Sustainable Data-Driven Secured Optimization Using Dynamic Programming for Green Internet of Things
Abstract
1. Introduction
- It provides a data-driven approach for sustainable smart cities using multistage graph-based structures and improves the system’s response time.
- Intelligent decisions are made based on dynamic programming, which allows for effective computing with minimum complexity on the IoT networks.
- Edge computing and deterministic technique are combined to create and maintain system security. Using an offloading method lessens the burden of security measures on the devices.
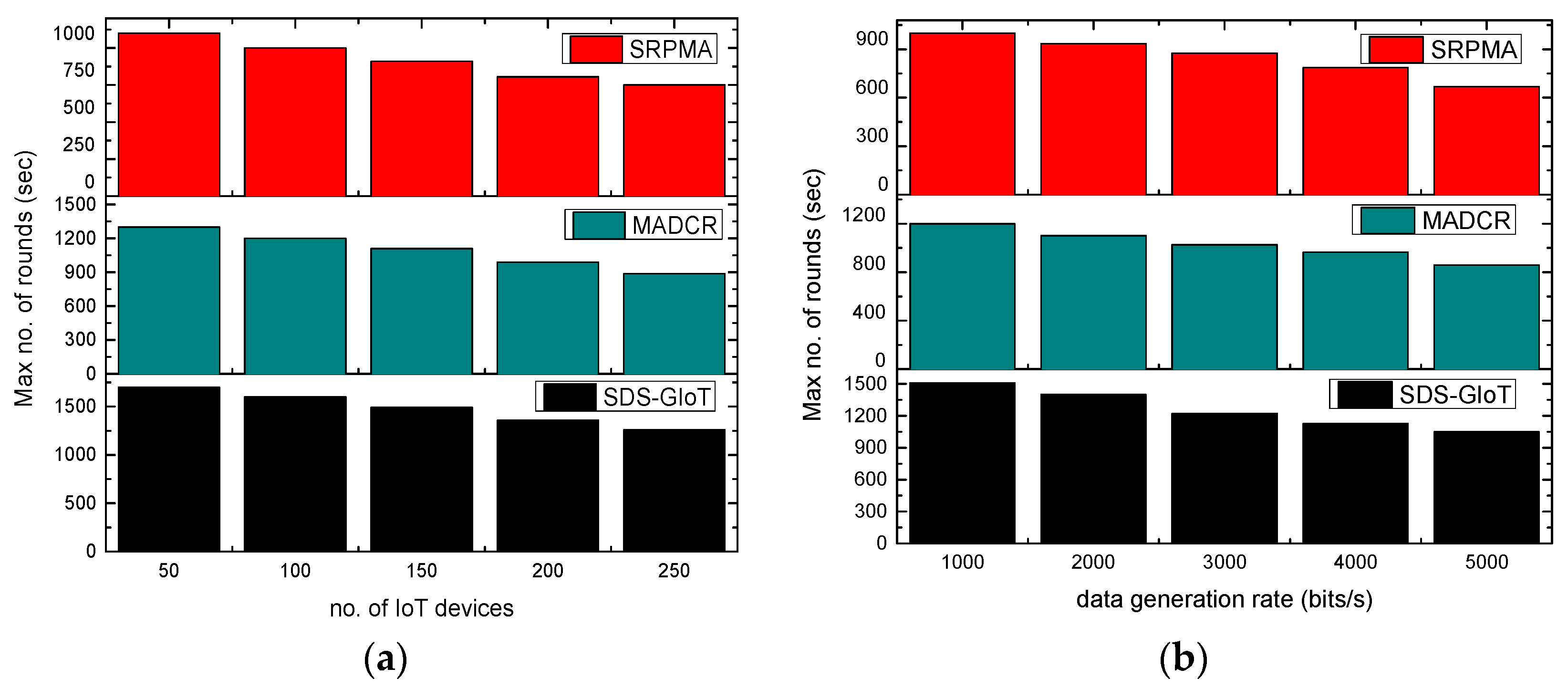
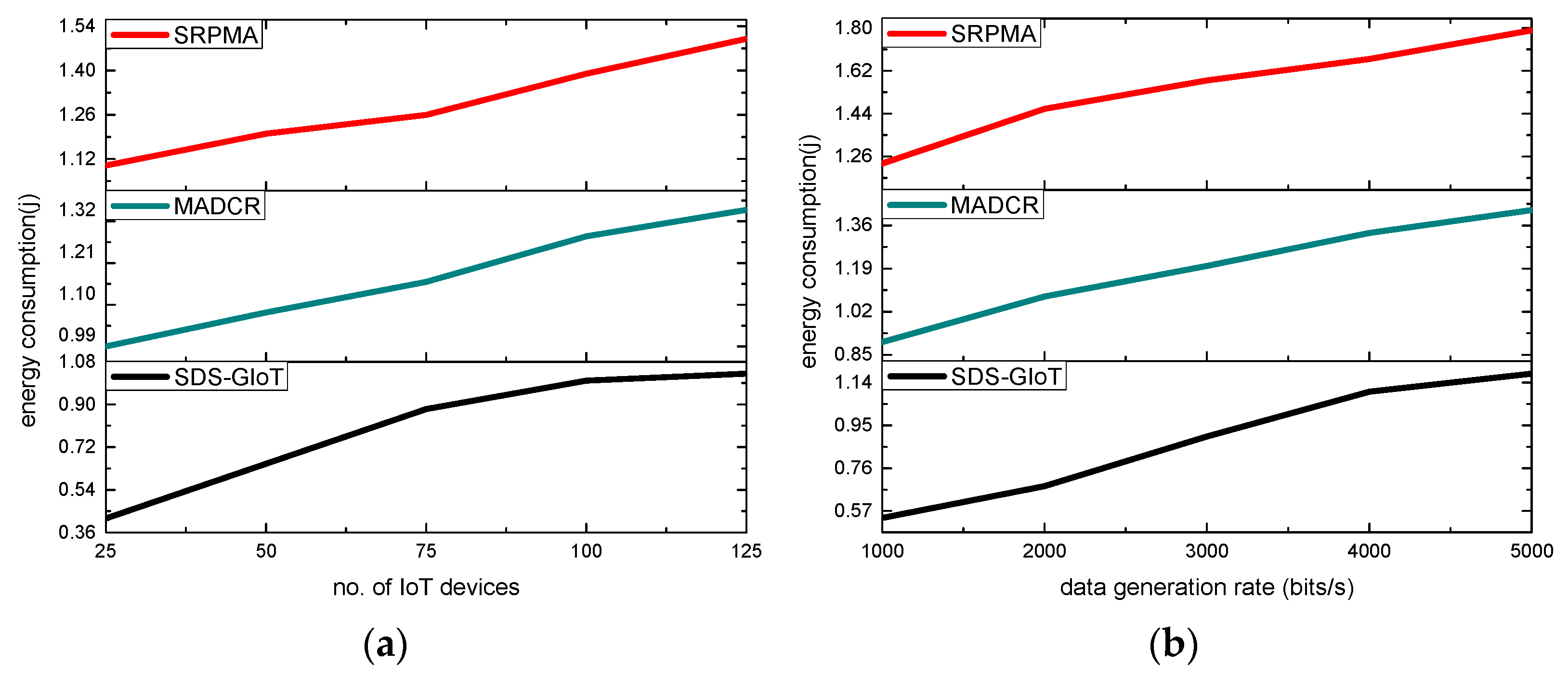
- The proposed SDS-GIoT model is verified in terms of green computing metrics against existing work.
2. Literature Review
3. Sustainable Data-Driven Secured Decision Protocol with Dynamic Programming
3.1. System Model
- The sensor nodes can only communicate with edge devices and are not mobile.
- There are no resource restrictions on the network edges or sink nodes.
- At the edge of a sensor’s vicinity, edge devices are randomly positioned.
- No more nodes or devices can be included after deployment.
- Malicious nodes can generate false information and compromise the sending data and wireless channels.
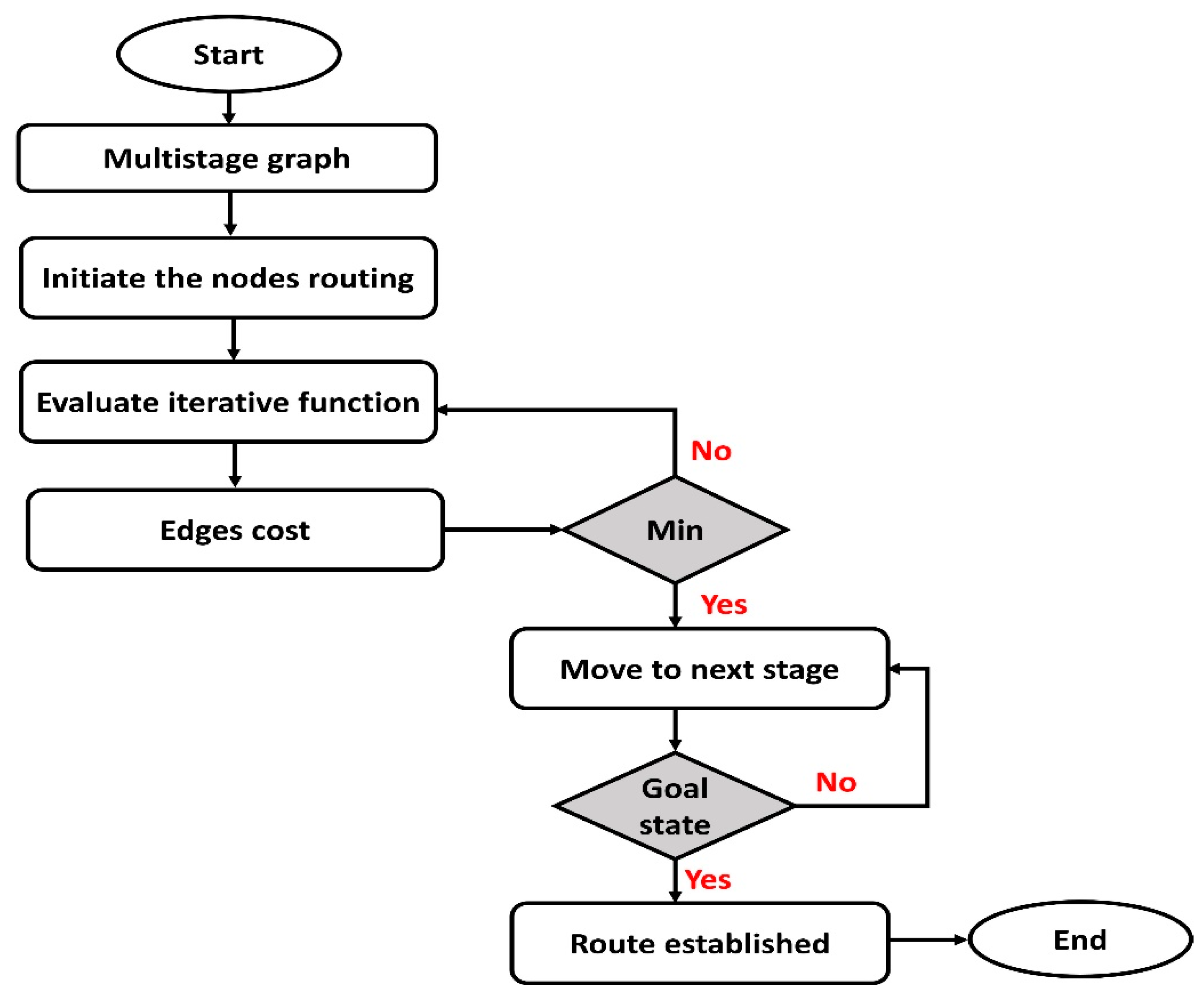
3.2. States of the SDS-GIoT Model
- Multistage graph: This stage organizes the nodes in the form of multiple stages, and stages are interconnected with edges.
- Tables’ initialization: In this state, nodes’ information and network conditions are recorded along with the identities of devices.
- Iterative function: The repeated function is performed to determine the optimal routing strategy in this state.
- Edge cost: Nodes compute the cost, and accordingly, the minimum value offers the optimal decisions. In case the outcome is not optimal, then the iterative function is executed again.
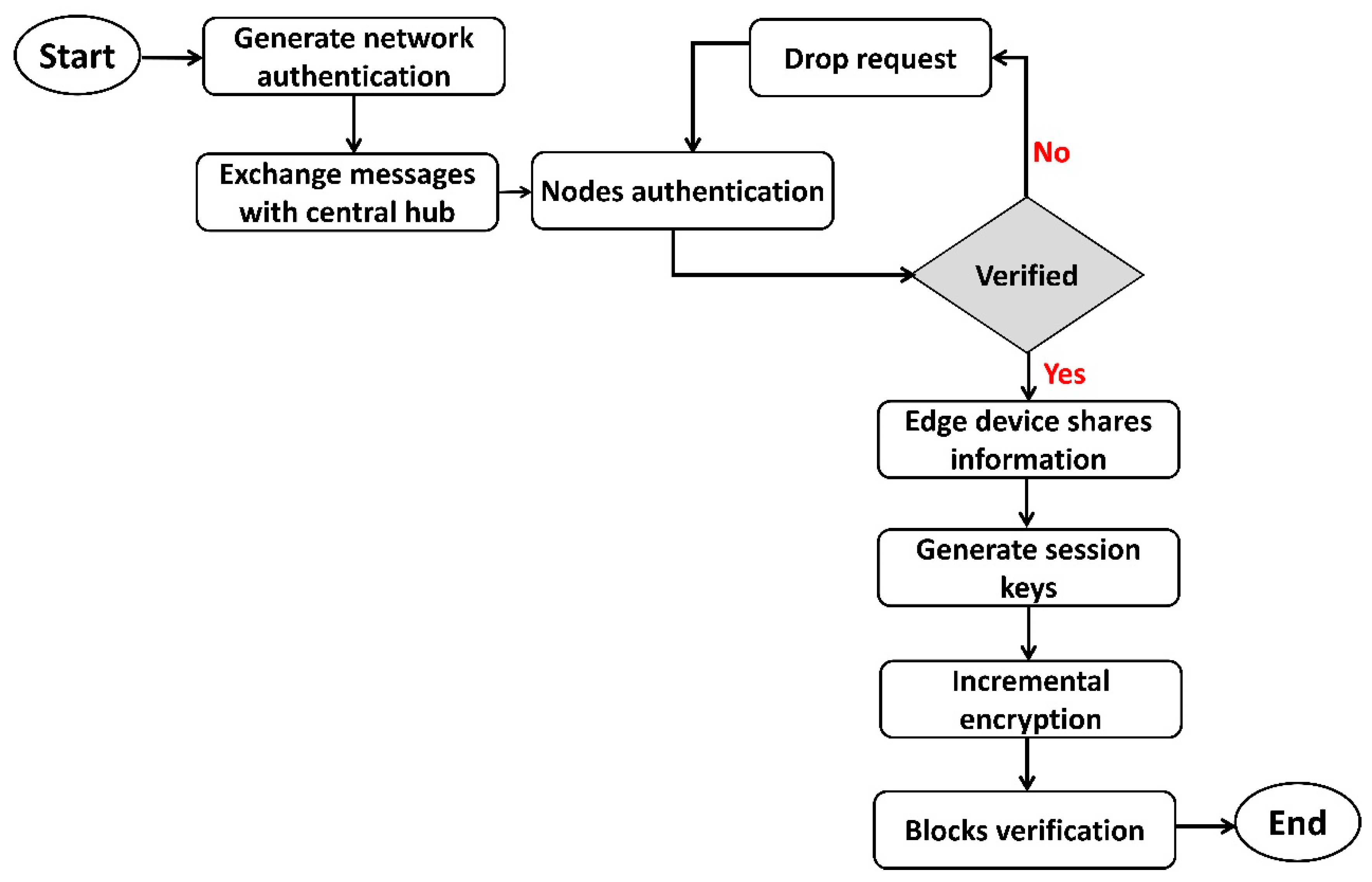
- Authentic nodes: This state determines the validity of devices in terms of authentication. If nodes are declared authentic, then communication is allowed by the system; otherwise, alert messages are recorded in the local tables.
- Secured sessions: In this state, the system attains data privacy with integrity using session keys and security methods.
3.3. Model Discussion
| Algorithm 1: Data-driven secured optimization model using dynamic programming |
| Step 1: Procedure Sec_data_driven Step 1: Network-setup Step 2: Multistage graphs with nodes and edges Step 3: Compute the traffic by exploring = Step 4: Compute = Step 5: Cost using objective function = + Step 6: Threshold evaluation for sending route request < Step 7: If the neighbor state is not equal to the destination then Repeat Steps 3 to 6 End if Step 8: Performs network authentication Step 9: If authenticity is verified then data transmission Else Drop the request packet End if Step 10: Generate random keys and perform a security function Step 11: If all data packets are delivered to the destination then Send ACK to the source device Else Perform incremental encryption End if Step 12: End procedure |
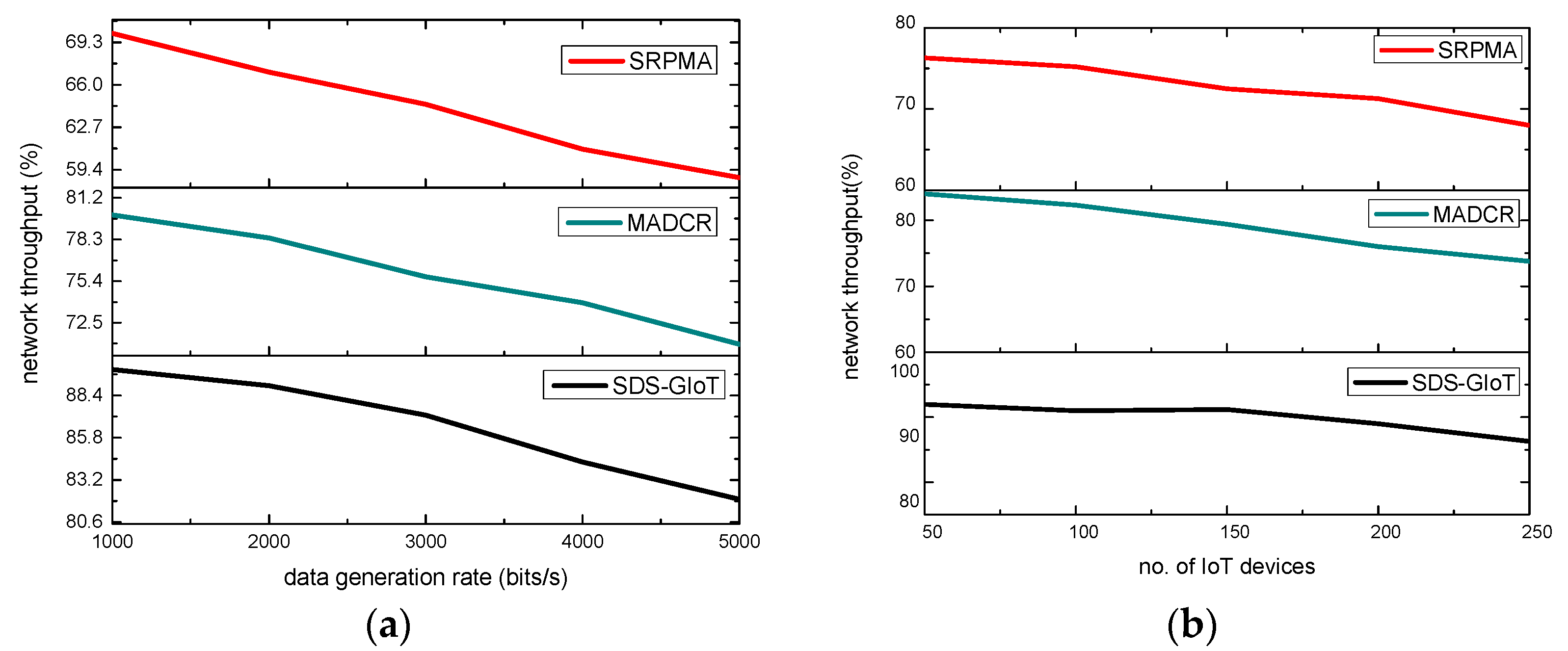
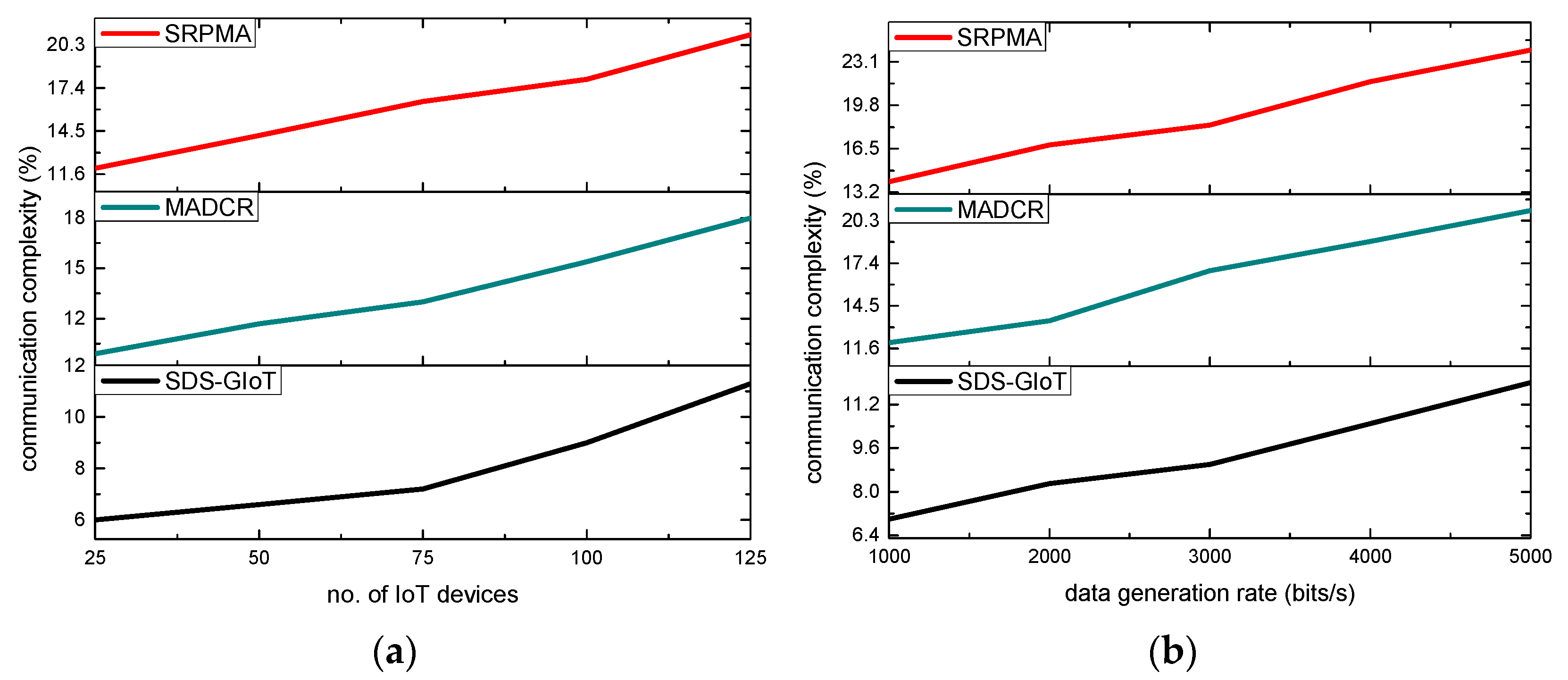
4. Simulations
Results and Discussion
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Mishra, S.; Tyagi, A.K. The role of machine learning techniques in internet of things-based cloud applications. In Artificial Intelligence-Based Internet of Things Systems; Springer: Cham, Switzerland, 2022; pp. 105–135. [Google Scholar]
- Rehman, A.; Haseeb, K.; Saba, T.; Lloret, J.; Ahmed, Z. Mobility Support 5G Architecture with Real-Time Routing for Sustainable Smart Cities. Sustainability 2021, 13, 9092. [Google Scholar] [CrossRef]
- Kamilaris, A.; Pitsillides, A. Mobile Phone Computing and the Internet of Things: A Survey. IEEE Internet Things J. 2016, 3, 885–898. [Google Scholar] [CrossRef]
- Muzammal, S.M.; Murugesan, R.K.; Jhanjhi, N.Z. A Comprehensive Review on Secure Routing in Internet of Things: Mitigation Methods and Trust-Based Approaches. IEEE Internet Things J. 2020, 8, 4186–4210. [Google Scholar] [CrossRef]
- Ávila, K.; Sanmartin, P.; Jabba, D.; Gómez, J. An analytical survey of attack scenario parameters on the techniques of attack mitigation in WSN. Wirel. Pers. Commun. 2021, 122, 3687–3717. [Google Scholar] [CrossRef]
- Haseeb, K.; Saba, T.; Rehman, A.; Ahmed, Z.; Song, H.H.; Wang, H.H. Trust management with fault-tolerant supervised routing for smart cities using internet of things. IEEE Internet Things J. 2022. [Google Scholar] [CrossRef]
- Sarkar, N.I.; Gul, S. Green computing and internet of things for smart cities: Technologies, challenges, and implementation. In Green Computing in Smart Cities: Simulation and Techniques; Springer: Cham, Switzerland, 2021; pp. 35–50. [Google Scholar]
- Gupta, U.; Elgamal, M.; Hills, G.; Wei, G.Y.; Lee HH, S.; Brooks, D.; Wu, C.J. ACT: Designing sustainable computer systems with an architectural carbon modeling tool. In Proceedings of the 49th Annual International Symposium on Computer Architecture, New York, NY, USA, 18–22 June 2022. [Google Scholar]
- Okewu, E.; Misra, S.; Maskeliūnas, R.; Damaševičius, R.; Fernandez-Sanz, L. Optimizing Green Computing Awareness for Environmental Sustainability and Economic Security as a Stochastic Optimization Problem. Sustainability 2017, 9, 1857. [Google Scholar] [CrossRef]
- Anand, P.; Singh, Y.; Selwal, A.; Alazab, M.; Tanwar, S.; Kumar, N. IoT Vulnerability Assessment for Sustainable Computing: Threats, Current Solutions, and Open Challenges. IEEE Access 2020, 8, 168825–168853. [Google Scholar] [CrossRef]
- Bibri, S.E.; Krogstie, J. Environmentally data-driven smart sustainable cities: Applied innovative solutions for energy efficiency, pollution reduction, and urban metabolism. Energy Inform. 2020, 3, 1–59. [Google Scholar] [CrossRef]
- Subramanian, N.; Jeyaraj, A. Recent security challenges in cloud computing. Comput. Electr. Eng. 2018, 71, 28–42. [Google Scholar] [CrossRef]
- Gai, K.; Guo, J.; Zhu, L.; Yu, S. Blockchain Meets Cloud Computing: A Survey. IEEE Commun. Surv. Tutor. 2020, 22, 2009–2030. [Google Scholar] [CrossRef]
- Kumar, M.; Sharma, S.; Goel, A.; Singh, S. A comprehensive survey for scheduling techniques in cloud computing. J. Netw. Comput. Appl. 2019, 143, 1–33. [Google Scholar] [CrossRef]
- Marcu, I.; Suciu, G.; Bălăceanu, C.; Vulpe, A.; Drăgulinescu, A.-M. Arrowhead Technology for Digitalization and Automation Solution: Smart Cities and Smart Agriculture. Sensors 2020, 20, 1464. [Google Scholar] [CrossRef]
- Haseeb, K.; Rehman, A.; Saba, T.; Bahaj, S.A.; Lloret, J. Device-to-Device (D2D) Multi-Criteria Learning Algorithm Using Secured Sensors. Sensors 2022, 22, 2115. [Google Scholar] [CrossRef]
- Gill, S.S.; Tuli, S.; Xu, M.; Singh, I.; Singh, K.V.; Lindsay, D.; Tuli, S.; Smirnova, D.; Singh, M.; Jain, U.; et al. Transformative effects of IoT, Blockchain and Artificial Intelligence on cloud computing: Evolution, vision, trends and open challenges. Internet Things 2019, 8, 100118. [Google Scholar] [CrossRef]
- Majid, M.; Habib, S.; Javed, A.R.; Rizwan, M.; Srivastava, G.; Gadekallu, T.R.; Lin, J.C.-W. Applications of Wireless Sensor Networks and Internet of Things Frameworks in the Industry Revolution 4.0: A Systematic Literature Review. Sensors 2022, 22, 2087. [Google Scholar] [CrossRef]
- Venckauskas, A.; Stuikys, V.; Damasevicius, R.; Jusas, N. Modelling of Internet of Things units for estimating security-energy-performance relationships for quality of service and environment awareness. Secur. Commun. Netw. 2016, 9, 3324–3339. [Google Scholar] [CrossRef]
- Stergiou, C.; Psannis, K.E.; Gupta, B.B.; Ishibashi, Y. Security, privacy & efficiency of sustainable Cloud Computing for Big Data & IoT. Sustain. Comput. Inform. Syst. 2018, 19, 174–184. [Google Scholar] [CrossRef]
- Farhan, L.; Kharel, R.; Kaiwartya, O.; Hammoudeh, M.; Adebisi, B. Towards green computing for Internet of things: Energy oriented path and message scheduling approach. Sustain. Cities Soc. 2018, 38, 195–204. [Google Scholar] [CrossRef]
- Sánchez-Corcuera, R.; Nuñez-Marcos, A.; Sesma-Solance, J.; Bilbao-Jayo, A.; Mulero, R.; Zulaika, U.; Azkune, G.; Almeida, A. Smart cities survey: Technologies, application domains and challenges for the cities of the future. Int. J. Distrib. Sens. Netw. 2019, 15, 1550147719853984. [Google Scholar] [CrossRef]
- Haque, A.K.M.B.; Bhushan, B.; Dhiman, G. Conceptualizing smart city applications: Requirements, architecture, security issues, and emerging trends. Expert Syst. 2021, 39. [Google Scholar] [CrossRef]
- Bhushan, B.; Khamparia, A.; Sagayam, K.M.; Sharma, S.K.; Ahad, M.A.; Debnath, N.C. Blockchain for smart cities: A review of architectures, integration trends and future research directions. Sustain. Cities Soc. 2020, 61, 102360. [Google Scholar] [CrossRef]
- Fernandez-Carames, T.M.; Fraga-Lamas, P. A Review on the Use of Blockchain for the Internet of Things. IEEE Access 2018, 6, 32979–33001. [Google Scholar] [CrossRef]
- Čolaković, A.; Hadžialić, M. Internet of Things (IoT): A review of enabling technologies, challenges, and open research issues. Comput. Netw. 2018, 144, 17–39. [Google Scholar] [CrossRef]
- Yarinezhad, R.; Azizi, S. An energy-efficient routing protocol for the Internet of Things networks based on geographical location and link quality. Comput. Netw. 2021, 193, 108116. [Google Scholar] [CrossRef]
- Sennan, S.; Ramasubbareddy, S.; Balasubramaniyam, S.; Nayyar, A.; Kerrache, C.A.; Bilal, M. MADCR: Mobility aware dynamic clustering-based routing protocol in Internet of Vehicles. China Commun. 2021, 18, 69–85. [Google Scholar] [CrossRef]
- Sun, Z.; Wei, M.; Zhang, Z.; Qu, G. Secure Routing Protocol based on Multi-objective Ant-colony-optimization for wireless sensor networks. Appl. Soft Comput. 2019, 77, 366–375. [Google Scholar] [CrossRef]
- Kalidoss, T.; Rajasekaran, L.; Kanagasabai, K.; Sannasi, G.; Kannan, A. QoS Aware Trust Based Routing Algorithm for Wireless Sensor Networks. Wirel. Pers. Commun. 2019, 110, 1637–1658. [Google Scholar] [CrossRef]
- Wang, X.; Lu, Y. Sustainable and Efficient Fog-assisted IoT Cloud Based Data Collection and Delivery for Smart Cities. IEEE Trans. Sustain. Comput. 2022. [Google Scholar] [CrossRef]


| Parameters | Values |
|---|---|
| Simulation area | 1000 m × 1000 m |
| Devices distribution | Random |
| IoT devices | 25–125 |
| Data generation rates | 1000–5000 bits/s |
| Transmission power | 10 m |
| Initial energy | 3–6 j |
| Simulations | 30 |
| Round interval | 20 s |
| Data flow | CBR |
| Sink node | 2 |
| Edge nodes | 10 |
| Size of control packet | 256 bits |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Saba, T.; Rehman, A.; Haseeb, K.; Bahaj, S.A.; Damaševičius, R. Sustainable Data-Driven Secured Optimization Using Dynamic Programming for Green Internet of Things. Sensors 2022, 22, 7876. https://doi.org/10.3390/s22207876
Saba T, Rehman A, Haseeb K, Bahaj SA, Damaševičius R. Sustainable Data-Driven Secured Optimization Using Dynamic Programming for Green Internet of Things. Sensors. 2022; 22(20):7876. https://doi.org/10.3390/s22207876
Chicago/Turabian StyleSaba, Tanzila, Amjad Rehman, Khalid Haseeb, Saeed Ali Bahaj, and Robertas Damaševičius. 2022. "Sustainable Data-Driven Secured Optimization Using Dynamic Programming for Green Internet of Things" Sensors 22, no. 20: 7876. https://doi.org/10.3390/s22207876
APA StyleSaba, T., Rehman, A., Haseeb, K., Bahaj, S. A., & Damaševičius, R. (2022). Sustainable Data-Driven Secured Optimization Using Dynamic Programming for Green Internet of Things. Sensors, 22(20), 7876. https://doi.org/10.3390/s22207876








