A Review of Blockchain Architecture and Consensus Protocols: Use Cases, Challenges, and Solutions
Abstract
1. Introduction
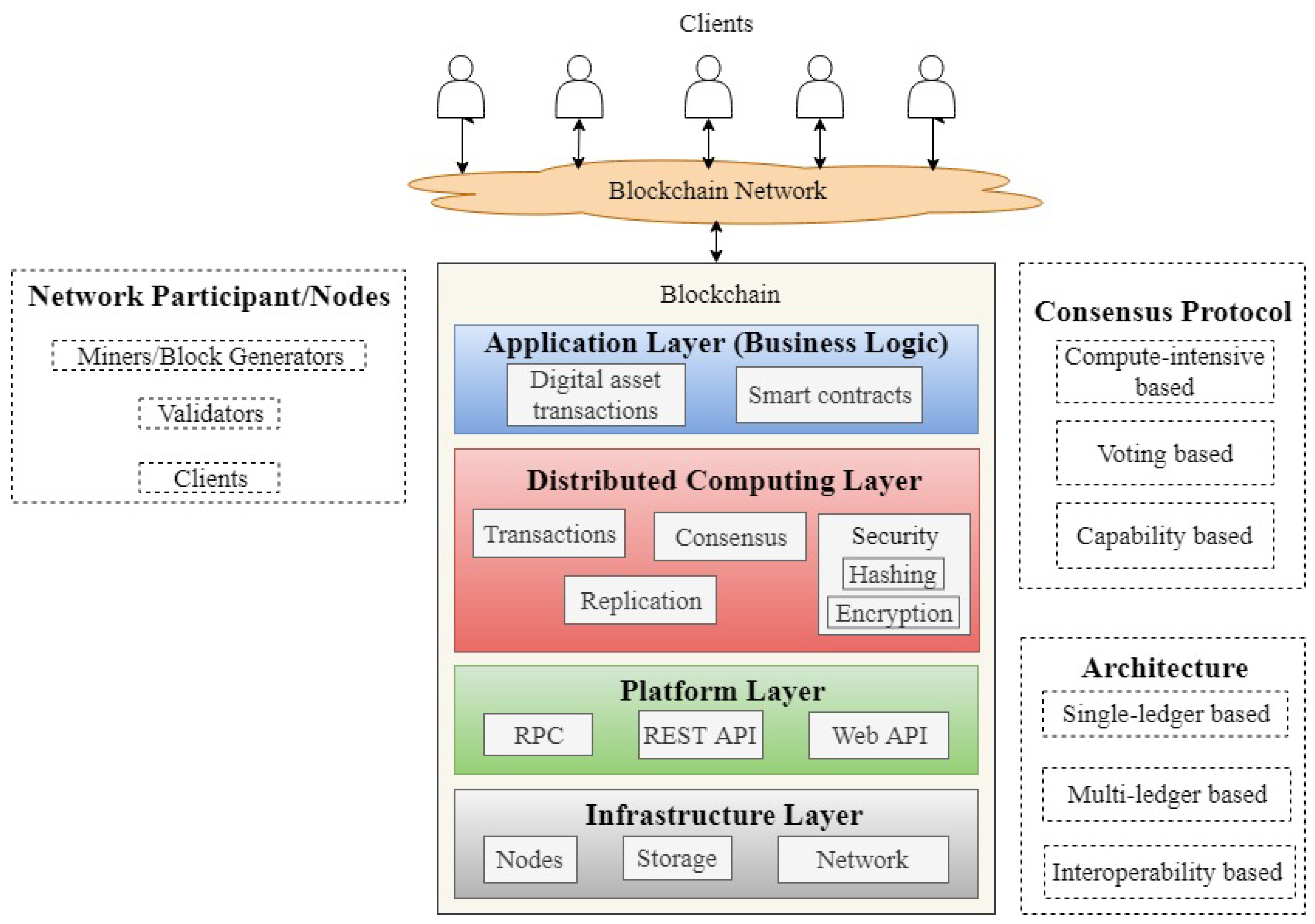
- We present an overview of the blockchain layers and its transaction execution and data flow which are common to all the blockchain architectures.
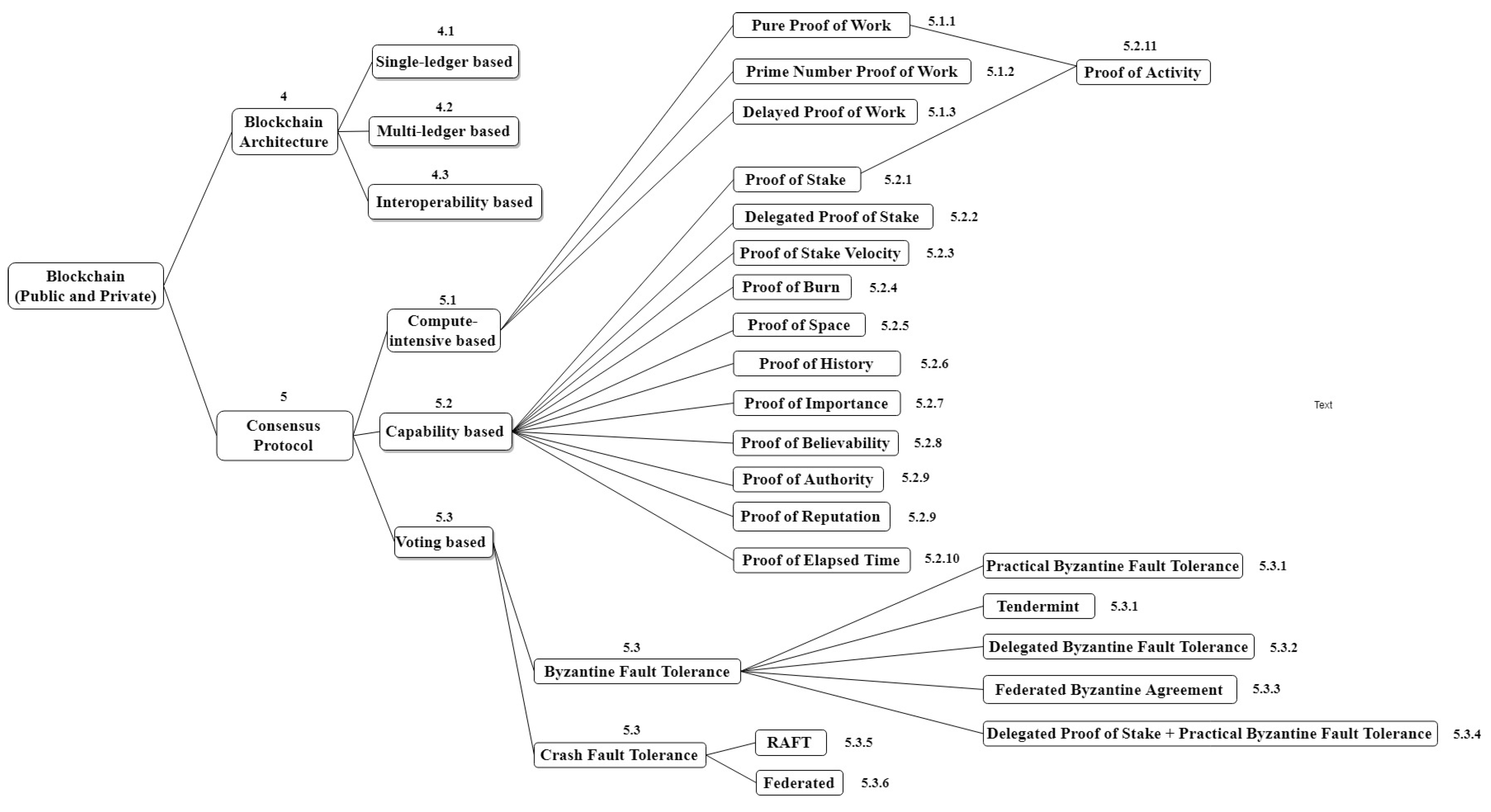
- We classify blockchain platforms architectures into three different types based on the nature of applications using them in terms of number of ledgers and interoperability. A taxonomy of different blockchain architecture mapped to corresponding development platforms is also presented.
- We present the scalable characteristics of each architecture and the security techniques employed.
- We introduce a taxonomy, classification, and comparison between the different consensus protocols used in the blockchain literature.
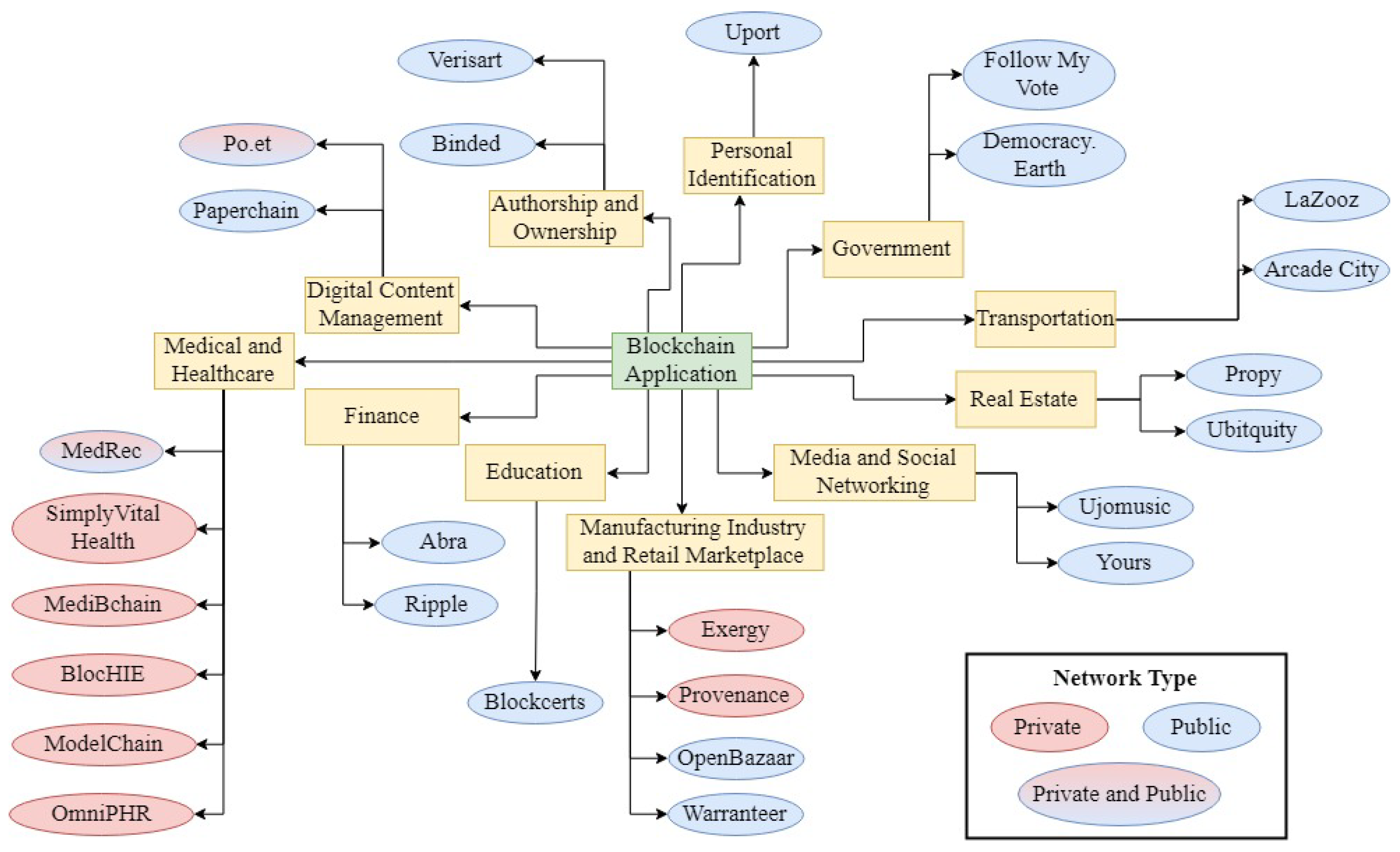
- We describe different existing and upcoming blockchain applications in areas such as medical, finance, education, manufacturing industry and retail marketplace, media, real estate, transportation, government, authorship and ownership, and digital content management.
- We provide critical analysis of the different issues prevailing in blockchain technology and the possible solutions that were proposed for these issues.
- We propose directions toward the development of scalable and energy-efficient blockchain to address the void between the existing blockchain architecture and consensus protocols and the services of the evolving applications.
2. Related Surveys
3. Blockchain: An Architecture Perspective
3.1. Blockchain Overview
- Decentralization: The transactions in blockchain are processed and validated by the consensus of most network nodes. They are replicated on the nodes in a ledger. This eliminates the need for an intermediary to share and maintain the transactions data [1].
- Immutability: The transactions in blockchain are stored into blocks. Each block in the chain is linked to the previous block using a cryptographic hash function. Any attempt to modify the content of a block will affect the subsequent blocks in the chain. Consequently, a malicious attacker needs to change all the succeeding blocks in the chain to modify a particular block, which is computationally difficult because the chained blocks are replicated over multiple nodes.
- Transparency: The ledger is only updated when most of the nodes reach a consensus. Changes in the network are publicly visible ensuring transparency and security.
- Traceability: The distributed and transparent nature of blockchain makes it easier to trace any transaction event. Each update in the state of an asset can be traced down back to its origin. This helps in making the network more secure, efficient and transparent.
- Trustless: Blockchain allows transaction of assets between unknown parties who do not trust each other. By distributing the ledger across several nodes in the network and updating this ledger via a consensus ensures the validity of transactions in an untrusted environment.
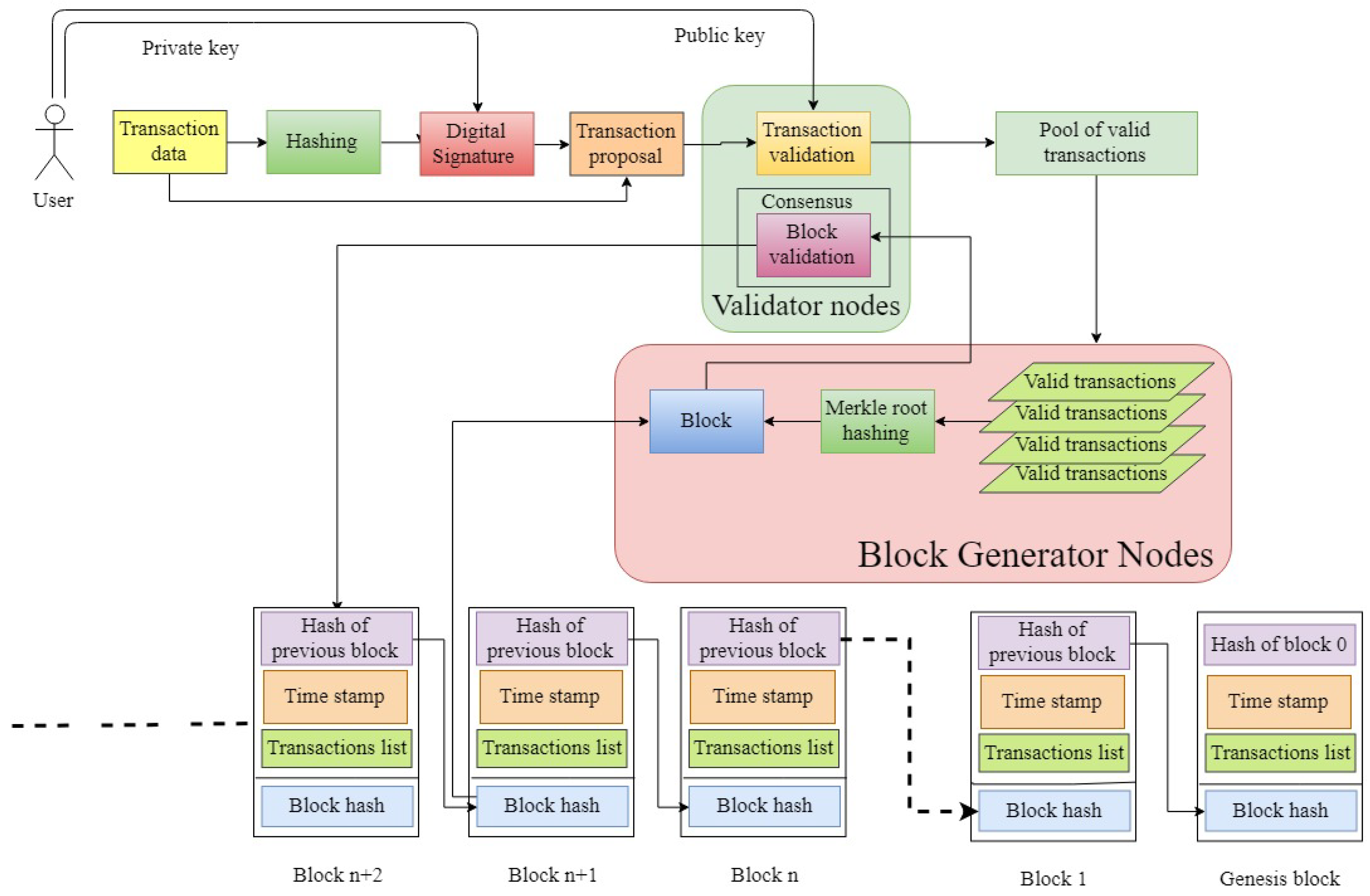
3.2. Transaction Execution Overview
- Transaction: A process that changes the state of the blockchain ledger. Depending on the application, the transaction can be the transfer of a financial value or the execution of a smart contract.
- Block: It consists of a block header and block data. The header consists of the block metadata information such as the Merkle tree root hash, the previous block hash, the timestamp, and the block version, whereas the data consists of a set of valid transactions [1].
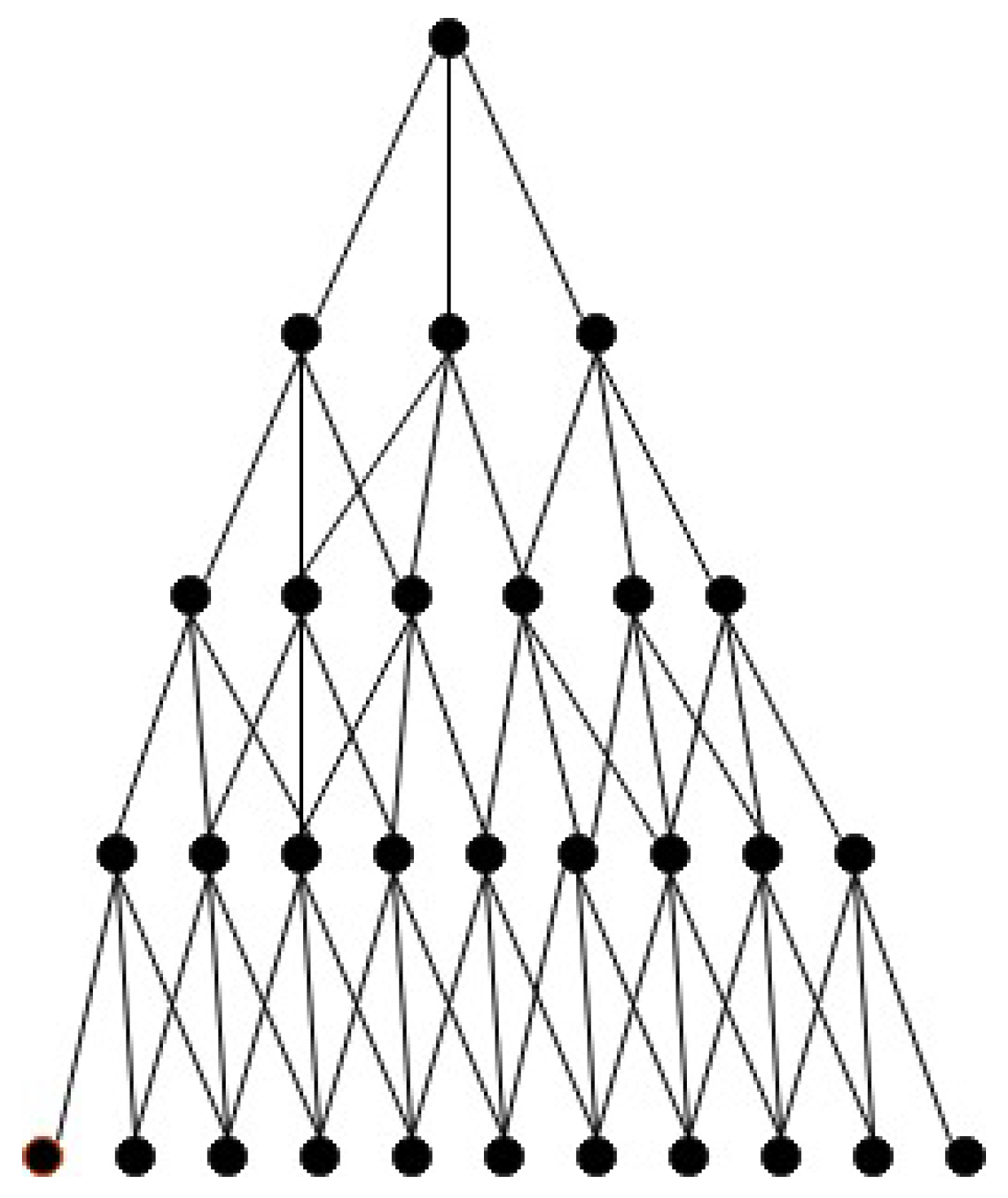
- Merkle tree root hash: All the transactions in the block are hashed individually by using a hashing algorithm. The hash values are then combined pairwise and are hashed again until a single hash value is obtained. This value is known as the Merkle tree root hash value.
- Block hash: It is the unique identifier of a particular block and is obtained by hashing the block header twice [25].
- Previous block hash: It is the hash of the block preceding the current block in the chain. The preceding block is known as the parent of the current block. The use of the previous block hash value in a block header is to ensure the immutability of the blockchain ledger.
- Timestamp: It indicates the time at which the block is created.
- Block version: It indicates the version of the blockchain protocols used.
- Mining: It is the process of adding the valid transactions in a block and broadcasting that block to the network.
- Genesis Block: This is the first block in the ledger. All the following blocks in the chain are linked to the genesis block. The genesis block generally includes the configuration for the network characteristics, the consensus protocol to be used, the access-control rights, the hash function, the block generation interval, and the block size.
- Transaction proposal: The user first hashes the transaction data using a hash function [26] for later verification of data integrity. The hashed data is then encrypted using the user’s private key to provide user authentication and the encrypted output is known as the digital signature of that transaction. The transaction data and the signature are broadcasted to the network.
- Transaction and block validation: Each full node in the network validates the transaction by performing two tasks: (a) user authentication by decrypting the digital signature using the public key of the proposing user, and (b) data integrity by hashing the transaction data and comparing it with the decrypted signature. The valid transaction is broadcasted to the block generators (miners) in the network. A selected miner (based on consensus) verifies the valid transactions and group them in a block in a way that the block size does not exceed a predetermined threshold. The miner computes the Merkle root hash value. The summarized hash of all the transactions by the Merkle root provides an efficient process to verify a transaction in a block. To verify whether a transaction is included in a block or not, a node only requires the hash values of the Merkle path connecting the transaction to the Merkle root. Consequently, a node that does not maintain the entire copy of the ledger can verify a transaction by requiring the path without the need to receive the entire block, reducing communication overhead. To verify a transaction in a block, consisting of n transactions, a node requires only hash values using Merkle root as compared to n hash values if Merkle root is not used [25]. After calculating the Merkle root hash value, the block hash is generated. The miner broadcasts the block to the network. The validating nodes verify the validity of the block by checking the correctness of the followings: (1) the block hash, (2) the block timestamp is greater than the timestamp of the previous block, (3) the block height and size values, (4) the previous block hash value, and (5) the validity of all the transactions in the block. Each validating node appends the valid block to its own copy of the ledger.
3.3. Blockchain Organizational Framework
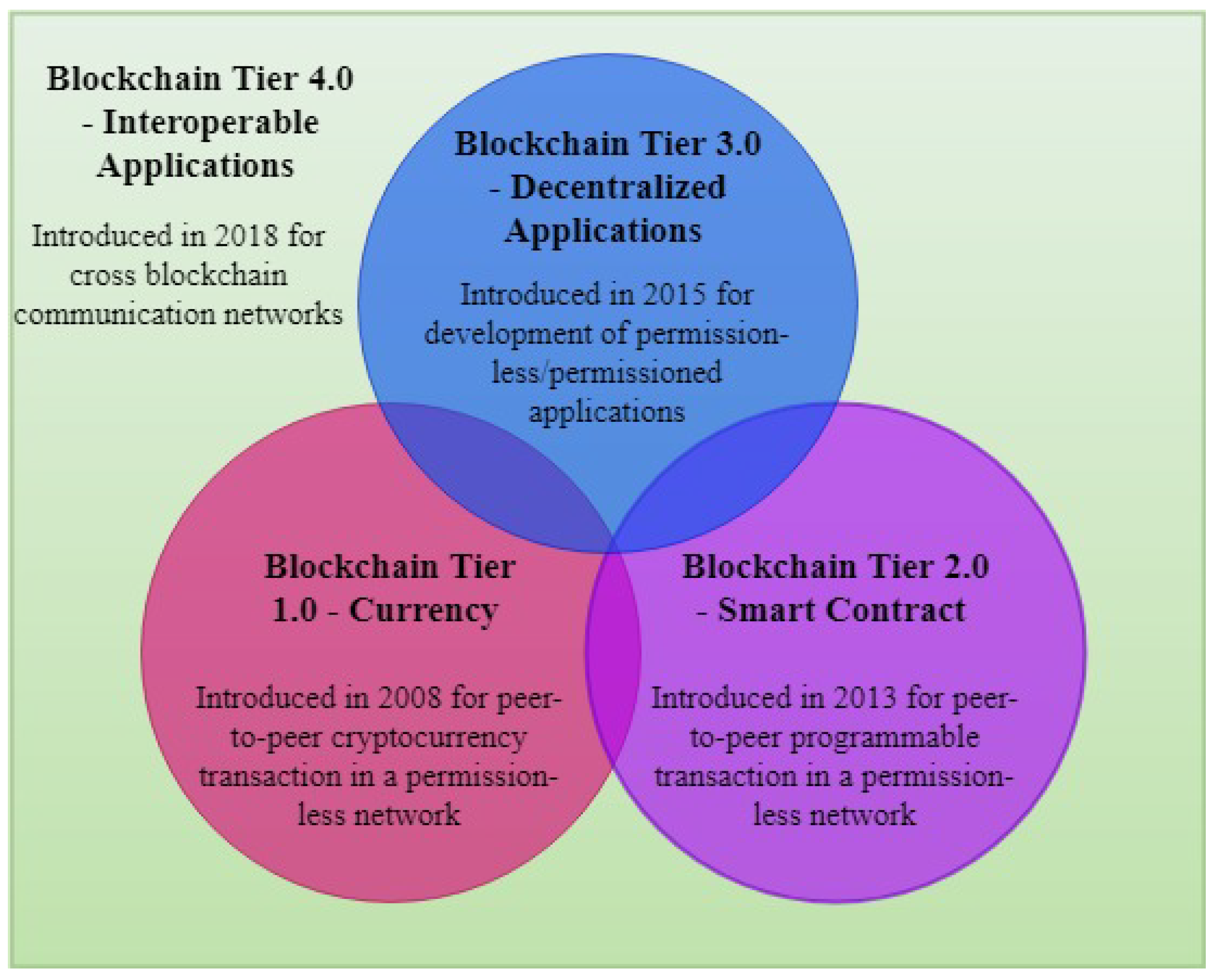
4. Evolution and Taxonomy of Blockchain Architectures
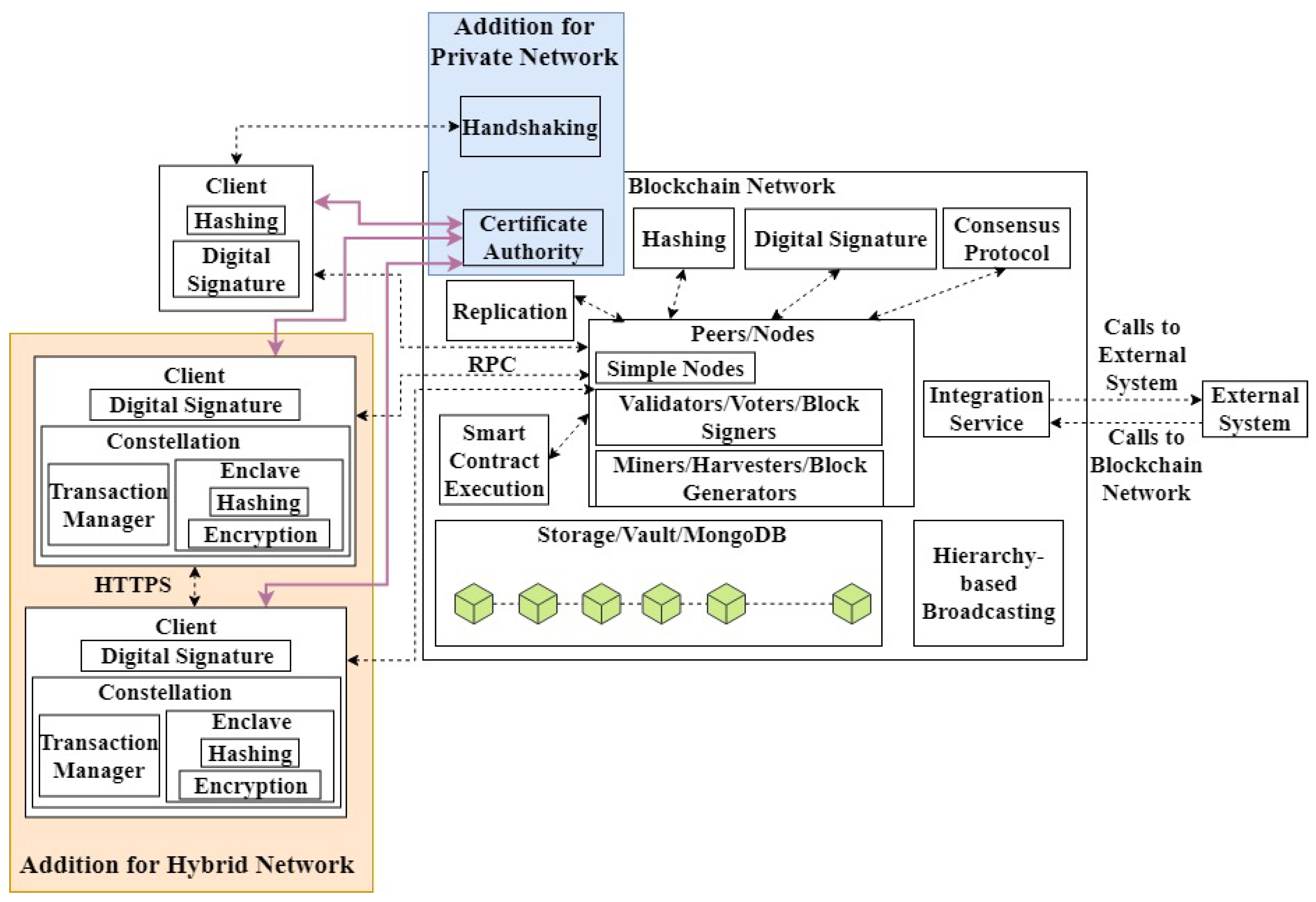
4.1. Single-Ledger-Based Architecture
4.1.1. Single-Ledger-Based Architecture for a Public Network
- A client creates and hashes the transaction payload.
- The digital signature of the hashed payload is generated.
- The transaction payload and the digital signature are broadcasted to the network.
- The transaction is validated by the validators and broadcasted to the miners.
- A block of valid transactions is generated by a selected miner.
- The block is broadcasted to the network.
- The block is verified by the validators and the ledger is updated.
4.1.2. Single-Ledger-Based Architecture for a Private Network
- A transaction initiating node sends a challenge message to the other nodes participating in the transaction.
- The message receiver nodes reply by signing the challenge message by using their private keys.
- The message sender node authenticates the signature by using the receivers’ public keys.
4.1.3. Single-Ledger-Based Architecture for a Hybrid Network
- Participant A (sender) creates and sends the transaction payload to its transaction manager along with the public keys of all the participants involved in the transaction. Let us suppose that participants B and C are the receivers of the transaction.
- The transaction manager of A stores the transaction payload in its local disk and sends the payload to its enclave for encryption.
- Participant A’s enclave encrypts the payload by using a generated symmetric key and hashes the encrypted payload.
- The enclave encrypts the symmetric key using the public key of A, B, and C individually.
- The encrypted payload, its hash, and the encrypted symmetric key are sent to the transaction manager.
- The transaction manager stores the encrypted payload and key by using the hash value as an index. The encrypted payload, the encrypted key by B’s public key, and the hash value are transferred to the transaction manager of B securely via the HyperText Transfer Protocol Secure (HTTPS) [46]. Similarly, the encrypted payload, the encrypted key by C’s public key, and the hash value are transferred to the transaction manager of C.
- The transaction managers of B and C reply with an acknowledgement message to the transaction manager of A.
- Participant A’s transaction manager replaces the payload data in its local disk by the hash value and broadcasts the data to the network.
- The network nodes which receive the hash value lookup for the received hash value in their respective transaction manager. The nodes which find the hash value pass it along with the encrypted payload and the key to their enclaves (B and C in this case).
- The enclave decrypts the symmetric key by using the participant’s private key and then decrypts the transaction payload by using the symmetric key. The decrypted payload is sent to the transaction manager.
- The transaction manager of participants A, B, and C executes the transaction. The nodes which are not part of this transaction skip the broadcasted hash value.
- The transaction is added to the ledger using the hash value.
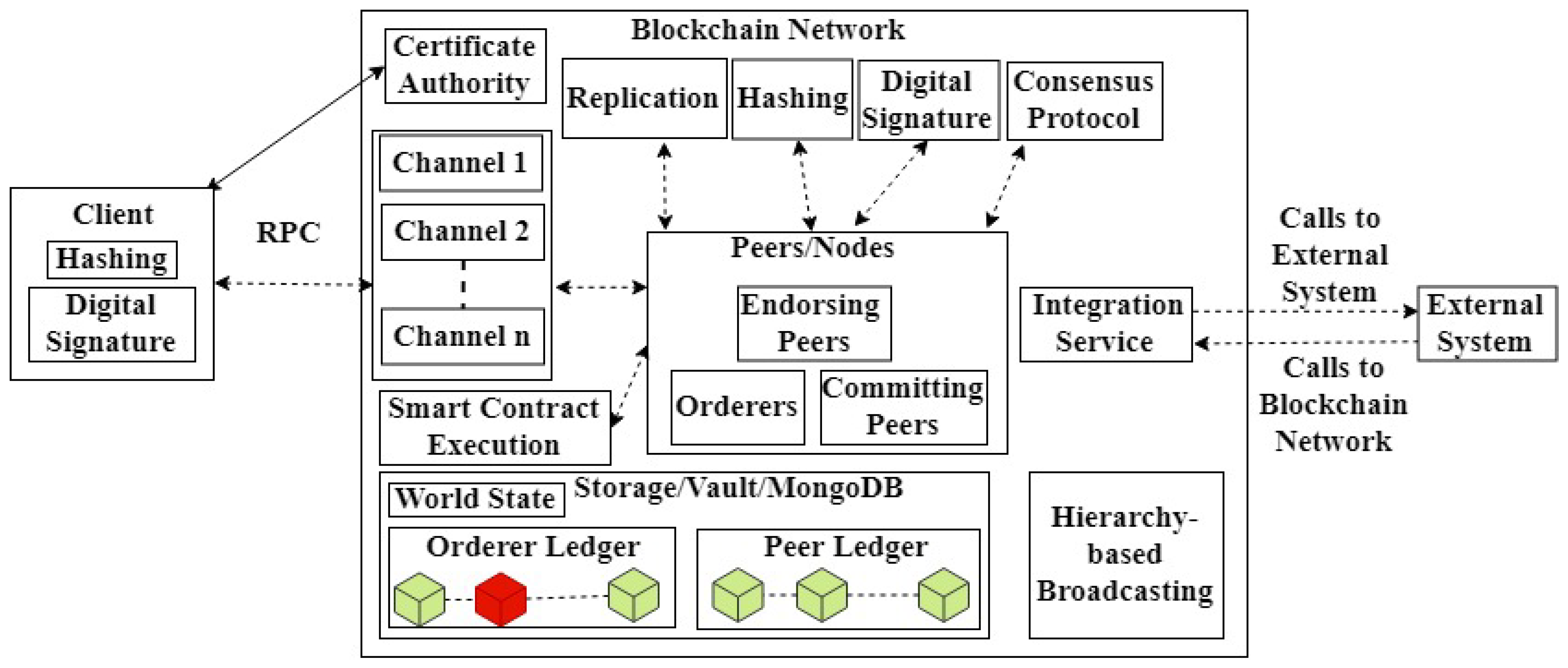
4.2. Multi-Ledger-Based Architecture for a Private Network
- A client creates the transaction payload containing a specific channel to be used for that transaction. The payload is hashed to generate a transaction ID to be used for future references.
- The transaction data is digitally signed and broadcasted to the network. The broadcasted transaction payload is called transaction proposal.
- The transaction payload is validated by the endorsers. Each endorser executes the chain code associated with a valid transaction.
- Each endorser digitally signs the transaction and sends back a proposal response to the client.
- The client waits until a predefined number of proposal responses are received. The client aggregates all the responses and sends them with the transaction to the orderer.
- The orderer generates a block of transactions (valid and invalid) received from the different clients and updates its ledger. It broadcasts the block to the peers in the network.
- Each peer in the network verifies the validity of the transaction in the block. A peer creates a block, called a vblock, of valid transactions (i.e., a transaction which has a threshold of endorsers signatures). The invalid transactions are logged in a file for future reference but are not included in the block.
- The client is notified of the successful execution of the transaction.
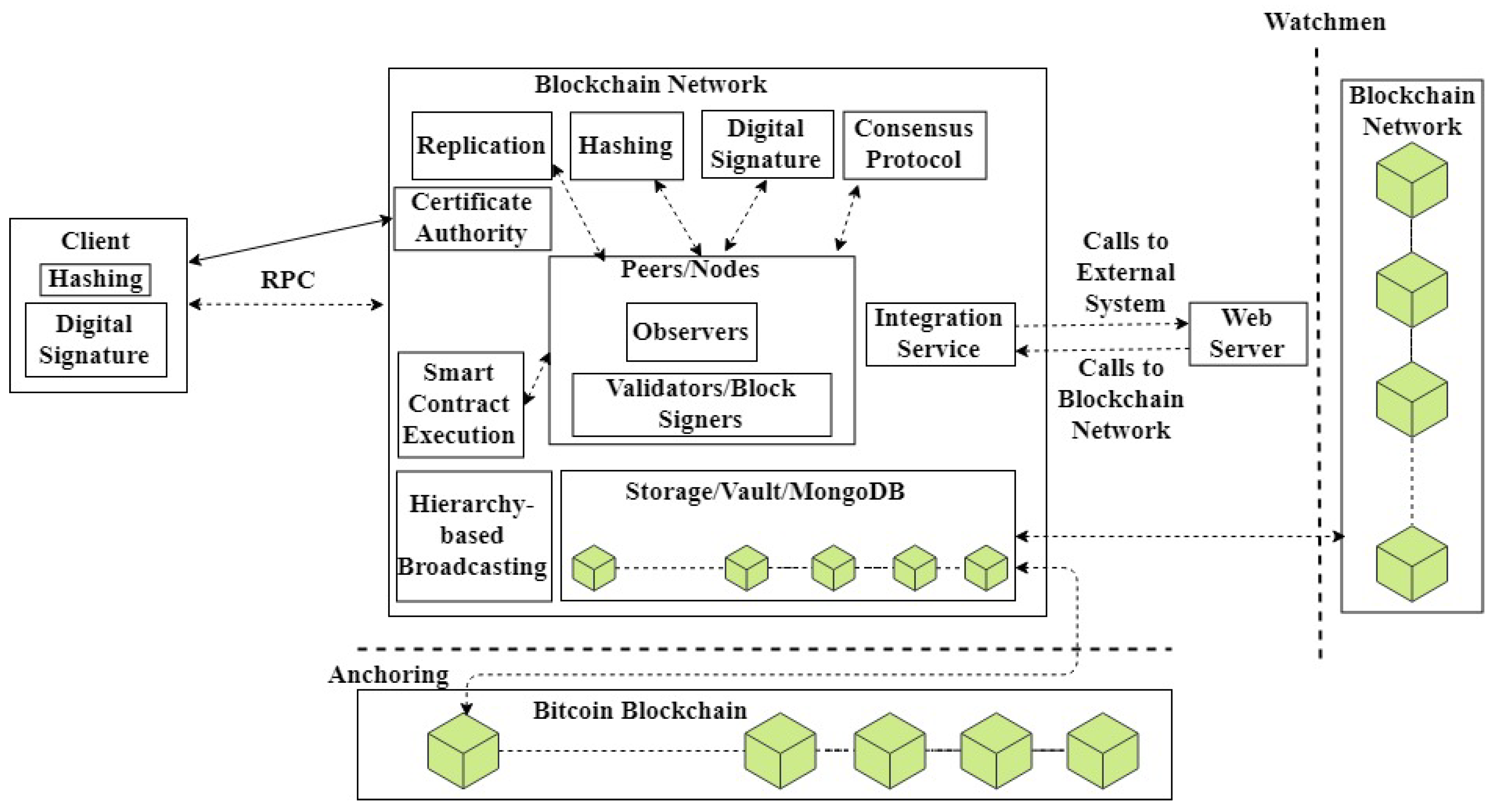
4.3. Interoperability-Based Architecture
- A node issuing a transaction in the first blockchain creates and signs the transaction payload and sends it to Watchmen.
- Watchmen validates the transaction and releases it to the second blockchain.
- A block signer (similar to a miner) in the second blockchain adds this transaction in a block and the ledger is updated after the block was verified.
5. Evolution of Consensus Protocols in Blockchain
5.1. Compute-Intensive Based Consensus Protocols
5.1.1. Pure Proof of Work (PoW)
5.1.2. Prime Number Proof of Work (Prime Number PoW)
5.1.3. Delayed Proof of Work (DPoW)
5.2. Capability-Based Consensus Protocols
5.2.1. Proof of Stake (PoS)
5.2.2. Delegated Proof of Stake (DPoS)
5.2.3. Proof of Stake Velocity (PoSV)
5.2.4. Proof of Burn (PoB)
5.2.5. Proof of Space (PoSpace)
5.2.6. Proof of History (PoH)
5.2.7. Proof of Importance (PoI)
5.2.8. Proof of Believability (PoBelievability)
5.2.9. Proof of Authority (PoAuthority)
5.2.10. Proof of Elapsed Time (PoET)
5.2.11. Proof of Activity (PoA)
5.3. Voting-Based Consensus Protocols
5.3.1. Practical Byzantine Fault Tolerance (PBFT)
5.3.2. Delegated Byzantine Fault Tolerance (DBFT)
5.3.3. Federated Byzantine Agreement (FBA)
5.3.4. Combined Delegated Proof of Stake and Byzantine Fault Tolerance (DPoS+BFT)
5.3.5. Raft
- Leader election: Raft divides time into chunks of arbitrary length known as terms. Each term is consecutively indexed and the election for the leader takes place at the beginning of a term. Initially, a node is in a follower state and continues to receive AppendEntries RPCs from a previous leader. If a node stops receiving the RPC requests from the leader for a specified period of time known as election timeout, the node assumes that there is no leader in the network and begins a new election. To begin a new election, the follower node increments the index of the current term, changes its status to a candidate state, and participates in the election. The candidate votes for itself to be the new leader and simultaneously issues RequestVote RPCs in parallel to all the other nodes. All the other candidates respond to the request by submitting their votes. This is continued until one of the possible outcomes occurs: (i) the candidate wins the election, (ii) another candidate wins the election, or (iii) no candidate is elected in the term.
- (i)
- If the candidate receives the votes from the majority of the nodes in the network, then the candidate wins the election and sends a message to all the other nodes stating its authority as the leader.
- (ii)
- While waiting for the votes, a candidate may receive an authority message from another node claiming to be a leader. The candidate then compares the index value of the current term with that of the node sending the authority message. If the term index of the node is less than that of the candidate, the candidate rejects the message. If the index is more than that of the candidate, the candidate recognizes the node as the leader and changes its state back to a follower.
- (iii)
- If multiple followers begin the election process simultaneously, the votes may split in a no candidate receives the majority of votes. In this case, each candidate times out and starts a new election process by incrementing the term index. To avoid the split of votes in the next election round, each candidate is allotted a random time out and the candidate with the shortest time out begins the election process.
- Log replication: The elected leader starts processing the transactions submitted by the clients. The leader validates each transaction and assigns a transaction index to all the valid transactions to maintain the order of the transactions. The leader creates a block of these transactions and issues an AppendEntries request in parallel to all the followers. The block is replicated by each follower, and an acknowledgement is sent to the leader to confirm the replication.
- Transaction execution: When the leader receives the majority of the acknowledgements from the followers, it executes all the transactions in the block and then notifies the clients regarding the execution. This is known as block commitment. This continues until the term ends.
5.3.6. Federated
6. Service Creation and Innovation Capabilities
6.1. Existing Blockchain Applications
6.1.1. Education
- Blockcerts: The application allows educational institutions to create and issue digital student certificates over the blockchain network. The students and the employees can view the certificates [135,136]. The application makes each individual capable of owning and sharing his/her own digital certificate on a peer-to-peer network. [137] develops a similar application and analyzes its performance within a University network.
6.1.2. Medical and Healthcare
- MedRec: The management of Electronic Health Records (EHRs) has become complex due to scattered medical data of patients moving across different medical organizations. Consequently, it becomes difficult to track patient medical history. MedRec provides easy access and management of EHRs using the blockchain technology [138]. It does not use the ledger for updating the record but encodes the metadata containing the information about ownership, permission and the integrity of the data so that records can be accessed securely.
- SimplyVital Health: Coordinating a patient’s treatment between a team of therapists, practitioners, and specialists is complex when the patient is receiving treatment from multiple healthcare providers. It is difficult to get analytics and insights from the patient data to support better treatment. SimplyVital Health allows different medical experts and organizations to share patient medical data securely over a private blockchain network [139]. The ledger is maintained by the patient’s healthcare providers. The platform uses machine learning algorithms to forecast the best treatment cost for a patient in near real time to aid medical experts and organizations increase their earnings.
- MediBchain: A distributed healthcare data management system that allows patients to update and share their personal health data [140]. The security of the data and the privacy of the patient are achieved by the blockchain characteristics. To tackle the issue of breaching, the data is encrypted before updating the blockchain ledger.
- ModelChain: A blockchain framework to preserve the privacy of medical health data by using machine learning techniques. It involves a scalable proof of information algorithm to determine the order of the online learning process [141].
- OmniPHR: A blockchain healthcare data management architecture to manage the scattered personal health data of patients [142]. The architecture allows patients to update their data using blockchain to have a unified view via access-control rights.
- BlocHIE: A blockchain platform to store and share Electronic Medical Records (EMRs) and Personal Health Data (PHD) [143]. EMRs include the medical reports and diagnostic results prepared for a patient by a health professional whereas, PHD includes the patient data generated from sensors and health monitors. The platform uses two different blockchains to store EMRs and PHD. To reduce the communication overhead, the medical data is stored in a local database by the doctors and the patients and the hash of the data is stored in the blockchain ledger to ensure the privacy and authenticity of the data.
6.1.3. Finance
- Abra: A mobile application that allows users to buy, sell, invest, and trade different digital and fiat currencies [144]. Abra resides in the Bitcoin network, with the miners and the validators maintaining a copy of the ledger. At the time of writing this paper, abra supports 30 different cryptocurrencies and 50 fiat currencies. The fiat currencies are used to buy or trade with cryptocurrencies or other fiat currencies via bank transfer/wire or credit/debit card.
- Ripple: A financial application for currency exchange and remittance for global payment and real-time transaction tracking [130]. Ripple connects different banks and payment providers over the blockchain network for transactions. It allows users to trade assets among each other by using the ripple native currency.
6.1.4. Manufacturing Industry and Retail Marketplace
- Exergy: A private blockchain platform that creates localized energy marketplaces for trading energy across existing grid infrastructures [145]. Exergy allows prosumers to transact the energy they generate using renewable resources in near real time with the consumers on the network creating a more efficient and sustainable community. The participants verify each transaction and maintain a copy of the ledger.
- Provenance: A blockchain platform to help business in developing trust by enhancing immutable and secure supply chain [146]. The network involves the consumers, producers, manufacturers, certifiers and auditors, and registrars. The consumers maintain a copy of the ledger. The consumers can trace and verify the origin, attributes and impact of the product.
- OpenBazaar: A peer-to-peer e-commerce that allows users to create their online store and to sell their products using cryptocurrency [147]. OpenBazaar is a Bitcoin powered marketplace where the users and buyers can trade directly eliminating the third-party fees. No banks or financial organizations are involved as the application does not use fiat currency.
- Warranteer: An application that allows users to save the warranty of their products electronically in a blockchain network [148]. The users upload the warranty of a product using the barcode and get notified for warranty status and expiration. The customers can get direct services from the service providers in case of a product malfunction by interacting with them over the network. Warranteer stores the data in the cloud over the Bitcoin network.
6.1.5. Media and Social Networking
- Ujomusic: A blockchain framework that allows music creators to own the rights of the music they create [149]. A music creator can directly trade a music content with the fans using cryptocurrency. Ujomusic runs over the Ethereum network and has an embedded wallet to pay for the music content in Ethereum’s digital currency.
- Yours: A social networking application to share valuable information with the community [150]. The application runs in the Bitcoin network and has an embedded Bitcoin wallet to pay the content creators and curators for their contributions.
6.1.6. Real Estate
- Ubitquity: A blockchain platform that allows transparent recording and tracking of title and property in the ledger [151]. It involves the property owners, the buyers, the real estate industry, and the government authorities in the network.
- Propy: A blockchain platform for overseas property transactions. The users can sell/buy a property online from any country by using either fiat currency or cryptocurrency [152]. All the documents related to a property transaction are added to the Ethereum network.
6.1.7. Transportation
- Arcade City: An application by which drivers can make local associations for ride-sharing and car-hiring underpinned by the Ethereum platform eliminating the need for a centralized cab service [153]. This would increase the income of the cab drivers by eliminating the intermediary fees by a centralized cab service such as Uber.
- LaZooz: A decentralized transportation platform using vehicles’ unused space to create a variety of smart transportation solutions [154]. LaZooz synchronizes empty seats with transportation needs in real time, matching like-minded people to create a great ride-sharing experience.
6.1.8. Government
- Follow My Vote: An open source blockchain voting system that connects all the voters and authorities [155]. This leads to a transparent election process making it traceable.
- Democracy Earth: An open source blockchain platform to develop decision-making smart contracts for democratic affairs at the state, the country, or the world level, eliminating political intermediaries [156].
6.1.9. Personal Identification
- Uport: A blockchain application for identity management where individuals can take ownership of their identities, running on the Ethereum platform [157]. The application allows users to request and send credentials, and to safely store their keys and data, and sign transactions.
6.1.10. Authorship and Ownership
- Binded: A blockchain copyright application where photographers can protect their images without any fees [158]. The photographers can do the copyright process by themselves without depending on a third party. The network generates a copyright certificate for an image uploaded to the network to ensure ownership in a transparent manner.
- Verisart: A blockchain application to generate tamper-proof digital certificates for artworks and collectables [159]. Verisart helps the artist to protect the artworks by securing them in an immutable blockchain ledger.
6.1.11. Digital Content Management
- Paperchain: A blockchain decentralized marketplace for organizations, content creators, and media companies to monetize their contents and to make them globally available [160].
- Po.et: A blockchain application to record a timestamped immutable information about content creation [161]. The publishers and content creators use the application to prevent content theft.
6.2. Emerging Blockchain Applications
6.2.1. Space
6.2.2. Finance
6.2.3. Education
6.2.4. Internet of Things (IoT)
6.2.5. Governance
7. Blockchain Issues and Possible Solutions
7.1. Scalability
7.2. High Energy Consumption
7.3. Throughput
7.4. Cost and Complexity
7.5. Data Privacy
7.6. Lack of Governance
7.7. Standardization and Interoperability
7.8. Access to External Data
- How to ensure the reliability of the external data?
- How to reach consensus in case some of the nodes cannot reach the external data source due to network connectivity issues or if the data source becomes unavailable?
- Who will govern the third-party data sources?
8. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Zheng, Z.; Xie, S.; Dai, H.N.; Wang, H. Blockchain challenges and opportunities: A survey. Int. J. Web Grid Serv. 2018, 14, 352–375. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-To-Peer Electronic Cash System. 2008. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 22 September 2019).
- Bitcoin Mining Consumes More Electricity a Year than Ireland|Technology|The Guardian. Available online: https://www.theguardian.com/technology/2017/nov/27/bitcoin-mining-consumes-electricity-ireland (accessed on 8 January 2019).
- Stoll, C.; Klaaßen, L.; Gallersdörfer, U. The Carbon Footprint of Bitcoin. Joule 2019. [Google Scholar] [CrossRef]
- Ahamad, S.; Nair, M.; Varghese, B. A survey on crypto currencies. In Proceedings of the 4th International Conference on Advances in Computer Science, AETACS, NCR, India, 13–14 December 2013; pp. 42–48. [Google Scholar]
- Tschorsch, F.; Scheuermann, B. Bitcoin and Beyond: A Technical Survey on Decentralized Digital Currencies. IEEE Commun. Surv. Tutor. 2016, 18, 2084–2123. [Google Scholar] [CrossRef]
- Shen, C.; Pena-Mora, F. Blockchain for Cities—A Systematic Literature Review. IEEE Access 2018, 6, 76787–76819. [Google Scholar] [CrossRef]
- Al-Jaroodi, J.; Mohamed, N. Blockchain in Industries: A Survey. IEEE Access 2019, 7, 36500–36515. [Google Scholar] [CrossRef]
- Jaoude, J.A.; Saade, R.G. Blockchain Applications—Usage in Different Domains. IEEE Access 2019, 7, 45360–45381. [Google Scholar] [CrossRef]
- Hölbl, M.; Kompara, M.; Kamišalić, A.; Nemec Zlatolas, L. A systematic review of the use of blockchain in healthcare. Symmetry 2018, 10, 470. [Google Scholar] [CrossRef]
- Conoscenti, M.; Vetro, A.; De Martin, J.C. Blockchain for the Internet of Things: A systematic literature review. In Proceedings of the 2016 IEEE/ACS 13th International Conference of Computer Systems and Applications (AICCSA), Agadir, Morocco, 29 November–2 December 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–6. [Google Scholar]
- Karafiloski, E.; Mishev, A. Blockchain solutions for big data challenges: A literature review. In Proceedings of the IEEE EUROCON 2017—17th International Conference on Smart Technologies, Ohrid, Macedonia, 6–8 July 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 763–768. [Google Scholar]
- Yli-Huumo, J.; Ko, D.; Choi, S.; Park, S.; Smolander, K. Where is current research on blockchain technology?—A systematic review. PLoS ONE 2016, 11, e0163477. [Google Scholar] [CrossRef] [PubMed]
- Li, X.; Jiang, P.; Chen, T.; Luo, X.; Wen, Q. A survey on the security of blockchain systems. Future Gener. Comput. Syst. 2017. [Google Scholar] [CrossRef]
- Feng, Q.; He, D.; Zeadally, S.; Khan, M.K.; Kumar, N. A survey on privacy protection in blockchain system. J. Netw. Comput. Appl. 2019, 126, 45–58. [Google Scholar] [CrossRef]
- Park, J.; Park, J. Blockchain security in cloud computing: Use cases, challenges, and solutions. Symmetry 2017, 9, 164. [Google Scholar] [CrossRef]
- Mukhopadhyay, U.; Skjellum, A.; Hambolu, O.; Oakley, J.; Yu, L.; Brooks, R. A brief survey of Cryptocurrency systems. In Proceedings of the 2016 14th Annual Conference on Privacy, Security and Trust (PST), Auckland, New Zealand, 12–14 December 2016; pp. 745–752. [Google Scholar] [CrossRef]
- Nguyen, T.; Kim, K. A survey about consensus algorithms used in Blockchain. J. Inf. Process. Syst. 2018, 14, 101–128. [Google Scholar] [CrossRef]
- Wahab, A.; Mehmood, W. Survey of Consensus Protocols. arXiv 2018, arXiv:1810.03357. [Google Scholar]
- Remote Procedure Call—Wikipedia. Available online: https://en.wikipedia.org/wiki/Remote_procedure_call (accessed on 13 January 2019).
- Web API—Wikipedia. Available online: https://en.wikipedia.org/wiki/Web_API (accessed on 13 January 2019).
- Representational State Transfer—Wikipedia. Available online: https://en.wikipedia.org/wiki/Representational_state_transfer (accessed on 13 January 2019).
- Merkle, R.C. A Digital Signature Based on a Conventional Encryption Function. In Proceedings of the Conference on the Theory and Applications of Cryptographic Techniques on Advances in Cryptology, CRYPTO ’87, Santa Barbara, CA, USA, 23–27 August 1988; Springer: London, UK, 1988; pp. 369–378. [Google Scholar]
- Swan, M. Blockchain: Blueprint for a New Economy; O’Reilly Media, Inc.: Newton, MA, USA, 2015. [Google Scholar]
- Antonopoulos, A.M. Mastering Bitcoin: Unlocking Digital Cryptocurrencies; O’Reilly Media, Inc.: Newton, MA, USA, 2014. [Google Scholar]
- Secure Hash Algorithms. Available online: https://en.wikipedia.org/wiki/Secure_Hash_Algorithms (accessed on 7 January 2019).
- Brewer, E. CAP twelve years later: How the“ rules” have changed. Computer 2012, 45, 23–29. [Google Scholar] [CrossRef]
- Girault, A.; Gössler, G.; Guerraoui, R.; Hamza, J.; Seredinschi, D.A. Why You Can’t Beat Blockchains: Consistency and High Availability in Distributed Systems. arXiv 2017, arXiv:1710.09209. [Google Scholar]
- Decker, C.; Wattenhofer, R. Information propagation in the bitcoin network. In Proceedings of the 2013 IEEE Thirteenth International Conference on Peer-to-Peer Computing (P2P), Trento, Italy, 9–11 September 2013; IEEE: Piscataway, NJ, USA, 2013; pp. 1–10. [Google Scholar]
- Szabo, N. Smart contracts: Building blocks for digital markets. Extropy J. Transhumanist Thought 1996, 18, 2. [Google Scholar]
- Seele: Blockchain 4.0 or Marketing?—CoinAnnouncer. Available online: https://www.coinannouncer.com/seele-blockchain-4-0-or-marketing/ (accessed on 3 January 2019).
- Pseudonymity. Available online: https://en.wikipedia.org/wiki/Pseudonymity (accessed on 18 January 2019).
- Joshi, A.P.; Han, M.; Wang, Y. A survey on security and privacy issues of blockchain technology. Math. Found. Comput. 2018, 1, 121–147. [Google Scholar] [CrossRef]
- Buterin, V. A Next-Generation Smart Contract and Decentralized Application Platform—White Paper. 2014. Available online: http://blockchainlab.com/pdf/Ethereum_white_paper-a_next_generation_smart_contract_and_decentralized_application_platform-vitalik-buterin.pdf (accessed on 22 September 2019).
- Lai, R.; Chuen, D.L.K. Blockchain—From public to private. In Handbook of Blockchain, Digital Finance, and Inclusion; Elsevier: Amsterdam, The Netherlands, 2018; Volume 2, pp. 145–177. [Google Scholar]
- Greenspan, G. MultiChain Private Blockchain—White Paper. 2015. Available online: http://www.multichain.com/download/MultiChain-White-Paper.pdf (accessed on 22 September 2019).
- Hyperledger Burrow. Available online: https://www.hyperledger.org/projects/hyperledger-burrow (accessed on 29 December 2018).
- Chain Core. Available online: https://chain.com/docs/1.2/core/get-started/introduction (accessed on 29 December 2018).
- Introduction—Sawtooth. Available online: https://sawtooth.hyperledger.org/docs/core/releases/1.0/introduction.html (accessed on 29 December 2018).
- GitHub—HydraChain/hydrachain: Permissioned Distributed Ledger based on Ethereum. Available online: https://github.com/HydraChain/hydrachain (accessed on 3 January 2019).
- Hyperledger Iroha—Hyperledger. Available online: https://www.hyperledger.org/projects/iroha (accessed on 29 December 2018).
- The Burst Dymaxion. Available online: https://www.burst-coin.org/wp-content/uploads/2017/07/The-Burst-Dymaxion-1.00.pdf (accessed on 16 January 2019).
- NEM White Paper. Available online: https://nem.io/wp-content/themes/nem/files/NEM_techRef.pdf (accessed on 16 January 2019).
- McConaghy, T.; Marques, R.; Müller, A.; De Jonghe, D.; McConaghy, T.; McMullen, G.; Henderson, R.; Bellemare, S.; Granzotto, A. BigchainDB: A Scalable Blockchain Database. White Paper, BigChainDB. 2016. Available online: https://www.bigchaindb.com/whitepaper/ (accessed on 22 September 2019).
- Quorum Overview. Available online: https://github.com/jpmorganchase/quorum/wiki/Quorum-Overview (accessed on 30 December 2018).
- Durumeric, Z.; Kasten, J.; Bailey, M.; Halderman, J.A. Analysis of the HTTPS certificate ecosystem. In Proceedings of the 2013 conference on Internet Measurement Conference, Barcelona, Spain, 23–25 October 2013; ACM: New York, NY, USA, 2013; pp. 291–304. [Google Scholar]
- Potlapally, N.R.; Ravi, S.; Raghunathan, A.; Jha, N.K. Analyzing the energy consumption of security protocols. In Proceedings of the 2003 international symposium on Low Power Electronics and Design, Seoul, Korea, 25–27 August 2003; ACM: New York, NY, USA, 2003; pp. 30–35. [Google Scholar]
- Androulaki, E.; Barger, A.; Bortnikov, V.; Cachin, C.; Christidis, K.; De Caro, A.; Enyeart, D.; Ferris, C.; Laventman, G.; Manevich, Y.; et al. Hyperledger Fabric: A Distributed Operating System for Permissioned Blockchains. In Proceedings of the Thirteenth EuroSys Conference, EuroSys ’18, Porto, Portugal, 23–26 April 2018; ACM: New York, NY, USA, 2018; pp. 30:1–30:15. [Google Scholar] [CrossRef]
- Hyperledger Fabric—Hyperledger. Available online: https://www.hyperledger.org/projects/fabric (accessed on 29 December 2018).
- Channels. Available online: https://hyperledger-fabric.readthedocs.io/en/release-1.3/channels.html (accessed on 29 December 2018).
- Thakkar, P.; Nathan, S.; Vishwanathan, B. Performance Benchmarking and Optimizing Hyperledger Fabric Blockchain Platform. arXiv 2018, arXiv:1805.11390. [Google Scholar]
- Blockchain Platform|Oracle Cloud. Available online: https://cloud.oracle.com/en_US/blockchain (accessed on 14 January 2019).
- Credits White Paper. Available online: https://credits.com/Content/Docs/TechnicalWhitePaperCREDITSEng.pdf (accessed on 29 December 2018).
- LZ77. Available online: https://en.wikipedia.org/wiki/LZ77_and_LZ78 (accessed on 29 December 2018).
- Huffman Coding. Available online: https://en.wikipedia.org/wiki/Huffman_coding (accessed on 29 December 2018).
- Dorri, A.; Kanhere, S.S.; Jurdak, R. Towards an optimized blockchain for IoT. In Proceedings of the Second International Conference on Internet-of-Things Design and Implementation, Pittsburgh, PA, USA, 18–21 April 2017; ACM: New York, NY, USA, 2017; pp. 173–178. [Google Scholar]
- Kousaridas, A.; Falangitis, S.; Magdalinos, P.; Alonistioti, N.; Dillinger, M. SYSTAS: Density-based algorithm for clusters discovery in wireless networks. In Proceedings of the 2015 IEEE 26th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Hong Kong, China, 30 August–2 September 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 2126–2131. [Google Scholar]
- Elements|elementsproject.org. Available online: https://elementsproject.org/ (accessed on 31 December 2018).
- Overview of Openchain. Available online: https://docs.openchain.org/en/latest/general/overview.html (accessed on 29 December 2018).
- Home|Lisk Documentation. Available online: https://lisk.io/documentation/home (accessed on 14 January 2019).
- Quorum White Paper. Available online: https://github.com/jpmorganchase/quorum-docs/blob/master/Quorum%20Whitepaper%20v0.1.pdf (accessed on 30 December 2018).
- Dwork, C.; Naor, M. Pricing via Processing or Combatting Junk Mail. In Proceedings of the 12th Annual International Cryptology Conference on Advances in Cryptology, CRYPTO ’92, Santa Barbara, CA, USA, 16–20 August 1992; Springer: London, UK, 1993; pp. 139–147. [Google Scholar]
- Back, A. Hashcash—A Denial of Service Counter-Measure. 2002. Available online: http://www.hashcash.org/hashcash.pdf (accessed on 22 September 2016).
- Brute-Force Search—Wikipedia. Available online: https://en.wikipedia.org/wiki/Brute-force_search (accessed on 18 January 2019).
- Eastlake, D.; Jones, P. US Secure Hash Algorithm (SHA1); Technical Report, RFC Editor; 2001. Available online: http://www.faqs.org/rfcs/rfc3174.html (accessed on 22 September 2019).
- Hashcash—Wikipedia. Available online: https://en.wikipedia.org/wiki/Hashcash (accessed on 18 December 2018).
- U.S. Department of Commerce; National Institute of Standards and Technology. Secure Hash Standard. 2012. Available online: https://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.180-4.pdf (accessed on 22 September 2019).
- Bitcoin—Wikipedia. Available online: https://en.wikipedia.org/wiki/Bitcoin (accessed on 8 January 2019).
- The Mystery Behind Block Time—FACILELOGIN. Available online: https://medium.facilelogin.com/the-mystery-behind-block-time-63351e35603a (accessed on 18 December 2018).
- Gervais, A.; Karame, G.O.; Wüst, K.; Glykantzis, V.; Ritzdorf, H.; Capkun, S. On the security and performance of proof of work blockchains. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; ACM: New York, NY, USA, 2016; pp. 3–16. [Google Scholar]
- Schrijvers, O.; Bonneau, J.; Boneh, D.; Roughgarden, T. Incentive compatibility of bitcoin mining pool reward functions. In Proceedings of the International Conference on Financial Cryptography and Data Security, Christ Church, Barbados, 22–26 February 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 477–498. [Google Scholar]
- Kroll, J.A.; Davey, I.C.; Felten, E.W. The economics of Bitcoin mining, or Bitcoin in the presence of adversaries. In Proceedings of the Twelfth Workshop on the Economics of Information Security (WEIS 2013), Washington, DC, USA, 11–12 June 2013; Available online: https://www.econinfosec.org/archive/weis2013/papers/KrollDaveyFeltenWEIS2013.pdf (accessed on 22 September 2019).
- Conti, M.; Kumar, E.S.; Lal, C.; Ruj, S. A Survey on Security and Privacy Issues of Bitcoin. IEEE Commun. Surv. Tutor. 2018, 20, 3416–3452. [Google Scholar] [CrossRef]
- Bitcoin Energy Consumption Index—Digiconomist. Available online: https://digiconomist.net/bitcoin-energy-consumption (accessed on 8 January 2019).
- Litecoin—Open Source P2P Digital Currency. Available online: https://litecoin.org/ (accessed on 18 December 2018).
- Dogecoin. Available online: https://dogecoin.com/ (accessed on 18 December 2018).
- King, S. Primecoin: Cryptocurrency with prime number proof-of-work. July 7th 2013, 1, 6. [Google Scholar]
- Ingham, A.E.; Ingham, A.E. The Distribution of Prime Numbers; Number 30; Cambridge University Press: Cambridge, UK, 1990. [Google Scholar]
- Young, A.; Yung, M. Finding length-3 positive cunningham chains and their cryptographic significance. In Proceedings of the International Algorithmic Number Theory Symposium, Portland, OR, USA, 21–25 June 1998; Springer: Berlin/Heidelberg, Germany, 1998; pp. 289–298. [Google Scholar]
- Forbes, T. Prime clusters and Cunningham chains. Math. Comput. Am. Math. Soc. 1999, 68, 1739–1747. [Google Scholar] [CrossRef][Green Version]
- Ribenboim, P. The New Book of Prime Number Records; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Cladwell, C. Fermat Primality Test. Available online: https://primes.utm.edu/prove/prove2_1.html (accessed on 10 January 2019).
- lifchitz, H. Generalization of Euler-Lagrange Theorem and New Primality Tests. Available online: http://www.primenumbers.net/Henri/us/NouvTh1us.htm (accessed on 10 January 2019).
- Primecoin. Available online: http://primecoin.io/ (accessed on 10 January 2019).
- Komodo White Paper. Available online: https://komodoplatform.com/wp-content/uploads/2018/05/2018-05-09-Komodo-White-Paper-Full.pdf (accessed on 25 January 2019).
- Confirmation—Bitcoin Wiki. Available online: https://en.bitcoin.it/wiki/Confirmation (accessed on 24 January 2019).
- Proof of Stake Instead of Proof of Work. Available online: https://bitcointalk.org/index.php?topic=27787.0 (accessed on 10 January 2019).
- King, S.; Nadal, S. PPCoin: Peer-to-Peer Crypto-Currency with Proof-of-Stake. 2018. Available online: https://decred.org/research/king2012.pdf (accessed on 22 September 2019).
- Whitepaper:Nxt—Nxt Wiki. Available online: http://nxtwiki.org/wiki/Whitepaper:Nxt (accessed on 10 January 2019).
- Larimer, D. Delegated Proof-of-Stake Consensus. 2014. Available online: https://bitshares.org/technology/delegated-proof-of-stake-consensus (accessed on 23 January 2019).
- bitshares.foundation/BitSharesBlockchain.pdf at master · bitshares-foundation/bitshares.foundation · GitHub. Available online: https://github.com/bitshares-foundation/bitshares.foundation/blob/master/download/articles/BitSharesBlockchain.pdf (accessed on 23 January 2019).
- Nano—An Instant, Zero-Fee, Scalable Currency. Available online: https://nano.org/en (accessed on 23 January 2019).
- Cardano—Home of the Ada Cryptocurrency and Technological Platform. Available online: https://www.cardano.org/en/home/ (accessed on 23 January 2019).
- Ren, L. Proof of Stake Velocity: Building the Social Currency of the Digital Age. 2014. Available online: https://www.reddcoin.com/papers/PoSV.pdf (accessed on 22 September 2019).
- Reddcoin Social Currency—Official Website. Available online: https://reddcoin.com/ (accessed on 10 January 2019).
- Proof of Burn—Bitcoin Wiki. Available online: https://en.bitcoin.it/wiki/Proof_of_burn (accessed on 10 January 2019).
- Slimcoin Whitepaper. Available online: http://www.doc.ic.ac.uk/~ids/realdotdot/crypto_papers_etc_worth_reading/proof_of_burn/slimcoin_whitepaper.pdf (accessed on 10 January 2019).
- Slimcoin|A Cryptocurrency for the Long Term. Available online: http://slimco.in/ (accessed on 10 January 2019).
- TGcoin. Available online: https://trade.tgco.in/ (accessed on 10 January 2019).
- Dziembowski, S.; Faust, S.; Kolmogorov, V.; Pietrzak, K. Proofs of space. In Proceedings of the Annual Cryptology Conference, Santa Barbara, CA, USA, 16–20 August 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 585–605. [Google Scholar]
- Bresson, E.; Canteaut, A.; Chevallier-Mames, B.; Clavier, C.; Fuhr, T.; Gouget, A.; Icart, T.; Misarsky, J.F.; Naya-Plasencia, M.; Paillier, P.; et al. Shabal, a Submission to NIST’s Cryptographic Hash Algorithm Competition. 2008. Available online: https://www.cs.rit.edu/~ark/20090927/Round2Candidates/Shabal.pdf (accessed on 22 September 2019).
- Space Coin. Available online: http://spacecoin.info/ (accessed on 10 January 2019).
- Home—Chia Network. Available online: https://chia.net/ (accessed on 10 January 2019).
- Burstcoin—The Linux of Blockchain. Available online: https://www.burst-coin.org/ (accessed on 10 January 2019).
- Solana: A New Architecture for a High Performance Blockchain. Available online: https://solana.com/solana-whitepaper.pdf (accessed on 11 January 2019).
- Proof of Importance. Available online: https://nem.io/xem/harvesting-and-poi/ (accessed on 18 January 2019).
- Proof of Believability. Available online: https://github.com/iost-official/Documents/blob/master/Technical_White_Paper/EN/Tech_white_paper_EN.md (accessed on 18 January 2019).
- IOST—UNLEASHING THE POWER OF BLOCKCHAIN. Available online: https://iost.io/ (accessed on 18 January 2019).
- Proof-of-Authority—Wikipedia. Available online: https://en.wikipedia.org/wiki/Proof-of-authority (accessed on 23 January 2019).
- Wiki/Proof-of-Authority-Chains.md at Master · paritytech/wiki · GitHub. Available online: https://github.com/paritytech/wiki/blob/master/Proof-of-Authority-Chains.md (accessed on 23 January 2019).
- POA Network: Public Ethereum Sidechain with Proof of Autonomy Consensus by Independent Validators. Available online: https://poa.network/ (accessed on 23 January 2019).
- Gochain-Whitepaper. Available online: https://gochain.io/gochain-whitepaper-v2.1.2.pdf (accessed on 23 January 2019).
- Menlo One—Tools that Make Blockchain Work for Business. Available online: https://www.menlo.one/ (accessed on 23 January 2019).
- The Second Coming of Blockchain|Intel® Software. Available online: https://software.intel.com/en-us/blogs/2017/02/14/the-second-coming-of-blockchain (accessed on 18 December 2018).
- Sabt, M.; Achemlal, M.; Bouabdallah, A. Trusted Execution Environment: What It is, and What It is Not. In Proceedings of the 2015 IEEE Trustcom/BigDataSE/ISPA, Helsinki, Finland, 20–22 August 2015; Volume 1, pp. 57–64. [Google Scholar] [CrossRef]
- Intel SGX Homepage|Intel® Software. Available online: https://software.intel.com/en-us/sgx (accessed on 18 December 2018).
- Chen, L.; Xu, L.; Shah, N.; Gao, Z.; Lu, Y.; Shi, W. On Security Analysis of Proof-of-Elapsed-Time (PoET); Springer: Cham, Switzerland, 2017. [Google Scholar]
- Chen, L.; Xu, L.; Shah, N.; Gao, Z.; Lu, Y.; Shi, W. On security analysis of proof-of-elapsed-time (poet). In Proceedings of the International Symposium on Stabilization, Safety, and Security of Distributed Systems, Boston, MA, USA, 5–8 November 2017; Springer: Piscataway, NJ, USA, 2017; pp. 282–297. [Google Scholar]
- Hardin, G. The tragedy of the commons. Science 1968, 162, 1243–1248. [Google Scholar] [PubMed]
- Bentov, I.; Lee, C.; Mizrahi, A.; Rosenfeld, M. Proof of activity: Extending bitcoin’s proof of work via proof of stake [extended abstract] y. ACM Sigmetrics Perform. Eval. Rev. 2014, 42, 34–37. [Google Scholar] [CrossRef]
- Decred—Autonomous Digital Currency. Available online: https://www.decred.org/ (accessed on 11 January 2019).
- Driscoll, K.; Hall, B.; Sivencrona, H.; Zumsteg, P. Byzantine fault tolerance, from theory to reality. In Proceedings of the International Conference on Computer Safety, Reliability, and Security, Edinburgh, UK, 23–26 September 2003; Springer: Piscataway, NJ, USA; 2003; pp. 235–248. [Google Scholar]
- Lamport, L.; Shostak, R.; Pease, M. The Byzantine generals problem. ACM Trans. Program. Lang. Syst. (TOPLAS) 1982, 4, 382–401. [Google Scholar] [CrossRef]
- Castro, M.; Liskov, B. Practical Byzantine fault tolerance. In Proceedings of the 3rd Symposium on Operating System Design and Implementation (OSDI), New Orleans, LA, USA, February 1999; Unisex Association: Berkeley, CA, USA, 1999; pp. 173–186. [Google Scholar]
- Kwon, J. Tendermint: Consensus without mining. Draft v. 0.6, fall 2014, 1, 11. [Google Scholar]
- Vukolić, M. The quest for scalable blockchain fabric: Proof-of-work vs. BFT replication. In Proceedings of the International Workshop on Open Problems in Network Security, Zurich, Switzerland, 29 October 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 112–125. [Google Scholar]
- Douceur, J.R. The sybil attack. In Proceedings of the International Workshop on Peer-to-Peer Systems, Cambridge, MA, USA, 7–8 March 2002; Springer: Berlin/Heidelberg, Germany, 2002; pp. 251–260. [Google Scholar]
- NEO White Paper. Available online: https://docs.neo.org/en-us/whitepaper.html (accessed on 19 January 2019).
- Schwartz, D.; Youngs, N.; Britto, A. The Ripple protocol consensus algorithm. Ripple Labs Inc White Pap. 2014, 5, 8. [Google Scholar]
- Ripple—One Frictionless Experience To Send Money Globally|Ripple. Available online: https://ripple.com/ (accessed on 29 December 2018).
- Mazieres, D. The Stellar Consensus Protocol: A Federated Model for Internet-Level Consensus. Stellar Development Foundation. 2015. Available online: https://www.stellar.org/papers/stellar-consensus-protocol.pdf (accessed on 29 December 2018).
- Ongaro, D.; Ousterhout, J. In Search of an Understandable Consensus Algorithm. In Proceedings of the 2014 USENIX Annual Technical Conference (USENIX ATC 14), Philadelphia, PA, USA, 19–20 June 2014; USENIX Association: Berkeley, CA, USA, 2014; pp. 305–319. [Google Scholar]
- Federated Consensus. Available online: https://chain.com/docs/1.2/protocol/papers/federated-consensus (accessed on 23 January 2019).
- Tromp, J. Cuckoo Cycle: A memory-hard proof-of-work system. IACR Cryptol. EPrint Arch. 2014, 2014, 59. [Google Scholar]
- Blockcerts: The Open Standard for Blockchain Credentials. Available online: https://www.blockcerts.org/ (accessed on 29 December 2018).
- About—Blockcerts: The Open Standard for Blockchain Credentials. Available online: https://www.blockcerts.org/about.html (accessed on 29 December 2018).
- Ismail, L.; Hameed, H.; AlShamsi, M.; AlHammadi, M.; AlDhanhani, N. Towards a Blockchain Deployment at UAE University: Performance Evaluation and Blockchain Taxonomy. In Proceedings of the 2019 International Conference on Blockchain Technology, Honolulu, HI, USA, 15–18 March 2019; ACM: New York, NY, USA, 2019; pp. 30–38. [Google Scholar]
- MedRec. Available online: https://medrec.media.mit.edu/ (accessed on 29 December 2018).
- SimplyVital Health. Available online: https://www.simplyvitalhealth.com/ (accessed on 29 December 2018).
- Al Omar, A.; Rahman, M.S.; Basu, A.; Kiyomoto, S. Medibchain: A blockchain based privacy preserving platform for healthcare data. In Proceedings of the International Conference on Security, Privacy and Anonymity in Computation, Communication and Storage, Guangzhou, China, 12–15 December 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 534–543. [Google Scholar]
- Kuo, T.T.; Ohno-Machado, L. Modelchain: Decentralized privacy-preserving healthcare predictive modeling framework on private blockchain networks. arXiv 2018, arXiv:1802.01746. [Google Scholar]
- Roehrs, A.; da Costa, C.A.; da Rosa Righi, R. OmniPHR: A distributed architecture model to integrate personal health records. J. Biomed. Inform. 2017, 71, 70–81. [Google Scholar] [CrossRef] [PubMed]
- Jiang, S.; Cao, J.; Wu, H.; Yang, Y.; Ma, M.; He, J. Blochie: A blockchain-based platform for healthcare information exchange. In Proceedings of the 2018 IEEE International Conference on Smart Computing (SMARTCOMP), Taormina, Italy, 18–20 June 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 49–56. [Google Scholar]
- Mobile Bitcoin Wallet App—BTC & Cryptocurrency Wallet App|Abra. Available online: https://www.abra.com/ (accessed on 29 December 2018).
- The Future of Energy|Blockchain, Transactive Grids, Microgrids, Energy Trading. Available online: https://lo3energy.com/ (accessed on 29 December 2018).
- Every Product Has a Story|Provenance. Available online: https://www.provenance.org/ (accessed on 29 December 2018).
- OpenBazaar. Available online: https://openbazaar.org/ (accessed on 29 December 2018).
- About Us—Warranteer. Available online: http://www.warranteer.com/about-us (accessed on 29 December 2018).
- Ujo Music. Available online: https://ujomusic.com/ (accessed on 29 December 2018).
- Home|Yours. Available online: https://www.yours.org/ (accessed on 29 December 2018).
- UBITQUITY—The First Enterprise Ready Blockchain-Secured Platform for Real Estate Recordkeeping|One Block At A Time. Available online: https://www.ubitquity.io/ (accessed on 29 December 2018).
- Propy-Buy or Sell Investment Properties. Available online: https://propy.com/ (accessed on 29 December 2018).
- Arcade City. Available online: https://arcade.city/ (accessed on 29 December 2018).
- LaZooz. Available online: http://lazooz.org/ (accessed on 29 December 2018).
- The Online Voting Platform of The Future—Follow My Vote. Available online: https://followmyvote.com/ (accessed on 29 December 2018).
- Democracy Earth Foundation. Available online: https://www.democracy.earth/ (accessed on 29 December 2018).
- uPort.me. Available online: https://www.uport.me/ (accessed on 29 December 2018).
- Binded: Copyright Made Simple. Available online: https://binded.com/ (accessed on 29 December 2018).
- Verisart. Available online: https://verisart.com/ (accessed on 29 December 2018).
- Get Paperchain—Digital Media’s First Global Marketplace for AR Financing. Available online: https://www.paperchain.io/ (accessed on 29 December 2018).
- Po.et—The decentralized Protocol for Content Ownership, Discovery and Monetization of Media. Available online: https://www.po.et/ (accessed on 29 December 2018).
- NASA Fund Researches the Potential of Blockchain Technology in Space. Available online: https://news.coinsquare.com/digital-currency/nasa-research-blockchain-in-space/ (accessed on 29 December 2018).
- Space Decentral: A Decentralized Autonomous Space Agency; Technical Report; 2015; Available online: https://spacedecentral.net/White_Paper.pdf (accessed on 21 September 2019).
- Coral. Available online: https://medium.com/spacedecentral/introducing-coral-an-open-lunar-space-program-702e293c9869 (accessed on 29 December 2018).
- SpaceChain—Community-Based Space Platform. Available online: https://spacechain.com/ (accessed on 29 December 2018).
- Qtum. Available online: https://qtum.org/en/ (accessed on 29 December 2018).
- Smart Insurance Policy Powered by Blockchain. Available online: https://www.ibm.com/think/fintech/aig-ibm-standard-chartered-deliver-first-multinational-insurance-policy-powered-by-blockchain/ (accessed on 29 December 2018).
- IBM News Room—2017-08-09 Sony and Sony Global Education Develop a New System to Manage Students’ Learning Data, Built on IBM Blockchain—United States. Available online: https://www-03.ibm.com/press/us/en/pressrelease/52970.wss (accessed on 19 December 2018).
- Sharples, M.; Domingue, J. The blockchain and kudos: A distributed system for educational record, reputation and reward. In Proceedings of the European Conference on Technology Enhanced Learning, Lyon, France, 13–16 September 2016; Springer: Piscataway, NJ, USA, 2016; pp. 490–496. [Google Scholar]
- Imagining a Blockchain University|Tom Vander Ark. Available online: https://www.gettingsmart.com/2018/06/imagining-a-blockchain-university/ (accessed on 19 December 2018).
- Turkanović, M.; Hölbl, M.; Košič, K.; Heričko, M.; Kamišalić, A. EduCTX: A blockchain-based higher education credit platform. IEEE Access 2018, 6, 5112–5127. [Google Scholar] [CrossRef]
- ChronoBank.io. Available online: https://chronobank.io/ (accessed on 19 December 2018).
- Use for Blockchain in Libraries. Available online: https://ischoolblogs.sjsu.edu/blockchains/blockchains-applied/applications/ (accessed on 19 December 2018).
- Spearpoint, M. A proposed currency system for academic peer review payments using the Blockchain Technology. Publications 2017, 5, 19. [Google Scholar] [CrossRef]
- Gipp, B.; Breitinger, C.; Meuschke, N.; Beel, J. CryptSubmit: Introducing Securely Timestamped Manuscript Submission and Peer Review Feedback Using the Blockchain. In Proceedings of the 2017 ACM/IEEE Joint Conference on Digital Libraries (JCDL), Toronto, ON, Canada, 19–23 June 2017; pp. 1–4. [Google Scholar] [CrossRef]
- Bore, N.; Karumba, S.; Mutahi, J.; Darnell, S.S.; Wayua, C.; Weldemariam, K. Towards Blockchain-enabled School Information Hub. In Proceedings of the Ninth International Conference on Information and Communication Technologies and Development, Lahore, Pakistan, 16–19 November 2017; ACM: New York, NY, USA, 2017; p. 19. [Google Scholar]
- Grech, A.; Camilleri, A.F. Blockchain in Education; Publications Office of the European Union: Luxembourg, 2017. [Google Scholar]
- Dorri, A.; Kanhere, S.S.; Jurdak, R.; Gauravaram, P. Blockchain for IoT security and privacy: The case study of a smart home. In Proceedings of the 2017 IEEE International Conference on Pervasive Computing and Communications Workshops (PerCom Workshops), Kona, HI, USA, 13–17 March 2017; pp. 618–623. [Google Scholar] [CrossRef]
- Kravitz, D.W.; Cooper, J. Securing user identity and transactions symbiotically: IoT meets blockchain. In Proceedings of the Global Internet of Things Summit (GIoTS), Geneva, Switzerland, 6–9 June 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–6. [Google Scholar]
- Christidis, K.; Devetsikiotis, M. Blockchains and Smart Contracts for the Internet of Things. IEEE Access 2016, 4, 2292–2303. [Google Scholar] [CrossRef]
- Rivera, R.; Robledo, J.G.; Larios, V.M.; Avalos, J.M. How digital identity on blockchain can contribute in a smart city environment. In Proceedings of the 2017 International Smart Cities Conference (ISC2), Wuxi, China, 14–17 September 2017; pp. 1–4. [Google Scholar] [CrossRef]
- Ibba, S.; Pinna, A.; Seu, M.; Pani, F.E. CitySense: Blockchain-oriented smart cities. In Proceedings of the XP2017 Scientific Workshops, Cologne, Germany, 22–26 May 2017; ACM: New York, NY, USA, 2017; p. 12. [Google Scholar]
- Biswas, K.; Muthukkumarasamy, V. Securing Smart Cities Using Blockchain Technology. In Proceedings of the 2016 IEEE 18th International Conference on High Performance Computing and Communications; IEEE 14th International Conference on Smart City; IEEE 2nd International Conference on Data Science and Systems (HPCC/SmartCity/DSS), Sydney, NSW, Australia, 12–14 December 2016; pp. 1392–1393. [Google Scholar] [CrossRef]
- Sharma, P.K.; Moon, S.Y.; Park, J.H. Block-VN: A Distributed Blockchain Based Vehicular Network Architecture in Smart City. JIPS 2017, 13, 184–195. [Google Scholar]
- Sullivan, C.; Burger, E. E-residency and blockchain. Comput. Law Secur. Rev. 2017, 33, 470–481. [Google Scholar] [CrossRef]
- Pichel, F. Blockchain for land administration. GIM Int. 2016, 30, 38–39. [Google Scholar]
- Meter, C. Design of Distributed Voting Systems. arXiv 2017, arXiv:1702.02566. [Google Scholar]
- Noizat, P. Chapter 22—Blockchain Electronic Vote. In Handbook of Digital Currency; Chuen, D.L.K., Ed.; Academic Press: San Diego, CA, USA, 2015; pp. 453–461. [Google Scholar] [CrossRef]
- Hjalmarsson, F.P.; Hreioarsson, G.K.; Hamdaqa, M.; Hjalmtysson, G. Blockchain-Based E-Voting System. In Proceedings of the 2018 IEEE 11th International Conference on Cloud Computing (CLOUD), San Francisco, CA, USA, 2–7 July 2018; Volume 00, pp. 983–986. [Google Scholar] [CrossRef]
- Panesir, M.S. Blockchain Applications for Disaster Management and National Security. Ph.D. Thesis, State University of New York at Buffalo, Buffalo, NY, USA, 2018. [Google Scholar]
- SegWit. Available online: https://github.com/bitcoin/bips/blob/master/bip-0141.mediawiki (accessed on 31 December 2018).
- Poon, J.; Dryja, T. The Bitcoin Lightning Network: Scalable Off-Chain Instant Payments Technical Report, Technical Report (Draft). 2015. Available online: https://lightning.network (accessed on 21 September 2019).
- Zilliqa. Available online: https://docs.zilliqa.com/positionpaper.pdf (accessed on 31 December 2018).
- Sharding. Available online: https://www.investopedia.com/terms/s/sharding.asp (accessed on 31 December 2018).
- Bitcoin Could Cost Us Our Clean-Energy Future|Grist. Available online: https://grist.org/article/bitcoin-could-cost-us-our-clean-energy-future/ (accessed on 31 December 2018).
- BITCOIN MINING HARDWARE ACCELERATOR WITH OPTIMIZED MESSAGE DIGEST AND MESSAGE SCHEDULER DATAPATH. Available online: http://appft.uspto.gov/netacgi/nph-Parser?Sect1=PTO2&Sect2=HITOFF&u=%2Fnetahtml%2FPTO%2Fsearch-adv.html&r=1&p=1&f=G&l=50&d=PG01&S1=20180089642.PGNR.&OS=dn/20180089642&RS=DN/20180089642 (accessed on 31 December 2018).
- Brown, R.G.; Carlyle, J.; Grigg, I.; Hearn, M. Corda: An introduction. R3 CEV 2016, 1, 15. [Google Scholar]
- Corda. Available online: https://docs.corda.net/ (accessed on 30 December 2018).
- Popov, S. The tangle. cit. on 2016, 131. Available online: http://tanglereport.com/wp-content/uploads/2018/01/IOTA_Whitepaper.pdf (accessed on 29 December 2018).
- What Is IOTA. Available online: https://docs.iota.org/introduction/what-is-iota (accessed on 29 December 2018).
- Tip Selection—IOTA Docs. Available online: https://docs.iota.org/introduction/tangle/tip-selection (accessed on 29 December 2018).
- Blockchain on Bluemix: IBM Blockchain Blog. Available online: https://www.ibm.com/blogs/blockchain/category/blockchain-on-cloud/ (accessed on 25 January 2019).
- Blockchain on AWS. Available online: https://aws.amazon.com/blockchain/ (accessed on 25 January 2019).
- Genkin, D.; Papadopoulos, D.; Papamanthou, C. Privacy in Decentralized Cryptocurrencies. Commun. ACM 2018, 61, 78–88. [Google Scholar] [CrossRef]
- Deterministic Wallet—Bitcoin Wiki. Available online: https://en.bitcoin.it/wiki/Deterministic_wallet. (accessed on 2 January 2019).
- Ring Signature—Wikipedia. Available online: https://en.wikipedia.org/wiki/Ring_signature (accessed on 2 January 2019).
- Noether, S.; Mackenzie, A.; The Monero Research Lab. Ring confidential transactions. Ledger 2016, 1, 1–18. [Google Scholar] [CrossRef]
- Coleman, J.; Horne, L.; Xuanji, L. Counterfactual: Generalized State Channels; 2018. Available online: https://l4.ventures/papers/statechannels.pdf (accessed on 18 September 2019).
- Seele. Available online: https://seele.pro/ (accessed on 3 January 2019).
- Hirn, M. Rlay: A Decentralized Information Network. Available online: https://rlay-project.github.io/rlay.com/rlay-whitepaper.pdf (accessed on 2 January 2019).
- Corda Nodes. Available online: https://docs.corda.net/corda-test-networks.html (accessed on 30 December 2018).
| Public | Private | |
|---|---|---|
| Network Join Permission | Open | Restricted/Authorized |
| Transaction Visibility | All members | Selected authorized members |
| Participants of Consensus Process | All block generators | Selected nodes |
| Trust in the Network | Not Required | Required |
| Data Privacy | Low | High |
| Architecture Type | Supporting Platform | Platform Specificity | Network Type | Operating System(s) Supported | Programming Language(s) | Applications Portability | Applications |
|---|---|---|---|---|---|---|---|
| Single-ledger-based | Ethereum [34] | - | Public | Linux, Windows and Mac OS | Solidity, Serpent, Lisp-Like-Language | Yes | Transportation, finance, supply chain, digital content and project managements, and energy |
| Hyperledger Burrow [37] | - | Private | Linux | Go | Yes | Education, healthcare, governance, national policy, and research | |
| Chain core [38] | Validator is known as block signer and miner is known as block generator | Linux, Windows and Mac OS | Ivy | ||||
| HyperLedger Sawtooth [39] | Validator is known as journal and the role of miner is performed by a validator | Linux, Windows and Mac OS | Java, Python, JavaScript, Go, C++, Rust | ||||
| Hydrachain [40] | The role of miner is performed by a validator | Ubuntu | Python | No | |||
| Hyperledger Iroha [41] | Validator is known as peer and miner is known as orderer | Linux and Mac OS | Python, Java, JavaScript, C++ | ||||
| Burst [42] | - | Linux, Windows and Mac OS | JavaScript | ||||
| NEM [43] | Miner is known as harvester | Linux, Windows and Mac OS | Java | ||||
| BigchainDB [44] | Validator is known as mongodb server and the role of miner is performed by a validator | Ubuntu | JavaScript, Python | ||||
| MultiChain [36] | The role of miner is performed by a validator | Linux and Windows | Python, C++, JavaScript, Ruby, Go | ||||
| Quorum [61] | The role of validator is performed by the constellation component. | Hybrid | Red Hat 6.5/7, SUSE 11m3/12, Ubuntu | Python,Java | Yes | Social networking, healthcare, real estate, retail industry, and research | |
| Credits [53] | Validator is known as trusted node and miner is known as main node | Linux and Windows | Java | ||||
| Multi-ledger-based | Hyperledger Fabric [48] | Validator is known as peer, miner is known as orderer, and smart contract is known as chain code | Private | Ubuntu 14.04/16.04 and Mac OS 10.12 | Java, Go, Node.js | No | Education, healthcare, and governance |
| Oracle [52] | Linux, Windows and Mac OS | Java | |||||
| Interoperability-based | Elements [58] | Miner is known as block signer and watchmen performs the role of validator and also supports interoperability | Private | Linux, Windows and Mac OS | C++ | No | Collaborative ecosystems such as smart cities |
| Lisk [60] | - | Ubuntu 14.04.5, Windows and Mac OS | JavaScript | ||||
| Openchain [59] | The role of a miner is performed by a validator and a simple node is known as observer | Linux, Windows and Mac OS | JavaScript |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ismail, L.; Materwala, H. A Review of Blockchain Architecture and Consensus Protocols: Use Cases, Challenges, and Solutions. Symmetry 2019, 11, 1198. https://doi.org/10.3390/sym11101198
Ismail L, Materwala H. A Review of Blockchain Architecture and Consensus Protocols: Use Cases, Challenges, and Solutions. Symmetry. 2019; 11(10):1198. https://doi.org/10.3390/sym11101198
Chicago/Turabian StyleIsmail, Leila, and Huned Materwala. 2019. "A Review of Blockchain Architecture and Consensus Protocols: Use Cases, Challenges, and Solutions" Symmetry 11, no. 10: 1198. https://doi.org/10.3390/sym11101198
APA StyleIsmail, L., & Materwala, H. (2019). A Review of Blockchain Architecture and Consensus Protocols: Use Cases, Challenges, and Solutions. Symmetry, 11(10), 1198. https://doi.org/10.3390/sym11101198







