Reliability Improved Cooperative Communication over Wireless Sensor Networks
Abstract
:1. Introduction
- (1)
- A Reliability Improved Cooperative Communications (RICC) with adjustable data transmission power [31] is proposed, in which the residual energy in non-hotspots is fully utilized to increase the transmission power of nodes to improve the data transmission reliability, whereas in hotspot areas, the transmission power is unchanged to maintain the previous network lifetime. For cooperative communications, the higher the transmission power of the nodes is, the shorter the lifetime of the nodes is. Thus, if the data transmission reliability is kept the same as before, the network lifetime is damaged. Due to different nodes load different amount of data, the energy consumption of different nodes is different, the non-hotspots area has much energy left. Therefore, in this paper, RICC adopts higher transmission power in non-hotspot regions, while using the same transmission power in hotspots areas as in previous schemes. Because most nodes are in non-hotspot areas, RICC can effectively improve the data transmission reliability.To the best of our knowledge, for coding-based cooperative communication WSNs, RICC is the first data collection strategy that enhances the reliability without harming the lifetime.
- (2)
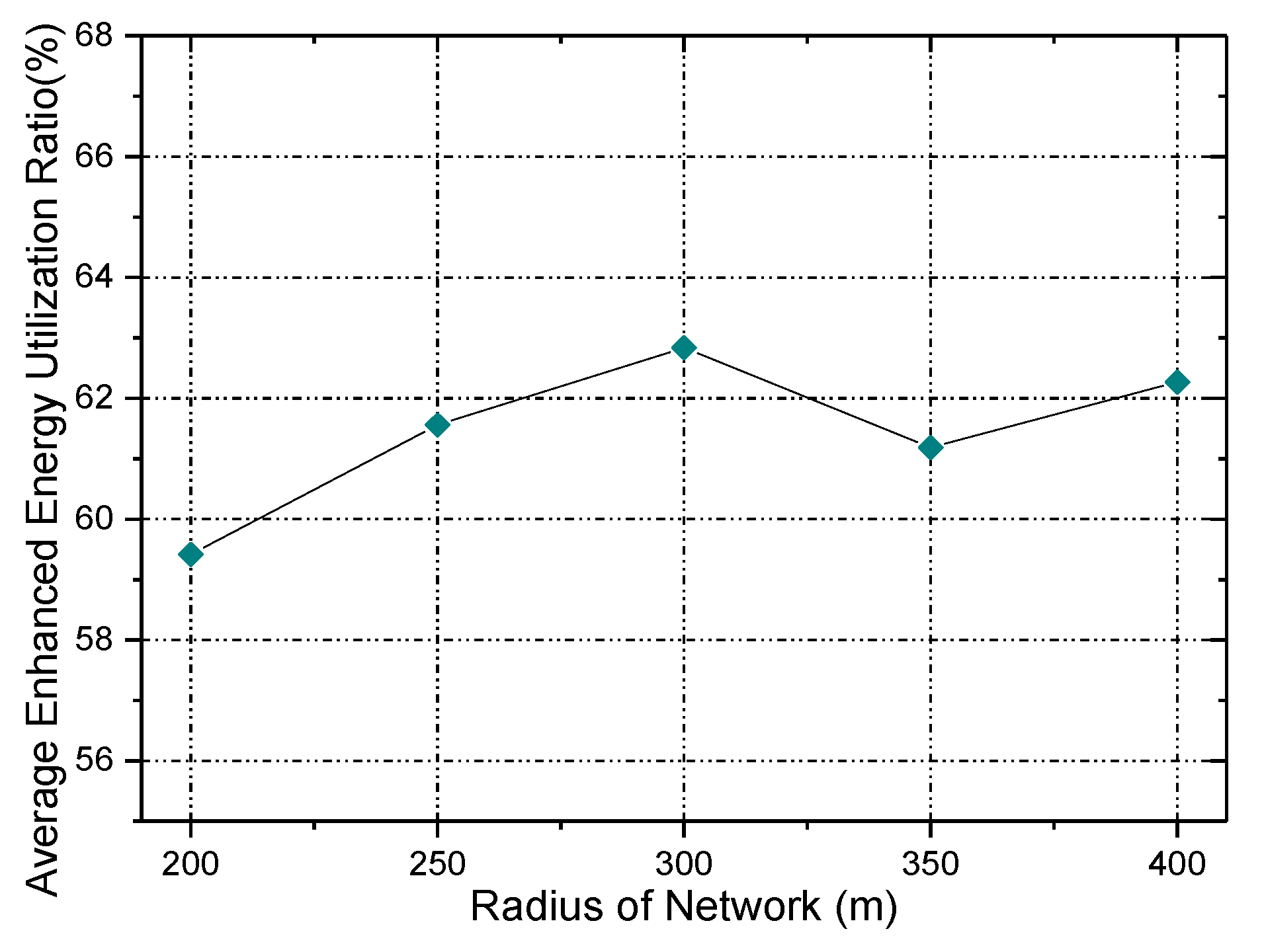
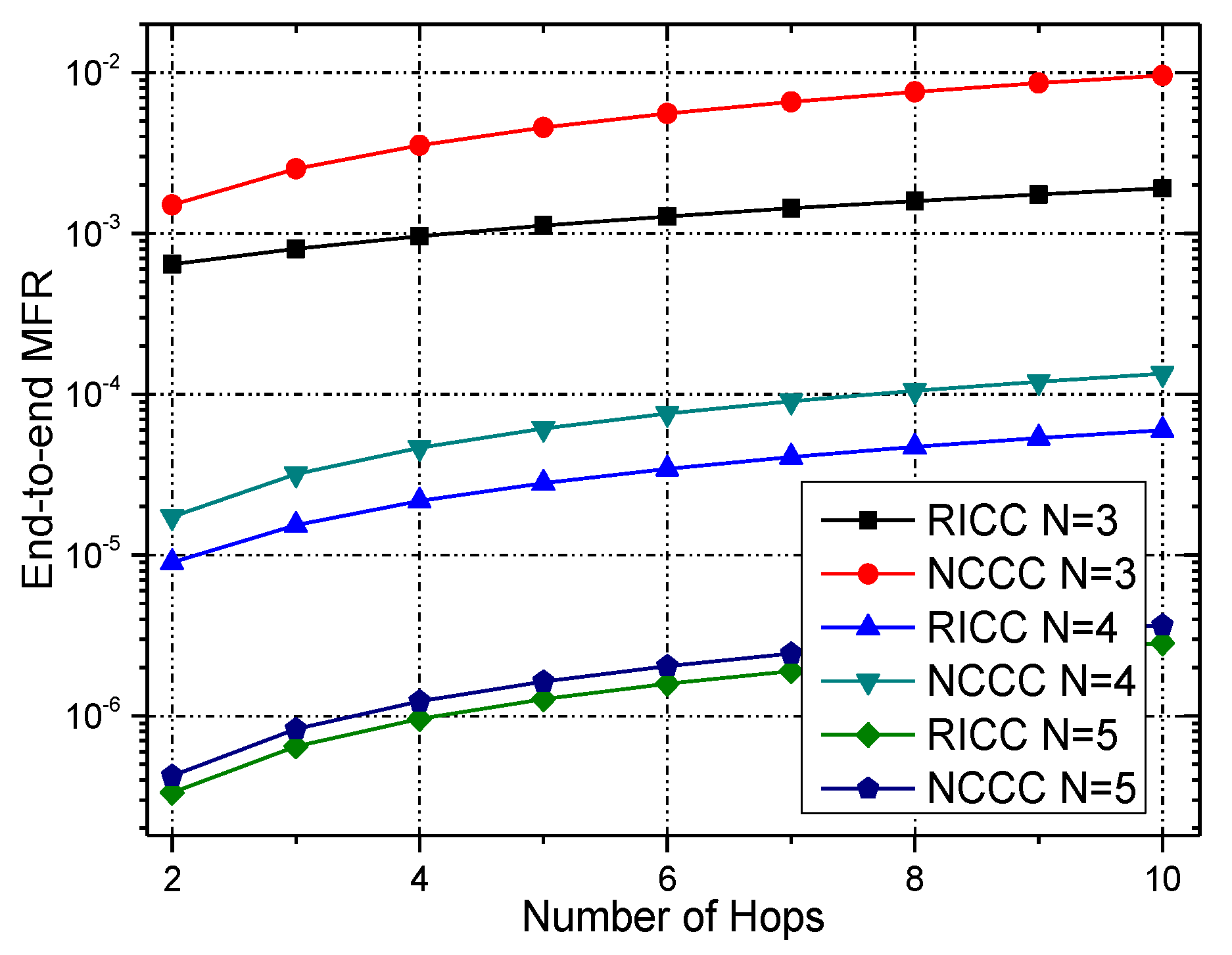
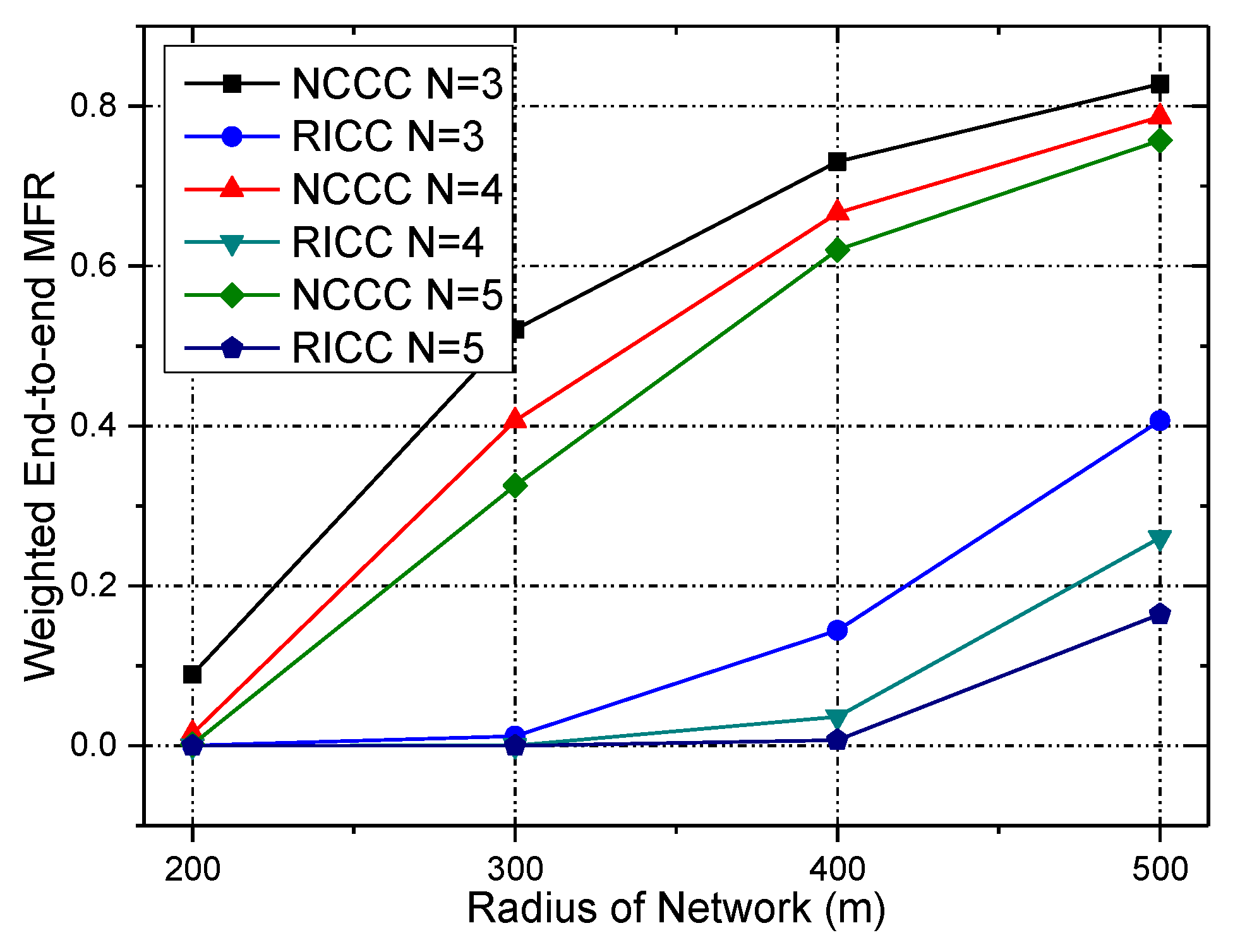
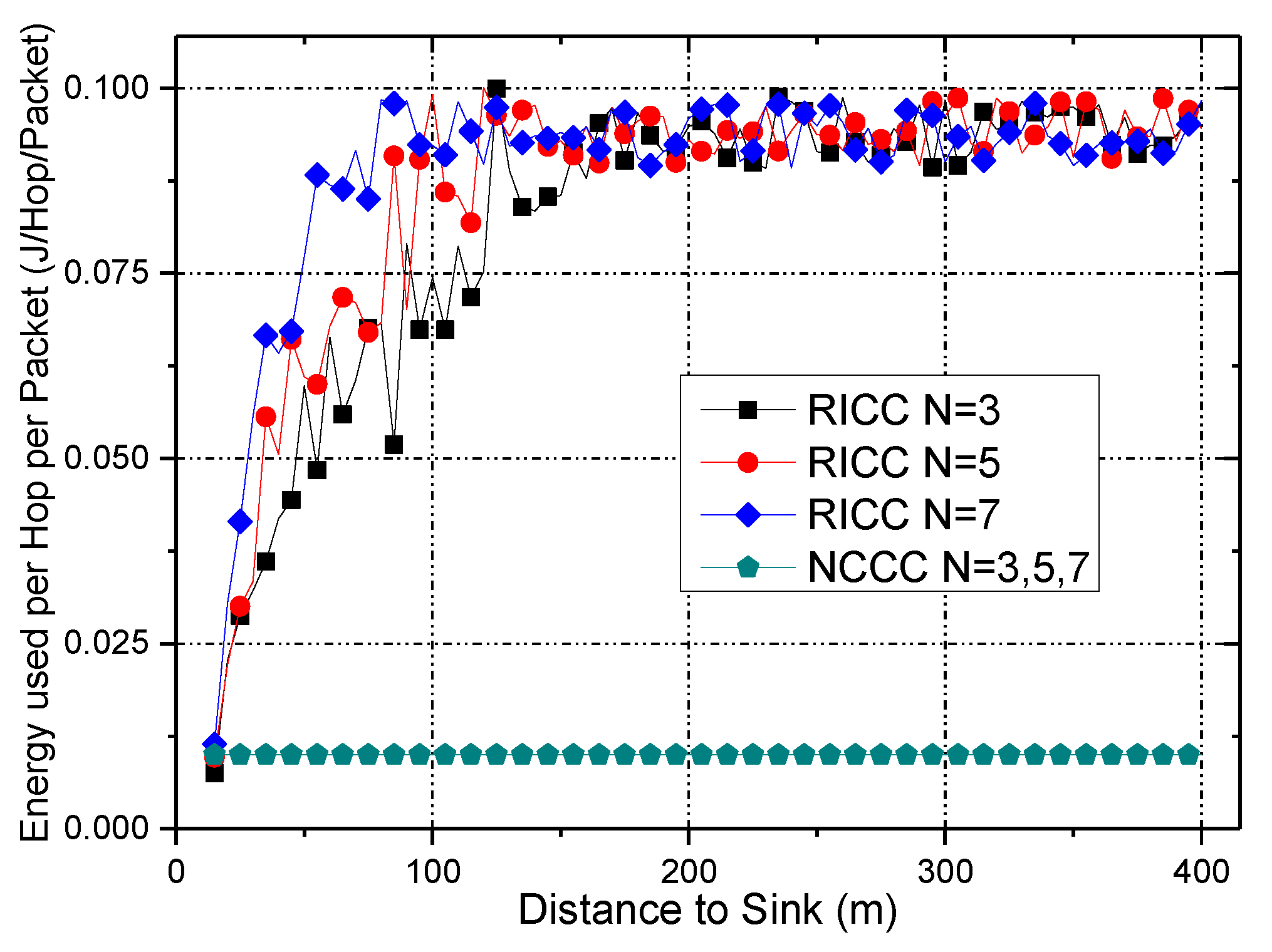
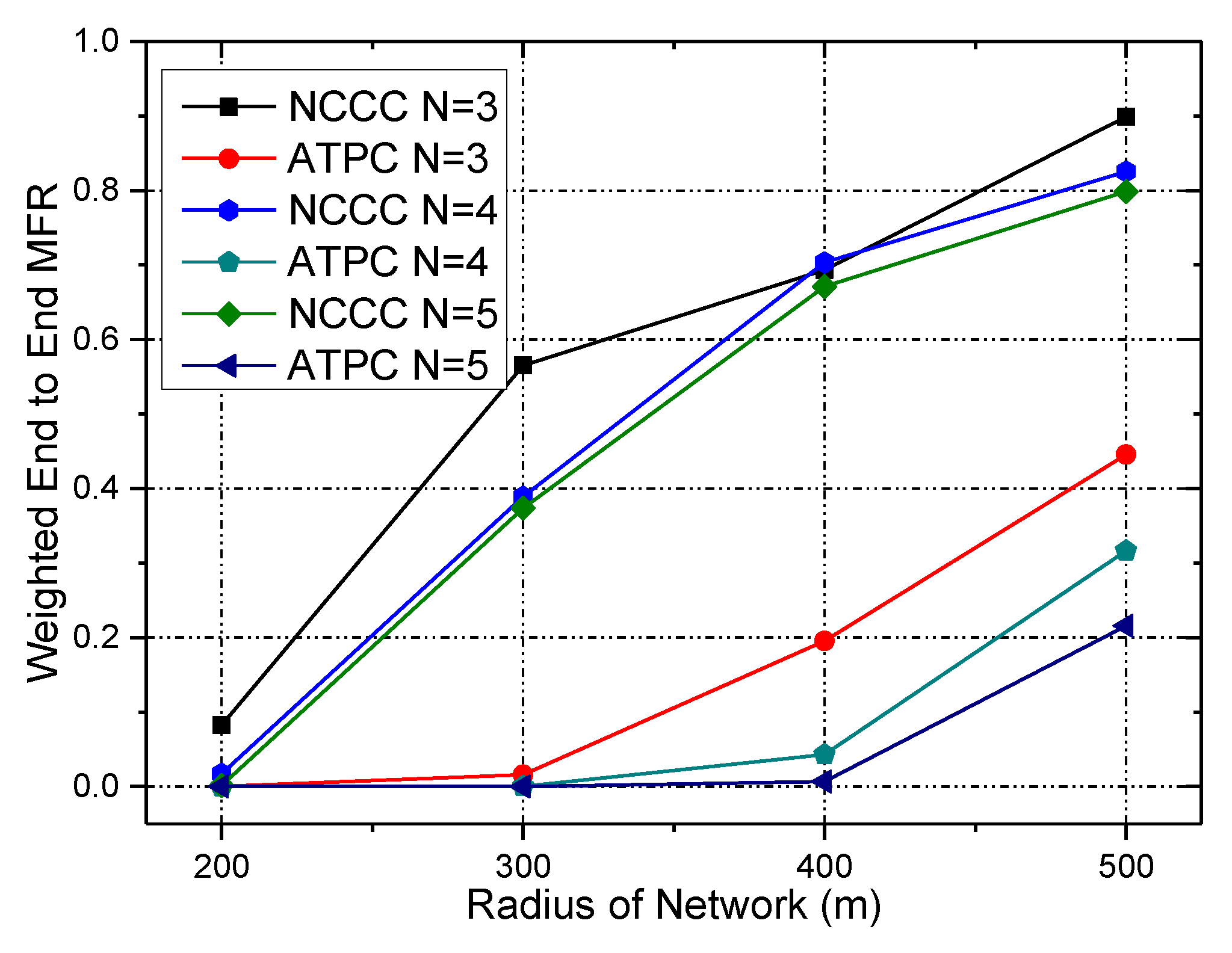
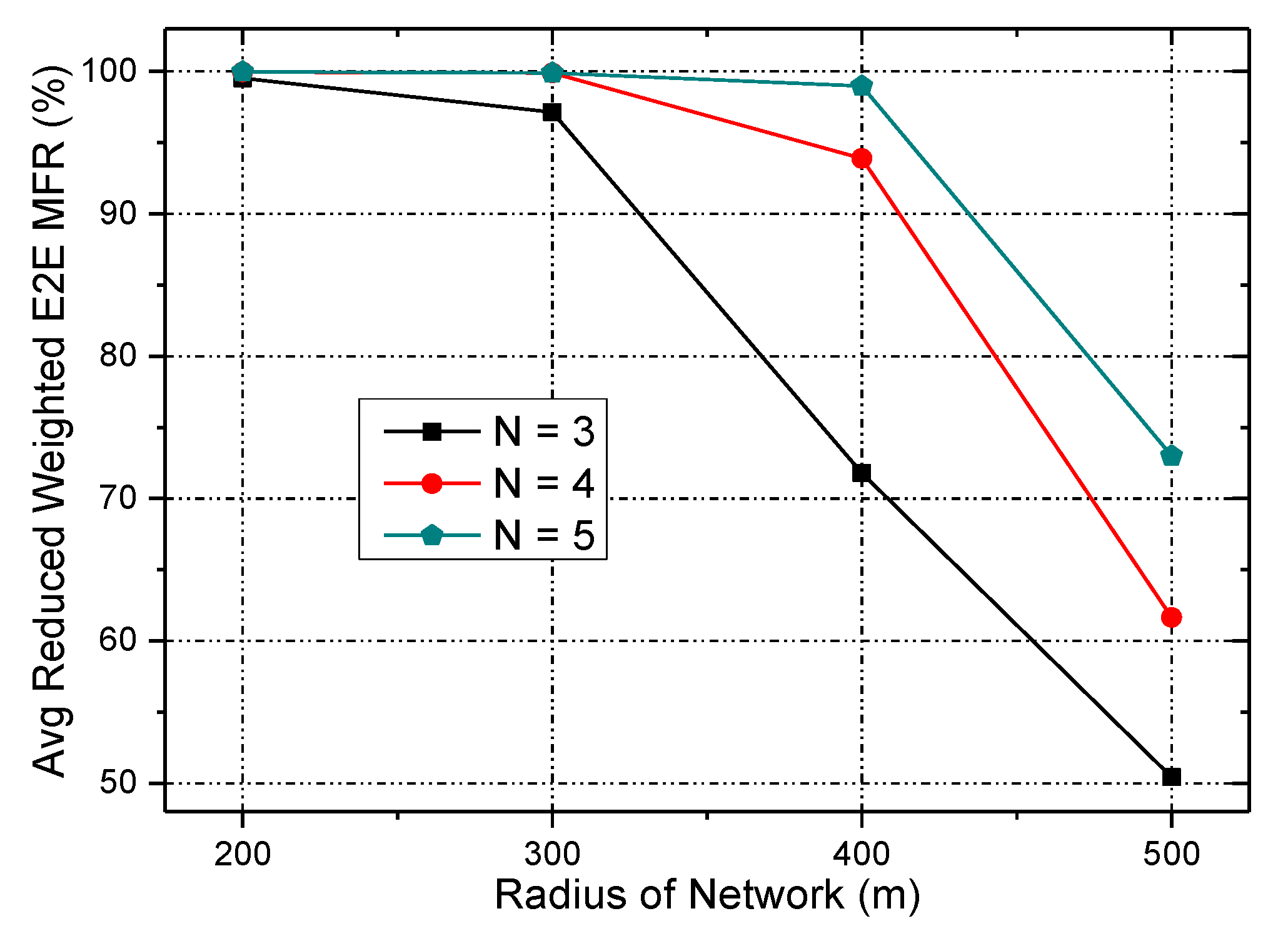
- The effectiveness of RICC is evaluated in this paper, and compared with Network Coding-based Cooperative Communications (NCCC), RICC has following features: (a) the network energy utilization ratio is enhanced by as much as 50% on average; and (b) it significantly improves the reliability of data collection, and specifically, under the same lifetime, RICC can reduce the weighted end-to-end MFR by approximately 59.4% to 62.8%.
2. Related Work
- (1)
- Retransmission-based mechanism. Automatic Repeat-Request can improve reliability of data transmission compared with traditions scheme [32]. The main strategy of an ARQ protocol is as follows: once node transmits a data packet, it waits for an acknowledgement (ACK, a message sent by the receiver) indicating that its data packet was correctly received. The sender does not send any additional packets until it receives an ACK signal or a timeout. In contrast, with GBN and SR, the nodes transmit packets continuously without the need to wait for individual ACKs from the receiver; only the ACK for the last packet is required [32]. In WSNs, an ACK could possibly be lost, which results in the transmitter resending a packet that was already successfully transmitted but an ACK was not received correctly or in time. Thus, in [33], we proposed a scheme to reduce the retransmission of packets by increasing the transmissions times of ACK when the receiver manages to receive a packet. Additional ACK transmissions will not cause significant increases in energy consumption but can further improve the lifetime of the WSN [33].The advantage of the retransmission-based mechanism is that it improves the network reliability at a low energy cost, so it is quite suitable for WSNs whose energy is extremely limited [4,32]. However, the unfavorable is that the network delay is usually long due to the repeat transmissions of data packets, especially in a link with high packet error rate [32] because the retransmission-based mechanism sends several data packets to the sink until the nodes receive ACK signals in response. If the ACK is dropped, nodes cannot receive the ACK and will send data packets to the sink, thereby increasing the transmission delay.
- (2)
- Forward error correction (FEC) [34,35]. In the FEC scheme, when source node sends one data packet to the sink, the data packet is encoded through errors-correcting code. If the error ratio of data packet is in a certain value, the sink will correct the error of data packet using errors-correcting code. But the transmission bandwidth is higher, and the cost is higher [34,35]. The reliability of data packet in the FEC is improved, however, in this scheme, the cost for encoding the message in a redundant way is larger; thus, the network lifetime is shorter.
- (3)
- Cooperative Communication (CC). Yu et al. [36], after an in-depth analysis on cooperative ARQ (automatic re-request), found that the cooperative ARQ protocols ensure the reliability of data packet better [33,36]. Zhang et al. [33], for the first time, determined the most appropriate value of the bit error ratio (BER) along with the number of cooperative nodes that reduce energy consumption for transmitting one bit of data through theoretical analysis. Then, they adjusted the transmission BER according to the energy left of nodes. As a result, not only could the energy of nodes in the clusters far from the sink node be fully used, but the energy cost of nodes in the nearer cluster could also be reduced, so the network lifetime was prolonged.
- (4)
- Network coding techniques. In the network coding techniques, the source node encodes the packets at the application layer with some level of redundancy. Because the data transmitted by the source node have some redundancy, this approach will not affect the reception of the correct packets by the destination node. Network coding techniques have many advantages, such as small data transmission delay, while their main disadvantage is the relatively large energy consumption due to the complex algorithm. Other studies can be found in [37].
- (5)
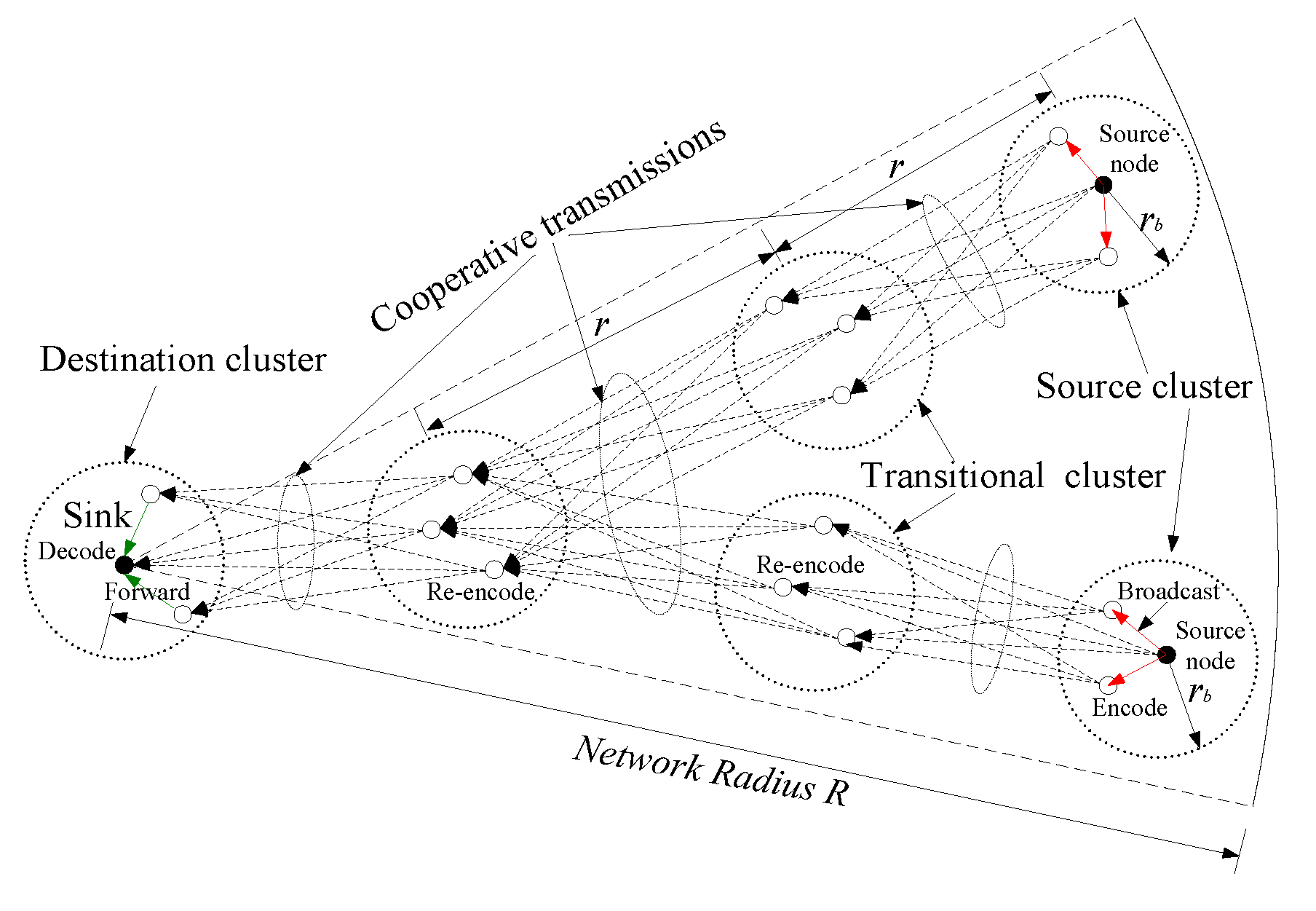
- Network-coding-based cooperative communications (NCCC). Reference [31] proposed a communication scheme whose main idea is the combination of coding techniques and cooperative communications. The scheme has two main operations: (a) the original data packets should be encoded before being sent from the source cluster and they should be re-encoded before being sent from the transitional cluster, where both encoding and re-encoding are performed using random network coding; and (b) in each hop, several sensor nodes with a certain probability of temporarily failing constitute a cluster to cooperatively send data packets. At the cost of acceptable delay, NCCC can achieve reliable performance. Although this scheme can achieve better reliability, the transmission delay is longer.
3. System Model and Problem Statement
3.1. Network Model
3.2. Problem Statement
- (1)
- Effective energy utilization (denoted as ). is the ratio of the used energy to the total energy in the network. Considering is the used energy of node , and denotes the initial energy:
- (2)
- Network lifetime (denoted as ). In our network model, the energy consumption of node includes (a) the energy consumed for delivering data packets, ; (b) the energy used for transmitting and receiving original packets, ; and (c) the energy spent for broadcasting and receiving status messages from other nodes in the same cluster, . As in [19], so maximizing is as follows.
- (3)
- End-to-end data collection reliability (denoted as ). This should be guaranteed, which means it should be higher than the minimum reliability, , required by the application. Let stand for the end-to-end reliability of a data packet generated by node , and let is the reliability of the packet at the i-th hop. Then, is as follows:Obviously, the goal of RICC can be summarized as Equation (4):
4. Main Design of RICC
4.1. Motivations of RICC
4.2. Preliminary Knowledge
4.2.1. Data Transmission Model
- (1)
- Source Cluster routing stage. First, the source node senses origin data and distributes them to the neighboring nodes in the same source cluster through broadcasting. After the functioning nodes receive , they split it into blocks:and generate a coding vector of size (denoted as ) over finite field GF(q) randomly. Then, the encode method for data packet is:
- (2)
- Transitional Cluster routing stage. When source node in the source cluster transmit data packet to the next cluster, which is called the transitional cluster. Then the data packet is transmitted by the transitional cluster using the same way until this packet is transmitted to the destination cluster [31], which contains the sink node.Assume data packets are received by a node in a certain transitional cluster. and are the coding vector and coded data, respectively. The coding coefficients are produced by GF(q), the encoding method of data packet is as follow:where and are the coding vector and coded data of the new coded packet, respectively [31].
- (3)
- Destination Cluster routing stage. All data packets are transmitted to the destination cluster, then some nodes will transmit data packet to destination cluster. Those redundancy data will be removed, and the other packets are decoded to retrieve the original packets.
4.2.2. Reliability Model
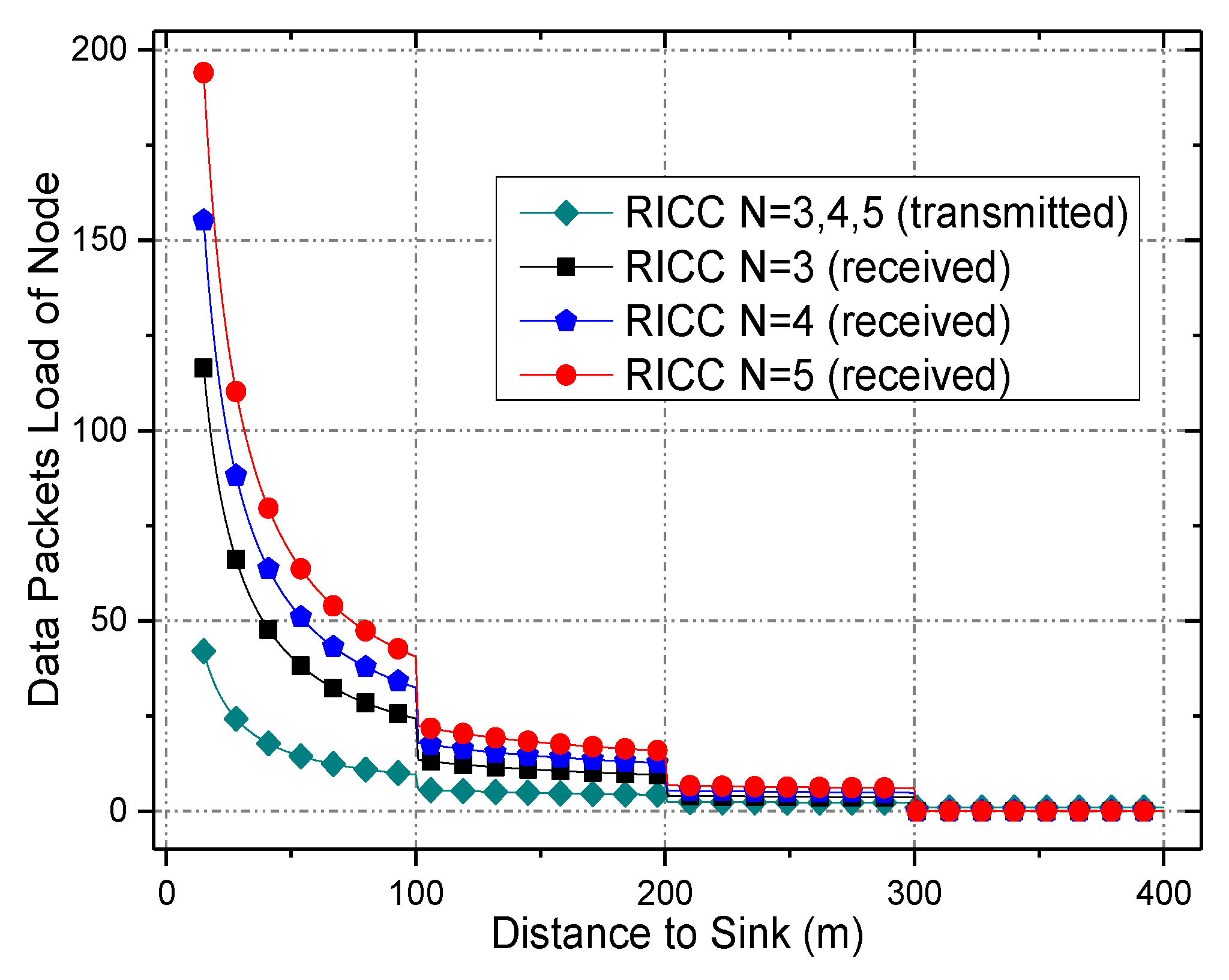
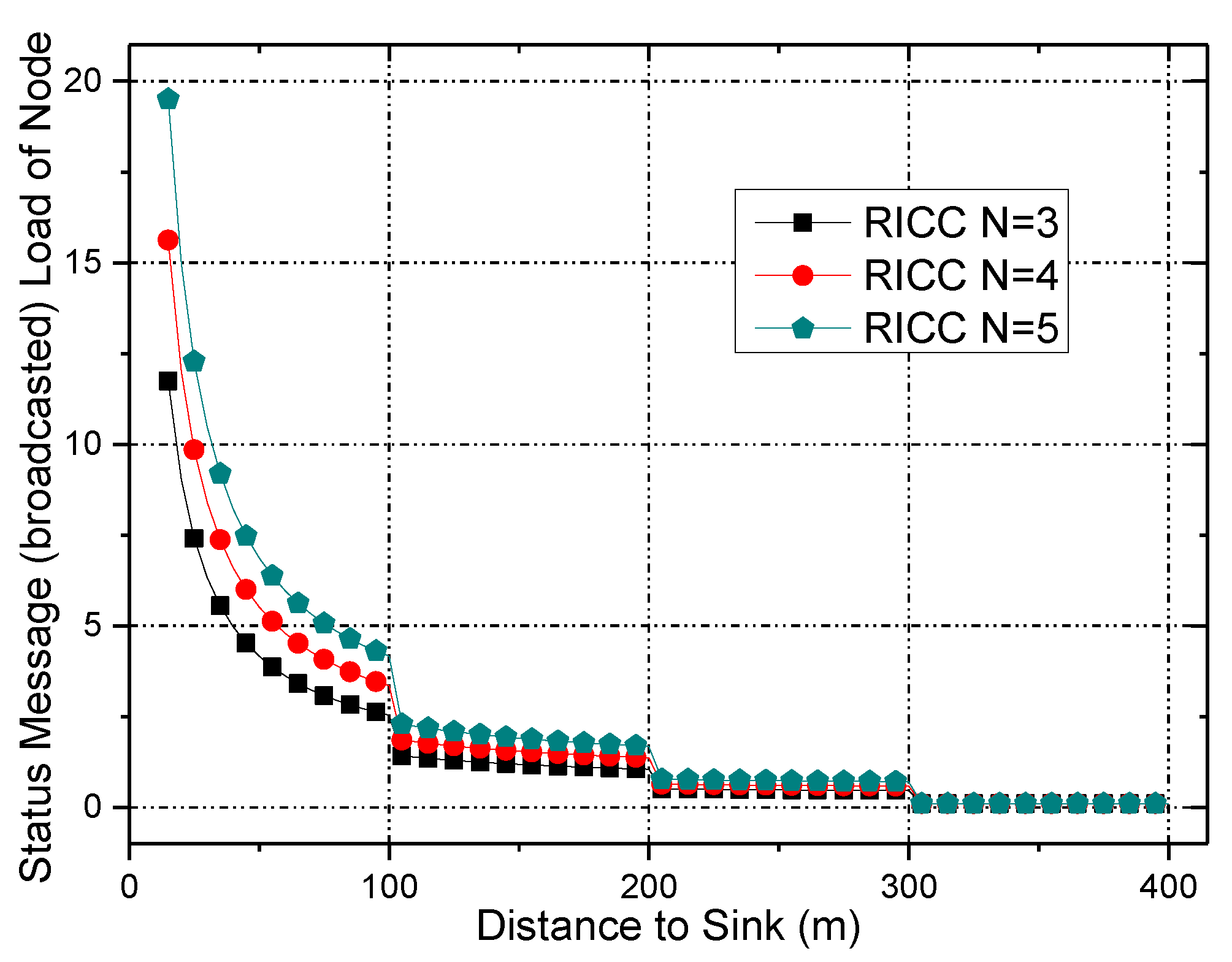
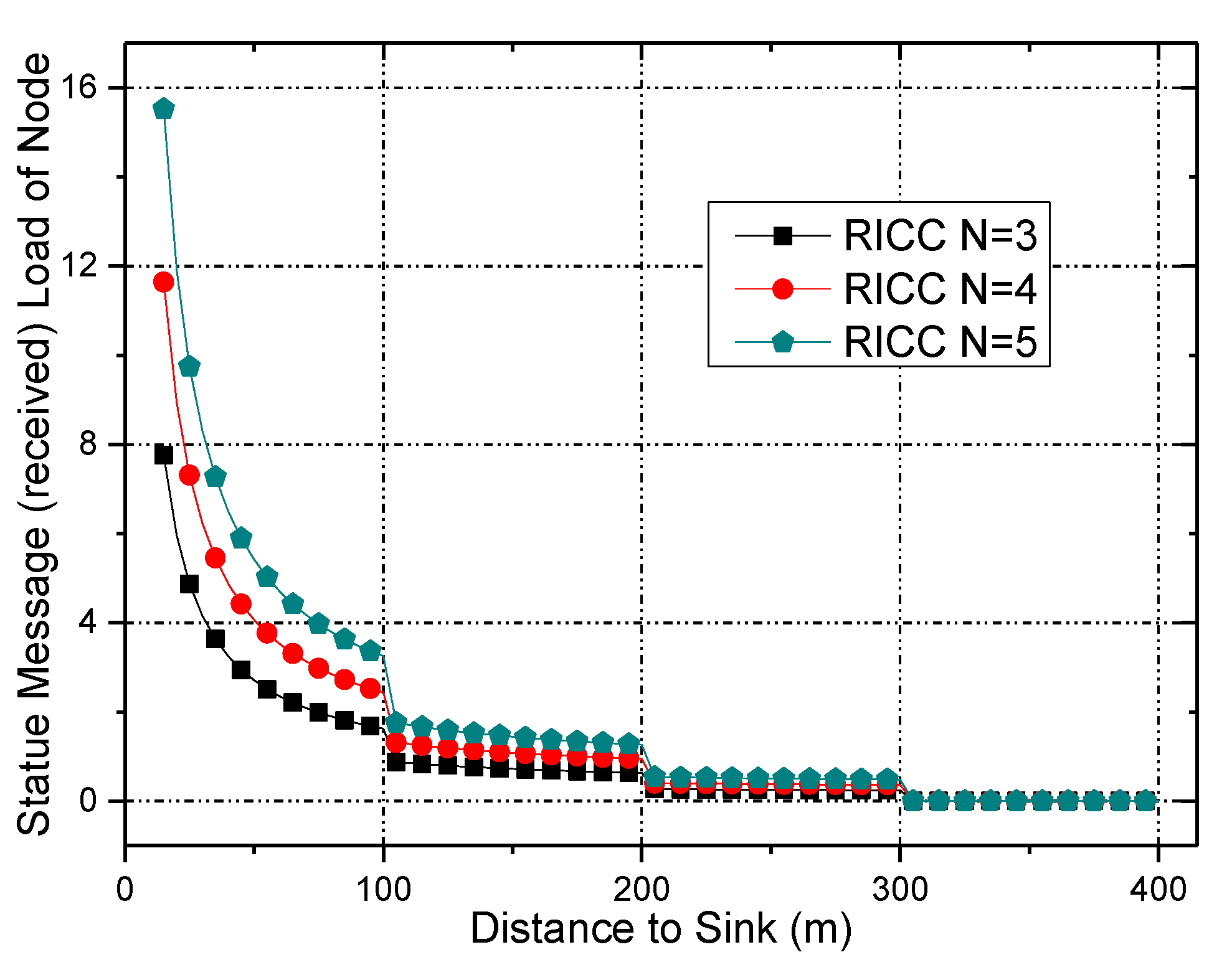
4.3. Data Load of Node
4.4. Energy Consumption of a Node
4.5. The Design of RICC
5. Performance Analysis of RICC
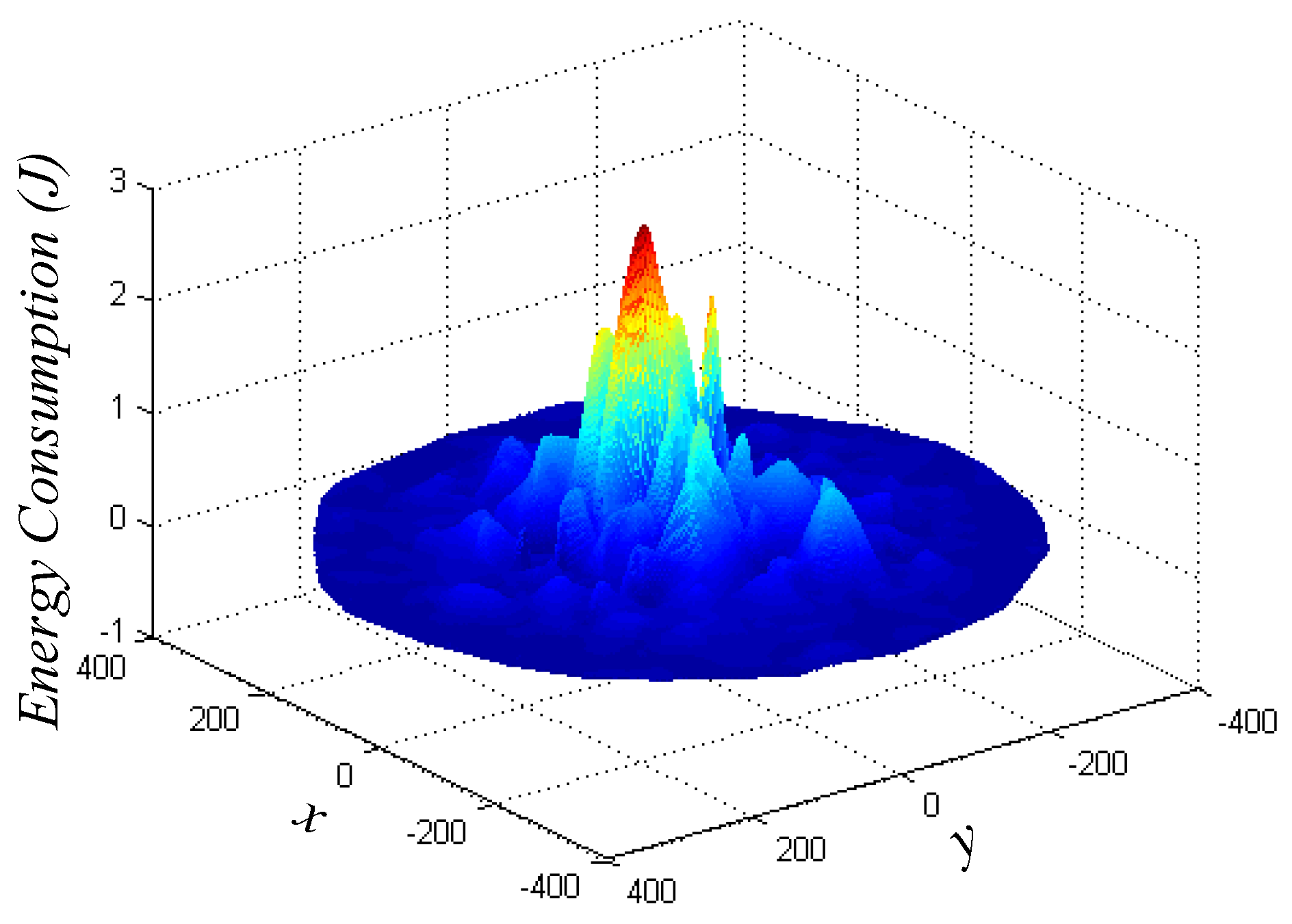
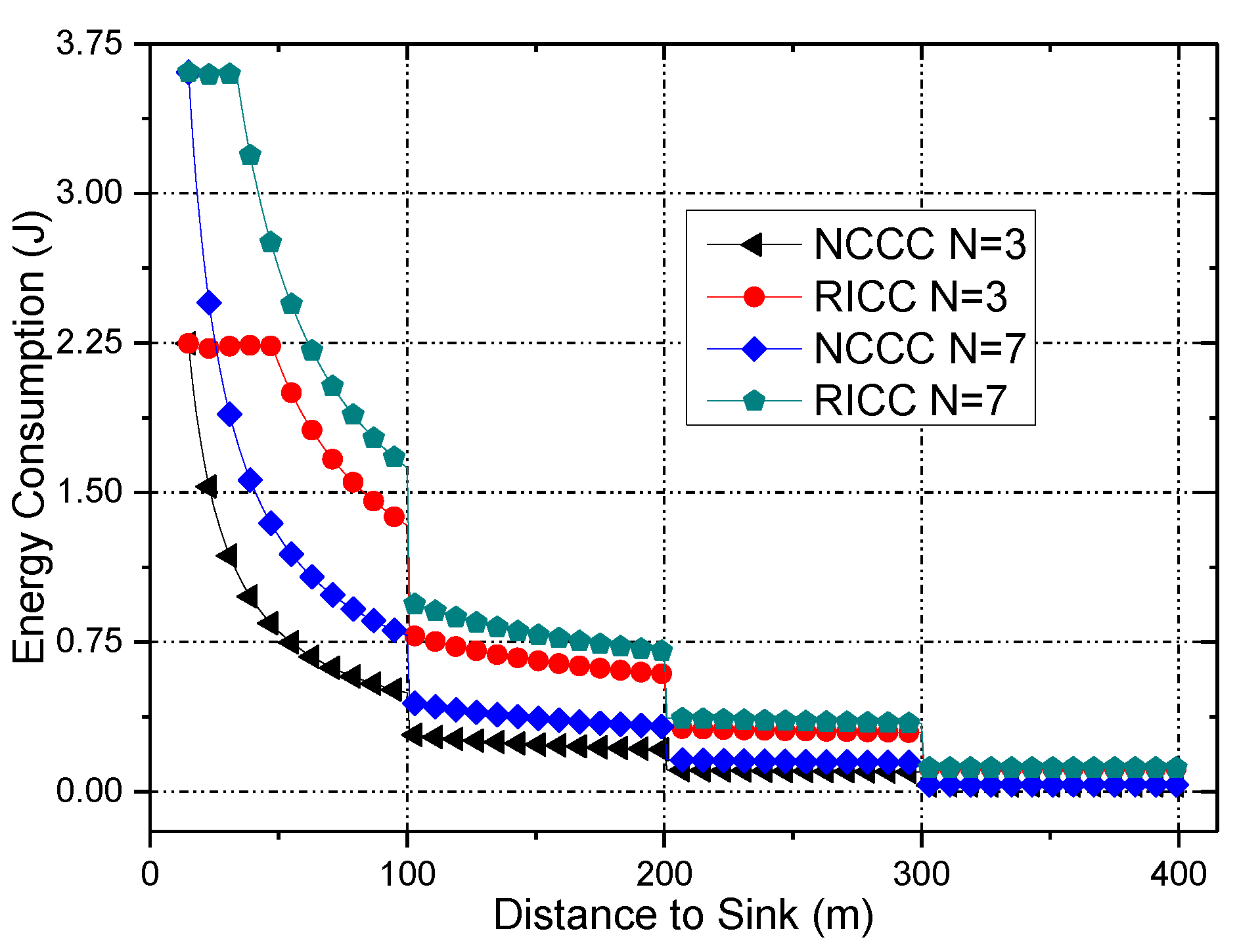
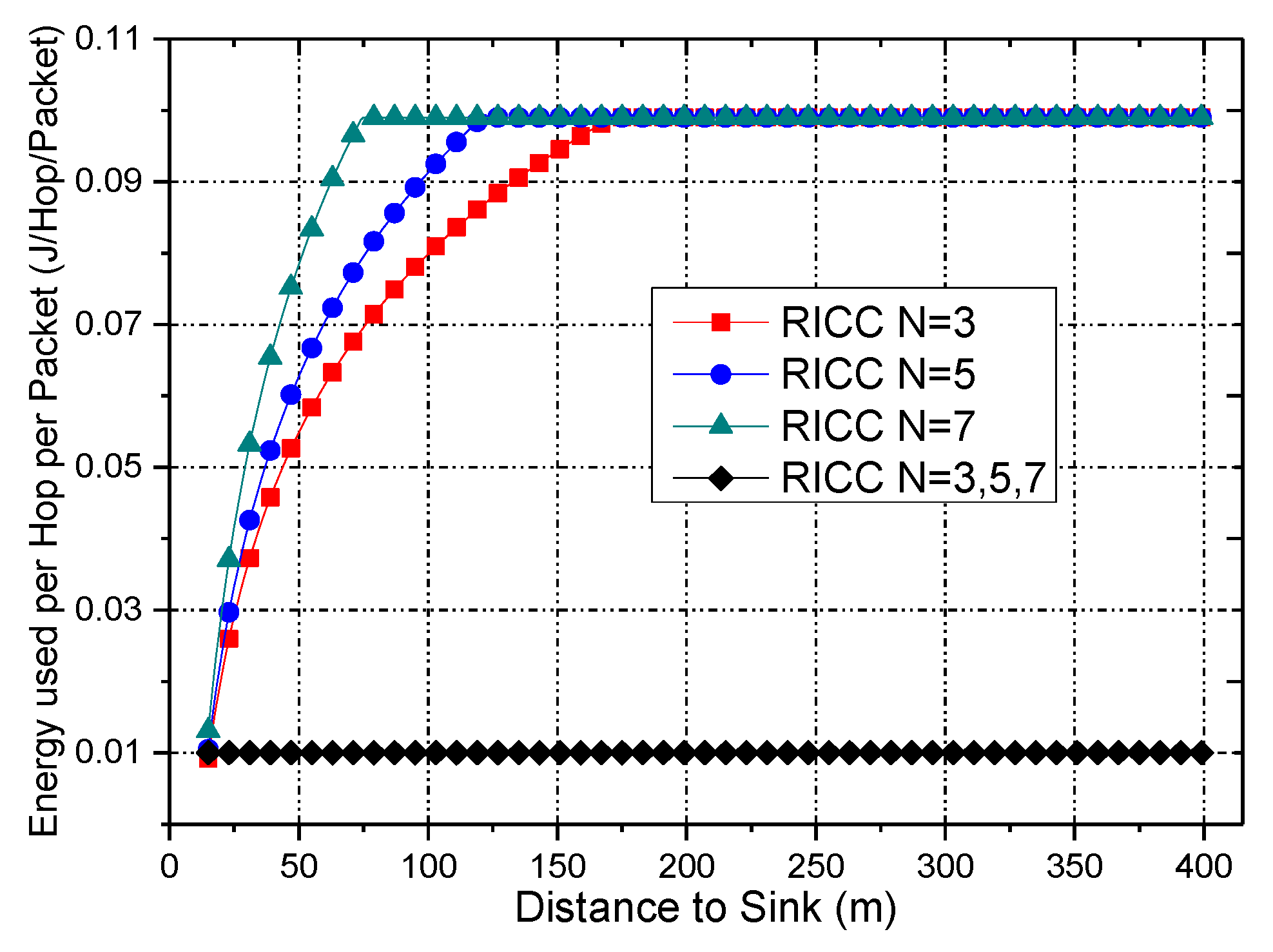
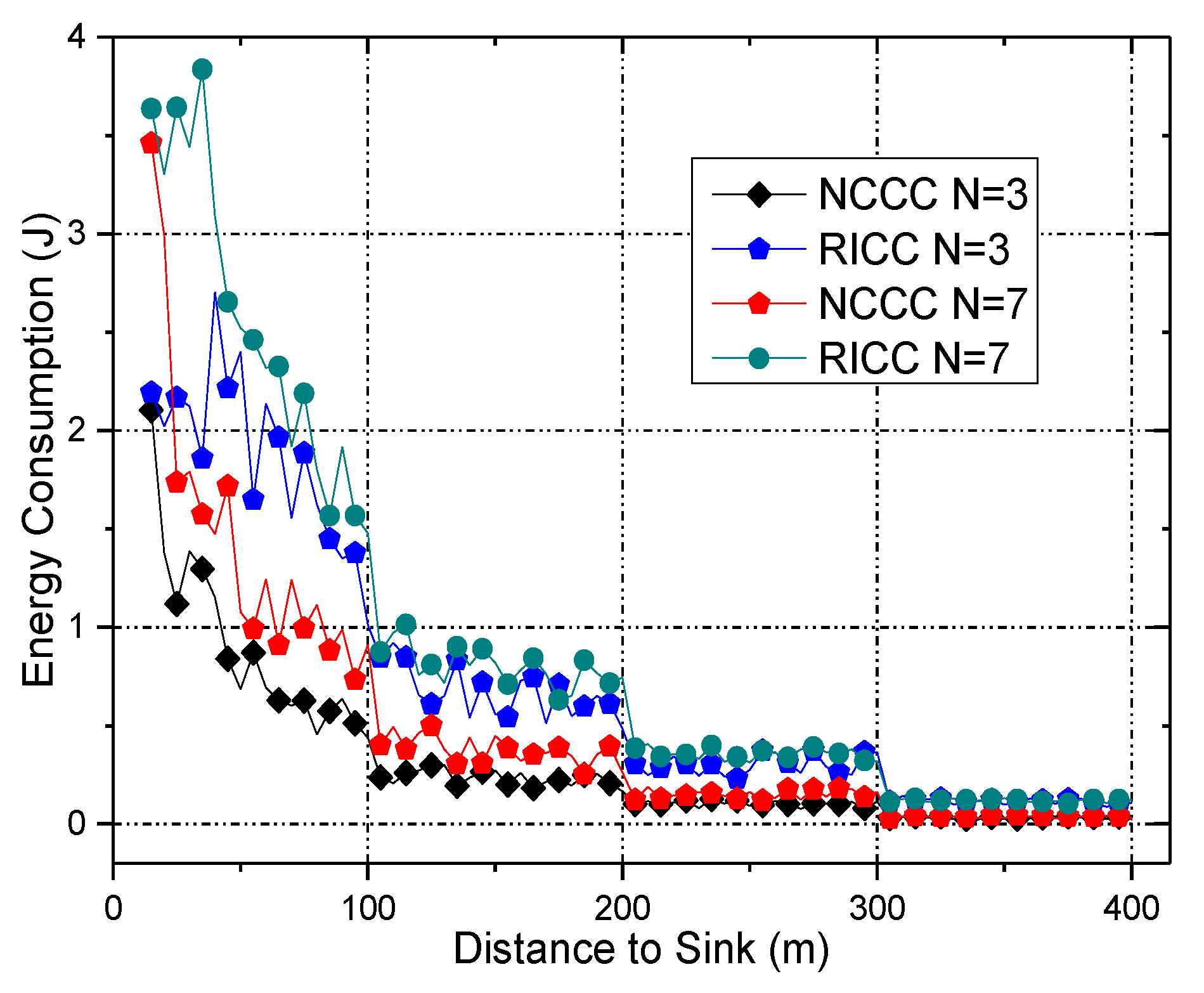
5.1. Energy Consumption of RICC
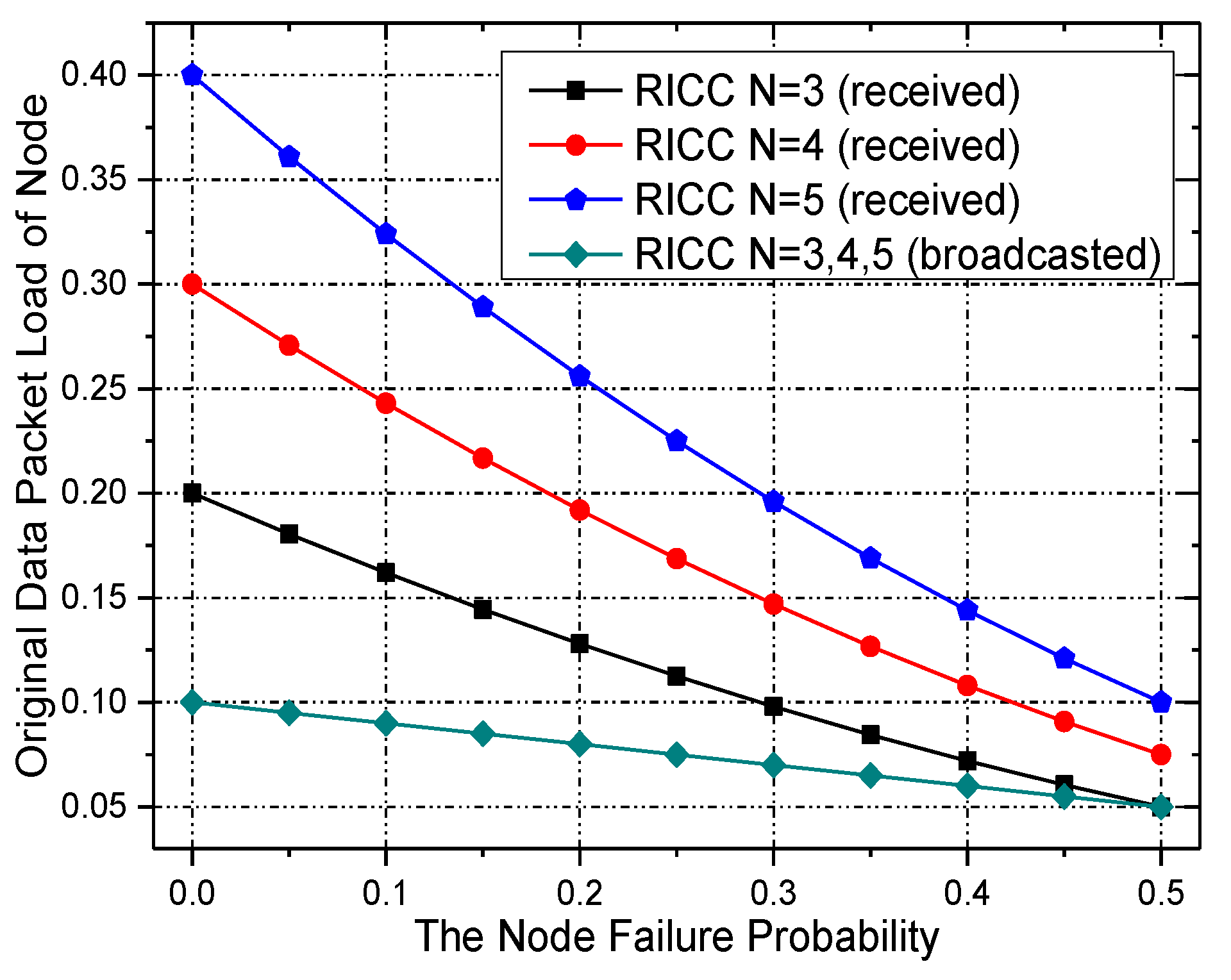
5.2. Network Reliability of RICC
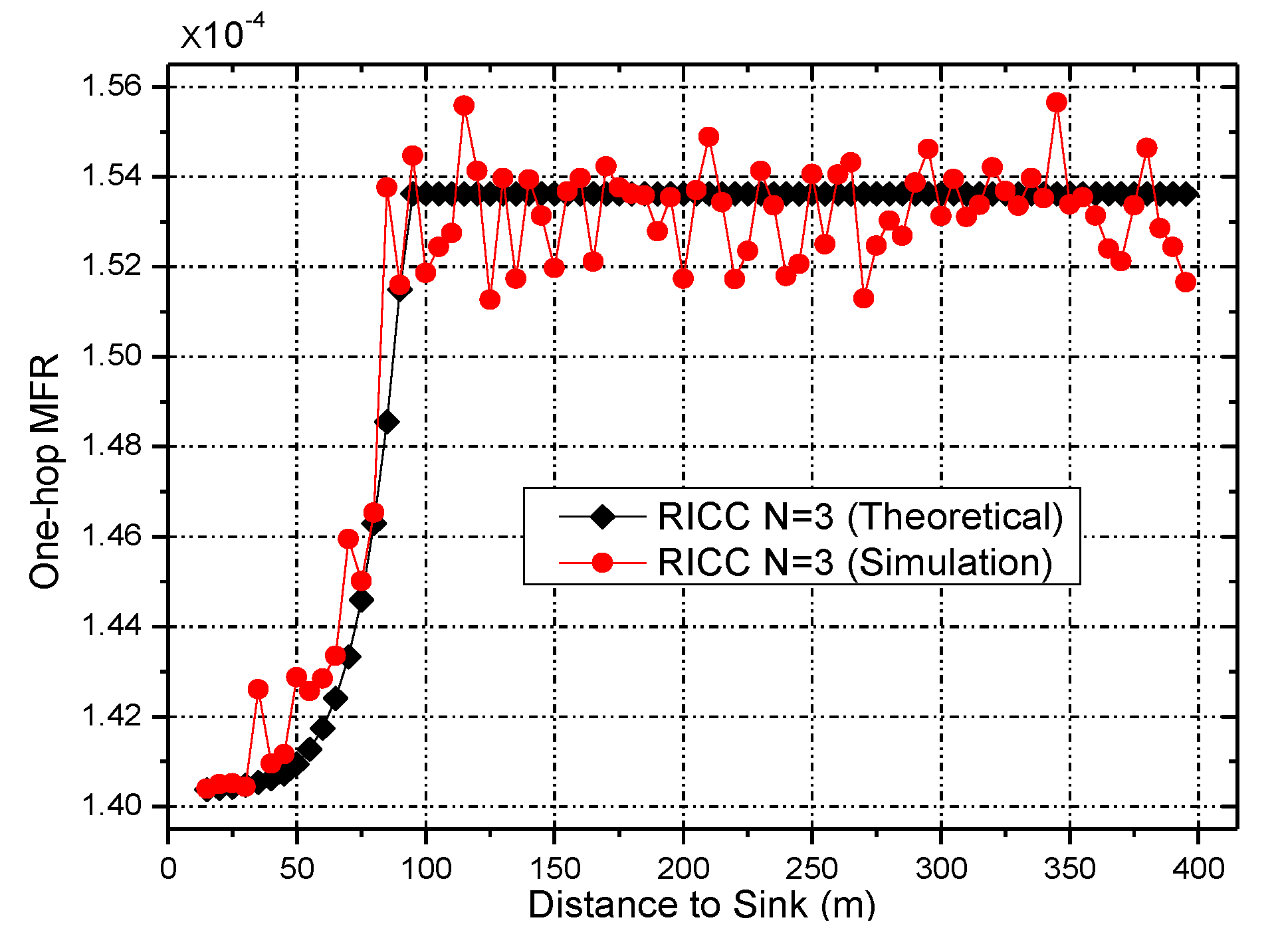
5.2.1. End-to-end MFR
5.2.2. Weighted End-to-end MFR
6. Experimental Results and Analyses
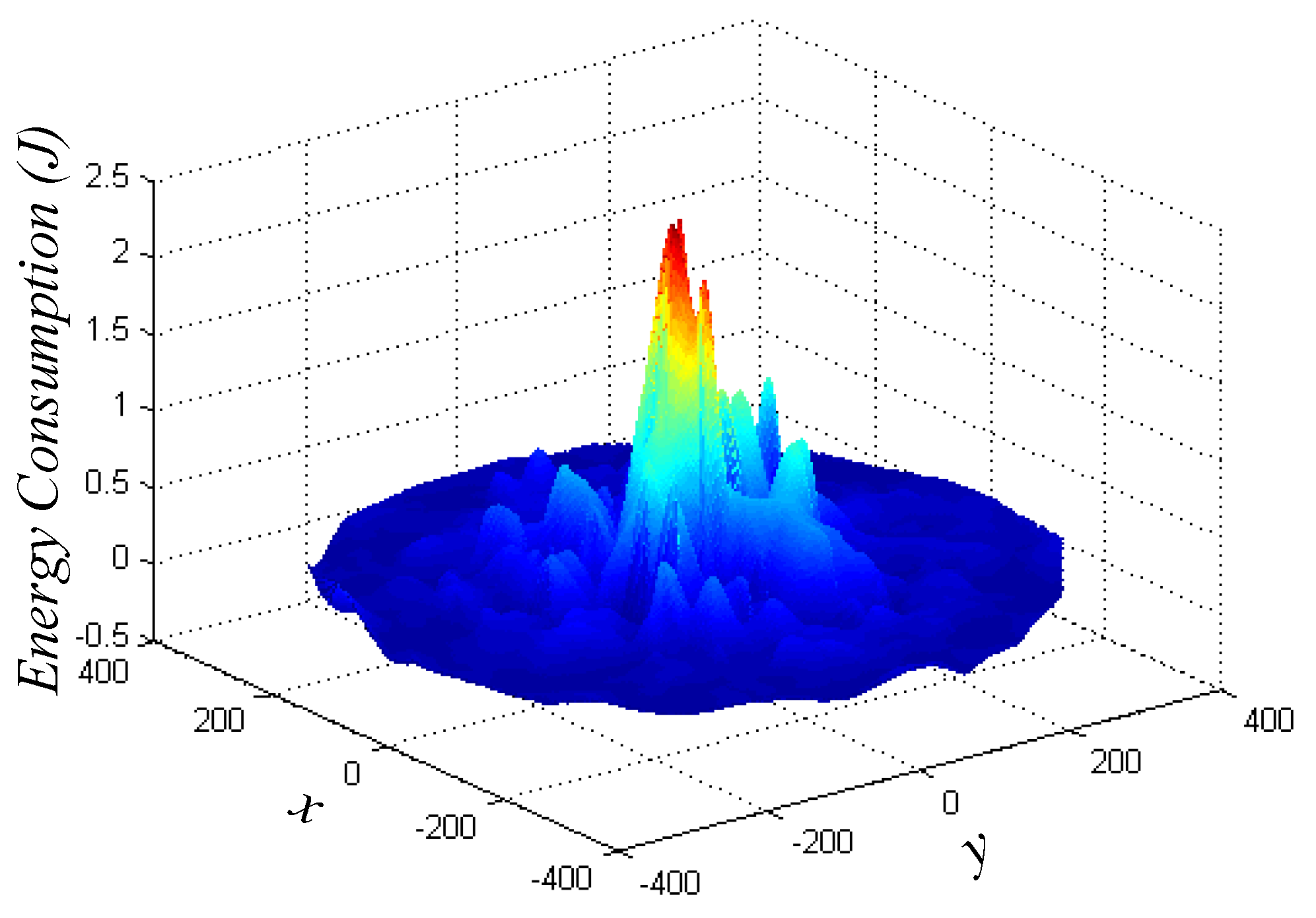
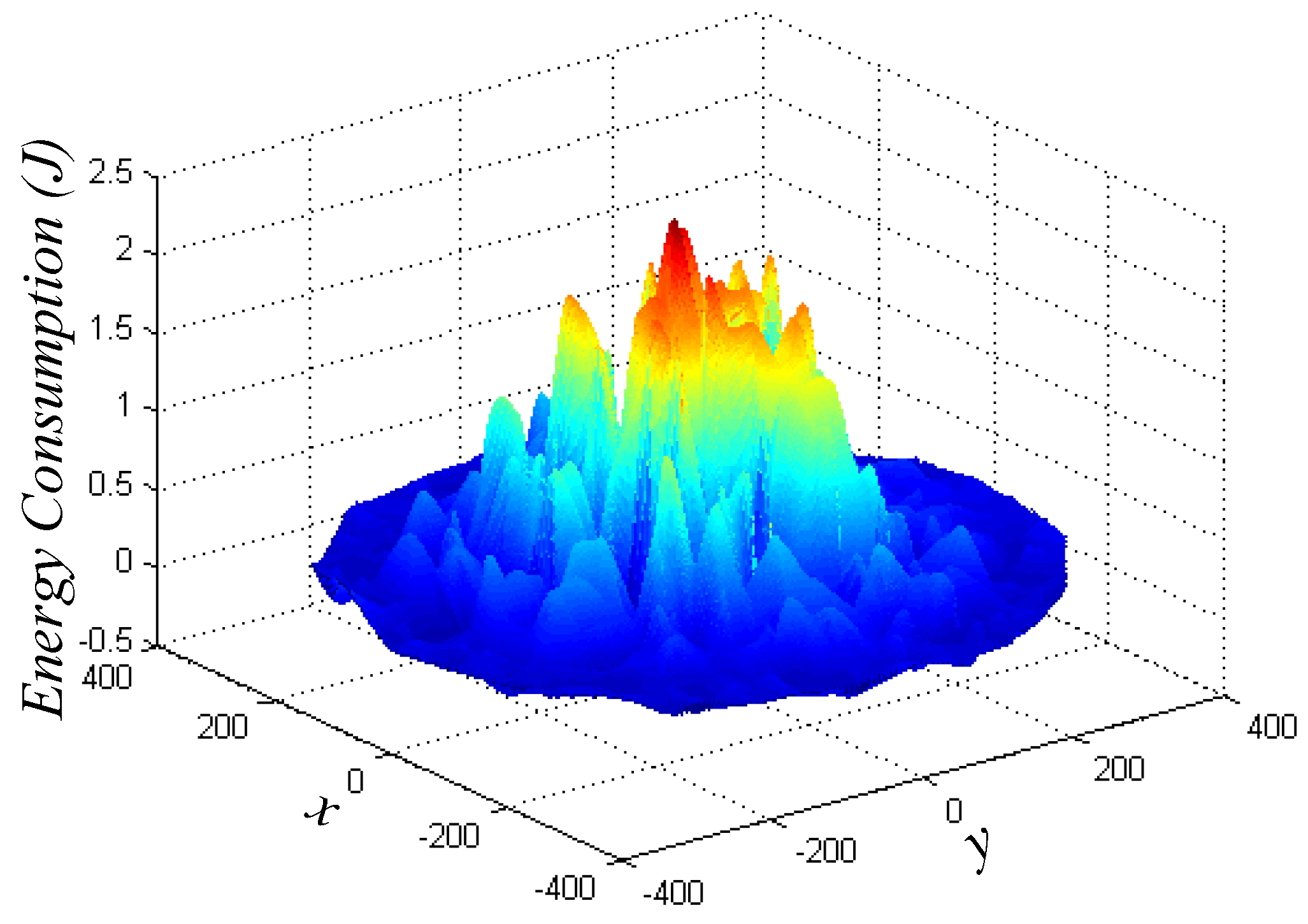
6.1. Energy Consumption
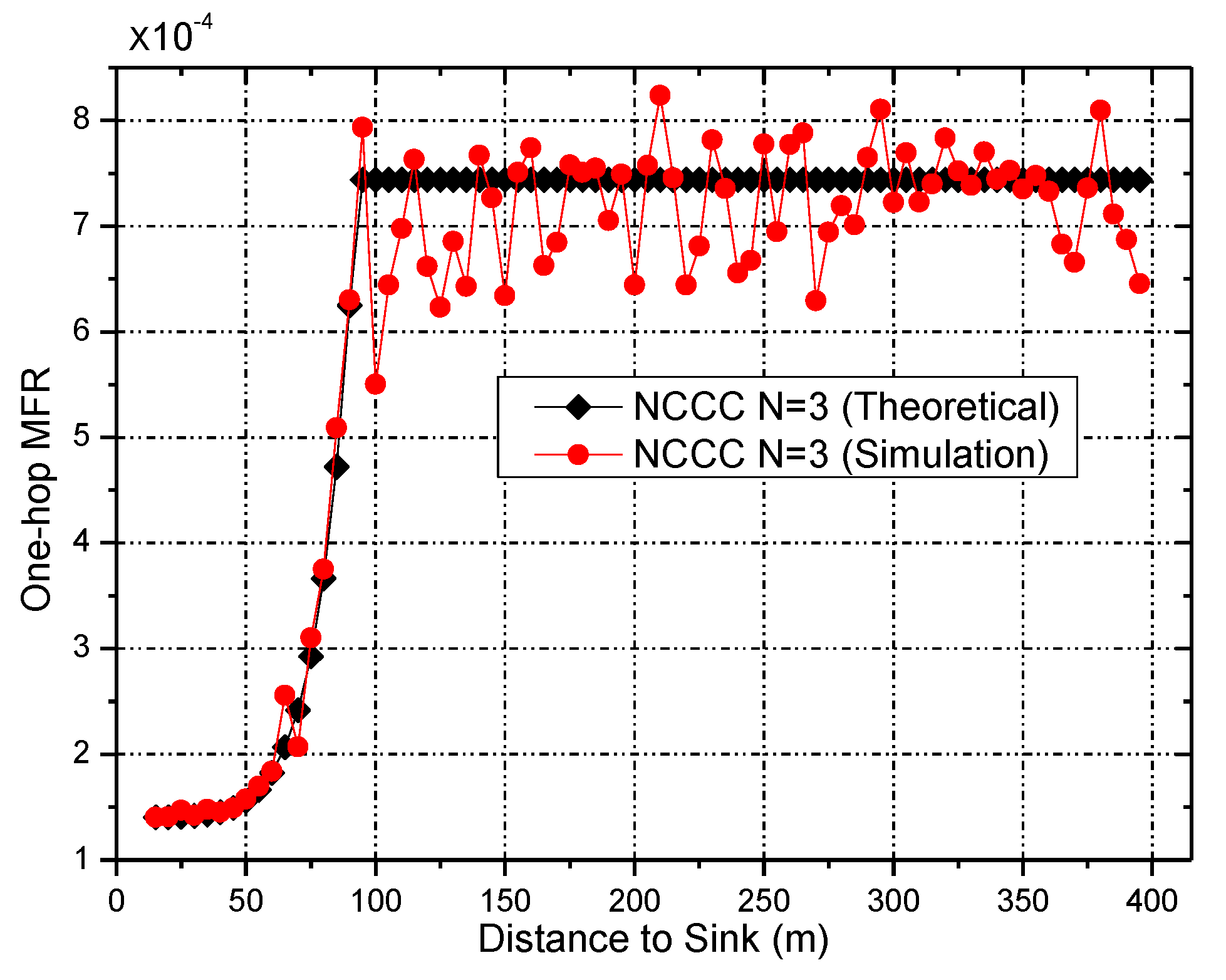
6.2. Network Reliability
7. Conclusions and Future Work
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Naranjo, P.G.V.; Shojafar, M.; Mostafaei, H.; Pooranian, Z.; Baccarelli, E. P-SEP: A prolong stable election routing algorithm for energy-limited heterogeneous fog-supported wireless sensor networks. J. Supercomput. 2017, 73, 733–755. [Google Scholar] [CrossRef]
- Qin, G.; Wang, L.; Li, Q. Resource symmetric dispatch model for internet of things on advanced logistics. Symmetry 2016, 8, 20. [Google Scholar] [CrossRef]
- Zhao, S.; Liu, A. High performance target tracking scheme with low prediction precision requirement in WSNs. Int. J. Ad Hoc Ubiquitous Comput. 2017, in press. [Google Scholar]
- Liu, X.; Zhao, S.; Liu, A.; Xiong, N.; Vasilakos, A.V. Knowledge-aware proactive nodes selection approach for energy management in Internet of Things. Future Gener. Comput. Syst. 2017. [Google Scholar] [CrossRef]
- Byun, S.S.; Gil, J.M. Fair Dynamic spectrum allocation using modified game theory for resource-constrained cognitive wireless sensor networks. Symmetry 2017, 9, 73. [Google Scholar] [CrossRef]
- Liu, A.; Zhang, Q.; Li, Z.; Choi, Y.J.; Li, J.; Komuro, N. A green and reliable communication modeling for industrial internet of things. Comput. Electr. Eng. 2017, 58, 364–381. [Google Scholar] [CrossRef]
- Baccarelli, E.; Naranjo, P.G.V.; Scarpiniti, M.; Shojafar, M.; Abawajy, J.H. Fog of everything: Energy-efficient networked computing architectures, research challenges, and a case study. IEEE Access 2017, 5, 9882–9910. [Google Scholar] [CrossRef]
- Huang, C.; Ma, M.; Liu, Y.; Liu, A. Preserving source location privacy for energy harvesting WSNs. Sensors 2017, 17, 724. [Google Scholar] [CrossRef] [PubMed]
- Li, T.; Liu, Y.; Gao, L.; Liu, A. A Cooperative-based model for smart-sensing tasks in fog computing. IEEE Access. 2017. [Google Scholar] [CrossRef]
- Chen, Z.; Liu, A.; Li, Z.; Choi, Y.J.; Sekiya, H.; Li, J. Energy-efficient broadcasting scheme for smart industrial wireless sensor networks. Mob. Inform. Syst. 2017. [Google Scholar] [CrossRef]
- Liu, X.; Dong, M.; Ota, K.; Yang, L.T.; Liu, A. Trace malicious source to guarantee cyber security for mass monitor critical infrastructure. J. Comput. Syst. Sci. 2016. [Google Scholar] [CrossRef]
- Li, T.; Liu, A.; Huang, C. A similarity scenario-based recommendation model with small disturbances for unknown items in social networks. IEEE Access 2016, 4, 9251–9272. [Google Scholar] [CrossRef]
- Liu, A.; Chen, Z.; Xiong, N. An adaptive virtual relaying set scheme for loss-and-delay sensitive WSNs. Inform. Sci. 2017. [Google Scholar] [CrossRef]
- Liu, A.; Liu, X.; Wei, T.; Yang, L.T.; Rho, S.C.; Paul, A. Distributed multi-representative re-fusion approach for heterogeneous sensing data collection. ACM Trans. Embed. Comput. Syst. 2017, 16, 73. [Google Scholar] [CrossRef]
- Liu, Y.; Liu, A.; Guo, S.; Li, Z.; Choi, Y.J.; Sekiya, H. Context-aware collect data with energy efficient in Cyber-physical cloud systems. Future Gener. Comput. Syst. 2017. [Google Scholar] [CrossRef]
- Liu, X.; Li, G.; Zhang, S.; Liu, A. Big program code dissemination scheme for emergency software-define wireless sensor networks. Peer-to-Peer Netw. Appl. 2017. [Google Scholar] [CrossRef]
- Liu, A.; Liu, X.; Tang, Z.; Yang, L.T.; Shao, Z. preserving smart sink location privacy with delay guaranteed routing scheme for WSNs. ACM Trans. Embed. Comput. Syst. 2017, 16, 68. [Google Scholar] [CrossRef]
- Liu, Q.; Liu, A. On the hybrid using of unicast-broadcast in wireless sensor networks. Comput. Electr. Eng. 2017. [Google Scholar] [CrossRef]
- Chen, X.; Ma, M.; Liu, A. Dynamic power management and adaptive packet size selection for IoT in e-Healthcare. Comput. Electr. Eng. 2017. [Google Scholar] [CrossRef]
- Chen, X.; Xu, Y.; Liu, A. Cross layer design for optimal delay, energy efficiency and lifetime in body sensor networks. Sensors 2017, 17, 900. [Google Scholar] [CrossRef] [PubMed]
- Xu, Y.; Chen, X.; Liu, A.; Hu, C. A latency and coverage optimized data collection scheme for smart cities based on vehicular ad-hoc networks. Sensors 2017, 17, 888. [Google Scholar] [CrossRef] [PubMed]
- Wang, J.; Liu, A.; Zhang, S. Key parameters decision for cloud computing: Insights from a multiple game model. Concurr. Comput. Pract. Exp. 2017. [Google Scholar] [CrossRef]
- Wang, J.; Liu, A.; Yan, T.; Zeng, Z. A resource allocation model based on double-sided combinational auctions for transparent computing. Peer-to-Peer Netw. Appl. 2017. [Google Scholar] [CrossRef]
- Liu, X.; Liu, Y.; Song, H.; Liu, A. Big data orchestration as a service networking. IEEE Commun. Mag. 2017, 55, 94–101. [Google Scholar]
- Liu, Y.; Liu, A.; Li, Y.; Li, Z.; Choi, Y.J.; Sekiya, H.; Li, J. APMD: A fast data transmission protocol with reliability guarantee for pervasive sensing data communication. Pervasive Mob. Comput. 2017. [Google Scholar] [CrossRef]
- Zhang, Q.; Liu, A. An unequal redundancy level based mechanism for reliable data collection in wireless sensor networks. EURASIP J. Wirel. Commun. Netw. 2016. [Google Scholar] [CrossRef]
- Xu, Y.; Liu, A.; Huang, C. Delay-aware program codes dissemination scheme in Internet of everything. Mob. Inform. Syst. 2016. [Google Scholar] [CrossRef]
- Liu, X.; Liu, A.; Li, Z.; Tian, S.; Choi, Y.J.; Sekiya, H.; Li, J. Distributed cooperative communication nodes control and optimization reliability for resource-constrained WSNs. Neurocomputing 2017. [Google Scholar] [CrossRef]
- Chen, Z.; Liu, A.; Li, Z.; Choi, Y.J.; Li, J. Distributed duty cycle control for delay improvement in wireless sensor networks. Peer-to-Peer Netw. Appl. 2017, 10, 559–578. [Google Scholar] [CrossRef]
- Cui, S.; Goldsmith, A.J.; Bahai, A. Energy-efficiency of MIMO and cooperative MIMO techniques in sensor networks. IEEE J. Sel. Areas Commun. 2004, 22, 1089–1098. [Google Scholar] [CrossRef]
- Liu, X.; Gong, X.; Zheng, Y. Reliable cooperative communications based on random network coding in multi-hop relay WSNs. IEEE Sens. J. 2014, 14, 2514–2523. [Google Scholar] [CrossRef]
- Rosberg, Z.; Liu, R.P.; Le Dinh, T.; Dong, Y.F.; Jha, S. Statistical reliability for energy efficient data transport in wireless sensor networks. Wirel. Netw. 2010, 16, 1913–1927. [Google Scholar] [CrossRef]
- Zhang, D.; Chen, Z. Energy-efficiency of cooperative communication with guaranteed E2E reliability in WSNs. Int. J. Distrib. Sens. Netw. 2013, 9. [Google Scholar] [CrossRef]
- Noda, C.; Prabh, S.; Alves, M.; Voigt, T. On packet size and error correction optimisations in low-power wireless networks. In Proceedings of the 2013 10th Annual IEEE Communications Society Conference on Sensor, Mesh and Ad Hoc Communications and Networks (SECON), New Orleans, LA, USA, 24–27 June 2013. [Google Scholar]
- Zhou, M.; Jin, C. QoS-aware forward error correction cooperating with opportunistic routing in wireless multi-hop networks. Wirel. Pers. Commun. 2017, 92, 1407–1422. [Google Scholar] [CrossRef]
- Yu, G.; Zhang, Z.; Qiu, P. Efficient ARQ protocols for exploiting cooperative relaying in wireless sensor networks. Comput. Commun. 2007, 30, 2765–2773. [Google Scholar] [CrossRef]
- Keller, L.; Atsan, E.; Argyraki, K.; Fragouli, C. SenseCode: Network coding for reliable sensor networks. ACM Trans. Sens. Netw. (TOSN) 2013, 9. [Google Scholar] [CrossRef]
- The OMNET++ Simulator. Available online: http://www.omnetpp.org/ (accessed on 23 March 2016).

| Symbol | Meaning | Value | Symbol | Meaning | Value |
|---|---|---|---|---|---|
| the power consumption of receiving circuits | 98.2 mW | the data time slot | 3.0 | ||
| the power consumption of transmitting circuits | 112.5 mW | the probability that a node does not transmit a data packet successfully | 0.05 | ||
| a fixed data rate | 10 kbps | the packet loss probability within the same cluster | 10−6 | ||
| the single-sided thermal noise Power Spectral Density (PSD) at room temperature | −171 dBm/Hz | the scale parameter of the distribution | 1.0 | ||
| the receiver noise figure | 10 dB | the carrier wavelength | 0.12 m | ||
| the link margin compensating the hardware process variations | 40 dB | the close-range reference distance between the receiver and transmitter | 1 m | ||
| communication constants | 3.47 × 108 | The number of splits of the network | 2 | ||
| the transmitter and receiver antenna gains, respectively | 7 dBi | the size of the packet header | 44 bits | ||
| a threshold of Signal-to-Noise Ratio (SNR) | 0 dB | the size of the data packet | 1200 bits | ||
| the probability of generating data in a period | 0.1 | the size of the status message | 100 bits | ||
| the transmission distance | - | the PSD of the total effective noise at the receiver input | - | ||
| the energy consumption of the power amplifier for transmitting one bit of data | - | the drain efficiency of the RF power amplifier | - | ||
| the channel gain | - | the Peak-to-Average Ratio (PAR) | - |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chen, Z.; Ma, M.; Liu, X.; Liu, A.; Zhao, M. Reliability Improved Cooperative Communication over Wireless Sensor Networks. Symmetry 2017, 9, 209. https://doi.org/10.3390/sym9100209
Chen Z, Ma M, Liu X, Liu A, Zhao M. Reliability Improved Cooperative Communication over Wireless Sensor Networks. Symmetry. 2017; 9(10):209. https://doi.org/10.3390/sym9100209
Chicago/Turabian StyleChen, Zhuangbin, Ming Ma, Xiao Liu, Anfeng Liu, and Ming Zhao. 2017. "Reliability Improved Cooperative Communication over Wireless Sensor Networks" Symmetry 9, no. 10: 209. https://doi.org/10.3390/sym9100209
APA StyleChen, Z., Ma, M., Liu, X., Liu, A., & Zhao, M. (2017). Reliability Improved Cooperative Communication over Wireless Sensor Networks. Symmetry, 9(10), 209. https://doi.org/10.3390/sym9100209






