Abstract
A group key establishment protocol is presented and proven secure in the common reference string mode. The protocol builds on a group-theoretic assumption, and a concrete example can be obtained with a decision Diffie–Hellman assumption. The protocol is derived from a two-party solution by means of a protocol compiler presented by Abdalla et al. at TCC 2007, evidencing the possibility of meaningfully integrating cryptographic and group-theoretic tools in cryptographic protocol design. This compiler uses a standard ring configuration, where all users behave symmetrically, exchanging keys with their left and right neighbor, which are later combined to yield a shared group key.
1. Introduction
Cryptography is the science of handling, storing, transmitting, and processing information securely, even in the presence of adversaries. For centuries, cryptographic techniques were developed for diplomatic or military scenarios, while nowadays individuals and institutions (often obliviously) make use of cryptographic tools every day. As a complex discipline, cryptography builds upon physics, mathematics, and different research areas within computer science. Mathematics are the main source of tools for cryptographic developments, in which, security is often demonstrated using the hardness of well understood mathematical problems. This paper is concerned with the construction of a widely used cryptographic tool, a group key exchange, using group theory as a base. Key exchange allows a number of users to establish a common secret value which will be subsequently used to secure their communication. Such cryptographic tools are often constructed from number theoretical problems (described in finite cyclic groups), and a challenging research question is whether secure constructions can be derived from different problems arising in group theory.
In recent years, not only due to the advent of quantum computation, significant efforts have been made to identify new mathematical platforms for implementing cryptographic schemes. One of the explored candidate platforms is the theory of finitely presented groups, where, in particular, a number of works on key establishment have been published. The first constructions in this direction where published about twenty years ago [1,2,3], and different approaches towards secure constructions have been explored regularly, such as [4,5,6,7,8,9], and the more recently [10]. Unfortunately, most of the proposed protocols have not been analyzed in a modern cryptographic security model (like [11,12,13,14,15,16]), and only few group-theoretic constructions with a rigorous security analysis seem to be known. This lack of formalism has resulted in weaknesses being overlooked (see, for instance, [17]).
One approach to facilitate the synergy between group-theoretic and cryptographic tools is the identification of general constructions that under suitable group-theoretic conditions yield an (efficient) cryptographic scheme with provable security guarantees. As examples for research along this line of thought, proposals for constructing IND-CCA secure asymmetric encryption schemes can be mentioned [18,19]. Also, constructions for building provably secure group key establishment schemes have been proposed (cf. [20,21]), but identifying practical non-abelian instances still appears to be a challenging problem. In this contribution, we build on [21], and try to extend and simplify their approach in the following sense:
- Instead of the random oracle model, we use the common reference string model. An (expected) price we pay for this, is the need of a decisional assumption instead of a computational one that is used in [21].
- Instead of setting out for a group key establishment directly, we suggest a construction for the two-party case and thereafter apply a protocol compiler of Abdalla et al. [22].
In terms of round complexity, we lose some efficiency through the modular design approach we chose. On the other hand, this modular design approach illustrates how an integration of group-theoretic and cryptographic tools can look like. Moreover, we obtain a comparatively clear group-theoretic condition which hopefully stimulates further research on finding concrete non-abelian instances. Concrete examples of our protocol can be derived from a decision Diffie–Hellman assumption, but we hope that in subsequent work also concrete non-abelian instances can be identified.
2. Preliminaries: Security Model and Protocol Goals
To explore the security of our protocol, we adopt the model used by Abdalla et al. [22], which can be traced back to [23,24,25,26,27]. Both to formulate our two-party solution and to use the “2-to-n compiler” from [22], we assume a common reference string (CRS) to be available that encodes the following information:
- Two values , These will be the input for a pseudorandom function at the time of computing the session identifier and session key;
- The information necessary to implement a non-interactive and non-malleable commitment scheme (see Section 3.1 for further details);
- Two elements, chosen independently and uniformly at random, each taken from a family of universal hash functions (one as needed for the compiler in [22] and one for our two-party solution as detailed in Section 3.1).
This is similar to the constructions for password-authenticated key establishment in [24,27].
2.1. Communication Model and Adversarial Capabilities
As usual, we model protocol participants as probabilistic polynomial time (ppt) Turing machines (all our proofs hold for both uniform and non-uniform machines). We denote by the total set of users which is assumed to be of polynomial size and by the set of protocol participants. To enable authentication among the protocol participants, we assume that an existentially unforgeable signature scheme is available with all signing keys being chosen independently in a trusted initialization phase. The verification keys are assumed to be distributed in a trusted initialization phase, prior to the protocol execution.
2.1.1. Protocol Instances
We allow each protocol participant to execute polynomially many protocols instances in parallel. Each single instance may be understood as a process executed by participant . We will denote by () the instance of user , and the following seven variables are assigned to each instance:
- will indicate whether this instance is or has been used for a protocol run. The flag is set through a protocol message received by the corresponding instance due to a call to the oracle (see below);
- stores the state information needed during the protocol execution;
- indicates if the execution has terminated;
- denotes a session identifier (which may be public) which may be later use as identifier for the session key (in particular, the adversary is thus allowed to learn session identifiers);
- stores the user identities that aims at establishing a key with. This set includes himself;
- indicates that the protocol instance completed a protocol successfully. That is, whether the involved user accepted the session key or not;
- stores a distinguished null value in the beginning. After a session key is accepted by this session key replaces the null value.
We refer to a paper of Bellare et al. [14] for more details on the usage of these variables.
2.1.2. Communication Network
The network is considered to be fully asynchronous and under complete control of the adversary. Arbitrary point-to-point connections among users are available, but the adversary may delay, eavesdrop, insert, and delete messages at will.
2.1.3. Adversarial Capabilities
We restrict to adversaries running in probabilistic polynomial time, whose capabilities are made explicit through the four oracles listed below. These oracles formalize the interaction between and the protocol instances run by the users. For the description of the oracle, we denote by b a bit that is chosen uniformly at random.
- Send(Ui, si, M)
- This oracle sends a message M to instance and returns the message generated by this instance. In case the instance is previously unused and the message contains a set of user identities, the -flag is set, initialized with . initiates the protocol with the first message which is returned.
- Reveal(Ui, si)
- This outputs the computed key of the instance stored in .
- Test(Ui, si)
- If the corresponding session key is defined (i. e., and null) and instance is fresh (see Definition 4), can execute this oracle query at any time when being activated. Then, if the session key is returned, while if a uniformly chosen random session key is returned. An arbitrary number of queries is allowed for the adversary , but once the oracle returned a value for an instance , the same value will be returned for all instances partnered with (see Definition 3).
- Corrupt(Ui)
- This oracle models forward secrecy, as this query will output the secret signing key of user .
2.2. Goals of a Key Establishment Protocol: Correctness, Integrity, and Security
We assume that an instance always accepts the session key constructed at the end of a protocol run if no deviation from the protocol specification has occurred. The subsequent definition of correctness captures the protocol goal that, if the adversary is passive, all users involved in the same protocol session should come up with the same session key. By being passive, we mean that must not use the oracle, and may query the oracle for the purpose of executing honest protocol executions only.
Definition 1
(Correctness). A group key establishment protocol is correct , if in the presence of a passive adversary the following holds: for all with both and , we have null and .
Unlike correctness, the concept of integrity imposes no restrictions on the adversary’s behavior:
Definition 2
(Key Integrity). A correct group key establishment protocol fulfills key integrity, if all instances of users that have accepted with the same session identifier hold with overwhelming probability identical session keys and identical partner identifiers .
Finally, for defining security, we detail our interpretation of partnering and freshness:
Definition 3
(Partnering). Instances and are partnered if , , and .
The idea of freshness is to characterize those instances where the adversary does not know the secret session key for trivial reasons. In particular, note that after revealing a session key from instance , the session keys of all instances partnered with are known, too:
Definition 4
(Freshness). An instance is called fresh provided that none of the following condition holds:
- For somea querywas executed before a query of the formhas taken place where.
- The adversary queriedwithandbeing partnered.
Now the advantage of a probabilistic polynomial time adversary in attacking a key establishment protocol is the function
in the security parameter ℓ. Here, denotes the probability that queries only on fresh instances and correctly outputs the bit b used by the oracle while preserving the freshness of all instances queried to .
Definition 5.
We say that an authenticated group key establishment protocolis secure , if the following inequality holds for every probabilistic polynomial time adversary some negligible function in the security parameter ℓ:
As in [22], our security definition above implies forward secrecy. Specifically, our freshness definition (Definition 4) allows queries to an instances, for which the long term secret key has been revealed by a query (or is partnered with a instance that has be queried ) as long as the adversary has not asked a query to any of these instances (or their partners) after the query.
3. Building on a Group-Theoretic Assumption
As already indicated, we construct our group key establishment protocol in two steps: In Section 3.1 we describe a two-party solution, which subsequently is lifted to an n-party solution by means of the protocol compiler in [22].
3.1. A Two-Party Solution
On the cryptographic side, our two-party solution mainly builds on three technical tools:
- A non-interactive non-malleable commitment scheme , satisfying the following requirements:
- –
- It is perfectly binding in the sense that every commitment can be decommitted to at most one value.
- –
- It is non-malleable for multiple commitments. This means that an adversary who knows commitments to a polynomial sized set of values , will not be able to output commitments to a polynomial sized set of values related to in a meaningful way. It is well-known that in the CRS model such a commitment scheme can be implemented by means of any IND-CCA2 secure public key encryption scheme, for instance.
- A family of universal hash functions mapping triples consisting of two elements from G and a -value onto a superpolynomial sized set . A universal hash function will be selected by the CRS from this family.
- A collision-resistant pseudorandom function family (see Katz and Shin [28]). We assume to be indexed by and further denote by a publicly known value such that no ppt adversary can find two different indices such that . We further use another public value fulfilling the same requirement as for deriving the session key (this can also be included in the CRS—see [28] for more details).
Our protocol builds on [21], and for the security proof we have to assume that the underlying group G (respectively, the family of groups , indexed by the security parameter) satisfies a number of conditions. Besides assuming products and inverses of group elements to be computable by efficient (ppt) algorithms, we further assume G to have a ppt computable canonical representation of elements. The latter allows us to identify group elements with their canonical representation. Furthermore, as in [21], we need three algorithms to perform the computations occurring in a protocol execution:
- , the domain parameter generation algorithm, is a (stateless) ppt algorithm that, upon input of the security parameter , outputs a finite sequence S of elements in G. The subgroup of G spanned by S, , will be publicly known. Note that, for the special case of applying our framework to a DDH-assumption, S specifies a public generator of a cyclic group.
- , the automorphism group sampling algorithm, is a (stateless) ppt algorithm that, upon input of the security parameter and a sequence S output by , returns a description of an automorphism on the subgroup , so that both and can be efficiently evaluated. For example, for a cyclic group, could be given as an exponent, or for an inner automorphism the conjugating group element could be specified.
- , the subgroup sampling algorithm, is a (stateless) ppt that, upon input of the security parameter and a sequence S output by , returns a word representing an element . Intuitively, chooses a random , so that it is hard to recognize x if we know elements of x’s orbit under . Thus, our protocol requires an explicit representation of x in terms of the generators S.
With this notation, we can now define a decision problem, whose supposed difficulty will be essential for our security proof. As usual, with the notation we describe that algorithm upon receiving input i outputs o:
Definition 6
(Decision Automorphism Application). Suppose that we have fixed a quadruple . Then the decision automorphism application (DAA) assumption states that for all ppt algorithms the advantage function
is negligible.
Example 1
(Building on decision Diffie–Hellman). Let G be a finite cyclic group and a prime order subgroup with generator g of order q. If we let choose uniformly at random an exponent and uniformly at a random exponent , then the DAA problem just described can be recognized as polynomial-time equivalent to a decision Diffie–Hellman (DDH) problem:
- “DDH solution ⇒ DAA solution”:
- When facing, the DAA problem, we obtain as input a tuplewhere either, or y has been chosen uniformly at random from—independently of x and thes. Given a DDH oracle, we just query it withto see with non-negligible success probability which is the case.
- “DDH solution ⇒ DAA solution”:
- When facing the DDH problem, we obtain as input a tuple, where either, or y has been chosen uniformly at random from—independently of x and. Choosing another random, we can compute the inputneeded for a DAA attacker. Running a successful DAA attacker with this input, we immediately obtain the desired DDH attacker.
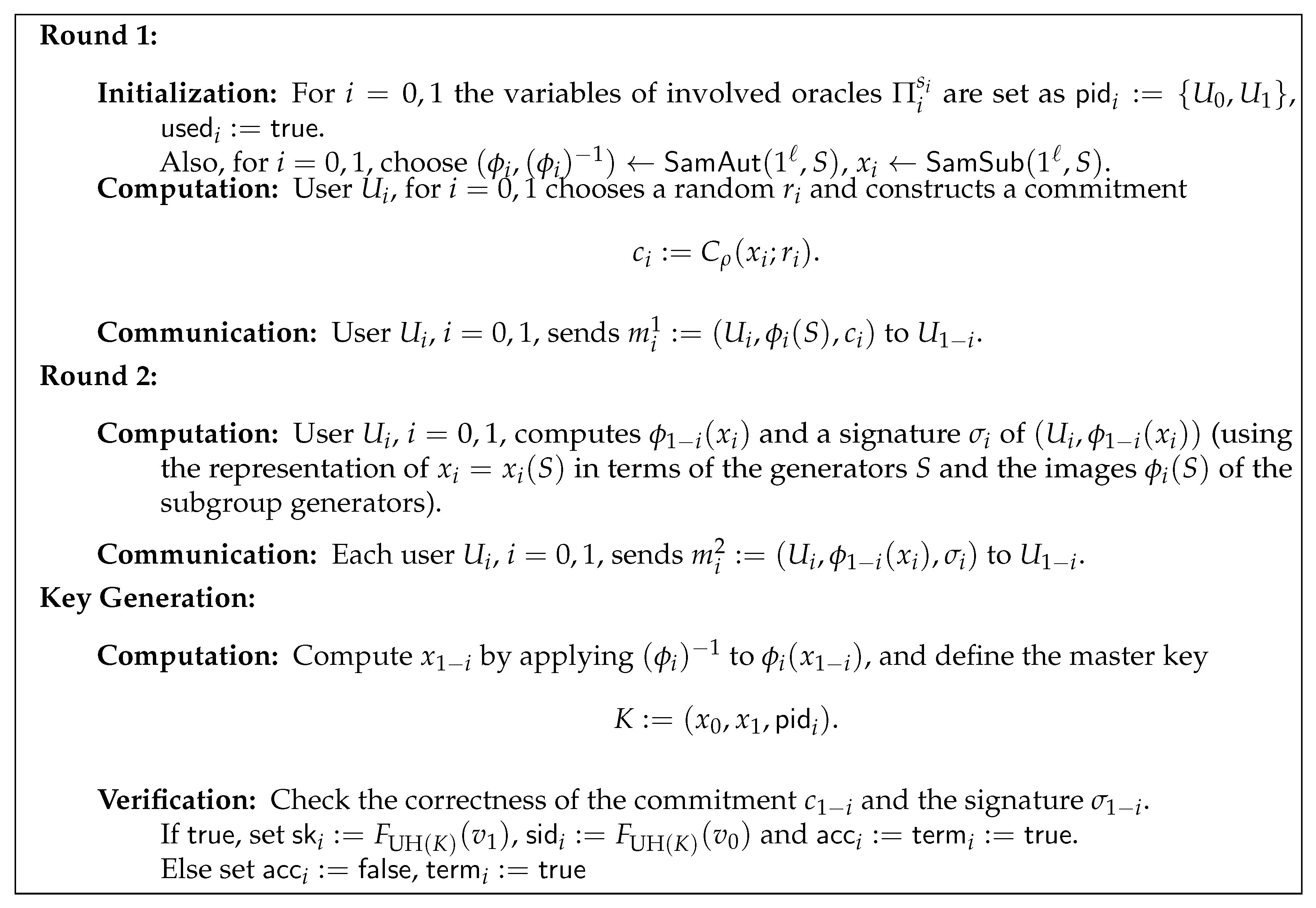
A two-party key establishment protocol building on the DAA assumption is presented in Figure 1. The figure describes the operations to be performed by instance of . For the sake of readability we name the users trying to establish a common key as and , and here, as in the sequel, we often omit making explicit the identifiers of the instances involved in the protocol execution and just write instead of , for instance. The common reference string is denoted by , and for a commitment to a value x involving random choices r we write . Finally, S denotes the subgroup generators which are to be fixed prior to the protocol execution by means of (and may also be included in the CRS ).
Figure 1.
A two-party key establishment protocol in the common reference string (CRS) model.
In the subsequent section we prove the following result:
Proposition 1
(Security of the Two-Party Protocol). Assume that for each ppt time algorithm , its advantage of achieving an existential forgery under the adaptive chosen-message attack for the underlying signature scheme, and its advantage of solving DAA, can be bounded by a negligible function (in ℓ). Then the protocol in Figure 1 is a correct and secure two-party key establishment protocol fulfilling key integrity.
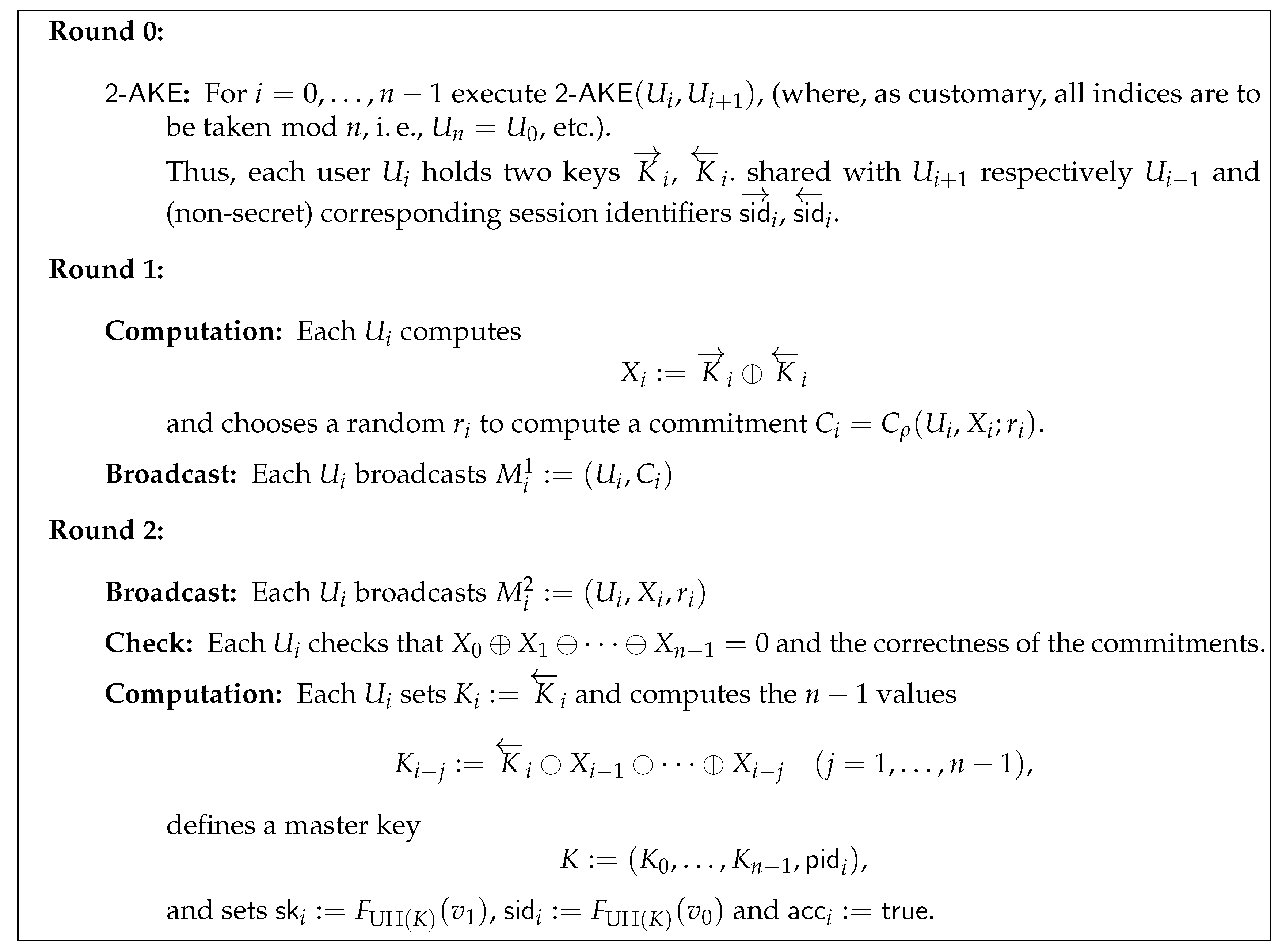
In Figure 2, we describe the group key establishment protocol obtained from a given two party group key establishment protocol via the compiler from [22]. We note here that given the result of Proposition 1, we can apply [22, Theorem 1] (which, as noted by Nam et al. in [29] is only valid if the underlying two party construction fulfills integrity) to obtain our desired security result:
Figure 2.
The protocol compiler from [22].
3.2. Security Analysis for the Two-Party Case: Proof of Proposition 1
Correctness and Integrity. Due to the collision-resistance of the family , all oracles that accept with identical session identifier use the same index value and therewith also obtain the same session key and have identical -values with overwhelming probability.
Security. Let and denote the (polynomially bounded) number of adversarial queries to the and oracle, respectively.
We consider a simulator simulating all oracles and instances for the adversary. The proof is thus set up following a sequence of experiments or games, where from game to game the simulator’s behavior deviates from the previous in a certain controlled way. We follow standard notation and we denote by the advantage of the adversary when confronted with Game i and by the success probability of winning in Game i. As usual, the security parameter will be denoted denoted by ℓ.
Game 0. All oracles are simulated as defined in the model. Thus, is exactly and is the probability of violating the security of our key exchange protocol.
Game 1. In this game, the simulator keeps a list with entries for every message M and corresponding signature he has produced and returned to the adversary in a Round 2 message following a query.
By we denote the event that queries the oracle with a message M containing a valid signature of an uncorrupted principal and with not being contained in the simulator’s list. If the event occurs, we abort the simulation and take the adversary for being successful in breaking the security of the protocol. Thus,
Lemma 1.
If the signature scheme used in the above protocol is existentially unforgeable under adaptive chosen-message attacks, thenis negligible:.
Proof.
Any ppt adversary provoking the event can be turned into an attacker against the underlying signature scheme by means of our simulator: The simulator obtains the public verification key and access to a signing oracle. In the initialization phase of the protocol, the simulator assigns the key uniformly at random to one of the at most users the adversary can involve. Whenever during the subsequent simulation a signature for this user has to be generated, the simulator queries the signing oracle.
If comes up with a message/signature pair that is not stored in the simulator’s list, the simulator returns this message as existential forgery. If does not come up with such a message, the simulator outputs ⊥. Having chosen the party uniformly at random, the simulator’s success probability for an existential forgery is at least , and we get . □
Thus, from Equation (1), we get
Game 2. Now the simulation of the oracle is modified, so that, on input of a fresh instance, it will always output an element selected uniformly at random in the key space. Thus,
Suppose that is able to distinguish between Game 2 and Game 1. We construct an attacker D, that breaks the DAA assumption and uses as a black-box. The attacker D will start by setting up the instances with key pairs for the signature scheme and receive a DAA-instance as a challenge. Further, D will choose an index uniformly at random and select two values chosen independently and uniformly at random subject to the condition . Then the adversary is started. D will simulate the model as in Game 1 except for the and instance activated by the adversary and the answers to the query. For the and instances activated by , the messages will be constructed from the DAA challenge. If these two instances do not end up in the same session, D aborts the simulation and starts anew. The same happens, if does not query his query to one of these two instances.
D will simulate the oracle as follows: The first queries of will be answered with the real session key, in the query, D will return the challenge, and from query on, D will always answer with a random element.
By a standard hybrid argument, D will win the challenge in of the cases where distinguished Game 1 and Game 2. Excluding the necessary aborts (namely, if the instances that were chosen were not those used in the query of ), we have:
4. Conclusions
Our discussion evidences the possibility of meaningfully integrating tools from group theory and cryptography. Unfortunately, so far we cannot provide a concrete non-abelian example, but a concrete instance of our protocol can be derived by means of the decision Diffie–Hellman assumption. We hope, however, that the modular approach taken above facilitates the design of group key establishment schemes building on group-theoretic tools and fertilizes the exchange of ideas between group theory and cryptography.
Author Contributions
All authors contributed equally to this paper, and were cooperatively involved in conceptualization, investigation, formal analysis and writing. All authors have read and agreed to the published version of the manuscript.
Funding
This research was sponsored in part by the NATO Science for Peace and Security Programme under grant G5448 and in part by Spanish MINECO under grant MTM2016-77213-R.
Acknowledgments
This paper was written in grateful memory of our advisor and friend Thomas Beth.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Anshel, I.; Anshel, M.; Goldfeld, D. An Algebraic Method for Public-Key Cryptography. Math. Res. Lett. 1999, 6, 287–291. [Google Scholar] [CrossRef]
- Ko, K.H.; Lee, S.J.; Cheon, J.H.; Han, J.W.; Kang, J.S.; Park, C. New Public-Key Cryptosystem Using Braid Groups. In Proceedings of the Advances in Cryptology—CRYPTO 2000, Santa Barbara, CA, USA, 20–24 August 2000; pp. 166–183. [Google Scholar]
- Anshel, I.; Anshel, M.; Fisher, B.; Goldfeld, D. New Key Agreement Protocols in Braid Group Cryptography. In Proceedings of the Topics in Cryptology—CT-RSA 2001, San Francisco, CA, USA, 8–12 April 2001; pp. 13–27. [Google Scholar]
- Grigoriev, D.; Ponomarenko, I. Constructions in public-key cryptography over matrix groups. In Contemporary Mathematics: Algebraic Methods in Cryptography; American Mathematical Society: Providence, RI, USA, 2006; Volume 418, pp. 103–119. [Google Scholar]
- Lee, H.K.; Lee, H.S.; Lee, Y.R. An Authenticated Group Key Agreement Protocol on Braid groups. Cryptology ePrint Archive: Report 2003/018. 2003. Available online: http://eprint.iacr.org/2003/018 (accessed on 1 December 2019).
- Shpilrain, V.; Ushakov, A. Thompson’s Group and Public Key Cryptography. In Proceedings of the ACNS 2005—Third International Conference on Applied Cryptography and Network Security, New York, NY, USA, 7–10 June 2005; Volume 3531, pp. 151–163. [Google Scholar]
- Shpilrain, V.; Zapata, G. Combinatorial group theory and public key cryptography. Appl. Algebra Eng. Commun. Comput. 2006, 17, 291–302. [Google Scholar] [CrossRef][Green Version]
- Shpilrain, V.; Ushakov, A. A new key exchange protocol based on the decomposition problem. In Contemporary Mathematics: Algebraic Methods in Cryptography; American Mathematical Society: Providence, RI, USA, 2006; Volume 418, pp. 161–167. [Google Scholar]
- Anshel, I.; Anshel, M.; Goldfeld, D.; Lemieux, S. Key agreement, the Algebraic EraserTM, and lightweight cryptography. In Contemporary Mathematics: Algebraic Methods in Cryptography; American Mathematical Society: Providence, RI, USA, 2006; Volume 418, pp. 1–34. [Google Scholar] [CrossRef]
- Anshel, I.; Atkins, D.; Goldfeld, D.; Gunnells, P.E. Ironwood Meta Key Agreement and Authentication Protocol. arXiv 2017, arXiv:1702.02450. [Google Scholar]
- Bellare, M.; Rogaway, P. Entitiy Authentication and Key Distribution. In Proceedings of the CRYPTO 1993—13th Annual International Cryptology Conference on Advances in Cryptology, Santa Barbara, CA, USA, 22–26 August 1993; Volume 773, pp. 232–249. [Google Scholar]
- Bellare, M.; Canetti, R.; Krawczyk, H. A Modular Approach to the Design and Analysis of Authentication and Key Exchange Protocols. In Proceedings of the 30th Annual ACM Symposium on Theory of Computing STOC, Dallas, TX, USA, 24–26 May 1998; pp. 319–428. [Google Scholar]
- Shoup, V. On Formal Models for Secure Key Exchange (Version 4). Revision of IBM Research Report RZ 3120 (April 1999). 1999. Available online: http://www.shoup.net/papers/skey.pdf (accessed on 1 December 2019).
- Bellare, M.; Pointcheval, D.; Rogaway, P. Authenticated Key Exchange Secure Against Dictionary Attacks. In Proceedings of the EUROCRYPT 2000—Advances in Cryptology, Bruges, Belgium, 14–18 May 2000; Volume 1807, pp. 139–155. [Google Scholar]
- Bresson, E.; Chevassut, O.; Pointcheval, D.; Quisquater, J.J. Provably Authenticated Group Diffie–Hellman Key Exchange. In Proceedings of the 8th ACM Conference on Computer and Communications Security; Samarati, P., Ed.; ACM Press: New York, NY, USA, 2001; pp. 255–264. [Google Scholar]
- Canetti, R.; Krawczyk, H. Analysis of Key-Exchange Protocols and Their Use for Building Secure Channels. In Advances in Cryptology—EUROCRYPT 2001; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2045, pp. 453–474. [Google Scholar]
- Ben-Zvi, A.; Blackburn, S.R.; Tsaban, B. A Practical Cryptanalysis of the Algebraic Eraser. In Advances in Cryptology—CRYPTO 2016 Proceedings, Part I; Lecture Notes in Computer Science; Robshaw, M., Katz, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2016; Volume 9814, pp. 179–189. [Google Scholar]
- Cramer, R.; Shoup, V. Universal Hash Proofs and a Paradigm for Adaptive Chosen Ciphertext Secure Public-Key Encryption. In Advances in Cryptology—EUROCRYPT 2002; Lecture Notes in Computer Science; Knudsen, L., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2332, pp. 45–64. [Google Scholar]
- González Vasco, M.I.; Martínez, C.; Steinwandt, R.; Villar, J.L. A new Cramer-Shoup like methodology for group based provably secure schemes. In Proceedings of the 2nd Theory of Cryptography Conference (TCC 2005); Lecture Notes in Computer Science; Kilian, J., Ed.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3378, pp. 495–509. [Google Scholar]
- Catalano, D.; Pointcheval, D.; Pornin, T. IPAKE: Isomorphisms for Password-based Authenticated Key Exchange. In Advances in Cryptology—CRYPTO 2004; Lecture Notes in Computer Science; Franklin, M.K., Ed.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3152, pp. 477–493. [Google Scholar]
- Bohli, J.M.; Glas, B.; Steinwandt, R. Towards Provably Secure Group Key Agreement Building on Group Theory. In Proceedings of VietCrypt 2006; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4341, pp. 322–336. [Google Scholar]
- Abdalla, M.; Bohli, J.; González Vasco, M.I.; Steinwandt, R. (Password) Authenticated Key Establishment: From 2-Party to Group. In Proceedings of the 4th Theory of Cryptography Conference TCC 2007; Lecture Notes in Computer Science; Vadhan, S.P., Ed.; Springer: Berlin/Heidelberg, Germany, 2007; Volume 4392, pp. 499–514. [Google Scholar]
- Burmester, M.; Desmedt, Y. A Secure and Efficient Conference Key Distribution System. In Advances in Cryptology—EUROCRYPT’94; Lecture Notes in Computer Science; Santis, A.D., Ed.; Springer: Berlin/Heidelberg, Germany, 1995; Volume 950, pp. 275–286. [Google Scholar]
- Gennaro, R.; Lindell, Y. A Framework for Password-Based Authenticated Key Exchange. Cryptology ePrint Archive: Report 2003/032. 2003. Available online: http://eprint.iacr.org/2003/032 (accessed on 1 December 2019).
- Gennaro, R.; Lindell, Y. A Framework for Password-Based Authenticated Key Exchange (Extended Abstract). In Advances in Cryptology—EUROCRYPT 2003; Lecture Notes in Computer Science; Biham, E., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2656, pp. 524–543. [Google Scholar]
- Bohli, J.M.; González Vasco, M.I.; Steinwandt, R. Secure group key establishment revisited. Int. J. Inf. Secur. 2007, 6, 243–254. [Google Scholar] [CrossRef]
- Bohli, J.M.; González Vasco, M.I.; Steinwandt, R. Password-authenticated group key establishment from smooth projective hash functions. Int. J. Appl. Math. Comput. Sci. 2019, 29, 797–815. Available online: http://eprint.iacr.org/2006/214 (accessed on 1 December 2019). [CrossRef]
- Katz, J.; Shin, J.S. Modeling insider attacks on group key-exchange protocols. In Proceedings of the 12th ACM Conference on Computer and Communications Security (CCS 2005); Atluri, V., Meadows, C.A., Juels, A., Eds.; ACM: New York, NY, USA, 2005; pp. 180–189. Available online: http://eprint.iacr.org/2005/163 (accessed on 1 December 2019).
- Nam, J.; Paik, J.; Won, D. A security weakness in Abdalla et al.’s generic construction of a group key exchange protocol. Inf. Sci. 2011, 181, 234–238. [Google Scholar] [CrossRef]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).