An Adaptive, Discrete Space Oriented Wolf Pack Optimization Algorithm for a Movable Wireless Sensor Network
Abstract
1. Introduction
2. Related Works
2.1. Adaptive Shrinking Grid Search Wolf Pack Optimization Algorithm (ASGS-CWOA) [25]
2.2. Some Covering Models
2.3. Assumptions
3. Proposed Method
3.1. Adaptive Expansion Based on the Minimum Overlapping Full Covering Model (AE-MOFCM)
3.2. Improvement of ASGS-CWOA
3.2.1. Target–Node Probability Matrix
| DisMatrix = | ||||||||||
| 43.7789 | 51.1520 | 23.4172 | 48.5644 | 41.0088 | 45.2269 | 43.7371 | 59.0807 | 22.8023 | 52.4575 | 52.6837 |
| 89.5848 | 102.7955 | 34.1164 | 96.6705 | 82.3390 | 96.4476 | 58.4000 | 110.9124 | 65.4490 | 57.7990 | 75.2081 |
| 94.5011 | 93.0703 | 57.3921 | 69.9634 | 50.2953 | 77.6262 | 14.6844 | 93.4426 | 43.7937 | 6.5906 | 28.7570 |
| 34.7525 | 8.1325 | 73.0260 | 27.7816 | 44.5392 | 13.7408 | 76.2582 | 8.9160 | 46.4362 | 86.9647 | 72.7660 |
| 17.3990 | 44.3956 | 56.5939 | 72.2643 | 78.9547 | 58.8652 | 94.9223 | 60.4114 | 67.2458 | 104.2120 | 100.6190 |
| 47.8966 | 67.9433 | 14.7869 | 76.3406 | 70.9614 | 69.5489 | 68.2461 | 80.3224 | 52.7804 | 74.5351 | 80.3976 |
| 57.7849 | 49.1607 | 51.7501 | 26.2510 | 11.3107 | 32.4638 | 31.1182 | 48.2635 | 7.3564 | 41.8103 | 29.7889 |
| 76.9987 | 97.0132 | 29.4629 | 101.4065 | 92.0827 | 96.7314 | 78.2804 | 108.6867 | 73.4754 | 80.9460 | 93.6696 |
| 87.0215 | 77.1456 | 68.8263 | 46.8968 | 27.5488 | 58.3573 | 18.0068 | 72.9921 | 33.1871 | 23.7224 | 1.2631 |
| 59.0808 | 37.5188 | 76.2551 | 4.4587 | 21.6885 | 17.8927 | 57.3080 | 27.4667 | 35.0345 | 67.3609 | 48.6140 |
| 42.9721 | 69.7695 | 44.1116 | 90.0214 | 90.5024 | 79.1930 | 95.3299 | 85.0845 | 74.3281 | 102.6011 | 105.5259 |
| ProbabilityTarget-Disperse = | ||||||||||
| 0.0397 | 0.0316 | 0.0307 | 0.0360 | 0.1003 | 0.0295 | 0.4967 | 0.0915 | 0.0781 | 0.0290 | 0.0369 |
| 0.0361 | 0.6205 | 0.0451 | 0.0287 | 0.0370 | 0.0416 | 0.0499 | 0.0387 | 0.0450 | 0.0275 | 0.0298 |
| 0.0798 | 0.0444 | 0.3827 | 0.0441 | 0.0384 | 0.2305 | 0.0438 | 0.0338 | 0.0330 | 0.0213 | 0.0482 |
| 0.0793 | 0.0479 | 0.0553 | 0.1109 | 0.1510 | 0.0552 | 0.0987 | 0.1252 | 0.0923 | 0.0813 | 0.1027 |
| 0.0439 | 0.0432 | 0.0369 | 0.0474 | 0.0880 | 0.0361 | 0.0823 | 0.1213 | 0.1197 | 0.3346 | 0.0466 |
| 0.0523 | 0.0784 | 0.0489 | 0.0482 | 0.0912 | 0.0467 | 0.1426 | 0.1252 | 0.2393 | 0.0782 | 0.0489 |
| 0.1403 | 0.0397 | 0.0618 | 0.1537 | 0.1159 | 0.0618 | 0.0902 | 0.0746 | 0.0592 | 0.0362 | 0.1666 |
| 0.0653 | 0.1827 | 0.0699 | 0.0572 | 0.0839 | 0.0663 | 0.1133 | 0.0970 | 0.1269 | 0.0790 | 0.0585 |
| 0.3359 | 0.0357 | 0.0958 | 0.1002 | 0.0519 | 0.1048 | 0.0502 | 0.0418 | 0.0375 | 0.0254 | 0.1208 |
| 0.0964 | 0.0397 | 0.0559 | 0.2127 | 0.1058 | 0.0568 | 0.0751 | 0.0778 | 0.0613 | 0.0469 | 0.1715 |
| 0.0525 | 0.0683 | 0.0480 | 0.0521 | 0.0900 | 0.0465 | 0.1038 | 0.1225 | 0.1689 | 0.1952 | 0.0521 |
| ProbabilityTarget = | ||||||||||
| 0.0397 | 0.0713 | 0.102 | 0.138 | 0.2384 | 0.2678 | 0.7645 | 0.856 | 0.9341 | 0.9631 | 1.0000 |
| 0.0361 | 0.6566 | 0.7017 | 0.7304 | 0.7674 | 0.809 | 0.859 | 0.8977 | 0.9427 | 0.9702 | 1.0000 |
| 0.0798 | 0.1242 | 0.507 | 0.551 | 0.5894 | 0.8199 | 0.8636 | 0.8975 | 0.9305 | 0.9518 | 1.0000 |
| 0.0793 | 0.1273 | 0.1826 | 0.2935 | 0.4445 | 0.4997 | 0.5984 | 0.7237 | 0.816 | 0.8973 | 1.0000 |
| 0.0439 | 0.0871 | 0.124 | 0.1714 | 0.2594 | 0.2955 | 0.3778 | 0.4992 | 0.6188 | 0.9534 | 1.0000 |
| 0.0523 | 0.1307 | 0.1796 | 0.2278 | 0.319 | 0.3657 | 0.5083 | 0.6335 | 0.8729 | 0.9511 | 1.0000 |
| 0.1403 | 0.18 | 0.2419 | 0.3956 | 0.5114 | 0.5732 | 0.6634 | 0.738 | 0.7973 | 0.8334 | 1.0000 |
| 0.0653 | 0.248 | 0.3179 | 0.3751 | 0.459 | 0.5253 | 0.6386 | 0.7356 | 0.8624 | 0.9415 | 1.0000 |
| 0.3359 | 0.3716 | 0.4675 | 0.5677 | 0.6195 | 0.7244 | 0.7746 | 0.8163 | 0.8538 | 0.8792 | 1.0000 |
| 0.0964 | 0.1361 | 0.192 | 0.4047 | 0.5106 | 0.5674 | 0.6424 | 0.7203 | 0.7816 | 0.8285 | 1.0000 |
| 0.0525 | 0.1208 | 0.1688 | 0.2209 | 0.3109 | 0.3575 | 0.4613 | 0.5838 | 0.7527 | 0.9479 | 1.0000 |
| Min-DisMatrix = | ||||||||||
| 7 | 5 | 8 | 9 | 1 | 11 | 4 | 2 | 3 | 6 | 10 |
| 2 | 7 | 3 | 9 | 6 | 8 | 5 | 1 | 11 | 4 | 10 |
| 3 | 6 | 1 | 11 | 2 | 4 | 7 | 5 | 8 | 9 | 10 |
| 5 | 8 | 4 | 11 | 7 | 9 | 10 | 1 | 3 | 6 | 2 |
| 10 | 8 | 9 | 5 | 7 | 4 | 11 | 1 | 2 | 3 | 6 |
| 9 | 7 | 8 | 5 | 2 | 10 | 1 | 11 | 3 | 4 | 6 |
| 11 | 4 | 1 | 5 | 7 | 8 | 3 | 6 | 9 | 2 | 10 |
| 2 | 9 | 7 | 8 | 5 | 10 | 3 | 6 | 1 | 11 | 4 |
| 1 | 11 | 6 | 4 | 3 | 5 | 7 | 8 | 9 | 2 | 10 |
| 4 | 11 | 5 | 1 | 8 | 7 | 9 | 6 | 3 | 10 | 2 |
| 10 | 9 | 8 | 7 | 5 | 2 | 1 | 4 | 11 | 3 | 6 |
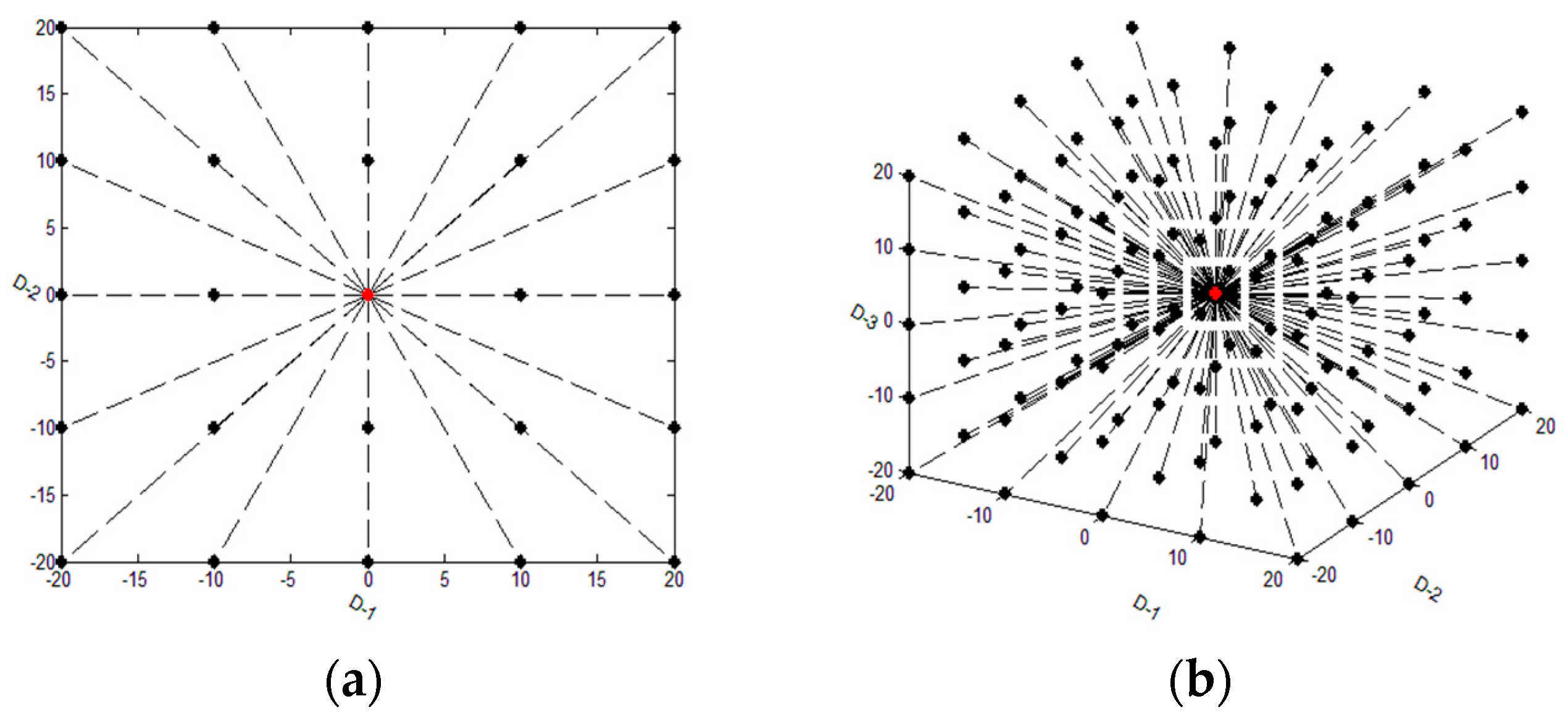
3.2.2. Adaptive Step Size
4. Main Steps
5. Experiments
6. Discussion and Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Kumar, D.P.; Amgoth, T.; Annavarapu, C.S.R. Machine learning algorithms for wireless sensor networks: A survey. Inf. Fusion 2019, 49, 1–25. [Google Scholar] [CrossRef]
- Dai, H.-N.; Wong, R.C.W.; Wang, H. On Capacity and Delay of Multichannel Wireless Networks With Infrastructure Support. IEEE Trans. Veh. Technol. 2017, 66, 1589–1604. [Google Scholar] [CrossRef]
- Dai, H.; Wong Raymond, C.; Wang, H. Big Data Analytics for Large ScaleWireless Networks: Challenges and Opportunities. ACM Comput. Surv. 2019. [Google Scholar] [CrossRef]
- Thakur, D.; Kumar, Y.; Kumar, A.; Singh, P.K. Applicability of Wireless Sensor Networks in Precision Agriculture: A Review. Wirel. Pers. Commun. 2019, 107, 471–512. [Google Scholar] [CrossRef]
- Li, G.; Zhao, J.; Wang, Z. Forest Fire Detection System based on Wireless Sensor Network. Chin. J. Sens. Actuators 2006, 19, 2760–2764. [Google Scholar]
- Xu, L.; Nie, J.; Ma, X.; Lv, H.; Yang, J. Design and Implementation of Water Environment Monitoring System Based on Wireless Sensor Network. Digit. Technol. Appl. 2018, 36, 128–129. [Google Scholar]
- Fu, X.; Yao, H.; Postolache, O.; Yang, Y. Message forwarding for WSN-Assisted Opportunistic Network in disaster scenarios. J. Netw. Comput. Appl. 2019, 137, 11–24. [Google Scholar] [CrossRef]
- Yick, J.; Bharathidasan, A.; Pasternack, G.; Mukherjee, B.; Ghosal, D. Optimizing Placement of Beacons and Data Loggers in a Sensor Network—A Case Study. In Proceedings of the IEEE Wireless Communications and Networking Conference (IEEE Cat. No.04TH8733), Atlanta, GA, USA, 21–25 March 2004; pp. 2486–2491. [Google Scholar]
- Qu, Y.; Zhai, Y.; Lin, Z.; Zhao, B.; Zhang, Y. A Novel Sensor Placement Model in Wireless Sensor Network. J. Beijing Univ. Posts Telecommun. Telecommun. 2004, 27. [Google Scholar] [CrossRef]
- Zhou, F.; Gao, J.; Fan, X.; An, K. Dynamic Covering Algorithm of Node Based on Virtual Force in Wireless Sensor Networks. J. Syst. Simul. 2018, 30, 97–106. [Google Scholar]
- Zhang, C. Coverage Algorithm based on Virtual Forces in Wireless Sensor Networks. Appl. Res. Comput. 2019, 36, 1854–1857. [Google Scholar]
- Yarinezhad, R.; Hashemi, S.N. A routing algorithm for wireless sensor networks based on clustering and an fpt-approximation algorithm. J. Syst. Softw. 2019, 155, 145–161. [Google Scholar] [CrossRef]
- Chen, Y.; Xu, X.; Wang, Y. Wireless sensor network energy efficient coverage method based on intelligent optimization algorithm. Discret. Contin. Dyn. Syst. S 2019, 12, 887–900. [Google Scholar] [CrossRef]
- Somaieh, Z.; Shahram, B. Dehcic: A Distributed Energy-aware Hexagon based Clustering Algorithm to Improve Coverage in Wireless Sensor Networks. Peer Peer Netw. Appl. 2019, 12, 689–704. [Google Scholar]
- Alavi, S.A.; Mehran, K.; Hao, Y.; Rahimian, A.; Mirsaeedi, H.; Vahidinasab, V. A Distributed Event-Triggered Control Strategy for DC Microgrids Based on Publish-Subscribe Model over Industrial Wireless Sensor Networks. IEEE Trans. Smart Grid 2019, 10, 4323–4337. [Google Scholar] [CrossRef]
- Sajwan, M.; Gosain, D.; Sharma, A.K. CAMP: Cluster aided multi-path routing protocol for wireless sensor networks. Wirel. Netw. 2018, 25, 2603–2620. [Google Scholar] [CrossRef]
- So-In, C.; Nguyen, T.; Nguyen, N. An Efficient Coverage Hole-Healing Algorithm for Area-Coverage Improvements in Mobile Sensor Networks. Peer-Peer Netw. Appl. 2019, 12, 541–552. [Google Scholar] [CrossRef]
- Wang, X.; Wang, S.; Ma, J. Parallel Particle Swarm Optimization based Mobile Sensor Node Deployment in Wireless Sensor Networks. Chin. J. Comput. 2007, 30. [Google Scholar] [CrossRef]
- Yang, C.; Tu, X.; Chen, J. Algorithm of Marriage in Honey Bees Optimization Based on the Wolf Pack Search. In Proceedings of the International Conference on Intelligent Pervasive Computing (IPC 2007), Institute of Electrical and Electronics Engineers (IEEE), Jeju City, Korea, 11–13 October 2007; Volume 2007, pp. 462–467. [Google Scholar]
- Wang, D.; Qian, X.; Liu, K.; Ban, X.; Guan, X. An Adaptive Distributed Size Wolf Pack Optimization Algorithm Using Strategy of Jumping for Raid (September 2018). IEEE Access 2018, 6, 65260–65274. [Google Scholar] [CrossRef]
- Huang, H.; Ren, Z.; Wei, J. Improved Wolf Group Algorithm for Solving Traveling Salesman Problem. Appl. Res. Comput. 2019, 36. [Google Scholar] [CrossRef]
- Wu, H.; Zhang, F.; Li, H.; Liang, X. Discrete Wolf Pack Algorithm for Traveling Salesman Problem. Control Decis. 2015, 30, 1861–1867. [Google Scholar]
- Martin, B.; Marot, J.; Bourennane, S. Improved Discrete Grey Wolf Optimizer. In Proceedings of the 26th European Signal Processing Conference (EUSIPCO), Rome, Italy, 3–7 September 2018; pp. 494–498. [Google Scholar]
- Wu, R.; Wang, S. Discrete Wolf Pack Search Algorithm based Transit Network Design. In Proceedings of the 7th IEEE International Conference on Software Engineering and Service Science (ICSESS), Beijing, China, 26–28 August 2016. [Google Scholar]
- Wang, D.; Qian, X.; Liu, K.; Ban, X. An Adaptive Shrinking Grid Search Chaos Wolf Optimization Algorithm with Adaptive Standard-Deviation Updating Amount. IEEE Access 2018. [Google Scholar] [CrossRef]
- Liu, Z.; Liu, Q.; Yuan, Y.; Guan, X. Location Scheme in Wireless Sensor Networks based on Bayesian Estimation, Virtual Force and Genetic Algorithm. Control Decis. 2013, 28, 899–903. [Google Scholar]
- Li, M.; Shi, W. Virtual Force-Directed Differential Evolution Algorithm based Coverage Enhancing Algorithm for Heterogeneous Mobile Sensor Networks. Chin. J. Sci. Instrum. 2011, 32, 1043–1050. [Google Scholar] [CrossRef]






| Algorithm | Initial Coverage Rate | Best Coverage Rate | Mean Coverage Rate | Worst Coverage Rate | Variance | Mean Time | Moving Distance |
|---|---|---|---|---|---|---|---|
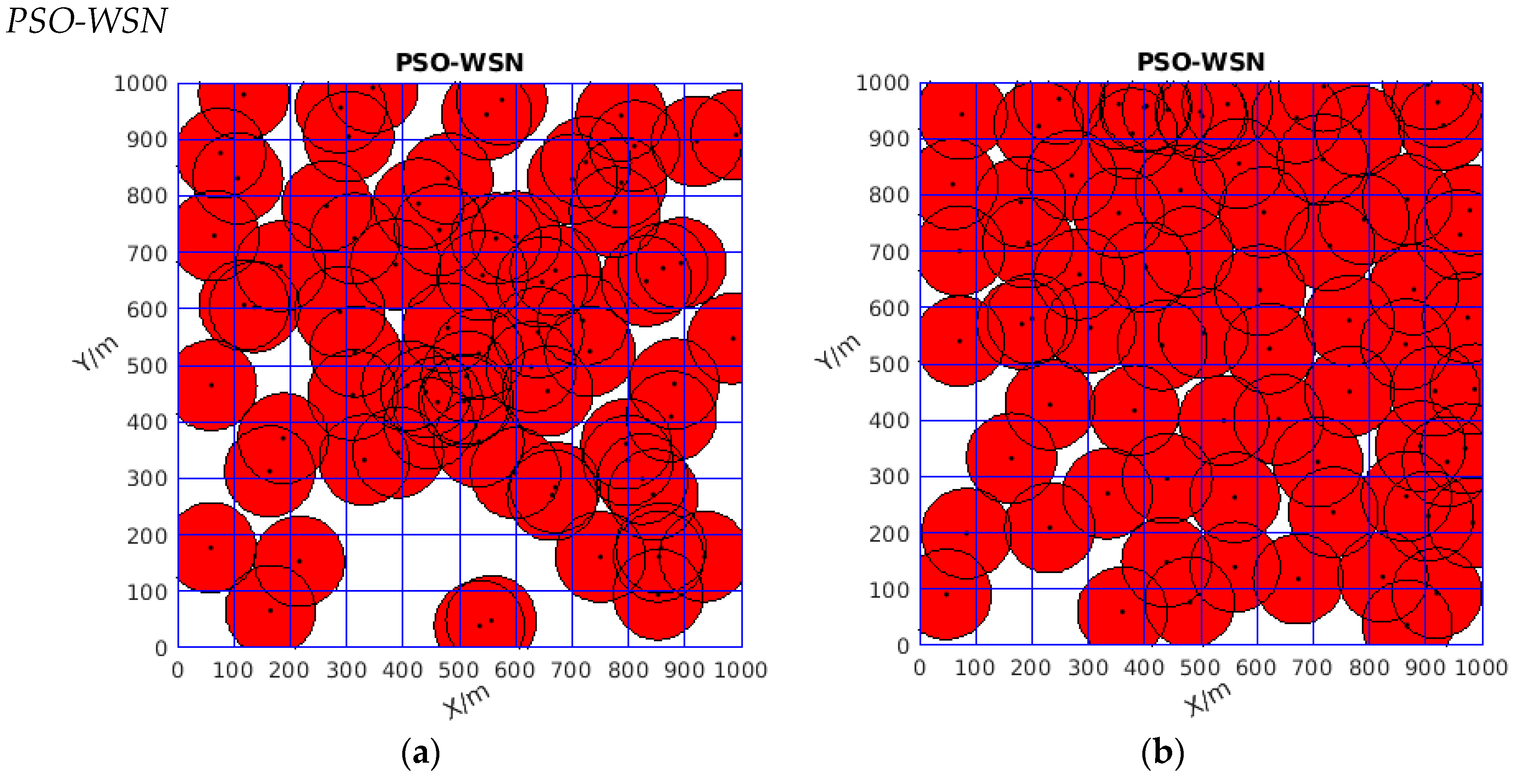
| PSO-WSN | 77.71% | 93.83% | 91.228% | 89.74% | 12593.36 | 2124.0355 | 36575.491 |
| VFA | 76.10% | 99.645% | 99.476% | 98.149% | 1.7324e-06 | 23.2982 | 11094.4339 |
| DSO-WPOA | 76.53% | 100% | 100% | 100% | 0 | 57.8892 | 7662.2987 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wang, D.; Wang, H.; Ban, X.; Qian, X.; Ni, J. An Adaptive, Discrete Space Oriented Wolf Pack Optimization Algorithm for a Movable Wireless Sensor Network. Sensors 2019, 19, 4320. https://doi.org/10.3390/s19194320
Wang D, Wang H, Ban X, Qian X, Ni J. An Adaptive, Discrete Space Oriented Wolf Pack Optimization Algorithm for a Movable Wireless Sensor Network. Sensors. 2019; 19(19):4320. https://doi.org/10.3390/s19194320
Chicago/Turabian StyleWang, Dongxing, Huibo Wang, Xiaojuan Ban, Xu Qian, and Jingxiu Ni. 2019. "An Adaptive, Discrete Space Oriented Wolf Pack Optimization Algorithm for a Movable Wireless Sensor Network" Sensors 19, no. 19: 4320. https://doi.org/10.3390/s19194320
APA StyleWang, D., Wang, H., Ban, X., Qian, X., & Ni, J. (2019). An Adaptive, Discrete Space Oriented Wolf Pack Optimization Algorithm for a Movable Wireless Sensor Network. Sensors, 19(19), 4320. https://doi.org/10.3390/s19194320






