Meet-in-the-Middle Differential Fault Analysis on ITUbee Block Cipher
Abstract
1. Introduction
2. Preliminaries
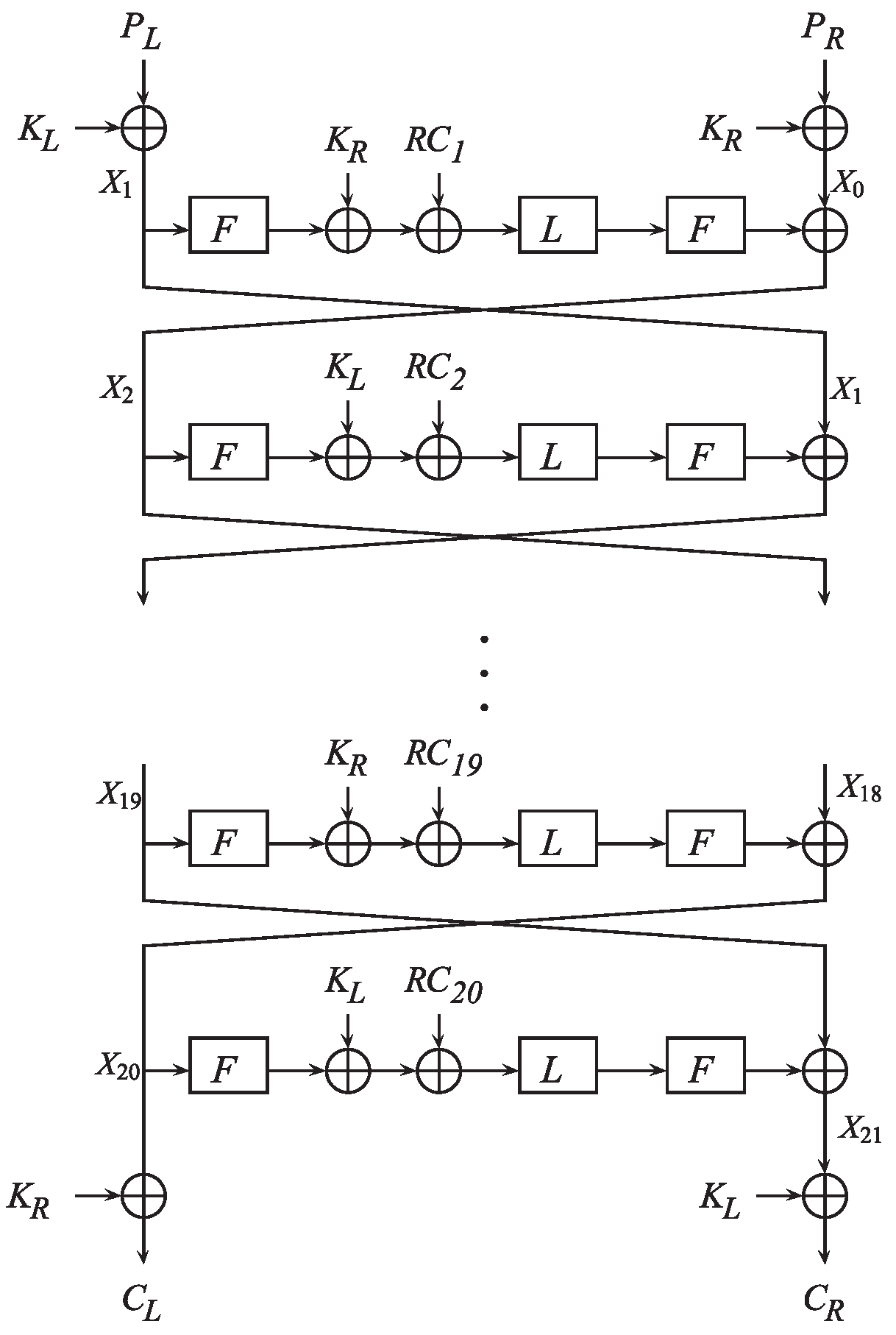
2.1. Description of the Block Cipher ITUBee
- -
- and are, respectively, two 40-bit parts of the 80-bit plaintexts and the 80-bit key.
- -
- is a 16-bit round constant which is added to the rightmost 16-bit.
- -
- , where are 8-bit values and S is the S-box same as that in AES [40].
- -
- , where are 8-bit values.
- -
- The F-function used in the round is defined as .
| Algorithm 1: Encryption Procedure of ITUbee () |
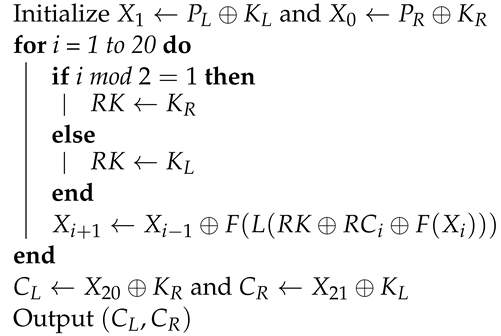 |
2.2. Obervations on ITUBee Block Cipher
2.2.1. Differential Property of S-Box
2.2.2. Property of F-Function
3. Previous DFA Scheme
3.1. Fault Model
- -
- The adversary can inject a byte fault to a selected state of the block cipher; for example, the adversary could inject a random byte fault to the output of the last in the last but two rounds.
- -
- The location of the fault in the word is known to the adversary. Moreover, the case of unknown location of injected fault is also discussed.
- -
- The adversary could obtain ciphertexts of both correct and faulty execution.
3.2. DFA Schemes
3.2.1. Attack 1
3.2.2. Scheme 2
3.3. Countermeasures
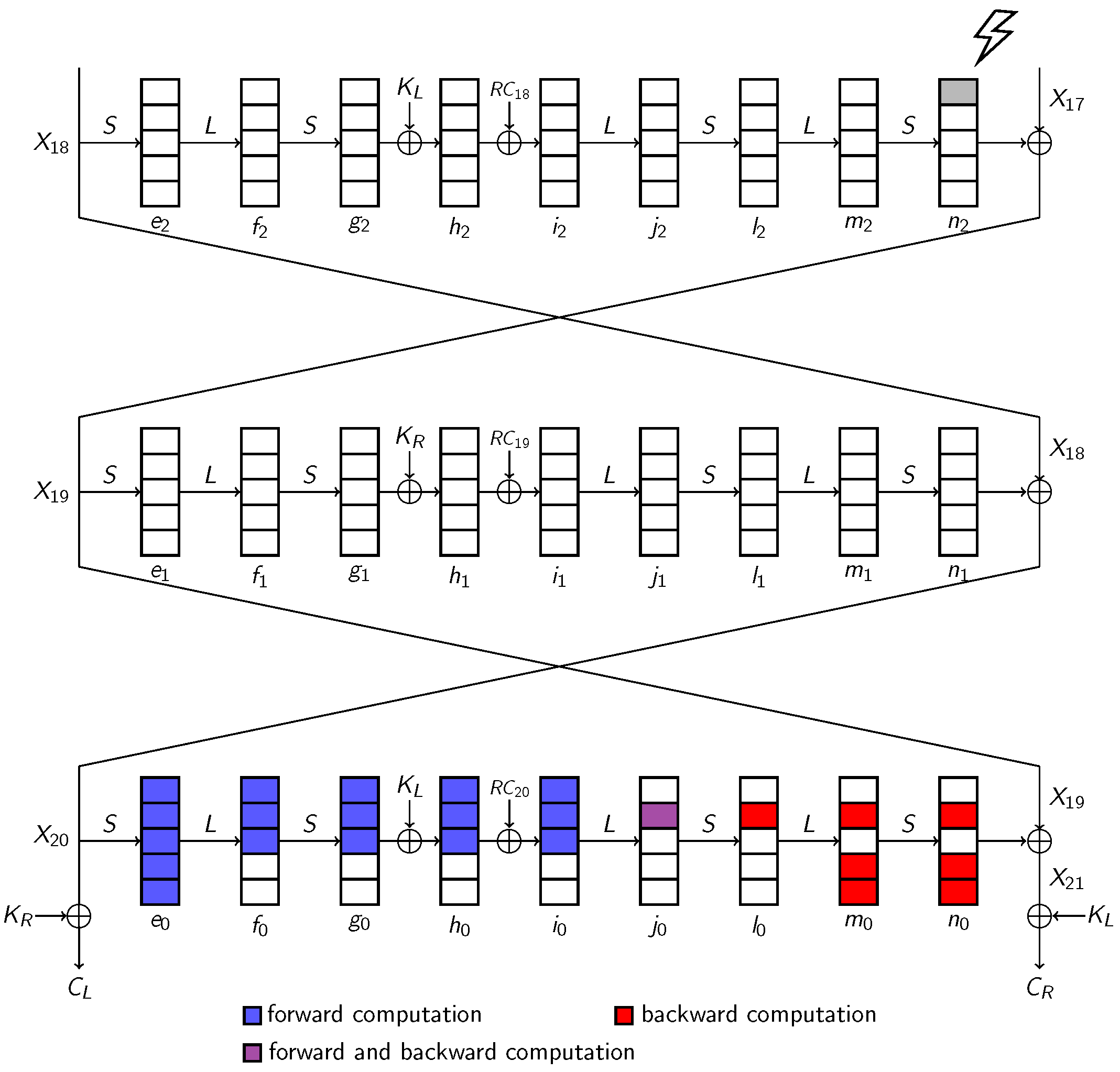
4. Improved DFA Schemes on ITUbee
4.1. Scheme 1: Differential Fault Attack with Exhaustive Search
4.2. Scheme 2: Meet-in-the-Middle Fault Attack with Complexity
- For each pair, guess all candidates of , compute the values of according to Equation (4), store the value of for each .
- For all candidates of , forward compute the value of for each pair, store the values of indexed by .
- For each pair, if the value of two computational directions is equal, mark the and as a valid candidate. This phase can be seen as a filter, with eight pairs filtered, the number of candidates of decreased to close to 1.
4.3. Scheme 3: Meet-in-the-Middle Attack with Complexity
- Compute the values of according to the left side of Equation (8) for all candidates of for each that we obtained before, and store the values of indexed by the vector of of five pairs in the six in a table.
- Compute the vector following the right side of Equation (8) for all candidates of of the five pairs we obtained before, and store the values in another table.
- We sort the two tables and find collisions for the index values. If there is a collision between the two tables, the corresponding is stored as a valid candidate. With the five-pair filter, there will exist just one candidate in theory.
4.4. Simulation Results
4.5. Further Countermeasures
| Algorithm 2: ITUbee-Cipher (Message, Key) |
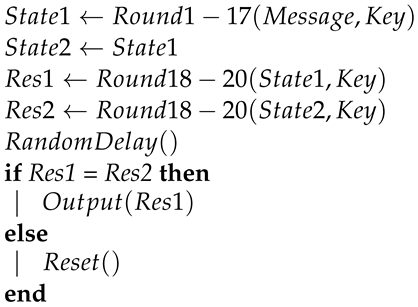 |
4.6. Discussions
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Zakaria, A.A.; Halim, A.H.A.; Ridzuan, F.; Zakaria, N.H.; Daud, M. LAO-3D: A Symmetric Lightweight Block Cipher Based on 3D Permutation for Mobile Encryption Application. Symmetry 2022, 14, 2042. [Google Scholar] [CrossRef]
- Alshammari, B.; Guesmi, R.; Guesmi, T.; Alsaif, H.; Alzamil, A. Implementing a Symmetric Lightweight Cryptosystem in Highly Constrained IoT Devices by Using a Chaotic S-Box. Symmetry 2021, 13, 129. [Google Scholar] [CrossRef]
- Aumüller, C.; Bier, P.; Fischer, W.; Hofreiter, P.; Seifert, J. Fault Attacks on RSA with CRT: Concrete Results and Practical Countermeasures. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2002, 4th International Workshop, Redwood Shores, CA, USA, 13–15 August 2002; Revised Paper; Lecture Notes in Computer Science; Kaliski, B.S., Jr., Koç, Ç.K., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2523, pp. 260–275. [Google Scholar] [CrossRef]
- Biham, E.; Shamir, A. Differential Fault Analysis of Secret Key Cryptosystems. In Proceedings of the Advances in Cryptology—CRYPTO ’97, 17th Annual International Cryptology Conference, Santa Barbara, CA, USA, 17–21 August 1997; Proceedings; Lecture Notes in Computer Science; Kaliski, B.S., Jr., Ed.; Springer: Berlin/Heidelberg, Germany, 1997; Volume 1294, pp. 513–525. [Google Scholar] [CrossRef]
- Hemme, L. A Differential Fault Attack against Early Rounds of (Triple-)DES. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2004: 6th International Workshop Cambridge, MA, USA, 11–13 August 2004; Proceedings; Lecture Notes in Computer Science; Joye, M., Quisquater, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3156, pp. 254–267. [Google Scholar] [CrossRef]
- Rivain, M. Differential Fault Analysis on DES Middle Rounds. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2009, 11th International Workshop, Lausanne, Switzerland, 6–9 September 2009; Proceedings; Lecture Notes in Computer Science; Clavier, C., Gaj, K., Eds.; Springer: Berlin/Heidelberg, Germany, 2009; Volume 5747, pp. 457–469. [Google Scholar] [CrossRef]
- Piret, G.; Quisquater, J. A Differential Fault Attack Technique against SPN Structures, with Application to the AES and KHAZAD. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2003, 5th International Workshop, Cologne, Germany, 8–10 September 2003; Proceedings; Lecture Notes in Computer Science; Walter, C.D., Koç, Ç.K., Paar, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2779, pp. 77–88. [Google Scholar] [CrossRef]
- Dusart, P.; Letourneux, G.; Vivolo, O. Differential Fault Analysis on A.E.S. In Proceedings of the Applied Cryptography and Network Security, First International Conference, ACNS 2003, Kunming, China, 16–19 October 2003; Proceedings; Lecture Notes in Computer Science; Zhou, J., Yung, M., Han, Y., Eds.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2846, pp. 293–306. [Google Scholar] [CrossRef]
- Blömer, J.; Seifert, J. Fault Based Cryptanalysis of the Advanced Encryption Standard (AES). In Proceedings of the Financial Cryptography, 7th International Conference, FC 2003, Guadeloupe, French West Indies, 27–30 January 2003; Revised Papers; Lecture Notes in Computer Science; Wright, R.N., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2742, pp. 162–181. [Google Scholar] [CrossRef]
- Giraud, C. DFA on AES. In Proceedings of the Advanced Encryption Standard—AES, 4th International Conference, AES 2004, Bonn, Germany, 10–12 May 2004; Revised Selected and Invited Papers; Lecture Notes in Computer Science; Dobbertin, H., Rijmen, V., Sowa, A., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3373, pp. 27–41. [Google Scholar] [CrossRef]
- Moradi, A.; Shalmani, M.T.M.; Salmasizadeh, M. A Generalized Method of Differential Fault Attack Against AES Cryptosystem. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2006, 8th International Workshop, Yokohama, Japan, 10–13 October 2006; Proceedings; Lecture Notes in Computer Science; Goubin, L., Matsui, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4249, pp. 91–100. [Google Scholar] [CrossRef]
- Derbez, P.; Fouque, P.; Leresteux, D. Meet-in-the-Middle and Impossible Differential Fault Analysis on AES. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2011—13th International Workshop, Nara, Japan, 28 September–1 October 2011; Proceedings; Lecture Notes in Computer Science; Preneel, B., Takagi, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; Volume 6917, pp. 274–291. [Google Scholar] [CrossRef]
- Yuce, B.; Schaumont, P.; Witteman, M. Fault Attacks on Secure Embedded Software: Threats, Design, and Evaluation. J. Hardw. Syst. Secur. 2018, 2, 111–130. [Google Scholar] [CrossRef]
- Selmke, B.; Heyszl, J.; Sigl, G. Attack on a DFA Protected AES by Simultaneous Laser Fault Injections. In Proceedings of the 2016 Workshop on Fault Diagnosis and Tolerance in Cryptography, FDTC 2016, Santa Barbara, CA, USA, 16 August 2016; IEEE Computer Society: Piscataway, NJ, USA, 2016; pp. 36–46. [Google Scholar] [CrossRef]
- Santis, F.D.; Guillen, O.M.; Sakic, E.; Sigl, G. Ciphertext-Only Fault Attacks on PRESENT. In Proceedings of the Lightweight Cryptography for Security and Privacy—Third International Workshop, LightSec 2014, Istanbul, Turkey, 1–2 September 2014; Revised Selected Papers; Lecture Notes in Computer Science; Eisenbarth, T., Öztürk, E., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8898, pp. 85–108. [Google Scholar] [CrossRef]
- Ghalaty, N.F.; Yuce, B.; Schaumont, P. Differential Fault Intensity Analysis on PRESENT and LED Block Ciphers. In Proceedings of the Constructive Side-Channel Analysis and Secure Design—6th International Workshop, COSADE 2015, Berlin, Germany, 13–14 April 2015; Revised Selected Papers; Lecture Notes in Computer Science; Mangard, S., Poschmann, A.Y., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9064, pp. 174–188. [Google Scholar] [CrossRef]
- Patranabis, S.; Breier, J.; Mukhopadhyay, D.; Bhasin, S. One Plus One is More than Two: A Practical Combination of Power and Fault Analysis Attacks on PRESENT and PRESENT-Like Block Ciphers. In Proceedings of the 2017 Workshop on Fault Diagnosis and Tolerance in Cryptography, FDTC 2017, Taipei, Taiwan, 25 September 2017; IEEE Computer Society: Piscataway, NJ, USA, 2017; pp. 25–32. [Google Scholar] [CrossRef]
- Fukunaga, T.; Takahashi, J. Practical Fault Attack on a Cryptographic LSI with ISO/IEC 18033-3 Block Ciphers. In Proceedings of the Sixth International Workshop on Fault Diagnosis and Tolerance in Cryptography, FDTC 2009, Lausanne, Switzerland, 6 September 2009; Breveglieri, L., Koren, I., Naccache, D., Oswald, E., Seifert, J., Eds.; IEEE Computer Society: Piscataway, NJ, USA, 2009; pp. 84–92. [Google Scholar] [CrossRef]
- Tupsamudre, H.; Bisht, S.; Mukhopadhyay, D. Differential Fault Analysis on the Families of SIMON and SPECK Ciphers. In Proceedings of the 2014 Workshop on Fault Diagnosis and Tolerance in Cryptography, FDTC 2014, Busan, Republic of Korea Korea, 23 September 2014; Tria, A., Choi, D., Eds.; IEEE Computer Society: Piscataway, NJ, USA, 2014; pp. 40–48. [Google Scholar] [CrossRef]
- Simon, T.; Batina, L.; Daemen, J.; Grosso, V.; Massolino, P.M.C.; Papagiannopoulos, K.; Regazzoni, F.; Samwel, N. Friet: An Authenticated Encryption Scheme with Built-in Fault Detection. In Proceedings of the Advances in Cryptology—EUROCRYPT 2020—39th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Zagreb, Croatia, 10–14 May 2020; Proceedings, Part I; Lecture Notes in Computer Science; Canteaut, A., Ishai, Y., Eds.; Springer: Berlin/Heidelberg, Germany, 2020; Volume 12105, pp. 581–611. [Google Scholar] [CrossRef]
- Beierle, C.; Leander, G.; Moradi, A.; Rasoolzadeh, S. CRAFT: Lightweight Tweakable Block Cipher with Efficient Protection Against DFA Attacks. IACR Trans. Symmetric Cryptol. 2019, 2019, 5–45. [Google Scholar] [CrossRef]
- Baksi, A.; Bhasin, S.; Breier, J.; Khairallah, M.; Peyrin, T.; Sarkar, S.; Sim, S.M. DEFAULT: Cipher Level Resistance against Differential Fault Attack. In Proceedings of the Advances in Cryptology—ASIACRYPT 2021—27th International Conference on the Theory and Application of Cryptology and Information Security, Singapore, 6–10 December 2021; Proceedings, Part II; Lecture Notes in Computer Science; Tibouchi, M., Wang, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2021; Volume 13091, pp. 124–156. [Google Scholar] [CrossRef]
- Medwed, M.; Standaert, F.; Großschädl, J.; Regazzoni, F. Fresh Re-keying: Security against Side-Channel and Fault Attacks for Low-Cost Devices. In Proceedings of the Progress in Cryptology—AFRICACRYPT 2010, Third International Conference on Cryptology in Africa, Stellenbosch, South Africa, 3–6 May 2010; Proceedings; Lecture Notes in Computer Science; Bernstein, D.J., Lange, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; Volume 6055, pp. 279–296. [Google Scholar] [CrossRef]
- Medwed, M.; Petit, C.; Regazzoni, F.; Renauld, M.; Standaert, F. Fresh Re-keying II: Securing Multiple Parties against Side-Channel and Fault Attacks. In Proceedings of the Smart Card Research and Advanced Applications—10th IFIPWG8.8/11.2 International Conference, CARDIS 2011, Leuven, Belgium, 14–16 September 2011; Revised Selected Papers; Lecture Notes in Computer Science; Prouff, E., Ed.; Springer: Berlin/Heidelberg, Germany, 2011; Volume 7079, pp. 115–132. [Google Scholar] [CrossRef]
- Dobraunig, C.; Koeune, F.; Mangard, S.; Mendel, F.; Standaert, F. Towards Fresh and Hybrid Re-Keying Schemes with Beyond Birthday Security. In Proceedings of the Smart Card Research and Advanced Applications—14th International Conference, CARDIS 2015, Bochum, Germany, 4–6 November 2015; Revised Selected Papers; Lecture Notes in Computer Science; Homma, N., Medwed, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9514, pp. 225–241. [Google Scholar] [CrossRef]
- Lomné, V.; Roche, T.; Thillard, A. On the Need of Randomness in Fault Attack Countermeasures—Application to AES. In Proceedings of the 2012 Workshop on Fault Diagnosis and Tolerance in Cryptography, Leuven, Belgium, 9 September 2012; Bertoni, G., Gierlichs, B., Eds.; IEEE Computer Society: Piscataway, NJ, USA, 2012; pp. 85–94. [Google Scholar] [CrossRef]
- Malkin, T.; Standaert, F.; Yung, M. A Comparative Cost/Security Analysis of Fault Attack Countermeasures. In Proceedings of the Fault Diagnosis and Tolerance in Cryptography, Third International Workshop, FDTC 2006, Yokohama, Japan, 10 October 2006; Proceedings; Lecture Notes in Computer Science; Breveglieri, L., Koren, I., Naccache, D., Seifert, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4236, pp. 159–172. [Google Scholar] [CrossRef]
- Maistri, P.; Leveugle, R. Double-Data-Rate Computation as a Countermeasure against Fault Analysis. IEEE Trans. Comput. 2008, 57, 1528–1539. [Google Scholar] [CrossRef]
- Joye, M.; Manet, P.; Rigaud, J. Strengthening hardware AES implementations against fault attacks. IET Inf. Secur. 2007, 1, 106–110. [Google Scholar] [CrossRef]
- Barenghi, A.; Breveglieri, L.; Koren, I.; Pelosi, G.; Regazzoni, F. Countermeasures against fault attacks on software implemented AES: Effectiveness and cost. In Proceedings of the 5th Workshop on Embedded Systems Security, WESS 2010, Scottsdale, AZ, USA, 24 October 2010; ACM: New York, NY, USA, 2010; p. 7. [Google Scholar] [CrossRef]
- Diffie, W.; Hellman, M.E. Special Feature Exhaustive Cryptanalysis of the NBS Data Encryption Standard. Computer 1977, 10, 74–84. [Google Scholar] [CrossRef]
- Dong, X.; Hua, J.; Sun, S.; Li, Z.; Wang, X.; Hu, L. Meet-in-the-Middle Attacks Revisited: Key-Recovery, Collision, and Preimage Attacks. In Proceedings of the Advances in Cryptology—CRYPTO 2021—41st Annual International Cryptology Conference, CRYPTO 2021, Virtual Event, 16–20 August 2021; Proceedings, Part III; Lecture Notes in Computer Science; Malkin, T., Peikert, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2021; Volume 12827, pp. 278–308. [Google Scholar] [CrossRef]
- Hua, J.; Dong, X.; Sun, S.; Zhang, Z.; Hu, L.; Wang, X. Improved MITM Cryptanalysis on Streebog. IACR Trans. Symmetric Cryptol. 2022, 2022, 63–91. [Google Scholar] [CrossRef]
- Dinur, I.; Dunkelman, O.; Keller, N.; Shamir, A. New Attacks on Feistel Structures with Improved Memory Complexities. In Proceedings of the Advances in Cryptology—CRYPTO 2015—35th Annual Cryptology Conference, Santa Barbara, CA, USA, 16–20 August 2015; Proceedings, Part I; Lecture Notes in Computer Science; Gennaro, R., Robshaw, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9215, pp. 433–454. [Google Scholar] [CrossRef]
- Dinur, I.; Dunkelman, O.; Keller, N.; Shamir, A. Cryptanalysis of Iterated Even-Mansour Schemes with Two Keys. In Proceedings of the Advances in Cryptology—ASIACRYPT 2014—20th International Conference on the Theory and Application of Cryptology and Information Security, Kaoshiung, Taiwan, 7–11 December 2014; Proceedings, Part I; Lecture Notes in Computer Science; Sarkar, P., Iwata, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8873, pp. 439–457. [Google Scholar] [CrossRef]
- Dunkelman, O.; Sekar, G.; Preneel, B. Improved Meet-in-the-Middle Attacks on Reduced-Round DES. In Proceedings of the Progress in Cryptology—INDOCRYPT 2007, 8th International Conference on Cryptology in India, Chennai, India, 9–13 December 2007; Proceedings; Lecture Notes in Computer Science; Srinathan, K., Rangan, C.P., Yung, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; Volume 4859, pp. 86–100. [Google Scholar] [CrossRef]
- Karakoç, F.; Demirci, H.; Harmanci, A.E. ITUbee: A Software Oriented Lightweight Block Cipher. In Proceedings of the Lightweight Cryptography for Security and Privacy—Second International Workshop, LightSec 2013, Gebze, Turkey, 6–7 May 2013; Revised Selected Papers; Lecture Notes in Computer Science; Avoine, G., Kara, O., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8162, pp. 16–27. [Google Scholar] [CrossRef]
- Soleimany, H. Self-similarity cryptanalysis of the block cipher ITUbee. IET Inf. Secur. 2015, 9, 179–184. [Google Scholar] [CrossRef]
- Fu, S.; Xu, G.; Pan, J.; Wang, Z.; Wang, A. Differential Fault Attack on ITUbee Block Cipher. ACM Trans. Embed. Comput. Syst. 2016, 16, 1–10. [Google Scholar] [CrossRef]
- Daemen, J.; Rijmen, V. The Design of Rijndael: AES—The Advanced Encryption Standard; Information Security and Cryptography; Springer: Berlin/Heidelberg, Germany, 2002. [Google Scholar] [CrossRef]
- Gilbert, H.; Peyrin, T. Super-Sbox Cryptanalysis: Improved Attacks for AES-Like Permutations. In Proceedings of the Fast Software Encryption, 17th International Workshop, FSE 2010, Seoul, Republic of Korea, 7–10 February 2010; Revised Selected Papers; Lecture Notes in Computer Science; Hong, S., Iwata, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2010; Volume 6147, pp. 365–383. [Google Scholar] [CrossRef]



| Number of Faults | Computational Complexity | Memory Complexity | Precomputational Complexity | |
|---|---|---|---|---|
| Scheme 1 | 1 | |||
| Scheme 2 | 4 | - | ||
| Scheme 3 | 3 |
| Number of Faults | Faults Injection Round | Computational Complexity | Memory Complexity | Precomputational Complexity | |
|---|---|---|---|---|---|
| Our Scheme 3 | 3 | third to last | |||
| Fu et al.’s Scheme 2 | 4 | second to last |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kang, Y.; Yu, Q.; Qin, L.; Zhang, G. Meet-in-the-Middle Differential Fault Analysis on ITUbee Block Cipher. Symmetry 2023, 15, 1196. https://doi.org/10.3390/sym15061196
Kang Y, Yu Q, Qin L, Zhang G. Meet-in-the-Middle Differential Fault Analysis on ITUbee Block Cipher. Symmetry. 2023; 15(6):1196. https://doi.org/10.3390/sym15061196
Chicago/Turabian StyleKang, Yongze, Qingyuan Yu, Lingyue Qin, and Guoyan Zhang. 2023. "Meet-in-the-Middle Differential Fault Analysis on ITUbee Block Cipher" Symmetry 15, no. 6: 1196. https://doi.org/10.3390/sym15061196
APA StyleKang, Y., Yu, Q., Qin, L., & Zhang, G. (2023). Meet-in-the-Middle Differential Fault Analysis on ITUbee Block Cipher. Symmetry, 15(6), 1196. https://doi.org/10.3390/sym15061196






