Data Sharing System Integrating Access Control Mechanism using Blockchain-Based Smart Contracts for IoT Devices
Abstract
1. Introduction
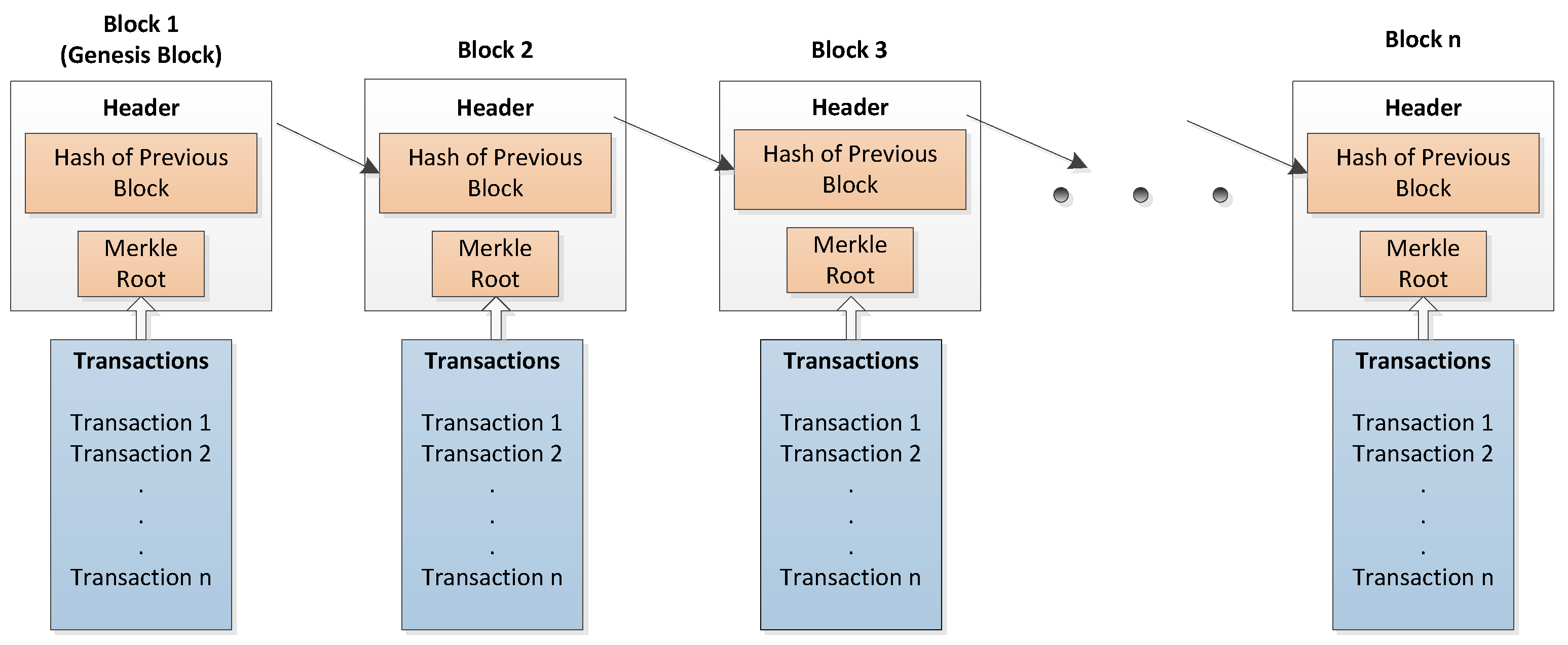
1.1. Blockchain
1.1.1. Ledger
1.1.2. Smart Contract
1.1.3. Consensus Mechanism
1.1.4. Cryptography
1.2. Motivation
1.3. Problem Statement
1.4. Contributions
- a blockchain-based system is proposed for efficient data sharing, trustworthy and authorized access control among IoT devices’ users,
- multiple smart contracts are used for efficient, secure, authorized, and trust-based access management of users in the network,
- secure and reliable data sharing is also achieved through smart contracts,
- one main smart contract; i.e., Access Control Contract (ACC) is used to manage the overall access control and sharing among users and also to enhance efficiency of the system in terms of cost,
- authentication of users in the network is maintained by Register Contract (RC) through users’ registration and the record is maintained in the user registration table,
- misbehavior of users is checked by JC; after that, the corresponding penalty is determined,
- misbehavior of each user is recorded in the system by creating a subject misbehavior record table,
- different permission levels are set to provide permissioned access rights to users, and to achieve the trustful and reliable sharing,
- in addition, both transaction and execution costs of smart contracts and their functions are calculated, and
- at the end, a comparison is made between existing and proposed systems, which is given in Table 1.
2. Related Work
3. Objectives of the Proposed Access Control and Data Sharing System
- Trustfulness: The trust of IoT devices’ users is maintained through a misbehavior-judging method, which is implemented by JC. The users who misbehave are known as untrusted users and are penalized. Only the trusted users are allowed to access their required services.
- Authentication: In this system, authentication of users is done by RC. Any user, who becomes part of the system is registered by RC. Furthermore, a record is maintained in the user registration table.
- Authorized access: In this system, only authorized users are allowed to access their required services. The users’ authorization is maintained through permission levels.
- Efficient data sharing: The data sharing among IoT devices’ users is maintained through the ACC. Which maintains the sharing of services among users. Furthermore, the permission-based sharing is also achieved through the permission levels.
- Understanding of user behavior [33]: In this system, the behavior of users is checked by implementing behavior judging method in JC. Misbehavior is conducted by subjects by sending too many requests. After identifying misbehavior, the requests of subjects are halted for a particular time. That is why, only the users who behave well are provided with the requested services.
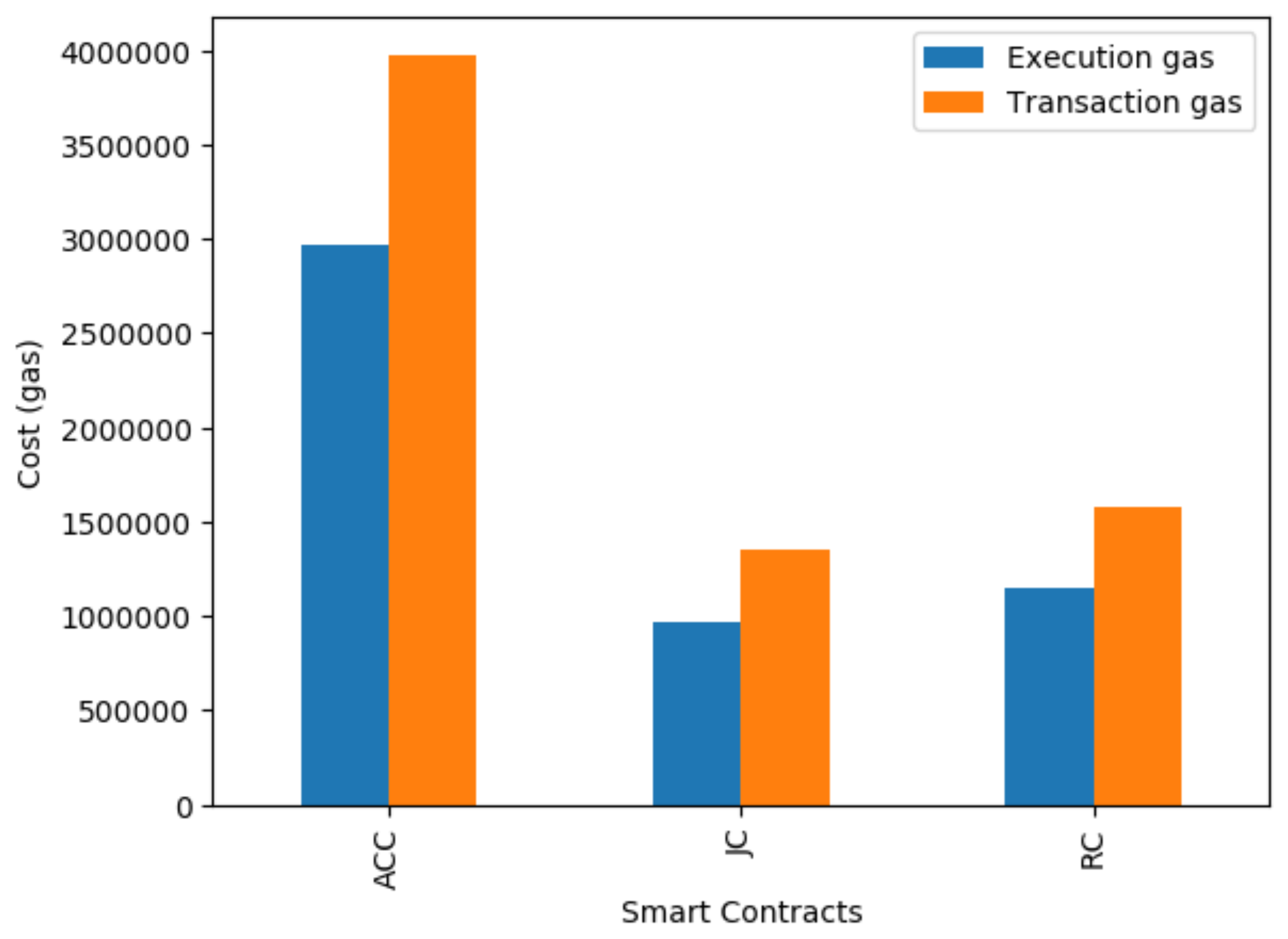
- Less cost consumption: The system consists of three smart contracts, as in [1]. In the previous scheme, ACC is generated by users, for every transaction. It will increase the overall cost of the system. However, in this system, single ACC is used to control the access of the system. It also reduces the cost in terms of gas consumption of smart contracts, which is given in the comparison section.
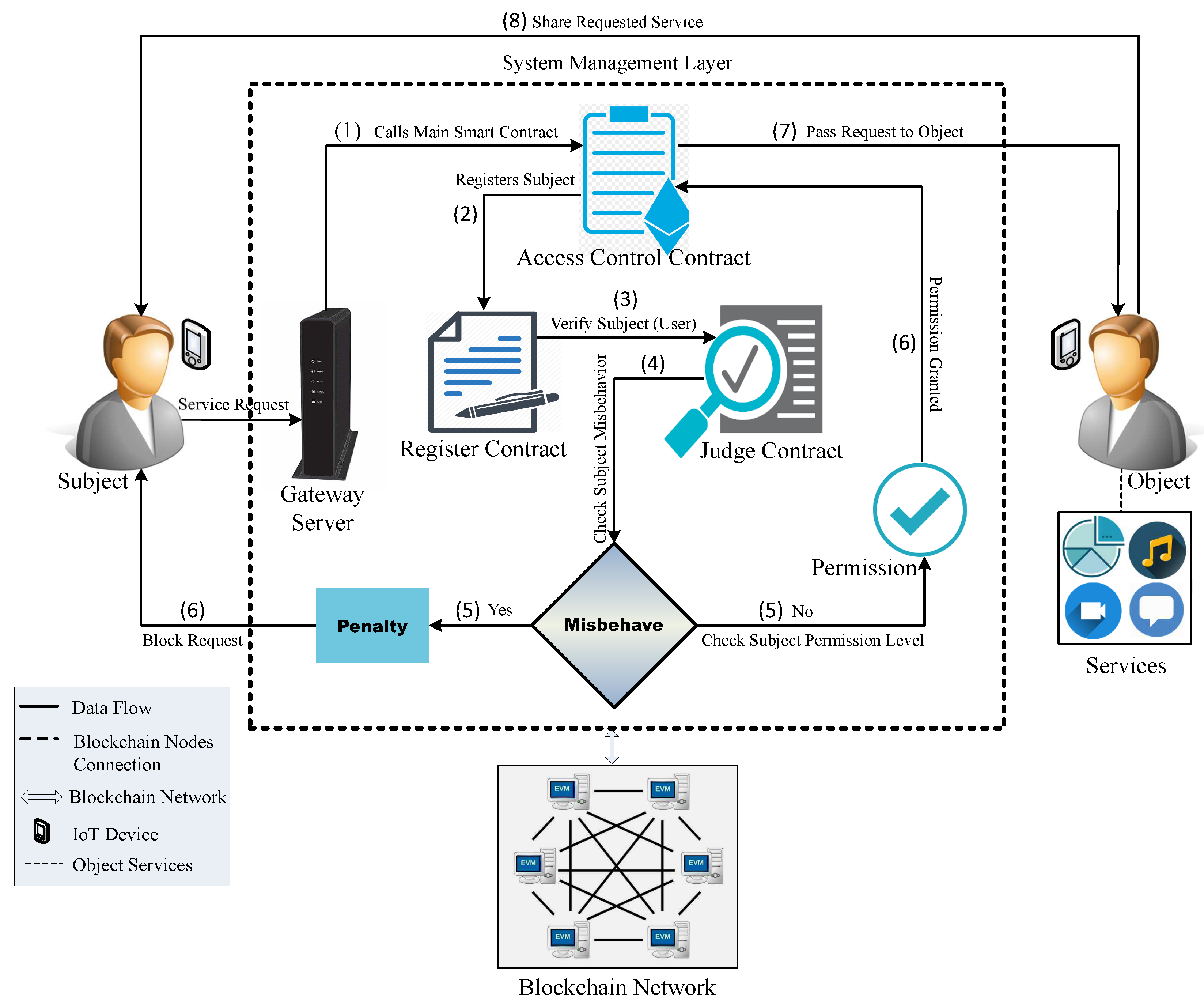
4. Proposed System Model
4.1. Smart Contracts
4.1.1. ACC
4.1.2. RC
- subject: the particular user that sends the service request,
- object: user that contains required services and entertains the request of the subject,
- service: particular data or service, which is requested by the subject, and
- time: the time at which a request is generated.
4.1.3. JC
- Access Authorized !
- Requests are Blocked !
- Static Check Failed !
- Misbehavior Detected !
- Static Check failed & Misbehavior Detected !
4.2. Misbehavior
- subject sends too frequent service access requests,
- subject sends multiple access requests for service(s) in a particular time, i.e., 5 requests in 10 min, and
- the request is canceled after generation.
4.3. Data Permission Control
- L0: Data is not accessible,
- L1: Data can be used in aggregated computation without revealing the raw data [10],
- L2: Data is partly allowed, and
- L3: Data or service is accessible.
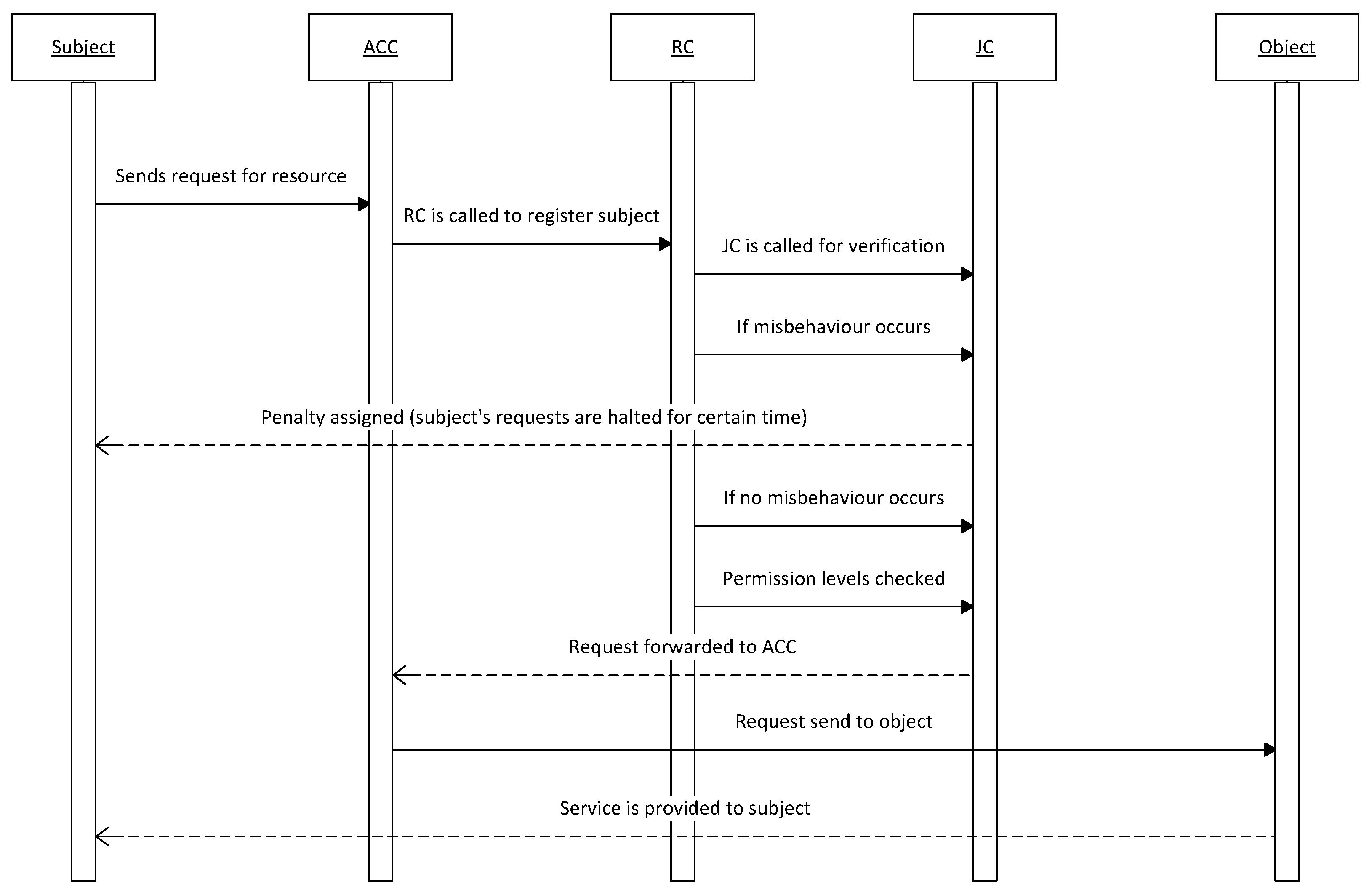
4.4. Workflow of System Model
- at fist, a subject sends request for any service (i.e., data, file, storage unit) in the IoT networks,
- further, communication and access management for subject is managed by the smart contracts in blockchain,
- when the request of subject is generated, ACC (main smart contract) is executed to control the overall access management,
- after that, authentication of the users is done by the RC, which registers the users’ information and maintains records of users via a registration table,
- then, trustfulness of the system is maintained by JC, which checks the behavior of a subject,
- if any type of misbehavior is conducted by the subject, JC determines penalty for the subject and halt its state in the system,
- in another case, if no misbehavior is done, then permission level for the subject is checked,
- then ACC forwards the request of subjects to corresponding objects,
- after that, request of the subject is fulfilled by the object, and
- at last, transaction is stored into the blockchain.
5. Simulations and Results
5.1. Simulations Setting
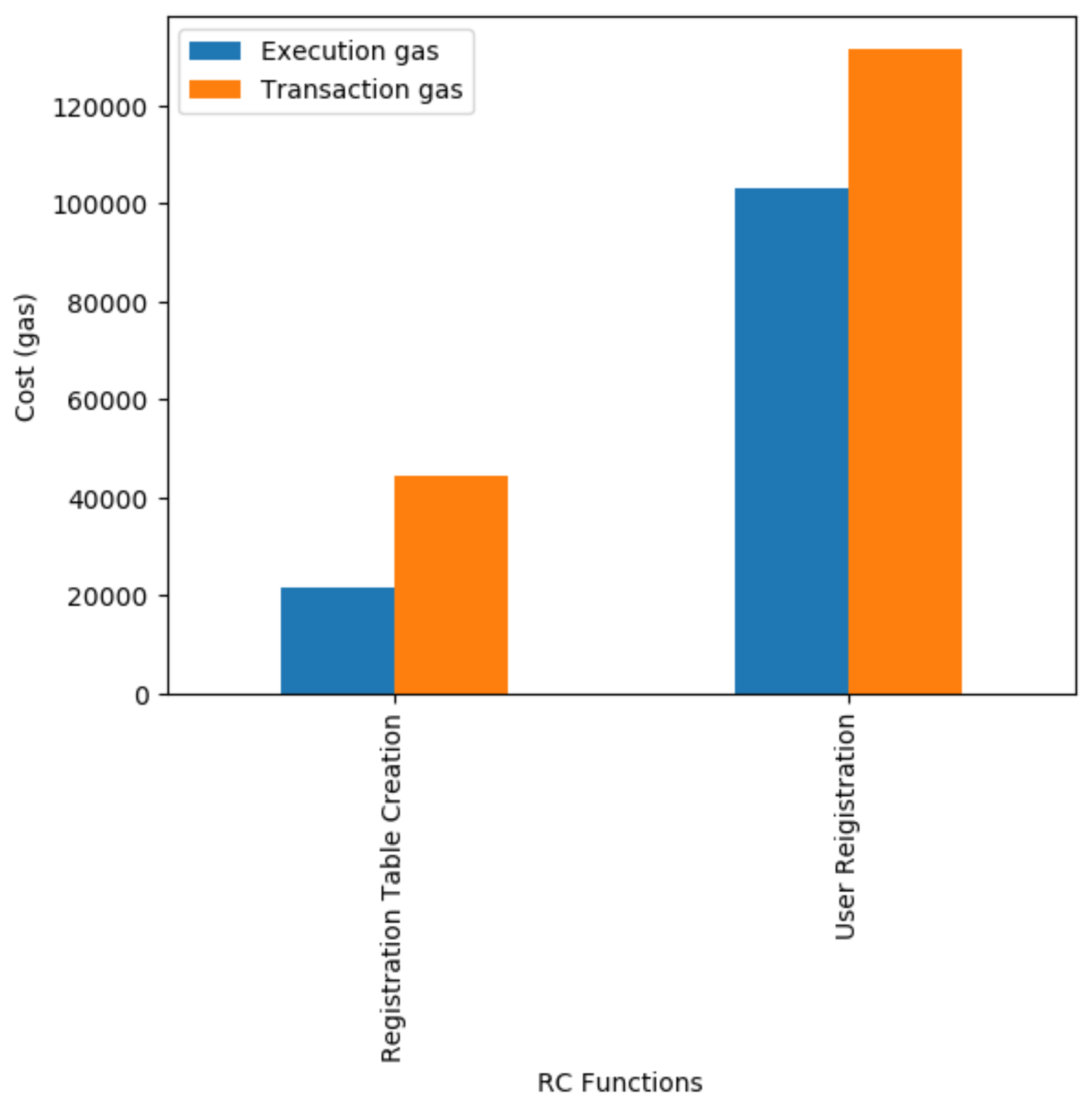
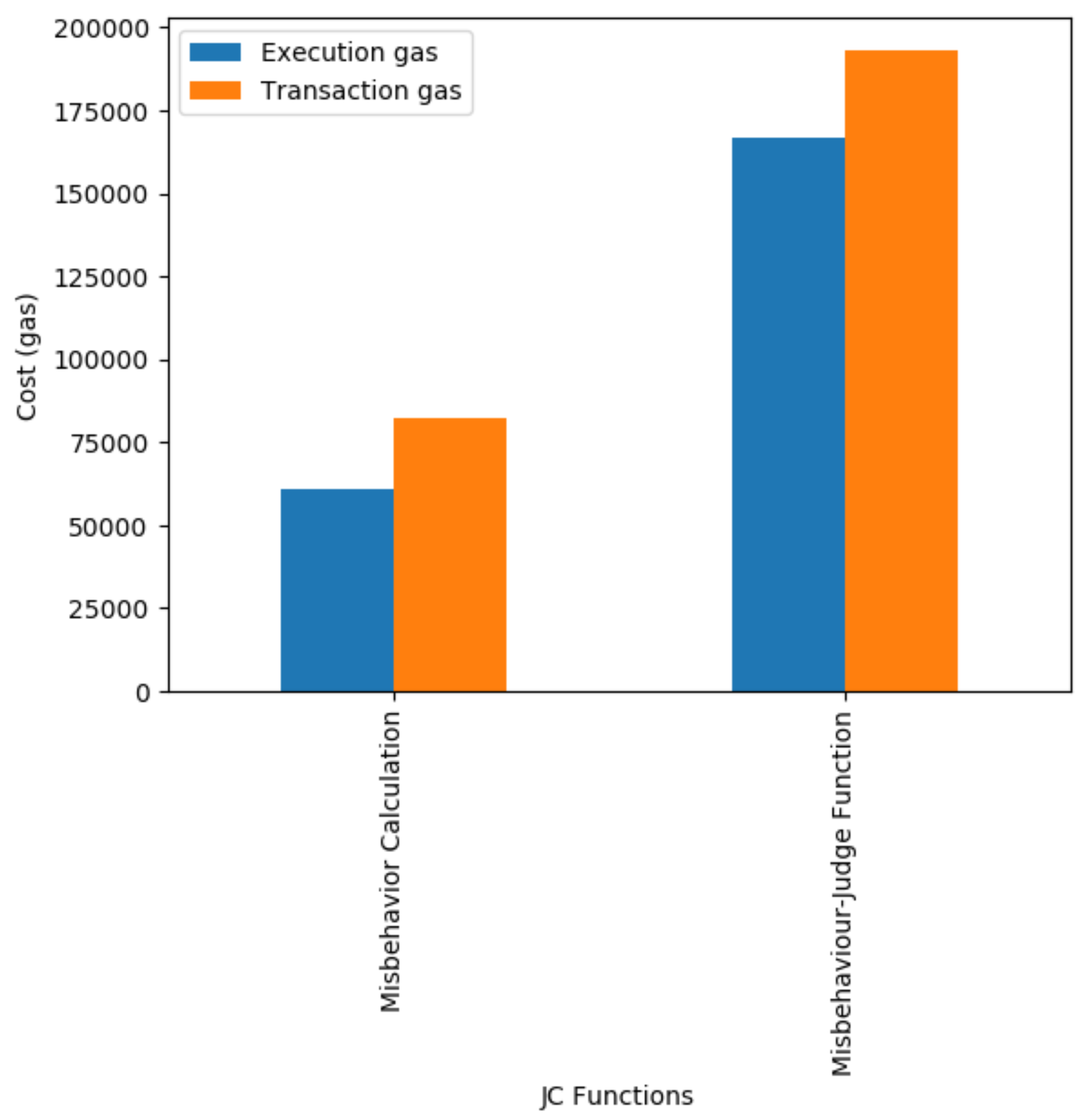
5.2. Cost Consumption
5.2.1. Smart Contracts Cost
5.2.2. Functions Cost
6. Analysis and Comparison
Comparison
- Availability: Any user can easily access the system, whenever it requires any service. As the public blockchain is open and available. The users can easily become part of the system.
- Trustfulness: The trustfulness of users is maintained through the JC smart contract. JC implements the behavior judging method that judges the behavior of each subject. If the misbehavior is conducted by subject, it is known as untrusted and its requests are halted for a particular time period. In another case, if the misbehavior is not conducted, then subject is considered as trusted.
7. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
Abbreviations
| ABAC | Attribute-Based Access Control |
| ABE | Attribute-Based Encryption |
| ACC | Access Control Contract |
| AES | Advanced Encryption Standard |
| AI | Artificial Intelligence |
| CNN | Conventional Neural Network |
| CSI | Channel State Information |
| D2D | Device-to-Device |
| DES | Data Encryption Standard |
| DRL | Deep Reinforcement Learning |
| DSA | Digital Signature Algorithm |
| DSSCB | Data security Sharing and Storage system based on Consortium Blockchain |
| DTLS | Datagram Transport Layer Security |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| EHRs | Electronic Health Records |
| FBSS | Fair Blind Signature Scheme |
| IDE | Integrated Development Environment |
| IoT | Internet of Things |
| JC | Judge Contract |
| Lw | Lightweight |
| MTs | Mobile Terminals |
| NBT | Naive Bayes Theorem |
| P2P | Peer-to-Peer |
| PBFT | Practical Byzantine Fault Tolerance |
| PoA | Proof of Authority |
| PoC | Proof of Concept |
| PoS | Proof of Stake |
| PoW | Proof of Work |
| RC | Register Contract |
| RSA | Rivest-Shamir-Adleman |
| SCKBS | Self Certified public Key Based System |
| SHA | Secure Hash Algorithm |
| XACML | eXtensible Access Control Markup Language |
References
- Zhang, Y.; Kasahara, S.; Shen, Y.; Jiang, X.; Wan, J. Smart Contract-Based Access Control for the Internet of Things. IEEE Internet Things J. 2018, 6, 1594–1605. [Google Scholar] [CrossRef]
- Novo, O. Scalable Access Management in IoT Using Blockchain: A Performance Evaluation. IEEE Internet Things J. 2018, 6, 4694–4701. [Google Scholar] [CrossRef]
- Ding, S.; Cao, J.; Li, C.; Fan, K.; Li, H. A Novel Attribute-Based Access Control Scheme Using Blockchain for IoT. IEEE Access 2019, 7, 38431–38441. [Google Scholar] [CrossRef]
- Lin, D.; Tang, Y. Blockchain Consensus Based User Access Strategies in D2D Networks for Data-Intensive Applications. IEEE Access 2018, 6, 72683–72690. [Google Scholar] [CrossRef]
- Jiang, Y.; Wang, C.; Wang, Y.; Gao, L. A Cross-Chain Solution to Integrating Multiple Blockchains for IoT Data Management. Sensors 2019, 19, 2042. [Google Scholar] [CrossRef]
- Ma, M.; Shi, G.; Li, F. Privacy-Oriented Blockchain-Based Distributed Key Management Architecture for Hierarchical Access Control in the IoT Scenario. IEEE Access 2019, 7, 34045–34059. [Google Scholar] [CrossRef]
- Sifah, E.B.; Xia, Q.; Agyekum, K.O.-B.O.; Amofa, S.; Gao, J.; Chen, R.; Xia, H.; Gee, J.C.; Du, X.; Guizani, M. Chain-based big data access control infrastructure. J. Supercomput. 2018, 74, 4945–4964. [Google Scholar] [CrossRef]
- Liu, H.C.; Lin, Q.; Wen, S. Blockchain-enabled Data Collection and Sharing for Industrial IoT with Deep Reinforcement Learning. IEEE Trans. Ind. Inform. 2018, 15, 3516–3526. [Google Scholar] [CrossRef]
- Xu, Y.; Wang, G.; Yang, J.; Ren, J.; Zhang, Y.; Zhang, C. Towards Secure Network Computing Services for Lightweight Clients Using Blockchain. Wirel. Commun. Mob. Comput. 2018, 2018, 1–12. [Google Scholar] [CrossRef]
- Zhang, G.; Li, T.; Li, Y.; Hui, P.; Jin, D. Blockchain-Based Data Sharing System for AI-Powered Network Operations. J. Commun. Inf. Netw. 2018, 3, 1–8. [Google Scholar] [CrossRef]
- Kang, J.; Yu, R.; Huang, X.; Wu, M.; Maharjan, S.; Xie, S.; Zhang, Y. Blockchain for secure and efficient data sharing in vehicular edge computing and networks. IEEE Internet Things J. 2019, 6, 4660–4670. [Google Scholar] [CrossRef]
- Rahman, A.; Rashid, M.; Hossain, M.S.; Hassanain, E.; Alhamid, M.F.; Guizani, M. Blockchain and IoT-Based Cognitive Edge Framework for Sharing Economy Services in a Smart City. IEEE Access 2019, 7, 18611–18621. [Google Scholar] [CrossRef]
- Zhang, L.; Luo, M.; Li, J.; Au, M.H.; Choo, K.-K.R.; Chen, T.; Tian, S. Blockchain based secure data sharing system for Internet of vehicles: A position paper. Veh. Commun. 2019, 16, 85–93. [Google Scholar] [CrossRef]
- Wu, A.; Zhang, Y.; Zheng, X.; Guo, R.; Zhao, Q.; Zheng, D. Efficient and privacy-preserving traceable attribute-based encryption in blockchain. Ann. Telecommun. 2019, 74, 401–411. [Google Scholar] [CrossRef]
- Zhang, X.; Chen, X. Data Security Sharing and Storage Based on a Consortium Blockchain in a Vehicular Ad-hoc Network. IEEE Access 2019, 7, 58241–58254. [Google Scholar] [CrossRef]
- Chen, L.; Lee, W.-K.; Chang, C.-C.; Choo, K.-K.R.; Zhang, N. Blockchain based searchable encryption for electronic health record sharing. Future Gener. Comput. Syst. 2019, 95, 420–429. [Google Scholar] [CrossRef]
- Lin, C.; He, D.; Huang, X.; Choo, K.-K.R.; Vasilakos, A.V. BSeIn: A blockchain-based secure mutual authentication with fine-grained access control system for industry 4.0. J. Netw. Comput. Appl. 2018, 116, 42–52. [Google Scholar] [CrossRef]
- Sultana, T.; Ghaffar, A.; Azeem, M.; Abubaker, Z.; Gurmani, M.U.; Javaid, N. Data Sharing System Integrating Access Control Based on Smart Contracts for IoT. In Proceedings of the International Conference on P2P, Parallel, Grid, Cloud and Internet Computing, Antwerp, Belgium, 7–9 November 2019; Springer: Cham, Switzerland, 2019; pp. 863–874. [Google Scholar]
- Hammi, M.T.; Hammi, B.; Bellot, P.; Serhrouchni, A. Bubbles of Trust: A decentralized blockchain-based authentication system for IoT. Comput. Secur. 2018, 78, 126–142. [Google Scholar] [CrossRef]
- Ren, Y.; Zhu, F.; Qi, J.; Wang, J.; Sangaiah, A.K. Identity Management and Access Control Based on Blockchain under Edge Computing for the Industrial Internet of Things. Appl. Sci. 2019, 9, 2058. [Google Scholar] [CrossRef]
- Yang, J.; Lu, Z.; Wu, J. Smart-toy-edge-computing-oriented data exchange based on blockchain. J. Syst. Arch. 2018, 87, 36–48. [Google Scholar] [CrossRef]
- Maesa, D.D.F.; Mori, P.; Ricci, L. A blockchain based approach for the definition of auditable Access Control systems. Comput. Secur. 2019, 84, 93–119. [Google Scholar] [CrossRef]
- Mateen, A.; Javaid, N.; Iqbal, S. Towards Energy Efficient Routing in Blockchain Based Underwater WSNs via Recovering the Void Holes. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Khan, R.J.H.; Javaid, N.; Iqbal, S. Blockchain Based Node Recovery Scheme for Wireless Sensor Networks. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Naz, M.; Javaid, N.; Iqbal, S. Research Based Data Rights Management Using Blockchain Over Ethereum Network. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Noshad, Z.; Javaid, N.; Imran, M. Analyzing and Securing Data using Data Science and Blockchain in Smart Networks. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Ali, I.; Javaid, N.; Iqbal, S. An Incentive Mechanism for Secure Service Provisioning for Lightweight Clients Based on Blockchain. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Samuel, O.; Javaid, N.; Awais, M.; Ahmed, Z.; Imran, M.; Guizani, M. A Blockchain Model for Fair Data Sharing in Deregulated Smart Grids. In Proceedings of the IEEE Global Communications Conference (GLOBCOM), Big Island, HI, USA, 9–13 December 2019. [Google Scholar]
- Rehman, M.; Javaid, N.; Awais, M.; Imran, M.; Naseer, N. Cloud based Secure Service Providing for IoTs using Blockchain. In Proceedings of the IEEE Global Communications Conference (GLOBCOM), Big Island, HI, USA, 9–13 December 2019. [Google Scholar]
- Javaid, A.; Javaid, N.; Imran, M. Ensuring Analyzing and Monetization of Data Using Data Science and Blockchain in LoT Devices. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Kazmi, H.S.Z.; Javaid, N.; Imran, M. Towards Energy Efficiency and Trustfulness in Complex Networks Using Data Science Techniques and Blockchain. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Zahid, M.; Javaid, N.; Rasheed, M.B. Balancing Electricity Demand and Supply in Smart Grids Using Blockchain. Master’s Thesis, COMSATS University Islamabad (CUI), Islamabad, Pakistan, 2019. [Google Scholar]
- Zhang, T.; Pota, H.; Chu, C.-C.; Gadh, R. Real-time renewable energy incentive system for electric vehicles using prioritization and cryptocurrency. Appl. Energy 2018, 226, 582–594. [Google Scholar] [CrossRef]

| Systems | Execution Cost | Transaction Cost |
|---|---|---|
| Access control system [1] | 5,484,074 gas units | - |
| Data sharing model [10] | 458,761 gas units | 662,673 gas units |
| Proposed data sharing and access control system | 5,200,000 gas units | 6,900,000 gas units |
| Techniques | Problems Addressed | Contributions | Evaluations | Limitations |
|---|---|---|---|---|
| Blockchain [1] | Critical access control | Smart contracts-based access control | Gas price and misbehavior | Cost and overhead |
| DTLS protocol [2] | Security, centralization | Access management architecture | Throughput, latency, and response time | Single management hub |
| PoC, AES-128, PBFT [3] | Complexity and security | ABAC and hash operation | Overhead | Consensus mechanism not efficient |
| PBFT, CNN [4] | Unauthorized access | D2D underlying cellular networks | Channel rate and spectral efficiency | Non-cooperative scenarios |
| PoW, PBFT [5] | Data management and security | Decentralized access | Security and cost consumption | User privacy |
| PoW [6] | Untrustworthiness and centralization | Distributed key management system | Auditability and scalability | Not persistency |
| ECDSA, PoC [7] | Security and data mismanagement | Sovereign blockchain | Execution time | Inefficient in industries |
| DRL [8] | Limited MT resources and security | Secure sharing | Energy consumption and data collection ratio | Trustfulness and security |
| PoA, PoW [9] | Security and untrustworthy | Service provisioning mechanism | Delay, throughput, and gas consumption | Un-authorization |
| PBFT [10] | Complex system and AI bottleneck | Data sharing system | Security, privacy, and scalability | Lacks efficiency |
| ECDSA [11] | Constrained resources and trust | Reputation-based data sharing | Efficiency and security | Not suitable for large area networks |
| MEC tier, NBT, SHA-256 [12] | Insecure sharing | Certificate-less aggregate signature scheme | Tests on different scenarios | Lacks efficiency |
| PBFT [13] | Security and un-authorization | Secure data sharing | Security analysis and efficiency | Ethereum does not perform well |
| FBSS [14] | Bottleneck of ABE | Encryption-based sharing | Security analysis | Lack efficiency |
| PBFT, SHA-256 [15] | Untrustworthiness and communication overhead | Data security sharing and storage system | Safety analysis | Real-time authentication and message verification |
| PoW, SHA-256 [16] | Privacy leakage | Permission-based access | Execution time | Real world implementation |
| ECDSA [18] | Un-authentication and high cost | Decentralized authentication mechanism | Time and financial cost | Compromised devices |
| SCKBS [19] | Security risks | Identity-based access control mechanism | Energy consumption, requests per second | Inefficient access mechanisms |
| Chain-code algorithm [20] | Security, reliability, and privacy leakage | Data exchange system | Request speed and transaction time | Delivery time and throughput |
| XACML, PoC [21] | Resource protection | XACML-based access control system | Monetary cost, resource and time | Performance lacks |
| PBFT, cryptographic algorithms [22] | Security problems | Mutual authentication system | Transaction time | No real implementation |
| System Models | Scenarios | Implementations | Platforms | Simulation Environments |
|---|---|---|---|---|
| Access control system [1] | Access control in IoT | Remix IDE, Go language | Ethereum, raspberry pi | Javascript |
| Access control system [5] | Cross-chain based access control in IoT | - | IOTA and Tangle | Ubuntu 16.04 |
| Access control [6] | Access control with key management in IoT | - | Multiple public blockchains | OMNeT++ 5.4.1 |
| Secure data sharing [8] | Data sharing among MTs using deep learning | Go | Ethereum | Python |
| Data sharing model [10] | Data sharing in AI powered network | - | Hyperledger fabric | - |
| Proposed data sharing and access control model | Access control and data sharing | Solidity language | Ethereum, spyder | Remix IDE, python |
| Systems | Trustfulness | Authorization | Authentication | Validation | Decentralized | Reliability |
|---|---|---|---|---|---|---|
| Access control system [1] | Yes | No | No | Yes | Yes | No |
| Access control system [5] | No | No | No | No | Yes | No |
| Access control system [6] | No | Yes | No | No | Yes | Yes |
| Data sharing system [8] | No | No | Yes | Yes | Yes | Yes |
| Data sharing system [10] | Yes | No | No | No | Yes | No |
| Proposed data sharing and access control system | Yes | Yes | Yes | Yes | Yes | Yes |
| Subject | Object | Service | Time |
|---|---|---|---|
| Subject A | Object X | File-1 | 2019/5/17 11:12 |
| Subject B | Object Y | Program-2 | 2019/6/14 1:15 |
| Subject C | Object Z | File-3 | 2019/8/8 3:00 |
| Subject | Object | Misbehavior | Misbehavior-Time | Penalty |
|---|---|---|---|---|
| Subject-A | Object-X | Multiple requests in 3 min | 2019/3/27 11:12 | Request halted for 2 h |
| Subject-B | Object-Y | Canceled request | 2019/4/1 1:05 | Request halted for 10 min |
| Subject-C | Object-Z | Frequent requests | 2019/4/3 3:09 | Request halted for 3 h |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sultana, T.; Almogren, A.; Akbar, M.; Zuair, M.; Ullah, I.; Javaid, N. Data Sharing System Integrating Access Control Mechanism using Blockchain-Based Smart Contracts for IoT Devices. Appl. Sci. 2020, 10, 488. https://doi.org/10.3390/app10020488
Sultana T, Almogren A, Akbar M, Zuair M, Ullah I, Javaid N. Data Sharing System Integrating Access Control Mechanism using Blockchain-Based Smart Contracts for IoT Devices. Applied Sciences. 2020; 10(2):488. https://doi.org/10.3390/app10020488
Chicago/Turabian StyleSultana, Tanzeela, Ahmad Almogren, Mariam Akbar, Mansour Zuair, Ibrar Ullah, and Nadeem Javaid. 2020. "Data Sharing System Integrating Access Control Mechanism using Blockchain-Based Smart Contracts for IoT Devices" Applied Sciences 10, no. 2: 488. https://doi.org/10.3390/app10020488
APA StyleSultana, T., Almogren, A., Akbar, M., Zuair, M., Ullah, I., & Javaid, N. (2020). Data Sharing System Integrating Access Control Mechanism using Blockchain-Based Smart Contracts for IoT Devices. Applied Sciences, 10(2), 488. https://doi.org/10.3390/app10020488






