Attack Graph Modeling for Implantable Pacemaker
Abstract
1. Introduction
1.1. Related Work
2. Pacemaker Automatic Remote Monitoring System (PARMS) Modeling
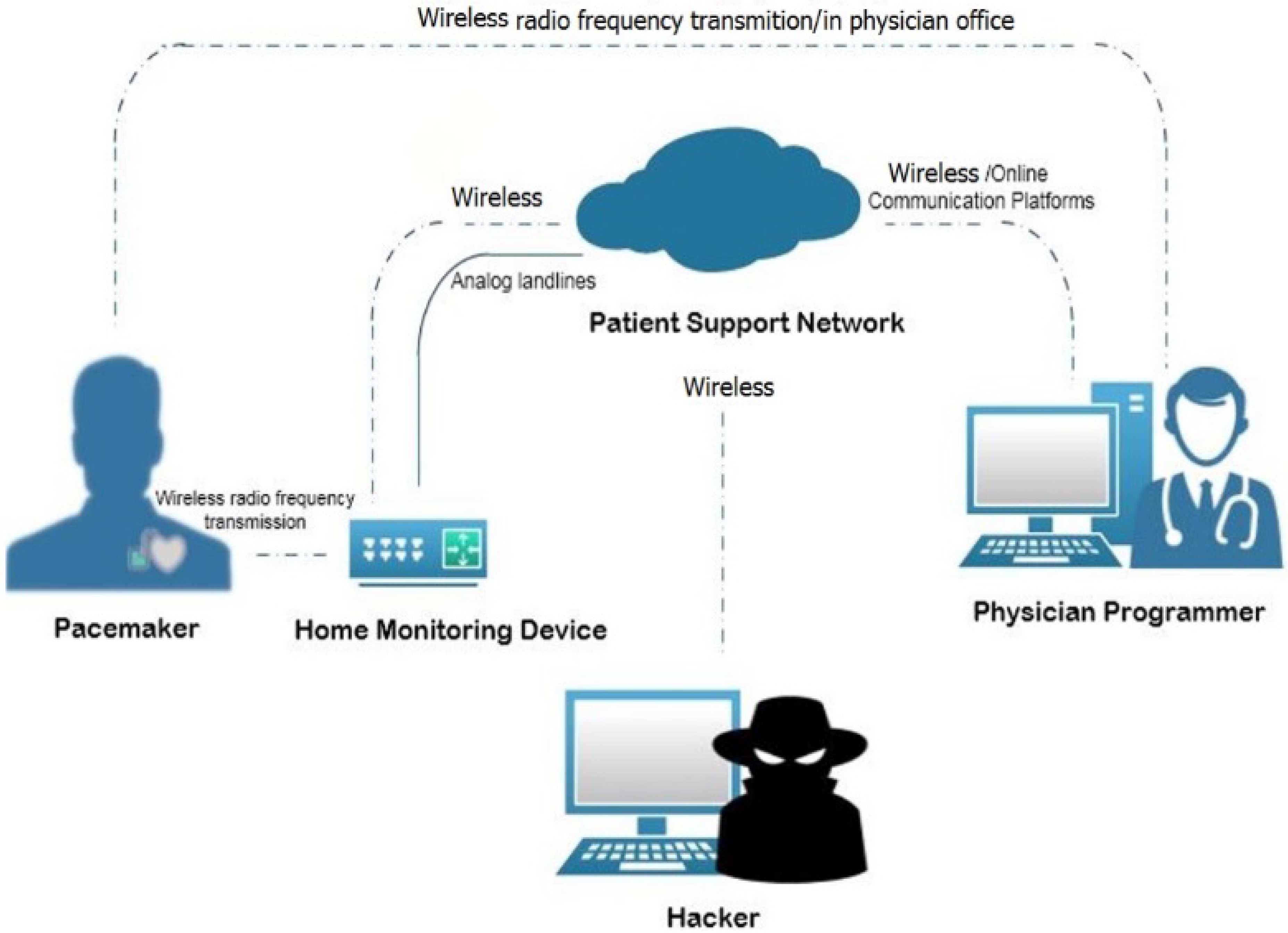
2.1. PARMS Topology
- Wireless Pacemaker: This is a battery-powered implantable device that produces an excitatory wave at an appropriate site within the heart. The pacemaker initiates the electrical depolarization cycle of the heart at approximately 72 beats/min in the atrioventricular (AV) node to replace a malfunctioning AV node. The AV node is the electrical connecting point from the atria to the ventricles, which continues excitation beyond a partial or total heart block. Modern pacemakers can also store diagnostic data [33].
- Physician Programmer (PP): A computer with specific software and associated hardware modifications is used to program the pacemaker at the time of implantation. It is used to test pacemaker functionality in the follow-up visits to the physician’s office by sending instructions to change therapy parameters, and reading battery status and heart rhythms. The physician programmer contains a transceiver which communicates with the pacemaker antenna via radio frequency (RF) [32,35].
- Home Monitoring Device (HS): This is a transceiver placed in proximity to the patient and used to monitor the pacemaker by collecting the data that the pacemaker sends periodically at a set of frequencies (e.g., every two days or every week) using RF transmissions via the micro-antenna. The HS then sends data to the physician programmer via analog landlines or wireless data networks. The data incorporate heart rate, battery status, pacing lead impedance, episodes of arrhythmias, conveyed antitachycardia pacing, percent pacing, histogram, real-time and magnet electrograms (EGM), reserved EGMs, arrhythmia reviews, and mode switch period [35,36].
- Access Point (AP): This exists for outside internet communication. We assume the attacker is located at this point.
- RF communication between the PP and the wireless pacemaker in order to program it and check its functionality.
- The PP and the PN are connected through online communication platforms: “cloud networking”.
- RF communication between the HS and the wireless pacemaker to inquire different measurements related to the pacemaker such as the battery state and pulse rate.
- The communication between the HS and the PN involves sending measurements to the PN to be stored there and accessed later by the responsible PP. The PN also transmits updates from the network to the HS using analog landlines, a wireless data network, or a wireless Global System for Mobile communications (GSM).
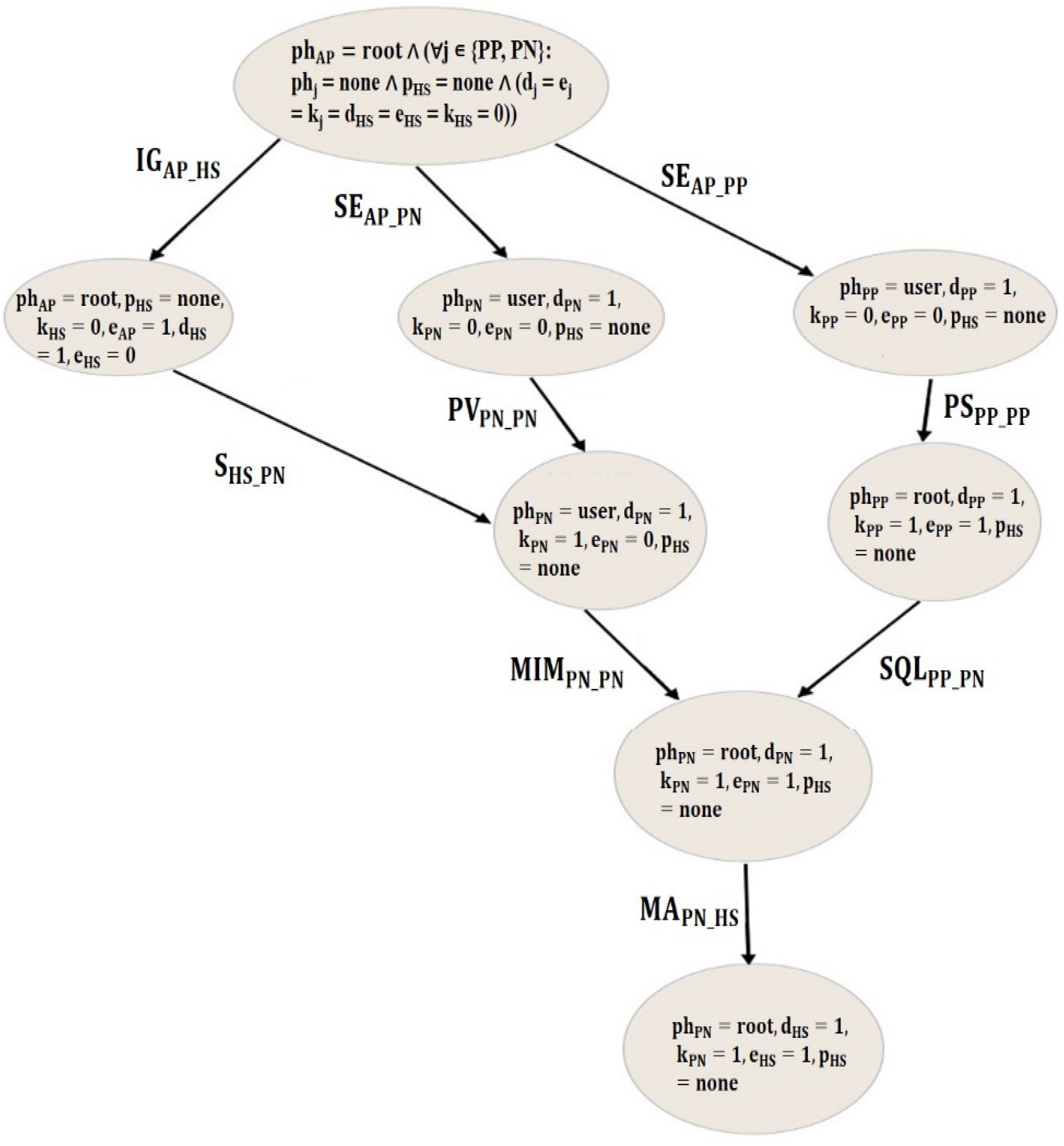
- Intelligent Gathering (IG): This is used for gathering information about IoT devices such as Internet Protocol (IP) addresses, and checking the type of firmware, as well as the existence of COTS.
- Social Engineering (SE): This attack is used to gain access and disclose information. It generally targets enterprises and organizations.
- Pivoting (PV): This is a standard technique used in penetration testing to navigate from machine to machine [37].
- Sniffing (S): This attack is used to steal or break off data by capturing the network traffic using a sniffer, for example to get login usernames and passwords that are sent by the HS [32].
- Man-in-the-Middle (MiM): This attack can occur when the attacker has access over the network connection. Thus, disclosing and manipulating the data flow between two parties.
- Phishing (PS): This is used to steal user data and allow the attacker to disguise as a trusted entity [38].
- Malware Injection (MA): The attacker can edit, copy, or install the code at the host. Thus, gaining a root access.
- SQL Injection (SQL): This attack is used to exploit the web application. Thus, allowing the attacker to gain unauthorized access to the PN database or retrieve information directly from it [39].
2.2. Formal Description of PARMS
- The attacker is assumed to be located at (AP) and has a root privilege.
- system components S; variable s ∈ {PP, PN, HS, AP} (static).
- system connectivity, C ⊆ PP × PN, HS × PN; cij = 1 if component i is connected to component j (static).
- System vulnerabilities V; Boolean vi = 1 if vulnerability v ∈ {COTS, firmware} exists on i (static).
- Set of possible attacks B; variable b ∈ {IG, SE, S, PS, PV, SQL, MiM, MA}.
- Attack instances, AI ⊆ B × C; labeled bij ≡ attack b from source i to target j, b ∈ B.
- Attacker level of privilege P on HS device; variable pHS ∈ {none, root} (dynamic).
- Attacker level of privilege PH on host i ∈ {PP, PN, AP}; variable phi ∈ {none, user, root} (dynamic).
- Data identification D of component i; Boolean di = 1 if identification data about i gets collected by attacker (dynamic).
- Confidential data disclosure K of component i; Boolean ki = 1 if confidential data of component i get disclosed to attacker (dynamic).
- Data alteration E of component i, Boolean ei = 1 if attacker is able to edit the setting on component i (dynamic).
- Attack instances pre-conditions:
- Pre(IGij) = (cij = 1) ∧ (phi = root) ∧ (pHS = none)
- Pre(SEij) = (cij = 1) ∧ (phi = root) ∧ (phj = none)
- Pre(SEij) = (cij = 1) ∧ (phi = root) ∧ (phj = none)
- Pre(Sij) = (cij = 1) ∧ (pHS = none) ∧ (dHS = 1) ꓥ (COTSj = 1)
- Pre(PSij) = (cij = 1) ∧ (phi = user) ∧ (dj = 1) ꓥ (firmwarej = 1)
- Pre(PVij) = (cij = 1) ∧ (phi = user) ∧ (dj = 1)
- Pre(SQLij) = (cij = 1) ∧ (phi = root) ∧ (phj = user) ∧ (dj = 1) ∧ (ej = 1) ∧ (kj = 1)
- Pre(MIMij) = (cij = 1) ∧ (phi = user) ∧ (dj = 1) ∧ (ej = 0) ∧ (kj = 1)
- Pre(MAij) = (cij = 1) ∧ (phi = root) ∧ (pHS = none) ∧ (dj = 1) ∧ (ej = 1) ∧ (kj = 1) ꓥ (COTSj = 1 ꓦ firmwarej = 1)
- Attack instances post-conditions:
- Post(IGij) = (dHS = 1) ∧ (pHS = none)
- Post (SEij) = (phj = user) ∧ (dj = 1)
- Post (SEij) = (phj = user) ∧ (dj = 1)
- Post (Sij) = (phj = user) ∧ (dj = 1) ∧ (kj = 1)
- Post (PSij) = (phj = root) ∧ (dj = 1) ∧ (ej = 1) ∧ (kj = 1)
- Post (PVij) = (ph j = user) ∧ (d j = 1) ∧ (k j = 1)
- Post (SQLij) = (phj = root) ∧ (dj = 1) ∧ (ej = 1) ∧ (kj = 1)
- Post (MIMij) = (phj = root) ∧ (dj = 1) ∧ (ej = 1) ∧ (kj = 1)
- Post (MAij) = (pHS = root) ∧ (dHS = 1) ∧ (eHS = 1) ∧ (kHS = 1)
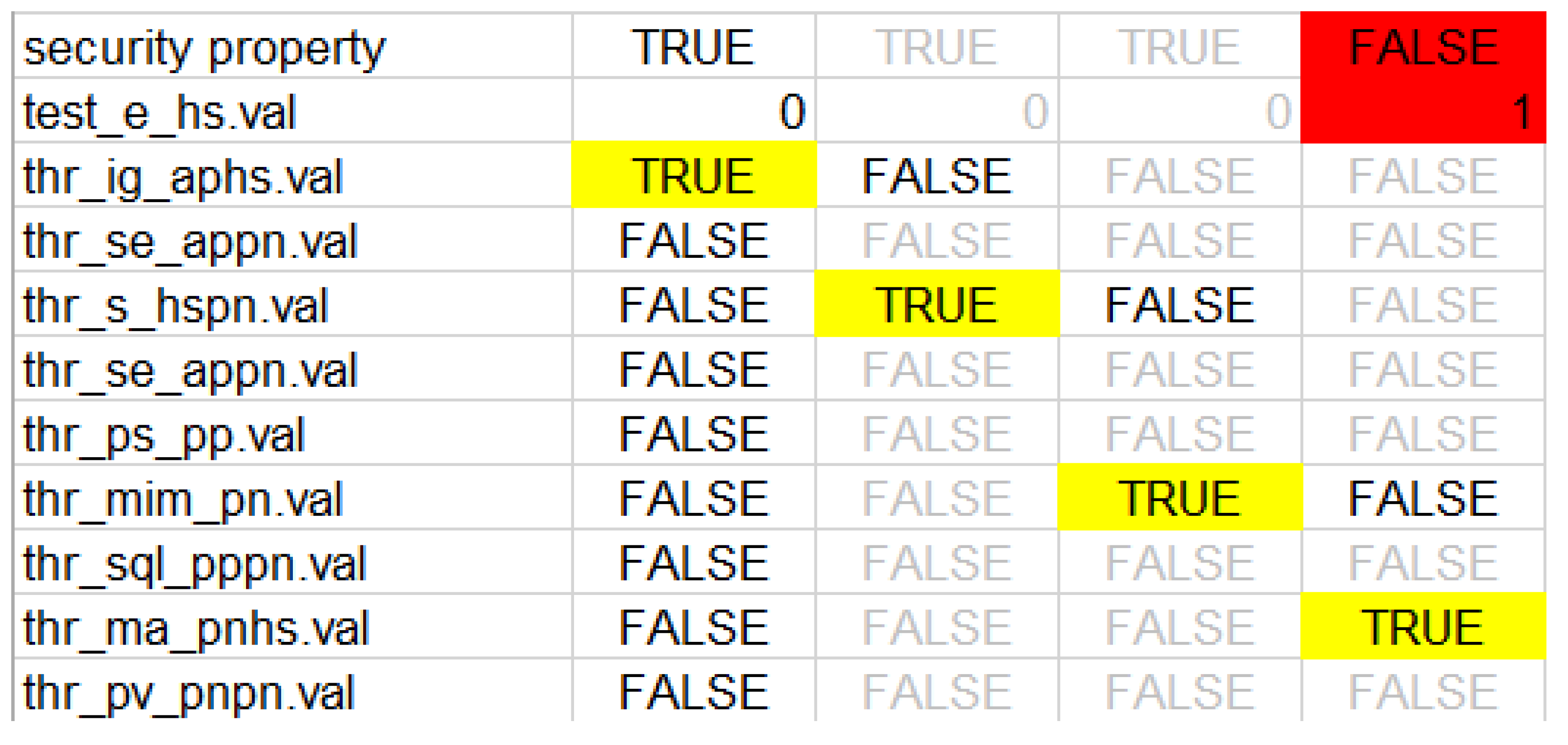
- Initial state: phAP = root ∧ (∀j ∊ {PP, PN}: phj = none ∧ pHS = none ∧ (dj = ej = kj = dHS = eHS = kHS = 0)). (Initially, the attacker has a root privilege on access point, no data identification, no confidential data disclosure, and no ability to alter the setting of HS).
- Security property (φ): The attacker has no ability to edit the setting on the home monitoring device HS. Thus, jeopardizing patient’s life. This property can be then described by a computational tree logic (CTL):φ ≡ AG (eHS = 0) ≡ AG (¬ (eHS = 1))
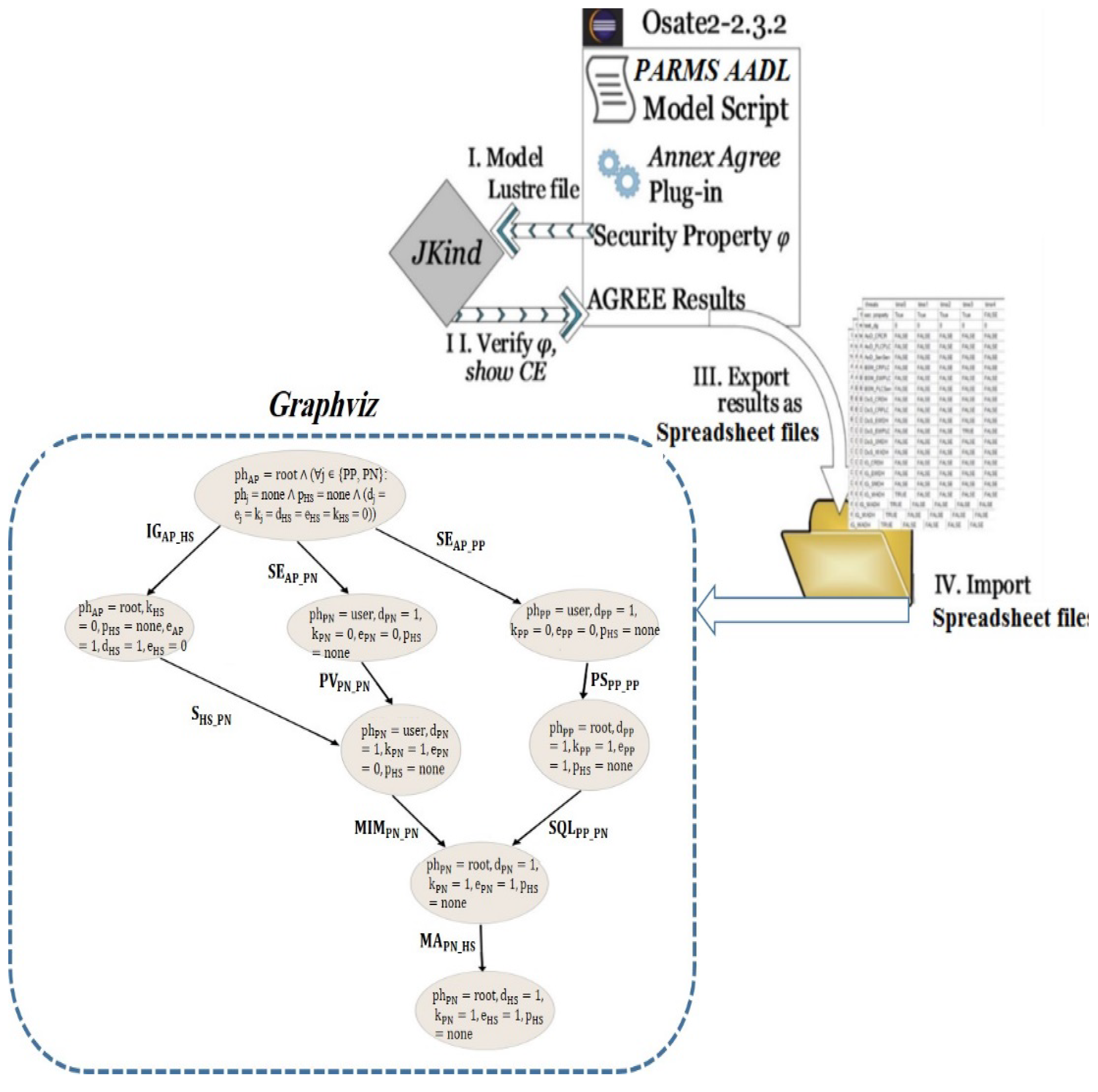
3. Attack Graph Generation
4. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Abouzakhar, N.S.; Jones, A.; Angelopoulou, O. Internet of Things Security: A Review of Risks and Threats to Healthcare Sector. In Proceedings of the 2017 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Exeter, UK, 21–23 June 2017; pp. 373–378. [Google Scholar]
- Xu, J. Systematic Vulnerability Evaluation of Interoperable Medical Device System using Attack Trees. Master’s Theses, Worcester Polytechnic Institute, Worcester, MA, USA, December 2015. [Google Scholar]
- Islam, S.M.R.; Kwak, D.; Kabir, H.; Hossain, M.; Kwak, K.S. The Internet of Things for Health Care: A Comprehensive Survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Taylor, C.; Venkatasubramanian, K.; Shue, C.A. Understanding the security of interoperable medical devices using attack graphs. In Proceedings of the 3rd International Conference on Mobile and Ubiquitous Multimedia (MUM ’04), College Park, MD, USA, 27–29 October 2014; pp. 31–40. [Google Scholar]
- Virat, M.S.; Bindu, S.; Aishwarya, B.; Dhanush, B.; Kounte, M.R.; M, B.S.; N, D.B. Security and Privacy Challenges in Internet of Things. In Proceedings of the 2018 2nd International Conference on Trends in Electronics and Informatics (ICOEI), Tirunelveli, India, 11–12 May 2018; pp. 454–460. [Google Scholar]
- Yaqoob, T.; Abbas, H.; Atiquzzaman, M. Security Vulnerabilities, Attacks, Countermeasures, and Regulations of Networked Medical Devices—A Review. IEEE Commun. Surv. Tutor. 2019, in press. [Google Scholar] [CrossRef]
- Peck, M. Medical Devices Are Vulnerable to Hacks, But Risk Is Low Overall. Available online: https://spectrum.ieee.org/biomedical/devices/medical-devices-are-vulnerable-to-hacks-but-risk-is-low-overall (accessed on 26 May 2019).
- Brandom, R. UK Hospitals Hit with Massive Ransomware Attack. Available online: https://www.theverge.com/2017/5/12/15630354/nhs-hospitals-ransomware-hack-wannacry-bitcoin (accessed on 26 May 2019).
- Center of Internet Security. DDoS Attacks: In the Healthcare Sector. Available online: https://www.cisecurity.org/blog/ddos-attacks-in-the-healthcare-sector/ (accessed on 26 May 2019).
- Abelson, R.; Goldstein, M. Millions of Anthem Customers Targeted in Cyberattack. Available online: https://www.nytimes.com/2015/02/05/business/hackers-breached-data-of-millions-insurer-says.html (accessed on 26 May 2019).
- Evenstad, L. NHS Data Breach Caused Details of 150,000 Patients to be Shared. Available online: https://www.computerweekly.com/news/252444145/NHS-data-breach-caused-details-of-150000-patients-to-be-shared (accessed on 26 May 2019).
- Vincent, J. 1.5 Million Affected by Hack Targeting Singapore’s Health Data. Available online: https://www.theverge.com/2018/7/20/17594578/singapore-health-data-hack-sing-health-prime-minister-lee-targeted (accessed on 26 May 2019).
- Xiao, Y.; Jia, Y.; Cheng, X.; Yu, J.; Liang, Z.; Tian, Z. I Can See Your Brain: Investigating Home-Use Electroencephalography System Security. IEEE Internet Things J. 2019, 6, 6681–6691. [Google Scholar] [CrossRef]
- Luckett, P.; McDonald, J.; Glisson, W. Attack-Graph Threat Modeling Assessment of Ambulatory Medical Devices. In Proceedings of the 50th Hawaii International Conference on System Sciences (2017), Hilton Waikoloa Village, HI, USA, 4–7 January 2017; Volume 4, pp. 3648–3657. [Google Scholar]
- Agmon, N.; Shabtai, A.; Puzis, R. Deployment optimization of IoT devices through attack graph analysis. In Proceedings of the 12th Conference on Security and Privacy in Wireless and Mobile Networks (WiSec ’19), Miami, FL, USA, 15–17 May 2019; pp. 192–202. [Google Scholar]
- Grispos, G.; Glisson, W.B.; Cooper, P. A Bleeding Digital Heart: Identifying Residual Data Generation from Smartphone Applications Interacting with Medical Devices. In Proceedings of the 52nd Hawaii International Conference on System Sciences, Maui, HI, USA, 8–11 January 2019. [Google Scholar]
- Ellouze, N.; Rekhis, S.; Boudriga, N.; Allouche, M.; Elouze, N. Cardiac Implantable Medical Devices forensics: Postmortem analysis of lethal attacks scenarios. Digit. Investig. 2017, 21, 11–30. [Google Scholar] [CrossRef]
- Carnegie-Mellon-University. Open Source Aadl Tool Environment for the SAE Architecture. 2018. Available online: http://osate.github.io/index.html (accessed on 15 May 2018).
- Sheeran, M.; Singh, S.; Stålmarck, G. Checking Safety Properties Using Induction and a SAT-Solver. In International Conference on Formal Methods in Computer-Aided Design; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1954, pp. 127–144. [Google Scholar]
- Graphviz—Graph Visualization Software. Available online: https://www.graphviz.org/download/ (accessed on 26 May 2019).
- Sango, M.; Godot, J.; Gonzalez, A.; Nolasco, R.R. Model-Based System, Safety and Security Co-Engineering Method and Toolchain for Medical Devices Design. In Proceedings of the 2019 Design of Medical Devices Conference, Saint Paul, MN, USA, 15–18 April 2019. [Google Scholar]
- Tian, Z.; Sun, Y.; Su, S.; Li, M.; Du, X.; Guizani, M. Automated Attack and Defense Framework for 5G Security on Physical and Logical Layers. arXiv 2019, arXiv:1902.04009. [Google Scholar]
- Xu, J.; Venkatasubramanian, K.K.; Sfyrla, V. A methodology for systematic attack trees generation for interoperable medical devices. In Proceedings of the 2016 Annual IEEE Systems Conference (SysCon), Orlando, FL, USA, 18–21 April 2016; pp. 1–7. [Google Scholar]
- Almohri, H.; Cheng, L.; Yao, D.; Alemzadeh, H. On Threat Modeling and Mitigation of Medical Cyber-Physical Systems. In Proceedings of the 2017 IEEE/ACM International Conference on Connected Health: Applications, Systems and Engineering Technologies (CHASE), Philadelphia, PA, USA, 17–19 July 2017; pp. 114–119. [Google Scholar]
- Tu, M.; Spoa-Harty, K.; Xiao, L. Data Loss Prevention Management and Control: Inside Activity Incident Monitoring, Identification, and Tracking in Healthcare Enterprise Environments. J. Digit. Forensics Secur. Law 2015, 10, 27–44. [Google Scholar] [CrossRef]
- Strielkina, A.; Kharchenko, V.; Uzun, D. Availability models for healthcare IoT systems: Classification and research considering attacks on vulnerabilities. In Proceedings of the 2018 IEEE 9th International Conference on Dependable Systems, Services and Technologies (DESSERT), Kyiv, Ukraine, 24–27 May 2018; pp. 58–62. [Google Scholar]
- Ghose, N.; Lazos, L.; Rozenblit, J.; Breiger, R. Multimodal graph analysis of cyber attacks. In Proceedings of the IEEE Spring Simulation Conference (SpringSim), Tucson, AZ, USA, 29 April–2 May 2019; pp. 1–12. [Google Scholar]
- Ge, M.; Kim, D.S. A Framework for Modeling and Assessing Security of the Internet of Things. In Proceedings of the 2015 IEEE 21st International Conference on Parallel and Distributed Systems (ICPADS), Melbourne, Australia, 14–17 December 2015; pp. 776–781. [Google Scholar]
- Kammüller, F.; Tryfonas, T. Formal Modeling and Analysis with Humans in Infrastructures for IoT Health Care Systems. In Proceedings of the Formal Aspects of Component Software, Braga, Portugal, 10–13 October 2017; Volume 10292, pp. 339–352. [Google Scholar]
- Doumbouya, M.B.; Kamsu-Foguem, B.; Kenfack, H.; Foguem, C. Combining conceptual graphs and argumentation for aiding in the teleexpertise. Comput. Boil. Med. 2015, 63, 157–168. [Google Scholar] [CrossRef] [PubMed]
- Siddiqi, M.A.; Seepers, R.M.; Hamad, M.; Prevelakis, V.; Strydis, C. Attack-tree-based Threat Modeling of Medical Implants. In Proceedings of the 7th International Workshop on Security Proofs for Embedded Systems, Amsterdam, The Netherlands, 13 September 2018; pp. 32–49. [Google Scholar]
- Rios, B.; Butts, J. Security Evaluation of the Implantable Cardiac Device Ecosystem Architecture and Implementation Interdependencies. 2017. Available online: https://a51.nl/whitescope-security-evaluation-implantable-cardiac-device-ecosystem-architecture-and-implementation (accessed on 17 May 2017).
- Sanders, R.S. The Pulse Generator. In Cardiac Pacing for the Clinician; Kusumoto, F.M., Goldschlager, N.F., Eds.; Springer: Boston, MA, USA, 2008; pp. 47–71. [Google Scholar]
- Chede, S.; Kulat, K. Design Overview of Processor Based Implantable Pacemaker. J. Comput. 2008, 3, 49–57. [Google Scholar] [CrossRef]
- Ibrahimi, S. A Secure Communication Model for the Pacemaker a Balance between Security Mechanisms and Emergency Access; Technische Universiteit Eindhoven: Eindhoven, The Netherland, 2014. [Google Scholar]
- Lakshmanadoss, U.; Shah, A.; Daubert, J.P. Telemonitoring of the pacemakers. In Modern Pacemakers-Present and Future; IntechOpen: London, UK, 2011; pp. 129–146. [Google Scholar]
- Meixell, B.; Forner, E. Out of control: Demonstrating SCADA exploitation. In Proceedings of the Black Hat, Las Vegas, NV, USA, 27 July–1 August 2013. [Google Scholar]
- Nagunwa, T. Behind Identity Theft and Fraud in Cyberspace: The Current Landscape of Phishing Vectors. Int. J. Cyber-Security Digit. Forensics 2014, 3, 72–83. [Google Scholar] [CrossRef]
- Patel, N. SQL Injection Attacks: Techniques and Protection Mechanisms. IJCSE 2011, 3, 199–203. [Google Scholar]
- Mebsout, A.; Tinelli, C. Proof certificates for SMT-based model checkers for infinite-state systems. In Proceedings of the Formal Methods in Computer-Aided Design (FMCAD), Mountain View, CA, USA, 3–6 October 2016; pp. 117–124. [Google Scholar]
- Halbwachs, N.; Caspi, P.; Raymond, P.; Pilaud, D. The synchronous data flow programming language LUSTRE. Proc. IEEE 1991, 79, 1305–1320. [Google Scholar] [CrossRef]
- Gollakota, S.; Hassanieh, H.; Ransford, B.; Katabi, D.; Fu, K. They can hear your heartbeats: Non-invasive security for implantable medical devices. In Proceedings of the ACM SIGCOMM Conference, Toronto, ON, Canada, 15–19 August 2011; pp. 2–13. [Google Scholar]
| Date | Country | Name | Description |
|---|---|---|---|
| August 2011 | United States | Medtronic insulin-delivery system | Hacked the insulin pump and completely disabled it [7] |
| 2008 | United States | Cardiac defibrillator | Hacked cardiac defibrillatorto change the device’s settings, ordering it to deliver a shock, and disabling it [7] |
| 2017 | United Kingdom | 16 United Kingdom hospitals | Freezing systems and encrypting files [8] |
| 2014 | United States | Boston Children’s Hospital | Caused the hospital network to lose internet access using distributed Denial of Service (DoS) attack [9] |
| January, 2015 | United States | Anthem | Breached a database with 80 million customers records [10] |
| July, 2018 | England | National Health Service (NHS) | A data breach caused the NHS to share confidential health data of 150,000 patients [11] |
| June, 2018 | Singapore | SingHealth | The data of 1.5 million patients were stolen [12] |
| 2019 | United States | NeuroSky 156 brain–computer interface application | Victims’ brain wave data were stolen [13] |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ibrahim, M.; Alsheikh, A.; Matar, A. Attack Graph Modeling for Implantable Pacemaker. Biosensors 2020, 10, 14. https://doi.org/10.3390/bios10020014
Ibrahim M, Alsheikh A, Matar A. Attack Graph Modeling for Implantable Pacemaker. Biosensors. 2020; 10(2):14. https://doi.org/10.3390/bios10020014
Chicago/Turabian StyleIbrahim, Mariam, Ahmad Alsheikh, and Aseel Matar. 2020. "Attack Graph Modeling for Implantable Pacemaker" Biosensors 10, no. 2: 14. https://doi.org/10.3390/bios10020014
APA StyleIbrahim, M., Alsheikh, A., & Matar, A. (2020). Attack Graph Modeling for Implantable Pacemaker. Biosensors, 10(2), 14. https://doi.org/10.3390/bios10020014





