Recent Advances in Digital Multimedia Tampering Detection for Forensics Analysis
Abstract
1. Introduction
2. Taxonomy
2.1. Digital Multimedia Forensics
2.2. Multimedia Tampering
2.3. Tampering Tttacks
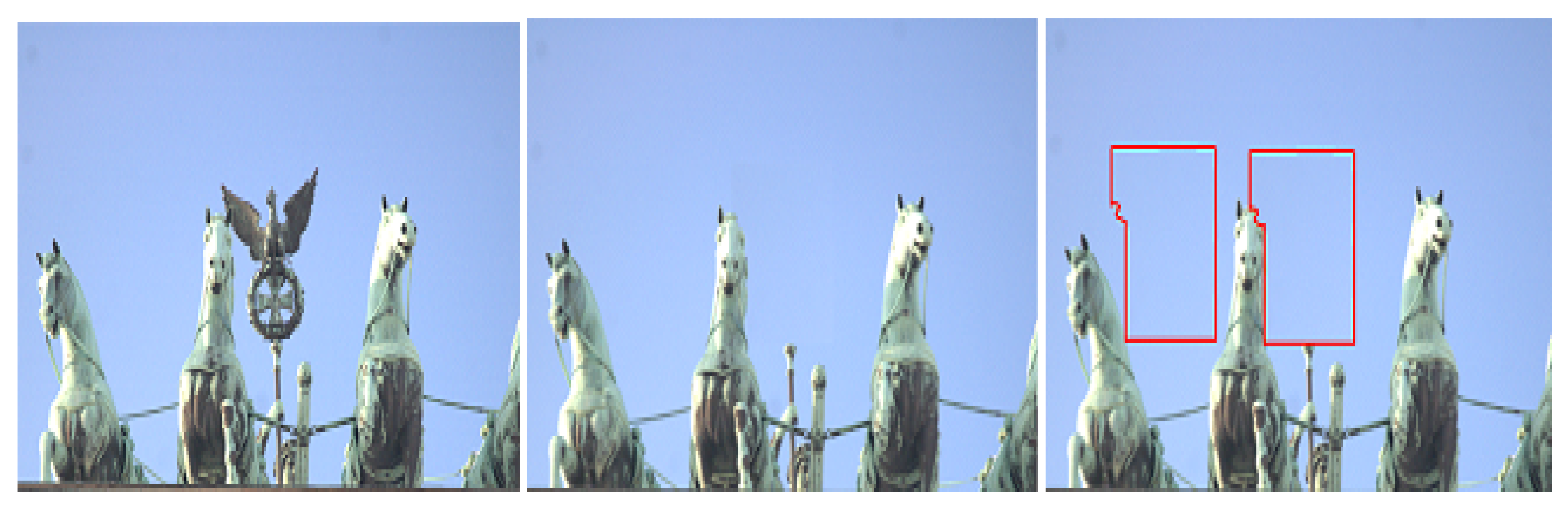
- Copy-move (cloning): This is one of the commonly applied attacks given its simplicity and effectiveness. It concerns all techniques that manipulate an image by copying certain region(s) and pasting them into another place on the same image (or video). As a result, some details will be hidden as well as others being duplicated in the same image.
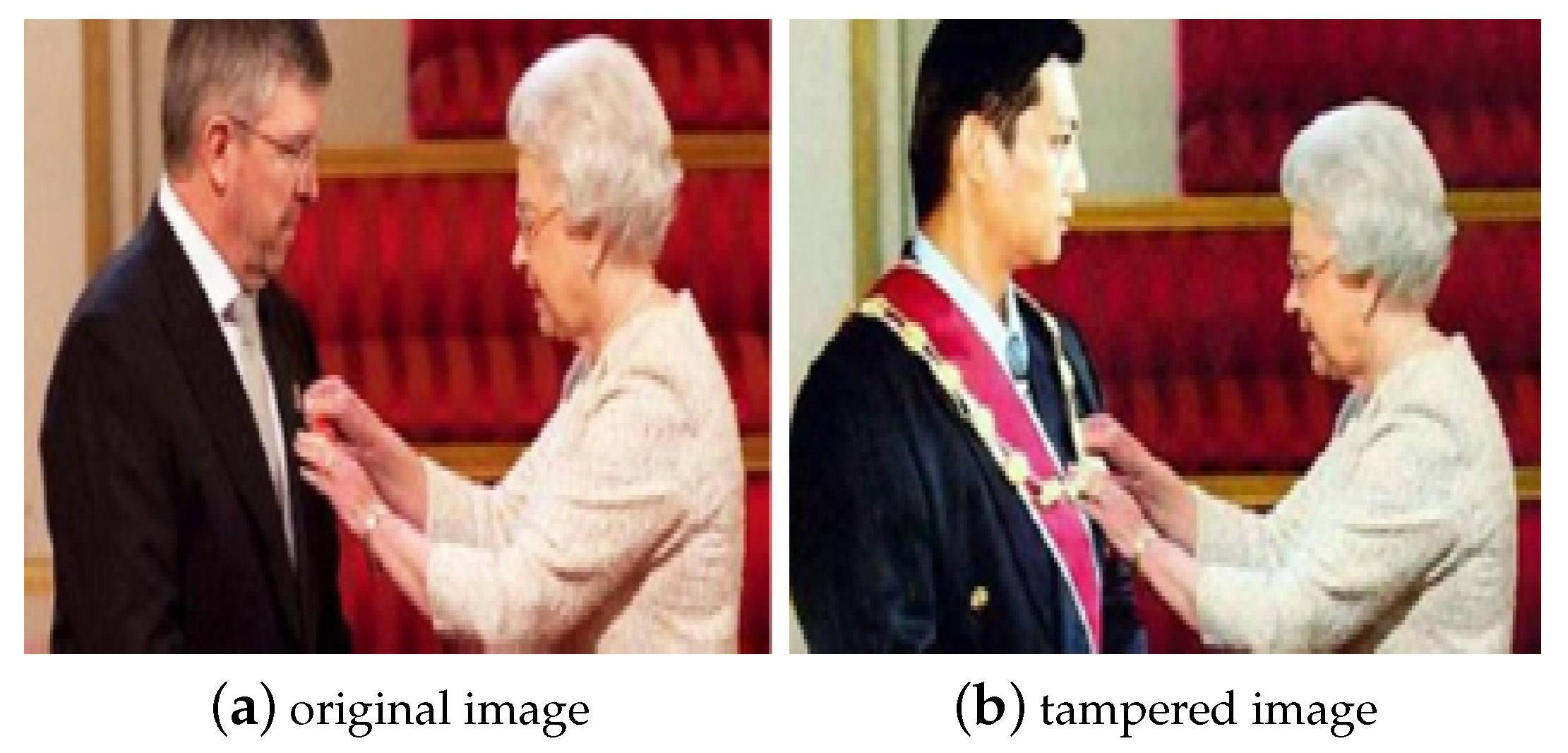
- Splicing: This involves replacing some image (or video) objects from one or more different images (or videos) into another image (or video) in order to generate a composite image (forged). The inserted parts disturb the pattern of the new image (or video), thus, detecting this kind of tampering deals with exploiting patterns and any presence of statistical correlation distortions. It is one of the most aggressive and frequently used attacks.
- Re-sampling: This is defined as the process of applying some geometric transformations (like scaling, rotation or skewing operations) or any interpolation algorithms in order to create a malicious transformed image or a portion of image and therefore a visually convincing forgery by, for example, increasing or decreasing the image size.
- Retouching: This attack is used in order to enhance the visual quality of the image, for instance, by adding onto brightness. It is usually applied as a post-processing operation of image tampering. In this case, the original image (or video) will not be modified significantly, but only a few reductions in certain properties and characteristics of the image.
- Inpainting: This is the process of drawing some missing content over the image or video using, for example, the “brush” software tool in order to repair damage. As a result, this operation can alter the original image and the faked part takes distinct features (noise, lighting, luminosity and compression rate) from the rest of the parts in the same image or frame-video. It is noted that it is possible to detect this type of attack with the same techniques for copy-move attack detection.
- Other tampering attacks: There are other types of operations, such as filtering, cropping or histogram adjustments, which are often applied without malevolent intention.
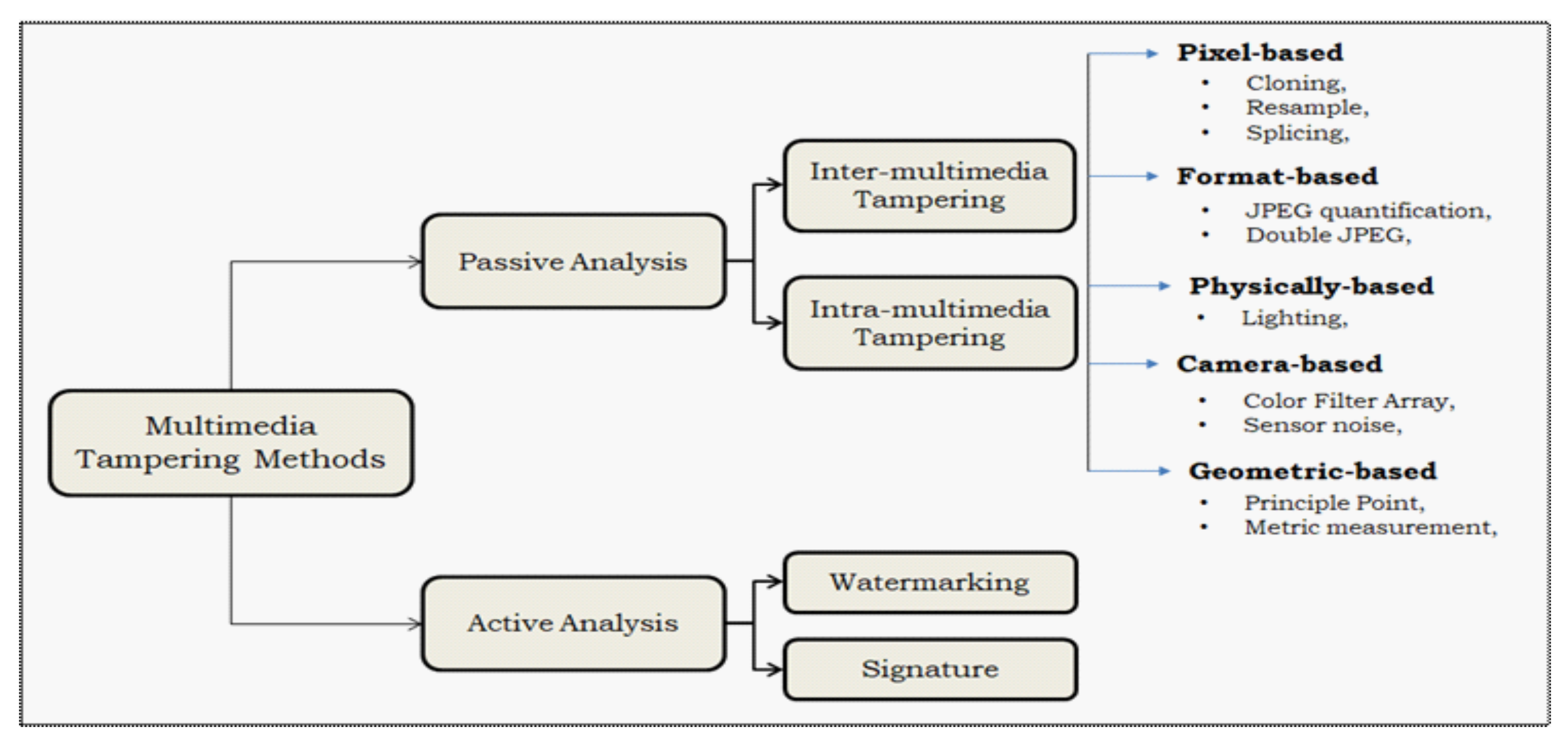
2.4. Active Tampering Detection
2.5. Passive Tampering Detection
- Pixel-based methods: emphasize the use of pixel properties and the correlation between pixels (in spatial or transformed domain) for detecting anomalies (such as copy-move or splicing).
- Camera-based methods: they use several evidences such as the camera’s model, artifacts and other features like camera sensors, lens, or some postprocessing steps including gamma correction, quantization, and filtering. These features help in detecting tampering.
- Format-based methods: exploit especially statistical correlations introduced by lossy compression scheme for such formats (like JPEG format) which are considered important clues for the presence of some manipulations. These techniques allow the detection of tampering in compressed media.
- Geometry-based methods: exploit the relative position of the object with respect to the camera as indication for further forgery detection process.
- Physics-based methods: take advantages of the inconsistencies between tampering scenes and physical objects in terms of differences in illumination, light, camera, and object size. These evidences are used to detect anomalies and forgeries.
2.6. Intra- and Inter-Multimedia Tampering
3. Digital Media Forensics Detection: Overview
3.1. Copy-Move Image Tampering Detection
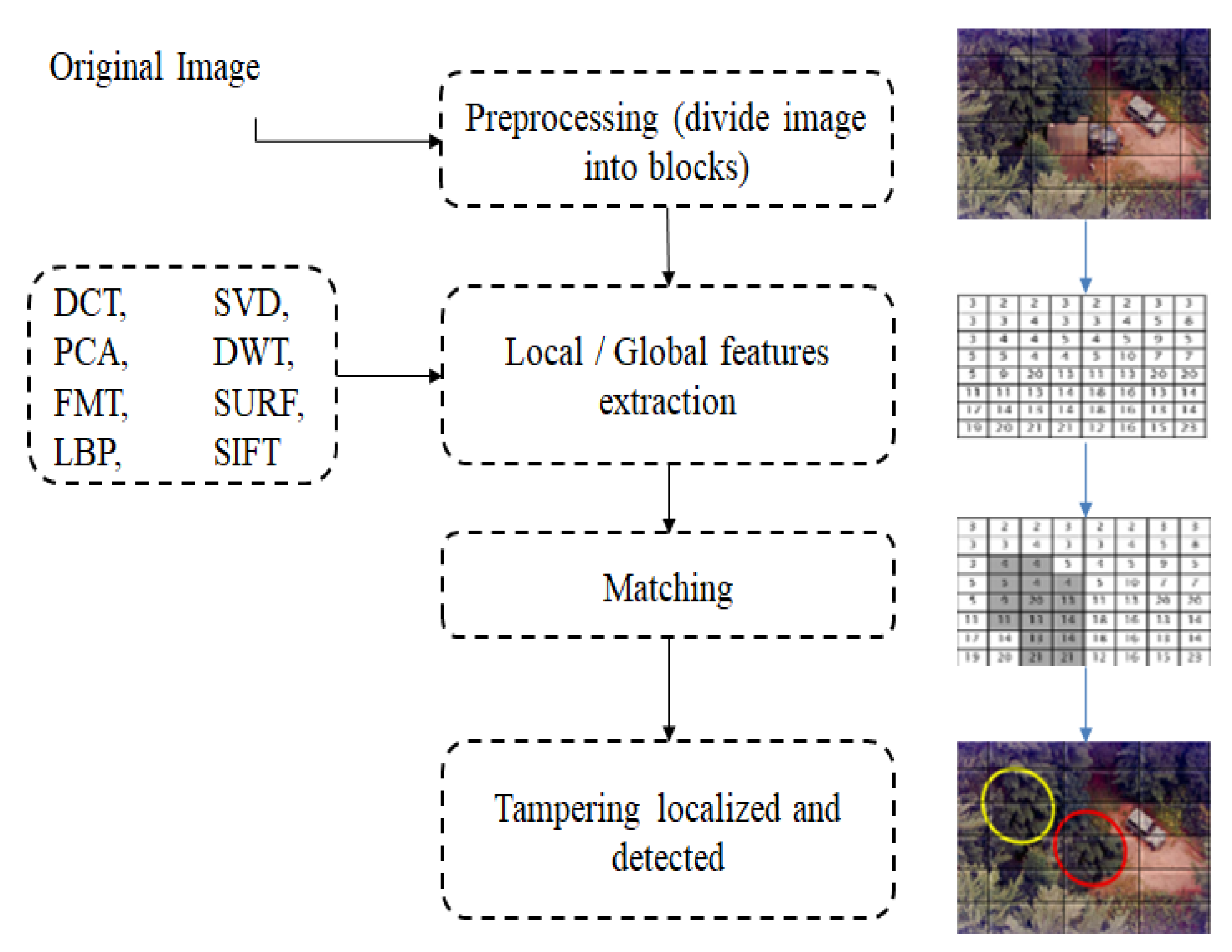
3.1.1. Block-Based Detection Techniques
3.1.2. Keypoints-Based Detection Techniques
3.2. Splicing Tampering Detection
3.3. Toward Hybrid Methods
- As image tampering detection is a hard problem, the computational time is relatively high for block-based techniques, given that all pixels or extracted features must be examined per block. Sometimes, large-scaling distortion is undetectable. In contrast, the feature-based techniques have less computational complexity. Thus, solving the trade-off speed–accuracy is now a challenging problem.
- Determining the best nd optimal feature extraction algorithm is not easy and final results are highly dependent on the used technique, which can be a keypoint-based or block-based technique.
- In many cases, the existing methods in the literature fail to detect particularly small duplicate regions (caused by copy-move operation), and therefore the accuracy will be very low.
- Some methods fail to locate multiple duplicated regions.
- In general, keypoint-based techniques cannot address the smoothing tampering.
- Sometimes, block-based methods are more accurate than keypoint-based ones in identifying the shapes of duplicated regions.
- Both the keypoint features and block-based matching have difficulties in accurately detecting the smoothed shape region.
- Most copy-move detection methods are unable to detect different types of attack at the same time (e.g., compression, scaling, and noise addition, copy-move and duplication).
- It is too difficult that just one single image tampering detection method or algorithm can reveal entirely forged images. Thus, involving several methodologies and abilities is highly recommended.
- Some tampering detectors may be misled by counter-intrusive processes created by counterfeiting.
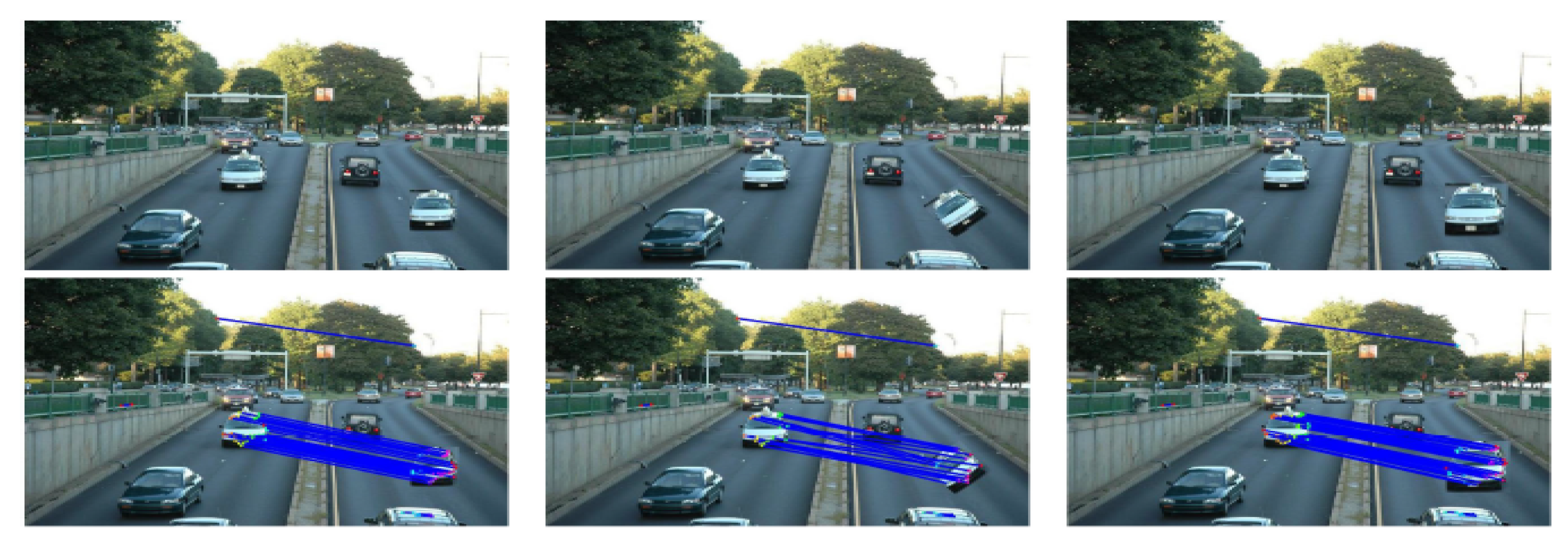
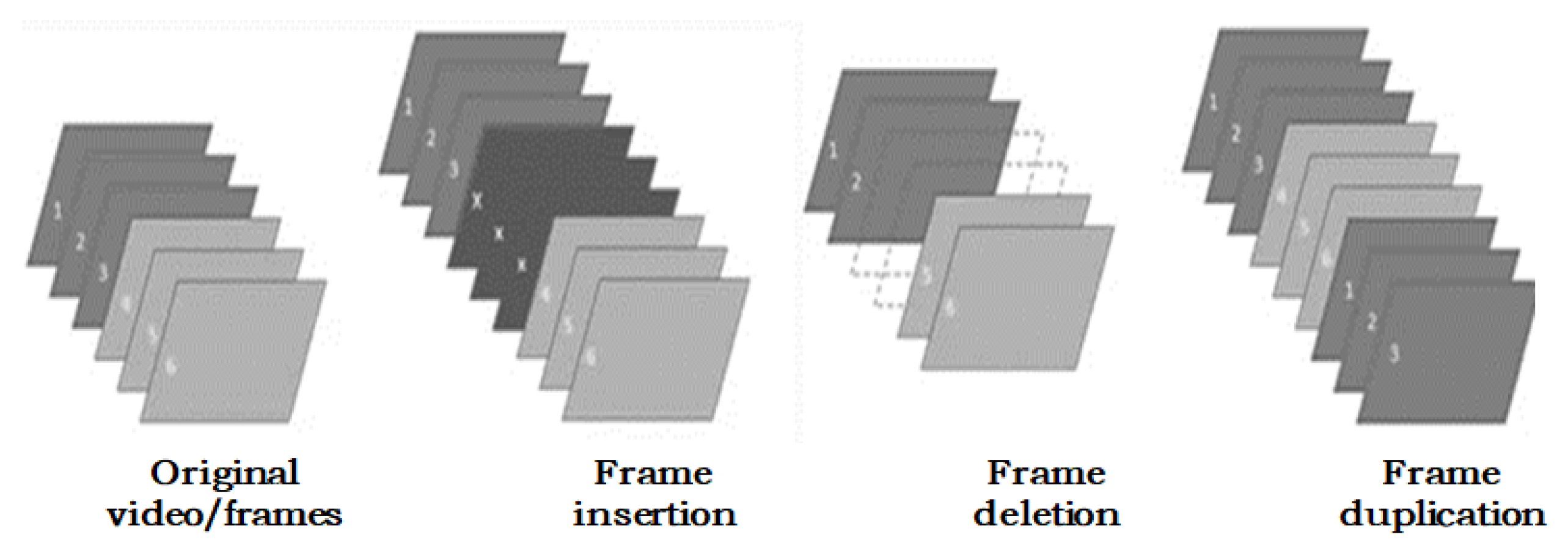
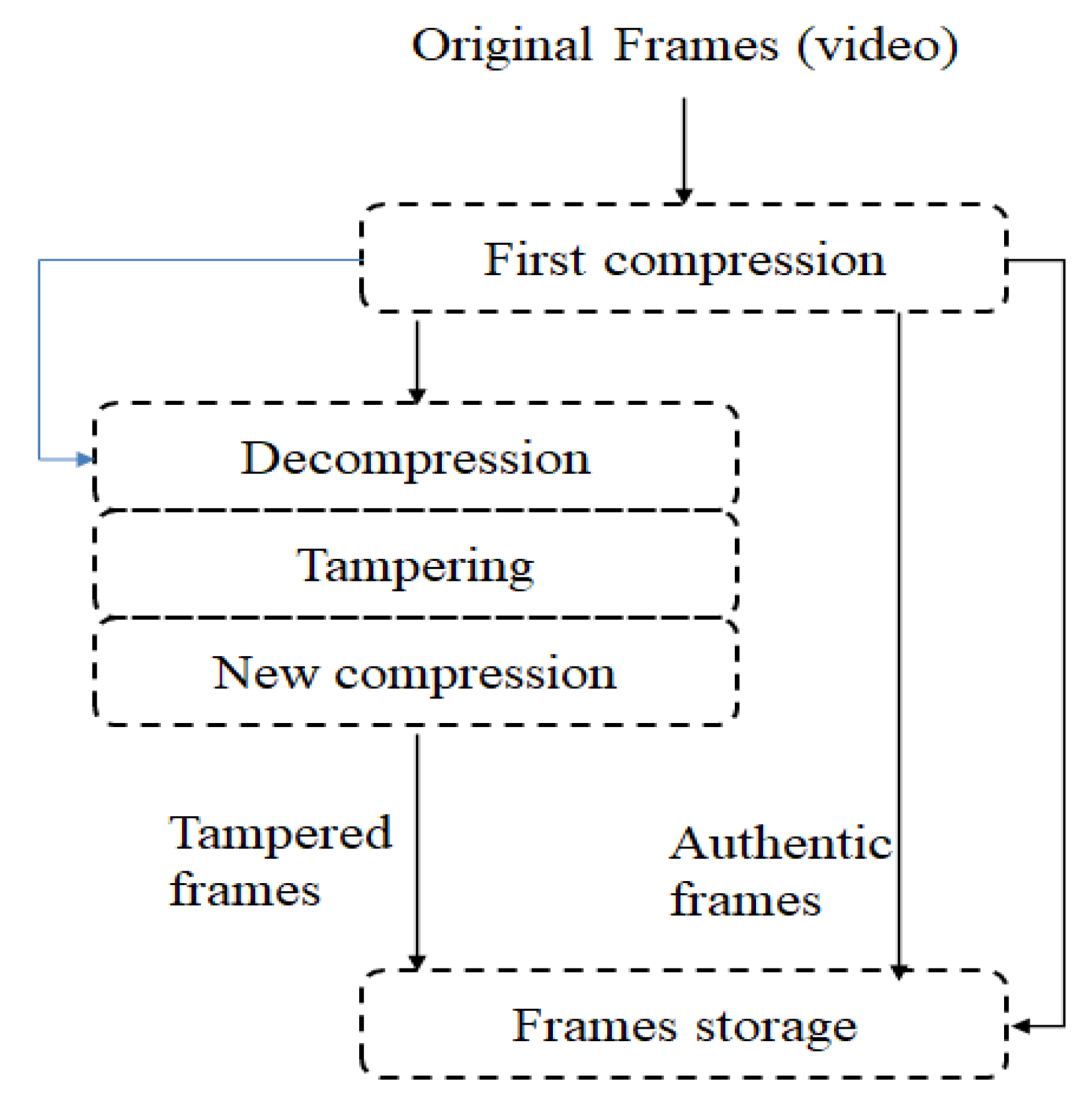
3.4. Video Tampering Detection
4. Forensics Multimedia Datasets
4.1. Datasets
- MICC-F220 dataset [15]: It is collected by 220 images: 110 are original images and 110 tampered. They represent different scenes like animals, plants, and artifacts.
- MICC-F2000 dataset [15]: This publicly accessible database contains in total 2000 images, where 1300 are authentic and the other 700 are tampered with.
- CoMoFoD dataset [137]: It is composed of 260 image sets, where each set includes the original image, a colored/binary mask and the tampered image. Several post-processing activities have been performed on this dataset. Overall, 200 original images with resolution (512 × 512) are post-processed to generate a total number of 10,400 images. The remaining 60 original images have a large resolution of (3000 × 2000) and are post-processed as well, to have a total number of 3120 images.
- Wild web-tampered image dataset [138]: It is a very large collection of tampered images from the web and social media sources, accompanied by a ground truth annotation masking the representation of the location of the forgery.
- CASIA-v2.0 dataset [139]: It is an available dataset for tampered image detection evaluation. It is composed of 7491 color authentic images and 5123 manipulated ones (spliced and/or blurred) of different large sizes, from 240 × 160 to 900 × 600. Certain original images are acquired from the well-known Corel dataset.
- CISD dataset [140]: It is a public collection for splicing detection with 1845 images provided by the lab DVMM at Columbia University. There are 933 authenticated images and the other 912 are faked blocks of size 128 × 128 pixels. Two fundamental operations are performed to create spliced images: crop-and-paste operations from the same source image or two different images.
- Multimedia forensics challenge (MFC) datasets [141]: It is a very large collection of digital media (images and videos) forensics challenge (MFC) evaluations. There are about 176,000 original images and 11,000 original videos, where more than 100,000 are manipulated images and 4000 are manipulated videos.
- Realistic tampering dataset [142]: This dataset contains 220 color authentic and 220 realistic forged images with size of 1920 × 1080 pixels. Images are captured by different cameras (Sony, Canon, Nikon D7000, Nikon D90).
- FaceForensics++ dataset [143]: It is a large scale publicly tampered video dataset composed of 1000 tampered face videos and 1000 authentic videos. Authentic videos were extracted from YouTube and social media. Each manipulated source video has an original counterpart.
- VTD dataset [144]: This video tampering dataset (VTD) is composed of 26 tampered videos and 26 original counterparts which are downloaded from YouTube. The forged video files are obtained as follows: 10 sequences based on splicing attacks, 6 based on an inter-frame forgery and 10 based on copy–move attacks. Each sequence contains between 420 and 480 frames.
4.2. Evaluation Metrics
- True positive rate (TPR) = =
- False positive rate (FPR) = =
- True Negative Rate (specificity) = .
- False Negative Rate (FNR) = .
- Accuracy = .
- MCC=.
- F1= .
5. Discussions and Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Radcliffe, D.; Abuhmaid, H. Social Media in the Middle East: 2019. 2020; in press. [Google Scholar]
- Available online: https://www.techradar.com/news/twitter-announces-expansion-to-mena-video-content-with-over-16-partnerships (accessed on 4 April 2020).
- Available online: https://www.statista.com/statistics/315405/snapchat-user-region-distribution/ (accessed on 4 April 2020).
- Available online: http://www.mideastmedia.org/survey/2019/chapter/social-media/ (accessed on 4 April 2020).
- Available online: https://www.thinkwithgoogle.com/intl/en-145/getting-know-youtubes-biggest-middle-eastern-audience-millennials/ (accessed on 4 April 2020).
- Radcliffe, D.; Abuhmaid, H. Social Media in the Middle East: 2019 in Review. 12 January 2020. Available online: https://ssrn.com/abstract=3517916 (accessed on 4 April 2020). [CrossRef]
- Available online: https://www.pewresearch.org/internet/2019/05/13/publics-in-emerging-economies-worry-social-media-sow-division-even-as-they-offer-new-chances-for-political-engagement/ (accessed on 4 April 2020).
- Fridrich, A.J.; Soukal, B.D.; Lukáš, A.J. Detection of copy-move forgery in digital images. In Proceedings of the Digital Forensic Research Workshop, Cleveland, OH, USA, 6–8 August 2003. [Google Scholar]
- Celik, M.U.; Sharma, G.; Saber, E.; Tekalp, A.M. Hierarchical watermarking for secure image authentication with localization. IEEE Trans. Image Process. 2002, 11, 585–595. [Google Scholar] [CrossRef] [PubMed]
- Meerwald, P.; Uhl, A. Survey of wavelet-domain watermarking algorithms. In Security and Watermarking of Multimedia Contents III; International Society for Optics and Photonics: Bellingham, WA, USA, 2001; pp. 505–516. [Google Scholar]
- Hartung, F.; Kutter, M. Multimedia watermarking techniques. Proc. IEEE 1999, 87, 1079–1107. [Google Scholar] [CrossRef]
- Farid, H. Image forgery detection. IEEE Signal Process. Mag. 2009, 26, 16–25. [Google Scholar] [CrossRef]
- Lin, H.J.; Wang, C.W.; Kao, Y.T. Fast copy-move forgery detection. WSEAS Trans. Signal Process. 2009, 5, 188–197. [Google Scholar]
- Huang, H.; Guo, W.; Zhang, Y. Detection of Copy-Move Forgery in Digital Images Using SIFT Algorithm. In Proceedings of the PACIIA IEEE Pacific-Asia Workshop on Computational Intelligence and Industrial Application, Wuhan, China, 19–20 December 2008; pp. 272–276. [Google Scholar]
- Amerini, I.; Ballan, L.; Caldelli, R.; Bimbo, A.D.; Serra, G. A SIFT-Based Forensic Method for Copy-Move Attack Detection and Transformation Recovery. IEEE Trans. Inf. Forensics Secur. 2011, 6, 1099–1110. [Google Scholar] [CrossRef]
- Popescu, A.C.; Farid, H. Exposing digital forgeries by detecting duplicated image regions. In Dartmouth College, Computer Science, Technology Report, TR2004-515; Dartmouth College: Hanover, NH, USA, 2004; pp. 1–11. [Google Scholar]
- Mahdian, B.; Saic, S. Detection of copy–move forgery using a method based on blur moment invariants. Forensic Sci. Int. 2007, 171, 180–189. [Google Scholar] [CrossRef]
- Farid, H.; Lyu, S. Higher-order Wavelet Statistics and their Application to Digital Forensics. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition, CVPR, Madison, WI, USA, 6–22 June 2003; p. 94. [Google Scholar]
- Pevný, T.; Fridrich, J.J. Detection of Double-Compression in JPEG Images for Applications in Steganography. IEEE Trans. Inf. Forensics Secur. 2008, 3, 247–258. [Google Scholar] [CrossRef]
- Johnson, M.K.; Farid, H. Exposing Digital Forgeries in Complex Lighting Environments. IEEE Trans. Inf. Forensics Secur. 2007, 2, 450–461. [Google Scholar] [CrossRef]
- Qu, Z.; Luo, W.; Huang, J. A convolutive mixing model for shifted double JPEG compression with application to passive image authentication. In Proceedings of the IEEE International Conference on Acoustics, Speech, and Signal Processing, ICASSP, Las Vegas, NV, USA, 31 March–4 April 2008; pp. 1661–1664. [Google Scholar]
- Liu, Y.; Huang, T. Exposing video inter-frame forgery by Zernike opponent chromaticity moments and coarseness analysis. Multimed. Syst. 2017, 23, 223–238. [Google Scholar] [CrossRef]
- Fadl, S.M.; Han, Q.; Li, Q. Authentication of surveillance videos: Detecting frame duplication based on residual frame. J. Forensic Sci. 2018, 63, 1099–1109. [Google Scholar] [CrossRef] [PubMed]
- Thakur, R.; Rohilla, R. Recent advances in digital image manipulation detection techniques: A brief review. Forensic Sci. Int. 2020, 312, 110311. [Google Scholar] [CrossRef]
- Teerakanok, S.; Uehara, T. Copy-Move Forgery Detection: A State-of-the-Art Technical Review and Analysis. IEEE Access 2019, 7, 40550–40568. [Google Scholar] [CrossRef]
- Lin, X.; Li, J.H.; Wang, S.L.; Liew, A.W.C.; Cheng, F.; Huang, X.S. Recent Advances in Passive Digital Image Security Forensics: A Brief Review. Engineering 2018, 4, 29–39. [Google Scholar] [CrossRef]
- Meena, K.B.; Tyagi, V. Image forgery detection: Survey and future directions. In Data, Engineering and Applications; Springer: Berlin/Heidelberg, Germany, 2019; pp. 163–194. [Google Scholar]
- Warif, N.B.A.; Wahab, A.W.A.; Idris, M.Y.I.; Ramli, R.; Salleh, R.; Shamshirband, S.; Choo, K.R. Copy-move forgery detection: Survey, challenges and future directions. J. Netw. Comput. Appl. 2016, 75, 259–278. [Google Scholar] [CrossRef]
- Christlein, V.; Riess, C.; Jordan, J.; Riess, C.; Angelopoulou, E. An Evaluation of Popular Copy-Move Forgery Detection Approaches. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1841–1854. [Google Scholar] [CrossRef]
- Khan, S.; Khan, K.; Ali, F.; Kwak, K. Forgery Detection and Localization of Modifications at the Pixel Level. Symmetry 2020, 12, 137. [Google Scholar] [CrossRef]
- Li, J.; Li, X.; Yang, B.; Sun, X. Segmentation-Based Image Copy-Move Forgery Detection Scheme. IEEE Trans. Inf. Forensics Secur. 2015, 10, 507–518. [Google Scholar]
- Alahmadi, A.A.; Hussain, M.; Aboalsamh, H.; Muhammad, G.; Bebis, G.; Mathkour, H. Passive detection of image forgery using DCT and local binary pattern. Signal Image Video Process. 2017, 11, 81–88. [Google Scholar] [CrossRef]
- Luo, W.; Huang, J.; Qiu, G. Robust Detection of Region-Duplication Forgery in Digital Image. In Proceedings of the 18th International Conference on Pattern Recognition (ICPR 2006), Hong Kong, China, 20–24 August 2006; pp. 746–749. [Google Scholar]
- Wang, X.; Liu, Y.; Xu, H.; Wang, P.; Yang, H. Robust copy-move forgery detection using quaternion exponent moments. Pattern Anal. Appl. 2018, 21, 451–467. [Google Scholar] [CrossRef]
- Prakash, C.S.; Kumar, A.; Maheshkar, S.; Maheshkar, V. An integrated method of copy-move and splicing for image forgery detection. Multimed. Tools Appl. 2018, 77, 26939–26963. [Google Scholar] [CrossRef]
- Zhong, J.; Gan, Y. Detection of copy–move forgery using discrete analytical Fourier–Mellin transform. Nonlinear Dyn. 2016, 84, 189–202. [Google Scholar] [CrossRef]
- Li, W.; Yu, N. Rotation robust detection of copy-move forgery. In Proceedings of the International Conference on Image Processing, ICIP 2010, Hong Kong, China, 26–29 September 2010; pp. 2113–2116. [Google Scholar]
- Zhao, J.; Guo, J. Passive forensics for copy-move image forgery using a method based on DCT and SVD. Forensic Sci. Int. 2013, 233, 158–166. [Google Scholar] [CrossRef]
- Cozzolino, D.; Poggi, G.; Verdoliva, L. Efficient Dense-Field Copy-Move Forgery Detection. IEEE Trans. Inf. Forensics Secur. 2015, 10, 2284–2297. [Google Scholar] [CrossRef]
- Ryu, S.; Kirchner, M.; Lee, M.; Lee, H. Rotation Invariant Localization of Duplicated Image Regions Based on Zernike Moments. IEEE Trans. Inf. Forensics Secur. 2013, 8, 1355–1370. [Google Scholar]
- Bashar, M.; Noda, K.; Ohnishi, N.; Mori, K. Exploring duplicated regions in natural images. IEEE Trans. Image Process. 2010. [Google Scholar] [CrossRef] [PubMed]
- Mahmood, T.; Irtaza, A.; Mehmood, Z.; Mahmood, M.T. Copy–move forgery detection through stationary wavelets and local binary pattern variance for forensic analysis in digital images. Forensic Sci. Int. 2017, 279, 8–21. [Google Scholar] [CrossRef]
- Pan, X.; Lyu, S. Region Duplication Detection Using Image Feature Matching. IEEE Trans. Inf. Forensics Secur. 2010, 5, 857–867. [Google Scholar] [CrossRef]
- Xu, B.; Wang, J.; Liu, G.; Dai, Y. Image copy-move forgery detection based on SURF. In Proceedings of the 2010 International Conference on Multimedia Information Networking and Security, Nanjing, China, 4–6 November 2010; pp. 889–892. [Google Scholar]
- Bianchi, T.; Piva, A. Image Forgery Localization via Block-Grained Analysis of JPEG Artifacts. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1003–1017. [Google Scholar] [CrossRef]
- Ferrara, P.; Bianchi, T.; Rosa, A.D.; Piva, A. Image Forgery Localization via Fine-Grained Analysis of CFA Artifacts. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1566–1577. [Google Scholar] [CrossRef]
- Valsesia, D.; Coluccia, G.; Bianchi, T.; Magli, E. User Authentication via PRNU-Based Physical Unclonable Functions. IEEE Trans. Inf. Forensics Secur. 2017, 12, 1941–1956. [Google Scholar] [CrossRef]
- Lin, X.; Li, C. Preprocessing Reference Sensor Pattern Noise via Spectrum Equalization. IEEE Trans. Inf. Forensics Secur. 2016, 11, 126–140. [Google Scholar] [CrossRef]
- Li, R.; Li, C.; Guan, Y. A compact representation of sensor fingerprint for camera identification and fingerprint matching. In Proceedings of the 2015 IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP 2015, South Brisbane, QL, Australia, 19–24 April 2015; pp. 1777–1781. [Google Scholar]
- Bahrami, K.; Kot, A.C.; Li, L.; Li, H. Blurred Image Splicing Localization by Exposing Blur Type Inconsistency. IEEE Trans. Inf. Forensics Secur. 2015, 10, 999–1009. [Google Scholar] [CrossRef]
- Lanh, T.V.; Chong, K.; Emmanuel, S.; Kankanhalli, M.S. A Survey on Digital Camera Image Forensic Methods. In Proceedings of the 2007 IEEE International Conference on Multimedia and Expo, ICME 2007, Beijing, China, 2–5 July 2007; pp. 16–19. [Google Scholar]
- Chen, B.; Yu, M.; Su, Q.; Li, L. Fractional quaternion cosine transform and its application in color image copy-move forgery detection. Multimed. Tools Appl. 2019, 78, 8057–8073. [Google Scholar] [CrossRef]
- Mahmood, T.; Mehmood, Z.; Shah, M.; Saba, T. A robust technique for copy-move forgery detection and localization in digital images via stationary wavelet and discrete cosine transform. J. Vis. Commun. Image Represent. 2018, 53, 202–214. [Google Scholar] [CrossRef]
- Meena, K.B.; Tyagi, V. A copy-move image forgery detection technique based on Gaussian-Hermite moments. Multimed. Tools Appl. 2019, 78, 33505–33526. [Google Scholar] [CrossRef]
- Abdalla, Y.E.; Iqbal, M.T.; Shehata, M.S. Convolutional Neural Network for Copy-Move Forgery Detection. Symmetry 2019, 11, 1280. [Google Scholar] [CrossRef]
- Song, C.; Zeng, P.; Wang, Z.; Li, T.; Qiao, L.; Shen, L. Image Forgery Detection Based on Motion Blur Estimated Using Convolutional Neural Network. IEEE Sens. J. 2019, 19, 11601–11611. [Google Scholar] [CrossRef]
- Zhong, J.; Pun, C. An End-to-End Dense-InceptionNet for Image Copy-Move Forgery Detection. IEEE Trans. Inf. Forensics Secur. 2020, 15, 2134–2146. [Google Scholar] [CrossRef]
- Chen, L.; Lu, W.; Ni, J.; Sun, W.; Huang, J. Region duplication detection based on Harris corner points and step sector statistics. J. Vis. Commun. Image Represent. 2013, 24, 244–254. [Google Scholar] [CrossRef]
- Bay, H.; Ess, A.; Tuytelaars, T.; Gool, L.V. Speeded-Up Robust Features (SURF). Comput. Vis. Image Underst. 2008, 110, 346–359. [Google Scholar] [CrossRef]
- Zandi, M.; Aznaveh, A.M.; Talebpour, A. Iterative Copy-Move Forgery Detection Based on a New Interest Point Detector. IEEE Trans. Inf. Forensics Secur. 2016, 11, 2499–2512. [Google Scholar] [CrossRef]
- Lowe, D.G. Distinctive Image Features from Scale-Invariant Keypoints. Int. J. Comput. Vis. 2004, 60, 91–110. [Google Scholar] [CrossRef]
- Warif, N.B.A.; Wahab, A.W.A.; Idris, M.Y.I.; Salleh, R.; Othman, F. SIFT-Symmetry: A robust detection method for copy-move forgery with reflection attack. J. Vis. Commun. Image Represent. 2017, 46, 219–232. [Google Scholar] [CrossRef]
- Guo, J.; Liu, Y.; Wu, Z. Duplication forgery detection using improved DAISY descriptor. Expert Syst. Appl. 2013, 40, 707–714. [Google Scholar] [CrossRef]
- Yu, L.; Han, Q.; Niu, X. Feature point-based copy-move forgery detection: Covering the non-textured areas. Multimed. Tools Appl. 2016, 75, 1159–1176. [Google Scholar] [CrossRef]
- Liu, L.; Ni, R.; Zhao, Y.; Li, S. Improved SIFT-Based Copy-Move Detection Using BFSN Clustering and CFA Features. In Proceedings of the 2014 Tenth International Conference on Intelligent Information Hiding and Multimedia Signal Processing, IIH-MSP 2014, Kitakyushu, Japan, 27–29 August 2014; pp. 626–629. [Google Scholar]
- Pun, C.; Yuan, X.; Bi, X. Image Forgery Detection Using Adaptive Oversegmentation and Feature Point Matching. IEEE Trans. Inf. Forensics Secur. 2015, 10, 1705–1716. [Google Scholar]
- Silva, E.; de Carvalho, T.J.; Ferreira, A.; Rocha, A. Going deeper into copy-move forgery detection: Exploring image telltales via multi-scale analysis and voting processes. J. Vis. Commun. Image Represent. 2015, 29, 16–32. [Google Scholar] [CrossRef]
- Lee, J.; Chang, C.; Chen, W. Detection of copy-move image forgery using histogram of orientated gradients. Inf. Sci. 2015, 321, 250–262. [Google Scholar] [CrossRef]
- Zhu, Y.; Shen, X.; Chen, H. Copy-move forgery detection based on scaled ORB. Multimed. Tools Appl. 2016, 75, 3221–3233. [Google Scholar] [CrossRef]
- Tralic, D.; Grgic, S.; Sun, X.; Rosin, P.L. Combining cellular automata and local binary patterns for copy-move forgery detection. Multimed. Tools Appl. 2016, 75, 16881–16903. [Google Scholar] [CrossRef]
- Isaac, M.M.; Wilscy, M. Image forgery detection using region - based Rotation invariant Co-occurrences among adjacent LBPs. J. Intell. Fuzzy Syst. 2018, 34, 1679–1690. [Google Scholar] [CrossRef]
- Bi, X.; Pun, C. Fast copy-move forgery detection using local bidirectional coherency error refinement. Pattern Recognit. 2018, 81, 161–175. [Google Scholar] [CrossRef]
- Fan, W.; Sallay, H.; Bouguila, N.; Bourouis, S. A hierarchical Dirichlet process mixture of generalized Dirichlet distributions for feature selection. Comput. Electr. Eng. 2015, 43, 48–65. [Google Scholar] [CrossRef]
- Najar, F.; Bourouis, S.; Bouguila, N.; Belghith, S. Unsupervised learning of finite full covariance multivariate generalized Gaussian mixture models for human activity recognition. Multim. Tools Appl. 2019, 78, 18669–18691. [Google Scholar] [CrossRef]
- Bourouis, S.; Zaguia, A.; Bouguila, N.; Alroobaea, R. Deriving Probabilistic SVM Kernels From Flexible Statistical Mixture Models and its Application to Retinal Images Classification. IEEE Access 2019, 7, 1107–1117. [Google Scholar] [CrossRef]
- Channoufi, I.; Bourouis, S.; Bouguila, N.; Hamrouni, K. Image and video denoising by combining unsupervised bounded generalized gaussian mixture modeling and spatial information. Multim. Tools Appl. 2018, 77, 25591–25606. [Google Scholar] [CrossRef]
- Najar, F.; Bourouis, S.; Zaguia, A.; Bouguila, N.; Belghith, S. Unsupervised Human Action Categorization Using a Riemannian Averaged Fixed-Point Learning of Multivariate GGMM. In Proceedings of the Image Analysis and Recognition—15th International Conference, ICIAR, Povoa de Varzim, Portugal, 27–29 June 2018; pp. 408–415. [Google Scholar]
- Bourouis, S.; Mashrgy, M.A.; Bouguila, N. Bayesian learning of finite generalized inverted Dirichlet mixtures: Application to object classification and forgery detection. Expert Syst. Appl. 2014, 41, 2329–2336. [Google Scholar] [CrossRef]
- Alharbi, A.; Alhakami, W.; Bourouis, S.; Najar, F.; Bouguila, N. Inpainting forgery detection using Hybrid Generative/Discriminative approach based on Bounded Generalized Gaussian mixture model. Appl. Comput. Inform. 2019. [Google Scholar] [CrossRef]
- Alroobaea, R.; Rubaiee, S.; Bourouis, S.; Bouguila, N.; Alsufyani, A. Bayesian inference framework for bounded generalized Gaussian-based mixture model and its application to biomedical images classification. Int. J. Imaging Syst. Technol. 2020, 30, 18–30. [Google Scholar] [CrossRef]
- Najar, F.; Bourouis, S.; Bouguila, N.; Belghith, S. A Fixed-Point Estimation Algorithm for Learning the Multivariate GGMM: Application to Human Action Recognition. In Proceedings of the IEEE Canadian Conference on Electrical & Computer Engineering, CCECE, Quebec, QC, Canada, 13–16 May 2018; pp. 1–4. [Google Scholar]
- Bourouis, S.; Channoufi, I.; Alroobaea, R.; Rubaiee, S.; Andejany, M.; Bouguila, N. Color object segmentation and tracking using flexible statistical model and level-set. Multimed. Tools Appl. 2020, 1–23. [Google Scholar] [CrossRef]
- Vaishnavi, D.; Subashini, T.S. Application of local invariant symmetry features to detect and localize image copy move forgeries. J. Inf. Secur. Appl. 2019, 44, 23–31. [Google Scholar] [CrossRef]
- Mehrish, A.; Subramanyam, A.V.; Emmanuel, S. Robust PRNU estimation from probabilistic raw measurements. Signal Process. Image Commun. 2018, 66, 30–41. [Google Scholar] [CrossRef]
- Hou, J.; Lee, H. Detection of Hue Modification Using Photo Response Nonuniformity. IEEE Trans. Circuits Syst. Video Technol. 2017, 27, 1826–1832. [Google Scholar] [CrossRef]
- Zeng, H.; Zhan, Y.; Kang, X.; Lin, X. Image splicing localization using PCA-based noise level estimation. Multimed. Tools Appl. 2017, 76, 4783–4799. [Google Scholar] [CrossRef]
- Sameer, V.U.; Sarkar, A.; Naskar, R. Source camera identification model: Classifier learning, role of learning curves and their interpretation. In Proceedings of the International Conference on Wireless Communications, Signal Processing and Networking (WiSPNET), Chennai, India, 22–24 March 2017; pp. 2660–2666. [Google Scholar]
- Roy, A.; Chakraborty, R.S.; Sameer, V.U.; Naskar, R. Camera Source Identification Using Discrete Cosine Transform Residue Features and Ensemble Classifier. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition Workshops, CVPR, Honolulu, HI, USA, 21–26 July 2017; pp. 1848–1854. [Google Scholar]
- Lukás, J.; Fridrich, J.J.; Goljan, M. Digital camera identification from sensor pattern noise. IEEE Trans. Inf. Forensics Secur. 2006, 1, 205–214. [Google Scholar] [CrossRef]
- Cao, Y.; Zhang, L.; Zalivaka, S.S.; Chang, C.; Chen, S. CMOS Image Sensor Based Physical Unclonable Function for Coherent Sensor-Level Authentication. IEEE Trans. Circuits Syst. 2015, 62, 2629–2640. [Google Scholar] [CrossRef]
- Qiao, T.; Retraint, F.; Cogranne, R.; Thai, T.H. Source camera device identification based on raw images. In Proceedings of the 2015 IEEE International Conference on Image Processing, ICIP 2015, Quebec City, QC, Canada, 27–30 September 2015; pp. 3812–3816. [Google Scholar]
- Thai, T.H.; Retraint, F.; Cogranne, R. Camera model identification based on the generalized noise model in natural images. Digit. Signal Process. 2016, 48, 285–297. [Google Scholar] [CrossRef]
- Lyu, S.; Pan, X.; Zhang, X. Exposing Region Splicing Forgeries with Blind Local Noise Estimation. Int. J. Comput. Vis. 2014, 110, 202–221. [Google Scholar] [CrossRef]
- Hu, W.; Dai, J.; Jian, J. Effective composite image detection method based on feature inconsistency of image components. Digit. Signal Process. 2015, 39, 50–62. [Google Scholar] [CrossRef]
- Yao, H.; Wang, S.; Zhang, X.; Qin, C.; Wang, J. Detecting Image Splicing Based on Noise Level Inconsistency. Multimed. Tools Appl. 2017, 76, 12457–12479. [Google Scholar] [CrossRef]
- Pun, C.; Liu, B.; Yuan, X. Multi-scale noise estimation for image splicing forgery detection. J. Vis. Commun. Image Represent. 2016, 38, 195–206. [Google Scholar] [CrossRef]
- Chihaoui, T.; Bourouis, S.; Hamrouni, K. Copy-move image forgery detection based on SIFT descriptors and SVD-matching. In Proceedings of the 2014 1st International Conference on Advanced Technologies for Signal and Image Processing (ATSIP), Sousse, Tunisia, 17–19 March 2014; pp. 125–129. [Google Scholar]
- Ardizzone, E.; Bruno, A.; Mazzola, G. Copy-Move Forgery Detection by Matching Triangles of Keypoints. IEEE Trans. Inf. Forensics Secur. 2015, 10, 2084–2094. [Google Scholar] [CrossRef]
- Ferreira, A.; Felipussi, S.C.; Alfaro, C.; Fonseca, P.; Vargas-Munoz, J.E.; dos Santos, J.A.; Rocha, A. Behavior Knowledge Space-Based Fusion for Copy-Move Forgery Detection. IEEE Trans. Image Process. 2016, 25, 4729–4742. [Google Scholar] [CrossRef]
- Soni, B.; Das, P.K.; Thounaojam, D.M. Geometric transformation invariant block based copy-move forgery detection using fast and efficient hybrid local features. J. Inf. Secur. Appl. 2019, 45, 44–51. [Google Scholar] [CrossRef]
- Soni, B.; Das, P.K.; Thounaojam, D.M. Keypoints based enhanced multiple copy-move forgeries detection system using density-based spatial clustering of application with noise clustering algorithm. IET Image Process. 2018, 12, 2092–2099. [Google Scholar] [CrossRef]
- Stamm, M.C.; Lin, W.S.; Liu, K.J.R. Temporal Forensics and Anti-Forensics for Motion Compensated Video. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1315–1329. [Google Scholar] [CrossRef]
- Wu, Y.; Jiang, X.; Sun, T.; Wang, W. Exposing video inter-frame forgery based on velocity field consistency. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP 2014, Florence, Italy, 4–9 May 2014; pp. 2674–2678. [Google Scholar]
- Sitara, K.; Mehtre, B.M. Digital video tampering detection: An overview of passive techniques. Digit. Investig. 2016, 18, 8–22. [Google Scholar] [CrossRef]
- Bestagini, P.; Fontani, M.; Milani, S.; Barni, M.; Piva, A.; Tagliasacchi, M.; Tubaro, S. An overview on video forensics. In Proceedings of the 20th European Signal Processing Conference, EUSIPCO 2012, Bucharest, Romania, 27–31 August 2012; pp. 1229–1233. [Google Scholar]
- Singh, R.D.; Aggarwal, N. Video content authentication techniques: A comprehensive survey. Multimed. Syst. 2018, 24, 211–240. [Google Scholar] [CrossRef]
- Conotter, V.; O’Brien, J.F.; Farid, H. Exposing Digital Forgeries in Ballistic Motion. IEEE Trans. Inf. Forensics Secur. 2012, 7, 283–296. [Google Scholar] [CrossRef]
- Richao, C.; Gaobo, Y.; Ningbo, Z. Detection of object-based manipulation by the statistical features of object contour. Forensic Sci. Int. 2014, 236, 164–169. [Google Scholar] [CrossRef]
- Chen, S.; Tan, S.; Li, B.; Huang, J. Automatic Detection of Object-Based Forgery in Advanced Video. IEEE Trans. Circuits Syst. Video Technol. 2016, 26, 2138–2151. [Google Scholar] [CrossRef]
- Yao, Y.; Shi, Y.; Weng, S.; Guan, B. Deep Learning for Detection of Object-Based Forgery in Advanced Video. Symmetry 2018, 10, 3. [Google Scholar] [CrossRef]
- Zhang, D.; Yang, G.; Li, F.; Wang, J.; Sangaiah, A.K. Detecting seam carved images using uniform local binary patterns. Multimed. Tools Appl. 2020, 79, 8415–8430. [Google Scholar] [CrossRef]
- Zhang, D.; Yin, T.; Yang, G.; Xia, M.; Li, L.; Sun, X. Detecting image seam carving with low scaling ratio using multi-scale spatial and spectral entropies. J. Vis. Commun. Image Represent. 2017, 48, 281–291. [Google Scholar] [CrossRef]
- Wang, W.; Farid, H. Exposing Digital Forgeries in Interlaced and Deinterlaced Video. IEEE Trans. Inf. Forensics Secur. 2007, 2, 438–449. [Google Scholar] [CrossRef]
- Milani, S.; Bestagini, P.; Tagliasacchi, M.; Tubaro, S. Multiple compression detection for video sequences. In Proceedings of the 14th IEEE International Workshop on Multimedia Signal Processing, MMSP 2012, Banff, AB, Canada, 17–19 September 2012; pp. 112–117. [Google Scholar]
- He, P.; Jiang, X.; Sun, T.; Wang, S. Detection of double compression in MPEG-4 videos based on block artifact measurement. Neurocomputing 2017, 228, 84–96. [Google Scholar] [CrossRef]
- Bian, S.; Luo, W.; Huang, J. Exposing Fake Bit Rate Videos and Estimating Original Bit Rates. IEEE Trans. Circuits Syst. Video Technol. 2014, 24, 2144–2154. [Google Scholar] [CrossRef]
- Gironi, A.; Fontani, M.; Bianchi, T.; Piva, A.; Barni, M. A video forensic technique for detecting frame deletion and insertion. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP 2014, Florence, Italy, 4–9 May 2014; pp. 6226–6230. [Google Scholar]
- He, P.; Jiang, X.; Sun, T.; Wang, S. Double compression detection based on local motion vector field analysis in static-background videos. J. Vis. Commun. Image Represent. 2016, 35, 55–66. [Google Scholar] [CrossRef]
- Kang, X.; Liu, J.; Liu, H.; Wang, Z.J. Forensics and counter anti-forensics of video inter-frame forgery. Multimed. Tools Appl. 2016, 75, 13833–13853. [Google Scholar] [CrossRef]
- Yu, L.; Wang, H.; Han, Q.; Niu, X.; Yiu, S.; Fang, J.; Wang, Z. Exposing frame deletion by detecting abrupt changes in video streams. Neurocomputing 2016, 205, 84–91. [Google Scholar] [CrossRef]
- Zheng, J.; Sun, T.; Jiang, X.; He, P. Double H.264 Compression Detection Scheme Based on Prediction Residual of Background Regions. In Proceedings of the Intelligent Computing Theories and Application—13th International Conference, Liverpool, UK, 7–10 August 2017; pp. 471–482. [Google Scholar]
- Li, Q.; Wang, R.; Xu, D. Detection of double compression in HEVC videos based on TU size and quantised DCT coefficients. IET Inf. Secur. 2019, 13, 1–6. [Google Scholar] [CrossRef]
- Yang, J.; Huang, T.; Su, L. Using similarity analysis to detect frame duplication forgery in videos. Multimed. Tools Appl. 2016, 75, 1793–1811. [Google Scholar] [CrossRef]
- Wang, W.; Farid, H. Exposing digital forgeries in video by detecting duplication. In Proceedings of the 9th Workshop on Multimedia & Security, MM&Sec, Dallas, TX, USA, 20–21 September 2007; pp. 35–42. [Google Scholar]
- Ulutas, G.; Ustubioglu, B.; Ulutas, M.; Nabiyev, V.V. Frame duplication detection based on BoW model. Multimed. Syst. 2018, 24, 549–567. [Google Scholar] [CrossRef]
- Fadl, S.; Han, Q.; Qiong, L. Exposing video inter-frame forgery via histogram of oriented gradients and motion energy image. Multidimens. Syst. Signal Process. 2020, 31, 1365–1384. [Google Scholar] [CrossRef]
- Singh, G.; Singh, K. Video frame and region duplication forgery detection based on correlation coefficient and coefficient of variation. Multimed. Tools Appl. 2019, 78, 11527–11562. [Google Scholar] [CrossRef]
- Bestagini, P.; Battaglia, S.; Milani, S.; Tagliasacchi, M.; Tubaro, S. Detection of temporal interpolation in video sequences. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP 2013, Vancouver, BC, Canada, 26–31 May 2013; pp. 3033–3037. [Google Scholar]
- Yao, Y.; Yang, G.; Sun, X.; Li, L. Detecting video frame-rate up-conversion based on periodic properties of edge-intensity. J. Inf. Secur. Appl. 2016, 26, 39–50. [Google Scholar] [CrossRef]
- Hsu, C.C.; Hung, T.Y.; Lin, C.W.; Hsu, C.T. Video forgery detection using correlation of noise residue. In Proceedings of the 2008 IEEE 10th Workshop on Multimedia Signal Processing, Cairns, QLD, Australia, 8–10 October 2008; pp. 170–174. [Google Scholar]
- Kobayashi, M.; Okabe, T.; Sato, Y. Detecting Forgery From Static-Scene Video Based on Inconsistency in Noise Level Functions. IEEE Trans. Inf. Forensics Secur. 2010, 5, 883–892. [Google Scholar] [CrossRef]
- Subramanyam, A.V.; Emmanuel, S. Pixel estimation based video forgery detection. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP 2013, Vancouver, BC, Canada, 26–31 May 2013; pp. 3038–3042. [Google Scholar]
- Li, R.; Liu, Z.; Zhang, Y.; Li, Y.; Fu, Z. Noise-level estimation based detection of motion-compensated frame interpolation in video sequences. Multimed. Tools Appl. 2018, 77, 663–688. [Google Scholar] [CrossRef]
- Ding, X.; Yang, G.; Li, R.; Zhang, L.; Li, Y.; Sun, X. Identification of Motion-Compensated Frame Rate Up-Conversion Based on Residual Signals. IEEE Trans. Circuits Syst. Video Technol. 2018, 28, 1497–1512. [Google Scholar] [CrossRef]
- Bourouis, S.; Al-Osaimi, F.R.; Bouguila, N.; Sallay, H.; Aldosari, F.M.; Mashrgy, M.A. Video Forgery Detection Using a Bayesian RJMCMC-Based Approach. In Proceedings of the 14th IEEE/ACS International Conference on Computer Systems and Applications, AICCSA 2017, Hammamet, Tunisia, 30 October–3 November 2017; pp. 71–75. [Google Scholar]
- Bourouis, S.; Al-Osaimi, F.R.; Bouguila, N.; Sallay, H.; Aldosari, F.M.; Mashrgy, M.A. Bayesian inference by reversible jump MCMC for clustering based on finite generalized inverted Dirichlet mixtures. Soft Comput. 2019, 23, 5799–5813. [Google Scholar] [CrossRef]
- Tralic, D.; Zupancic, I.; Grgic, S.; Grgic, M. CoMoFoD—New database for copy-move forgery detection. In Proceedings of the ELMAR, Zadar, Croatia, 25–27 September 2013; pp. 49–54. [Google Scholar]
- Zampoglou, M.; Papadopoulos, S.; Kompatsiaris, Y. Large-scale evaluation of splicing localization algorithms for web images. Multimed. Tools Appl. 2017, 76, 4801–4834. [Google Scholar] [CrossRef]
- Dong, J.; Wang, W.; Tan, T. CASIA Image Tampering Detection Evaluation Database. In Proceedings of the 2013 IEEE China Summit and International Conference on Signal and Information Processing, ChinaSIP, Beijing, China, 6–10 July 2013; pp. 422–426. [Google Scholar]
- Ng, T.T.; Chang, S.F.; Sun, Q. A Data Set of Authentic and Spliced Image Blocks; ADVENT Technical Report; Columbia University: New York, NY, USA, 2004; pp. 203–2004. [Google Scholar]
- Guan, H.; Kozak, M.; Robertson, E.; Lee, Y.; Yates, A.N.; Delgado, A.; Zhou, D.; Kheyrkhah, T.; Smith, J.; Fiscus, J. MFC datasets: Large-scale benchmark datasets for media forensic challenge evaluation. In Proceedings of the IEEE Winter Applications of Computer Vision Workshops (WACVW), Waikoloa Village, HI, USA, 7–11 January 2019; pp. 63–72. [Google Scholar]
- Korus, P.; Huang, J. Multi-Scale Analysis Strategies in PRNU-Based Tampering Localization. IEEE Trans. Inf. Forensics Secur. 2017, 12, 809–824. [Google Scholar] [CrossRef]
- Rössler, A.; Cozzolino, D.; Verdoliva, L.; Riess, C.; Thies, J.; Nießner, M. FaceForensics++: Learning to Detect Manipulated Facial Images. In Proceedings of the 2019 IEEE/CVF International Conference on Computer Vision, ICCV, Seoul, Korea, 27 October–2 November 2019; pp. 1–11. [Google Scholar]
- Al-Sanjary, O.I.; Ahmed, A.A.; Sulong, G. Development of a video tampering dataset for forensic investigation. Forensic Sci. Int. 2016, 266, 565–572. [Google Scholar] [CrossRef]
- Schaefer, G.; Stich, M. UCID: An uncompressed color image database. In Storage and Retrieval Methods and Applications for Multimedia 2004; International Society for Optics and Photonics: Bellingham, WA, USA, 2003; Volume 5307, pp. 472–480. [Google Scholar]
- Hsu, Y.; Chang, S. Detecting Image Splicing using Geometry Invariants and Camera Characteristics Consistency. In Proceedings of the 2006 IEEE International Conference on Multimedia and Expo, ICME 2006, Toronto, ON, Canada, 9–12 July 2006; pp. 549–552. [Google Scholar]
- Available online: https://http://sulfa.cs.surrey.ac.uk/forged.php (accessed on 4 April 2020).



| Attack Type | Tampering Detection Technique |
|---|---|
| Copy-move (cloning) | Block matching, Discrete Cosine Transform (DCT), Principle Component Analysis (PCA), Autocorrelation |
| Splicing | Bi-spectral analysis, bi-coherence analysis, noise variation estimation, higher order statistics. |
| Re-sampling | Statistical approaches (EM-algorithm.) |
| Double JPEG compression | JPEG artifact estimation (frequency analysis) |
| Editing (luminance, noise nonlinearities) | EM-algorithm, higher order statistics |
| Multimedia enhancement | Blind statistical estimators (blur estimator, noise estimation, geometry transform estimation) |
| Geometric transformation (translation, rotation, scaling, skewing, reflection) | Provide spatial information between copied blocks and its neighbors |
| Post-processing (JPEG/MPEG compression, noise, blurring) | Eliminate any noticeable indications of manipulation especially sharp edges |
| Tampering Type | Tampering Detection Method |
|---|---|
| Copy-move detection | Discrete Cosine Transform (DCT) [32,33] |
| Geometric Moments [34,35] | |
| Fourier–Mellin Transform (FMT) [36,37] | |
| Singular Value Decomposition (SVD) [38] | |
| Zernike moments [39,40] | |
| Wavelet Transform [41,42] | |
| Scale-invariant Feature Transform (SIFT) [15,43] | |
| Speeded Up Robust Features (SURF) [44] | |
| Splicing detection | DCT per Block [45] |
| Color Filter Array (CFA) artifacts [46] | |
| Photo Response Non-uniformity (PRNU) [47,48,49] | |
| Blur inconsistency [50] |
| Dataset | Description |
|---|---|
| MICC-F600 [15] | Used for image copy-move tampering detection: (110 original, 110 tampered) |
| where the image size is 800 × 533. | |
| MICC-F2000 [15] | Used for image copy-move tampering detection: (1300 original, 700 tampered) |
| where the image size is: 2018 × 1536. | |
| CISD [140] | Used for image splicing detection: (933 original, 912 tampered) |
| where the image size is: 128 × 128. | |
| UCID [145] | Used for image retouching detection: contains 1338 images. |
| CMH [67] | Used for image copy-move tampering detection: (108 original, 108 tampered) |
| where the image size is: 845 × 634. | |
| Wild Web tampered [138] | Very large collection of tampered images from the Web |
| CUISDE [146] | Used for image splicing detection: (180 original, 181 tampered) |
| where the image size is (757 × 568). | |
| CASIA-v1.0 [139] | Used for color image splicing detection: (800 original, 921 tampered) |
| where the image size is (374 × 256). | |
| CASIA-v2.0 [139] | Used for color image splicing detection: (7491 original, 5123 tampered) |
| where the image size is (240 × 160 and 900 × 600). | |
| CMFDA [29] | Used for image copy-move tampering detection: contains 48 images with |
| JPEG compression | |
| CoMoFoD [137] | Used for image copy-move tampering detection: (200 original, 60 tampered) |
| where the image size is (512 × 512). | |
| MFC [141] | Used for both images and videos forensics challenge. (176,000 original images, |
| 100,000 tampered) and (11,000 original videos, 4000 tampered videos). | |
| VTD [144] | Used for video forgery detection: (26 original videos, 26 tampered videos). |
| FaceForensics++[143] | Used for video tampering detection: (1000 original videos, 1000 tampered videos). |
| SULFA [147] | Used for video tampering detection: (10 original videos, 10 tampered videos). |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bourouis, S.; Alroobaea, R.; Alharbi, A.M.; Andejany, M.; Rubaiee, S. Recent Advances in Digital Multimedia Tampering Detection for Forensics Analysis. Symmetry 2020, 12, 1811. https://doi.org/10.3390/sym12111811
Bourouis S, Alroobaea R, Alharbi AM, Andejany M, Rubaiee S. Recent Advances in Digital Multimedia Tampering Detection for Forensics Analysis. Symmetry. 2020; 12(11):1811. https://doi.org/10.3390/sym12111811
Chicago/Turabian StyleBourouis, Sami, Roobaea Alroobaea, Abdullah M. Alharbi, Murad Andejany, and Saeed Rubaiee. 2020. "Recent Advances in Digital Multimedia Tampering Detection for Forensics Analysis" Symmetry 12, no. 11: 1811. https://doi.org/10.3390/sym12111811
APA StyleBourouis, S., Alroobaea, R., Alharbi, A. M., Andejany, M., & Rubaiee, S. (2020). Recent Advances in Digital Multimedia Tampering Detection for Forensics Analysis. Symmetry, 12(11), 1811. https://doi.org/10.3390/sym12111811







