If the Secret Session Key Is Compromised?
4.3.2. What If the Group Key Is Compromised?
5. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Hong, J.; Karnati, R.; Ten, C.W.; Lee, S.; Choi, S. Implementation of Secure Sampled Value (SeSV) Messages in Substation Automation System. IEEE Trans. Power Deliv. 2021. [Google Scholar] [CrossRef]
- Markets, R.A. The $39.9 Billion Worldwide Substation Automation Industry Is Expected to Reach $54.2 Billion by 2026. GlobeNewswire News Room. Available online: https://www.globenewswire.com/news-release/2021/06/04/2241918/28124/en/The-39-9-Billion-Worldwide-Substation-Automation-Industry-is-Expected-to-Reach-54-2-Billion-by-2026.html (accessed on 8 July 2021).
- Saxena, N.; Grijalva, S.; Choi, B.J. Securing restricted publisher-subscriber communications in smart grid substations. In Proceedings of the 10th International Conference on Communication Systems & Networks (COMSNETS), Bangalore, India, 3–7 January 2018; pp. 364–371. [Google Scholar]
- Aftab, M.A.; Hussain, S.S.; Ali, I.; Ustun, T.S. IEC 61850 based substation automation system: A survey. Int. J. Electr. Power Energy Syst. 2020, 120, 106008. [Google Scholar] [CrossRef]
- Saxena, N.; Grijalva, S. Dynamic secrets and secret keys based scheme for securing last mile smart grid wireless communication. IEEE Trans. Ind. Inform. 2016, 13, 1482–1491. [Google Scholar] [CrossRef]
- Saxena, N.; Grijalva, S. Efficient signature scheme for delivering authentic control commands in the smart grid. IEEE Trans. Smart Grid 2017, 9, 4323–4334. [Google Scholar] [CrossRef] [Green Version]
- Hussain, S.S.; Farooq, S.M.; Ustun, T.S. A method for achieving confidentiality and integrity in IEC 61850 GOOSE messages. IEEE Trans. Power Deliv. 2020, 35, 2565–2567. [Google Scholar] [CrossRef]
- Elbaset, A.A.; Mohamed, Y.S.; Elghaffar, A.N.A. IEC 61850 Communication Protocol with the Protection and Control Numerical Relays for Optimum Substation Automation System. J. Eng. Sci. Technol. Rev. 2020, 13, 1–12. [Google Scholar]
- Pal, A.; Jolfaei, A.; Kant, K. A Fast Prekeying-Based Integrity Protection for Smart Grid Communications. IEEE Trans. Ind. Inform. 2020, 17, 5751–5758. [Google Scholar] [CrossRef]
- Nweke, L.O.; Weldehawaryat, G.K.; Wolthusen, S.D. Adversary model for attacks against IEC 61850 real-time communication protocols. In Proceedings of the 16th International Conference on the Design of Reliable Communication Networks (DRCN), Milan, Italy, 25–27 March 2020; pp. 1–8. [Google Scholar]
- Quincozes, S.E.; Albuquerque, C.; Passos, D.; Mossé, D. A survey on intrusion detection and prevention systems in digital substations. Comput. Netw. 2021, 184, 107679. [Google Scholar] [CrossRef]
- Wannous, K.; Toman, P. IEC 61850 communication based distance protection. In Proceedings of the 15th International Scientific Conference on Electric Power Engineering (EPE), Brno-Bystrc, Czech Republic, 12–14 May 2014; pp. 107–112. [Google Scholar]
- Saxena, N.; Choi, B.J. Integrated Distributed Authentication Protocol for Smart Grid Communications. IEEE Syst. J. 2018, 12, 2545–2556. [Google Scholar] [CrossRef]
- Hou, D.; Dolezilek, D. IEC 61850–What It Can and Cannot Offer to Traditional Protection Schemes. 2008. Available online: https://cdn.selinc.com/assets/Literature/Publications/Technical%20Papers/6335_IEC61850_DH-DD_20080912_Web.pdf (accessed on 20 July 2021).
- Yeh, T.H.; Hsu, S.C.; Chung, C.K.; Lin, M.S. Conformance test for IEDs based on IEC 61850 communication protocol. J. Power Energy Eng. 2015, 3, 289. [Google Scholar] [CrossRef]
- Falk, H. Securing IEC 61850. In Proceedings of the IEEE Power and Energy Society General Meeting-Conversion and Delivery of Electrical Energy in the 21st Century, Clemson, SC, USA, 14–17 March 2006; pp. 1–3. [Google Scholar]
- Fateri, S.; Ni, Q.; Taylor, G.A.; Panchadcharam, S.; Pisica, I. Design and analysis of multicast-based publisher/subscriber models over wireless platforms for smart grid Communications. In Proceedings of the 2012 IEEE 11th International Conference on Trust, Security and Privacy in Computing and Communications, Liverpool, UK, 25–27 June 2012; pp. 1617–1623. [Google Scholar]
- Kabra, A.; Kumar, S.; Kasbekar, G.S. Efficient, Flexible and Secure Group Key Management Protocol for Dynamic IoT Settings. EAI Endorsed Trans. Internet Things 2021, 7, 1–17. [Google Scholar] [CrossRef]
- Ozansoy, C.R.; Zayegh, A.; Kalam, A. The real-time publisher/subscriber communication model for distributed substation systems. IEEE Trans. Power Deliv. 2007, 22, 1411–1423. [Google Scholar] [CrossRef]
- Galla, L.K.; Koganti, V.S.; Nuthalapati, N. Implementation of RSA. In Proceedings of the International Conference on Control, Instrumentation, Communication and Computational Technologies (ICCICCT), Kumaracoil, India, 16–17 December 2016; pp. 81–87. [Google Scholar]
- Rebeiro, C.; Selvakumar, D.; Devi, A. Bitslice implementation of AES. In International Conference on Cryptology and Network Security; Springer: Berlin/Heidelberg, Germany, 2006; pp. 203–212. [Google Scholar]
- Yuan, Y.; Yang, Y.; Wu, V.; Zhang, X. A high performance encryption system based on AES algorithm with novel hardware implementation, In Proceedings of the 2018 IEEE International Conference on Electron. Devices and Solid State Circuits (EDSSC), Shenzhen, China, 6–8 June 2018; pp. 1–2. [Google Scholar] [CrossRef]
- Bernstein, D.J. The Salsa20 Family of Stream Ciphers. In New Stream Cipher Designs; Springer: Berlin/Heidelberg, Germany, 2008; pp. 84–97. [Google Scholar]
- Cryptopp.com. 2021. Speed Comparison of Popular Crypto Algorithms. 2021. Available online: https://www.cryptopp.com/benchmarks.html (accessed on 6 August 2021).
- Bernstein, D.J.; ChaCha, a Variant of Salsa. Workshop Record of SASC: The State of the Art of Stream Ciphers. Available online: https://cr.yp.to/chacha/chacha-20080120.pdf (accessed on 12 August 2021).
- Mundra, A.; Agarwal, M. Human Machine Interface (HMI) for Protection Relay Reference Design; [ebook] Texas. 2017. Available online: https://www.ti.com/lit/ug/tidudn5/tidudn5.pdf?ts=1627122810724&ref_url=https%253A%252F%252Fwww.google.com%252F (accessed on 26 August 2021).

| ID | Message Type | Requirement Name | Criteria | Comment |
|---|---|---|---|---|
| R1 | GOOSE, SMV | Time Constraint | The total time from publisher encryption to the message being decrypted by the subscriber should take no longer than 4 ms | This is the defining requirement for the algorithm is the time complexity will dictate what solutions should be discussed |
| R2 | GOOSE, SMV | Model | The system should support multicast communication for the publisher–subscriber model | This is to emulate the real-world communication the smart grids use to communicate |
| R3 | MMS | Time Constraint | Time is less critical with total time ranging from 100–500 depending on if it’s a low/medium or command message | These are not very quick time conditions so a wide range of algorithms should be applicable |
| R3 | MMS | Model | Follows a client–server model | This is a more standard model to implement |
| ID | Requirement Name | Priority | Criteria | Comment |
|---|---|---|---|---|
| NF1 | Algorithms must be lightweight | High | To be deployed to IEDs, the algorithms must be able to run in a limited environment | This directly ties into how quickly the algorithm runs with most fast encryption methods based on lightweight methods |
| NF2 | Time constraints | High | The specification for message types must be met | Any implementation must meet the constraints for each message type, as mentioned previously |
| NF3 | Message Integrity | High | The message sent on any model must be able to be decoded and read by the recipient | All encryptions must be able to be decrypted by the intended recipient |
| NF4 | Attack prevention | High | All encryption algorithms used must not be susceptible to any known attack | The implementation must be cryptographically secure from known attacks such as Man-in-the-middle or replay attacks |
| F1 | User Comparison | High | It should be easy for the user to compare different algorithms with different message types | Using the tool, it should be easy to look at the results of |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Orr, F.; Nafees, M.N.; Saxena, N.; Choi, B.J. Securing Publisher–Subscriber Smart Grid Infrastructure. Electronics 2021, 10, 2355. https://doi.org/10.3390/electronics10192355
Orr F, Nafees MN, Saxena N, Choi BJ. Securing Publisher–Subscriber Smart Grid Infrastructure. Electronics. 2021; 10(19):2355. https://doi.org/10.3390/electronics10192355
Chicago/Turabian StyleOrr, Fraser, Muhammad Nouman Nafees, Neetesh Saxena, and Bong Jun Choi. 2021. "Securing Publisher–Subscriber Smart Grid Infrastructure" Electronics 10, no. 19: 2355. https://doi.org/10.3390/electronics10192355
APA StyleOrr, F., Nafees, M. N., Saxena, N., & Choi, B. J. (2021). Securing Publisher–Subscriber Smart Grid Infrastructure. Electronics, 10(19), 2355. https://doi.org/10.3390/electronics10192355








