An Information Theoretically Secure E-Lottery Scheme Based on Symmetric Bivariate Polynomials
Abstract
1. Introduction
1.1. Related Works
1.2. Our Contributions
1.3. Organization of the Paper
2. Preliminaries
3. Models and Definitions
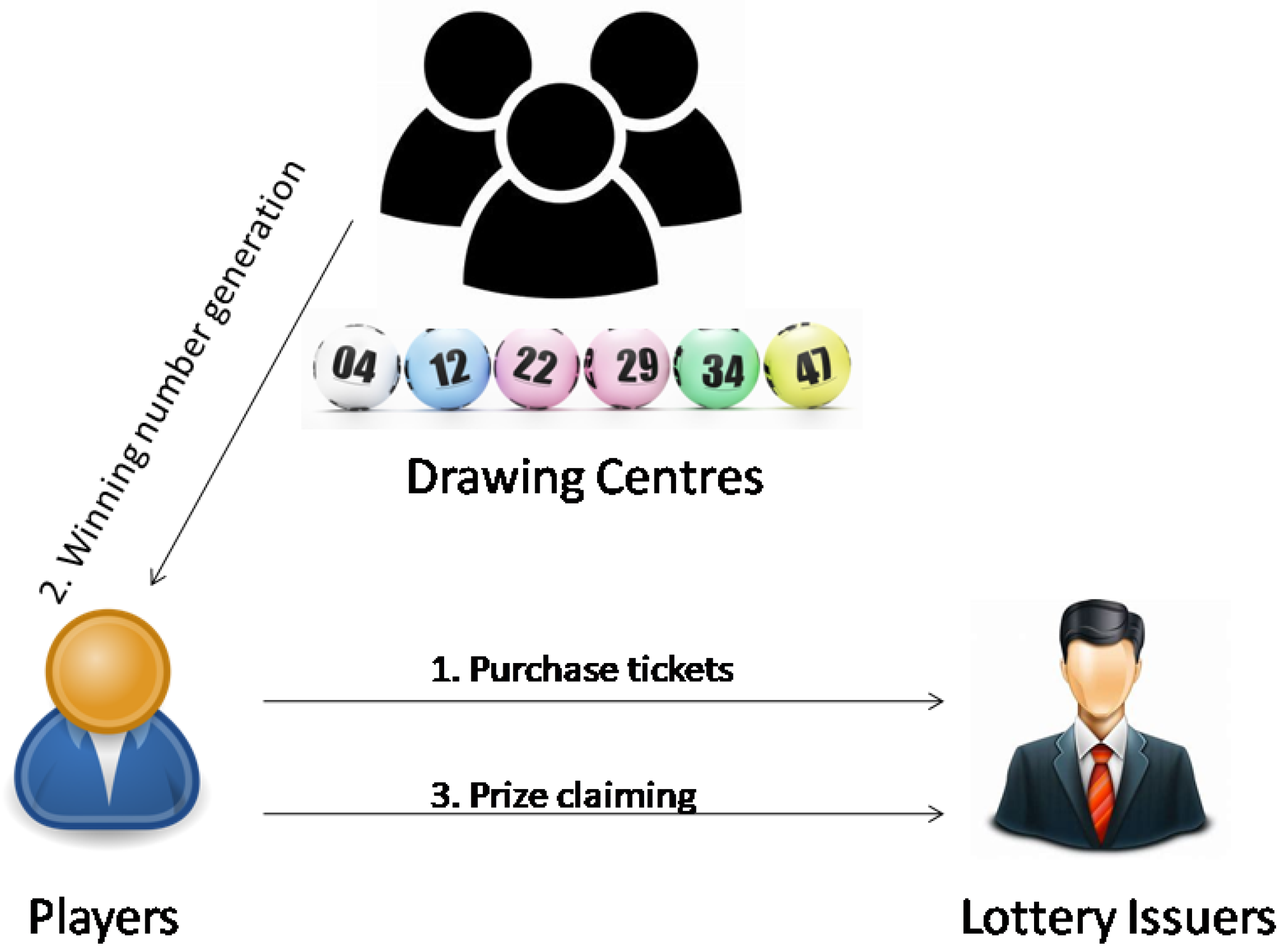
- Lottery issuers: They sell tickets to the players and provide the prize to the winner. We assume that the lottery issuers are honest.
- Players: They buy tickets and hope to win a large fortune.
- Drawing centers: They follow the public procedure to generate the winning number.
- Adversary: The adversary is assumed to have unlimited computational resources, and can control at most b of the drawing centers. Controlling a drawing center means learning its internal states, modifying its messages, disconnecting it, changing its intended behavior, and so on.
- Purchasing phase: The players can only purchase the tickets in this phase. To purchase a ticket, the player chooses a number in a pre-defined large domain and bets a small amount of money on it. Note that each player can purchase as many tickets as she/he likes. The purchased tickets are physically signed by these lottery issuers, so that they cannot be counterfeited by the players.
- Drawing phase: This phase begins after the purchasing phase. The drawing centers generate the winning number in a distributed fashion. The winning number is required to be randomly distributed in the pre-defined large domain, and it is unpredictable before its announcement. Moreover, this phase should be transparent so that the generation of the winning number can be verified.
- Claiming phase: Once the winning number is announced, the player who has selected the wining number can use her/his ticket to claim the prize from the lottery issuers.
- Correctness: The proposed scheme will output the winning number that is randomly distributed in the pre-defined domain in the drawing phase.
- Unpredictability: The adversary cannot predict the winning number before it is announced. Note that the correctness property together with the unpredictability property guarantee that each player will have a fair chance to win the prize.
- Verifiability: It can be verified that the winning number is generated according to the public procedure.
- Robustness: The winning number is generated in a distributed fashion, so that neither TTP nor the delay function needs to be employed.
4. An E-Lottery Scheme with Information Theoretical Security
4.1. The Proposed Scheme
- Each drawing center chooses a random symmetric bivariate polynomial with degree at most in both x and y:where for all . Then, computes and sends it to every other drawing center through the pairwise secure channel. Note that each is a univariate polynomial with degree at most in x. At the same time, each sends to every a random value through the pairwise secure channel for .
- After receiving from and from the other drawing centers, each computes the value for every and broadcasts these values.
- Each computes the maximum subset such that any ordered pair satisfies the equation . If , then broadcasts a bit and puts the value k in a list . Otherwise, simply broadcasts .
- If , then each broadcasts a bit and computes her/his aggregated share as:Otherwise, simply broadcasts and stops.
- If , each computes and sends it to the other drawing centers in through the pairwise secure channels.
- Finally, after receiving the values from the other drawing centers in , each computes the winning number for at least of the values she/he has received. Note that this operation can be computed efficiently using the error-correction codes.
4.2. Some Discussions
5. Security and Efficiency Analysis
5.1. Security Analysis
5.2. Comparison with Some Existing Works
5.3. Efficiency Analysis
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Rivest, R.L. Electronic lottery tickets as micropayments. In Lecture Notes in Computer Science, Proceedings of the International Conference on Financial Cryptography, Anguilla, Anguilla, 24–28 February 1997; Springer: Berlin, Germany, 1997; pp. 307–314. [Google Scholar]
- Goldschlag, D.M.; Stubblebine, S.G. Publicly verifiable lotteries: Applications of delaying functions. In Lecture Notes in Computer Science, Proceedings of the International Conference on Financial Cryptography, Anguilla, Anguilla, 23–25 February 1998; Springer: Berlin, Germany, 1998; pp. 214–226. [Google Scholar]
- Syverson, P. Weakly Secret Bit Commitment: Applications to Lotteries and Fair Exchange; Technical Report, NAVAL Research Lab Washington DC Center for High Assurance Computing Systems (CHACS); NAVAL Research Lab: Washington, DC, USA, 1998. [Google Scholar]
- Kushilevitz, E.; Rabin, T. Fair e-lotteries and e-casinos. In Lecture Notes in Computer Science, Proceedings of the Cryptographers’ Track at the RSA Conference, San Francisco, CA, USA, 8–12 April 2001; Springer: Berlin, Germany, 2001; pp. 100–109. [Google Scholar]
- Zhou, J.; Tan, C. Playing lottery on the Internet. In Lecture Notes in Computer Science, Proceedings of the International Conference on Information and Communications Security, Singapore, 9–12 December 2001; Springer: Berlin, Germany, 2001; pp. 189–201. [Google Scholar]
- Chow, S.S.; Hui, L.C.; Yiu, S.M.; Chow, K. Practical electronic lotteries with offline TTP. Comput. Commun. 2006, 29, 2830–2840. [Google Scholar] [CrossRef]
- Liu, Y.; Hu, L.; Liu, H. Using an efficient hash chain and delaying function to improve an e-lottery scheme. Int. J. Comput. Math. 2007, 84, 967–970. [Google Scholar] [CrossRef]
- Goldschlag, D.M.; Stubblebine, S.G.; Syverson, P.F. Temporarily hidden bit commitment and lottery applications. Int. J. Inf. Secur. 2010, 9, 33–50. [Google Scholar] [CrossRef]
- Sako, K. Implementation of a digital lottery server on WWW. In Secure Networking—CQRE [Secure]’99; Springer: Berlin, Germany, 1999; pp. 101–108. [Google Scholar]
- Konstantinou, E.; Liagkou, V.; Spirakis, P.; Stamatiou, Y.C.; Yung, M. Electronic national lotteries. In Lecture Notes in Computer Science, Proceedings of the International Conference on Financial Cryptography, Key West, FL, USA, 9–12 February 2004; Springer: Berlin, Germany, 2004; pp. 147–163. [Google Scholar]
- Fouque, P.A.; Poupard, G.; Stern, J. Sharing decryption in the context of voting or lotteries. In Lecture Notes in Computer Science, Proceedings of the International Conference on Financial Cryptography, Anguilla, Anguilla, 20-24 February 2000; Springer: Berlin, Germany, 2000; pp. 90–104. [Google Scholar]
- Paillier, P. Public-key cryptosystems based on composite degree residuosity classes. In Lecture Notes in Computer Science, Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Prague, Czech Republic, 2–6 May 1999; Springer: Berlin, Germany, 1999; pp. 223–238. [Google Scholar]
- Lee, J.S.; Chan, C.S.; Chang, C.C. Non-iterative privacy preservation for online lotteries. IET Inf. Secur. 2009, 3, 139–147. [Google Scholar] [CrossRef]
- Lee, J.S.; Chang, C.C. Design of electronic t-out-of-n lotteries on the Internet. Comput. Stand. Interfaces 2009, 31, 395–400. [Google Scholar] [CrossRef]
- Liu, Y.N.; Cheng, C.; Jiang, T.; Chang, C.C. A practical lottery using oblivious transfer. Int. J. Commun. Syst. 2016, 29, 277–282. [Google Scholar] [CrossRef]
- Marszałek, Z. Parallelization of modified merge sort algorithm. Symmetry 2017, 9, 176. [Google Scholar] [CrossRef]
- Allem, L.E.; Hoppen, C. A pre-test for factoring bivariate polynomials with coefficients in F2. Inf. Process. Lett. 2017, 121, 22–28. [Google Scholar] [CrossRef]
- Marszałek, Z.; Woźniak, M.; Połap, D. Fully Flexible Parallel Merge Sort for Multicore Architectures. Complexity 2018, 2018, 8679579. [Google Scholar] [CrossRef]
- Nakatsukasa, Y.; Noferini, V.; Townsend, A. Vector spaces of linearizations for matrix polynomials: A bivariate polynomial approach. SIAM J. Matrix Anal. Appl. 2017, 38, 1–29. [Google Scholar] [CrossRef]
- Plestenjak, B. Minimal determinantal representations of bivariate polynomials. Linear Algebra Its Appl. 2017, 532, 550–569. [Google Scholar] [CrossRef]
- Blom, R. An optimal class of symmetric key generation systems. In Lecture Notes in Computer Science, Proceedings of the Workshop on the Theory and Application of of Cryptographic Techniques, Paris, France, 9–11 April 1984; Springer: Berlin, Germany, 1984; pp. 335–338. [Google Scholar]
- Stinson, D.R.; Wei, R. Unconditionally secure proactive secret sharing scheme with combinatorial structures. In Lecture Notes in Computer Science, Proceedings of the International Workshop on Selected Areas in Cryptography, Kingston, ON, Canada, 9–10 August 1999; Springer: Berlin, Germany, 1999; pp. 200–214. [Google Scholar]
- D’Arco, P.; Stinson, D.R. On unconditionally secure robust distributed key distribution centers. In Lecture Notes in Computer Science, Proceedings of the International Conference on the Theory and Application of Cryptology and Information Security, Queenstown, New Zealand, 1–5 December 2002; Springer: Berlin, Germany, 2002; pp. 346–363. [Google Scholar]
- Ben-Or, M.; Goldwasser, S.; Wigderson, A. Completeness theorems for non-cryptographic fault-tolerant distributed computation. In Proceedings of the ACM Twentieth Annual ACM Symposium on Theory of Computing, Chicago, IL, USA, 2–4 May 1988; pp. 1–10. [Google Scholar]
- Shamir, A. How to share a secret. Commun. ACM 1979, 22, 612–613. [Google Scholar] [CrossRef]
- Benaloh, J.C. Secret sharing homomorphisms: Keeping shares of a secret secret. In Lecture Notes in Computer Science, Proceedings of the Conference on the Theory and Application of Cryptographic Techniques, Santa Barbara, CA, USA, 11–15 August 1986; Springer: Berlin, Germany, 1986; pp. 251–260. [Google Scholar]
- Liu, Y.; Guo, W.; Fan, C.I.; Chang, L.; Cheng, C. A practical privacy-preserving data aggregation (3PDA) scheme for smart grid. IEEE Trans. Ind. Inform. 2018. [Google Scholar] [CrossRef]
- Liu, Y.; Wang, Y.; Wang, X.; Xia, Z.; Xu, J.F. Privacy-preserving raw data collection without a trusted authority for IoT. Comput. Netw. 2018. [Google Scholar] [CrossRef]
- Gennaro, R.; Ishai, Y.; Kushilevitz, E.; Rabin, T. The round complexity of verifiable secret sharing and secure multicast. In Proceedings of the ACM Thirty-Third Annual ACM Symposium on Theory of Computing, Santa Barbara, CA, USA, 16–20 August 2001; pp. 580–589. [Google Scholar]
- Håstad, J.; Impagliazzo, R.; Levin, L.A.; Luby, M. Construction of a pseudo-random generator from any one-way function. SIAM J. Comput. Citeseer 1993, 28, 12–24. [Google Scholar]
| Correctness | Unpredictability | Verifiability | Robustness | IT Security | |
|---|---|---|---|---|---|
| Goldschlag’s scheme [2] | Yes | Yes | Yes | No | No |
| Kushilevitz’s scheme [4] | Yes | Yes | Yes | No | No |
| Fouque’s scheme [11] | Yes | Yes | Yes | Yes | No |
| Zhou’s scheme [5] | Yes | Yes | Yes | No | No |
| Lee’s scheme [13] | Yes | Yes | No | No | No |
| Liu’s scheme [15] | Yes | Yes | Yes | Yes | No |
| Our proposed scheme | Yes | Yes | Yes | Yes | Yes |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Xia, Z.; Liu, Y.; Hsu, C.-F.; Chang, C.-C. An Information Theoretically Secure E-Lottery Scheme Based on Symmetric Bivariate Polynomials. Symmetry 2019, 11, 88. https://doi.org/10.3390/sym11010088
Xia Z, Liu Y, Hsu C-F, Chang C-C. An Information Theoretically Secure E-Lottery Scheme Based on Symmetric Bivariate Polynomials. Symmetry. 2019; 11(1):88. https://doi.org/10.3390/sym11010088
Chicago/Turabian StyleXia, Zhe, Yining Liu, Ching-Fang Hsu, and Chin-Chen Chang. 2019. "An Information Theoretically Secure E-Lottery Scheme Based on Symmetric Bivariate Polynomials" Symmetry 11, no. 1: 88. https://doi.org/10.3390/sym11010088
APA StyleXia, Z., Liu, Y., Hsu, C.-F., & Chang, C.-C. (2019). An Information Theoretically Secure E-Lottery Scheme Based on Symmetric Bivariate Polynomials. Symmetry, 11(1), 88. https://doi.org/10.3390/sym11010088






