Another Step in the Ladder of DNS-Based Covert Channels: Hiding Ill-Disposed Information in DNSKEY RRs
Abstract
1. Introduction
2. DNS as a Covert Channel
2.1. DNS-Based C&C
2.2. DNS Tunneling
2.3. Fileless Malware
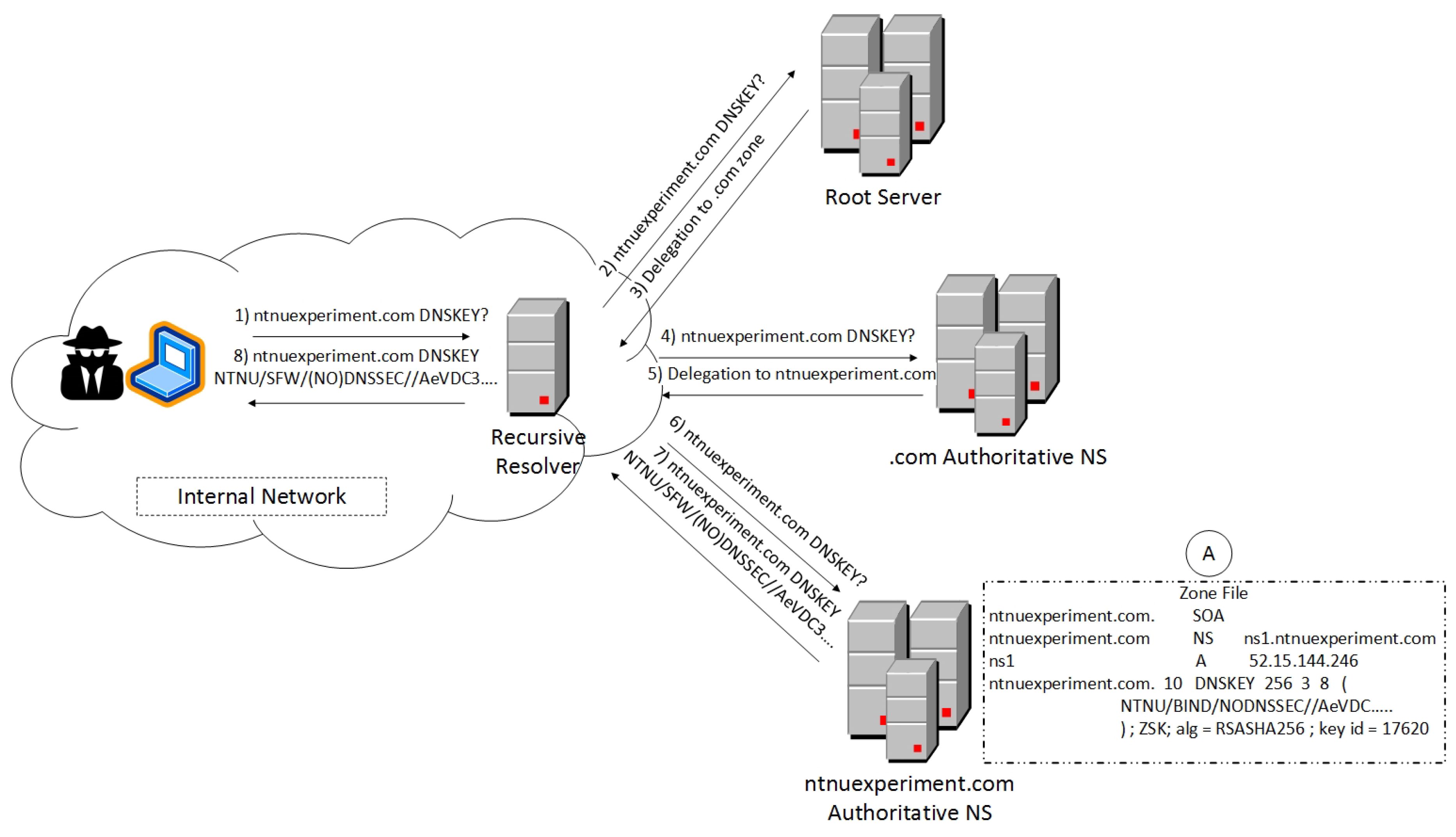
3. Proposed Architecture: DNSKEY as a Covert C&C Channel
3.1. Threat Model
3.2. Covert Channel
4. Implementation and Results

5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| ANS | Authoritative NameServer |
| C&C | Command and Control |
| DDoS | Distributed Denial of Service |
| DNS | Domain Name System |
| DNSSEC | DNS Security extention |
| DoS | Denial of Service |
| DS | Delegation Signer |
| KSK | Key Signing Key |
| NS | NameServer |
| RR | Resource Record |
| RDATA | Resource Data |
| ZSK | Zone Signing Key |
| VM | Virtual Machine |
References
- Arends, R.; Austein, R.; Larson, M.; Massey, D.; Rose, S. RFC 4033: DNS Security Introduction and Requirements. 2005. RFC Editor. Available online: https://tools.ietf.org/html/rfc4033 (accessed on 17 July 2019).
- Nadler, A.; Aminov, A.; Shabtai, A. Detection of malicious and low throughput data exfiltration over the DNS protocol. Comput. Secur. 2019, 80, 36–53. [Google Scholar] [CrossRef]
- Williamson, D. Protecting Networks from DNS Exfiltration. 2017. Help Net Security. Available online: https://www.helpnetsecurity.com/2017/10/02/dns-exfiltration/ (accessed on 17 July 2019).
- Kara, A.M.; Binsalleeh, H.; Mannan, M.; Youssef, A.; Debbabi, M. Detection of malicious payload distribution channels in DNS. In Proceedings of the 2014 IEEE International Conference on Communications (ICC), Sydney, Australia, 10–14 June 2014; pp. 853–858. [Google Scholar]
- Mullaney, C. Morto Worm Sets a (DNS) Record. 2011. Symantec. Available online: https://www.symantec.com/connect/blogs/morto-worm-sets-dns-record (accessed on 17 July 2019).
- Ahmed, J.; Gharakheili, H.H.; Raza, Q.; Russell, C.; Sivaraman, V. Real-Time Detection of DNS Exfiltration and Tunneling from Enterprise Networks. In Proceedings of the 2019 IFIP/IEEE Symposium on Integrated Network and Service Management (IM), Washington, DC, USA, 8–12 April 2019; pp. 649–653. [Google Scholar]
- Brumaghin, E.; Grady, C. Covert Channels and Poor Decisions: The Tale of DNSMessenger. 2017. Talos. Available online: https://blog.talosintelligence.com/2017/03/dnsmessenger.html (accessed on 17 July 2019).
- Kitterman, S. RFC 7208: Sender Policy Framework (SPF) for Authorizing Use of Domains in Email. 2014. RFC Editor. Available online: https://tools.ietf.org/html/rfc7208 (accessed on 17 July 2019).
- Mockapetris, P. RFC 1035: Domain Names—Implementation and Specification. 1987. RFC Editor. Available online: https://www.ietf.org/rfc/rfc1035.txt (accessed on 17 July 2019).
- Anagnostopoulos, M.; Kambourakis, G.; Kopanos, P.; Louloudakis, G.; Gritzalis, S. DNS Amplification Attack Revisited. Comput. Secur. 2013, 39, 475–485. [Google Scholar] [CrossRef]
- Ianelli, N.; Hackworth, A. Botnets as a Vehicle for Online Crime; White Paper; CERT Coordination Center: Pittsburgh, PA, USA, 2005. [Google Scholar]
- Anagnostopoulos, M.; Kambourakis, G.; Drakatos, P.; Karavolos, M.; Kotsilitis, S.; Yau, D. Botnet Command and Control Architectures Revisited: Tor Hidden Services and Fluxing. In Proceedings of the Web Information Systems Engineering (WISE 2017), Puschino, Russia, 7–11 October 2017. [Google Scholar]
- Anagnostopoulos, M.; Kambourakis, G.; Gritzalis, S. New facets of mobile botnet: architecture and evaluation. Int. J. Inf. Secur. 2015, 15, 455–473. [Google Scholar] [CrossRef]
- Nussbaum, L.; Neyron, P.; Richard, O. On Robust Covert Channels Inside DNS. In Proceedings of the 24th IFIP TC 11 International Information Security Conference (SEC 2009); Springer: Berlin/Heidelberg, Germany, 2009; pp. 51–62. [Google Scholar]
- Dietrich, C.J.; Rossow, C.; Freiling, F.C.; Bos, H.; van Steen, M.V.; Pohlmann, N. On Botnets That Use DNS for Command and Control. In Proceedings of the Seventh European Conference on Computer Network Defense (EC2ND), Gothenburg, Sweden, 6–7 September 2011; pp. 9–16. [Google Scholar]
- Xu, K.; Butler, P.; Saha, S.; Yao, D. DNS for Massive-Scale Command and Control. IEEE Trans. Depend. Secur. Comput. 2013, 10, 143–153. [Google Scholar] [CrossRef]
- Mansfield-Devine, S. Fileless attacks: Compromising targets without malware. Netw. Secur. 2017, 2017, 7–11. [Google Scholar] [CrossRef]
- Yadav, S.; Reddy, A.K.K.; Reddy, A.N.; Ranjan, S. Detecting Algorithmically Generated Malicious Domain Names. In Proceedings of the 10th ACM SIGCOMM IMC ’10, Melbourne, Australia, 1–3 November 2010; pp. 48–61. [Google Scholar]
- Internet Systems Consortium; BIND 9. Available online: https://www.isc.org/bind/ (accessed on 17 July 2019).
- NLnet Labs; Name Server Daemon (NSD). Available online: https://www.nlnetlabs.nl/projects/nsd/about/ (accessed on 17 July 2019).
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Anagnostopoulos, M.; Seem, J.A. Another Step in the Ladder of DNS-Based Covert Channels: Hiding Ill-Disposed Information in DNSKEY RRs. Information 2019, 10, 284. https://doi.org/10.3390/info10090284
Anagnostopoulos M, Seem JA. Another Step in the Ladder of DNS-Based Covert Channels: Hiding Ill-Disposed Information in DNSKEY RRs. Information. 2019; 10(9):284. https://doi.org/10.3390/info10090284
Chicago/Turabian StyleAnagnostopoulos, Marios, and John André Seem. 2019. "Another Step in the Ladder of DNS-Based Covert Channels: Hiding Ill-Disposed Information in DNSKEY RRs" Information 10, no. 9: 284. https://doi.org/10.3390/info10090284
APA StyleAnagnostopoulos, M., & Seem, J. A. (2019). Another Step in the Ladder of DNS-Based Covert Channels: Hiding Ill-Disposed Information in DNSKEY RRs. Information, 10(9), 284. https://doi.org/10.3390/info10090284




