SVD-Based Image Watermarking Using the Fast Walsh-Hadamard Transform, Key Mapping, and Coefficient Ordering for Ownership Protection
Abstract
1. Introduction
- A blind image watermarking method is proposed that is highly robust and secured against numerous attacks while providing good quality watermarked images;
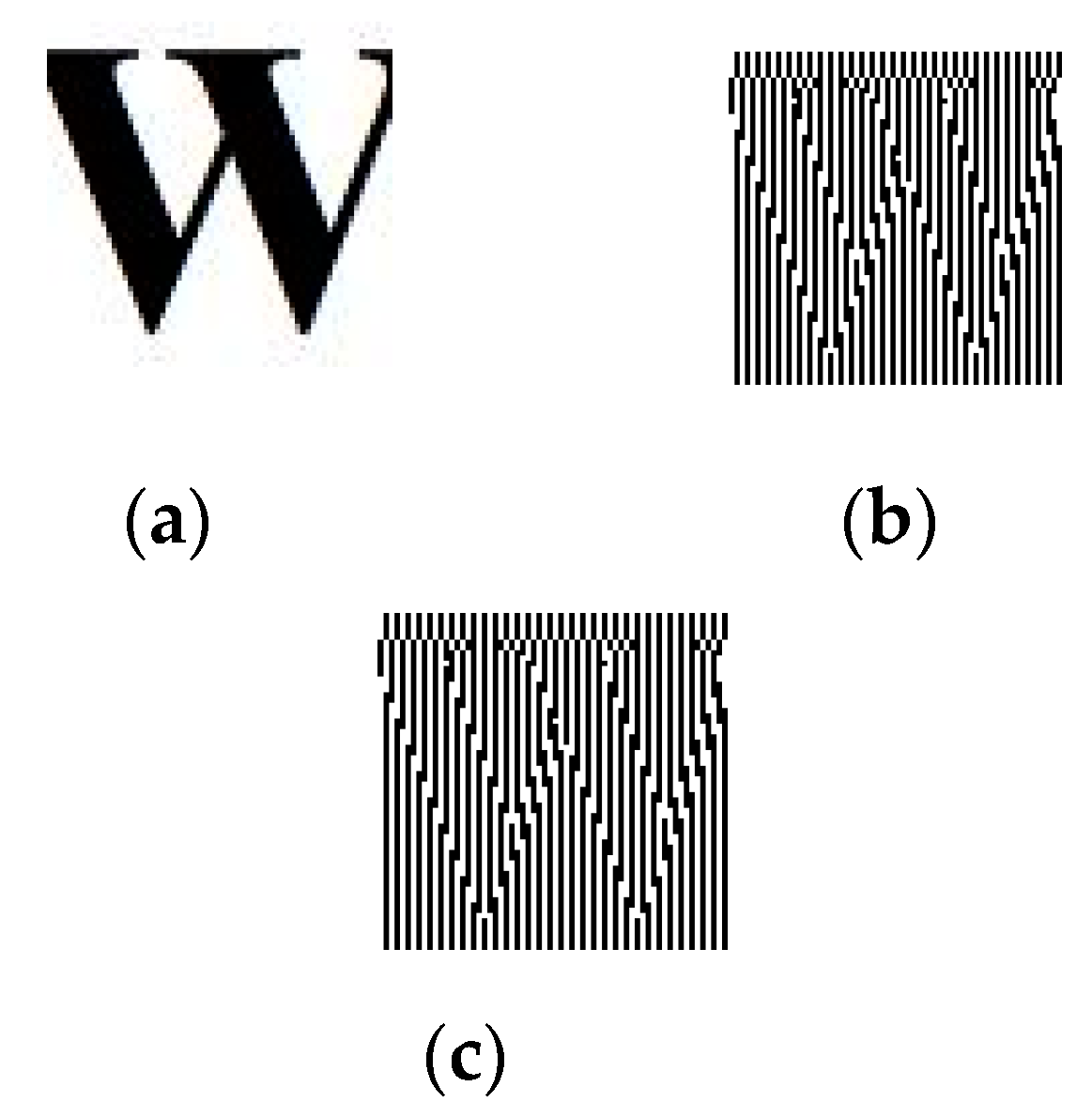
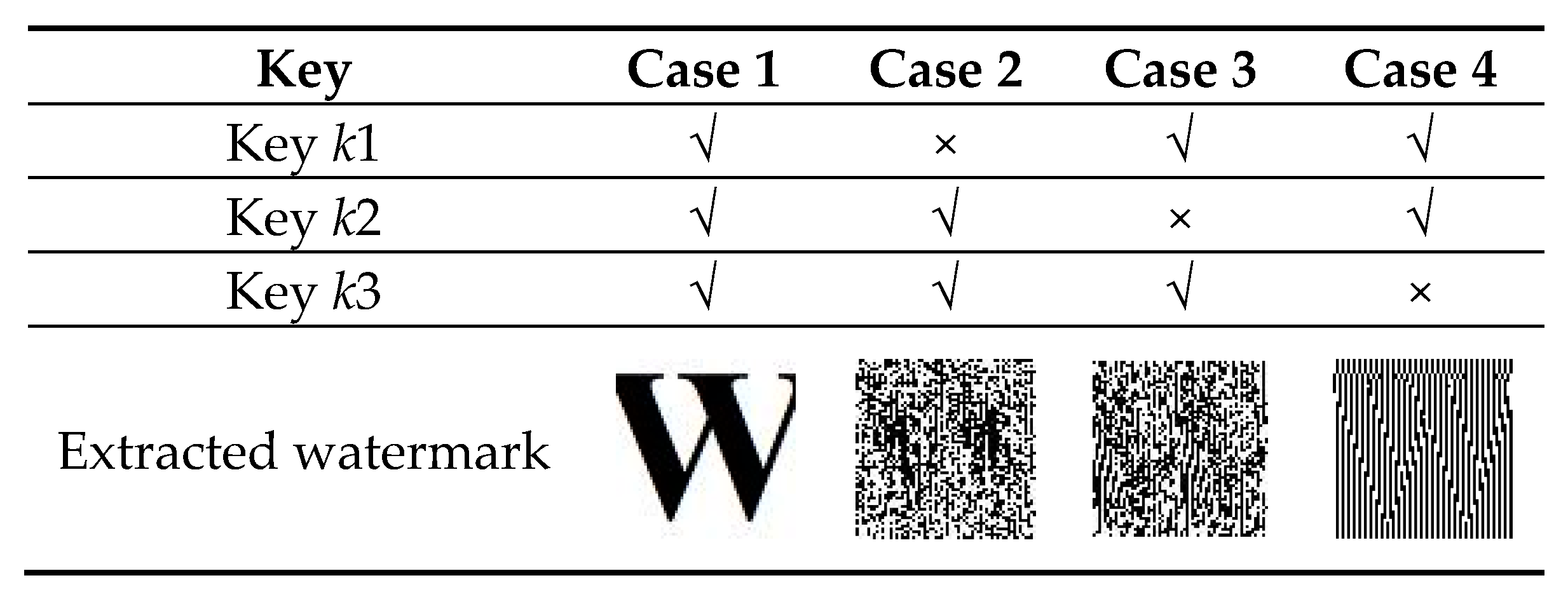
- To safeguard the unauthorized detection, the Gaussian mapping is used to scramble the watermark;
- To facilitate authentic and errorless extraction of the watermark image by generating the keys from the singular values the FWHT blocks of the cover image;
- It provides a good trade-off among robustness, security, and imperceptibility.
2. Background Information
2.1. Singular Value Decomposition
2.2. Fast Walsh-Hadamard Transform
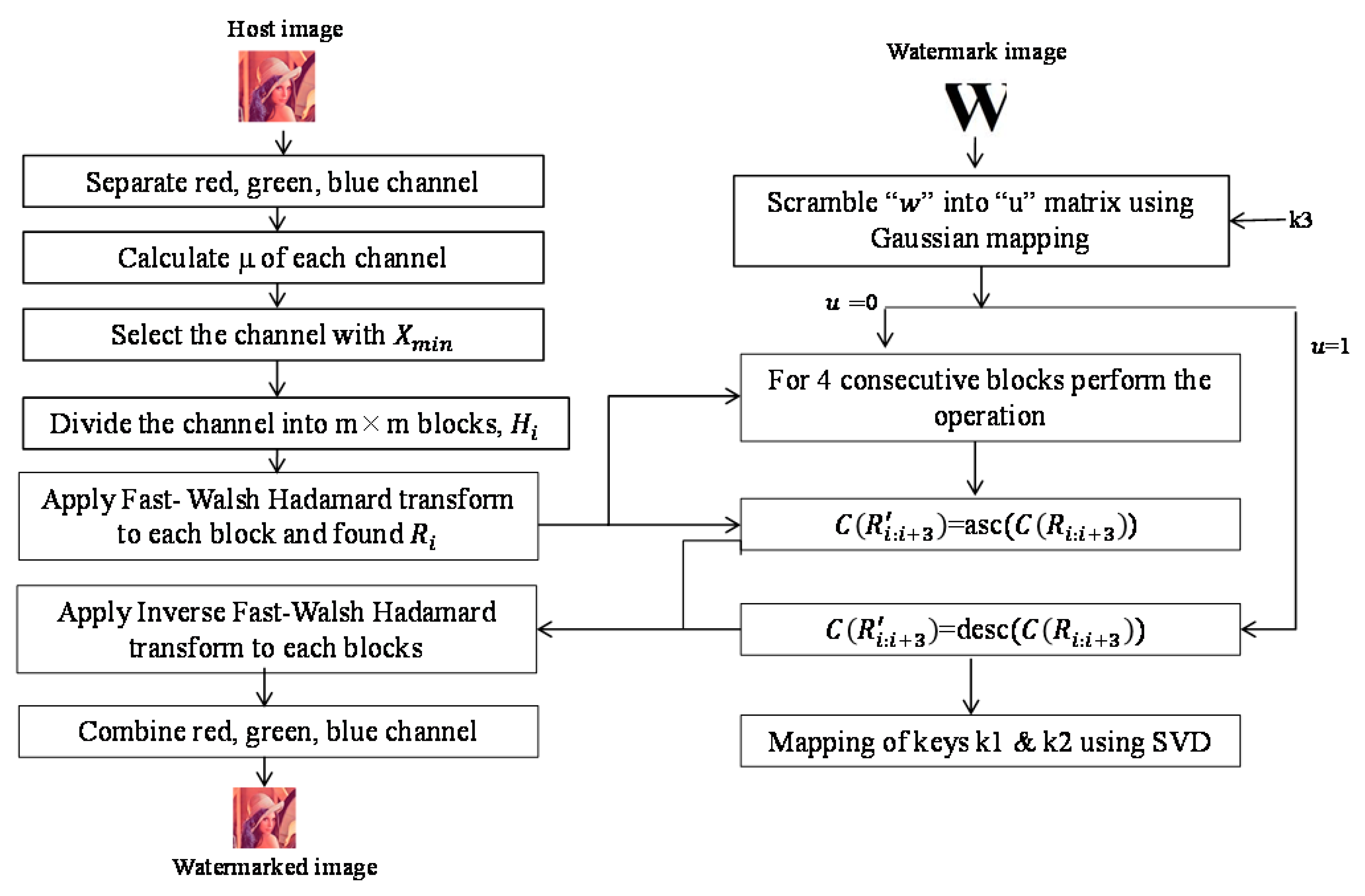
3. Proposed Method
3.1. Watermark Preprocessing
- Step 1.
- The watermark image W is reshaped into a one-dimensional sequence Q = {q(r), }.
- Step 2.
- Initially, a reference pattern is generated using a Gaussian map, which is defined in Equation (4).where a, b, and are predefined constants and are used as key as shown in Figure 1.
- Step 3.
- Then, the binary reference pattern is calculated using the following equation:where T is a predefined threshold.
- Step 4.
- Finally, the watermark sequence q(r) is scrambled with z(r) using Equation (6):where denotes the bitwise XOR operation.
3.2. Watermark Embedding Process
- Step 1.
- The original host image is first divided into three channels , where represent the red, green, and blue channels of the original image, respectively. Then, the mean of the pixel values of each channel is calculated using Equation (7).where indicate the mean of the pixel values of the red, green, and blue channels, respectively. After that, the channel with minimum mean is selected, which is either .
- Step 2.
- The selected channel is further divided into m × m non-overlapping blocks, n}, where is the block number and m is the length of the row and column of each block.
- Step 3.
- FWHT is applied in each block to obtain the transformed block , where Ri contains the FWHT coefficients.
- Step 4.
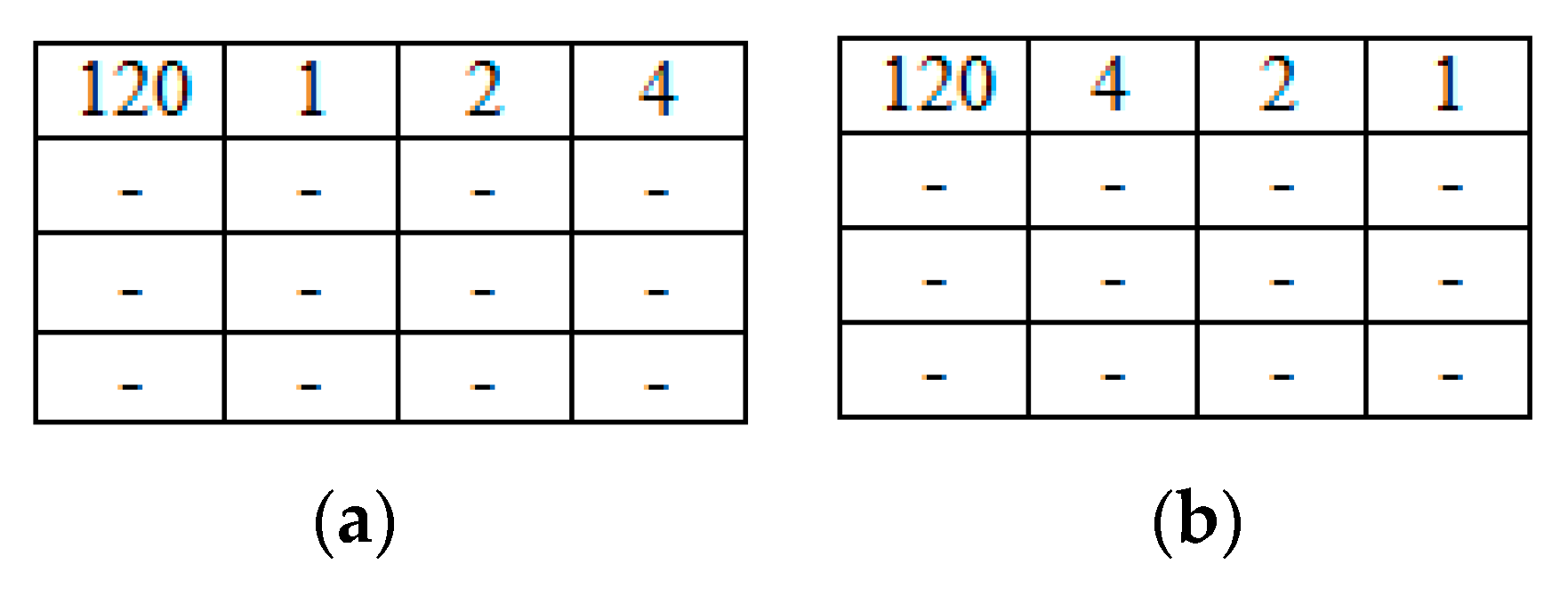
- Among all theblocks, each set of four consecutive blocks Ri, Ri+1, Ri+2, and Ri+3 is selected to embed a watermark bit. The main idea of the embedding process is to sort the coefficients of the first row represented by of each set of selected blocks Ri, Ri+1, Ri+2, and Ri+3 except the DC value. If the watermark bit is 1, the selected low-frequency coefficients are sorted in descending order; otherwise, they are sorted in ascending order. The concept of embedding the watermark bit in ascending and descending order with a block size of 4 × 4 where, m = 4, is shown in Figure 2.
- (1)
- Each block of the selected channel is decomposed into three matrices:using Equation (9).where are the singular values of the matrix Di of each block . These singular values are unique for each block Hi. The keys k1 and k2 are calculated using these singular values. Thus, unauthorized people could not map the keys without the host image to prove fake ownership. To do this, initially, a null key is defined. Then, is generated using these singular values as defined in Equation (10) below:where i indicates the block number, j m} indicates the singular values of each block, asc and desc represent sorting the data in ascending order and descending order, respectively, and indicates the concatenation operation The singular values are sorted according to the watermark bit 0 or 1.
- (2)
- Finally, k1 is converted into a one-dimensional sequence of length L = , where n is the total number of blocks and m is the total number of singular values in each block.
- (3)
- To generate key k2, define a null key with length S, where S = n/m. Then, is generated from key using the following Equation (11):where is the mean of consecutive t values of key and the length of key k2 is (n/m) + 1. Although the first key can be generated by the owner only, the second key is generated to authenticate the first key in the extraction process.
- Step 5.
- Inverse FWHT is applied to each transformed block and the watermarked blocks are found.
- Step 6.
- Finally, three watermarked channels are combined to generate the watermarked image .
| Algorithm 1: Watermark Insertion |
| Variable Declaration: X: Host image : Mean intensity value of each channel of host image (Lena) : Channel with minimum mean : Non-overlapping blocks of (size 4 × 4) FWHT, SVD: Transformation and decomposition used in the algorithm : FWHT transformed block of : Three coefficients of first row (except DC value) of the consecutive transformed block : Coefficients in ascending or descending order W: Watermark image u: Scrambled watermark sequence Watermark Embedding Procedure: 1. Watermark preprocess: scramble W to obtain u using Gaussian mapping 2. Read the host image and calculate of each channel (Red, Green, Blue) X.bmp (host image with size of 256 × 256) W.bmp (watermark image with size of 32 × 32) 3. Select channel and divide it into 4 × 4 blocks 4. Apply FWHT to each block and found 5. Watermark Insertion // Use SVD to map keys 6. Perform inverse FWHT and combine the channels to get the Watermarked Image |
3.3. Watermark Detection Process
- Step 1.
- The attacked watermarked image is first divided into three channels, {}. Then, the mean value of the pixels of the red, green, and blue channels represented by are calculated. Thereafter that, the channel with minimum mean is selected for extracting the watermark.
- Step 2.
- The selected channel is further divided into m × m non-overlapping blocks, where is the block number.
- Step 3.
- FWHT is carried out on each block. After applying this operation, the transformed blocks are found.
- Step 4.
- The degree of ascendant/descendant denoted by dof is calculated for four consecutive transformed blocks }. Therefore, dof(asc) represents the number of times that the low-frequency coefficients in the first rowof each transformed block except for the DC value are in ascending order. Similarly, the dof(desc) represents the number of times that the low-frequency coefficients in the first row of each transformed block except the DC value are in descending order.
- Step 5.
- The hidden binary sequence is found using the following rule:
If
then
else If
then - Step 6.
- The binary watermark sequence q*(r) is extracted with key k3 using the following equation:
| Algorithm 2: Watermark Extraction |
| Variable Declaration: : Attacked watermarked image : Mean intensity value of each channel of : Channel with minimum mean : Non-overlapping blocks of (size 4 × 4) FWHT: Transformations used in the algorithm : FWHT transformed block of : Three coefficients of first row (except DC value) of four consecutive transformed block W: Watermark image u: Scrambled watermark sequence dof(asc/desc): The number of times low-frequency coefficients in the first row of each transformed block except the DC value are in ascending/descending order. Watermark Extraction Procedure: 1. Read and calculate of each channel (Red, Green, Blue) 2. Select channel and divide into 4 × 4 blocks 3. Apply FWHT to each block and found 4. Watermark extraction (a) Modifying dof(asc/desc) into dof′(asc/desc) with key // Consecutive t values of the key are considered each time for extracting a one-bit watermark, where and means mean of these t values (c) Watermark extraction If then else If then where, (d) Re-scramble u to get W |
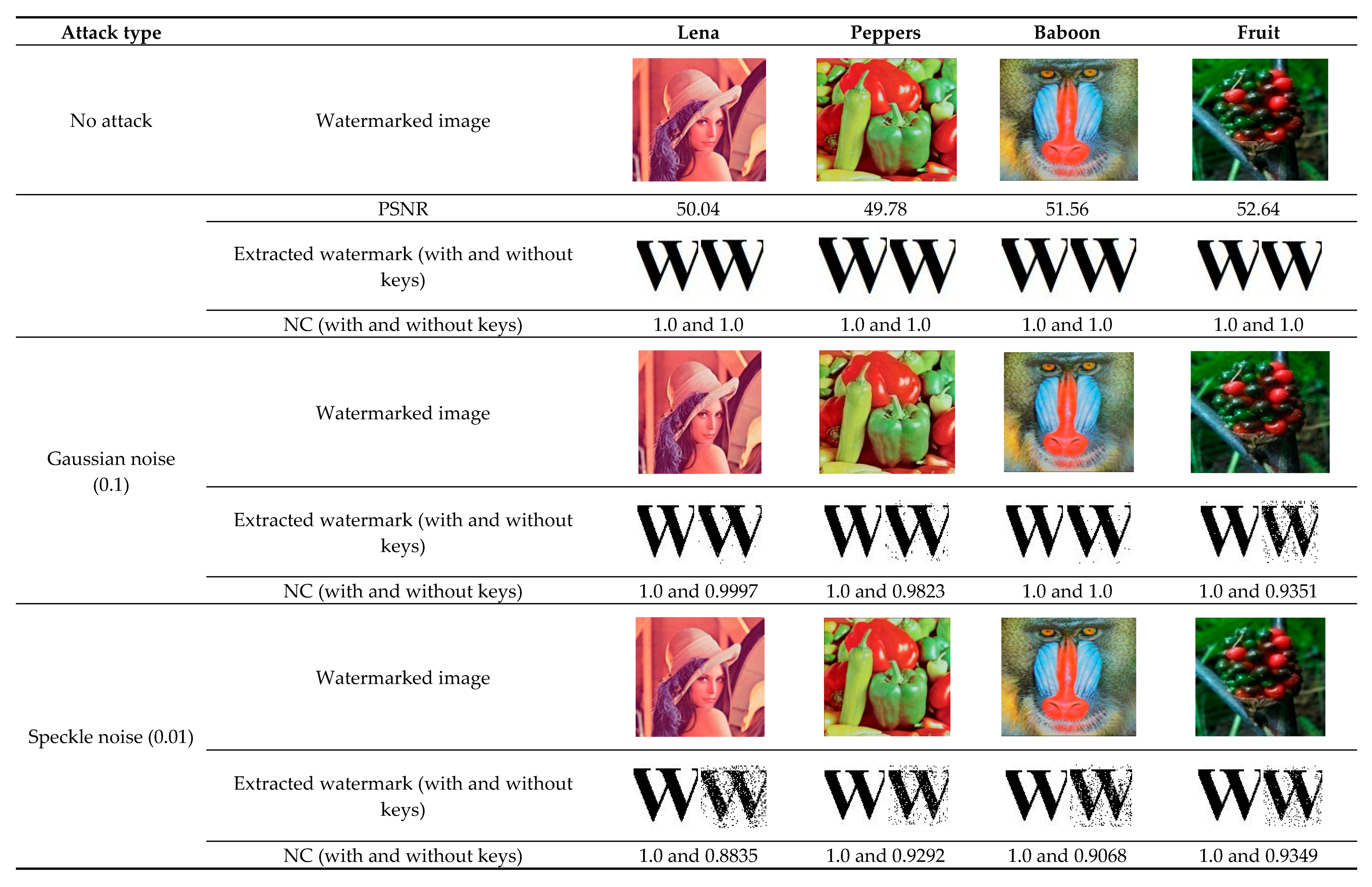
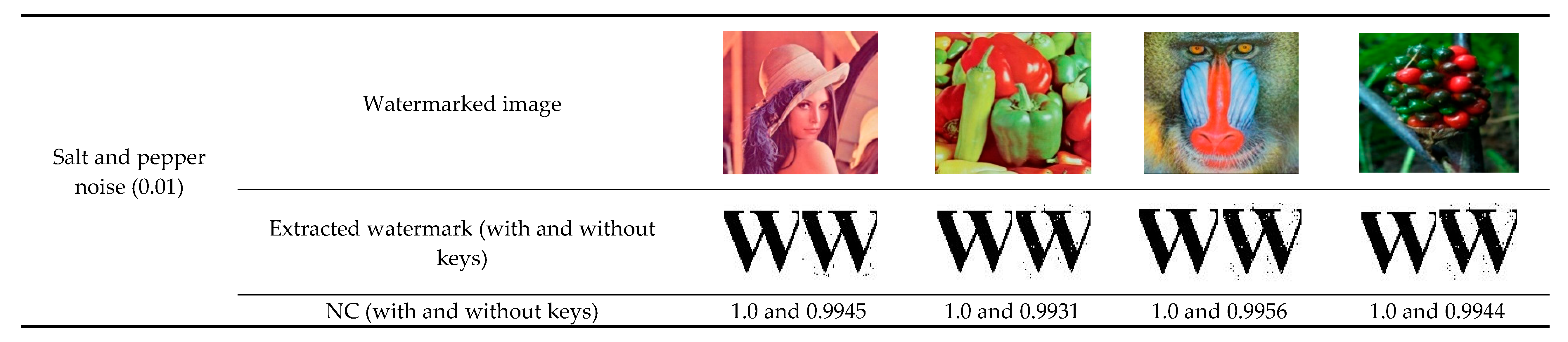
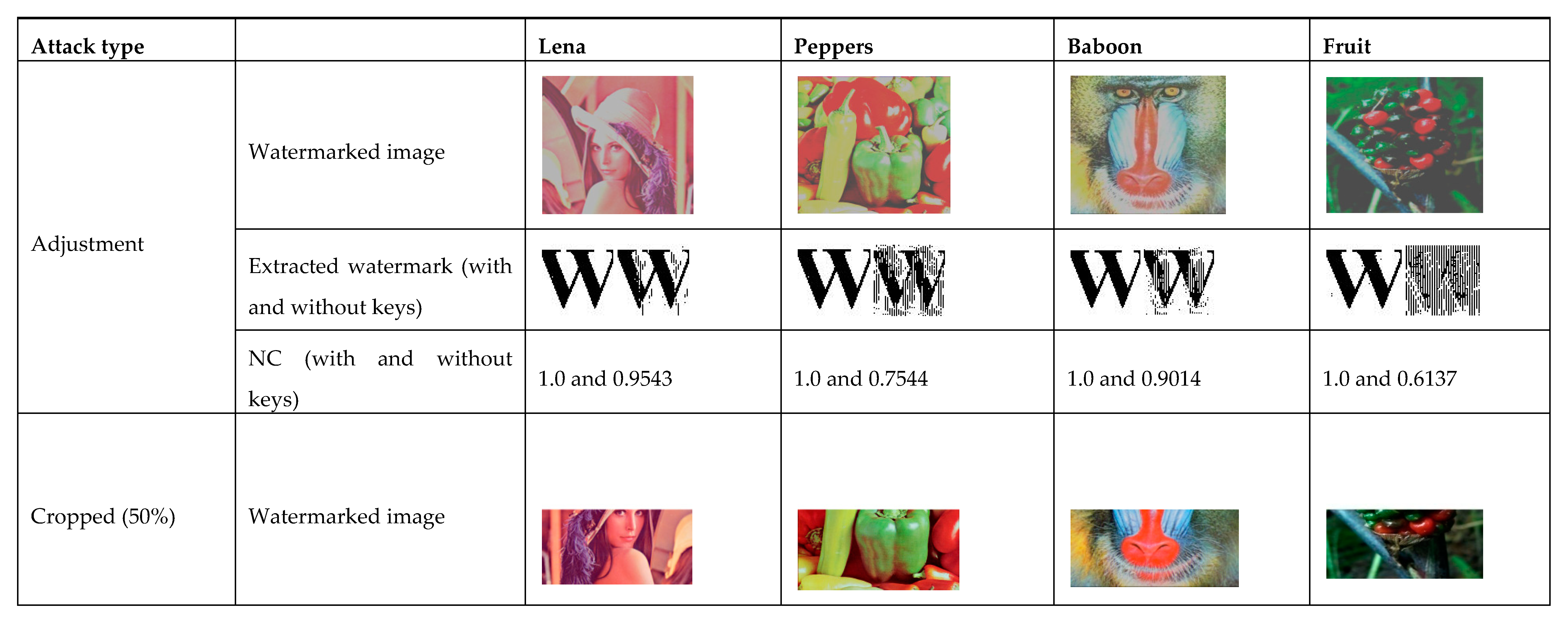
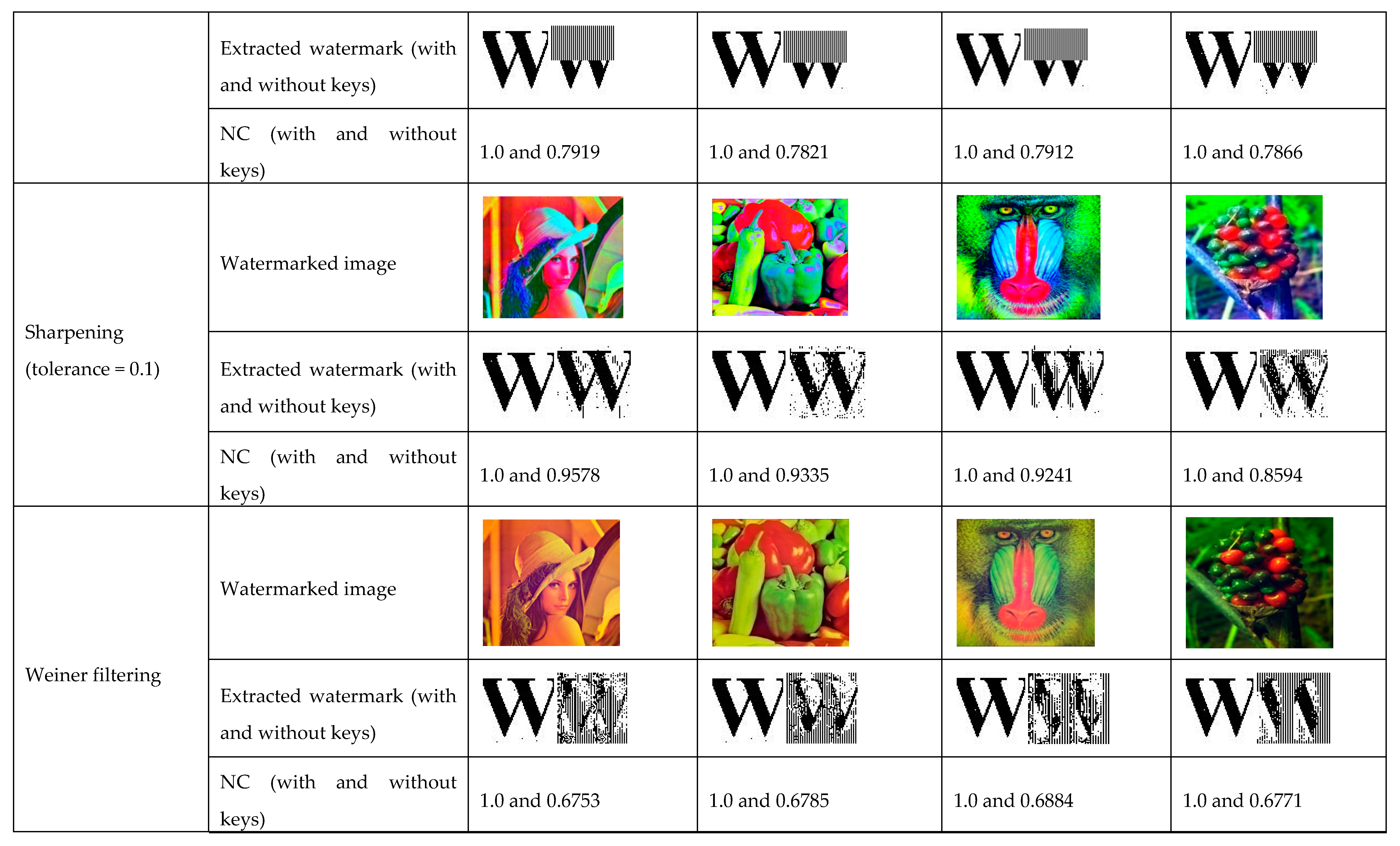
4. Experimental Results and Discussions
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Bakhsh, F.Y.; Moghaddam, M.E. A robust HDR images watermarking method using artificial bee colony algorithm. J. Inf. Secur. Appl. 2018, 41, 12–27. [Google Scholar]
- Guo, Y.; Au, O.C.; Wang, R.; Fang, L.; Cao, X. Halftone image watermarking by content aware double-sided embedding error diffusion. IEEE Trans. Image Process. 2018, 27, 3387–3402. [Google Scholar] [CrossRef] [PubMed]
- Chetan, K.R.; Nirmala, S. An efficient and secure robust watermarking scheme for document images using Integer wavelets and block coding of binary watermarks. J. Inf. Secur. Appl. 2015, 24, 13–24. [Google Scholar] [CrossRef]
- Wanga, H.; Yina, B.; Zhoub, L. Geometrically invariant image watermarking using connected objects and gravity centers. KSII Trans. Internet Inf. Syst. 2013, 7, 2893–2912. [Google Scholar]
- Lin, P.Y.; Chen, Y.H.; Chang, C.C.; Lee, J.S. Contrast adaptive removable visible watermarking (CARVW) mechanism. Image Vis. Comput. 2013, 31, 311–321. [Google Scholar] [CrossRef]
- Su, Q.; Niu, Y.; Zou, H.; Liu, X. A blind dual color images watermarking based on singular value decomposition. Appl. Math. Comput. 2013, 219, 8455–8466. [Google Scholar] [CrossRef]
- Wu, X.; Sun, W. Robust copyright protection scheme for digital images using overlapping DCT and SVD. Appl. Soft Comput. 2013, 13, 1170–1182. [Google Scholar] [CrossRef]
- Bhatnagar, G.; Wua, Q.M.J.; Raman, B. A new robust adjustable logo watermarking scheme. Comput. Secur. 2012, 31, 40–58. [Google Scholar] [CrossRef]
- Tsai, H.H.; Huang, Y.J.; Lai, Y.S. An SVD-based image watermarking in wavelet domain using SVR and PSO. Appl. Soft Comput. 2012, 12, 2442–2453. [Google Scholar] [CrossRef]
- Hun, H.T.; Chen, W.H. A dual cepstrum based watermarking scheme with self-synchronization. Signal Process. 2012, 92, 1109–1116. [Google Scholar]
- Lin, C.C. An information hiding scheme with minimal image distortion. Comput. Stand. Interfaces 2011, 33, 477–484. [Google Scholar] [CrossRef]
- Lee, Y.; Kim, H.; Park, Y. A new data hiding scheme for binary image authentication with small image distortion. Inf. Sci. 2009, 179, 3866–3884. [Google Scholar] [CrossRef]
- Su, Q.; Wang, G.; Zhang, X. A new algorithm of blind color image watermarking based on LU decomposition. Multidimens. Syst. Signal Process. 2018, 29, 1055–1074. [Google Scholar] [CrossRef]
- Murty, P.S.; Kumar, S.D.; Kumar, P.R. A semi blind self reference image watermarking in DCT using Singular Value Decomposition. Int. J. Comput. Appl. 2013, 62, 29–36. [Google Scholar]
- Shen, J.J.; Ren, J.M. A robust associative watermarking technique based on vector quantization. Digit. Signal Process. 2010, 20, 1408–1423. [Google Scholar] [CrossRef]
- Bhatnagar, G.; Raman, B. A new robust reference watermarking scheme based on DWT-SVD. Comput. Stand. Interfaces 2009, 31, 1002–1013. [Google Scholar] [CrossRef]
- Zhou, X.; Zhang, H.; Wang, C. A robust image watermarking technique based on DWT, APDCBT, and SVD. Symmetry 2018, 10, 77. [Google Scholar] [CrossRef]
- Sarker, M.I.H.; Khan, M.I. An efficient image watermarking scheme using BFS technique based on Hadamar Transform. Smart Comput. Rev. 2013, 3, 298–308. [Google Scholar]
- Kumar, A.; Luhach, A.K.; Pal, D. Robust digital image watermarking technique using image normalization and Discrete Cosine Transformation. Int. J. Comput. Appl. 2013, 65, 5–13. [Google Scholar]
- Liua, J.; Liub, G.; Hea, W.; Lia, Y. A new digital watermarking algorithm based on WBCT. Procedia Eng. 2012, 29, 1559–1564. [Google Scholar] [CrossRef][Green Version]
- Lai, C.C.; Tsai, C.C. Digital image watermarking using Discrete Wavelet Transform and Singular Value Decomposition. IEEE Trans. Instrum. Meas. 2010, 59, 3060–3063. [Google Scholar] [CrossRef]
- Mohammad, A.A.; Alhaj, A.; Shaltaf, S. An improved SVD-based watermarking scheme for protecting rightful ownership. Signal Process. 2008, 88, 2158–2180. [Google Scholar] [CrossRef]
- Ahmed, K.A.; Ozturk, S. A novel hybrid DCT and DWT based robust watermarking algorithm for color images. Multimed. Tools Appl. 2019, 78, 17027–17049. [Google Scholar]
- Patvardhan, C.; Kumar, P.; Lakshmi, C.V. Effective color image watermarking scheme using YCbCr color space and QR code. Multimed. Tools Appl. 2018, 77, 12655–12677. [Google Scholar] [CrossRef]


| Watermarked Images | Proposed Method | Ahmed et al. [23] | Patvardhar et al. [24] | Su et al. [13] |
|---|---|---|---|---|
 | 50.04 | 54.2577 | 39.4428 | |
 | 49.78 | 47.1961 | 40.8216 | |
 | 51.56 | 47.1836 | 54.3499 | |
 | 52.64 |
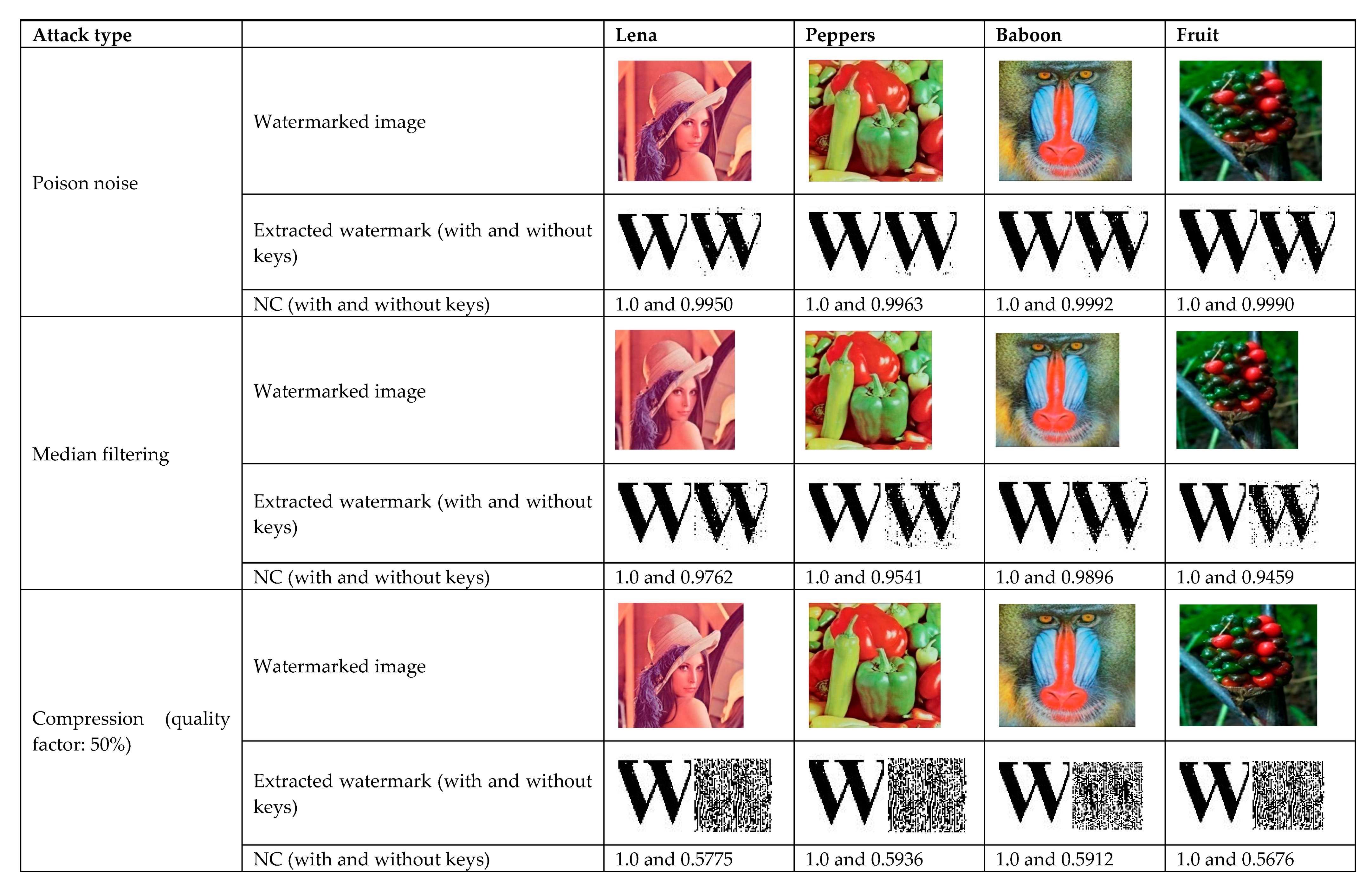
| No | Attack Type | Lena | Peppers | Baboon | Fruit |
|---|---|---|---|---|---|
| 1 | Gaussian (0.01) | 1.0 | 1.0 | 1.0 | 1.0 |
| 2 | Speckle (0.01) | 1.0 | 1.0 | 1.0 | 1.0 |
| 3 | Adjustment | 1.0 | 1.0 | 1.0 | 1.0 |
| 4 | Cropping (50%) | 1.0 | 1.0 | 1.0 | 1.0 |
| 5 | Sharpening (tol = 0.1) | 1.0 | 1.0 | 1.0 | 1.0 |
| 6 | Rotation (400) | 1.0 | 1.0 | 1.0 | 1.0 |
| 7 | Wiener filtering | 1.0 | 1.0 | 1.0 | 1.0 |
| 8 | Poison noise | 1.0 | 1.0 | 1.0 | 1.0 |
| 9 | Salt and pepper noise (0.01) | 1.0 | 1.0 | 1.0 | 1.0 |
| 10 | Median filtering | 1.0 | 1.0 | 1.0 | 1.0 |
| 11 | Compression (quality factor = 50%) | 1.0 | 1.0 | 1.0 | 1.0 |
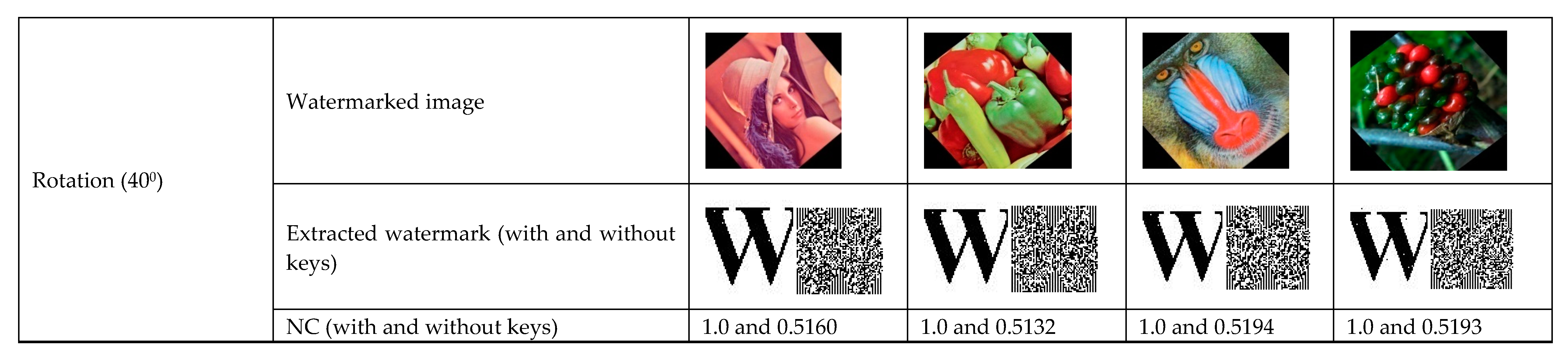
| No | Attack Type | Lena | Peppers | Baboon | Fruit |
|---|---|---|---|---|---|
| 1 | Gaussian (0.1) | 0.9997 | 0.9823 | 1.0 | 0.9351 |
| 2 | Speckle (0.01) | 0.8835 | 0.9292 | 0.9068 | 0.9349 |
| 3 | Adjustment | 0.9543 | 0.7544 | 0.9014 | 0.6137 |
| 4 | Cropping (50%) | 0.7919 | 0.7821 | 0.7912 | 0.7866 |
| 5 | Sharpening (tol = 0.1) | 0.9578 | 0.9335 | 0.9241 | 0.8594 |
| 6 | Rotation (400) | 0.5160 | 0.5132 | 0.5194 | 0.5193 |
| 7 | Wiener filtering | 0.6753 | 0.6785 | 0.6884 | 0.6771 |
| 8 | Poison noise | 0.9950 | 0.9963 | 0.9992 | 0.9990 |
| 9 | Salt and pepper noise (0.01) | 0.9945 | 0.9931 | 0.9956 | 0.9944 |
| 10 | Median filtering | 0.9762 | 0.9541 | 0.9896 | 0.9459 |
| 11 | Compression (quality factor = 50%) | 0.5775 | 0.5936 | 0.5912 | 0.5676 |
| No | Attack Type | Ahmed et al. [23] | Patvardhar et al. [24] | Su et al. [13] | Proposed |
|---|---|---|---|---|---|
| 1 | Gaussian noise (0.1) | 0.9625 | 0.9885 | 0.9131 | 1.0 |
| 2 | Speckle noise (0.01) | 0.9601 | -- | -- | 1.0 |
| 3 | Contrast Adjustment | -- | 0.9491 | -- | 1.0 |
| 4 | Cropping (50%) | -- | 0.9947 | 0.9604 | 1.0 |
| 5 | Sharpening | 0.9388 | -- | 0.9999 | 1.0 |
| 6 | Rotation (25°) | 0.7991 | 0.9989 | -- | 1.0 |
| 7 | Poison noise | 0.9884 | -- | -- | 1.0 |
| 8 | Salt and pepper noise (0.01) | 0.9117 | 0.9807 | 0.9902 | 1.0 |
| 9 | Median filtering | 0.9908 | 0.9989 | 0.8814 | 1.0 |
| 10 | JPEG compression (quality factor = 20%) | 0.9784 | 0.9895 | 0.8469 | 1.0 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khanam, T.; Dhar, P.K.; Kowsar, S.; Kim, J.-M. SVD-Based Image Watermarking Using the Fast Walsh-Hadamard Transform, Key Mapping, and Coefficient Ordering for Ownership Protection. Symmetry 2020, 12, 52. https://doi.org/10.3390/sym12010052
Khanam T, Dhar PK, Kowsar S, Kim J-M. SVD-Based Image Watermarking Using the Fast Walsh-Hadamard Transform, Key Mapping, and Coefficient Ordering for Ownership Protection. Symmetry. 2020; 12(1):52. https://doi.org/10.3390/sym12010052
Chicago/Turabian StyleKhanam, Tahmina, Pranab Kumar Dhar, Saki Kowsar, and Jong-Myon Kim. 2020. "SVD-Based Image Watermarking Using the Fast Walsh-Hadamard Transform, Key Mapping, and Coefficient Ordering for Ownership Protection" Symmetry 12, no. 1: 52. https://doi.org/10.3390/sym12010052
APA StyleKhanam, T., Dhar, P. K., Kowsar, S., & Kim, J.-M. (2020). SVD-Based Image Watermarking Using the Fast Walsh-Hadamard Transform, Key Mapping, and Coefficient Ordering for Ownership Protection. Symmetry, 12(1), 52. https://doi.org/10.3390/sym12010052






