An Efficient Dummy-Based Location Privacy-Preserving Scheme for Internet of Things Services
Abstract
1. Introduction
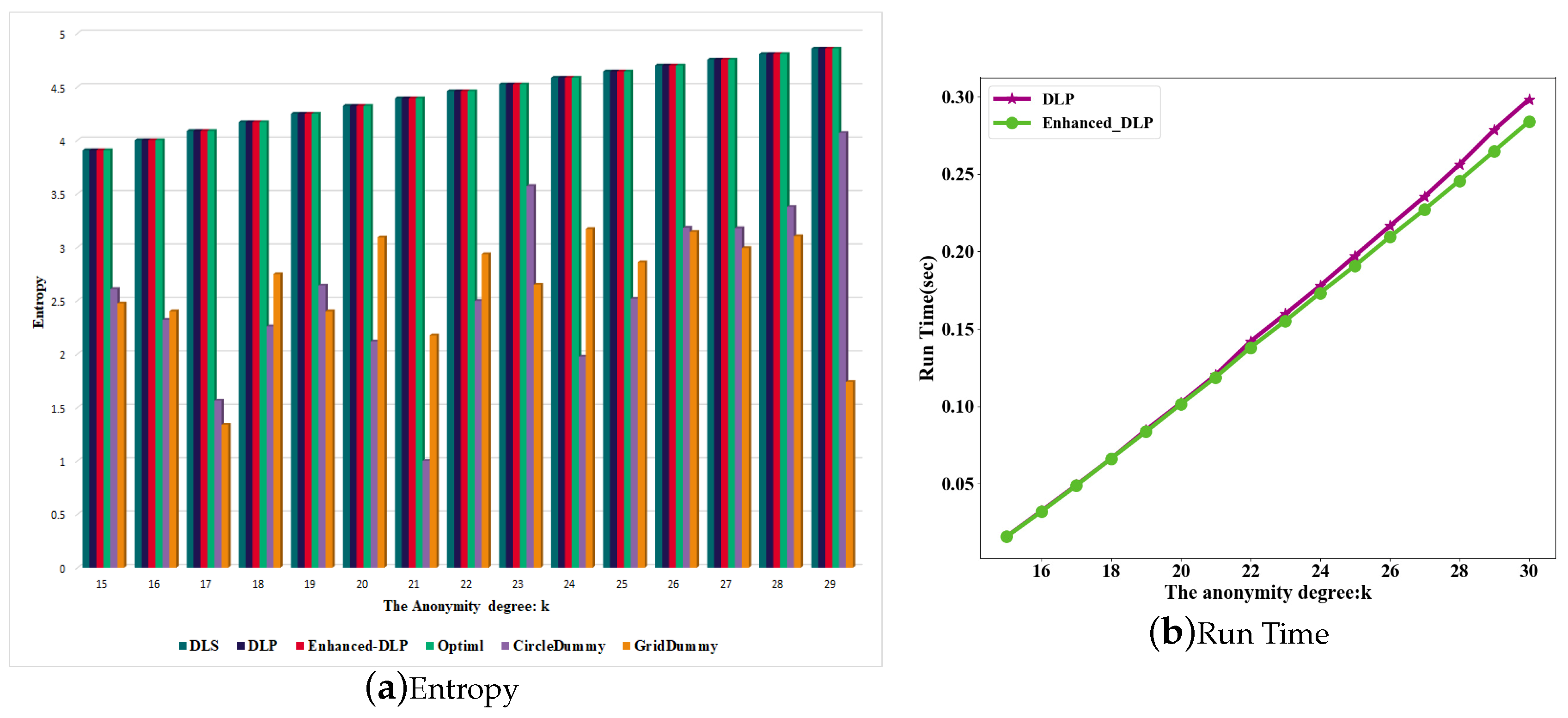
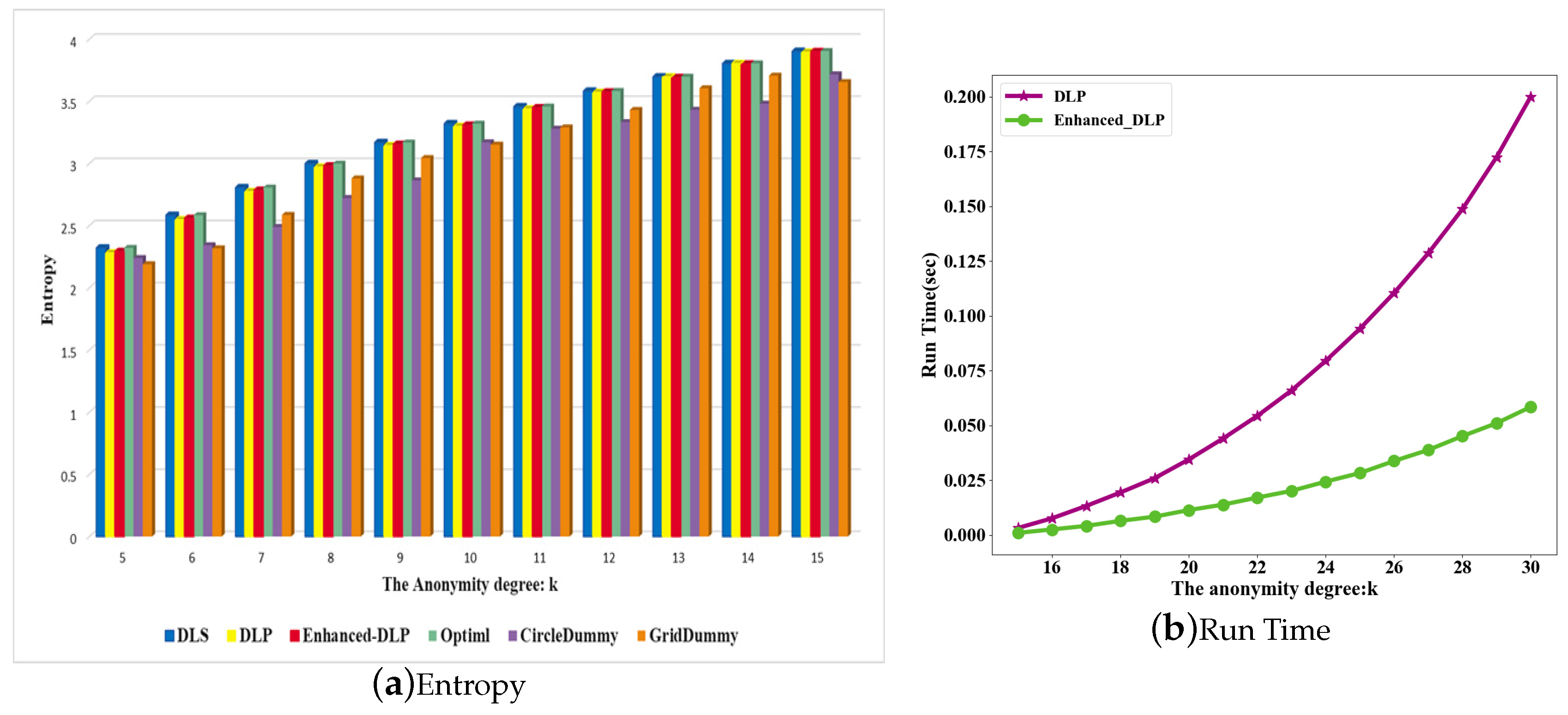
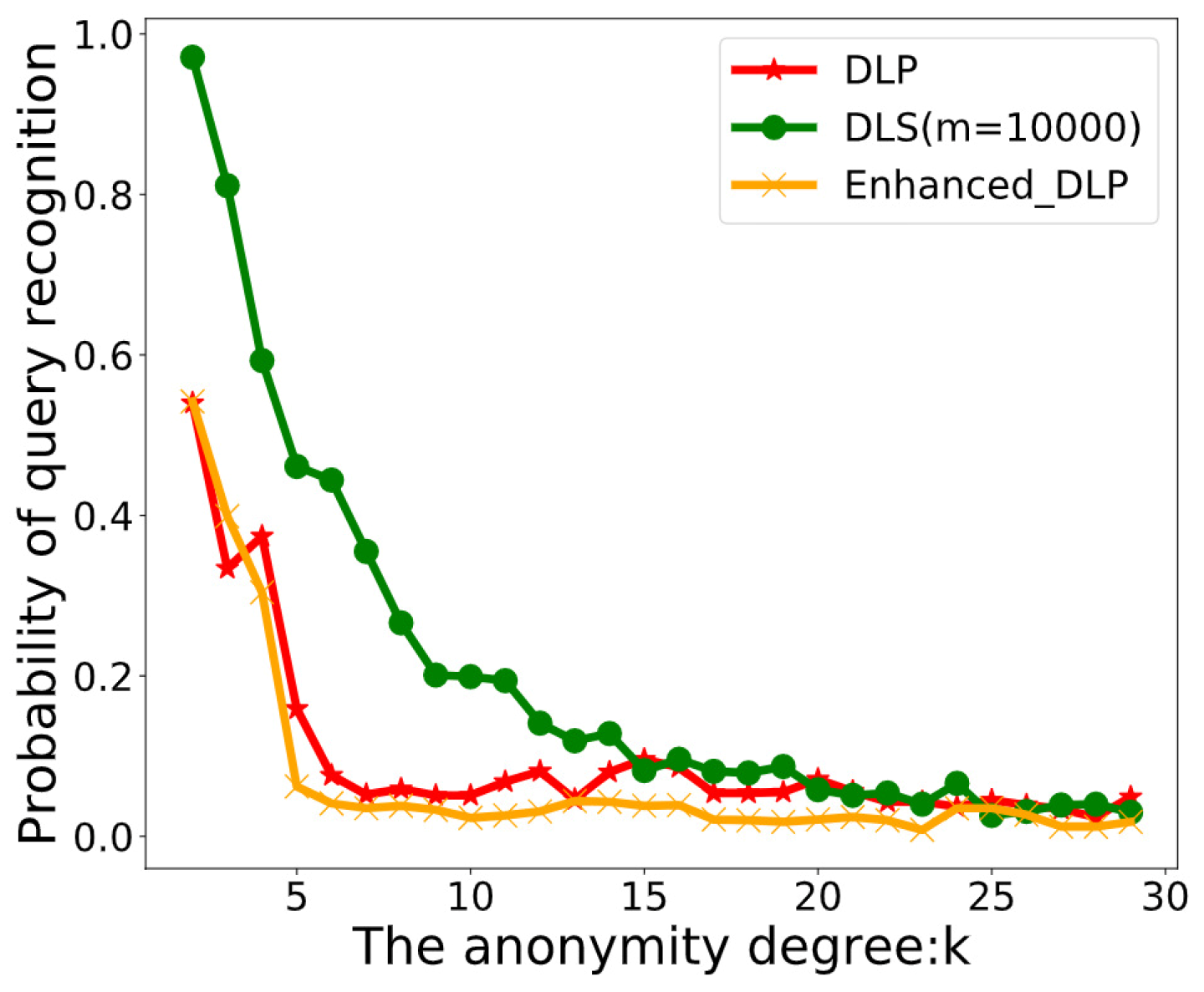
- The dummy-based privacy protection scheme is a privacy protection scheme without a third trusted party, and is more suitable for the IoT environment. In this paper, we propose an enhanced greedy manner to improve the existing dummy-based location selection scheme (such as DLP) and improve the efficiency of dummy location generation. Compared with the DLP scheme, the dummy location generation time of our scheme is reduced by 68.14%.
- The Enhanced-DLP scheme enhances the user’s privacy protection, making it difficult for an attacker to distinguish the user’s real location from the anonymous set. Compared with the DLP scheme, the probability of our scheme revealing the user’s real position is reduced by 33.63% under the same attack conditions.
2. Preliminaries
2.1. Side Information
2.2. The Entropy-Based Privacy Measurement Method
2.3. Review the Dummy-Based Location Privacy-Preserving Scheme
- A user needs to give the degree of anonymity k.
- The DLP scheme needs to obtain the historical query probability of all locations and sort them in ascending order. Then, the DLP scheme calculates the number of locations (denoted as N) with the same historical query probability of the user’s location (denoted as p). The anonymous set of the user is denoted as C.
- If , the DLP scheme arbitrarily selects locations whose query probability is the same as p from N locations and user location p to form an anonymous set C.
- If , the DLP scheme selects locations with the same query probability as the user location p from the sorted list and puts them into C. The DLP scheme selects locations that are the most similar to the user’s location p as a candidate set (denoted as S). The DLP scheme uses the greedy scheme times to find dummy locations from S, and also puts them into C to form the anonymous set.
- If , the DLP scheme chooses locations less than, and locations greater than the real location to form a candidate set from the sorted list (denoted as ). Then, the DLP arbitrarily selects one location from and puts the location and the user’s real location into C. The DLP scheme uses the greedy scheme times to find dummy locations and puts them into C to form an anonymous set.
- Finally, the optimal anonymous set C is found.
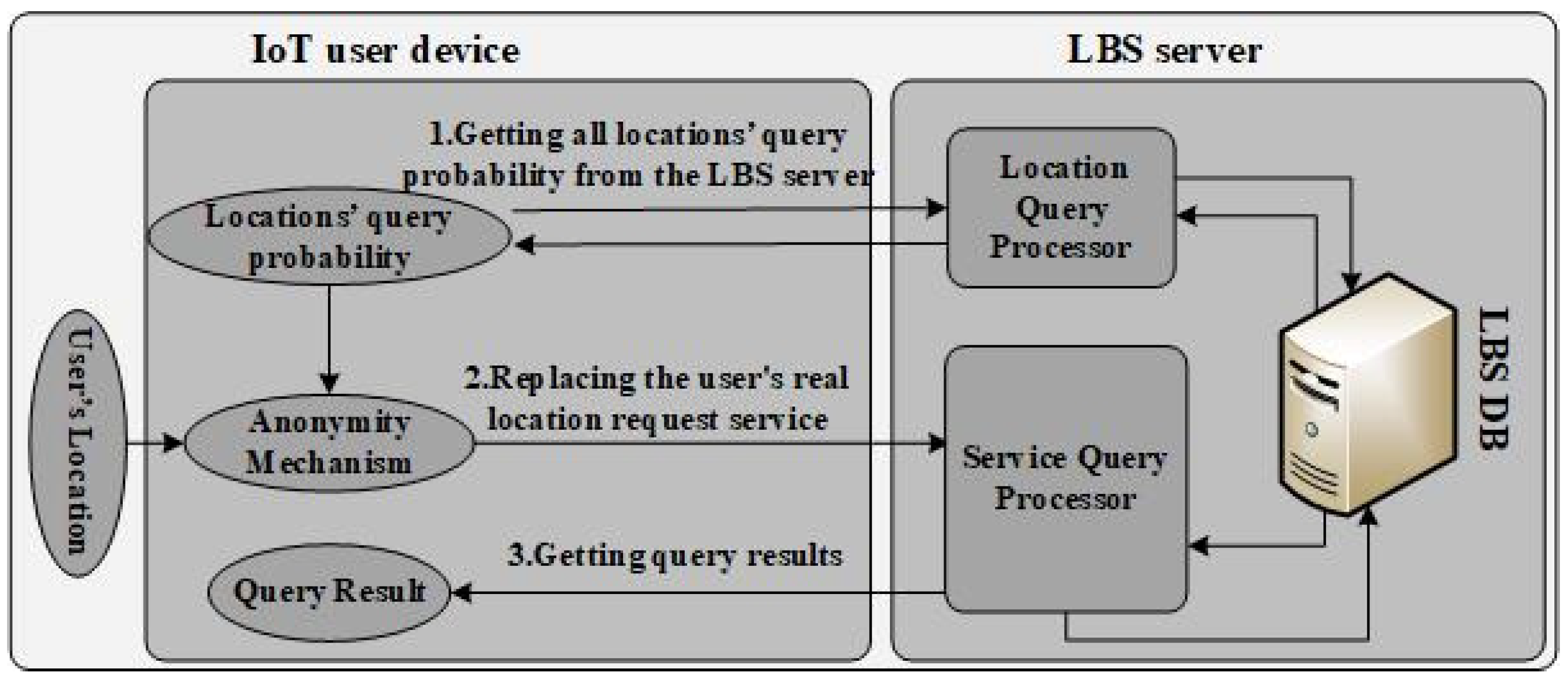
2.4. System Model
- The LBS server: The LBS server receives the location service request from the user devices, and then searches the requested service in the LBS database and sends the search results back to the user. The LBS server contains various types of service databases and provides users with diverse services. Moreover, the server may also count the probability of each user’s query at all locations when providing service information for each user according to the location.
- The IoT user device: The IoT user device is a typical part of the location service system, which usually obtains user location information through a GPS module embedded in the device (e.g., a smartphone). The IoT device obtains the corresponding high-quality location service by sending its high-precision location information to the LBS server. In order to prevent the user’s location information from being used twice, the location information submitted to the LBS server should include the accurate location and dummy location, which ensures that the LBS server is not able to obtain the user’s real location.
2.5. Attack Model
3. Enhanced-DLP Scheme
3.1. The Basic Idea of the Enhanced-DLP Scheme
- In the beginning, a user sets the value of the privacy degree k according to the privacy requirement. Then, the Enhanced-DLP obtains all the historical query probability of all locations on the LBS server and sorts them in ascending order according to the historical query probability (denoted as S). Let p denote the query probability of the user’s real location, and let C denote the final anonymous set.
- The Enhanced-DLP scheme counts the number of locations that have the same historical query probability as p in set S, which is denoted by .
- If size () ≥ k, then the Enhanced-DLP randomly selects locations that have the same historical query probabilities as the user’s location p from and puts them into C. Then, the Enhanced-DLP randomly inserts the user’s real location p into C.
- If 1 < size() <k, the Enhanced-DLP scheme puts each location in and user’s location p into C. Then, the Enhanced-DLP selects -2 candidate locations (denoted as set D), in which locations are less than the p and the other locations are greater than the p in the set S.Otherwise, it goes to Step (7).
- The Enhanced-DLP finds the location maximum with query probability (denoted as ) and location with minimum query probability (denoted as ) from set C. The Enhanced-DLP finds two locations in set D, which is the location with the maximum query probability less than (denoted by ), and the other is the location minimum query probability being greater than (denoted by ). Then, the Enhanced-DLP needs to calculate and according to Equation (3) and add the location into set C, to attempt to achieve max entropy in set C.
- Repeat Step (5) while the size of anonymity set C is less than k.
- If size () ≤ 1, the Enhanced-DLP chooses locations less than P and other locations greater than the p as candidate locations from the sorted set S and denoted as . Both and are set by users based on their privacy requirements, and is greater than . Then, the Enhanced-DLP randomly gets one location from as a dummy location, and puts this location and the user’s location p into C.
- In order to meet the requirements of k-anonymity, the Enhanced-DLP selects other locations from . For the location that Enhanced-DLP selected, The Enhanced DLP must make sure that is the largest of the remaining positions in set .
- If the size of set C < k. Repeat Step (8).And then outputs the anonymous set C.
| Algorithm 1 Enhanced-DLP algorithm. |
|
3.2. Security Analysis
- Resistance to the Colluding Attack
- Resistance to a Side Information Inference Attack
4. Experimental Results and Analysis
5. Related Work
5.1. Privacy Protection and Security in the Internet of Things
5.2. LBS Location Anonymous Scheme
5.3. Dummy-Based Location Selection in the Internet of Things Privacy Protection
6. Discussion
6.1. Limitations of Our Scheme
6.2. Threats-to-Validity
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| POI | point of interest |
| LBS | Location-based services |
| LSP | Location-based services providers |
| DLS | Dummy location selection |
| DLP | dummy-based location privacy-preserving |
| ADLS | Attack algorithm for DLS |
| Enhanced-DLP | Enhanced dummy-based location privacy-preserving |
| CPAL | conditional privacy protection authentication with access link |
| SRR | sector-based random routing |
| MEC | multi-access edge computing |
| MSS | mobility support system |
| CR | cloaking region |
| TTP | trusted third party |
| DDP | dual privacy preserving |
| RDG | robust dummy generation |
References
- Statista Inc. Internet of Things (IoT) Connected Devices Installed Base Worldwide from 2015 to 2025 (In Billions). Available online: https://www.statista.com/statistics/471264/iot-number-of-connected-devices-worldwide/ (accessed on 30 August 2019).
- Ironpaper, Growth Agency. Internet of Things Market Statistics-2016. Available online: https://www.ironpaper.com (accessed on 30 August 2019).
- Chen, L.; Thombre, S.; Järvinen, K.; Lohan, E.S.; Alén-Savikko, A.; Leppäkoski, H.; Bhuiyan, M.Z.H.; Bu-Pasha, S.; Ferrara, G.N.; Honkala, S.; et al. Robustness, Security and Privacy in Location-Based Services for Future IoT: A Survey. IEEE Access 2017, 5, 8956–8977. [Google Scholar] [CrossRef]
- Zhang, X.J.; Gui, X.L.; Wu, Z.D. Privacy preservation for location-based services: A survey. Ruan Jian Xue Bao/J. Softw. 2015, 26, 2373–2395. (In Chinese) [Google Scholar]
- Zhu, X.; Chi, H.; Niu, B.; Zhang, W.; Li, Z.; Li, H. MobiCache: When k-anonymity meets cache. In Proceedings of the 2013 IEEE Global Communication and Information System Security Symposium (GLOBECOM), Atlanta, GA, USA, 9–13 December 2013; pp. 820–825. [Google Scholar]
- Sun, G.; Song, L.; Liao, D.; Yu, H.; Chang, V. Towards privacy preservation for “check-in” services in location-based social networks. Inf. Sci. 2019, 481, 616–634. [Google Scholar] [CrossRef]
- Liu, X.; Liu, K.; Guo, L.; Li, X.; Fang, Y. A game-theoretic approach for achieving k-anonymity in Location Based Services. In Proceedings of the 2013 Proceedings IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 2985–2993. [Google Scholar]
- Niu, B.; Li, Q.; Zhu, X.; Cao, G.; Li, H. Achieving k-anonymity in privacy-aware location-based services. In Proceedings of the IEEE INFOCOM 2014—IEEE Conference on Computer Communications, Toronto, ON, Canada, 27 April–2 May 2014; pp. 754–762. [Google Scholar]
- Sun, G.; Chang, V.; Ramachandran, M.; Sun, Z.; Li, G.; Yu, H.; Liao, D. Efficient location privacy algorithm for Internet of Things (IoT) services and applications. J. Netw. Comput. Appl. 2017, 89, 3–13. [Google Scholar] [CrossRef]
- Ma, C.Y.; Yau, D.K.; Yip, N.K.; Rao, N.S. Privacy Vulnerability of Published Anonymous Mobility Traces. IEEE/ACM Trans. Netw. 2013, 21, 720–733. [Google Scholar] [CrossRef]
- Serjantov, A.; Danezis, G. Towards an information theoretic metric for anonymity. In Privacy Enhancing Technologies; Springer: Berlin, Germany, 2002; pp. 41–53. [Google Scholar]
- Pingley, A.; Zhang, N.; Fu, X.; Choi, H.; Subramaniam, S.; Zhao, W. Protection of query privacy for continuous location-based services. In Proceedings of the 2011 IEEE INFOCOM, Shanghai, China, 10–15 April 2011; pp. 1710–1718. [Google Scholar]
- Zhang, X.; Huang, H.; Huang, S.; Chen, Q.; Ju, T.; Du, X. A Context-Aware Location Differential Perturbation Scheme for Privacy-Aware Users in Mobile Environment. Wirel. Commun. Mob. Comput. 2018, 2018, 9173519. [Google Scholar] [CrossRef]
- Lu, H.; Jensen, C.; Yiu, M. PAD: Privacy-area aware, dummy based location privacy in mobile services. In Proceedings of the Seventh ACM International Workshop on Data Engineering for Wireless and Mobile Access, Vancouver, BC, Canada, 13 June 2008; pp. 16–23. [Google Scholar]
- Henze, M.; Hermerschmidt, L.; Kerpen, D.; Häußling, R.; Rumpe, B.; Wehrle, K. A comprehensive approach to privacy in the cloud-based Internet of Things. Future Gener. Comput. Syst. 2016, 56, 701–718. [Google Scholar] [CrossRef]
- Appavoo, P.; Chan, M.C.; Bhojan, A.; Chang, E.C. Efficient and privacy-preserving access to sensor data for Internet of Things (IoT) based services. In Proceedings of the IEEE International Conference on Communication Systems and Networks, Bangalore, India, 5–10 January 2016; pp. 1–8. [Google Scholar]
- Jin, J.; Gubbi, J.; Marusic, S.; Palaniswami, M. An Information Framework for Creating a Smart City Through Internet of Things. IEEE Internet Things J. 2014, 1, 112–121. [Google Scholar] [CrossRef]
- Lai, C.; Li, H.; Liang, X.; Lu, R.; Zhang, K.; Shen, X. CPAL: A Conditional Privacy-Preserving Authentication With Access Linkability for Roaming Service. IEEE Internet of Things J. 2014, 1, 46–57. [Google Scholar] [CrossRef]
- Premnath, S.; Haas, Z. Security and privacy in the internet-of-things under time-and-budget-limited adversary mode. IEEE Wirel. Commun. Lett. 2015, 4, 277–280. [Google Scholar] [CrossRef]
- Wu, Q.; Liu, H.; Zhang, C.; Fan, Q.; Li, Z.; Wang, K. Trajectory Protection Schemes Based on a Gravity Mobility Model in IoT. Electronics 2019, 8, 148. [Google Scholar] [CrossRef]
- Yin, C.; Xi, J.; Sun, R.; Wang, J. Location Privacy Protection Based on Differential Privacy Strategy for Big Data in Industrial Internet of Things. IEEE Trans. Ind. Inform. 2018, 14, 3628–3636. [Google Scholar] [CrossRef]
- Song, W.T.; Hu, B.; Zhao, X.F. Privacy Protection of IoT Based on Fully Homomorphic Encryption. Wirel. Commun. Mob. Comput. 2018, 2018, 5787930. [Google Scholar] [CrossRef]
- Sfar, A.R.; Challal, Y.; Moyal, P.; Natalizio, E. A Game Theoretic Approach for Privacy Preserving Model in IoT-Based Transportation. IEEE Trans. Intell. Transp. Syst. 2019. [Google Scholar] [CrossRef]
- He, Y.; Han, G.; Wang, H.; Ansere, J.A.; Zhang, W. A sector-based random routing scheme for protecting the source location privacy in WSNs for the Internet of Things. Future Gener. Comput. Syst. 2019, 96, 438–448. [Google Scholar] [CrossRef]
- Ravidas, S.; Lekidis, A.; Paci, F.; Zannone, N. Access control in Internet-of-Things: A survey. J. Netw. Comput. Appl. 2019, 144, 79–101. [Google Scholar] [CrossRef]
- Venckauskas, A.; Stuikys, V.; Damasevicius, R.; Jusas, N. Modelling of Internet of Things units for estimating security-energy-performance relationships for quality of service and environment awareness. Secur. Commun. Netw. 2016, 9, 3324–3339. [Google Scholar] [CrossRef]
- Zhang, P.; Durresi, M.; Durresi, A. Multi-access edge computing aided mobility for privacy protection in internet of things. Computing 2019, 101, 729–742. [Google Scholar] [CrossRef]
- Gedik, B.; Liu, L. Protecting Location Privacy with Personalized k-Anonymity: Architecture and Algorithms. IEEE Trans. Mob. Comput. 2008, 7, 1–18. [Google Scholar] [CrossRef]
- Ying, B.; Makrakis, D. Protecting Location Privacy with Clustering Anonymization in vehicular networks. In Proceedings of the 2014 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Toronto, ON, Canada, 27 April–2 May 2014; pp. 305–310. [Google Scholar]
- Hossain, A.; Jang, S.; Chang, J. Privacy-aware cloaking technique in location-based services. In Proceedings of the IEEE First International Conference on MobileServices, Honolulu, HI, USA, 24–29 June 2012; pp. 9–16. [Google Scholar]
- Zhang, S.; Choo, K.K.R.; Liu, Q.; Wang, G. Enhancing privacy through uniform grid and caching in location-based services. Future Gener. Comput. Syst. 2018, 86, 881–892. [Google Scholar] [CrossRef]
- Sun, R.; Xi, J.; Yin, C.; Wang, J.; Kim, G.J. Location Privacy Protection Research Based on Querying Anonymous Region Construction for Smart Campus. Mob. Inf. Syst. 2018, 2018, 3682382. [Google Scholar] [CrossRef]
- Wu, H.; Li, M.; Zhang, H. Enabling Smart Anonymity Scheme for Security Collaborative Enhancement in Location-Based Services. IEEE Access 2019, 7, 50031–50040. [Google Scholar] [CrossRef]
- Zhang, S.; Wang, G.; Bhuiyan, M.Z.A.; Liu, Q. A Dual Privacy Preserving Scheme in Continuous Location-Based Services. IEEE Internet Things J. 2018, 5, 4191–4200. [Google Scholar] [CrossRef]
- Shaham, S.; Ding, M.; Liu, B.; Lin, Z.; Li, J. Privacy Preservation in Location-Based Services: A Novel Metric and Attack Model. arXiv 2018, arXiv:1805.06104. [Google Scholar]
| Scheme | Anonymity Degree: k | |||
|---|---|---|---|---|
| k = 15 | k = 20 | k = 25 | k = 29 | |
| DLP | 0.019 s | 0.117 s | 0.217 | 0.298 s |
| DLS | 0.431 s | 3.184 s | 6.870 s | 10.553 s |
| CircleDummy | 1.236 s | 9.003 s | 19.316 s | 29.604 s |
| GridDummy | 0.00003 s | 0.0002 s | 0.0004 s | 0.0006 s |
| Enhanced-DLP | 0.018 s | 0.116 s | 0.215 s | 0.295 s |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Du, Y.; Cai, G.; Zhang, X.; Liu, T.; Jiang, J. An Efficient Dummy-Based Location Privacy-Preserving Scheme for Internet of Things Services. Information 2019, 10, 278. https://doi.org/10.3390/info10090278
Du Y, Cai G, Zhang X, Liu T, Jiang J. An Efficient Dummy-Based Location Privacy-Preserving Scheme for Internet of Things Services. Information. 2019; 10(9):278. https://doi.org/10.3390/info10090278
Chicago/Turabian StyleDu, Yongwen, Gang Cai, Xuejun Zhang, Ting Liu, and Jinghua Jiang. 2019. "An Efficient Dummy-Based Location Privacy-Preserving Scheme for Internet of Things Services" Information 10, no. 9: 278. https://doi.org/10.3390/info10090278
APA StyleDu, Y., Cai, G., Zhang, X., Liu, T., & Jiang, J. (2019). An Efficient Dummy-Based Location Privacy-Preserving Scheme for Internet of Things Services. Information, 10(9), 278. https://doi.org/10.3390/info10090278





