An Efficient Key Management Technique for the Internet of Things
Abstract
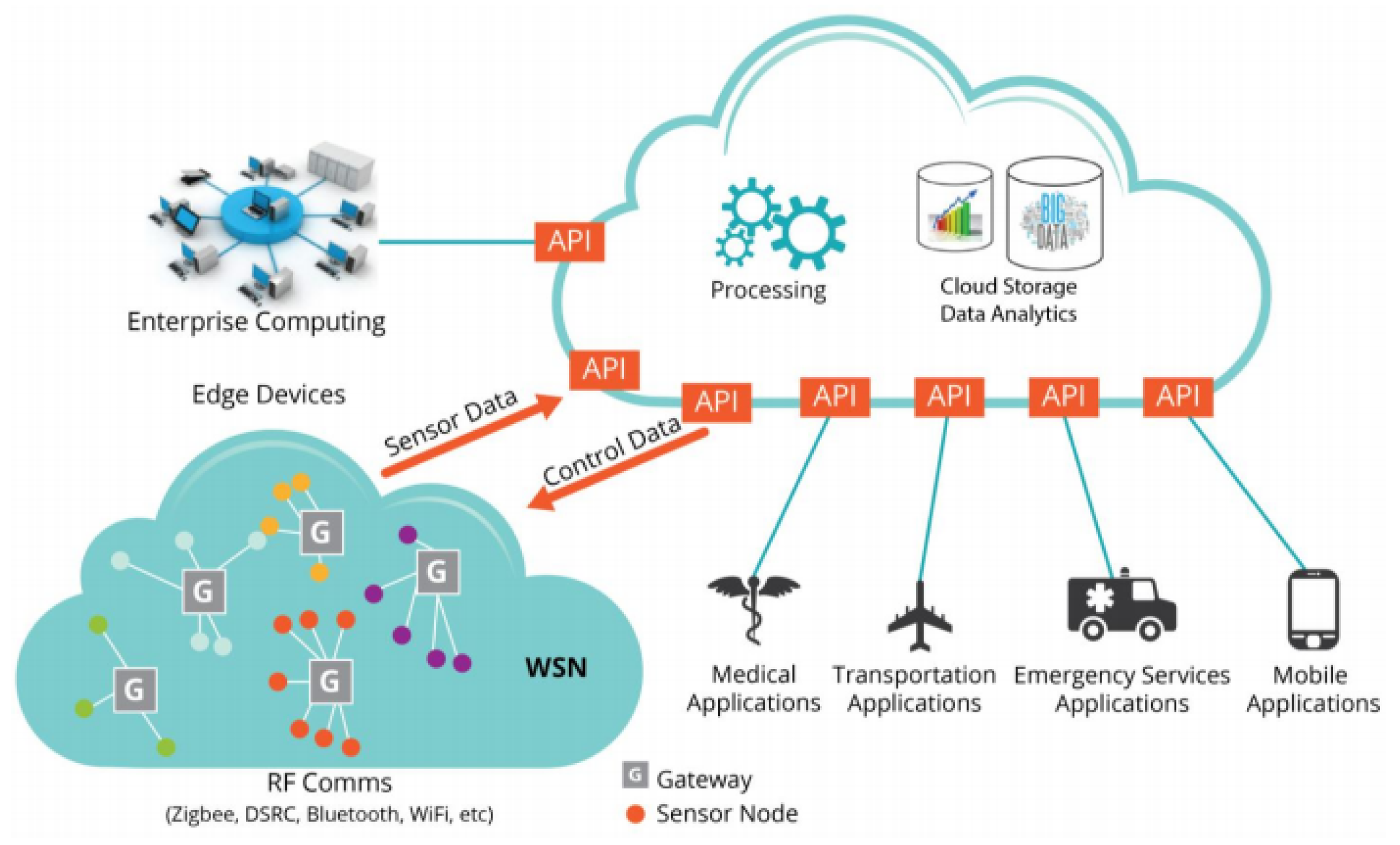
1. Introduction
2. Related Works
2.1. Mutual Key Management Technique
2.2. Group Key Management Technique
2.3. XOR Based Key Management
2.4. ECC/ECDH Based Key Management
2.5. CA-Less Key Management
3. Proposed Method
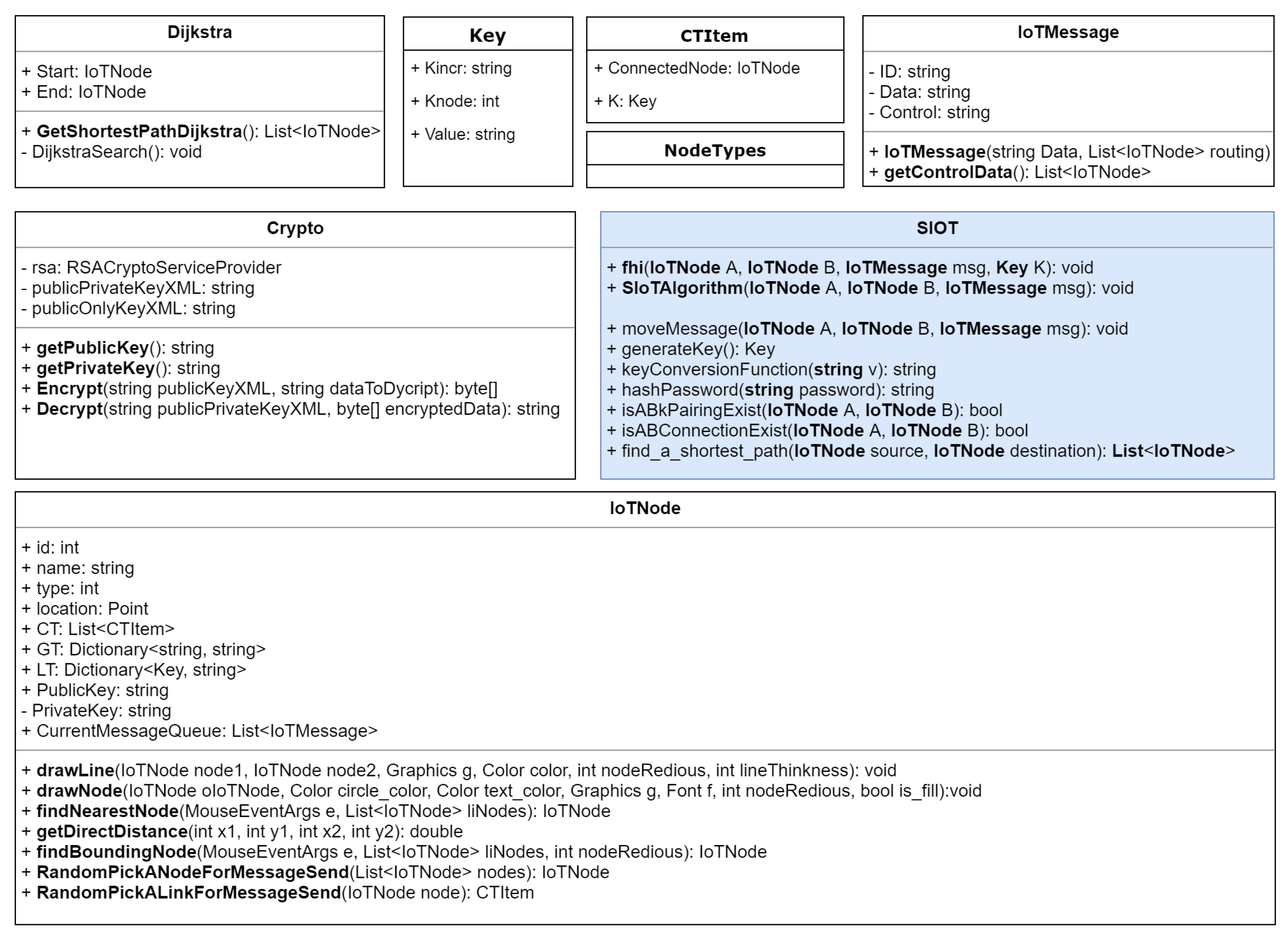
3.1. Proposed Key Management Process
3.1.1. Key Sharing Process
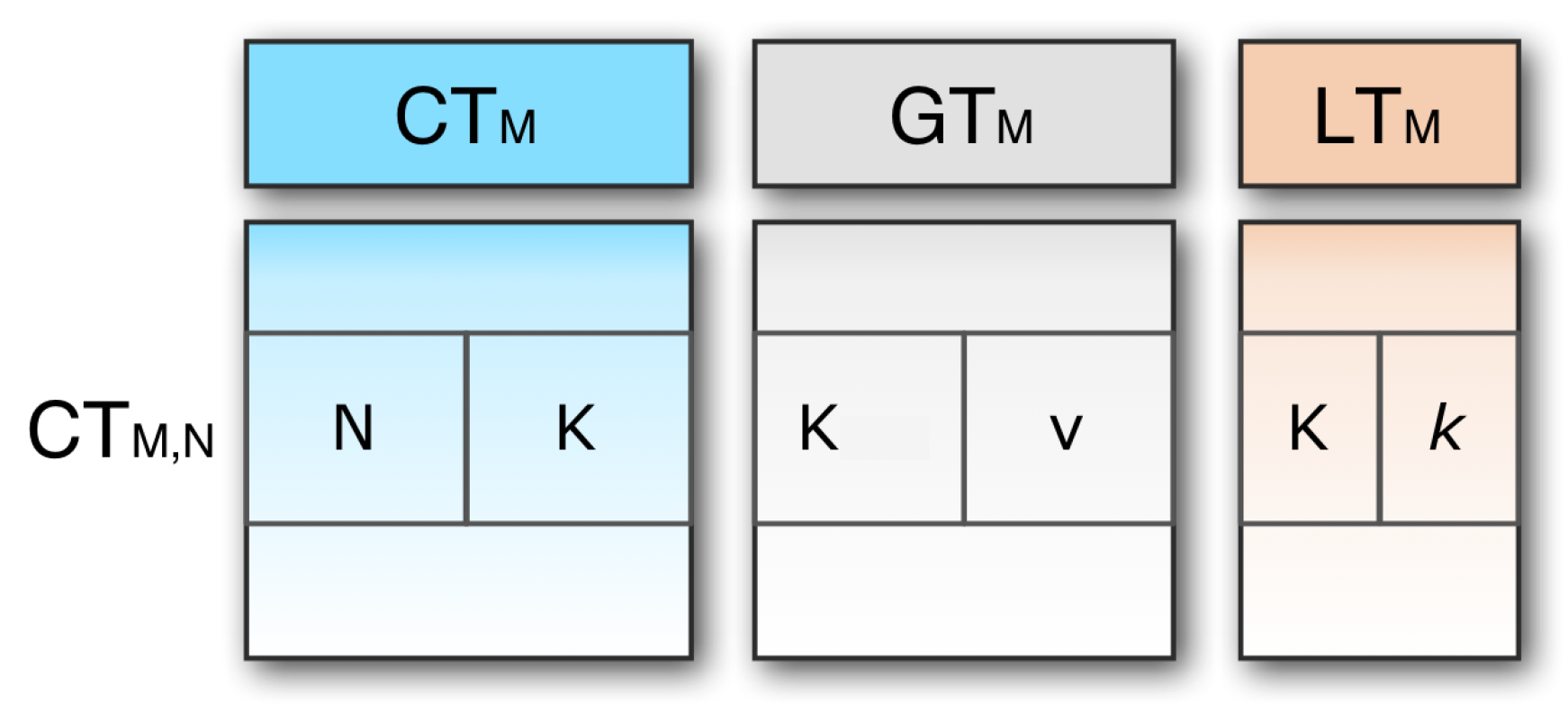
3.1.2. Key-Table Structure
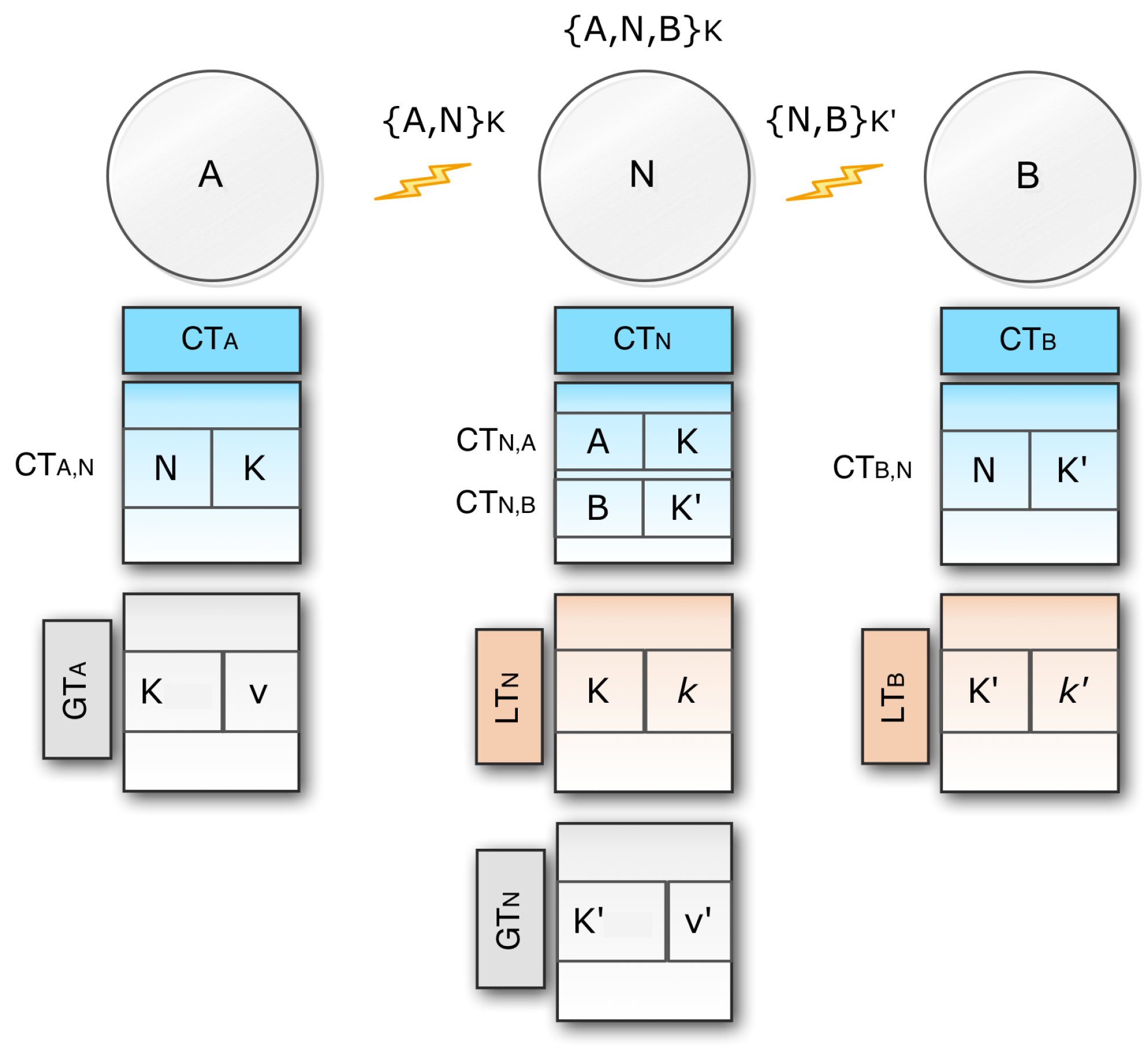
- Connection table (): This table contains a single entry for each pair of linked nodes. The row is node N and key K. It should be remembered here that and carry the same key as the two-directional links. With respect to , and are called the outgoing and incoming connection respectively.
- Global key table (): This table allocates one entry for each key K. Each entry has two parts: the key K, and this key’s value v. The name of this table is global because the table contains the information that is used by the external nodes. is needed because if an origin node tries to send a message to a destination that has not previously been recorded, communication will be defined by means of the global key table.
- Local key table (): This table contains one single entry created by another node for each local key K. The name of this table is local because only the current node uses this table information, and no information goes outside of this table from the current node. All the incoming connections are stored in this table. As the source node has no incoming connection, it does not require any local table. It has only two tables: the connection table and the global table. Similarly, the destination node has no outgoing connection, so it does not require any global key table.
3.1.3. Direct Message Transfer
- When exists in then exists in as well, this means that the relation is two-way. If any bidirectional connection exists, this is represented by . If there is , the key setup is ready to send the message.
- If exists but does not exist, A may use the correct global key to send a message to B. When B receives K from A, it looks up for the reverse connection in its connection table. If no connection exists, it needs to add values to its local and connection table.
- If does not exist, then A needs to generate a new key K and finally needs to store in its global table . After adding the entry to its global key A, it also adds to its connection table . Lastly A calculates the value and send the pair to node B. If B collects , it then saves it for in its local table. Through submitting a constructive return message from B to A, the key setup will be closed. Eventually, the key configuration is completed, so A may send a message to B by using K to encrypt the control part of the message when B decrypts the message.
- If B is the destination node, then it also decrypts the data part of the message by using its private key. In this way, the data part is protected using the public-key encryption system, and the control part is protected by using the symmetric key encryption system.
3.1.4. Message Transfer Via Intermediate Nodes
- In this scenario node A sends a message m through an intermediate node N to end node B. So for bidirectional connections between A and N, A and N have and respectively. Similarly, for bidirectional connections between N and B, N and B provide and .
- A uses the link to send a message to N, and N uses the link to send a message to B.
- Now, if A wants to send a message to B, it will first pair with A and N with the same mechanism we talked about in the case of a direct link. When the message is received by N, it combines with B to send the message in the same manner to B. Eventually, the secure communication network is enabled.
3.2. Key Generation and Distribution Process
| Algorithm 1:(A, B, m) |
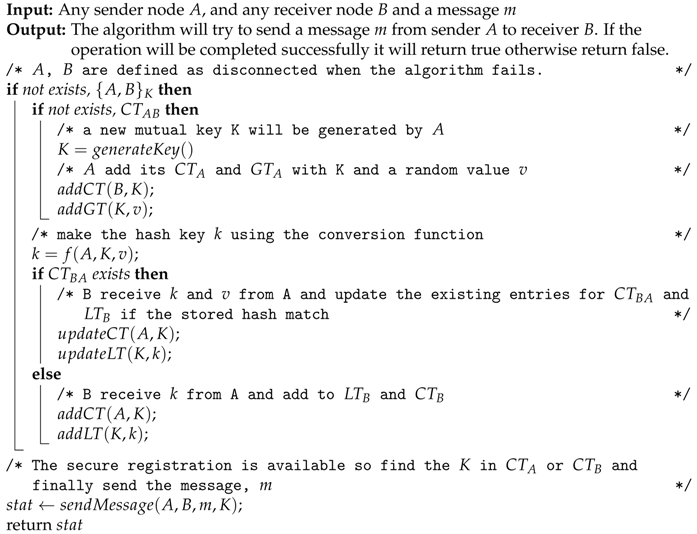 |
3.2.1. Space Complexity
| Algorithm 2:(A, B, m, K) |
| Input: Sender node A, receiver node B, message m and mutual key K |
| Output: True if the message sending operation completed successfully, otherwise return false |
| /* perform encryption operation */ |
| extract control part from m and encrypt the control part using K; Finally merge the encrypted control part with the message m |
| /* Node A transmits the encrypted message to node B, where B receives it and decrypts the control part */ |
| /* If B receives the message successfully then return a positive acknoledgment |
| */ |
| return |
3.2.2. Time Complexity
3.3. Key Update Process
- Node A wants to change all its keys or a specific key. In the first stage, A checks for for all key entries, then submit message change commands to all link nodes with A that share the same key.
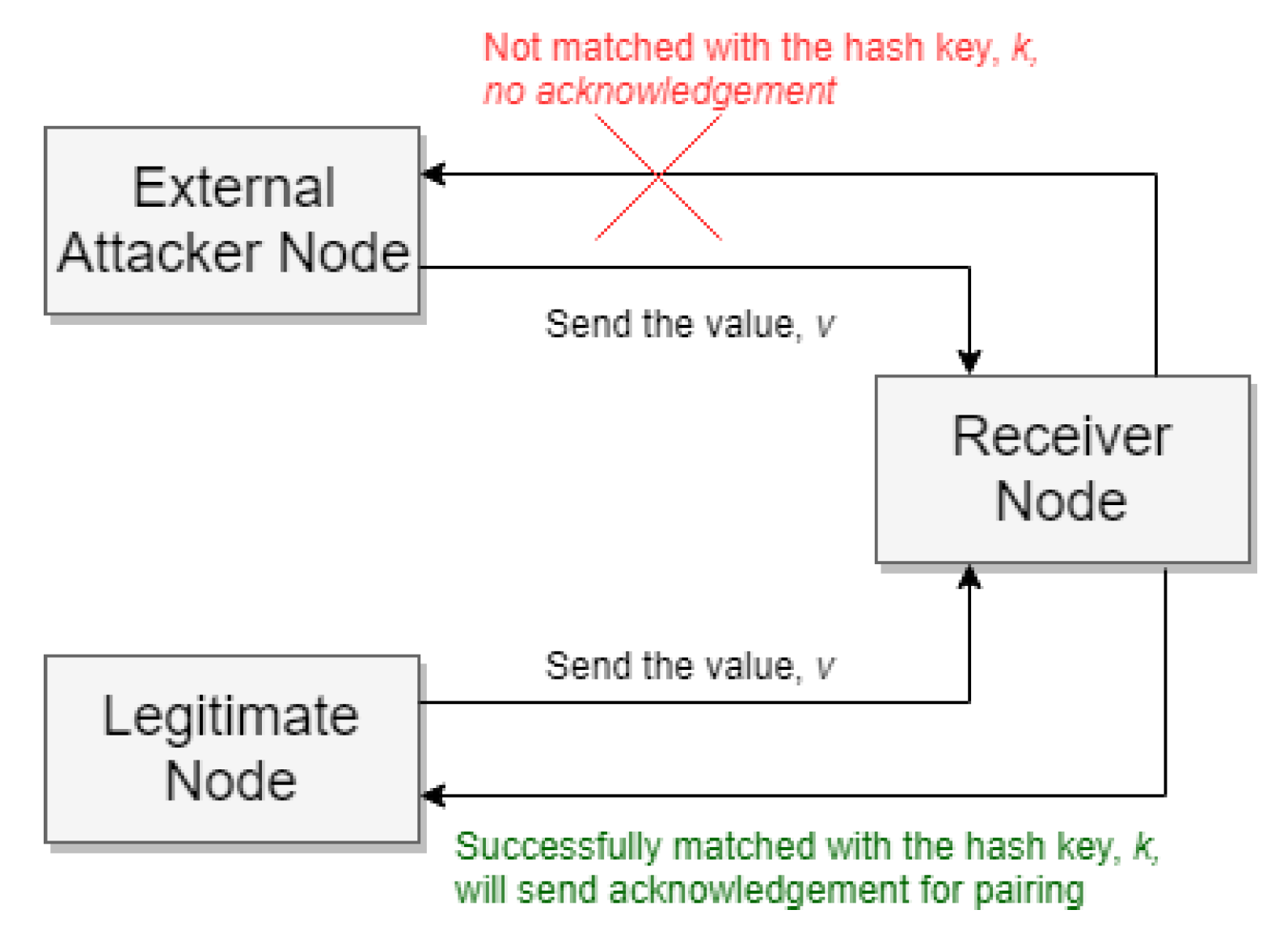
- Now say B gets a A change message. Using the hash key k and the value v that it previously stored in and tables, verifies this change message to ensure security. So B authenticates v with k. If no match is found, the key change request will be discarded by B. If found, then B updates its key entry in all associated tables.
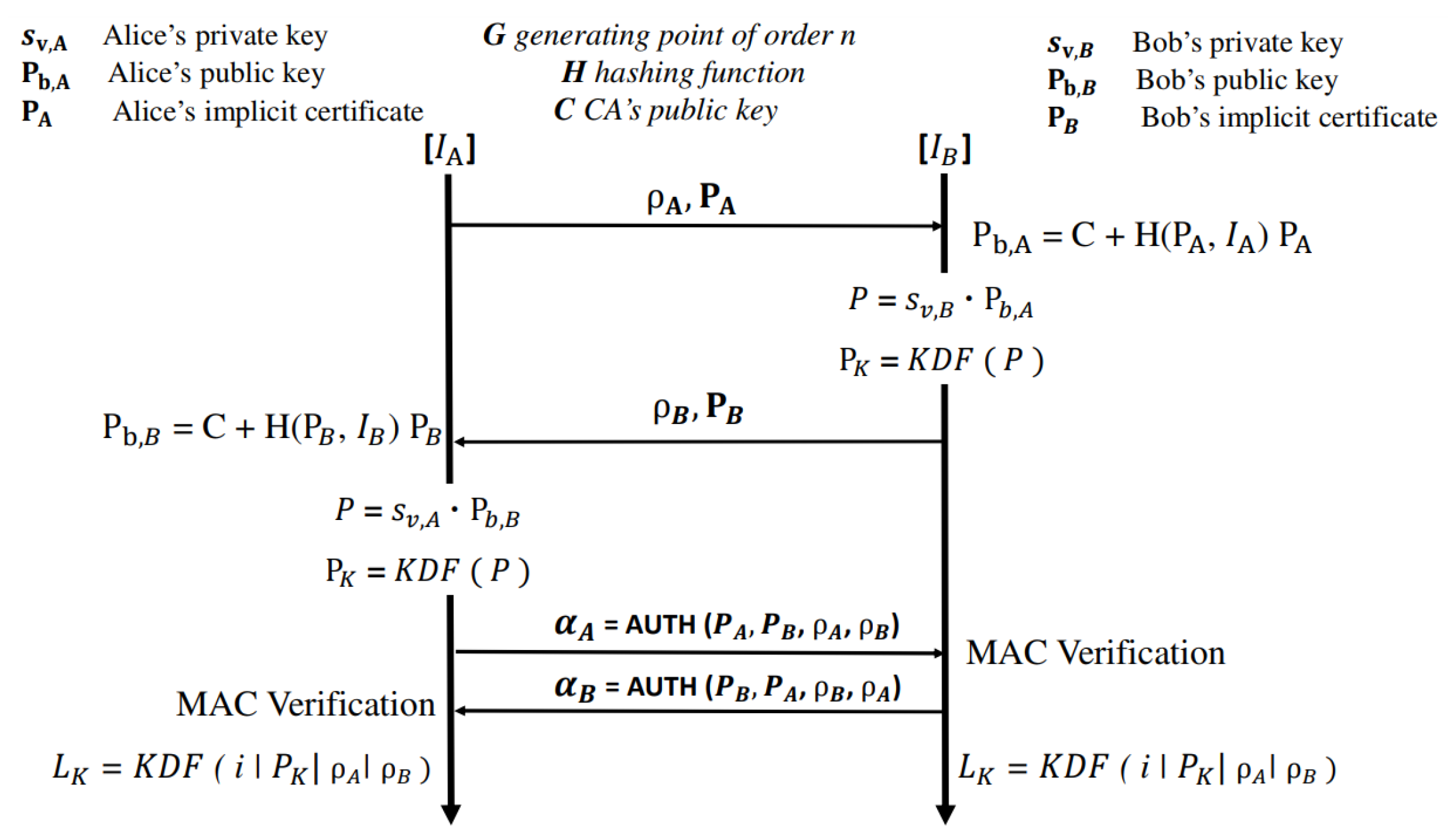
3.4. Secure Authentication
3.5. Robustness in Case of Malicious Attacks
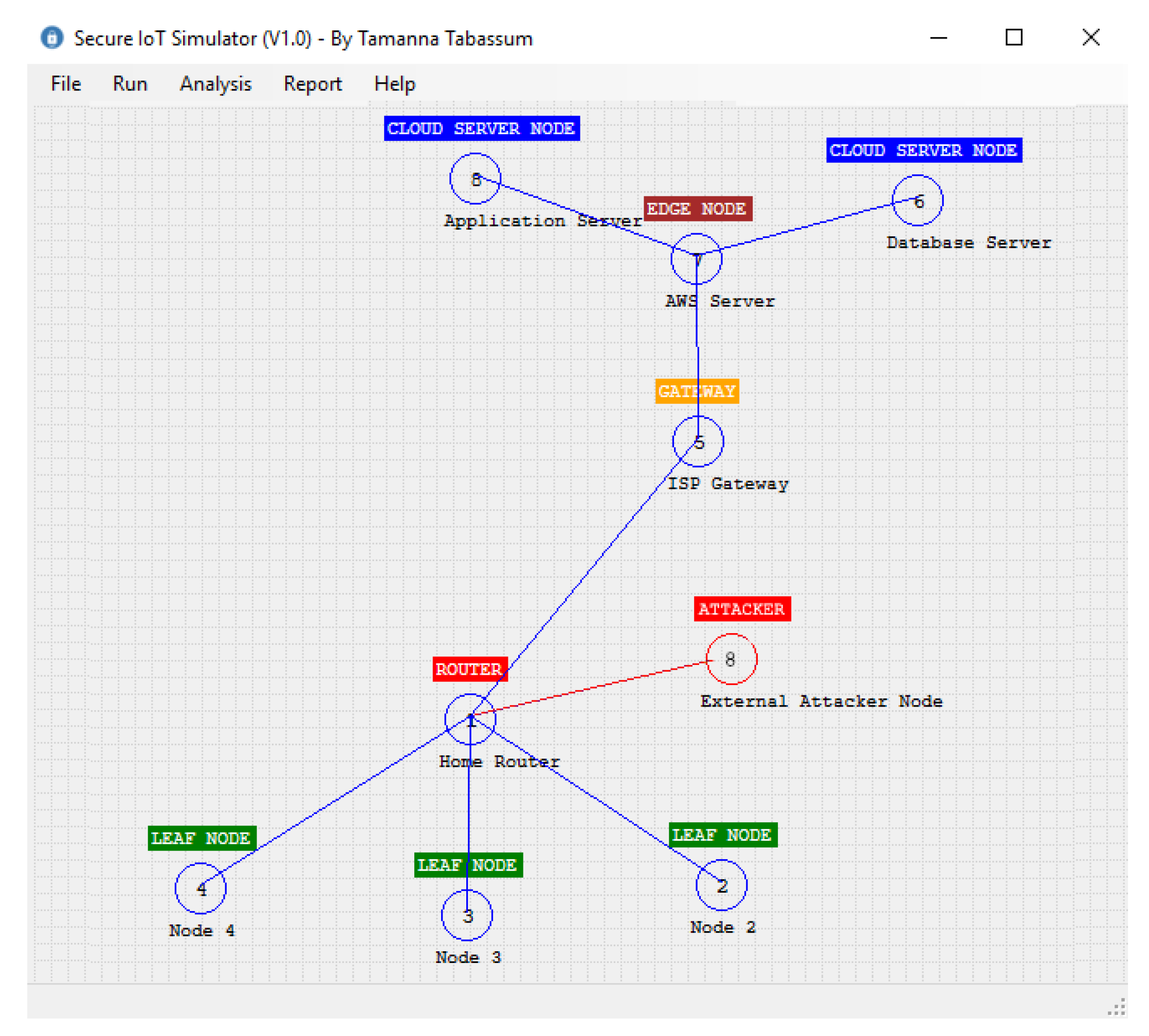
4. Implementation
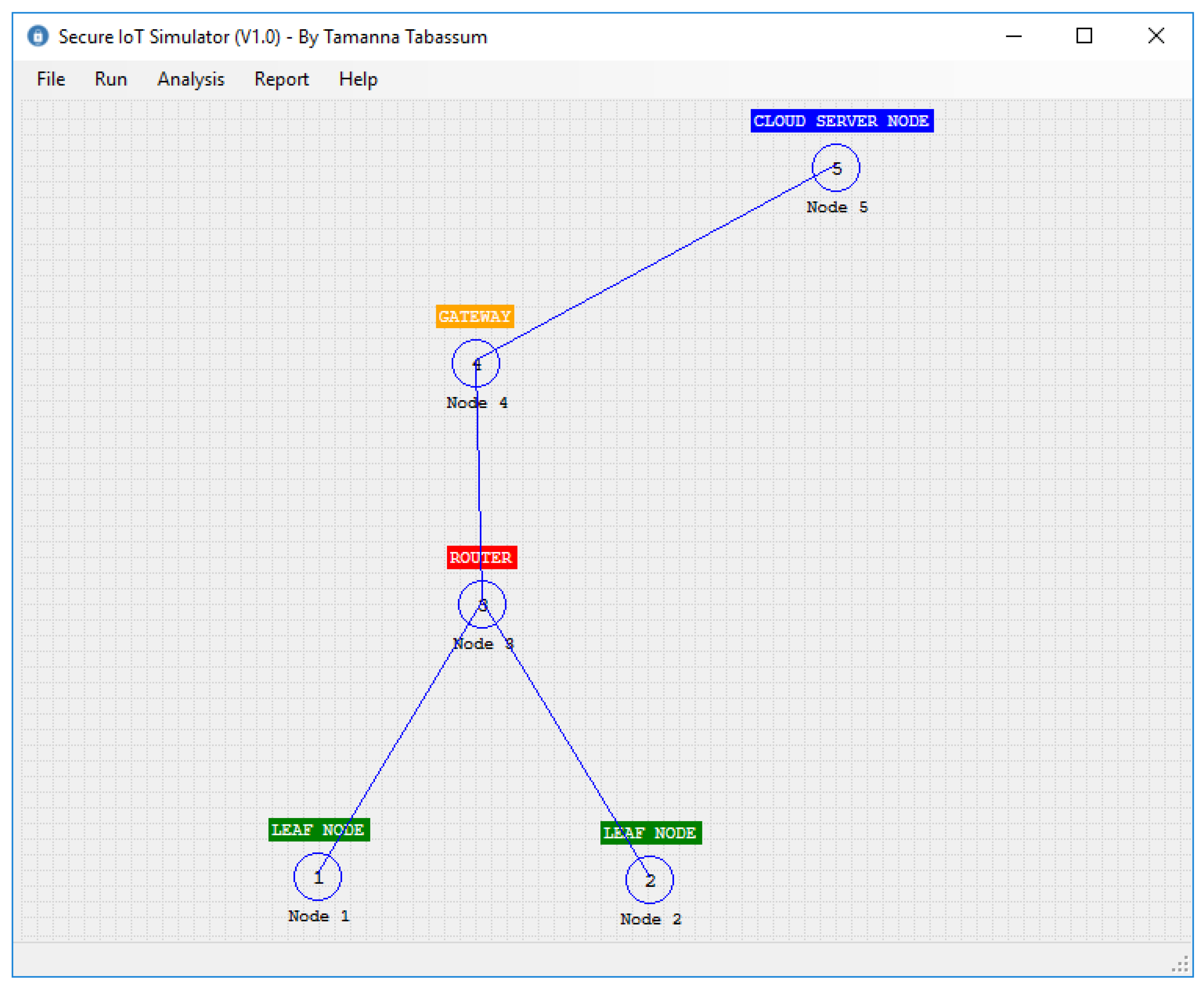
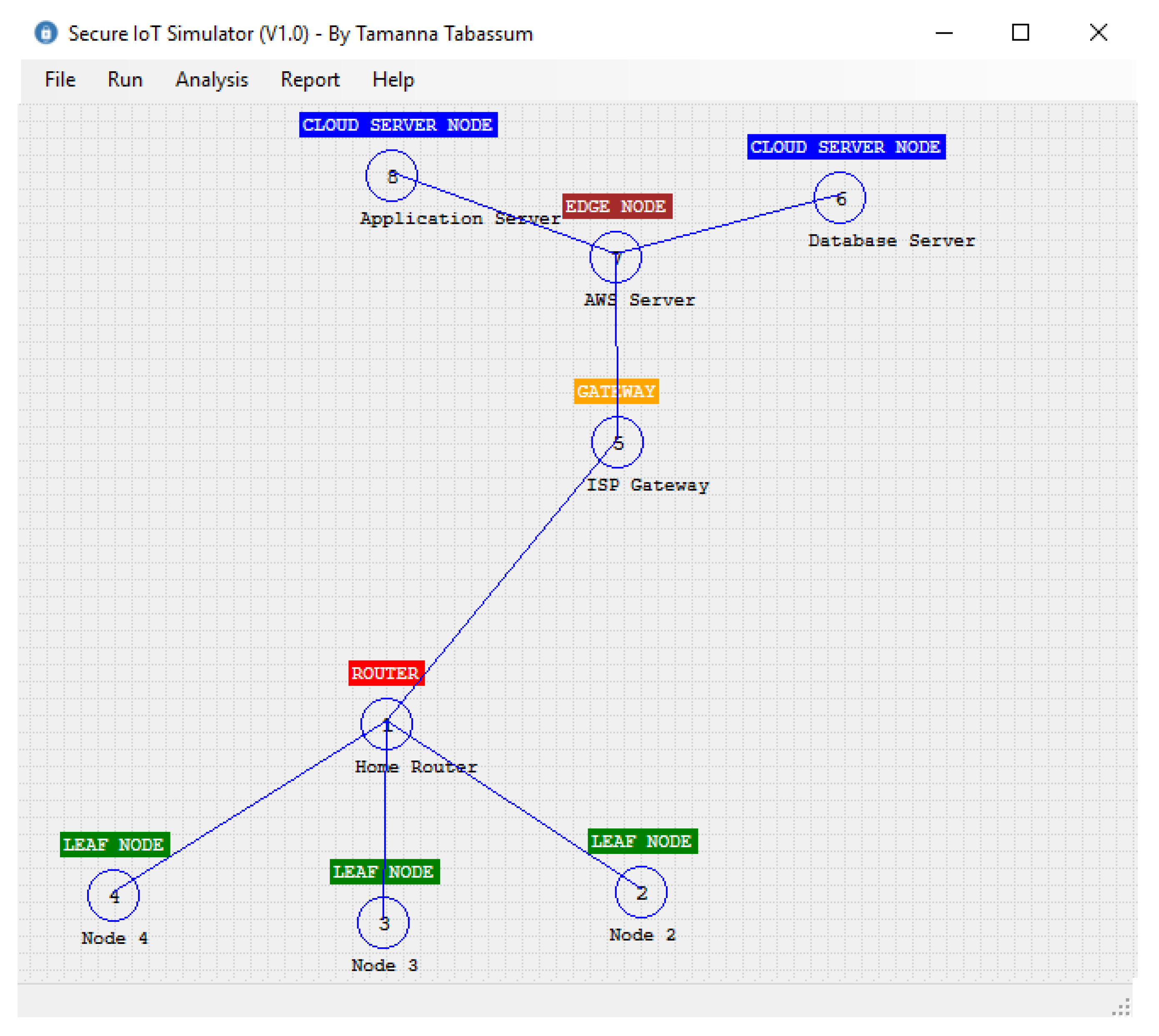
4.1. The Design of IoT Simulator
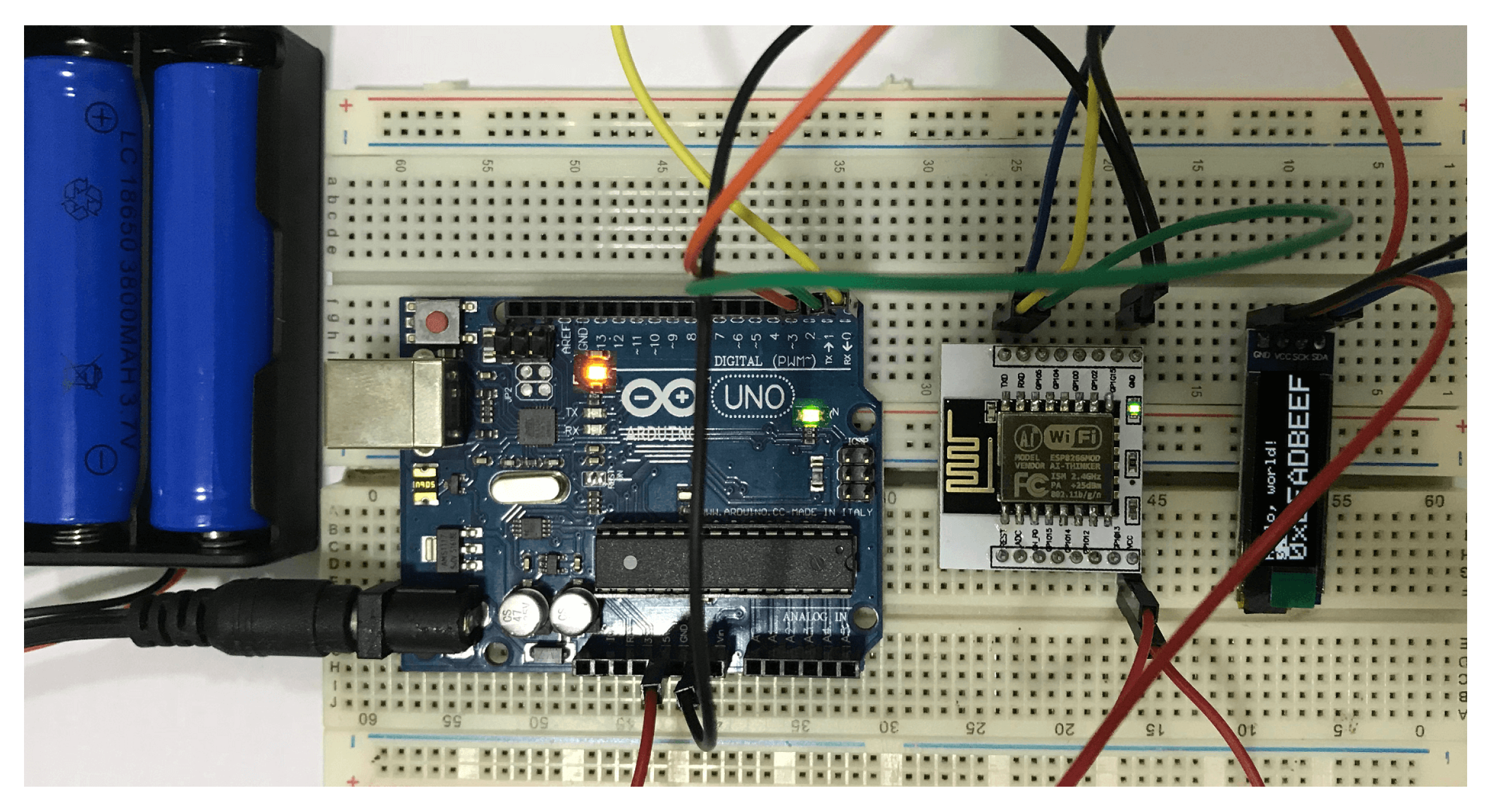
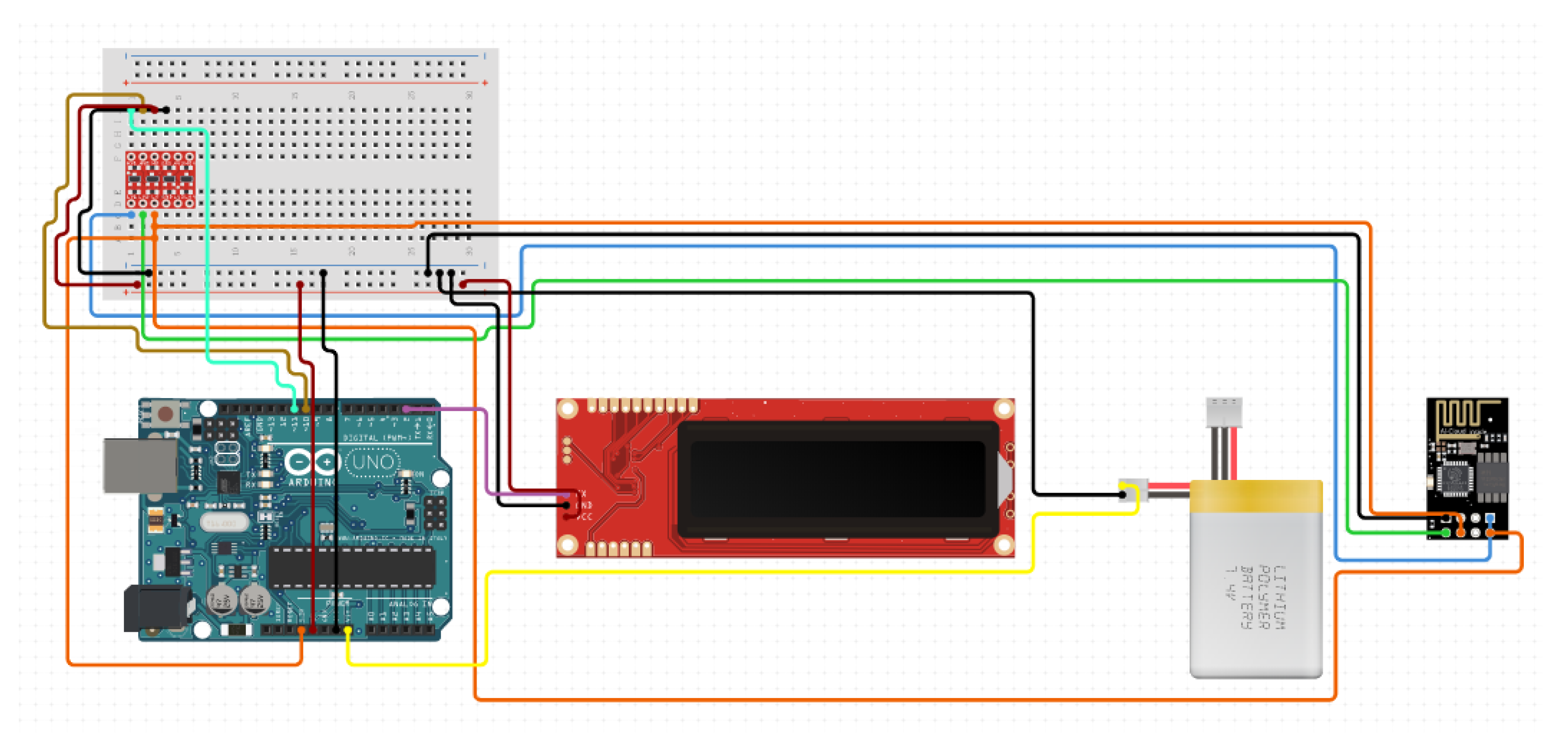
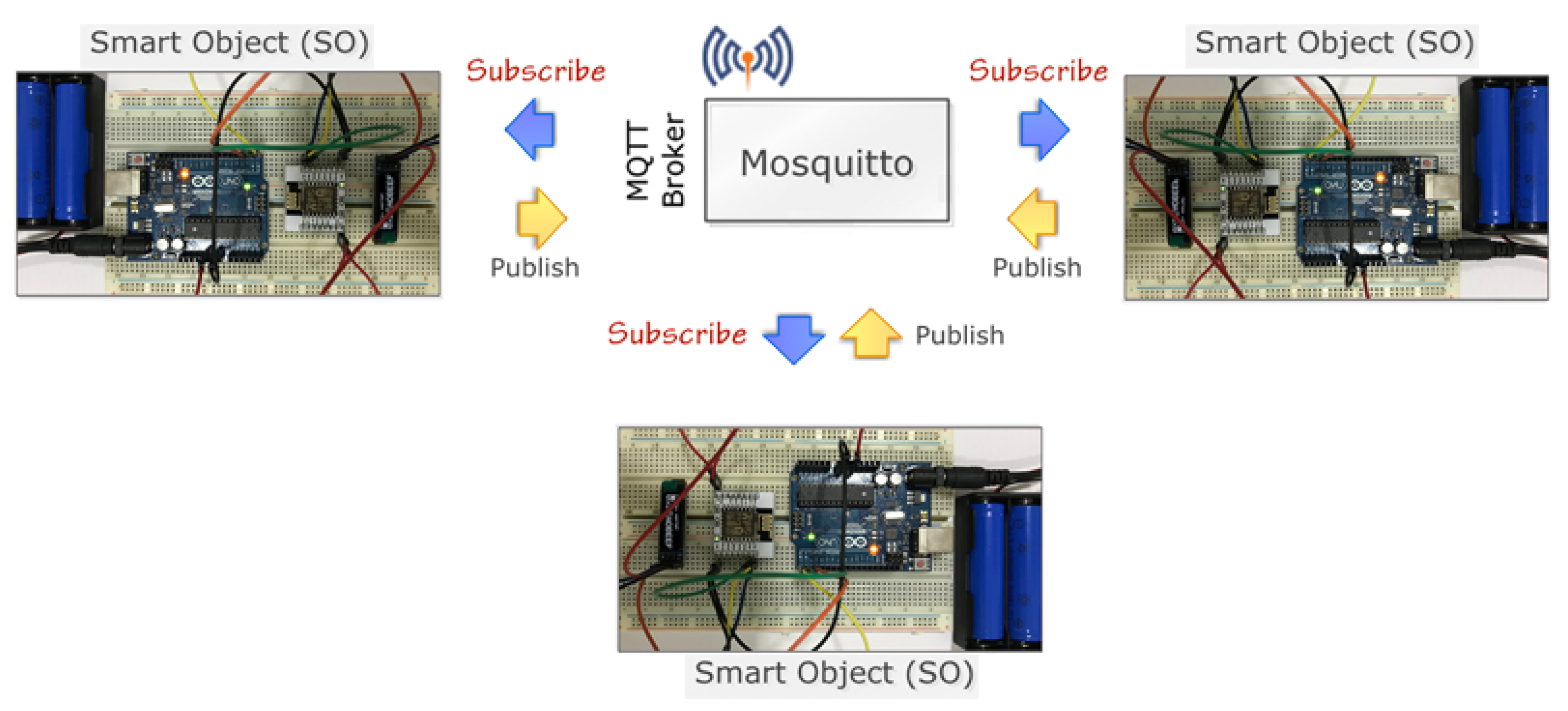
4.2. Prototype System
5. Experimental Results
5.1. Smart Home Scenario
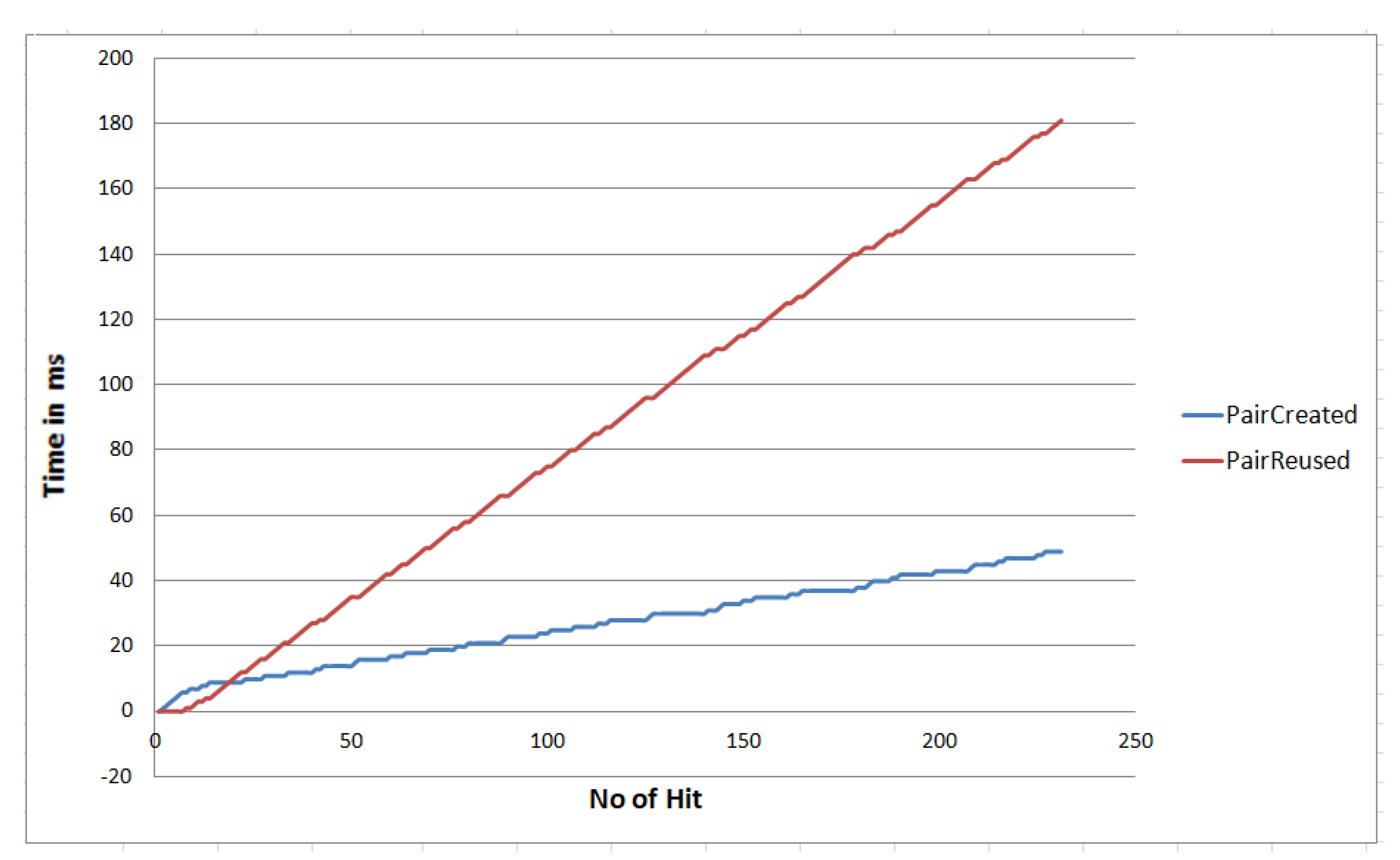
5.2. Performance
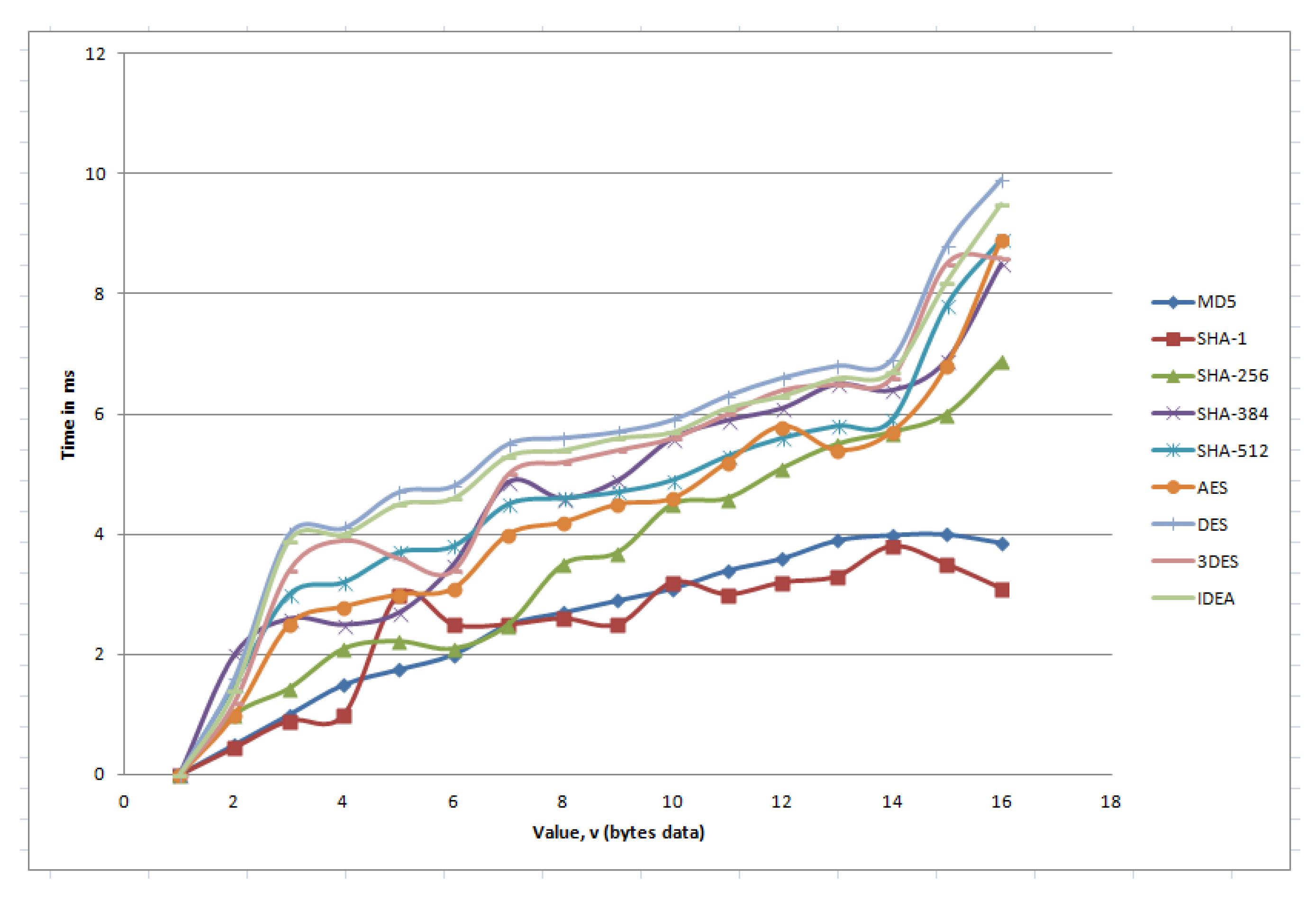
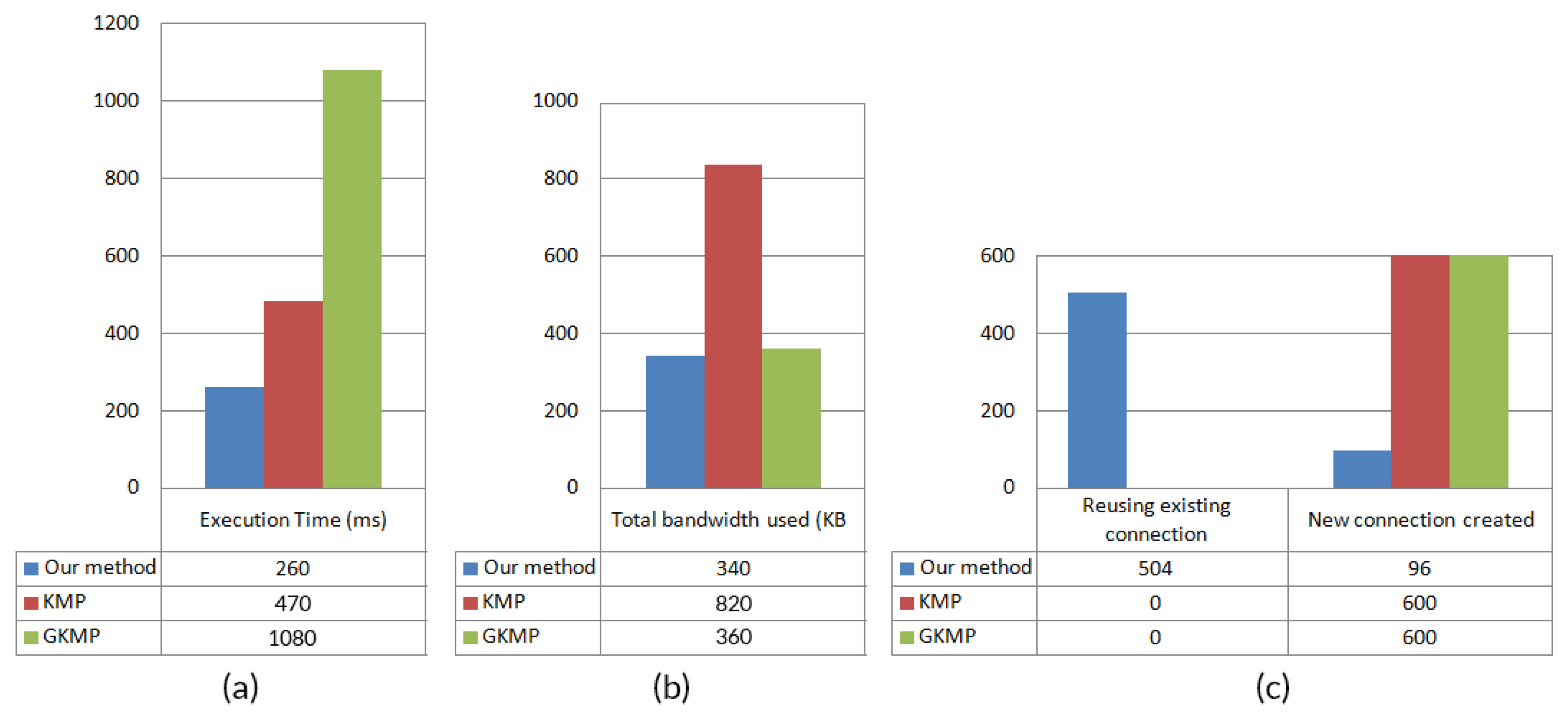
5.3. Effect on Different Key Conversion Function
5.4. Key Generation and Distribution Time
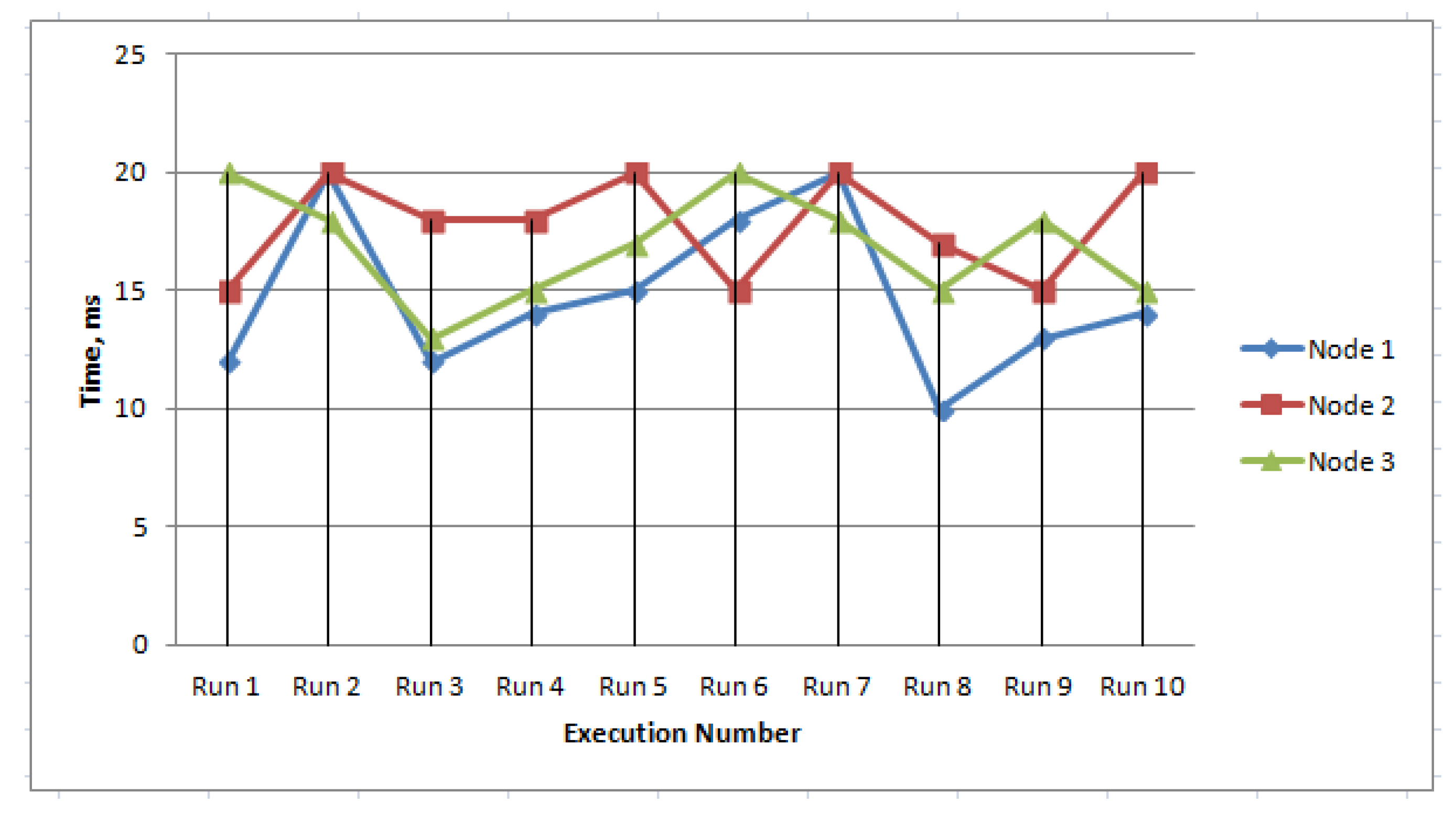
5.5. Service Response Analysis
5.6. Prevention of Attacks
- Man-in-the middle attack (MITM): In MITM, an adversary impersonates a valid device. It then transmits reply messages to authenticated servers. In our case, this will happen if any malicious node is added to our network and receives messages from the source. If this happens, the malicious node can not decrypt the messages because the malicious node needs to know the private receiver key, which is not possible without the full control of the receiver node. If the receiver node is hacked, only the messages that are received by the receiver will be compromised, and there will be no effect on other messages that are received by other receivers.
- Passive attacks: This type of attack highlights unauthorized listening to the routing packets or silently refusing execution of the requested function. It might be an attempt by the attacker to extrapolate data about the positions of each node with respect to the others. Such an attack is usually impossible to detect, since the attacker only attempts to discover valuable information by listening to the routed traffic instead of disrupting the operation of a routing mechanism. In our key management approach, it is not possible to listen to the routing information as for every message transfer the source node encrypts the control information (containing the routing information) by using the shared key between the source and destination. One of the forms of passive attack is eavesdropping, in which case the eavesdropped message are easily detected by the receiver and are discarded as our communication channel is fully protected using the mutual key.
- Target-oriented attack: The traffic analysis based on the identity of a peer we are interested in is usually passive. After performing traffic analysis, an adversary can set a target peer and conduct an intensive attack against the peer. As an example, sending too much unwanted traffic to a specific peer to overwhelm communication and make the peer inactive in the network. A specific jamming signal can be set up for that specific peer to make the peer inactive in the network for the case of communication. We call such an attack target-oriented. Such attacks are often active. In our approach, this kind of attack is not possible as the destination node discards all incoming message from a source node if the mutual key is not matched. The process of how our algorithm discards any unauthorized sender is described in details in Section 3.5.
- Masquerade attack: In this attack, a malicious peer may pretend to be a valid target of a source by stealing the identity of the real target. Thus, a malicious peer may gain access to the data of the source. The easiest point of an entry for a masquerade peer is provided by a weak authentication between the source and the target. Once the malicious node passes the authentication process, it may be authorized by the source as a target to access its data. Similarly, a malicious node may falsely act as a source for a target. Therefore, a malicious node may be able to tamper with both exchanged data and the data exchange policy between a source and a target. In this attack, an attacker may drop, modify, or even forge the exchanged data to interrupt the data exchange between a source and a target. In our proposed method masquerade attack is not possible as if by any chance a malicious peer act as a valid target, the receiver node will discard the data as in our method for each pair of connection a different key is used. If it happens for the final destination node the destination node easily discards the malicious peer as the destination node easily detects it by decrypting the data part of the message by using its private key.
5.7. Performance Comparison with other Existing Works
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Singh, D.; Tripathi, G.; Jara, A.J. A survey of Internet-of-Things: Future vision, architecture, challenges and services. In Proceedings of the IEEE World Forum on Internet of Things (WF-IoT), Seoul, Korea, 6–8 March 2014; pp. 287–292. [Google Scholar]
- Sicari, S.; Rizzardi, A.; Cappiello, C.; Miorandi, D.; Coen-Porisini, A. Toward Data Governance in the Internet of Things. In New Advances in the Internet of Things; Springer: Berlin/Heidelberg, Germany, 2018; pp. 59–74. [Google Scholar]
- Barreto, L.; Celesti, A.; Villari, M.; Fazio, M.; Puliafito, A. An authentication model for IoT clouds. In Proceedings of the IEEE/ACM International Conference on Advances in Social Networks Analysis and Mining (ASONAM), Paris, France, 25–28 Auguest 2015; pp. 1032–1035. [Google Scholar]
- Benabdessalem, R.; Hamdi, M.; Kim, T.H. A survey on security models, techniques, and tools for the internet of things. In Proceedings of the 7th International Conference on Advanced Software Engineering and Its Applications, Haikou, China, 20–23 December 2014; pp. 44–48. [Google Scholar]
- García-Guerrero, E.; Inzunza-González, E.; López-Bonilla, O.; Cárdenas-Valdez, J.; Tlelo-Cuautle, E. Randomness improvement of chaotic maps for image encryption in a wireless communication scheme using PIC-microcontroller via Zigbee channels. Chaos, Solitons Fractals 2020, 133, 109646. [Google Scholar] [CrossRef]
- Zhang, Z.K.; Cho, M.C.Y.; Wang, C.W.; Hsu, C.W.; Chen, C.K.; Shieh, S. IoT security: Ongoing challenges and research opportunities. In Proceedings of the IEEE 7th International Conference on Service-Oriented Computing and Applications, Matsue, Japan, 17–19 November 2014; pp. 230–234. [Google Scholar]
- Jang, S.; Lim, D.; Kang, J.; Joe, I. An Efficient Device Authentication Protocol Without Certification Authority for Internet of Things. Wirel. Pers. Commun. 2016, 91, 1681–1695. [Google Scholar] [CrossRef]
- Abdulkader, O.; Bamhdi, A.M.; Thayananthan, V.; Jambi, K.; Al Ghamdi, B.; Patel, A. A Secure Lightweight Mutual Authentication and Message Exchange Protocol for IoT Environments Based on the Existence of Active Server. In Proceedings of the Fourth International Congress on Information and Communication Technology, London, UK, 27–28 February 2019; pp. 375–384. [Google Scholar]
- Kandi, M.A.; Lakhlef, H.; Bouabdallah, A.; Challal, Y. A versatile Key Management protocol for secure Group and Device-to-Device Communication in the Internet of Things. J. Netw. Comput. Appl. 2020, 150, 102480. [Google Scholar] [CrossRef]
- Hsiao, T.C.; Chen, T.L.; Chen, T.S.; Chung, Y.F. Elliptic Curve Cryptosystems-based Date-constrained Hierarchical Key Management Scheme in Internet of Things. Sensors Mater. 2019, 31, 355–364. [Google Scholar] [CrossRef]
- Tabassum, T.; Hossain, S.A.; Rahman, M.A. A Secure Key Management Technique Through Distributed Middleware for the Internet of Things. In Intelligent Computing; Arai, K., Kapoor, S., Bhatia, R., Eds.; Springer: Berlin/Heidelberg, Germany, 2018; pp. 1128–1139. [Google Scholar]
- Park, N.; Kang, N. Mutual authentication scheme in secure internet of things technology for comfortable lifestyle. Sensors 2015, 16, 20. [Google Scholar] [CrossRef] [PubMed]
- Roman, R.; Alcaraz, C.; Lopez, J.; Sklavos, N. Key management systems for sensor networks in the context of the Internet of Things. Comput. Electr. Eng. 2011, 37, 147–159. [Google Scholar] [CrossRef]
- Porambage, P.; Braeken, A.; Schmitt, C.; Gurtov, A.V.; Ylianttila, M.; Stiller, B. Group Key Establishment for Enabling Secure Multicast Communication in Wireless Sensor Networks Deployed for IoT Applications. IEEE Access 2015, 3, 1503–1511. [Google Scholar] [CrossRef]
- Hillmann, P.; Knüpfer, M.; Guggemos, T.; Streit, K. CAKE: An Efficient Group Key Management for Dynamic Groups. arXiv 2020, arXiv:2002.10722. Available online: https://arxiv.org/abs/2002.10722 (accessed on 15 November 2019).
- Di Pietro, R.; Mancini, L.V.; Jajodia, S. Providing secrecy in key management protocols for large wireless sensors networks. Hoc Networks 2003, 1, 455–468. [Google Scholar] [CrossRef]
- Abdmeziem, M.R.; Tandjaoui, D. An end-to-end secure key management protocol for e-health applications. Comput. Electr. Eng. 2015, 44, 184–197. [Google Scholar] [CrossRef]
- Tlelo-Cuautle, E.; Díaz-Muñoz, J.D.; González-Zapata, A.M.; Li, R.; León-Salas, W.D.; Fernández, F.V.; Guillén-Fernández, O.; Cruz-Vega, I. Chaotic Image Encryption Using Hopfield and Hindmarsh–Rose Neurons Implemented on FPGA. Sensors 2020, 20, 1326. [Google Scholar] [CrossRef] [PubMed]
- Sciancalepore, S.; Capossele, A.; Piro, G.; Boggia, G.; Bianchi, G. Key management protocol with implicit certificates for IoT systems. In Proceedings of the 13th Annual International Conference on Mobile Systems, Applications, and Services, Florence, Italy, 19–22 May 2015; pp. 37–42. [Google Scholar]
- Iqbal, U.; Shafi, S. A provable and secure key exchange protocol based on the elliptical curve diffe–hellman for wsn. In Advances in Big Data and Cloud Computing; Springer: Berlin/Heidelberg, Germany, 2019; pp. 363–372. [Google Scholar]
- Marin, L.; Pawlowski, M.P.; Jara, A. Optimized ECC implementation for secure communication between heterogeneous IoT devices. Sensors 2015, 15, 21478–21499. [Google Scholar] [CrossRef] [PubMed]
- Singh, S.R.; Ajoy, K.K. Key Management Scheme for Internet of Things Using an Elliptic Curve. J. Comput. Theor. Nanosci. 2020, 17, 115–121. [Google Scholar] [CrossRef]
- Malani, S.; Srinivas, J.; Das, A.K.; Srinathan, K.; Jo, M. Certificate-Based Anonymous Device Access Control Scheme for IoT Environment. IEEE Internet Things J. 2019, 6, 9762–9773. [Google Scholar] [CrossRef]
- Carneiro, G. NS-3: Network simulator 3. In Proceedings of the UTM Lab Meeting April, Porto, Portugal, 20 April 2010; Volume 20, pp. 4–5. [Google Scholar]
- Chen, M.; Miao, Y.; Humar, I. Introduction to OPNET Network Simulation. In OPNET IoT Simulation; Springer: Berlin/Heidelberg, Germany, 2019; pp. 77–153. [Google Scholar]
- Bagula, B.; Erasmus, Z. Iot Emulation with Cooja. Available online: http://wireless.ictp.it/school_2015/presentations/firstweek/ICTP-Cooja-Presentation-version0.pdf (accessed on 2 March 2020).
- Veith, T.L.; Kobza, J.E.; Koelling, C.P. Netsim: Java™-based simulation for the world wide web. Comput. Oper. Res. 1999, 26, 607–621. [Google Scholar] [CrossRef]
- Mehdi, K.; Lounis, M.; Bounceur, A.; Kechadi, T. Cupcarbon: A multi-agent and discrete event wireless sensor network design and simulation tool. In Proceedings of the 7th International ICST Conference on Simulation Tools and Techniques, Lisbon, Portugal, 17–19 March 2014; pp. 126–131. [Google Scholar]
- Rajalakshmi, A.; Shahnasser, H. Internet of Things using Node-Red and alexa. In Proceedings of the 17th International Symposium on Communications and Information Technologies (ISCIT), Cairns, QLD, Australia, 25–27 September 2017; pp. 1–4. [Google Scholar]
- OASIS. MQTT 3.1.1 Specification. Available online: http://docs.oasis-open.org/mqtt/mqtt/v3.1.1/mqtt-v3.1.1.html. (accessed on 20 October 2019).
- Eclipse. Mosquitto. Available online: https://mosquitto.org (accessed on 20 October 2019).
- Nawir, M.; Amir, A.; Yaakob, N.; Lynn, O.B. Internet of Things (IoT): Taxonomy of security attacks. In Proceedings of the 3rd International Conference on Electronic Design (ICED), Phuket, Thailand, 11–12 Auguest 2016; pp. 321–326. [Google Scholar]
- Deogirikar, J.; Vidhate, A. Security attacks in IoT: A survey. In Proceedings of the International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), Palladam, India, 10–11 February 2017; pp. 32–37. [Google Scholar]





| Reference | Key Type Using | Good for When Number of Messages Is | Complexity | Drawbacks |
|---|---|---|---|---|
| [12] | Mutual Key | low | simple | generates a session key for every session which degrade performance when message is high |
| [8] | Mutual Key | medium | simple | generates a session key for new connection but security is not high |
| [14] | Group Key | medium | simple | creating multicast group is time-consuming |
| [9] | Group Key | medium | simple | creating multicast group in an intelligent way but still time-consuming when message number is high |
| [16] | XOR Based | low | moderate | for high resource consumption this method is not suggested |
| [17] | XOR Based | low | high | performance and scalability are affected for using a third party certificate provider |
| [19] | ECC/ECDH | low | high | implicit IoT device certificates make the system slower |
| [20] | ECC/ECDH | medium | moderate | uses complex certificate based approach |
| [10] | ECC/ECDH | medium | high | uses complex certificate based approach |
| [7] | CA-Less | low | high | It is difficult to manage the Certificate Authority (CA) placing it on a server |
| [22] | CA-Less | high | high | the method is still in its preliminary stage and detailed investigation is needed for realistic use in various environments |
| Component | Purpose |
|---|---|
| Arduino Uno | Running our SIoT algorithm |
| ESP8266-01—Wifi Module | Connecting other node through WiFi |
| Serial Enabled 16 × 2 LCD | Displaying the connection and pair status |
| Logic Level Converter—Bi-Directional | Is used to coordinate voltage levels between 5 V controllers and 3.3 V components and vice versa |
| Lithium Polymer Battery—7.4 V | Power source |
| Jumper Wires Pack—M/M | Electrical circuits to connect its various components |
| Jumper Wires Pack—M/F | A pack of 20 standard 6in female-male Jumper wires |
| Step | From Connection | To Connection |
|---|---|---|
| 1 | ArduinoUno Vin | LipoBattery7v4 VCC |
| 2 | ArduinoUno GND | Bus GND |
| 3 | ArduinoUno 5v | Bus POS |
| 4 | serLCD GND | Bus GND |
| 5 | serLCD RX | ArduinoUno 2 |
| 6 | serLCD VCC | Bus POS |
| 7 | ESP8266 RXD | LogicLevelConverter LV1 |
| 8 | ESP8266 TXD | LogicLevelConverter LV2 |
| 9 | ESP8266 VCC | LogicLevelConverter LV |
| 10 | ESP8266 GND | Bus GND |
| 11 | LogicLevelConverter LV | ESP8266 CH_PD |
| 12 | LogicLevelConverter LV | ArduinoUno 3.3 V |
| 13 | LogicLevelConverter GND | Bus GND |
| 14 | LogicLevelConverter HV2 | ArduinoUno 10 |
| 15 | LogicLevelConverter HV1 | ArduinoUno 11 |
| 16 | LogicLevelConverter HV | Bus POS |
| 17 | LipoBattery7v4 GND | Bus GND |
| Factor | Proposed Technique | KMP [19,20] | GKMP [9] |
|---|---|---|---|
| Key assign | A symmetric key for each node pair | Two certificates for each node pair | Group key for each group |
| Auth | Hash key | Two certificates | Digital signature |
| Re-key | Need to update the GT and LT | No action required | Need to assign new to all members that are in a group |
| Space | Moderately high | Low | Low |
| Speed | High | Slow | Slow |
| Drawback | Moderately high space required for storing data in GT and LT | Using same implicit key, so if the key is compromised, the communication may break down | Practically it is almost impossible to make grouping of nodes |
| Attack resistance | Man-in-the-middle attack, Eavesdropping | Reply-attack | Man-in-the-middle attack |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tabassum, T.; Hossain, S.A.; Rahman, M.A.; Alhamid, M.F.; Hossain, M.A. An Efficient Key Management Technique for the Internet of Things. Sensors 2020, 20, 2049. https://doi.org/10.3390/s20072049
Tabassum T, Hossain SA, Rahman MA, Alhamid MF, Hossain MA. An Efficient Key Management Technique for the Internet of Things. Sensors. 2020; 20(7):2049. https://doi.org/10.3390/s20072049
Chicago/Turabian StyleTabassum, Tamanna, SK Alamgir Hossain, Md. Anisur Rahman, Mohammed F. Alhamid, and M. Anwar Hossain. 2020. "An Efficient Key Management Technique for the Internet of Things" Sensors 20, no. 7: 2049. https://doi.org/10.3390/s20072049
APA StyleTabassum, T., Hossain, S. A., Rahman, M. A., Alhamid, M. F., & Hossain, M. A. (2020). An Efficient Key Management Technique for the Internet of Things. Sensors, 20(7), 2049. https://doi.org/10.3390/s20072049





