Symmetric Key Encryption Based on Rotation-Translation Equation
Abstract
1. Introduction
2. Symmetric Key Encryption Algorithms Based on Numerical Methods
- Lack of rules on how to choose the function f and suitable iterative method so that the convergence of the process is always guaranteed.
- Vulnerability to attack because in these types of algorithms the same letter is encoded with the same real number of each occurrence in the plaintext.
3. On Numerical Methods and Rotation–Translation Equation
3.1. On Numerical Methods for Solving Nonlinear Equations
- the convergence speed of the iteration,
- an interval of convergence and the rules for choosing the initial approximations.
- need to have an interval containing a single root of f, and
- the derivatives and must not have zeros in the interval .
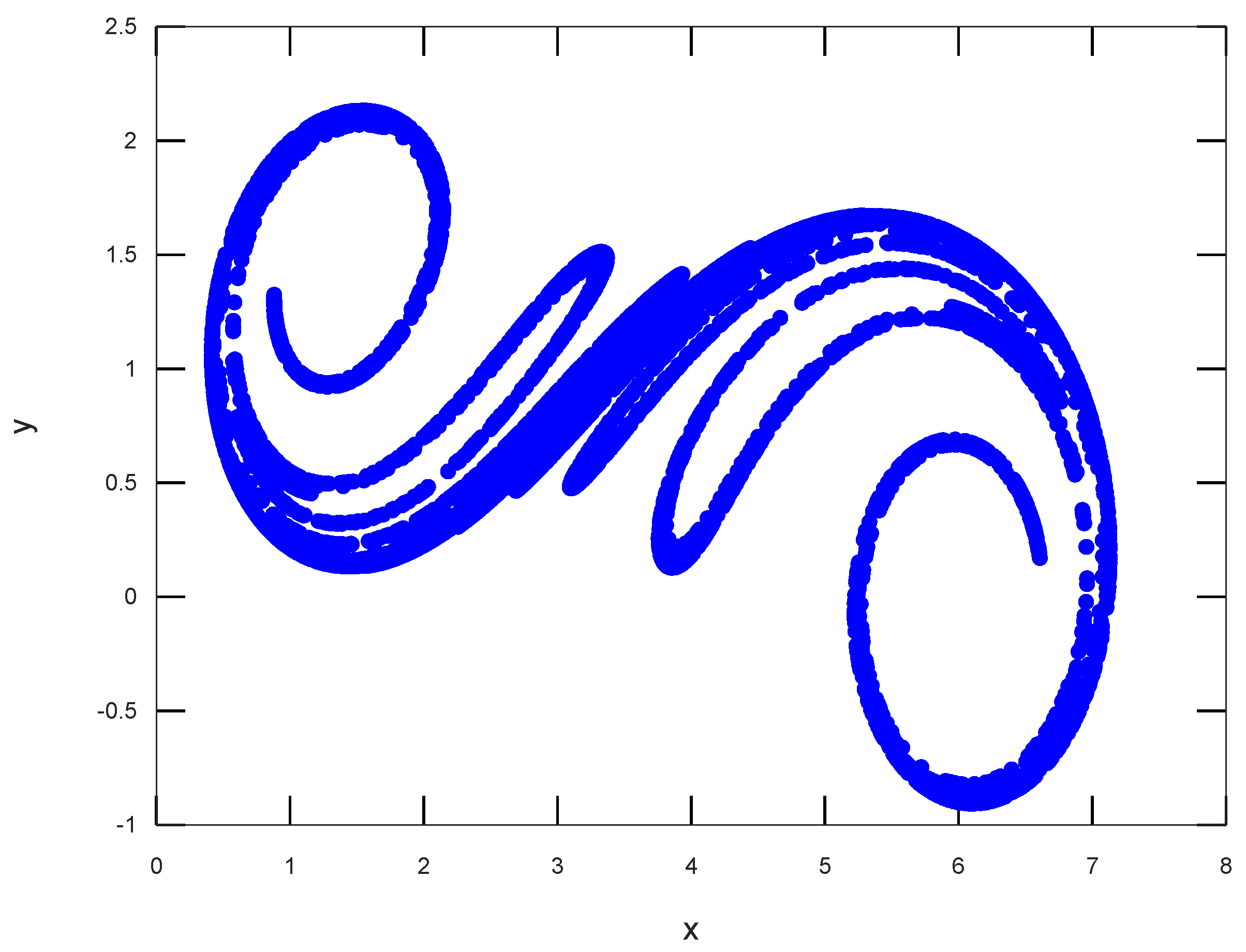
3.2. Base of Rotation–Translation Equation
4. Proposed Encryption Algorithm Based on Numerical Method and Rotation–Translation Equation
- Read the symbols from the plaintext data and get the ASCII values of the different symbols;
- Construct a system of L nonlinear equations by subtracting the ASCII values from the function f and equate with zero;
- Solve individually the nonlinear equations and put the results into an array B;
- The loop of Equation (4) continues, and as an output, two real numbers and are generated. We take the sum of and to produce the real number , which is put into an array R.
- Return to Step 4 until a stream of real numbers R with length L is reached.
- We get the sum of the two arrays B and R to produce E, the output array of real numbers.
4.1. Approaches for Choosing a Nonlinear Function
4.1.1. Nonlinear Function
4.1.2. Polynomial Function
4.2. An Example of Encryption
- , and
- ,
4.3. Brute-Force Attack Analysis
4.4. Statistical Test Analysis of the Proposed Encryption
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Appendix A.
Appendix A.1. Real Roots Counting of Polynomials
- ;
- is an even integer.
Appendix A.2. Bounds of Real Roots of Polynomials
References
- Stallings, W. Cryptography and Network Security: Principles and Practice; Pearson: Upper Saddle River, NJ, USA, 2017. [Google Scholar]
- Shannon, C.E. Communication theory of secrecy systems. Bell Syst. Tech. J. 1949, 28, 656–715. [Google Scholar] [CrossRef]
- Daemen, J.; Rijmen, V. The Rijndael block cipher: AES proposal. In Proceedings of the First, Candidate Conference (AeS1), Rome, Italy, 22–23 March 1999; pp. 343–348. [Google Scholar]
- Bernstein, D.J. ChaCha, a variant of Salsa20. In Proceedings of the Workshop Record of SASC, Lausanne, Switzerland, 13–14 February 2008; Volume 8, pp. 3–5. [Google Scholar]
- Schneier, B. Description of a new variable-length key, 64-bit block cipher (Blowfish). In Fast Software Encryption; Anderson, R., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; pp. 191–204. [Google Scholar]
- Lai, X.; Massey, J.L. A Proposal for a New Block Encryption Standard. In Advances in Cryptology—EUROCRYPT ’90; Damgård, I.B., Ed.; Springer: Berlin/Heidelberg, Germany, 1991; pp. 389–404. [Google Scholar]
- Rivest, R.L.; Shamir, A.; Adleman, L.M. Cryptographic Communications System and Method. U.S. Patent 4,405,829, 20 September 1983. [Google Scholar]
- Koblitz, N. Elliptic curve cryptosystems. Math. Comput. 1987, 48, 203–209. [Google Scholar] [CrossRef]
- Mathur, N.; Bansode, R. AES Based Text Encryption Using 12 Rounds with Dynamic Key Selection. Procedia Comput. Sci. 2016, 79, 1036–1043. [Google Scholar] [CrossRef]
- Panda, M.; Nag, A. Plain Text Encryption Using AES, DES and SALSA20 by Java Based Bouncy Castle API on Windows and Linux. In Proceedings of the 2015 Second International Conference on Advances in Computing and Communication Engineering, Rohtak, India, 1–2 May 2015; pp. 541–548. [Google Scholar] [CrossRef]
- Babaei, M. A novel text and image encryption method based on chaos theory and DNA computing. Natural Comput. 2013, 12, 101–107. [Google Scholar] [CrossRef]
- Min, L.; Lan, X.; Hao, L.; Yang, X. A 6 Dimensional Chaotic Generalized Synchronization System and Design of Pseudorandom Number Generator with Application in Image Encryption. In Proceedings of the 2014 Tenth International Conference on Computational Intelligence and Security, Yunnan, China, 15–16 November 2014; pp. 356–362. [Google Scholar] [CrossRef]
- Murillo-Escobar, M.; Abundiz-Pérez, F.; Cruz-Hernández, C.; López-Gutiérrez, R. A novel symmetric text encryption algorithm based on logistic map. In Proceedings of the International Conference on Communications, Signal Processing and Computers, Guilin, China, 5–8 August 2014; Volume 32, pp. 49–53. [Google Scholar]
- Murillo-Escobar, M.; Cruz-Hernández, C.; Cardoza-Avendaño, L.; Méndez-Ramírez, R. A novel pseudorandom number generator based on pseudorandomly enhanced logistic map. Nonlinear Dyn. 2017, 87, 407–425. [Google Scholar] [CrossRef]
- Volos, C.K.; Kyprianidis, I.; Stouboulos, I. Text Encryption Scheme Realized with a Chaotic Pseudo-Random Bit Generator. J. Eng. Sci. Technol. Rev. 2013, 6, 9–14. [Google Scholar] [CrossRef]
- Wang, X.Y.; Gu, S.X. New chaotic encryption algorithm based on chaotic sequence and plain text. IET Inf. Secur. 2014, 8, 213–216. [Google Scholar] [CrossRef]
- Akgül, A.; Kaçar, S.; Aricıoğlu, B.; Pehlivan, I. Text encryption by using one-dimensional chaos generators and nonlinear equations. In Proceedings of the 2013 IEEE 8th International Conference on Electrical and Electronics Engineering (ELECO), Bursa, Turkey, 28–30 November 2013; pp. 320–323. [Google Scholar]
- Chen, C.; Lin, C. Text encryption using ECG signals with chaotic Logistic map. In Proceedings of the 2010 5th IEEE Conference on Industrial Electronics and Applications, Taichung, Taiwan, 15–17 June 2010; pp. 1741–1746. [Google Scholar] [CrossRef]
- Volos, C.K.; Andreatos, A.S. Secure text encryption based on hardware chaotic noise generator. J. Appl. Math. Bioinform. 2015, 5, 15–35. [Google Scholar]
- Giakoumis, A.; Volos, C.K.; Munoz-Pacheco, J.M.; del Carmen Gomez-Pavon, L.; Stouboulos, I.N.; Kyprianidis, I.M. Text encryption device based on a chaotic random bit generator. In Proceedings of the 2018 IEEE 9th Latin American Symposium on Circuits Systems (LASCAS), Puerto Vallarta, Mexico, 25–28 February 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Stoyanov, B.; Kordov, K. Image Encryption Using Chebyshev Map and Rotation Equation. Entropy 2015, 17, 2117–2139. [Google Scholar] [CrossRef]
- Ge, R.; Yang, G.; Wu, J.; Chen, Y.; Coatrieux, G.; Luo, L. A Novel Chaos-Based Symmetric Image Encryption Using Bit-Pair Level Process. IEEE Access 2019, 7, 99470–99480. [Google Scholar] [CrossRef]
- Nesa, N.; Ghosh, T.; Banerjee, I. Design of a chaos-based encryption scheme for sensor data using a novel logarithmic chaotic map. J. Inf. Secur. Appl. 2019, 47, 320–328. [Google Scholar] [CrossRef]
- Ghosh, A.; Saha, A. A Numerical Method Based Encryption Algorithm With Steganography. Comput. Sci. Inf. Technol. 2013, 3, 149–157. [Google Scholar] [CrossRef]
- Othman, H.; Hassoun, Y.; Owayjan, M. Entropy model for symmetric key cryptography algorithms based on numerical methods. In Proceedings of the 2015 International Conference on Applied Research in Computer Science and Engineering (ICAR), Beirut, Lebanon, 8–9 October 2015; pp. 1–2. [Google Scholar] [CrossRef]
- Hassoun, Y.; Othman, H. Symmetric Key Cryptography Algorithms Based on Numerical Methods. In Proceedings of the NumAn 2014 Conference, Crete, Greece, 22–27 June 2014; pp. 151–155. [Google Scholar]
- AL-Siaq, I.R. Public Key Cryptosystem Based on Numerical Methods. Glob. J. Pure Appl. Math. 2017, 13, 3105–3112. [Google Scholar]
- Traub, J.F. Iterative Methods for the Solution of Equations; Prentice-Hall Series in Automatic Computation; Prentice-Hall: Englewood Cliffs, NJ, USA, 1982. [Google Scholar]
- Jarrat, P. Some fourth order multipoint iterative methods for solving equations. Math. Comput. 1966, 20, 434–437. [Google Scholar] [CrossRef]
- Nedzhibov, G.H.; Hasanov, V.I.; Petkov, M.G. On some families of multi-point iterative methods for solving nonlinear equations. Numer. Algorithms 2006, 42, 127–136. [Google Scholar] [CrossRef]
- Skiadas, C.H.; Skiadas, C. Chaotic Modelling and Simulation: Analysis of Chaotic Models, Attractors and Forms; Chapman and Hall/CRC: London, UK, 2008. [Google Scholar]
- IEEE Standard for Floating-Point Arithmetic; IEEE Std 754-2008; IEEE Computer Society: New York, NY, USA, 2008; pp. 1–70. [CrossRef]
- Alvarez, G.; Li, S. Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. Chaos 2006, 16, 2129–2151. [Google Scholar] [CrossRef]
- Rukhin, A.; Soto, J.; Nechvatal, J.; Smid, M.; Barker, E.; Leigh, S.; Levenson, M.; Vangel, M.; Banks, D.; Heckert, A.; et al. A Statistical Test Suite for Random and Pseudorandom Number Generators for Cryptographic Application. In NIST Special Publication 800-22: Revision 1a, Lawrence E. Bassham III; NIST: Gaithersburg, MD, USA, 2010. [Google Scholar]
- Walker, J. ENT: A Pseudorandom Number Sequence Test Program; Fourmilab: Switzerland, 2008. [Google Scholar]
- Doty-Humphrey, C. PractRand: C++ Library of Pseudo-Random Number Generators And Statistical Tests for RNGs. 2014. Available online: http://pracrand.sourceforge.net/ (accessed on 17 December 2019).
- Abubaker, S.; Wu, K. DAFA—A Lightweight DES Augmented Finite Automaton Cryptosystem. In Security and Privacy in Communication Networks; Keromytis, A.D., Di Pietro, R., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; pp. 1–18. [Google Scholar]
- Mushtaq, M.F.; Jamel, S.; Disina, A.H.; Pindar, Z.A.; Shakir, N.S.A.; Deris, M.M. A Survey on the cryptographic encryption algorithms. Int. J. Adv. Comput. Sci. Appl. 2017, 8, 333–344. [Google Scholar]
- Cauchy, A. Exercises de Mathematiques; IV Annee de Bure Freres: Paris, France, 1829. [Google Scholar]
- Joyal, G.L.; Rahman, Q.I. On the Location of Zeros of Polynomials. Can. Math. Bull. 1967, 10, 53–63. [Google Scholar] [CrossRef]
| Letter | ASCII | NM | JM | Array B | Array R | Array E |
|---|---|---|---|---|---|---|
| (Char) | Code | Iterations | Iterations | Reached Root () | ||
| S | 83 | 6 | 3 | 2.596938615169214 | 1.13761418319195 | 3.73455279836116 |
| h | 104 | 6 | 3 | 2.707594514758099 | 3.83246813052273 | 6.54006264528082 |
| u | 117 | 6 | 3 | 2.767550880788345 | 2.58986907946370 | 5.35741996025204 |
| m | 109 | 6 | 3 | 2.731316748315844 | 4.91511042783787 | 7.64642717615371 |
| e | 101 | 6 | 3 | 2.692927857503279 | 2.09200715087053 | 4.78493500837380 |
| n | 110 | 6 | 3 | 2.735958159508397 | 7.52948634851868 | 10.2654445080271 |
| 94 | 6 | 3 | 2.657327240630354 | 0.10782288092075 | 2.76515012155110 | |
| U | 85 | 6 | 3 | 2.608365856583876 | 5.70292778455835 | 8.31129364114222 |
| n | 110 | 6 | 3 | 2.735958159508397 | 1.30796668243219 | 4.04392484194058 |
| i | 105 | 6 | 3 | 2.712409561369016 | 7.38162948307289 | 10.0940390444419 |
| v | 118 | 6 | 3 | 2.771941812496392 | 0.13478345799064 | 2.90672527048704 |
| e | 101 | 6 | 3 | 2.692927857503279 | 5.23813805178474 | 7.93106590928801 |
| r | 114 | 6 | 3 | 2.754198397484480 | 1.66157719938621 | 4.41577559687069 |
| s | 115 | 6 | 3 | 2.758679632039476 | 7.40857522965636 | 10.1672548616958 |
| i | 105 | 6 | 3 | 2.712409561369016 | 0.16954303210037 | 2.88195259346938 |
| t | 116 | 6 | 3 | 2.763130305077092 | 6.32301454738480 | 9.08614485246189 |
| y | 121 | 6 | 3 | 2.784941120909602 | 0.81874887373720 | 3.60368999464681 |
| NIST Test | p-Value | Success Rate |
|---|---|---|
| Monobit | 0.556460 | 992/1000 |
| Block frequency | 0.010093 | 981/1000 |
| Cumulative sums forward | 0.399442 | 993/1000 |
| Cumulative sums reverse | 0.299736 | 993/1000 |
| Runs | 0.605916 | 986/1000 |
| Longest run of ones | 0.605916 | 988/1000 |
| Rank | 0.830808 | 988/1000 |
| Fourier | 0.200115 | 980/1000 |
| Non overlapping templates | 0.498222 | 990/1000 |
| Overlapping templates | 0.859637 | 992/1000 |
| Universal | 0.653773 | 988/1000 |
| Approximate entropy | 0.693142 | 988/1000 |
| Serial one | 0.894918 | 990/1000 |
| Serial two | 0.282626 | 986/1000 |
| Linear complexity | 0.051942 | 995/1000 |
| State | p-Value | Success Rate |
|---|---|---|
| −4 | 0.696617 | 610/614 |
| −3 | 0.746463 | 606/614 |
| −2 | 0.211467 | 610/614 |
| −1 | 0.501472 | 606/614 |
| +1 | 0.933509 | 607/614 |
| +2 | 0.584363 | 605/614 |
| +3 | 0.873629 | 610/614 |
| +4 | 0.672912 | 608/614 |
| State | p-Value | Success Rate |
|---|---|---|
| −9 | 0.283657 | 608/614 |
| −8 | 0.444875 | 607/614 |
| −7 | 0.699986 | 609/614 |
| −6 | 0.775401 | 607/614 |
| −5 | 0.876173 | 610/614 |
| −4 | 0.921867 | 607/614 |
| −3 | 0.135745 | 607/614 |
| −2 | 0.036332 | 610/614 |
| −1 | 0.574229 | 612/614 |
| +1 | 0.345203 | 609/614 |
| +2 | 0.366645 | 607/614 |
| +3 | 0.517714 | 610/614 |
| +4 | 0.024235 | 612/614 |
| +5 | 0.990938 | 612/614 |
| +6 | 0.447934 | 610/614 |
| +7 | 0.232430 | 609/614 |
| +8 | 0.193732 | 611/614 |
| +9 | 0.659297 | 611/614 |
| ENT Test | Input of Bits | Input of Bytes |
|---|---|---|
| Entropy | 1.000000 | 7.999999 |
| Optimum compression | Reduce size by 0% | Reduce size by 0% |
| square | 0.16, exceed 68.56 % | 242.28, exceed 70.66% |
| Arithmetic mean value | 0.5000 | 127.5055 |
| Monte Carlo for | 3.141226994 (error 0.01%) | 3.141226994 (error 0.01%) |
| Serial correlation | −0.000002 | 0.000180 |
| Test Name | Raw | Processed | Evaluation |
|---|---|---|---|
| BCFN(2,13):! | R = +0.0 | “pass” | normal |
| BCFN(2+0,13−0) | R = −0.7 | p = 0.608 | normal |
| BCFN(2 + 1,13 − 0) | R = +2.3 | p = 0.172 | normal |
| BCFN(2 + 2,13 − 1) | R = −0.1 | p = 0.504 | normal |
| BCFN(2 + 3,13 − 1) | R = −2.2 | p = 0.812 | normal |
| BCFN(2 + 4,13 − 2) | R = −4.4 | p = 0.968 | normal |
| BCFN(2 + 5,13 − 3) | R = −1.1 | p = 0.669 | normal |
| BCFN(2 + 6,13 − 3) | R = −4.1 | p = 0.960 | normal |
| BCFN(2 + 7,13 − 4) | R = +4.8 | p = 0.032 | normal |
| BCFN(2 + 8,13 − 5) | R = +3.3 | p = 0.093 | normal |
| BCFN(2 + 9,13 − 5) | R = −0.3 | p = 0.524 | normal |
| BCFN(2 + 10,13 − 6) | R = −4.3 | p = 0.981 | normal |
| BCFN(2 + 11,13 − 6) | R = −0.9 | p = 0.614 | normal |
| BCFN(2 + 12,13 − 7) | R = +1.6 | p = 0.219 | normal |
| BCFN(2 + 13,13 − 8) | R = −2.7 | p = 0.914 | normal |
| DC6-9x1Bytes-1 | R = −1.0 | p = 0.795 | normal |
| Gap-16:! | R = +0.0 | “pass” | normal |
| Gap-16:A | R = +0.0 | p = 0.614 | normal |
| Gap-16:B | R = −3.2 | p = 0.987 | normal |
| (Low1/8)BCFN(2,13):! | R = +0.0 | “pass” | normal |
| (Low1/8)BCFN(2+0,13 − 1) | R = −1.7 | p = 0.754 | normal |
| (Low1/8)BCFN(2+1,13 − 2) | R = +1.0 | p = 0.336 | normal |
| (Low1/8)BCFN(2+2,13 − 3) | R = +1.7 | p = 0.243 | normal |
| (Low1/8)BCFN(2+3,13 − 3) | R = −0.7 | p = 0.605 | normal |
| (Low1/8)BCFN(2+4,13 − 4) | R = +2.7 | p = 0.138 | normal |
| (Low1/8)BCFN(2+5,13 − 5) | R = −0.3 | p = 0.528 | normal |
| (Low1/8)BCFN(2+6,13 − 5) | R = −0.9 | p = 0.626 | normal |
| (Low1/8)BCFN(2+7,13 − 6) | R = −2.3 | p = 0.838 | normal |
| (Low1/8)BCFN(2+8,13 − 6) | R = −2.4 | p = 0.853 | normal |
| (Low1/8)BCFN(2+9,13 − 7) | R = +1.6 | p = 0.223 | normal |
| (Low1/8)BCFN(2+10,13 − 8) | R = +3.1 | p = 0.096 | normal |
| (Low1/8)DC6-9x1Bytes-1 | R = −0.5 | p = 0.730 | normal |
| (Low1/8)Gap-16:! | R = +0.0 | “pass” | normal |
| (Low1/8)Gap-16:A | R = −0.1 | p = 0.675 | normal |
| (Low1/8)Gap-16:B | R = −1.7 | p = 0.888 | normal |
| Algorithm | Key Size | Correlation | Entropy | Arithmetic Mean | Performance Evaluation |
|---|---|---|---|---|---|
| Proposed | −0.000002 | 7.999999 | 127.5055 | 0.105 | |
| [14] Murillo-Escobar | −0.002100 | 7.994500 | - | - | |
| [21] Stoyanov 2015 | 0.000001 | 7.999998 | 127.4982 | 0.19 | |
| [37,38] AES-128 | −0.002100 | 7.954880 | 127.5281 | 0.12 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Stoyanov, B.; Nedzhibov, G. Symmetric Key Encryption Based on Rotation-Translation Equation. Symmetry 2020, 12, 73. https://doi.org/10.3390/sym12010073
Stoyanov B, Nedzhibov G. Symmetric Key Encryption Based on Rotation-Translation Equation. Symmetry. 2020; 12(1):73. https://doi.org/10.3390/sym12010073
Chicago/Turabian StyleStoyanov, Borislav, and Gyurhan Nedzhibov. 2020. "Symmetric Key Encryption Based on Rotation-Translation Equation" Symmetry 12, no. 1: 73. https://doi.org/10.3390/sym12010073
APA StyleStoyanov, B., & Nedzhibov, G. (2020). Symmetric Key Encryption Based on Rotation-Translation Equation. Symmetry, 12(1), 73. https://doi.org/10.3390/sym12010073






