Blind Color Image Watermarking Using Fan Beam Transform and QR Decomposition
Abstract
1. Introduction
2. Background Information
2.1. Fan Beam Transform
2.2. QR Decomposition
3. Proposed Watermarking Algorithm
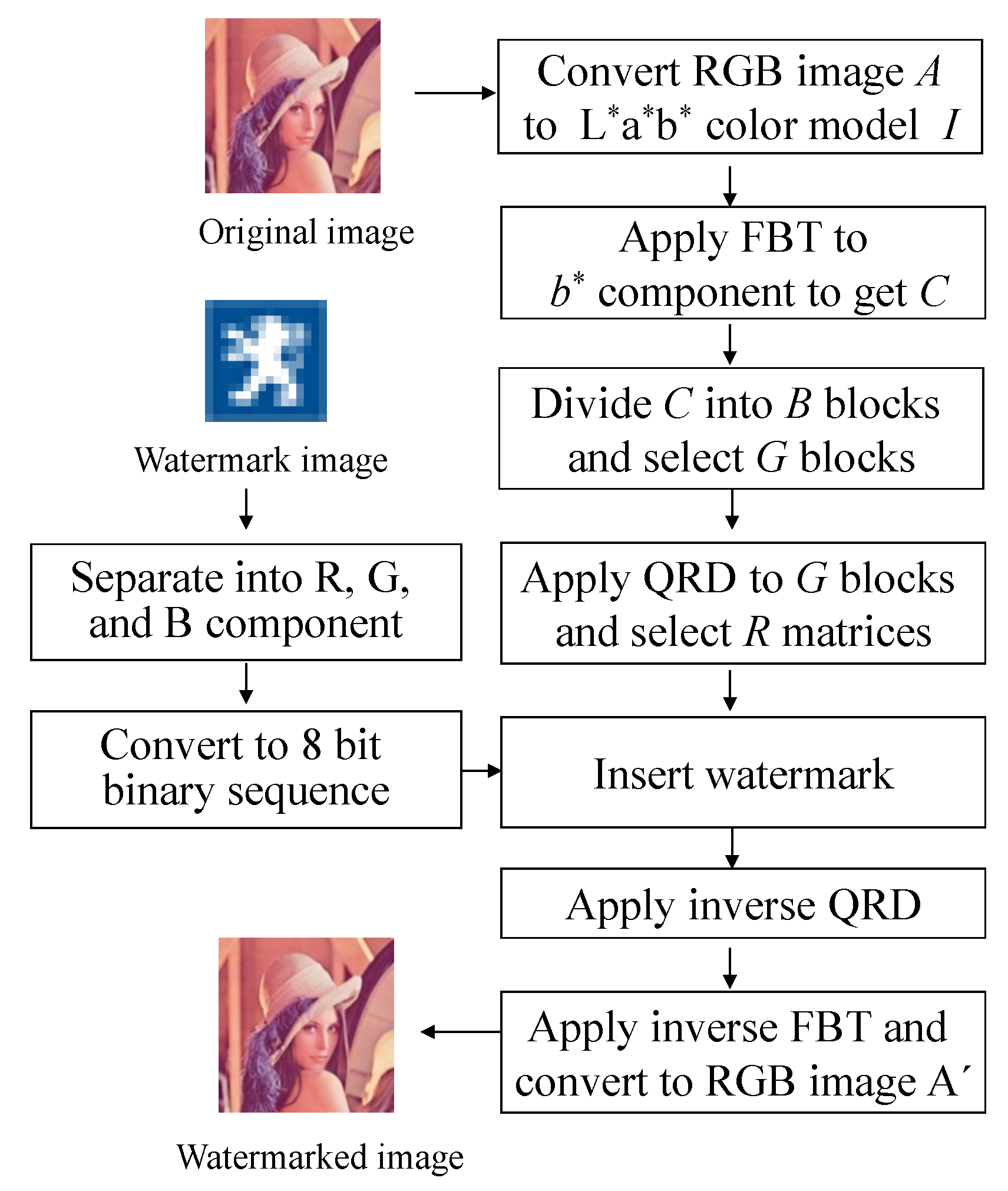
3.1. Watermark Embedding Process
| Algorithm 1: Watermark Inserting Procedure |
| Declaring variables: |
| A: original RGB image |
| : converted L*a*b* image |
| Y: watermark sequence |
| C: FBT coefficients |
| B: block with size m × m |
| G: selected block with size m × m |
| Q: unitary matrix with size m × m |
| R: upper triangular matrix with size of m × m |
| = selected element for embedding watermark |
| FBT and QRD: transformation and decomposition used in the algorithm |
| Watermark Embedding Procedure: |
| Read the host image and watermark image |
| A.bmp (original image with size 512 × 512) |
| W.bmp (color watermark image with size of 16 × 16) |
| for i = 1: N |
| j = 1: N do |
| Separate W into R, G, and B components and convert them into binary sequence |
| end for |
| return the watermark sequence |
| for k = 1: M |
| l = 1: M do |
| A is transferred from RGB to L*a*b* color model |
| end for |
| Select b* channel and apply FBT to obtain C |
| for i = 1: r |
| Separate C into r blocks B |
| end for |
| Calculate determinant of each block B and select largest n blocks |
| for p = 1: N × N |
| Insert watermark using Equation (5) when y(p) = 0 |
| Insert watermark using Equation (6) when y(p) = 1 |
| end for |
| Perform inverse QRD |
| Perform IFBT to get modified channel b* |
| The modified L*a*b’* color model is transformed into RGB color model |
| return watermarked image A’ |
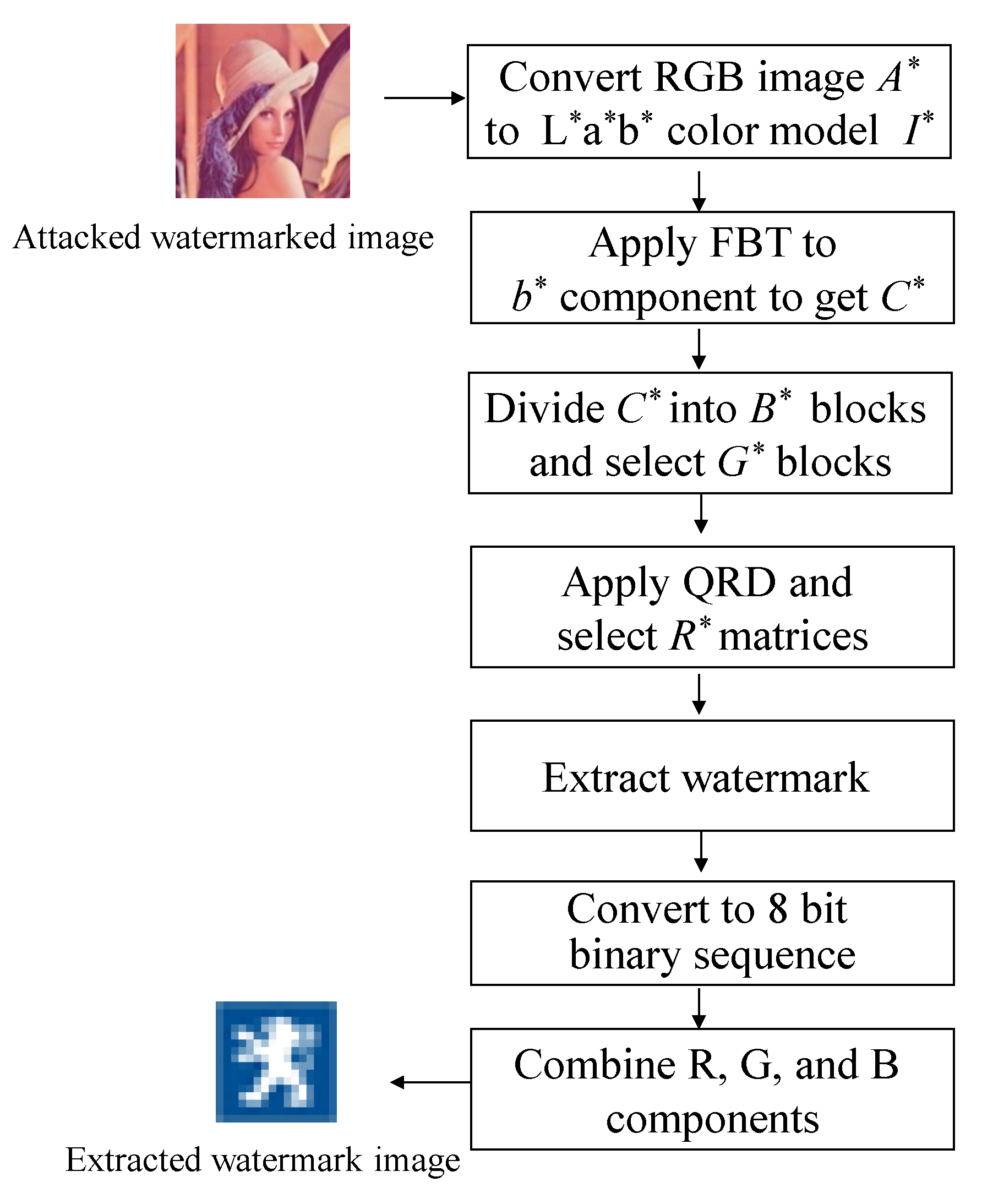
3.2. Watermark Detection Process
| Algorithm 2: Watermark extracting procedure |
| Declaring variables: |
| A*: attacked watermarked RGB image |
| I*: attacked watermarked L*a*b* image |
| Y*: extracted watermark sequence |
| C*: modified FBT coefficients |
| B*: modified block with size m × m |
| G*: modified selected block with size m × m |
| Q*: modified unitary matrix with size m × m |
| R*: modified upper triangular matrix with size m × m |
| = selected element for extracted watermark |
| FBT and QRD: transformation and decomposition used in the algorithm |
| Watermark extraction procedure: |
| Read the attacked watermarked image |
| A*.bmp (attacked watermark image with size of 512 × 512) |
| for k = 1: M |
| l = 1: M do |
| A* is transferred from RGB to L*a*b* color model |
| end for |
| Select b* channel and apply FBT to obtain C* |
| for i = 1: r |
| Separate C* into r blocks B* |
| end for |
| Calculate determinant of each block B* and select largest n blocks |
| for p = 1: N × N |
| Extract watermark using Equation (7) |
| end for |
| Separate the extracted bits into 8-bits per group |
| Convert each group into decimal value to get the R, G, B components |
| Combine the R, G, and B components to get the watermark image |
3.3. Performance Assessment of Proposed Algorithm
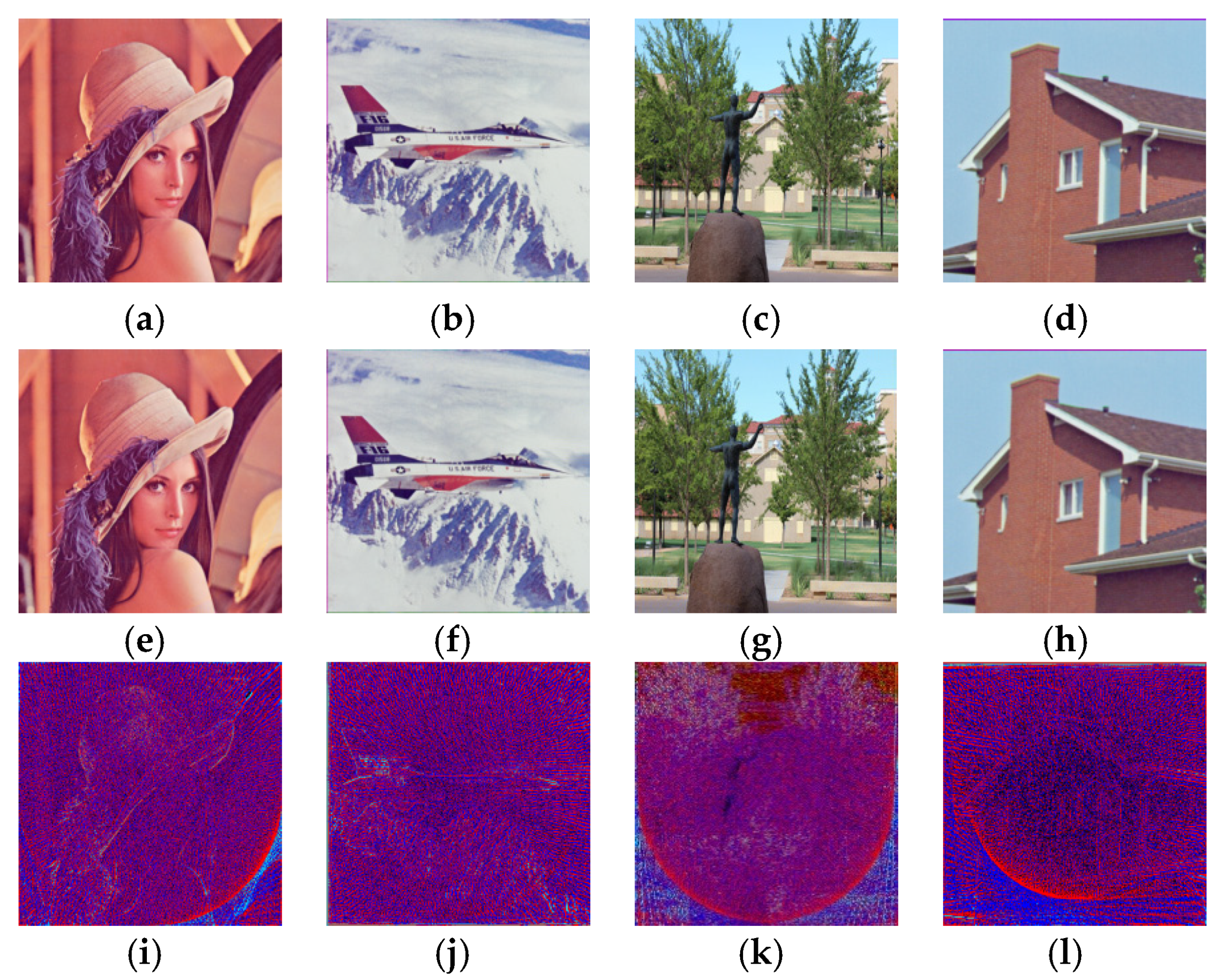
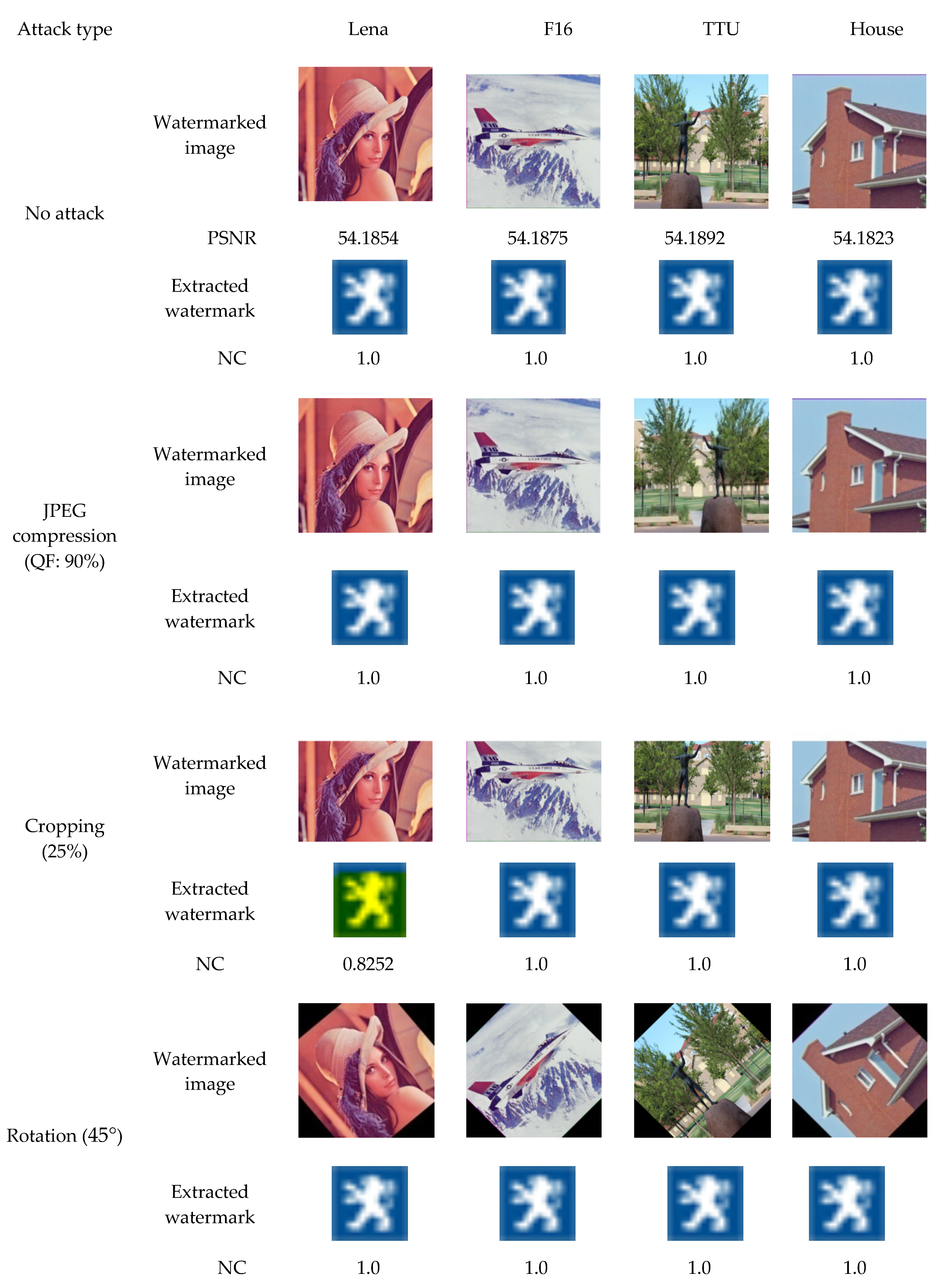
4. Simulation Results and Discussion
- JPEG compression: the watermarked images were compressed using JPEG compression (QF = 90);
- Cropping: the watermarked images were cropped (25%) from the top;
- Rotation attack: the watermarked images were rotated by 45° and the rotated images were re-rotated in a counter-clockwise for extraction;
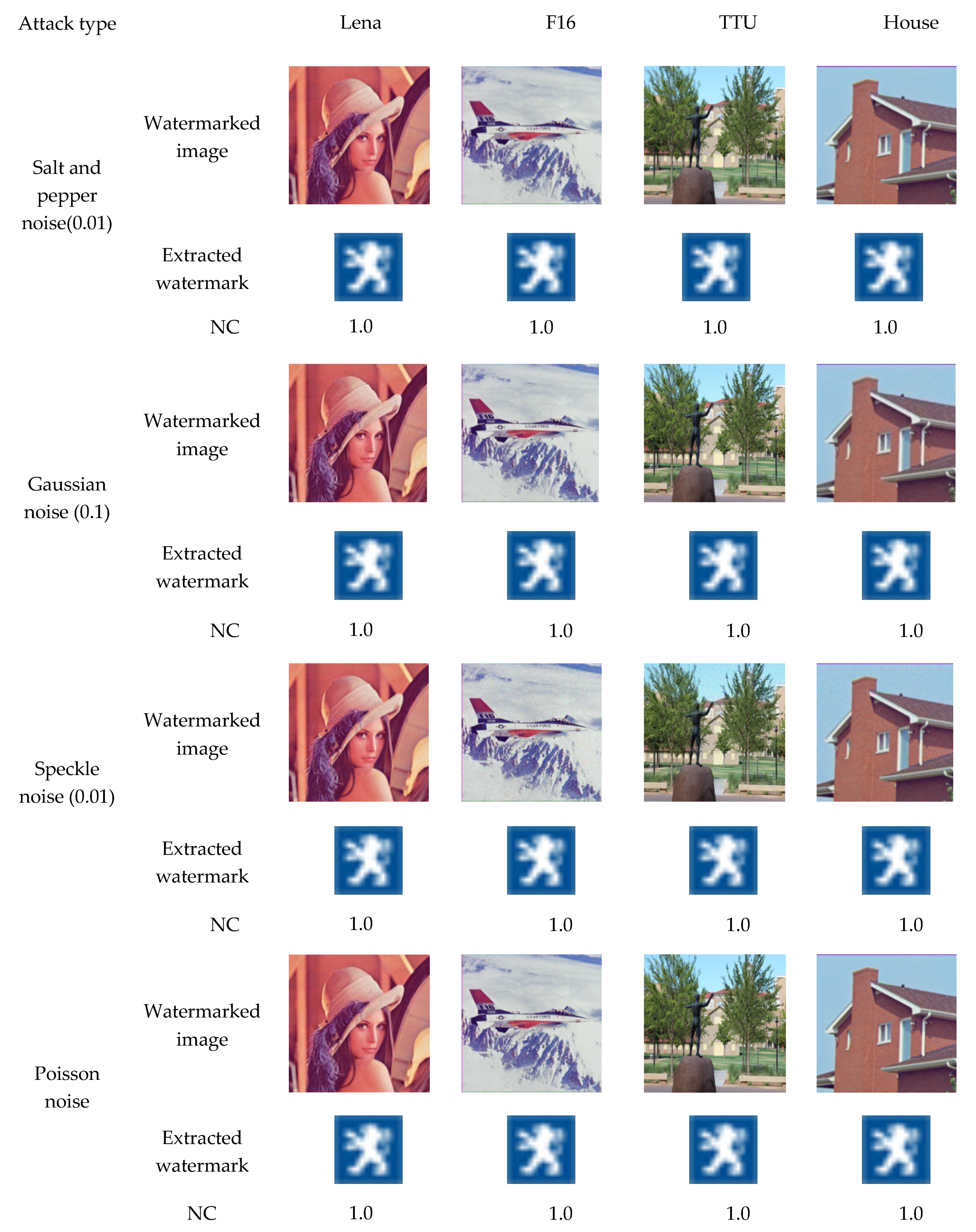
- Gaussian noise: the watermarked images were attacked by Gaussian noise with variance 0.1;
- Speckle noise: the watermarked images were attacked by speckle noise with variance 0.01;
- Salt and pepper noise: Salt and pepper noise with variance 0.01 is performed to the watermarked images;
- Poisson noise: the watermarked images were attacked by Poisson noise with scaling factor 1e12;
- Contrast adjustment: the watermarked images were attacked by contrast adjustment;
- Sharpening: the watermarked images were attacked by sharpening with tolerance 0.1;
- Median filtering: the watermarked images were attacked by 3 × 3 median filter;
- Wiener filtering: the watermarked images were attacked by 3 × 3 wiener filter.
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Cox, I.J.; Miller, M.L. The first 50 years of electronic watermarking. EURASIP J. Adv. Signal Proces. 2002, 56, 126–132. [Google Scholar] [CrossRef]
- Tao, H.; Chongmin, L.; Zain, J.M.; Abdalla, A.N.T. Robust image watermarking theories and techniques: A review. J. Appl. Res. Technol. 2014, 12, 122–138. [Google Scholar] [CrossRef]
- Dhar, P.K.; Shimamura, T. Advances in Audio Watermarking Based on Singular Value Decomposition; Springer: Berlin, Germany, 2015; ISBN 978-3-319-14799-4. [Google Scholar]
- Celik, M.; Sharma, U.; Saber, G.E.; Tekalp, A.M. Hierarchical watermarking for secure image authentication with localization. IEEE Trans. Image Process. 2002, 11, 585–595. [Google Scholar] [CrossRef] [PubMed]
- Haj, A.A. Combined DWT-DCT digital image watermarking. J. Comput. Sci. 2007, 3, 740–746. [Google Scholar]
- Dejey, D.; Rajesh, R.S. Robust discrete wavelet–fan beam transforms-based color image watermarking. IET Image Process. 2011, 5, 315–322. [Google Scholar] [CrossRef]
- Shuai, L.; Zheng, P.; Houbing, S. Digital image watermarking method based on DCT and fractal encoding. IET Image Process. 2017, 11, 815–821. [Google Scholar]
- Roy, S.; Pal, A.K. A robust blind hybrid image watermarking scheme in RDWT-DCT domain using Arnold scrambling. Multimed. Tools Appl. 2017, 76, 3577–3616. [Google Scholar] [CrossRef]
- Abdulrahman, A.K.; Ozturk, S. A novel hybrid DCT and DWT based robust watermarking algorithm for color images. Multimed. Tools Appl. 2019, 78, 17027–17049. [Google Scholar] [CrossRef]
- Hamidi, M.; El Haziti, M.; Cherifi, H.; El Hassouni, M. Hybrid blind robust image watermarking technique based on DFT-DCT and Arnold transform. Multimed. Tools Appl. 2018, 77, 27181–27214. [Google Scholar] [CrossRef]
- Ahmad, A.M.; Ali, A.; Sameer, S. An improved SVD-based watermarking scheme for protecting rightful ownership. Signal Process. 2008, 88, 2158–2180. [Google Scholar]
- Mohashin, A.H.M.; Dhar, P.K.; Shimamura, T. Blind image watermarking based on discrete Hilbert transform and polar decomposition. In Proceedings of the 11th International Conference on Knowledge and Smart Technology (KST-2019), Phuket, Thailand, 23–26 January 2019; pp. 78–81. [Google Scholar]
- Li, J.; Zhang, C. Blind and robust watermarking scheme combining bimodal distribution structure with iterative selection method. Multimed. Tools Appl. 2019, 1–35. [Google Scholar] [CrossRef]
- Roy, S.; Pal, A.K. A blind DCT based color watermarking algorithm for embedding multiple watermarks. AEU Int. J. Electron. Commun. 2017, 72, 149–161. [Google Scholar] [CrossRef]
- Su, Q.; Niu, Y.; Wang, G.; Jia, S.; Yue, J. Color image blind watermarking scheme based on QR decomposition. Signal Process. 2014, 94, 219–235. [Google Scholar] [CrossRef]
- Su, Q.; Niu, Y.; Zou, H.; Liu, X. A blind dual color image watermarking based on singular value decomposition. Appl. Math. Comput. 2013, 219, 8455–8466. [Google Scholar] [CrossRef]
- Chih-Chin, L.; Cheng-Chih, T. Digital image watermarking using discrete wavelet transform and singular value decomposition. IEEE Trans. Instrum. Meas. 2010, 59, 3060–3063. [Google Scholar]
- Bhatnagar, G.; Raman, B. A new robust reference watermarking scheme based on DWT-SVD. Comput. Stand. Interfaces 2009, 31, 1002–1013. [Google Scholar] [CrossRef]
- Su, Q.; Yuan, Z.; Liu, D. An approximate schur decomposition-based spatial domain color image watermarking method. IEEE Access 2018, 7, 4358–4370. [Google Scholar] [CrossRef]
- Su, Q.; Wang, G.; Zhang, X.; Lv, G.; Chen, B. A new algorithm of blind color image watermarking based on LU decomposition. Multidimens. Syst. Signal Process. 2018, 29, 1055–1074. [Google Scholar] [CrossRef]
- Khanam, T.; Dhar, P.K.; Kowsar, S.; Kim, J.-M. SVD-based image watermarking using the fast walsh-Hadamard transform, key mapping, and coefficient ordering for ownership protection. Symmetry 2020, 12, 52. [Google Scholar] [CrossRef]
- Wang, Z.; Bovik, A.C.; Sheikh, H.R.; Simoncelli, E.P. Image quality assessment: From error visibility to structural similarity. IEEE Trans. Image Process. 2004, 13, 600–612. [Google Scholar] [CrossRef] [PubMed]
- The USC-SIPI Image Database. 2009. Available online: http://sipi.usc.edu/database/ (accessed on 7 January 2019).


| Image | Parameter | Su et al. [19] | Su et al. [20] | Khanam et al. [21] | Proposed Method |
|---|---|---|---|---|---|
| Lena | PSNR | 40.5079 | 39.4428 | 50.0467 | 54.1854 |
| SSIM | 0.9534 | 0.9416 | 0.9542 | 0.9696 | |
| F16 | PSNR | 41.6091 | 37.1729 | 51.6431 | 54.1875 |
| SSIM | 0.9540 | 0.9311 | 0.9426 | 0.9664 | |
| TTU | PSNR | 39.4805 | 39.6781 | 50.7542 | 54.1892 |
| SSIM | 0.9537 | 0.9458 | 0.9331 | 0.9285 | |
| House | PSNR | 39.7134 | 41.1739 | 48.3143 | 54.1823 |
| SSIM | 0.9663 | 0.9524 | 0.9372 | 0.9579 | |
| Average | PSNR | 40.3277 | 39.3669 | 50.1896 | 54.1861 |
| SSIM | 0.9568 | 0.9427 | 0.9418 | 0.9595 |
| Attack Type | Su et al. [19] | Su et al. [20] | Khanam et al. [21] (With Key) | Khanam et al. [21] (Without Key) | Proposed Method |
|---|---|---|---|---|---|
| Gaussiannoise (0.1) | 0.9625 | 0.8823 | 1.0 | 0.9351 | 1.0 |
| Specklenoise (0.01) | 0.9663 | 0.9647 | 1.0 | 0.9349 | 1.0 |
| Cropping (25%) | 0.6482 | 0.8619 | 1.0 | 0.8352 | 0.8252 |
| Sharpening (tol = 0.1) | 0.9935 | 0.9882 | 1.0 | 0.8594 | 1.0 |
| Rotation (45°) | 0.9361 | 0.9225 | 1.0 | 0.5193 | 1.0 |
| Wiener filtering | 0.9578 | 0.9765 | 1.0 | 0.6771 | 1.0 |
| Salt and pepper noise (0.01) | 0.9478 | 0.9733 | 1.0 | 0.9944 | 1.0 |
| Median filtering | 0.9419 | 0.8997 | 1.0 | 0.9459 | 1.0 |
| JPEG Compression (90%) | 0.9998 | 0.9791 | 1.0 | 0.7876 | 1.0 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Dhar, P.K.; Hazra, P.; Shimamura, T. Blind Color Image Watermarking Using Fan Beam Transform and QR Decomposition. Symmetry 2020, 12, 486. https://doi.org/10.3390/sym12030486
Dhar PK, Hazra P, Shimamura T. Blind Color Image Watermarking Using Fan Beam Transform and QR Decomposition. Symmetry. 2020; 12(3):486. https://doi.org/10.3390/sym12030486
Chicago/Turabian StyleDhar, Pranab Kumar, Pulak Hazra, and Tetsuya Shimamura. 2020. "Blind Color Image Watermarking Using Fan Beam Transform and QR Decomposition" Symmetry 12, no. 3: 486. https://doi.org/10.3390/sym12030486
APA StyleDhar, P. K., Hazra, P., & Shimamura, T. (2020). Blind Color Image Watermarking Using Fan Beam Transform and QR Decomposition. Symmetry, 12(3), 486. https://doi.org/10.3390/sym12030486




