Energy-Efficient Collision Avoidance MAC Protocols for Underwater Sensor Networks: Survey and Challenges
Abstract
:1. Introduction
2. Characteristics of Underwater Sensor Networks
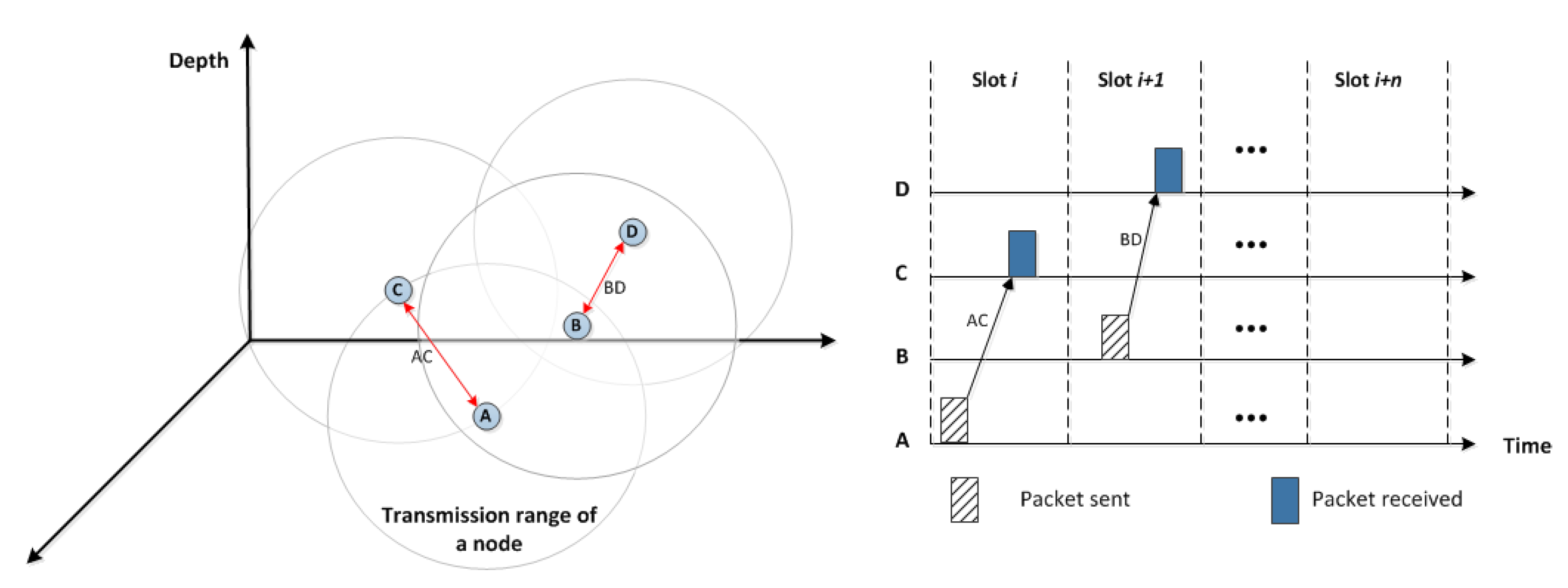
2.1. Node Movement in Three-Dimensionality Area
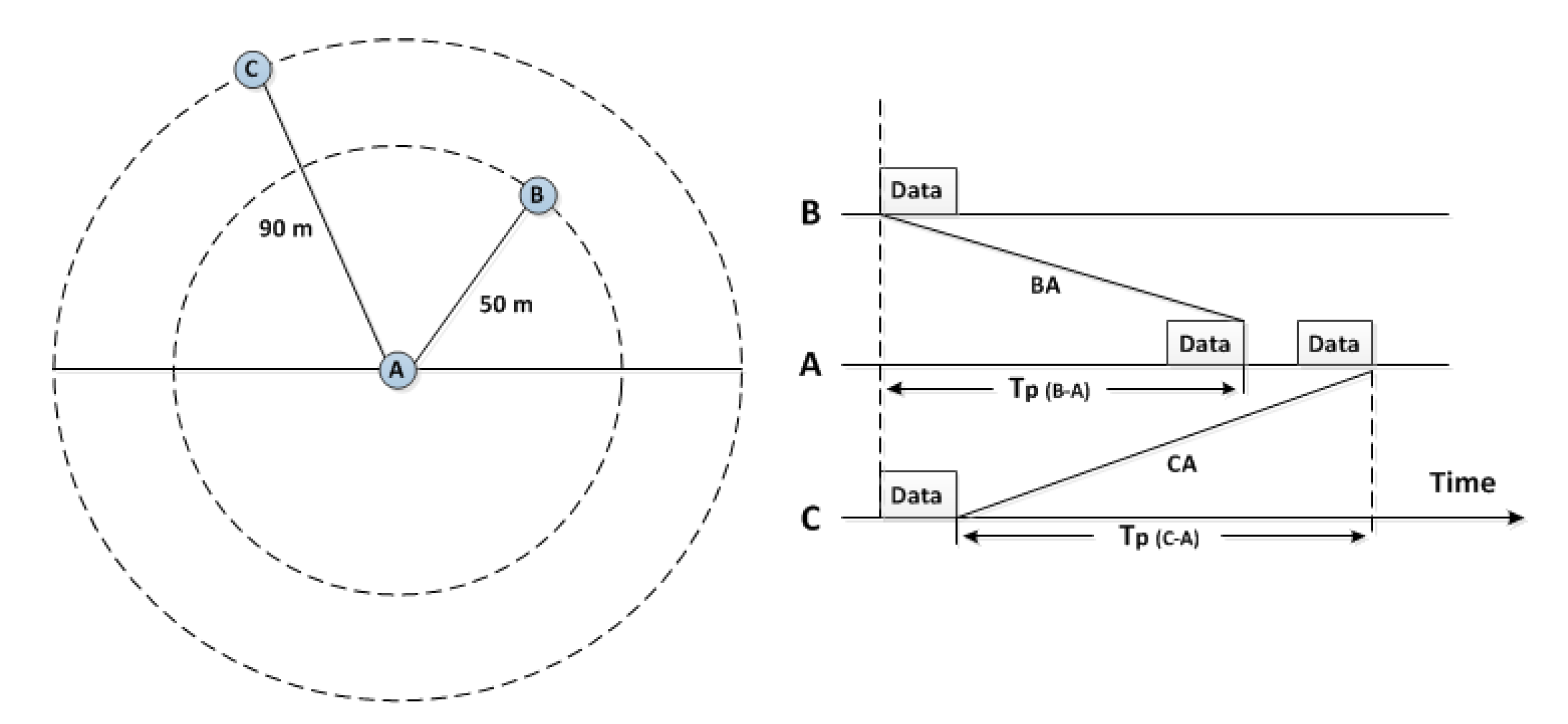
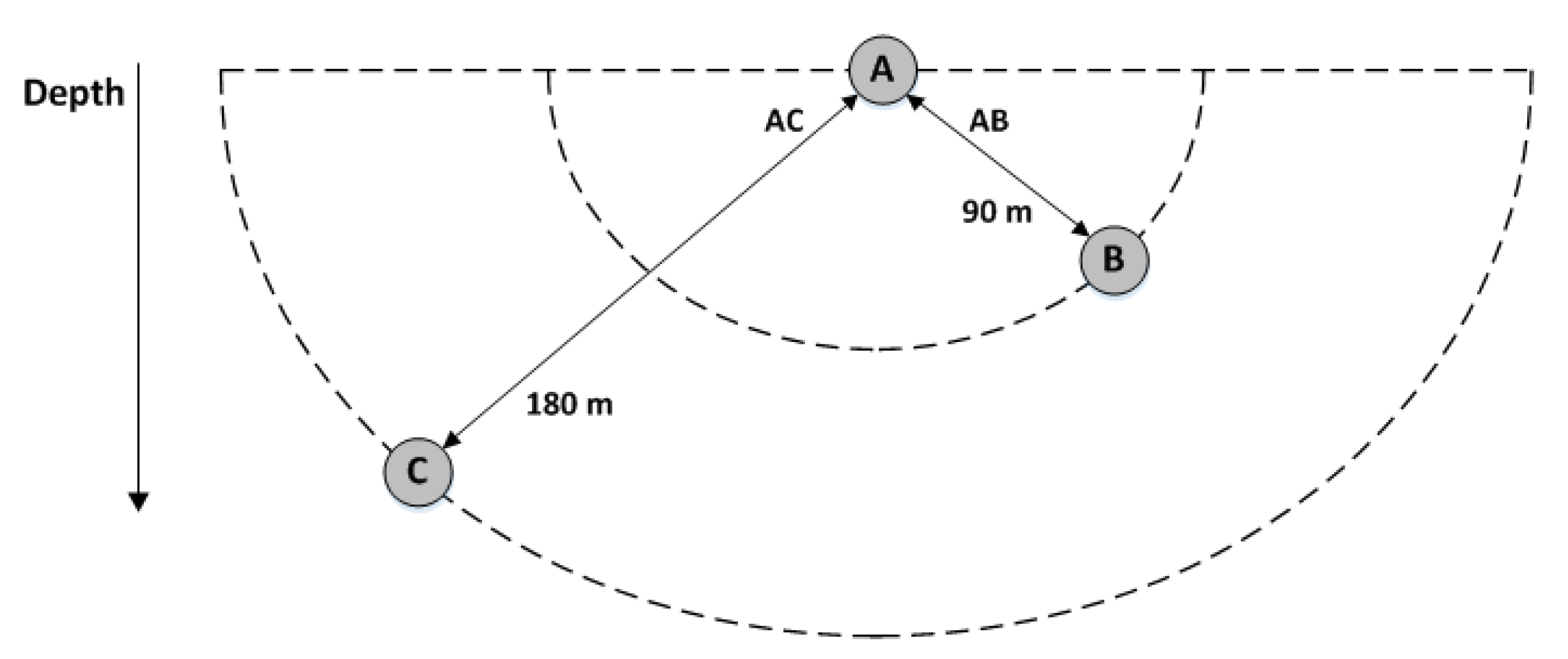
2.2. Impact of High Propagation Delays on MAC Protocols
2.3. Impacts of Low Available Bandwidth on MAC Protocols
2.4. Acoustic Noises
2.5. Path Loss
2.6. High Energy Cost
3. Problem Definition and Challenges
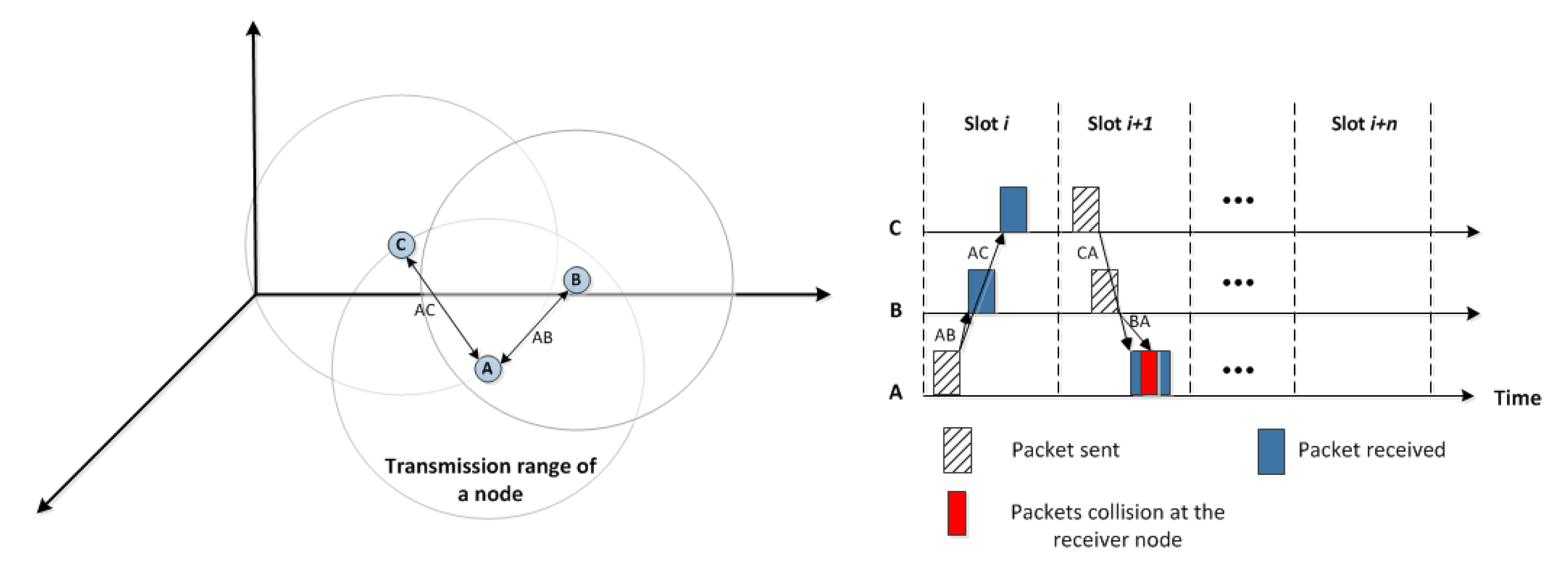
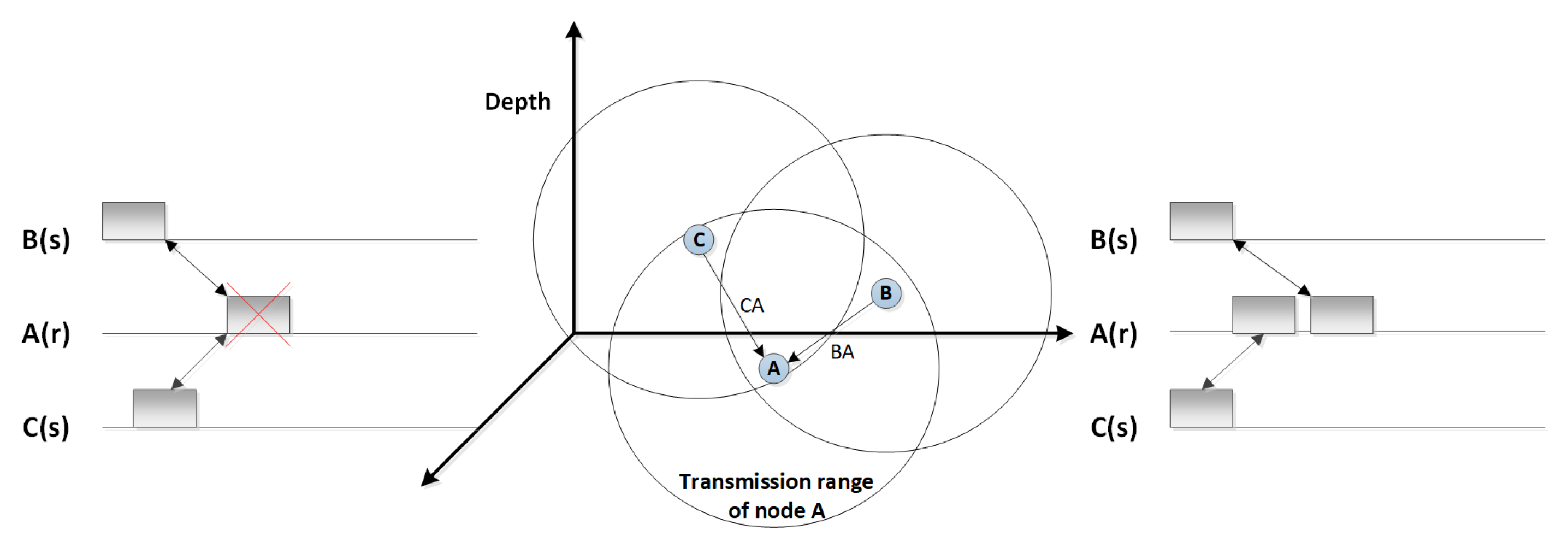
3.1. Hidden Terminal Problem
3.2. Exposed Terminal Problem
3.3. Spatial-Temporal Uncertainty Problem
- If a collision occurred at the receiver node, it would be depending on the sending time and the propagation delay between the sender and the receiver sensors. This is known as a duality that differs between the sending time and the location of the sensor nodes.
- Different distances among the underwater sensor nodes leads to uncertainty based on the current channel status, and a packet collision can be occurred even if there is no other node transmitting at the same time.
3.4. Near and Far Problem
3.5. Synchronisation
3.6. Centralisation
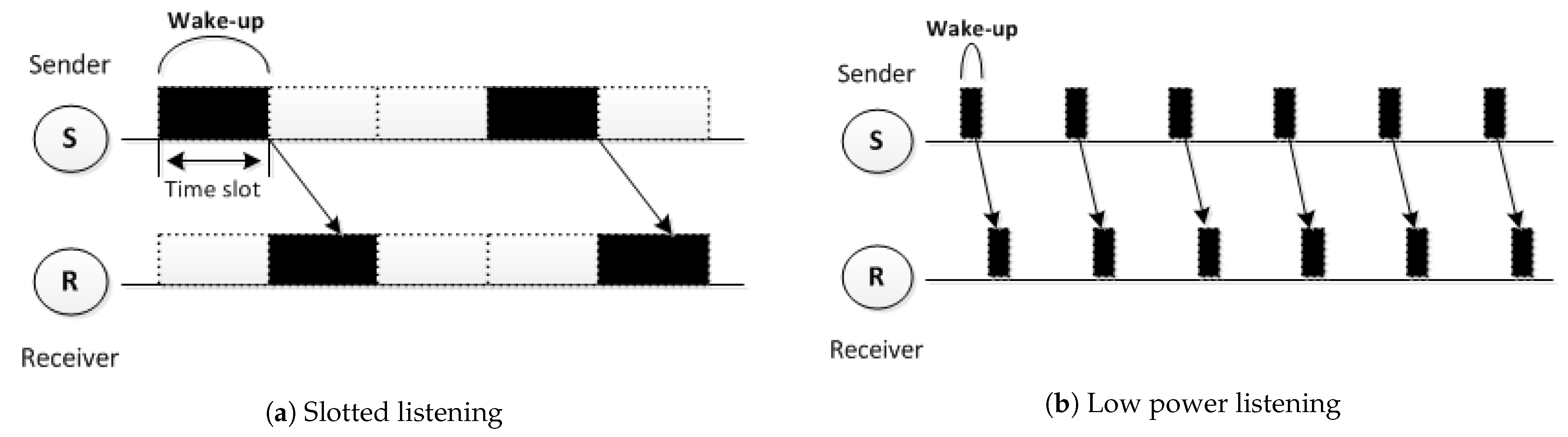
4. Duty Cycle Mechanism
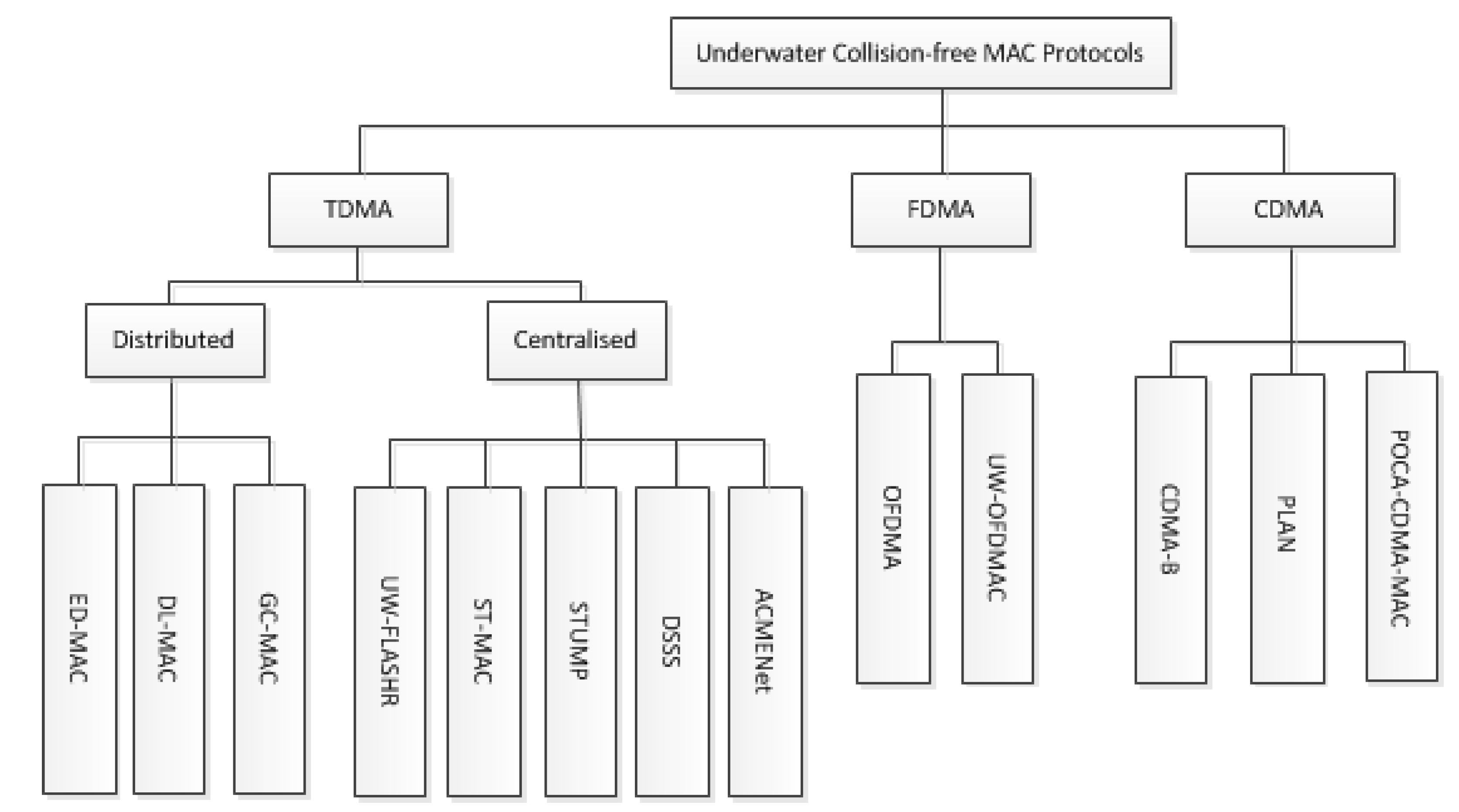
5. Classification of Underwater Collision-Free MAC Protocols
5.1. Code Division Multiple Access (CDMA)
5.2. Frequency Division Multiple Access (FDMA)
5.3. Time Division Multiple Access (TDMA)
5.3.1. Centralised
5.3.2. Distributed
6. Qualitative Comparison
7. Conclusions and Open Research Issues
- A wide variety of schemes to improve underwater MAC performance have been proposed in this study. These proposals were shown to enhance the performance of the MAC protocol in different network sizes, scenarios, and applications, especially by addressing spatial-temporal uncertainty, the near-far effect, and hidden/exposed node problems. The ideas reviewed in this paper consider concepts and mechanisms that target the achievement of collision-free MAC algorithms for underwater sensor networks. Research along these lines would involve a smart MAC protocol that is able to let a sensor capture environmental characteristics with real-time predication on possible changes. This can be achieved using learning techniques, such as reinforcement learning, that solve decision problems [87,88,89].
- Systematic research on cross-layer designs for underwater sensor networks is vital to increase the efficiency of the MAC protocol, such as those protocols proposed particularly for cross-layer designs. They may cross either the physical or the network layers, but not both concurrently. Furthermore, they mainly concentrate on the MAC function without jointly considering other network functions for overall performance improvement, such as congestion control. A systematic design should consider all possible optimal options collectively in order to maximise performance gain [83,90].
- Finally, as the different ideas proposed in this study were based on different concepts and mechanisms of the MAC protocol for underwater sensor networks, an integration of their combined effects and algorithms should be attempted along with using the mobile Autonomous Underwater Vehicle (AUV) in a distributed manner in order to design effective AUV employed data-gathering schemes for time-critical scenarios [91,92].
Funding
Acknowledgments
Conflicts of Interest
References
- Akyildiz, I.F.; Pompili, D.; Melodia, T. Underwater acoustic sensor networks: Research challenges. Ad Hoc Netw. 2005, 3, 257–279. [Google Scholar] [CrossRef]
- Hsu, C.C.; Lai, K.F.; Chou, C.F.; Lin, K.C.J. ST-MAC: Spatial-temporal mac scheduling for underwater sensor networks. In Proceedings of the IEEE INFOCOM 2009, Rio de Janeiro, Brazil, 19–25 April 2009; pp. 1827–1835. [Google Scholar]
- Noh, Y.; Lee, U.; Han, S.; Wang, P.; Torres, D.; Kim, J.; Gerla, M. DOTS: A propagation delay-aware opportunistic MAC protocol for mobile underwater networks. IEEE Trans. Mob. Comput. 2014, 13, 766–782. [Google Scholar] [CrossRef]
- Partan, J.; Kurose, J.; Levine, B.N. A survey of practical issues in underwater networks. ACM SIGMOBILE Mob. Comput. Commun. Rev. 2007, 11, 23–33. [Google Scholar] [CrossRef] [Green Version]
- Yu, H.; Yao, N.; Wang, T.; Li, G.; Gao, Z.; Tan, G. WDFAD-DBR: Weighting depth and forwarding area division DBR routing protocol for UASNs. Ad Hoc Netw. 2016, 37, 256–282. [Google Scholar] [CrossRef]
- Potter, J.; Alves, J.; Green, D.; Zappa, G.; Nissen, I.; McCoy, K. The JANUS underwater communications standard. In Proceedings of the 2014 Underwater Communications and Networking (UComms), Sestri Levante, Italy, 3–5 September 2014. [Google Scholar]
- Heidemann, J.; Ye, W.; Wills, J.; Syed, A.; Li, Y. Research challenges and applications for underwater sensor networking. In Proceedings of the IEEE Wireless Communications and Networking Conference, 2006, WCNC 2006, Las Vegas, NV, USA, 3–6 April 2006; Volume 1, pp. 228–235. [Google Scholar]
- Kredo, K., II; Djukic, P.; Mohapatra, P. STUMP: Exploiting position diversity in the staggered TDMA underwater MAC protocol. In Proceedings of the IEEE INFOCOM 2009, Rio de Janeiro, Brazil, 19–25 April 2009; pp. 2961–2965. [Google Scholar]
- Stojanovic, M.; Preisig, J. Underwater acoustic communication channels: Propagation models and statistical characterization. Commun. Mag. 2009, 47, 84–89. [Google Scholar] [CrossRef]
- Luo, J.; Chen, Y.; Wu, M.; Yang, Y. A Survey of Routing Protocols for Underwater Wireless Sensor Networks. IEEE Commun. Surv. Tutor. 2021, 23, 137–160. [Google Scholar] [CrossRef]
- Liao, W.H.; Huang, C.C. SF-MAC: A spatially fair MAC protocol for underwater acoustic sensor networks. Sens. J. 2012, 12, 1686–1694. [Google Scholar] [CrossRef]
- Zhu, Y.; Peng, Z.; Cui, J.H.; Chen, H. Toward practical MAC design for underwater acoustic networks. IEEE Trans. Mob. Comput. 2015, 14, 872–886. [Google Scholar] [CrossRef]
- Lee, U.; Wang, P.; Noh, Y.; Vieira, L.F.; Gerla, M.; Cui, J.H. Pressure routing for underwater sensor networks. In Proceedings of the 2010 Proceedings IEEE INFOCOM, San Diego, CA, USA, 14–19 March 2010; pp. 1–9. [Google Scholar]
- Zhou, Z.; Peng, Z.; Cui, J.H.; Shi, Z.; Bagtzoglou, A. Scalable localization with mobility prediction for underwater sensor networks. IEEE Trans. Mob. Comput. 2011, 10, 335–348. [Google Scholar] [CrossRef]
- Cheng, W.; Teymorian, A.Y.; Ma, L.; Cheng, X.; Lu, X.; Lu, Z. Underwater localization in sparse 3D acoustic sensor networks. In Proceedings of the IEEE INFOCOM 2008—The 27th Conference on Computer Communications, Phoenix, AZ, USA, 13–18 April 2008; pp. 236–240. [Google Scholar]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. Performance comparison of sender-based and receiver-based scheduling mac protocols for underwater sensor networks. In Proceedings of the 2016 19th International Conference on Network-Based Information Systems (NBiS), Ostrava, Czech Republic, 7–9 September 2016; pp. 99–106. [Google Scholar]
- Chen, K.; Ma, M.; Cheng, E.; Yuan, F.; Su, W. A survey on MAC protocols for underwater wireless sensor networks. Commun. Surv. Tutor. 2014, 16, 1433–1447. [Google Scholar] [CrossRef]
- Fazel, F.; Fazel, M.; Stojanovic, M. Random access compressed sensing for energy-efficient underwater sensor networks. IEEE J. Sel. Areas Commun. 2011, 29, 1660–1670. [Google Scholar] [CrossRef] [Green Version]
- Luo, J.; Fan, L.; Wu, S.; Yan, X. Research on Localization Algorithms Based on Acoustic Communication for Underwater Sensor Networks. Sensors 2018, 18, 67. [Google Scholar] [CrossRef] [Green Version]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. Efficient depth-based scheduling MAC protocol for underwater sensor networks. In Proceedings of the 2017 Ninth International Conference on Ubiquitous and Future Networks (ICUFN), Milan, Italy, 4–7 July 2017; pp. 827–832. [Google Scholar]
- Climent, S.; Sanchez, A.; Capella, J.V.; Meratnia, N.; Serrano, J.J. Underwater acoustic wireless sensor networks: Advances and future trends in physical, MAC and routing layers. Sensors 2014, 14, 795–833. [Google Scholar] [CrossRef]
- Akyildiz, I.F.; Pompili, D.; Melodia, T. Challenges for efficient communication in underwater acoustic sensor networks. ACM Sigbed Rev. 2004, 1, 3–8. [Google Scholar] [CrossRef]
- Lanbo, L.; Shengli, Z.; Jun-Hong, C. Prospects and problems of wireless communication for underwater sensor networks. Wirel. Commun. Mob. Comput. 2008, 8, 977–994. [Google Scholar] [CrossRef]
- Han, Y.; Fei, Y. A delay-aware probability-based MAC protocol for underwater acoustic sensor networks. In Proceedings of the 2015 International Conference on Computing, Networking and Communications (ICNC), Garden Grove, CA, USA, 16–19 February 2015; pp. 938–944. [Google Scholar]
- Wei, X.; Guo, H.; Wang, X.; Wang, X.; Wang, C.; Guizani, M.; Du, X. A Co-Design-Based Reliable Low-Latency and Energy-Efficient Transmission Protocol for UWSNs. Sensors 2020, 20, 6370. [Google Scholar] [CrossRef] [PubMed]
- Siwach, V.; Sehrawat, H.; Singh, Y. Energy-Efficient Schemes in Underwater Wireless Sensor Network: A Review. Comput. Methods Data Eng. 2021, 495–510. [Google Scholar]
- Zhu, Y.; Jiang, Z.; Peng, Z.; Zuba, M.; Cui, J.H.; Chen, H. Toward practical MAC design for underwater acoustic networks. In Proceedings of the 2013 Proceedings IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 683–691. [Google Scholar]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.; Boutaleb, T. An Efficient Scalable Scheduling MAC Protocol for Underwater Sensor Networks. Sensors 2018, 18, 2806. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. An Energy-conserving Depth-based Layering MAC Protocol for Underwater Sensor Networks. In Proceedings of the 2018 IEEE 88th Vehicular Technology Conference (VTC-Fall), Chicago, IL, USA, 27–30 August 2018; pp. 1–6. [Google Scholar]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. Graph Colouring MAC Protocol for Underwater Sensor Networks. In Proceedings of the 2018 IEEE 32nd International Conference on Advanced Information Networking and Applications (AINA), Krakow, Poland, 16–18 May 2018; pp. 120–127. [Google Scholar]
- Zhu, Y.; Le, S.N.; Peng, Z.; Cui, J.H. DOS: Distributed on-Demand Scheduling for High Performance MAC in Underwater Acoustic Networks; Tech. Rep. UbiNet-TR13-07; Computer Science and Engineering Department University of Connecticut: Storrs, CT, USA, 2013. [Google Scholar]
- Pompili, D.; Melodia, T.; Akyildiz, I.F. A CDMA-based medium access control for underwater acoustic sensor networks. IEEE Trans. Wirel. Commun. 2009, 8, 1899–1909. [Google Scholar] [CrossRef]
- Xie, P.; Cui, J.H. R-MAC: An energy-efficient MAC protocol for underwater sensor networks. In Proceedings of the International Conference on Wireless Algorithms, Systems and Applications (WASA 2007), Chicago, IL, USA, 1–3 August 2007; pp. 187–198. [Google Scholar]
- Caruso, A.; Paparella, F.; Vieira, L.F.M.; Erol, M.; Gerla, M. The meandering current mobility model and its impact on underwater mobile sensor networks. In Proceedings of the IEEE INFOCOM 2008—The 27th Conference on Computer Communication, Phoenix, AZ, USA, 13–18 April 2008; pp. 221–225. [Google Scholar]
- Han, Y.; Fei, Y. DAP-MAC: A delay-aware probability-based MAC protocol for underwater acoustic sensor networks. Ad Hoc Netw. 2016, 48, 80–92. [Google Scholar] [CrossRef] [Green Version]
- Jiang, S. State-of-the-art medium access control (MAC) protocols for underwater acoustic networks: A survey based on a MAC reference model. IEEE Commun. Surv. Tutor. 2018, 20, 1. [Google Scholar] [CrossRef]
- Khalil, I.M.; Gadallah, Y.; Hayajneh, M.; Khreishah, A. An adaptive OFDMA-based MAC protocol for underwater acoustic wireless sensor networks. Sensors 2012, 12, 8782–8805. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Preisig, J. Acoustic propagation considerations for underwater acoustic communications network development. ACM SIGMOBILE Mob. Comput. Commun. Rev. 2007, 11, 2–10. [Google Scholar] [CrossRef]
- Stojanovic, M. On the relationship between capacity and distance in an underwater acoustic communication channel. ACM SIGMOBILE Mob. Comput. Commun. Rev. 2007, 11, 34–43. [Google Scholar] [CrossRef]
- Ghoreyshi, S.M.; Shahrabi, A.; Boutaleb, T. Void-handling techniques for routing protocols in underwater sensor networks: Survey and challenges. IEEE Commun. Surv. Tutor. 2017, 19, 800–827. [Google Scholar] [CrossRef] [Green Version]
- Ghoreyshi, S.M.; Shahrabi, A.; Boutaleb, T. A novel cooperative opportunistic routing scheme for underwater sensor networks. Sensors 2016, 16, 297. [Google Scholar] [CrossRef]
- Casari, P.; Tomasi, B.; Zorzi, M. A comparison between the tone-lohi and slotted fama mac protocols for underwater networks. In Proceedings of the OCEANS 2008, Quebec City, QC, Canada, 15–18 September 2008; pp. 1–8. [Google Scholar]
- Yu, H.; Yao, N.; Liu, J. An adaptive routing protocol in underwater sparse acoustic sensor networks. Ad Hoc Netw. 2015, 34, 121–143. [Google Scholar] [CrossRef]
- Coutinho, R.W.; Boukerche, A.; Vieira, L.F.; Loureiro, A.A. A novel void node recovery paradigm for long-term underwater sensor networks. Ad Hoc Netw. 2015, 34, 144–156. [Google Scholar] [CrossRef]
- Khan, J.U.; Cho, H.S. A distributed data-gathering protocol using AUV in underwater sensor networks. Sensors 2015, 15, 19331–19350. [Google Scholar] [CrossRef] [Green Version]
- Brekhovskikh, L.M.; Lysanov, Y.P.; Lysanov, J.P. Fundamentals of Ocean Acoustics; Springer Science & Business Media: New York, NY, USA, 2003. [Google Scholar]
- Rodoplu, V.; Park, M.K. An energy-efficient MAC protocol for underwater wireless acoustic networks. In Proceedings of the OCEANS 2005 MTS/IEEE, Washington, DC, USA, 17–23 September 2005; pp. 1198–1203. [Google Scholar]
- Ghoreyshi, S.M.; Shahrabi, A.; Boutaleb, T. An opportunistic void avoidance routing protocol for underwater sensor networks. In Proceedings of the 2016 IEEE 30th International Conference on Advanced Information Networking and Applications (AINA), Crans-Montana, Switzerland, 23–25 March 2016; pp. 316–323. [Google Scholar]
- Kredo, K.B., II; Mohapatra, P. A hybrid medium access control protocol for underwater wireless networks. In Proceedings of the Second Workshop on Underwater Networks, Montreal, QC, Canada, 14 September 2007; ACM: New York, NY, USA, 2007; pp. 33–40. [Google Scholar]
- Fan, G.; Chen, H.; Xie, L.; Wang, K. A hybrid reservation-based MAC protocol for underwater acoustic sensor networks. Ad Hoc Netw. 2013, 11, 1178–1192. [Google Scholar] [CrossRef]
- Dang, D.N.M.; Nguyen, V.; Le, H.T.; Hong, C.S.; Choe, J. An efficient multi-channel MAC protocol for wireless ad hoc networks. Ad Hoc Netw. 2016, 44, 46–57. [Google Scholar] [CrossRef]
- Su, Y.; Zhu, Y.; Mo, H.; Cui, J.H.; Jin, Z. A joint power control and rate adaptation MAC protocol for underwater sensor networks. Ad Hoc Netw. 2015, 26, 36–49. [Google Scholar] [CrossRef]
- Chen, H.; Fan, G.; Xie, L.; Cui, J.H. A Hybrid Path-Oriented Code Assignment CDMA-Based MAC Protocol for Underwater Acoustic Sensor Networks. Sensors 2013, 13, 15006–15025. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Li, Z.; Guo, Z.; Hong, F.; Hong, L. E 2 DTS: An energy efficiency distributed time synchronization algorithm for underwater acoustic mobile sensor networks. Ad Hoc Netw. 2013, 11, 1372–1380. [Google Scholar] [CrossRef]
- Syed, A.A.; Heidemann, J.S. Time Synchronization for High Latency Acoustic Networks. In Proceedings of the IEEE INFOCOM 2006, 25TH IEEE International Conference on Computer Communications, Barcelona, Spain, 23–29 April 2006; Volume 6, pp. 1–12. [Google Scholar]
- Sozer, E.M.; Stojanovic, M.; Proakis, J.G. Underwater acoustic networks. IEEE J. Ocean. Eng. 2000, 25, 72–83. [Google Scholar] [CrossRef]
- Park, M.K.; Rodoplu, V. UWAN-MAC: An energy-efficient MAC protocol for underwater acoustic wireless sensor networks. J. Ocean. Eng. 2007, 32, 710–720. [Google Scholar] [CrossRef]
- Anastasi, G.; Conti, M.; Di Francesco, M.; Passarella, A. Energy conservation in wireless sensor networks: A survey. Ad Hoc Netw. 2009, 7, 537–568. [Google Scholar] [CrossRef]
- Tseng, Y.C.; Hsu, C.S.; Hsieh, T.Y. Power-saving protocols for IEEE 802.11-based multi-hop ad hoc networks. Comput. Netw. 2003, 43, 317–337. [Google Scholar] [CrossRef]
- Zheng, R.; Hou, J.C.; Sha, L. Asynchronous wakeup for ad hoc networks. In Proceedings of the 4th ACM International Symposium on Mobile ad Hoc Networking & Computing, Annapolis, MD, USA, 1–3 June 2003; ACM: New York, NY, USA, 2003; pp. 35–45. [Google Scholar]
- Polastre, J.; Hill, J.; Culler, D. Versatile low power media access for wireless sensor networks. In Proceedings of the 2nd International Conference on Embedded Networked Sensor Systems, Baltimore, MD, USA, 3–5 November 2004; ACM: New York, NY, USA, 2004; pp. 95–107. [Google Scholar]
- Hsu, C.C.; Kuo, M.S.; Chou, C.F.; Lin, K.C.J. The elimination of spatial-temporal uncertainty in underwater sensor networks. IEEE/ACM Trans. Netw. 2013, 21, 1229–1242. [Google Scholar] [CrossRef]
- Hong, L.; Hong, F.; Guo, Z.; Li, Z. ECS: Efficient communication scheduling for underwater sensor networks. Sensors 2011, 11, 2920–2938. [Google Scholar] [CrossRef] [Green Version]
- Zheng, J.; Jamalipour, A. Wireless Sensor Networks: A Networking Perspective; John Wiley & Sons: Hoboken, NJ, USA, 2009. [Google Scholar]
- Xu, M.; Liu, G.; Guan, J. Towards a secure medium access control protocol for cluster-based underwater wireless sensor networks. Int. J. Distrib. Sens. Netw. 2015, 2015, 40. [Google Scholar] [CrossRef]
- Tracy, L.T.; Roy, S. A reservation MAC protocol for ad-hoc underwater acoustic sensor networks. In Proceedings of the Third ACM International Workshop on Underwater Networks, San Francisco, CA, USA, 15 September 2008; ACM: New York, NY, USA, 2008; pp. 95–98. [Google Scholar]
- Sozer, E.; Proakis, J.; Stojanovic, R.; Rice, J.; Benson, A.; Hatch, M. Direct sequence spread spectrum based modem for under water acoustic communication and channel measurements. In Proceedings of the Oceans’99, MTS/IEEE, Riding the Crest into the 21st Century, Conference and Exhibition, Conference Proceedings (IEEE Cat. No.99CH37008), Seattle, WA, USA, 13–16 September 1999; Volume 1, pp. 228–233. [Google Scholar]
- Freitag, L.; Stojanovic, M.; Singh, S.; Johnson, M. Analysis of channel effects on direct-sequence and frequency-hopped spread-spectrum acoustic communication. IEEE J. Ocean. Eng. 2001, 26, 586–593. [Google Scholar] [CrossRef]
- Kalofonos, D.N.; Stojanovic, M.; Proakis, J.G. Performance of adaptive MC-CDMA detectors in rapidly fading Rayleigh channels. IEEE Trans. Wirel. Commun. 2003, 2, 229–239. [Google Scholar] [CrossRef]
- Tan, H.X.; Seah, W.K. Distributed CDMA-based MAC protocol for underwater sensor networks. In Proceedings of the 32nd IEEE Conference on Local Computer Networks (LCN 2007), Dublin, Ireland, 15–18 October 2007; pp. 26–36. [Google Scholar]
- Kim, J.P.; Lee, J.W.; Jang, Y.S.; Son, K.; Cho, H.S. A CDMA-based MAC protocol in tree-topology for underwater acoustic sensor networks. In Proceedings of the 2009 International Conference on Advanced Information Networking and Applications Workshops, Bradford, UK, 26–29 May 2009; pp. 1166–1171. [Google Scholar]
- Stojanovic, M.; Freitag, L. Multichannel detection for wideband underwater acoustic CDMA communications. IEEE J. Ocean. Eng. 2006, 31, 685–695. [Google Scholar] [CrossRef] [Green Version]
- Hayajneh, M.; Khalil, I.; Gadallah, Y. An OFDMA-based MAC protocol for underwater acoustic wireless sensor networks. In Proceedings of the 2009 International Conference on Wireless Communications and Mobile Computing: Connecting the World Wirelessly, Leipzig, Germany, 21–24 June 2009; ACM: New York, NY, USA, 2009; pp. 810–814. [Google Scholar]
- Bouabdallah, F.; Boutaba, R. A Distributed OFDMA Medium Access Control for Underwater Acoustic Sensors Networks. In Proceedings of the 2011 IEEE International Conference on Communications (ICC), Kyoto, Japan, 5–9 June 2011; pp. 1–5. [Google Scholar]
- Proakis, J.G.; Rice, J.A.; Sozer, E.M.; Stojanovic, M. Shallow-Water Acoustic Networks. Wiley Encycl. Telecommun. 2003, 39, 114–119. [Google Scholar]
- Qin, Z.; Sun, Y.; Sun, L.; Shu, L.; Wang, L.; Zhang, W.; Lu, B. A Joint Duty Cycle and Network Coding MAC Protocol for Underwater Wireless Sensor Networks. In Proceedings of the 2016 25th International Conference on Computer Communication and Networks (ICCCN), Waikoloa, HI, USA, 1–4 August 2016; pp. 1–9. [Google Scholar]
- Van Hoesel, L.; Nieberg, T.; Kip, H.; Havinga, P.J. Advantages of a TDMA based, energy-efficient, self-organizing MAC protocol for WSNs. In Proceedings of the V2004 IEEE 59th Vehicular Technology Conference. VTC 2004-Spring (IEEE Cat. No.04CH37514), Milan, Italy, 17–19 May 2004; Volume 3, pp. 1598–1602. [Google Scholar]
- Yackoski, J.; Shen, C.C. UW-FLASHR: Achieving high channel utilization in a time-based acoustic MAC protocol. In Proceedings of the Third ACM International Workshop on Underwater Networks, San Francisco, CA, USA, 15 September 2008; ACM: New York, NY, USA, 2008; pp. 59–66. [Google Scholar]
- Acar, G.; Adams, A. ACMENet: An underwater acoustic sensor network protocol for real-time environmental monitoring in coastal areas. Proc. Radar Sonar Navig. 2006, 153, 365–380. [Google Scholar] [CrossRef]
- Chen, Y.D.; Lien, C.Y.; Chuang, S.W.; Shih, K.P. DSSS: A TDMA-based MAC protocol with dynamic slot scheduling strategy for underwater acoustic sensor networks. In Proceedings of the OCEANS 2011 IEEE-Spain, Santander, Spain, 6–9 June 2011; pp. 1–6. [Google Scholar]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. An Energy-conserving Collision-free MAC Protocol for Underwater Sensor Networks. IEEE Access 2019, 7, 27155–27171. [Google Scholar] [CrossRef]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. A Collision-Free Graph Colouring MAC Protocol for Underwater Sensor Networks. IEEE Access 2019, 7, 39862–39878. [Google Scholar] [CrossRef]
- Alfouzan, F.A.; Ghoreyshi, S.M.; Shahrabi, A.; Ghahroudi, M.S. An AUV-Aided Cross-Layer Mobile Data Gathering Protocol for Underwater Sensor Networks. Sensors 2020, 20, 4813. [Google Scholar] [CrossRef]
- Xie, P.; Zhou, Z.; Peng, Z.; Yan, H.; Hu, T.; Cui, J.H.; Shi, Z.; Fei, Y.; Zhou, S. Aqua-Sim: An NS-2 based simulator for underwater sensor networks. In Proceedings of the OCEANS, MTS/IEEE Biloxi-Marine Technology for Our Future: Global and Local Challenges, Biloxi, MS, USA, 26–29 October 2009; pp. 1–7. [Google Scholar]
- Alfouzan, F.; Shahrabi, A.; Ghoreyshi, S.M.; Boutaleb, T. A comparative performance evaluation of distributed collision-free MAC protocols for underwater sensor networks. In Proceedings of the 8th International Conference on Sensor Networks. (SENSORNETS), Prague, Czech Republic, 2019; pp. 1–9. [Google Scholar]
- Fan, G.; Chen, H.; Xie, L.; Wang, K. An improved CDMA-based MAC protocol for underwater acoustic wireless sensor networks. In Proceedings of the 2011 7th International Conference on Wireless Communications, Networking and Mobile Computing, Wuhan, China, 23–25 September 2011; pp. 1–4. [Google Scholar]
- Valerio, V.D.; Petrioli, C.; Pescosolido, L.; Van Der Shaar, M. A reinforcement learning-based data-link protocol for underwater acoustic communications. In Proceedings of the 10th International Conference on Underwater Networks & Systems, Washington, DC, USA, 22–24 October 2015; ACM: New York, NY, USA, 2015; p. 2. [Google Scholar]
- Hu, T.; Fei, Y. QELAR: A machine-learning-based adaptive routing protocol for energy-efficient and lifetime-extended underwater sensor networks. IEEE Trans. Mob. Comput. 2010, 9, 796–809. [Google Scholar]
- Yigitel, M.A.; Incel, O.D.; Ersoy, C. QoS-aware MAC protocols for wireless sensor networks: A survey. Comput. Netw. 2011, 55, 1982–2004. [Google Scholar] [CrossRef]
- Wang, H.; Wang, S.; Bu, R.; Zhang, E. A novel cross-layer routing protocol based on network coding for underwater sensor networks. Sensors 2017, 17, 1821. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Alfouzan, F.A.; Ghoreyshi, S.M.; Shahrabi, A.; Ghahroudi, M.S. A Novel Cross-layer Mobile Data-gathering Protocol for Underwater Sensor Networks. In Proceedings of the 2020 IEEE 91st Vehicular Technology Conference (VTC2020-Spring), Antwerp, Belgium, 25–28 May 2020; pp. 1–6. [Google Scholar]
- Wang, J.; Zhang, S.; Chen, W.; Kong, D.; Zuo, X.; Yu, Z. Design and implementation of SDN-based underwater acoustic sensor networks with multi-controllers. IEEE Access 2018, 6, 25698–25714. [Google Scholar] [CrossRef]
| ED-MAC | DL-MAC | GC-MAC | |
|---|---|---|---|
| Year | 2017 | 2018 | 2018 |
| Category | TDMA-based | TDMA-based | TDMA-based |
| TDMA status | Adaptive slotted | Adaptive slotted | Adaptive slotted |
| Schedule | Distributed | Distributed | Distributed |
| Synchronised | Yes | Yes | Yes |
| Clustered | No | Yes | Yes |
| Network division | No | Divided into layers | Divided into cubes |
| Priority | Depth-based timer | Degree timer | Node ID |
| neighbourhood info | One-hop neighbours | One-hop neighbours | Two-hop neighbours |
| Random time | No | Yes | No |
| GPS | No | No | Yes |
| Conflict Avoidance | No | No | Yes |
| Number of slots | 2 × | Equal to | Fixed |
| Protocol | Source | Classification | Description |
|---|---|---|---|
| POCA-CDMA-MAC | [86] | CDMA-based | Use a round-robin method and CDMA technique to reduce data packets collisions. |
| Round-robin technology | Route (from sensors to the sink) is built in the first phase based on the sensor’s position. | ||
| Sender-based scheduling | Every sensor follows the order to send its own packet in a round-robin manner. | ||
| PLAN | [70] | CDMA-based | Multiple nodes need to exchange RTS/CTS dialogue with the destination node before transmission. |
| Handshake-based | Exploit the ability of CDMA-based to receive concurrently from multi senders using various codes. | ||
| Receiver-based scheduling | Improve throughput while reducing packet losses arising from unsynchronised data transmissions. | ||
| CDMA-B | [71] | CDMA-based | Sensors are awake and sleep periodically in order to reduce undesirable energy consumption. |
| Multi-hop | The network is classified into multiple hierarchical levels from bottom-nodes to the top-node. | ||
| Multi-code allocation | Sensors located in same hierarchical level are multiplexed by means of various orthogonal codes. | ||
| UW-OFDMAC | [74] | FDMA-based | Single-hop MAC assumption. |
| Transmitter-based | Based on estimating the number of contenders. | ||
| OFDMA-based scheme | Random back-off promotes fairness. | ||
| OFDMAC | [37,73] | Reservation-based | Generates packet exchange overhead. |
| Handshake-based | For a dynamic topology, it is not practical to schedule transmissions at each sensor node. | ||
| Receiver-based scheduling | |||
| ACMENet | [79] | Reservation-based | Provides fairness and mobility support through CSMA. |
| CSMA-based | Clock synchronisation is assumed. | ||
| TDMA-like approach | Sensors overhear messages to learn the transmission schedules and propagation delay for their neighbours. | ||
| DSSS | [80] | Reservation-based | Receiver waits for an additional duration before replying to an RTS with CTS. |
| Handshake-based | Accurate timing is required among sensor nodes. | ||
| Time-based | Its operation depends on the estimation of the propagation delay between two nodes. | ||
| STUMP | [8] | Reservation-based | Exploit node position diversity and low propagation speed to improve the channel use. |
| TDMA-based | Through synchronisation, sensors share the estimated propagation delay and time slot requirements with their two-hop neighbours. | ||
| CSMA-based | Sensors are assumed to be stationary for more accuracy. | ||
| ST-MAC | [2] | Reservation-based | Focused on spatial-temporal uncertainty. |
| Network information is collected at the sink to schedule transmissions. | |||
| TDMA-based | A centralised scheduling algorithm is used based on global topology information. | ||
| Impairs the fairness of the network and means that some nodes starve. | |||
| UW-FLASHR | [78] | Reservation-based | Multiple time slots can be reserved by a single node. |
| Handshake-based | Nodes require an absolute time reference. | ||
| Time-slotted | A scheduled transmission cannot be cancelled even if another one is detected. | ||
| ED-MAC | [20,28] | Reservation-based | A packet train is formed for multiple neighbours to achieve high throughput. |
| Handshake-based | Sender has to know the propagation delay from itself to all intended receivers. | ||
| MACA-based | CTS packets collide when the receivers are at the same distance from the sender. | ||
| DL-MAC | [29] | Reservation-based | State transitions of MACA are defined according to propagation delays. |
| Handshake-based | Packets are assigned different priorities to avoid starvation in the case of simultaneous transmission attempts. | ||
| MACA-based | |||
| GC-MAC | [30] | Reservation-based | The transmission order is determined at the receiving side. |
| Handshake-based | The receiver waits for RTS from all contenders. | ||
| Receiver-based scheduling | Fairness is achieved at the expense of channel use. |
| Protocol | Topology | Advantage | Disadvantage |
|---|---|---|---|
| POCA-CDMA-MAC | Multi-hop | A round-robin technique is used | Multiple nodes in different paths |
| to receive multiple packets from | transmit their packets periodically at | ||
| neighbours simultaneously. | the same interval time for simplicity. | ||
| PLAN | Distributed | Exploit the ability of CDMA-based | Use RTS/CTS handshaking control |
| systems to receive concurrently from | packets which take a long time to | ||
| multiple nodes. | propagate in the network. | ||
| CDMA-B | Multi-hop | A sleeping mode is periodically used | The performance of the network |
| in order to save energy when there is | is highly affected by near and far | ||
| no data transmission or reception. | problem. | ||
| UW-OFDMAC | Distributed | Improve energy conservation and | The performance of UW-OFDMAC |
| bandwidth efficiency by adapting an | protocol is significantly affected | ||
| orthogonal FDMA MAC framework. | by PAPR and ISI. | ||
| OFDMAC | Centralised | Adjust the orthogonal FDMA MAC | OFDMAC’s performance is affected |
| framework and eliminate the hidden/ | by the diversity of frequency and | ||
| exposed terminal problems. | multi-user. | ||
| ACMENet | Centralised | Exploit the high latency to avoid | Design for a small UWSN and high |
| collisions and provide highly efficient | energy consumption due to idle | ||
| use of the scarce network resources. | listening. | ||
| DSSS | Centralised | Simultaneous transmission by multi | Accurate synchronisation is |
| nodes increases the channel use | required. | ||
| with no chance of collision. | |||
| STUMP | Centralised | Estimate the high latency to schedule | Based on its scheduling constraints, |
| conflict transmissions without | some slots are not scheduled leading | ||
| requiring strict synchronisation. | to insufficient channel uses. | ||
| ST-MAC | Multi-hop | Concentrate on spatial-temporal | It is not suitable for mobile |
| uncertainty and solve the conflict | scenarios as well as the global | ||
| graph (i.e., vertex colour problem). | topology information is required. | ||
| UW-FLASHR | Centralised | Tight clock synchronisation and | Sensors stay awake during all the |
| accurate propagation delay are not | established portion (i.e., second | ||
| required. | part of the cycle). | ||
| ED-MAC | Distributed | Guarantee collision-free scheduling | Number of slots are doubled per cycle, |
| while improving the energy | to detect two-hop horizontal nodes, | ||
| efficiency. | which reduces the channel uses. | ||
| DL-MAC | Distributed | Lower complexity using underwater | The scheduling packet should be |
| features (e.g., 3D and depth of the nodes) | forwarded up to (d + 3) hops before | ||
| and higher reliability and flexibility. | any of them send their packets. | ||
| GC-MAC | Distributed | Employ the graph colouring algorithm | The location of the reference points, |
| to improve a reservation-based | , situated in the internal cube | ||
| contention-free MAC protocol. | is required (e.g., using GPS). |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alfouzan, F.A. Energy-Efficient Collision Avoidance MAC Protocols for Underwater Sensor Networks: Survey and Challenges. J. Mar. Sci. Eng. 2021, 9, 741. https://doi.org/10.3390/jmse9070741
Alfouzan FA. Energy-Efficient Collision Avoidance MAC Protocols for Underwater Sensor Networks: Survey and Challenges. Journal of Marine Science and Engineering. 2021; 9(7):741. https://doi.org/10.3390/jmse9070741
Chicago/Turabian StyleAlfouzan, Faisal Abdulaziz. 2021. "Energy-Efficient Collision Avoidance MAC Protocols for Underwater Sensor Networks: Survey and Challenges" Journal of Marine Science and Engineering 9, no. 7: 741. https://doi.org/10.3390/jmse9070741
APA StyleAlfouzan, F. A. (2021). Energy-Efficient Collision Avoidance MAC Protocols for Underwater Sensor Networks: Survey and Challenges. Journal of Marine Science and Engineering, 9(7), 741. https://doi.org/10.3390/jmse9070741






