Improvement of Cyber-Attack Detection Accuracy from Urban Water Systems Using Extreme Learning Machine
Abstract
1. Introduction
2. Cyber-Attack Situations in WDSs
2.1. Security Goals and Cyber–Physical Attacks
2.2. Attack Model
2.3. Attack Scenarios and Specifications
- Scenario 1: This scenario focuses on a direct attack on the components of WDSs, such as pumps, valves, and tanks. For example, a tank overflow may be caused by a direct attack on a pumping station through the activation of unscheduled pumps.
- Scenario 2: This scenario is caused by a disturbance in the reading or transportation of data between the sensors and PLC. For instance, manipulated water level readings can lead to the depletion or low levels of water in the tanks. This problem may be due to the physical manipulation of the water level sensor or the miscommunication of information between the sensor and PLC.
- Scenario 3: This scenario relates to the connection among PLCs. If Tank 1 is connected to PLC 1, and the information of Tank 1 (e.g., water level) is intercepted by the attack and is transmitted instead to PLC 2, the other tank connected to PLC 2 will either overflow or be depleted.
- Scenario 4: This scenario is an attack to conceal the PLC connection problem (Scenario 3) and disrupt the information between SCADA and PLC. An example would be a situation wherein there is a problem in the identification of attacks due to the malfunction of communication links between the PLC and SCADA.
- Scenario 5: This scenario focuses on the SCADA data transportation problem. This attack scenario entails the alteration of the packages being sent by SCADA to change the operations of a PLC it supervises. In particular, the communication link between SCADA and PLC is attacked, resulting in pump activation and tank overflow.
- Scenario 6: This scenario contains random multiple combinations of attacks on PLCs.
3. Application and Comparison of Various Classification Methods
3.1. K-Nearest Neighbor Algorithm
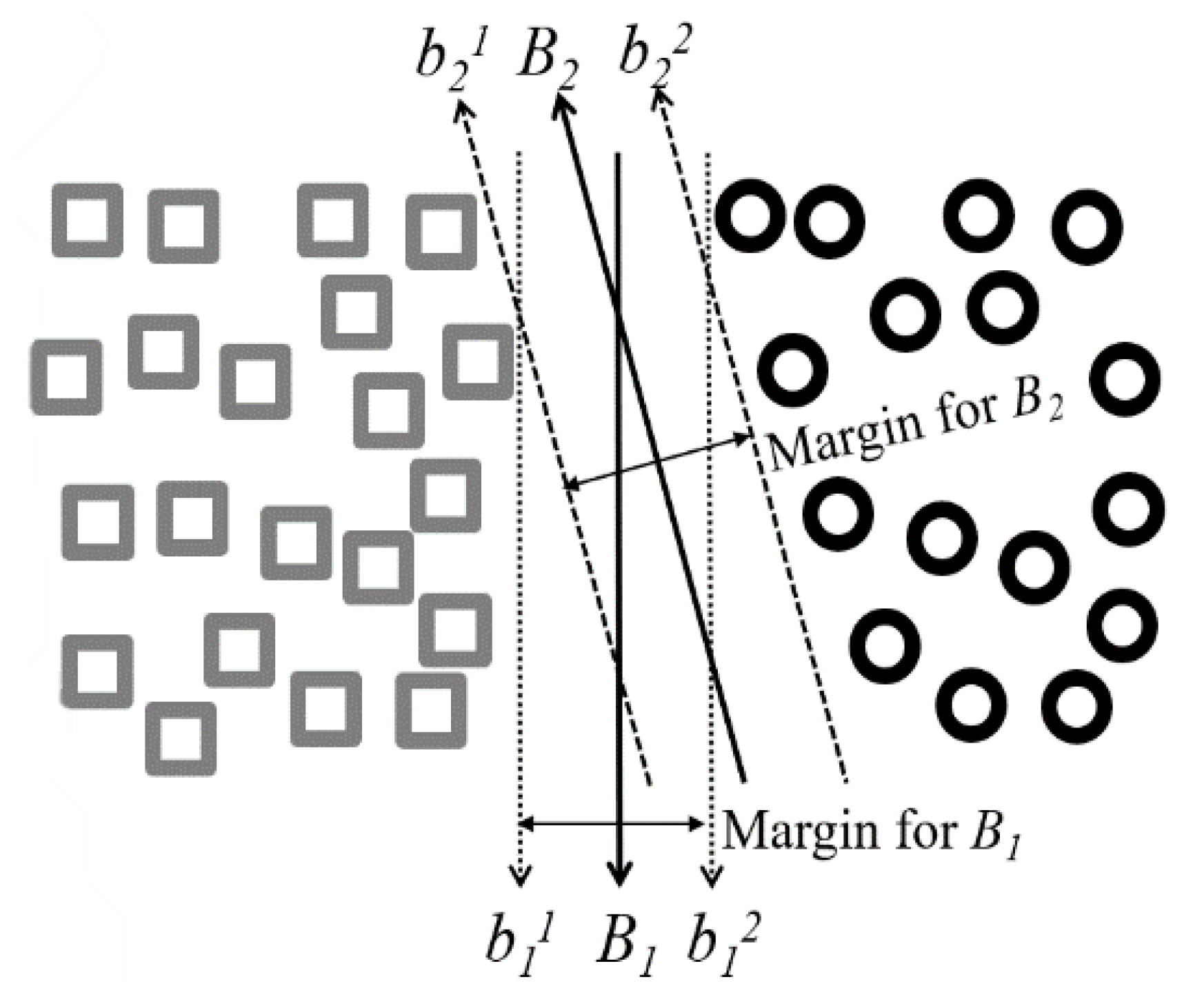
3.2. Support Vector Machine
3.3. Artificial Neural Networks
3.4. Standard Extreme Learning Machine
- Step 1:
- Randomly assign input weight (wi) and bias (bi, i = 1, ..., N).
- Step 2:
- Calculate the hidden layer output matrix (H).
- Step 3:
- Calculate the output weight (β),
3.5. Online Sequential ELM
3.6. Bidirectional ELM
3.7. Weighted ELM
- (1)
- the W-ELM can deal with data with imbalanced class distribution while maintaining good performance with well-balanced data.
- (2)
- By assigning different weights for each example according to users’ needs, the W-ELM can be generalized to cost-sensitive learning.
4. Applications, Results, and Discussion
4.1. Performance Indices
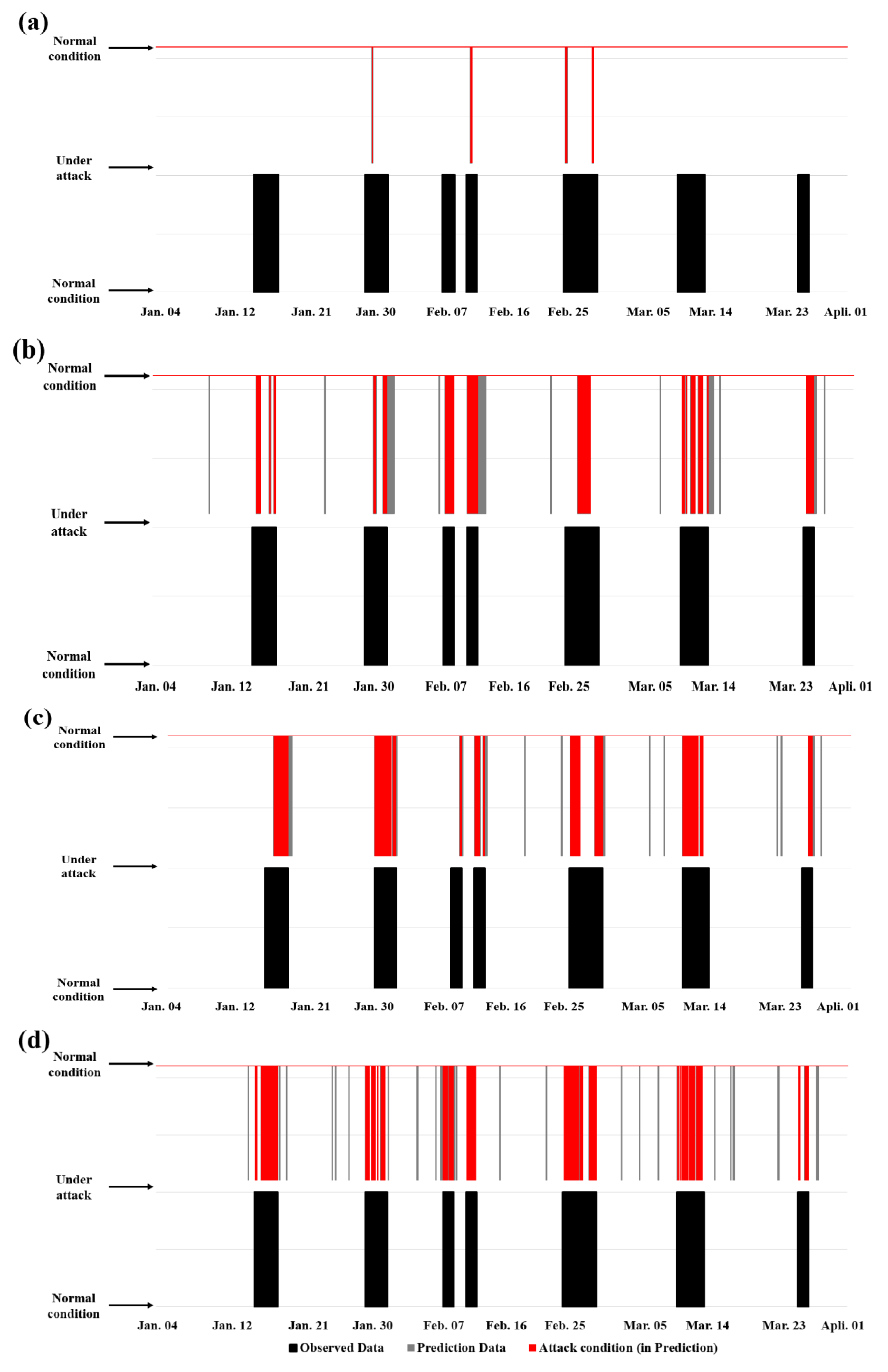
4.2. Comparison of Prediction Results for the Various Standard Classification Approaches
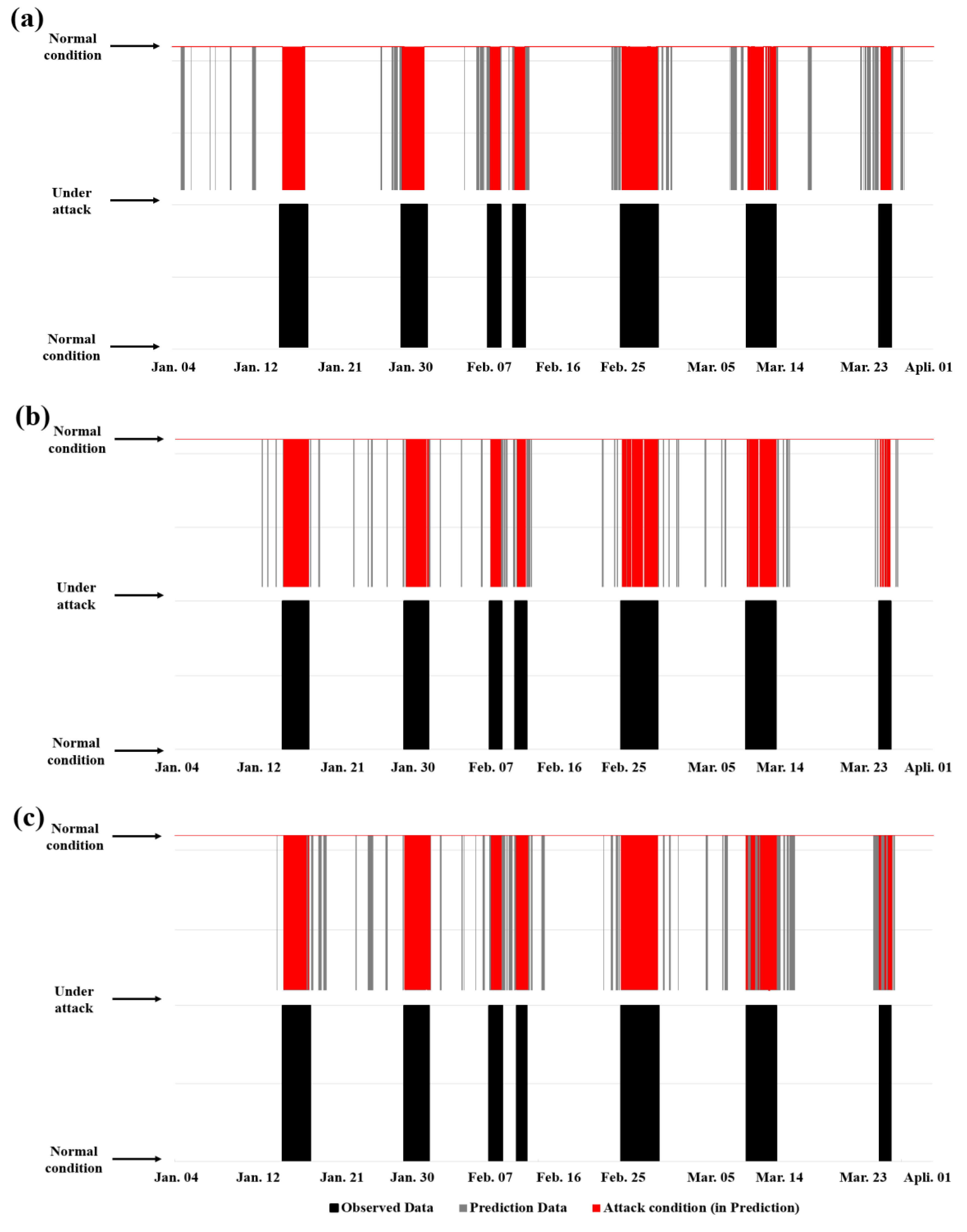
4.3. Comparison of Prediction Results of Improved Versions of ELM
5. Conclusions and Future Studies
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Spellman, F.R. Handbook of Water and Wastewater Treatment Plant Operations; CRC Press: Boca Raton, FL, USA, 2013. [Google Scholar]
- Bobat, A.; Gezgin, T.; Aslan, H. The SCADA system applications in management of Yuvacik Dam and Reservoir. Desalin. Water Treat. 2014, 54, 2108–2119. [Google Scholar] [CrossRef]
- Rasekh, A.; Hassanzadeh, A.; Mulchandani, S.; Modi, S.; Banks, M.K. Smart Water Networks and Cyber Security. J. Water Resour. Plan. Manag. 2016, 142, 01816004. [Google Scholar] [CrossRef]
- Moyer, J.; Dakin, R.; Hewman, R.; Groves, D. The Case for Cyber Security in the Water Sector. J. Am. Water Work. Assoc. 2009, 101, 30–32. [Google Scholar] [CrossRef]
- ICS-CERT. NCCIC/ICS-CERT Year in Review: FY 2015; Report No. 15e50569; U.S. Department of Homeland Security Industrial Control Systems-Cyber Emergency Response Team: Washington, DC, USA, 2016.
- Slay, J.; Miller, M. Lessons learned from the maroochy water breach. In Proceedings of the International Conference on Critical Infrastructure Protection, Hanover, NH, USA, 19–21 March 2007; pp. 73–82. [Google Scholar]
- Ostfeld, A.; Salomons, E.; Ormsbee, L.; Uber, J.G.; Bros, C.M.; Kalungi, P.; Burd, R.; Zazula-Coetzee, B.; Belrain, T.; Kang, D.; et al. Battle of the Water Calibration Networks. J. Water Resour. Plan. Manag. 2012, 138, 523–532. [Google Scholar] [CrossRef]
- Wu, Y.; Liu, S.; Wu, X.; Liu, Y.; Guan, Y. Burst detection in district metering areas using a data driven clustering algorithm. Water Res. 2016, 100, 28–37. [Google Scholar] [CrossRef] [PubMed]
- Gong, W.; Suresh, M.A.; Smith, L.; Ostfeld, A.; Stoleru, R.; Rasekh, A.; Banks, M.K. Mobile sensor networks for optimal leak and backflow detection and localization in municipal water networks. Environ. Model. Softw. 2016, 80, 306–321. [Google Scholar] [CrossRef]
- Choi, Y.H.; Kim, J.H. Topological and mechanical redundancy-based optimal design of water distribution systems in many-objective optimization. Eng. Optim. 2019, 1–18. [Google Scholar] [CrossRef]
- Jung, D.; Lansey, K.E.; Choi, Y.H.; Kim, J.H. Robustness-based optimal pump design and scheduling for water distribution systems. J. Hydroinformatics 2015, 18, 500–513. [Google Scholar] [CrossRef]
- Choi, Y.H.; Jung, D.; Jun, H.; Kim, J.H. Improving Water Distribution Systems Robustness through Optimal Valve Installation. Water 2018, 10, 1223. [Google Scholar] [CrossRef]
- Yang, D.; Usynin, A.; Hines, J.W. Anomaly-based intrusion detection for SCADA systems. In Proceedings of the 5th International Topical Meeting on Nuclear Plant Instrumentation, Control and Human Machine Interface Technologies (npic&hmit 05), Albuquerque, NM, USA, 12–16 November 2006; pp. 12–16. [Google Scholar]
- Cleveland, F.M. Cyber security issues for advanced metering infrastructure (AMI). In Proceedings of the 2008 IEEE Power and Energy Society General Meeting-Conversion and Delivery of Electrical Energy in the 21st Century, Pittsburgh, PA, USA, 20–24 July 2008; pp. 1–5. [Google Scholar] [CrossRef]
- Xie, L.; Mo, Y.; Sinopoli, B. False Data Injection Attacks in Electricity Markets. In Proceedings of the 2010 First IEEE International Conference on Smart Grid Communications, Gaithersburg, MD, USA, 4–6 October 2010; pp. 226–231. [Google Scholar]
- Kim, T.T.; Poor, H.V. Strategic Protection Against Data Injection Attacks on Power Grids. IEEE Trans. Smart Grid 2011, 2, 326–333. [Google Scholar] [CrossRef]
- Liu, X.; Liu, X.; Li, Z. Cyber Risk Assessment of Transmission Lines in Smart Grids. Energies 2015, 8, 13796–13810. [Google Scholar] [CrossRef]
- Miche, Y.; Sorjamaa, A.; Bas, P.; Simula, O.; Jutten, C.; Lendasse, A. OP-ELM: Optimally Pruned Extreme Learning Machine. IEEE Trans. Neural Netw. 2009, 21, 158–162. [Google Scholar] [CrossRef]
- Negrete-Pincetic, M.; Yoshida, F.; Gross, G. Towards quantifying the impacts of cyber attacks in the competitive electricity market environment. IEEE Buchar. Power Tech. 2009, 1–8. [Google Scholar] [CrossRef]
- Kosut, O.; Jia, L.; Thomas, R.J.; Tong, L. Limiting false data attacks on power system state estimation. In Proceedings of the 2010 44th Annual Conference on Information Sciences and Systems (CISS), Princeton, NJ, USA, 17–19 March 2010; pp. 1–6. [Google Scholar]
- Esmalifalak, M.; Shi, G.; Han, Z.; Song, L. Bad Data Injection Attack and Defense in Electricity Market Using Game Theory Study. IEEE Trans. Smart Grid 2013, 4, 160–169. [Google Scholar] [CrossRef]
- Goh, J.; Adepu, S.; Tan, M.; Lee, Z.S. Anomaly Detection in Cyber Physical Systems Using Recurrent Neural Networks. In Proceedings of the 2017 IEEE 18th International Symposium on High Assurance Systems Engineering (HASE), Singapore, 12–14 January 2017; pp. 140–145. [Google Scholar]
- Inoue, J.; Yamagata, Y.; Chen, Y.; Poskitt, C.M.; Sun, J. Anomaly Detection for a Water Treatment System Using Unsupervised Machine Learning. In Proceedings of the 2017 IEEE International Conference on Data Mining Workshops (ICDMW), New Orleans, LA, USA, 18–24 November 2017; pp. 1058–1065. [Google Scholar]
- Kravchik, M.; Shabtai, A. Detecting Cyber Attacks in Industrial Control Systems Using Convolutional Neural Networks. In Proceedings of the 2018 Workshop on Cyber-Physical Systems Security and PrivaCy-CPS-SPC ‘18, Toronto, ON, Canada, 19 October 2018; pp. 72–83. [Google Scholar]
- Amin, S.; Litrico, X.; Sastry, S.; Bayen, A.M. Cyber Security of Water SCADA Systems—Part I: Analysis and Experimentation of Stealthy Deception Attacks. IEEE Trans. Control. Syst. Technol. 2013, 21, 1963–1970. [Google Scholar] [CrossRef]
- Perelman, L.; Amin, S. A network interdiction model for analyzing the vulnerability of water distribution systems. In Proceedings of the 3rd International Conference on PErvasive Technologies Related to Assistive Environments-PETRA ‘10, Samos, Greece, 23–25 June 2014; pp. 135–144. [Google Scholar]
- Almalawi, A.; Fahad, A.; Tari, Z.; Alamri, A.; Alghamdi, R.; Zomaya, A.Y. An Efficient Data-Driven Clustering Technique to Detect Attacks in SCADA Systems. IEEE Trans. Inf. Forensics Secur. 2016, 11, 893–906. [Google Scholar] [CrossRef]
- Taormina, R.; Galelli, S.; Tippenhauer, N.O.; Salomons, E.; Ostfeld, A. Characterizing Cyber-Physical Attacks on Water Distribution Systems. J. Water Resour. Plan. Manag. 2017, 143, 04017009. [Google Scholar] [CrossRef]
- Rossman, L.A. EPANET 2: Users’ Manual; BiblioGov, U.S. Environmental Protection Agency: Washington, DC, USA, 2000.
- Taormina, R.; Galelli, S. Deep-Learning Approach to the Detection and Localization of Cyber-Physical Attacks on Water Distribution Systems. J. Water Resour. Plan. Manag. 2018, 144, 04018065. [Google Scholar] [CrossRef]
- Taormina, R.; Galelli, S.; Tippenhauer, N.O.; Salomons, E.; Ostfeld, A.; Eliades, D.G.; Aghashahi, M.; Sundararajan, R.; Pourahmadi, M.; Banks, M.K.; et al. Battle of the Attack Detection Algorithms: Disclosing Cyber Attacks on Water Distribution Networks. J. Water Resour. Plan. Manag. 2018, 144, 04018048. [Google Scholar] [CrossRef]
- Altman, N.S. An Introduction to Kernel and Nearest-Neighbor Nonparametric Regression. Am. Stat. 1992, 46, 175. [Google Scholar] [CrossRef]
- Bhatia, N. Survey of nearest neighbor techniques. arXiv 2010, arXiv:1007.0085. [Google Scholar]
- Tay, B.; Hyun, J.K.; Oh, S. A Machine Learning Approach for Specification of Spinal Cord Injuries Using Fractional Anisotropy Values Obtained from Diffusion Tensor Images. Comput. Math. Methods Med. 2014, 2014, 1–8. [Google Scholar] [CrossRef]
- Vapnik, V. Statistical Learning Theory; Wiley: New York, NY, USA, 1998. [Google Scholar]
- Cho, D. Mixed-effects LS-SVM for longitudinal data. J. Korean Data Inf. Sci. Soc. 2010, 21, 363–369. [Google Scholar]
- Gallant, S.I.; Gallant, S.I. Neural Network Learning and Expert Systems; A Bradford Book; MIT Press: Cambridge, MA, USA, 1993. [Google Scholar]
- Smith, M. Neural Networks for Statistical Modelling; John Wiley & Sons: New York, NY, USA, 1994; p. 235. [Google Scholar]
- Dreyfus, G.; Martinez, J.-M.; Samuelides, M.; Gordon, M.B.; Badran, F.; Thiria, S.; Herault, L. Reseaux de Neurones: Methodologie et Applications; Editions Eyrolles: Paris, France, 2002. [Google Scholar]
- Karunanithi, N.; Grenney, W.J.; Whitley, D.; Bovee, K. Neural Networks for River Flow Prediction. J. Comput. Civ. Eng. 1994, 8, 201–220. [Google Scholar] [CrossRef]
- ASCE Task Committee on Application of Artificial Neural Networks in Hydrology. Artificial Neural Networks in Hydrology. II: Hydrologic Applications. J. Hydrol. Eng. 2000, 5, 124–137. [Google Scholar] [CrossRef]
- Hagan, M.T.; Demuth, H.B.; Beale, M. Neural Network Design; Thomson Learning, Oklahoma State University: Stillwater, OK, USA, 2002. [Google Scholar]
- Huang, G.B.; Zhu, Q.Y.; Siew, C.K. Extreme learning machine: A new learning scheme of feedforward neural networks. In Proceedings of the 2004 IEEE International Joint Conference on Neural Networks (IEEE Cat. No. 04CH37541), Budapest, Hungary, 25–29 July 2004; Volume 2, pp. 985–990. [Google Scholar] [CrossRef]
- Li, M.-B.; Huang, G.-B.; Saratchandran, P.; Sundararajan, N. Fully complex extreme learning machine. Neurocomputing 2005, 68, 306–314. [Google Scholar] [CrossRef]
- Igelnik, B.; Pao, Y.-H. Stochastic choice of basis functions in adaptive function approximation and the functional-link net. IEEE Trans. Neural Netw. 1995, 6, 1320–1329. [Google Scholar] [CrossRef]
- Huang, G.-B.; Zhu, Q.-Y.; Siew, C.-K. Extreme learning machine: Theory and applications. Neurocomputing 2006, 70, 489–501. [Google Scholar] [CrossRef]
- Liang, N.-Y.; Huang, G.-B.; Saratchandran, P.; Sundararajan, N. A Fast and Accurate Online Sequential Learning Algorithm for Feedforward Networks. IEEE Trans. Neural Netw. 2006, 17, 1411–1423. [Google Scholar] [CrossRef]
- Zhao, J.; Wang, Z.; Park, D.S. Online sequential extreme learning machine with forgetting mechanism. Neurocomputing 2012, 87, 79–89. [Google Scholar] [CrossRef]
- Yang, Y.; Wang, Y.; Yuan, X. Bidirectional Extreme Learning Machine for Regression Problem and Its Learning Effectiveness. IEEE Trans. Neural Networks Learn. Syst. 2012, 23, 1498–1505. [Google Scholar] [CrossRef] [PubMed]
- Zong, W.; Huang, G.-B.; Chen, Y. Weighted extreme learning machine for imbalance learning. Neurocomputing 2013, 101, 229–242. [Google Scholar] [CrossRef]
- Wang, G.; Hao, J.; Ma, J.; Huang, L. A new approach to intrusion detection using Artificial Neural Networks and fuzzy clustering. Expert Syst. Appl. 2010, 37, 6225–6232. [Google Scholar] [CrossRef]
- Cao, W.; Gao, J.; Ming, Z.; Cai, S. Some tricks in parameter selection for extreme learning machine. In Proceedings of the IOP Conference Series: Materials Science and Engineering, HI, USA, 30 August–2 September 2017; Volume 261, p. 012002. [Google Scholar]

| Attack Cases | Scenarios | Duration (hr) | Period (YYYY.MM.DD HH: mm) | Attack Descriptions |
|---|---|---|---|---|
| 1 | Scenario 2 | 50 | 2016.09.13 23:00–2016.09.16. 16:00 | Attacker changes L_T7 thresholds controlling PU10 and PU11 by altering SCADA transmission to PLC5. This causes low levels in T7. |
| 2 | Scenario 2 | 24 | 2016.09.26 11:00–2016.09.27. 10:00 | Attacker changes L_T7 thresholds controlling PU10 and PU11 by altering SCADA transmission to PLC5. This causes low levels in T7. |
| 3 | Scenario 3 | 60 | 2016.10.09 09:00–2016.10.11. 20:00 | Attacker alters L_T1 readings arriving to PLC2 with a constant low level. PLC1 receives the manipulated readings from PLC2 and keeps Pumps PU1 and PU2 on, driving T1 to overflow. |
| 4 | Scenario 3 | 94 | 2016.10.29 19:00–2016.11.02. 16:00 | Attacker alters L_T1 readings arriving to PLC2 with a constant low level. PLC1 receives the manipulated readings from PLC2 and keeps Pumps PU1 and PU2 on, driving T1 to overflow. |
| 5 | Scenario 1 | 60 | 2016.11.26 17:00–2016.11.29. 04:00 | Working speed of PU7 reduced to 0.9 of nominal speed causes lower water levels in T4. |
| 6 | Scenario 1 | 94 | 2016.12.06 07:00–2016.12.10. 04:00 | Working speed of PU7 reduced to 0.7 of nominal speed causes lower water levels in T4. |
| 7 | Scenario 1 | 110 | 2016.12.14 15:00–2016.12.19. 04:00 | Working speed of PU7 reduced to 0.7 of nominal speed causes lower water levels in T4. |
| 8 | Scenario 1 | 70 | 2017.01.16 09:00–2017.01.19. 06:00 | Working speed of PU7 reduced to 0.7 of nominal speed causes lower water levels in T4. |
| 9 | Scenario 3 | 65 | 2017.01.30 08:00–2017.02.02. 17:00 | Attacker alters L_T2 readings arriving to PLC3, which reads a constant low level and forces Valve V2 open, leading T2 to overflow. |
| 10 | Scenario 5 | 31 | 2017.02.09 03:00–2017.02.10. 09:00 | Malicious activation of Pump PU3. |
| 11 | Scenario 5 | 31 | 2017.02.12 01:00–2017.02.17. 07:00 | Malicious activation of Pump PU3. |
| 12 | Scenario 3 | 100 | 2017.02.24 05:00–2017.02.28. 08:00 | Attacker alters L_T2 readings arriving to PLC3, which reads a constant low level and forces Valve V2 open, leading T2 to overflow. |
| 13 | Scenario 6 | 80 | 2017.03.10 14:00–2017.03.13. 21:00 | Attacker changes L_T7 thresholds controlling PU10 and PU11 by gaining control of PLC5, causing the pumps to switch continuously. |
| 14 | Scenario 4 | 30 | 2017.03.25 20:00–2017.03.27. 01:00 | Alteration of T4 signal arriving at PLC6. |
| Definition:X: training data, Y: class labels of X, x: unknown sample Initialize: Set variables X, Y, x for i = 1 to m Compute distance d(Xi, x) end Compute set I containing indices for the k smallest distances d(Xi,x) Return majority label for {Yi where i ∈ I } |
| Input: A training set {X, T} = {xi, ti}Ni = 1 Output: A trained ELM model (Standard ELM phase) Let k = 0, Calculate the hidden layer output matrix H0 using initial training data Estimate the initial output weight β0 → P0 = (H0TH0)−1 (OS- ELM phase) - When the (k + 1)-th chunk of new data {Xk+1, Tk+1} arrives, update the hidden layer output matrix as Hk+1 = [HkT, ΔHk+1T]T where ΔHk+1 is the hidden layer output matrix corresponding to the newly arrived data - Update the output weights as βk+1 = βk + Pk+1Hk+1T(Tk+1 − Hk+1βk) where Pk+1 = Pk − Pk Hk+1T(I + Hk+1PHk+1T)−1Hk+1Pk - Set k = k + 1 |
| Input: A training set {X, T} = {xi, ti}Ni =1 ⊂ Rn×R The hidden node output function H(a, b, x), the continuous target function f and the hidden node number L, and the expected learning accuracy η. (Initialization) Let the number of hidden nodes L = 0, residual error E = T, where t = [t1,..., tN]. (Learning step) while L < Lmax, ||E|| > η Increase by one the number of hidden nodes L:L = L+1 if L∈{2n + 1, n∈Z} then -Assign random input weight aL and bias bL for new hidden node L -Calculate the output weight βL for the new hidden node βL: β2n+1 = (e2n, He2n+1)/||He2n+1||2 -Calculate E after adding the new hidden node L:E = E-HL · βL end if if L∈{2n, n∈Z} then -Calculate the error feedback function sequence HL: H2ne= e2n-1 (β2n-1)−1, where, en = f − fn. -Calculate the input weight aL, bias bL and update HL for the new hidden node L -Calculate the output weight βL for the new hidden node βL: β2n = (e2n-1, He2n)/||He2n||2 -Calculate E after adding the new hidden node L:E =E-HL βL end if end while |
| Algorithms | User Parameters |
|---|---|
| KNN | -Number of nearest neighbors = 5 |
| ANNs | -Training function = Bayesian regularization back-propagation (TRAINBR) -Adaptation learning function = Bias learning function (LEARNGD) -Transfer function = Log-sigmoid (LOGISIG) -Number of layers = 3 -Number of neurons = 10 -70% training, 15% validation, and 15% test datasets, respectively |
| SVM | -Mathematical functions = Kernel Functions -Polynomial order = 3 |
| ELM | -Activation function = Sine function -Number of hidden neurons = 52 |
| Performance Indices | KNN | ANNs | SVM | ELM |
|---|---|---|---|---|
| S | 0.418 | 0.749 | 0.754 | 0.891 |
| SCLF | 0.512 | 0.708 | 0.786 | 0.841 |
| STTD | 0.323 | 0.789 | 0.722 | 0.941 |
| F1 | 0.048 | 0.558 | 0.694 | 0.764 |
| TNR | 1.000 | 0.952 | 0.967 | 0.959 |
| TPR | 0.025 | 0.464 | 0.604 | 0.722 |
| PPV | 1.000 | 0.700 | 0.815 | 0.810 |
| Accuracy | 0.810 | 0.857 | 0.876 | 0.913 |
| TP | 10 | 189 | 246 | 294 |
| FP | 0 | 81 | 56 | 69 |
| TN | 1682 | 1601 | 1626 | 1613 |
| FN | 397 | 218 | 161 | 113 |
| Performance Indices | ELM | OS-ELM | B-ELM | W-ELM |
|---|---|---|---|---|
| S | 0.891 | 0.910 | 0.900 | 0.906 |
| SCLF | 0.841 | 0.880 | 0.865 | 0.832 |
| STTD | 0.941 | 0.940 | 0.935 | 0.980 |
| F1 | 0.764 | 0.806 | 0.768 | 0.744 |
| TNR | 0.959 | 0.952 | 0.958 | 0.951 |
| TPR | 0.722 | 0.808 | 0.732 | 0.713 |
| PPV | 0.810 | 0.804 | 0.808 | 0.777 |
| Accuracy | 0.913 | 0.924 | 0.914 | 0.904 |
| TP | 294 | 329 | 298 | 290 |
| FP | 69 | 80 | 71 | 83 |
| TN | 1613 | 1602 | 1611 | 1599 |
| FN | 113 | 78 | 109 | 117 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Choi, Y.H.; Sadollah, A.; Kim, J.H. Improvement of Cyber-Attack Detection Accuracy from Urban Water Systems Using Extreme Learning Machine. Appl. Sci. 2020, 10, 8179. https://doi.org/10.3390/app10228179
Choi YH, Sadollah A, Kim JH. Improvement of Cyber-Attack Detection Accuracy from Urban Water Systems Using Extreme Learning Machine. Applied Sciences. 2020; 10(22):8179. https://doi.org/10.3390/app10228179
Chicago/Turabian StyleChoi, Young Hwan, Ali Sadollah, and Joong Hoon Kim. 2020. "Improvement of Cyber-Attack Detection Accuracy from Urban Water Systems Using Extreme Learning Machine" Applied Sciences 10, no. 22: 8179. https://doi.org/10.3390/app10228179
APA StyleChoi, Y. H., Sadollah, A., & Kim, J. H. (2020). Improvement of Cyber-Attack Detection Accuracy from Urban Water Systems Using Extreme Learning Machine. Applied Sciences, 10(22), 8179. https://doi.org/10.3390/app10228179







