A Novel Data-Driven Evaluation Framework for Fork after Withholding Attack in Blockchain Systems
Abstract
:1. Introduction
- At present, there are a few evaluation frameworks for FAW attacks, and there is a lack of revenue evaluation when the target mining pool encounters FAW attacks. Effective security evaluation of the target mining pool is difficult.
- The evaluation of FAW attacks in the evaluation mining pool and target mining pool are both considered to be single, i.e., one evaluation mining pool evaluates one target mining pool. There is a lack of one evaluation mining pool that evaluates multiple target mining pools, and a consensus revenue model for evaluating the attack revenues of multiple target mining pools is also needed.
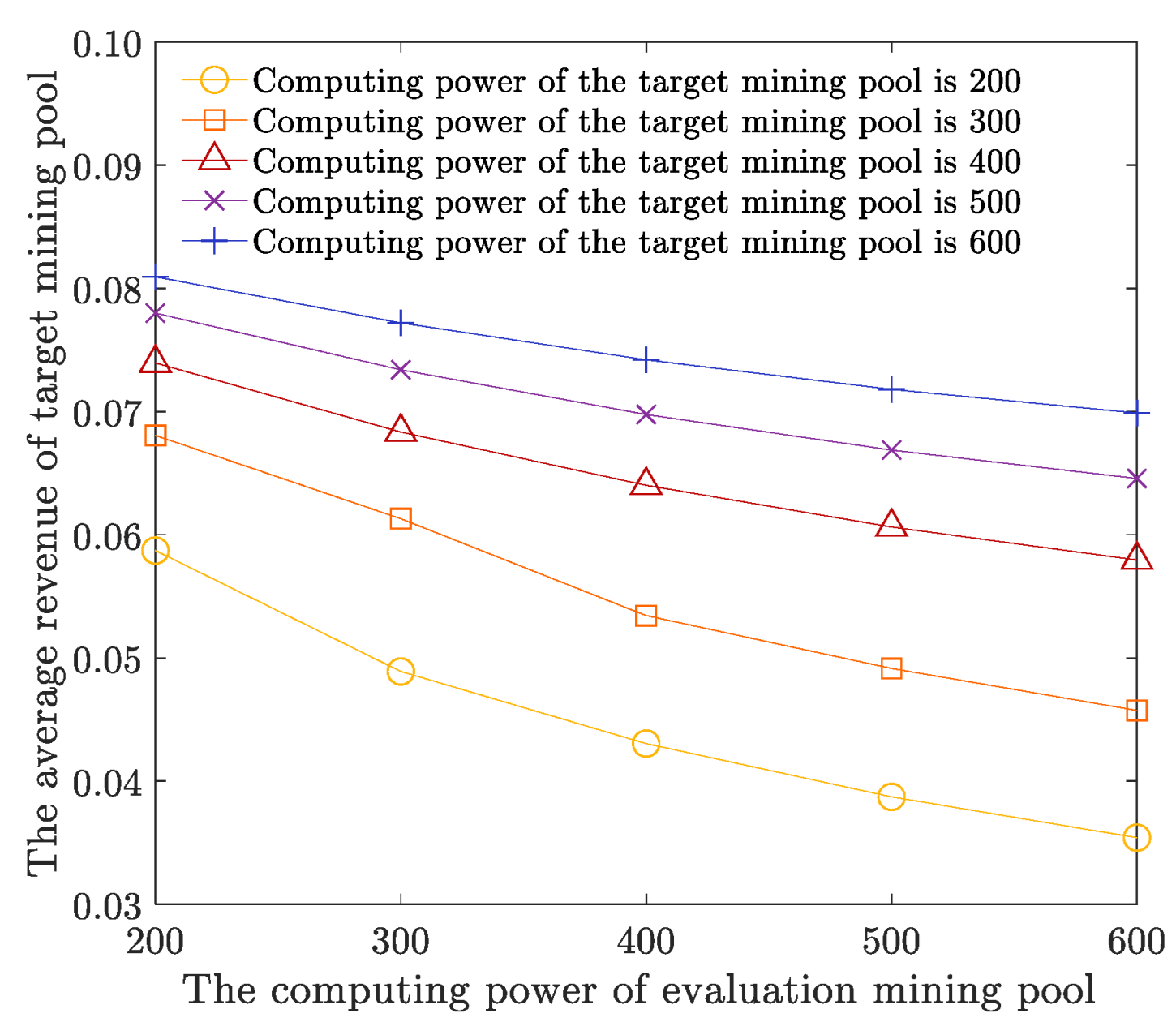
- The traditional FAW attack evaluation allocates the attack computing power fixedly, and excessive computing power may be wasted on the target mining pools with small revenue. Thus, the evaluation computing power cannot be efficiently allocated by the size of the target mining pool to maximize the attack revenue.
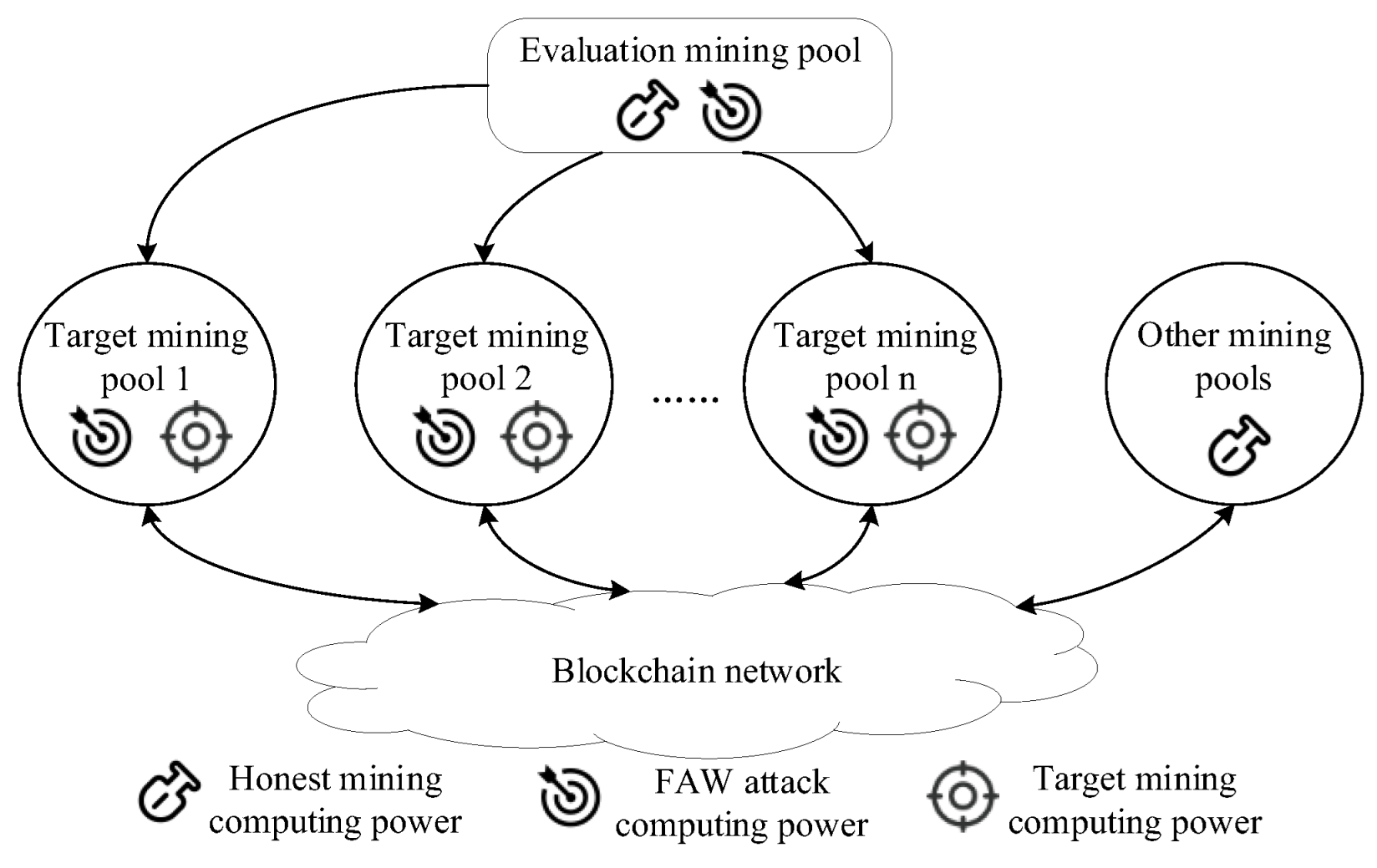
- Given the above problems, this paper considers the target mining pools to be multiple and proposes a novel evaluation framework for target mining pools. In this framework, we take advantage of optimization theory and the traditional FAW attack method and propose a computing power allocation optimization algorithm (CPAOA) of the FAW evaluation mining pool for multiple target mining pools. The main contributions of this paper are as follows:
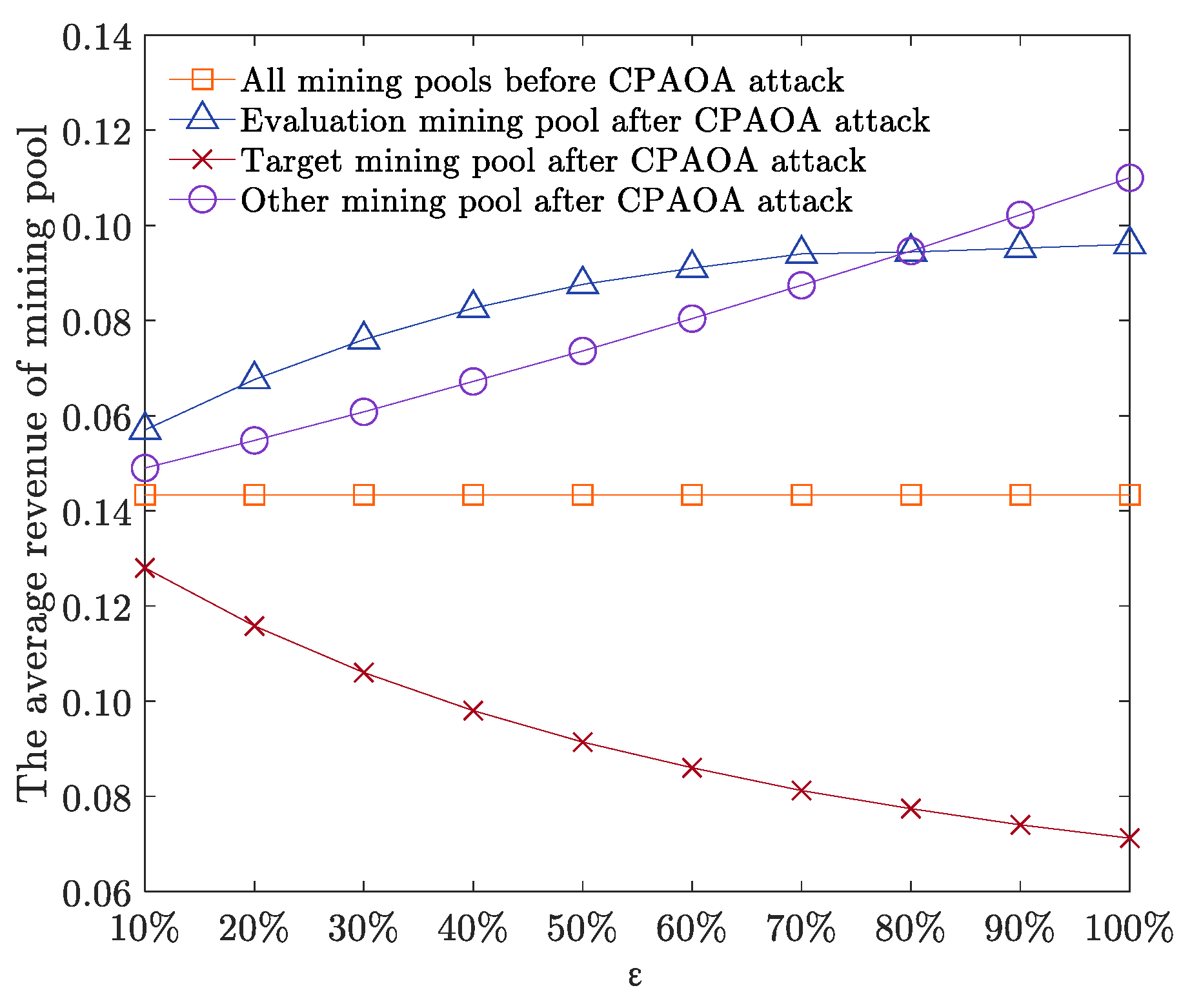
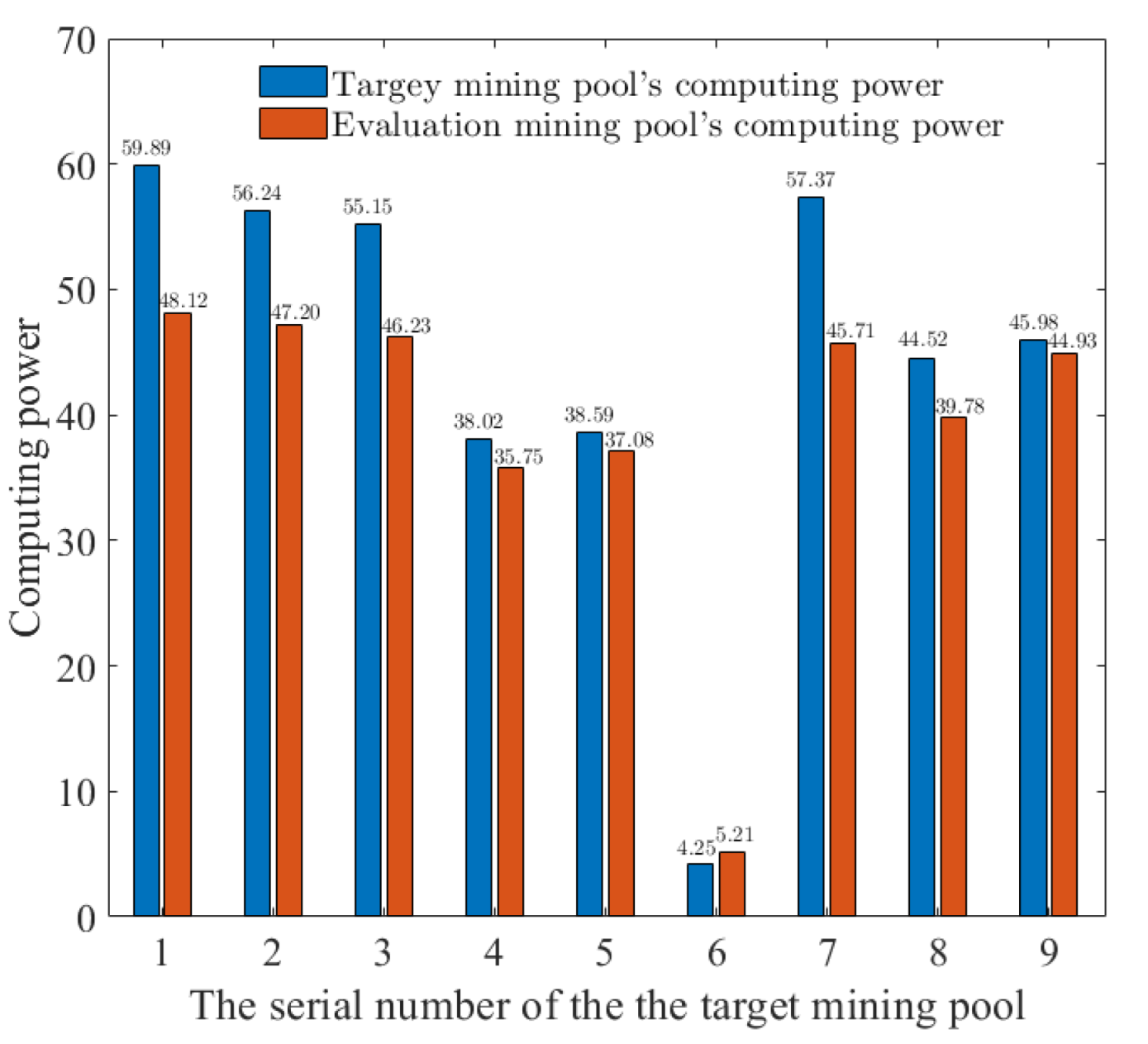
- We propose a novel evaluation framework for target mining pools. We extend the evaluation of FAW attacks on one target mining pool to multiple target mining pools. We establish the mathematical equations for honest consensus revenue, block withholding revenue, successful fork revenue, consensus cost, etc. Then we establish an adaptive revenue optimization model for the computing power of the evaluation mining pools. At the same time, we also establish the revenue models of target mining pools and other mining pools to evaluate the attack revenue after the adaptive computing power allocation.
- We propose an improved Aquila optimization-based model-solving algorithm. More specifically, based on the traditional Aquila optimization algorithm, we improve the selection mechanism of different optimization processes and the fitness calculation of the proposed revenue optimization model. The algorithm can improve the convergence speed of the solution of the attack revenue optimization model and find the global optimal solution efficiently.
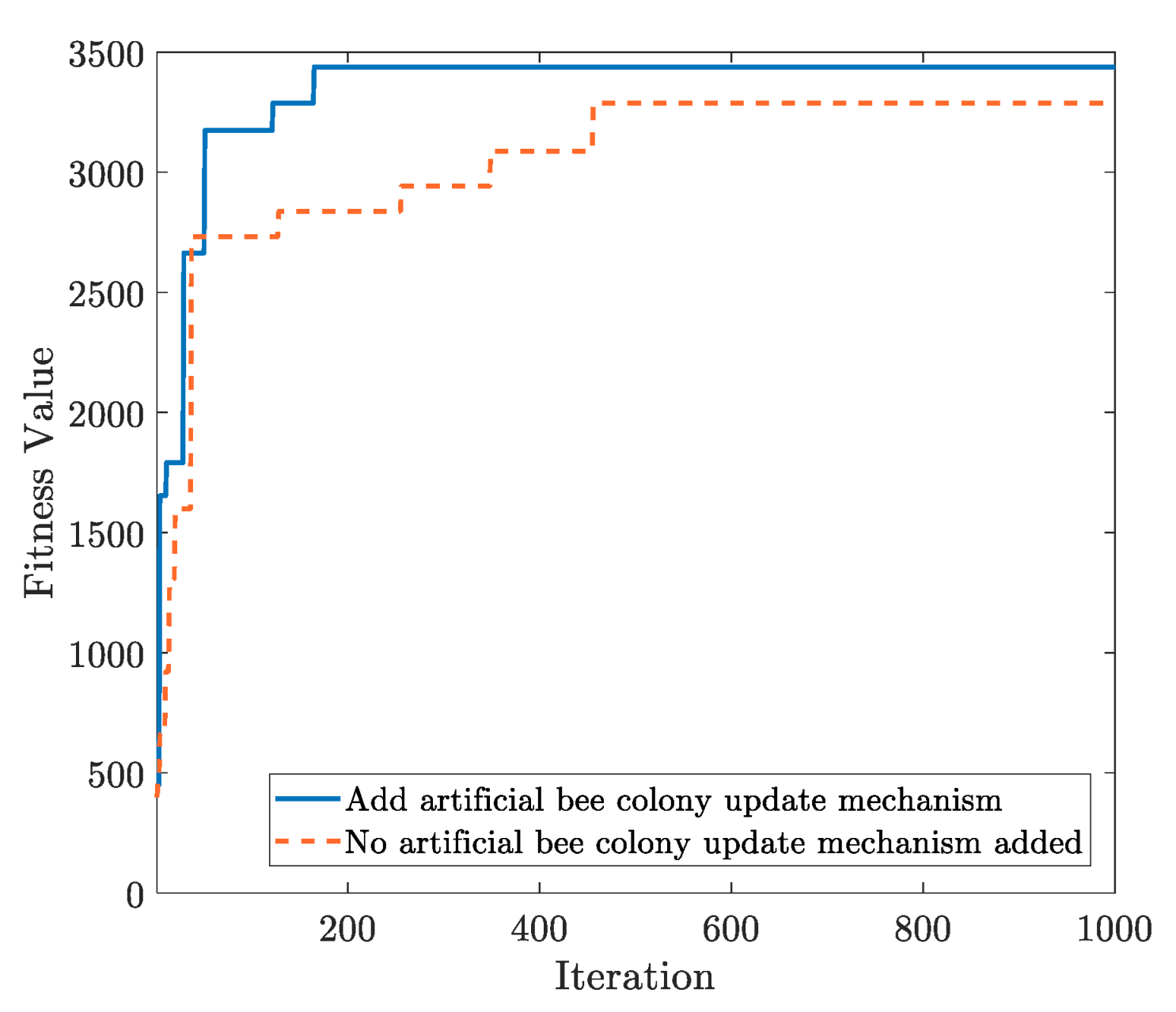
- We propose a solution update mechanism to prevent the algorithm from falling into local optimal solutions. The mechanism combines the idea of scout bees in an artificial bee colony optimization algorithm and the constraint of allocating computing power. According to the similarity ratio of solutions in the process of multiple iterations, the solution update mechanism can replace the relevant solutions in time and help prevent the algorithm from falling into the local optimal solution dilemma during the solution process.
2. Related Work
3. Framework Principle
3.1. Model Building
3.2. Model Solving
4. Algorithm Implementation
| Algorithm 1: Computing Power Allocation Optimization Algorithm (CPAOA) |
| Input: Number of target mining pools 1: = 1000; = 50; = 1/4; = 90; = 80; 2: Calculate the computing power of the target mining pool and other mining pools; 3: Establish the revenue models of evaluation mining pool, target mining pool, and other mining pool; 4: Determine the solution model and construct the search space; 5: for (I = 0; I < T; i++) 6: Randomly generate attack computing power distribution schemes and form them into a distribution scheme matrix ; 7: for (j = 0; j < K; j++) 8: Calculate the fitness of each attack computing power distribution scheme; 9: Update the optimal allocation scheme; 10: if judged that the current scheme is in one of the four stages of AO algorithm; 11: Execute the formula at this stage to update the attack computing power distribution scheme; 12: Calculate the fitness value of the scheme; 13: Calculate the fitness value after the artificial bee colony updates the scheme; 14: Compare with the optimal scheme at the current moment and update the optimal scheme; 15: or else 16: Obtain the optimal distribution scheme of attack computing power for this round; 17: T = T + 1; 18: Update global optimal scheme; 19: end 20: end 21: Determine the optimal distribution scheme of attack computing power; 22: Launch FAW attacks on multiple target mining pools; 23: Evaluate the protection capabilities of multiple target mining pools; |
5. Experiment and Analysis
5.1. Parameters and Performance Indicators
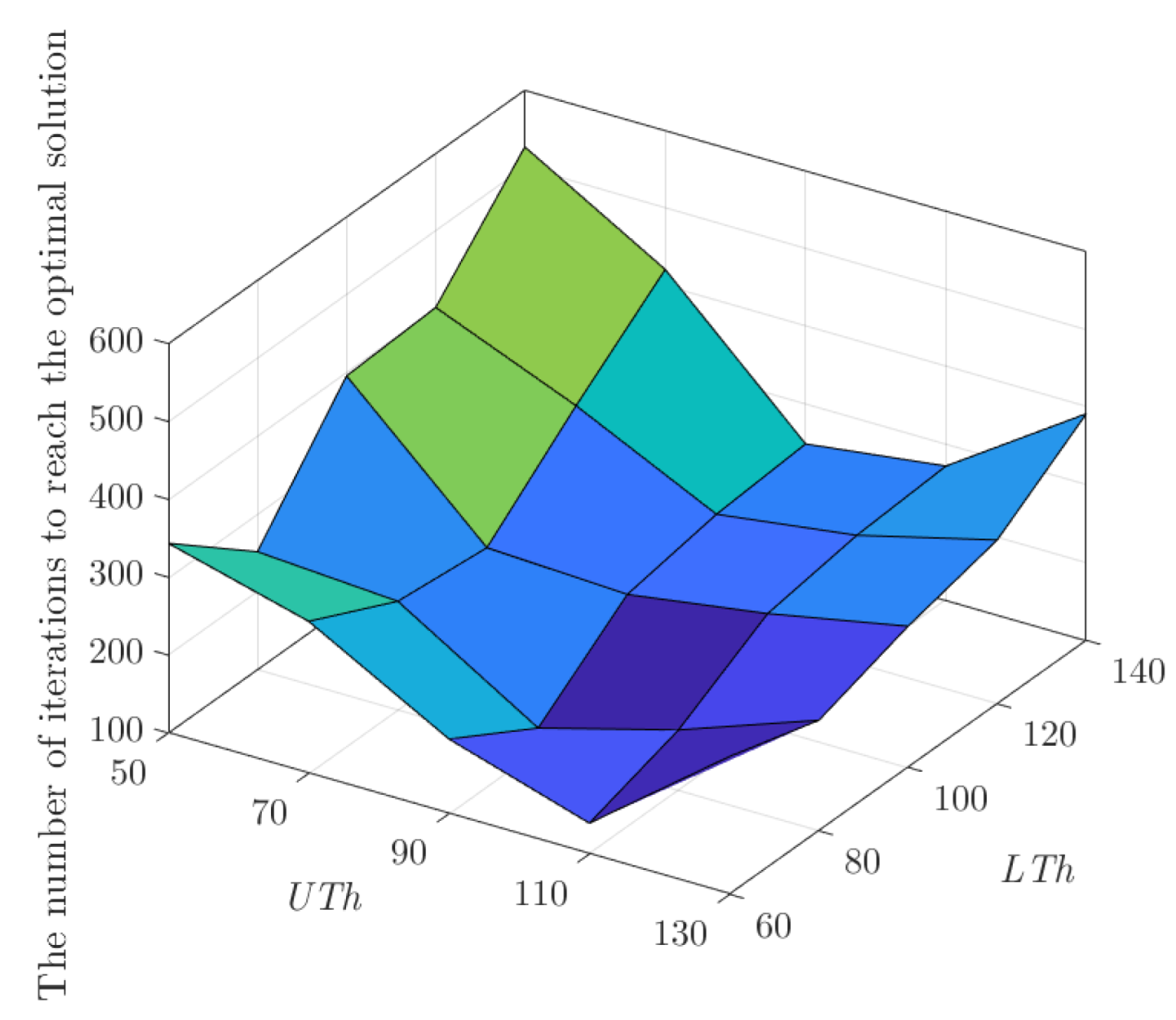
5.2. Parameter Selection Analysis
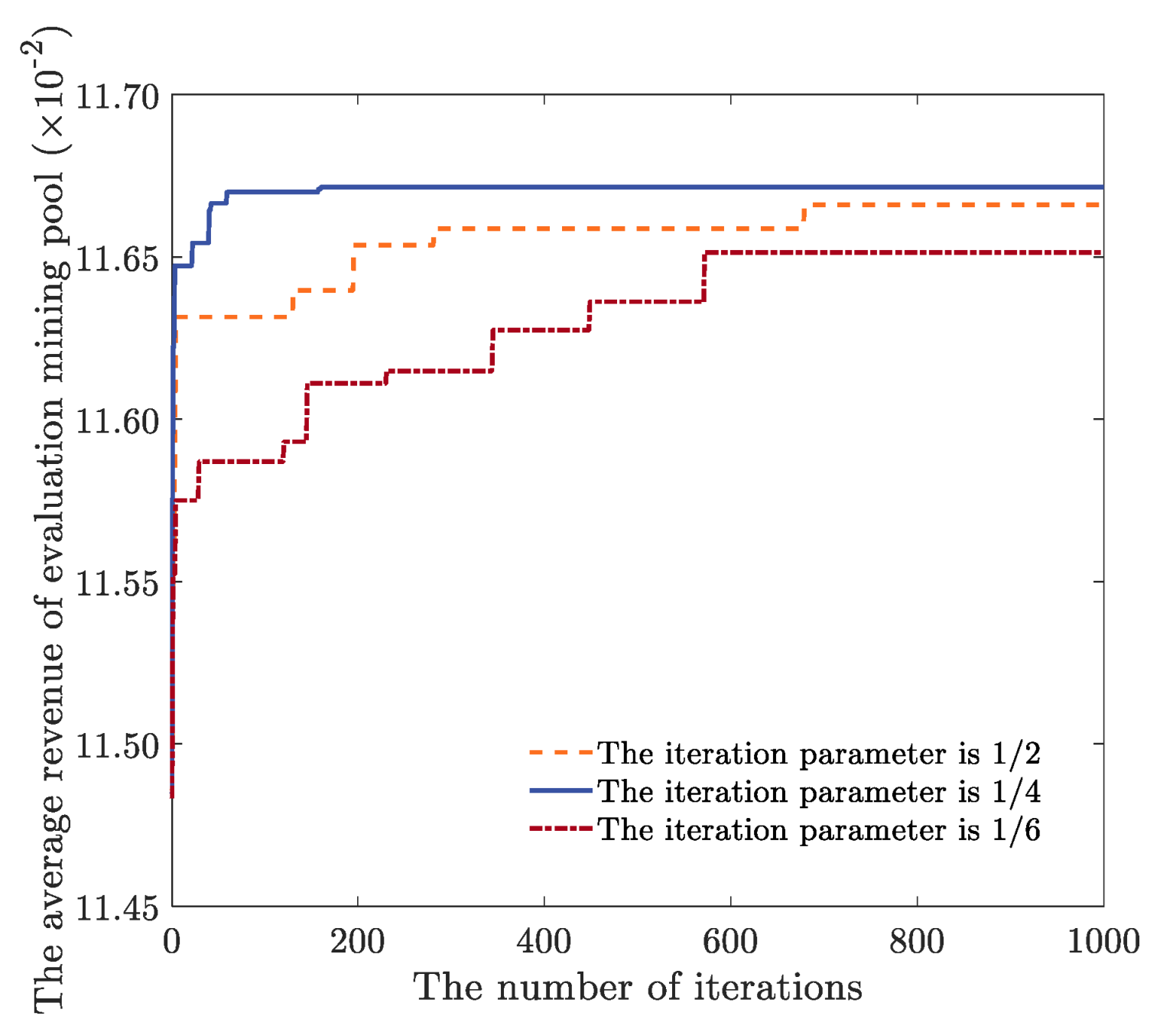
5.3. Algorithm Performance Analysis
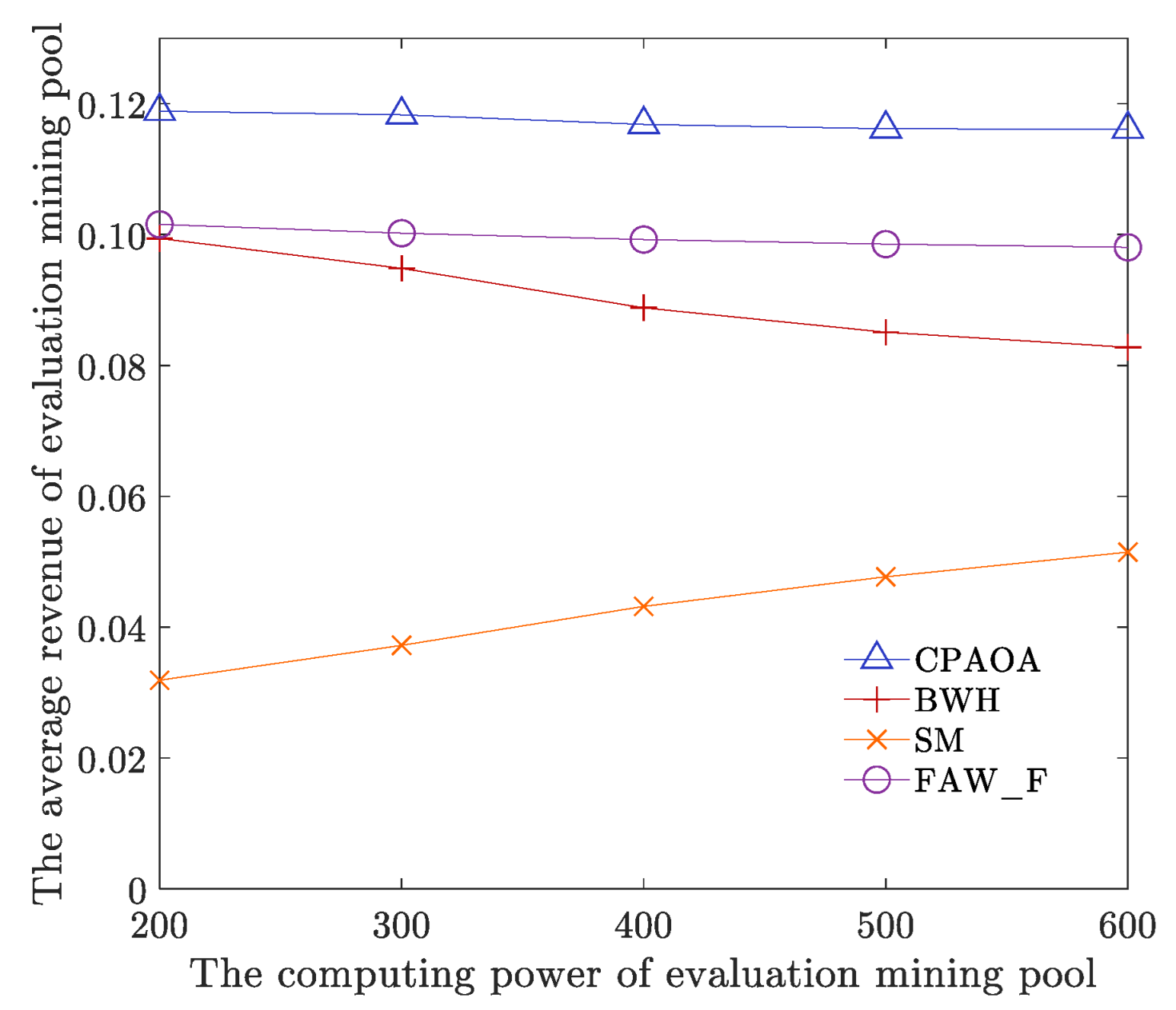
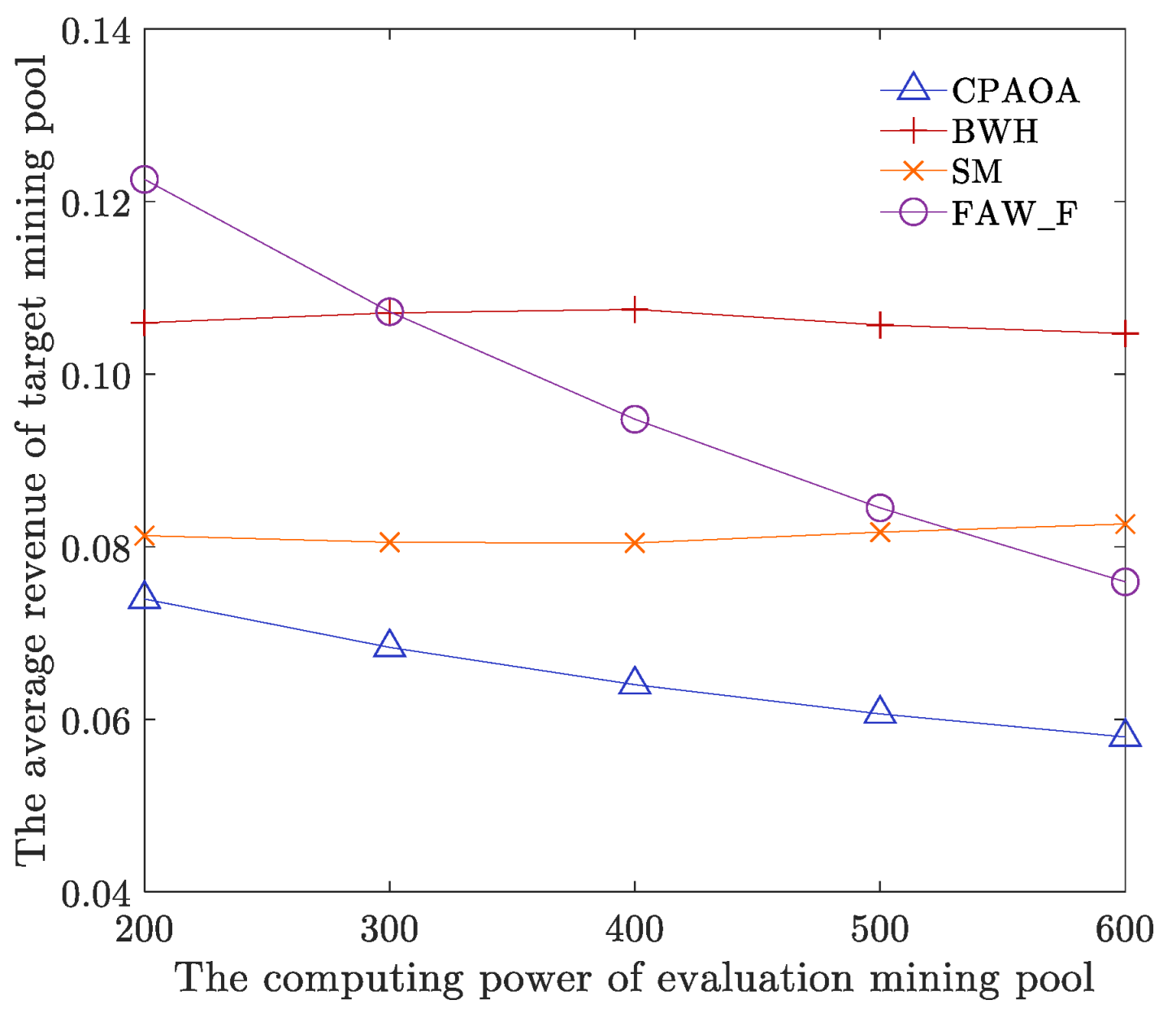
5.4. Algorithm Comparison Analysis
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Warnat-Herresthal, S.; Schultze, H.; Shastry, K.L.; Manamohan, S.; Mukherjee, S.; Garg, V.; Sarveswara, R.; Händler, K.; Pickkers, P.; Aziz, N.A.; et al. Swarm learning for decentralized and confidential clinical machine learning. Nature 2021, 594, 265–270. [Google Scholar] [CrossRef]
- Liu, M.; Quan, Z.W.; Wu, J.M.; Liu, Y.; Han, M. Embedding temporal networks inductively via mining neighborhood and community influences. Appl. Intell. 2022, 1, 16069–16088. [Google Scholar] [CrossRef]
- Chen, Y.; Chen, H.; Zhang, Y.; Han, M.; Siddula, M.; Cai, Z. A survey on blockchain systems: Attacks, defenses, and privacy preservation. High-Confidence Computing. 2022, 2, 100048. [Google Scholar] [CrossRef]
- Berdik, D.; Otoum, S.; Schmidt, N.; Porter, D.; Jararweh, Y. A survey on blockchain for information systems management and security. Inf. Process. Manag. 2021, 58, 102397–102425. [Google Scholar] [CrossRef]
- Da Xu, L.; Lu, Y.; Li, L. Embedding blockchain technology into IoT for security: A survey. IEEE Internet Things J. 2021, 8, 10452–10473. [Google Scholar]
- Attaran, M. Blockchain technology in healthcare: Challenges and opportunities. Int. J. Healthc. Manag. 2022, 15, 70–83. [Google Scholar] [CrossRef]
- Bi, R.; Peng, T.; Ren, J.; Fang, X.; Tan, G. Joint service placement and computation scheduling in edge clouds. In Proceedings of the 2022 IEEE International Conference on Web Services (ICWS), Barcelona, Spain, 10–16 July 2022; IEEE: Piscataway, NJ, USA, 2022; pp. 47–56. [Google Scholar]
- Li, P.L.; Xu, H.X. Blockchain user anonymity and traceability technology. J. Electron. Inf. Technol. 2020, 42, 1061–1067. [Google Scholar]
- Bouraga, S. A taxonomy of blockchain consensus protocols: A survey and classification framework. Expert Syst. Appl. 2021, 168, 1–47. [Google Scholar] [CrossRef]
- Ghosh, A.; Gupta, S.; Dua, A.; Kumar, N. Security of Cryptocurrencies in blockchain technology: State-of-art, challenges and future prospects. J. Netw. Comput. Appl. 2020, 163, 102635–102715. [Google Scholar] [CrossRef]
- Szalachowski, P.; Reijsbergen, D.; Homoliak, I.; Sun, S. {StrongChain}: Transparent and Collaborative {Proof-of-Work} Consensus. In Proceedings of the 28th USENIX Security Symposium (USENIX Security 19), Santa Clara, CA, USA, 14–16 August 2019; USENIX Association: Berkeley, CA, USA, 2019; pp. 819–836. [Google Scholar]
- Schwarz-Schilling, C.; Li, S.N.; Tessone, C.J. Stochastic Modelling of Selfish Mining in Proof-of-Work Protocols. J. Cybersecur. Priv. 2022, 2, 292–310. [Google Scholar] [CrossRef]
- Chen, H.; Chen, Y.; Xiong, Z.; Han, M.; He, b.; Liu, B.; Wang, Z.; Ma, Z. Prevention method of block withholding attack based on miners’ mining behavior in blockchain. Appl. Intell. 2022, 1, 1–19. [Google Scholar] [CrossRef]
- Chen, W.; Guo, X.; Chen, Z.; Zheng, Z.; Lu, Y. Phishing Scam Detection on Ethereum: Towards Financial Security for Blockchain Ecosystem. In Proceedings of the 29th International Joint Conference on Artificial Intelligence (IJCAI), Yokohama, Japan, 7–15 January 2020; Morgan Kaufmann: Burlington, MA, USA, 2020; pp. 4506–4512. [Google Scholar]
- Eyal, I.; Sirer, E.G. Majority is not enough: Bitcoin mining is vulnerable. Commun. ACM 2018, 61, 95–102. [Google Scholar] [CrossRef]
- Bag, S.; Ruj, S.; Sakurai, K. Bitcoin block withholding attack: Analysis and mitigation. IEEE Trans. Inf. Secur. 2016, 12, 1967–1978. [Google Scholar] [CrossRef]
- Kwon, Y.; Kim, D.; Son, Y.; Vasserman, E.; Kim, Y. Be selfish and avoid dilemmas: Fork after withholding (faw) attacks on bitcoin. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017; ACM: New York, NY, USA, 2017; pp. 195–209. [Google Scholar]
- Fan, L.; Zheng, H.; Huang, J.; Li, Z.; Jiang, Y. Cooperative evolution method for blockchain mining pool based on adaptive zero-determinant strategy. J. Comput. Appl. 2019, 39, 918–923. [Google Scholar]
- Davidson, M.; Diamond, T. On the profitability of selfish mining against multiple difficulty adjustment algorithms. Cryptol. Eprint Arch. 2020, 2020, 94–105. [Google Scholar]
- Wang, Y.; Yang, G.; Li, T.; Zhang, L.; Wang, Y.; Ke, L.; Dou, Y.; Li, S.; Yu, X. Optimal mixed block withholding attacks based on reinforcement learning. Int. J. Intell. Syst. 2020, 35, 2032–2048. [Google Scholar] [CrossRef]
- Ke, J.; Jiang, H.; Song, X.; Zhao, S.; Wang, H.; Xu, Q. Analysis on the block reward of fork after withholding (FAW). Prcceedings of the International Conference on Network and System Security, Hong Kong, China, 27–29 August 2020; Springer: Cham, Switzerland, 2020; pp. 16–31. [Google Scholar]
- Dong, X.; Wu, F.; Faree, A.; Guo, D.; Shen, Y.; Ma, J. Selfholding: A combined attack model using selfish mining with block withholding attack. Comput. Secur. 2019, 87, 101584–101595. [Google Scholar] [CrossRef]
- Gao, S.; Li, Z.; Peng, Z.; Xiao, B. Power adjusting and bribery racing: Novel mining attacks in the bitcoin system. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, London, UK, 11–15 November 2019; ACM: New York, NY, USA, 2019; pp. 833–850. [Google Scholar]
- Yang, R.; Chang, X.; Mišić, J.; Mišić, V.; Zhu, H. Evaluating fork after withholding (FAW) attack in Bitcoin. In Proceedings of the 19th ACM International Conference on Computing Frontiers, Turin, Italy, 17–22 May 2022; ACM: New York, NY, USA, 2022; pp. 67–74. [Google Scholar]
- Abualigah, L.; Yousri, D.; Abd Elaziz, M.; Ewees, A.A.; Al-Qaness, M.A.; Gandomi, A.H. Aquila optimizer: A novel me-ta-heuristic optimization algorithm. Comput. Ind. Eng. 2021, 157, 107250. [Google Scholar] [CrossRef]
| Parameter | Number |
|---|---|
| Number of iterations | 1000 |
| Number of randomly generated evaluation mining pool computing Power distribution schemes | 50 |
| Consensus cost per unit of computing power | 0.00015 |
| Cost of FAW attack per unit of computing power | 0.00005 |
| Computing power of the entire network | 3000 |
| Probability of successful hashing of blocks in target mining pools | 0.6 |
| Reward of single block consensus | 500 |
| Algorithm | Mining Pool | Total Average Revenue | Comparison |
|---|---|---|---|
| CPAOA | Evaluation mining pool | 0.1173 | 1 |
| Target mining pool | 0.0650 | 1 | |
| BWH | Evaluation mining pool | 0.0902 | 30.54% |
| Target mining pool | 0.1062 | −38.83% | |
| SM | Evaluation mining pool | 0.0423 | 186.04% |
| Target mining pool | 0.0813 | −20.04% | |
| FAW_F | Evaluation mining pool | 0.0995 | 17.82% |
| Target mining pool | 0.0970 | −32.07% |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, Y.; Chen, Y.; Miao, K.; Ren, T.; Yang, C.; Han, M. A Novel Data-Driven Evaluation Framework for Fork after Withholding Attack in Blockchain Systems. Sensors 2022, 22, 9125. https://doi.org/10.3390/s22239125
Zhang Y, Chen Y, Miao K, Ren T, Yang C, Han M. A Novel Data-Driven Evaluation Framework for Fork after Withholding Attack in Blockchain Systems. Sensors. 2022; 22(23):9125. https://doi.org/10.3390/s22239125
Chicago/Turabian StyleZhang, Yang, Yourong Chen, Kelei Miao, Tiaojuan Ren, Changchun Yang, and Meng Han. 2022. "A Novel Data-Driven Evaluation Framework for Fork after Withholding Attack in Blockchain Systems" Sensors 22, no. 23: 9125. https://doi.org/10.3390/s22239125
APA StyleZhang, Y., Chen, Y., Miao, K., Ren, T., Yang, C., & Han, M. (2022). A Novel Data-Driven Evaluation Framework for Fork after Withholding Attack in Blockchain Systems. Sensors, 22(23), 9125. https://doi.org/10.3390/s22239125







