1. Introduction
Interconnectivity between dissimilar devices to form a pervasive network of services is possible among a broad variety of electronic devices due to the miniaturisation of these devices and reductions in their cost [
1]. Such electronic devices are made smart by endowing physical things with local intelligence, thereby bridging the gulf between the physical world and the world of information [
2]. The network connecting these smart devices, i.e., intelligent things, has been termed the Internet of Things (IoT) [
3]. IoT technology is driving the third wave of the information technology (IT) revolution, which is striving towards an era of ubiquity, heterogeneity, and connectivity [
4]. This revolution is occurring in concert with the popularisation of wireless and sensor technologies enabled by wireless sensor networks (WSNs) [
5,
6]. The IoT is a communicating-actuating network of devices that augment digital information with information about the physical world, i.e., the environment around us [
7]. In other words, devices in an IoT network dynamically cooperate to fulfil an IoT application’s goal.
An IoT network is characterised by its ability to offer comprehensive perception, reliable transmission, and intelligent processing [
1]. Identification technology and sensors are utilised in an IoT network to enable people to interact with the real world remotely via a variety of wired and wireless technologies for transmission and communication among machines (i.e., machine-to-machine, or M2M, communication) and with the users of IoT applications. Within the context of the IoT, WSNs permit the utilisation of different network topologies and multi-hop communication to enable the monitoring of physical and environmental conditions via spatially distributed devices. The instantaneous and intelligent processing of the collected data is facilitated by intelligent computing technologies, e.g., cloud computing, and the results are communicated to humans or other devices. Human-to-device communication is implemented in IoT applications to provide reliable and robust interaction. Device-to-device interactions are also made possible in IoT applications through the utilisation of intelligent devices that are able to identify a problem, communicate effectively, and resolve the issue without human intervention [
8].
The capabilities of IoT applications are varied and depend on the types of services being offered by said applications. For instance, IoT applications for smart agriculture (e.g., [
9]) are currently being used for the clean and sustainable growing of food. An application of this sort requires the deployment of a large number of sensors to detect environmental and ecological factors to support the remote control of actuators based on those readings. As another example, an IoT application intended for electronic health (e-health) monitoring (e.g., [
10]) collects and analyses data from an ad hoc network of several devices that are placed on a patient’s body to provide end users with feedback on health-related habits and advice. The performance of IoT applications is further impacted by the capabilities of the devices being utilised and of the network itself. This is because most IoT devices are resource-challenged devices, with limited memory, processing capabilities, electrical energy supplies, and other abilities [
11].
Often, an IoT application requires additional computational power to process the data collected by the sensors. This requires the sensors to forward their data to a control station (i.e., sink) for further operations. This is accomplished through efficient routing protocols, such as gossiping protocols, which can, in turn, impact the performance of the IoT network and application. Gossiping is a traditional communication mechanism that mimics the behaviour of common dissemination phenomena, such rumours or epidemics. In a traditional gossiping protocol, a message is generated by a source and is propagated to the sink node with the active participation of most nodes in the network to ensure that the message is received at the sink [
12]. A sender node (beginning with the source node) transmits the message to a single neighbour chosen at random. The selected node then chooses another random neighbour to which to forward the packet. This process is repeated until the message is received at the destination, i.e., the sink node [
13]. It is evident from this simple procedure that message redundancy may be an issue, as the same message can be received more than once. Energy is also wasted due to the participation of most of the nodes in the network in the dissemination of a message, directly impacting the network’s lifetime. These challenges can potentially be remedied through the utilisation of election scores for optimisation to limit the number of participating nodes.
IoT applications can provide access to comprehensive intelligent services and information [
1,
14]. This can be achieved by the utilisation of the underlying sensor networks. Therefore, the performance of such application will depend on the communication protocol that facilities the data dissemination among sensors in the network. However, the problem with designing such protocol is tightly related to the underlying sensor network, where sensors have limited resources and capabilities, particularly in terms of power consumption, storage capacity, and bandwidth. In addition, the emerging use of fog computing in IoT applications has raised the need for an efficient multi-hop communication mechanism [
15]. In fog computing, sensed data would be sent to the network’s edge device (i.e., sink node), rather than a gateway device. This should reduce network traffic and enhance the performance of IoT applications [
16]. In smart city environments, communication has been introduced as a customised solution to resolve the issue with Internet connectivity due to obstacles that impede transmission [
17,
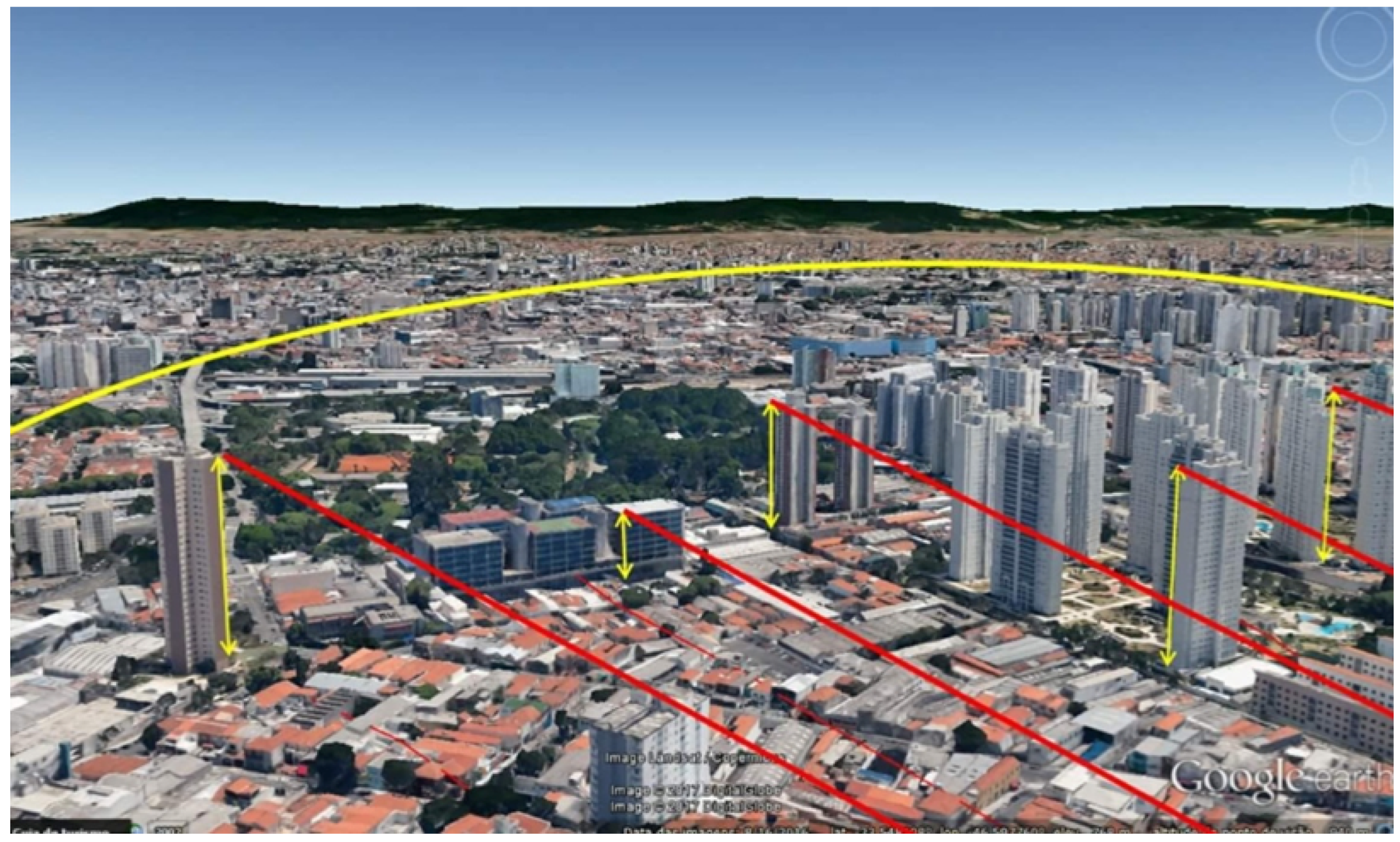
18]. In a recent smart city project, three different types of stations are considered: (1) sender, (2) sender/receiver, and (3) receiver. Information is gathered from the level of the street (type 1 stations) to the top of the building (type 2 stations) and then to another building (type 3 station). Therefore, the information is passed through the stations as follows: (1) > (2) > (3). The reason for using type 2 stations is because type 1 stations cannot directly communicate to type 3 station due to buildings and obstacles that exist in the way. In addition, stations 1 and 2 do not have Internet connection, while stations 3 do. This solution is illustrated in
Figure 1.
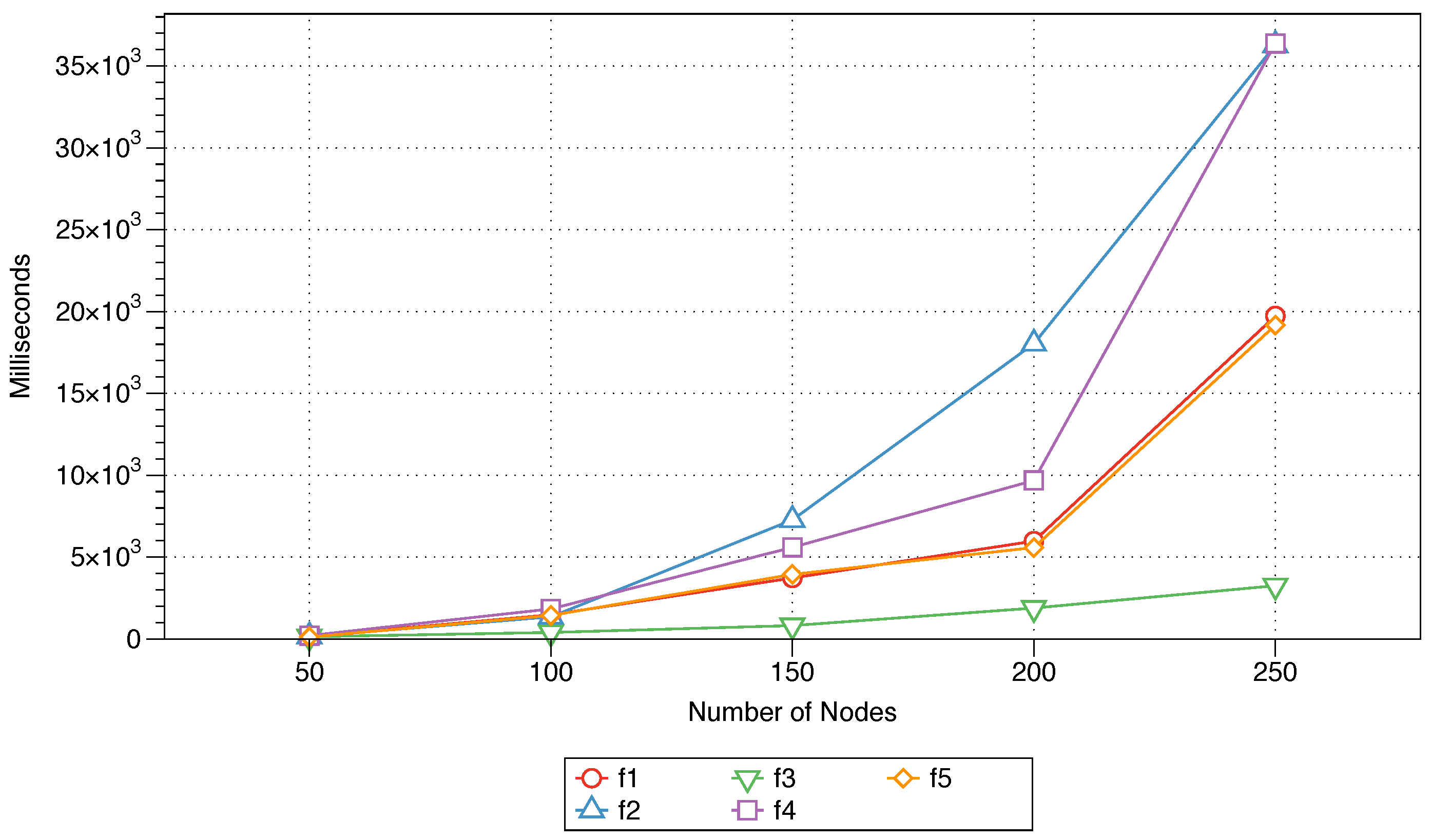
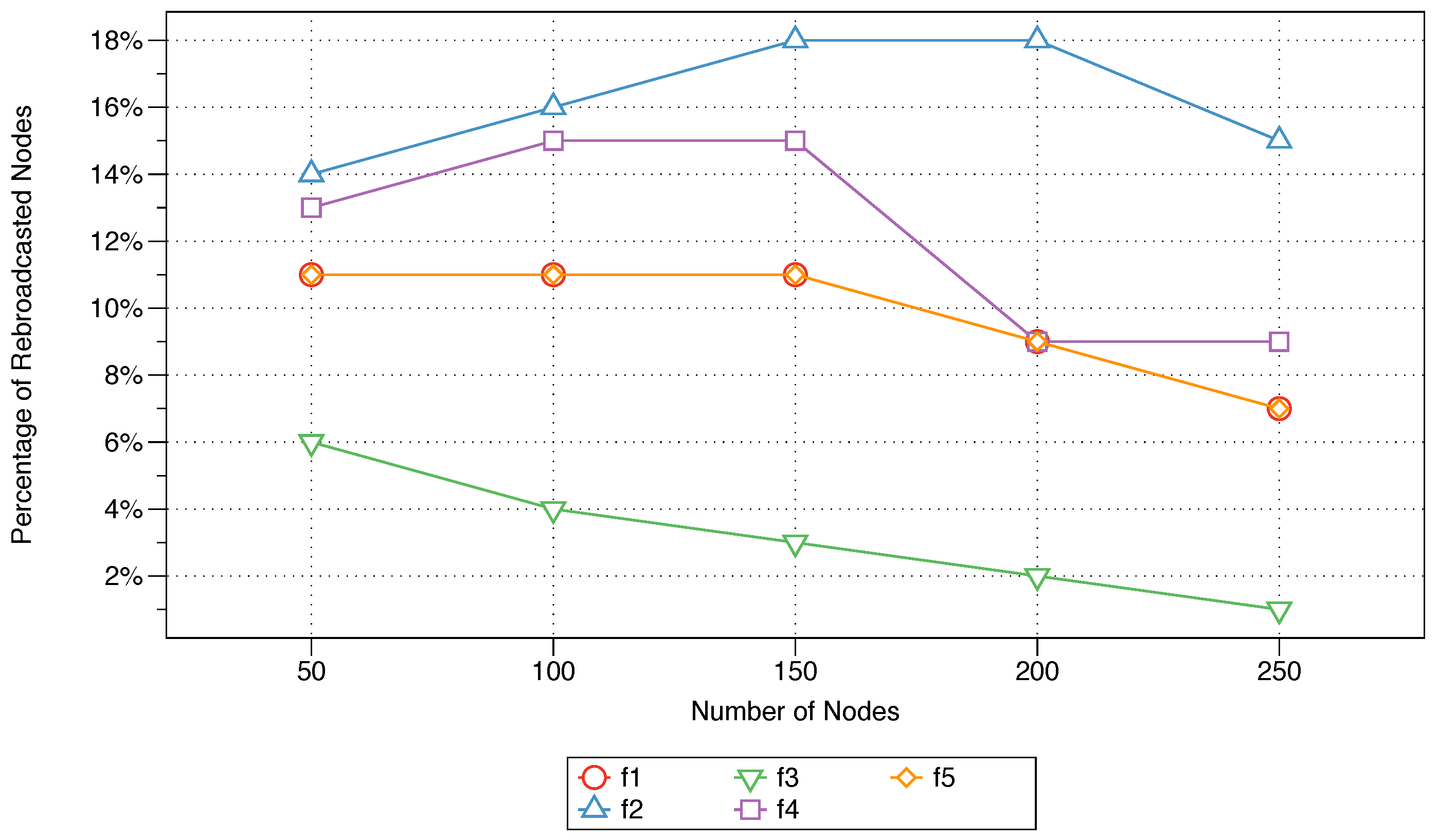
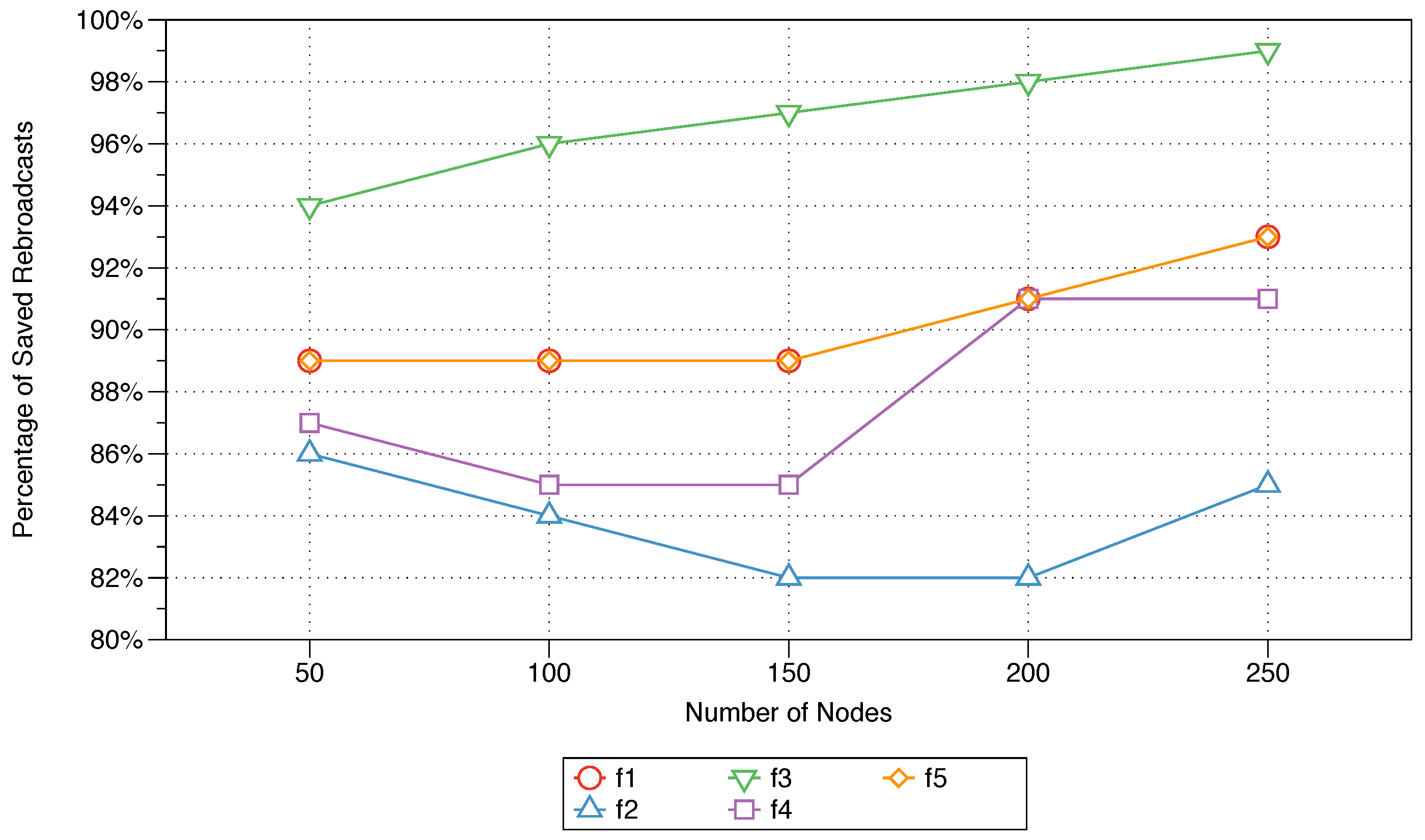
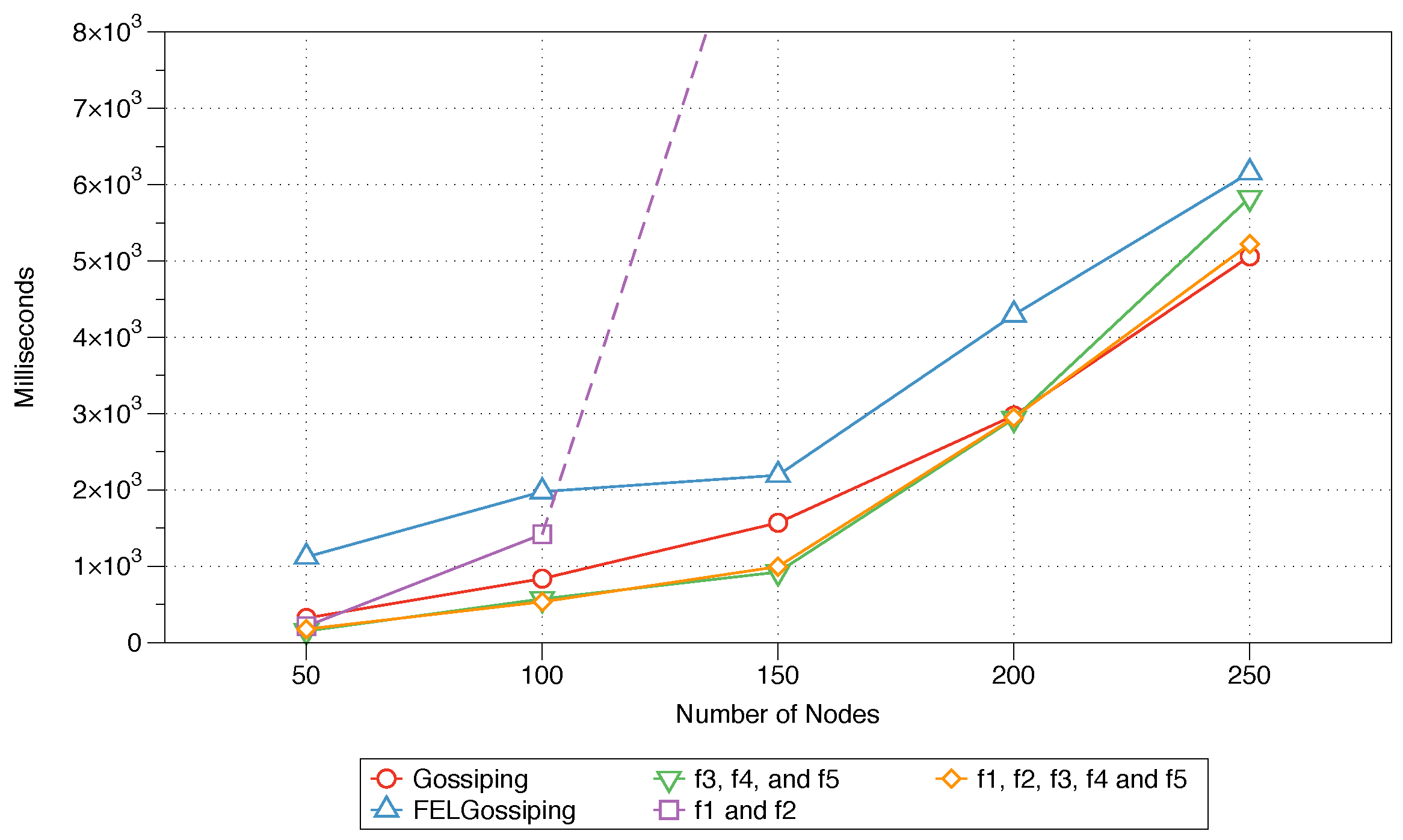
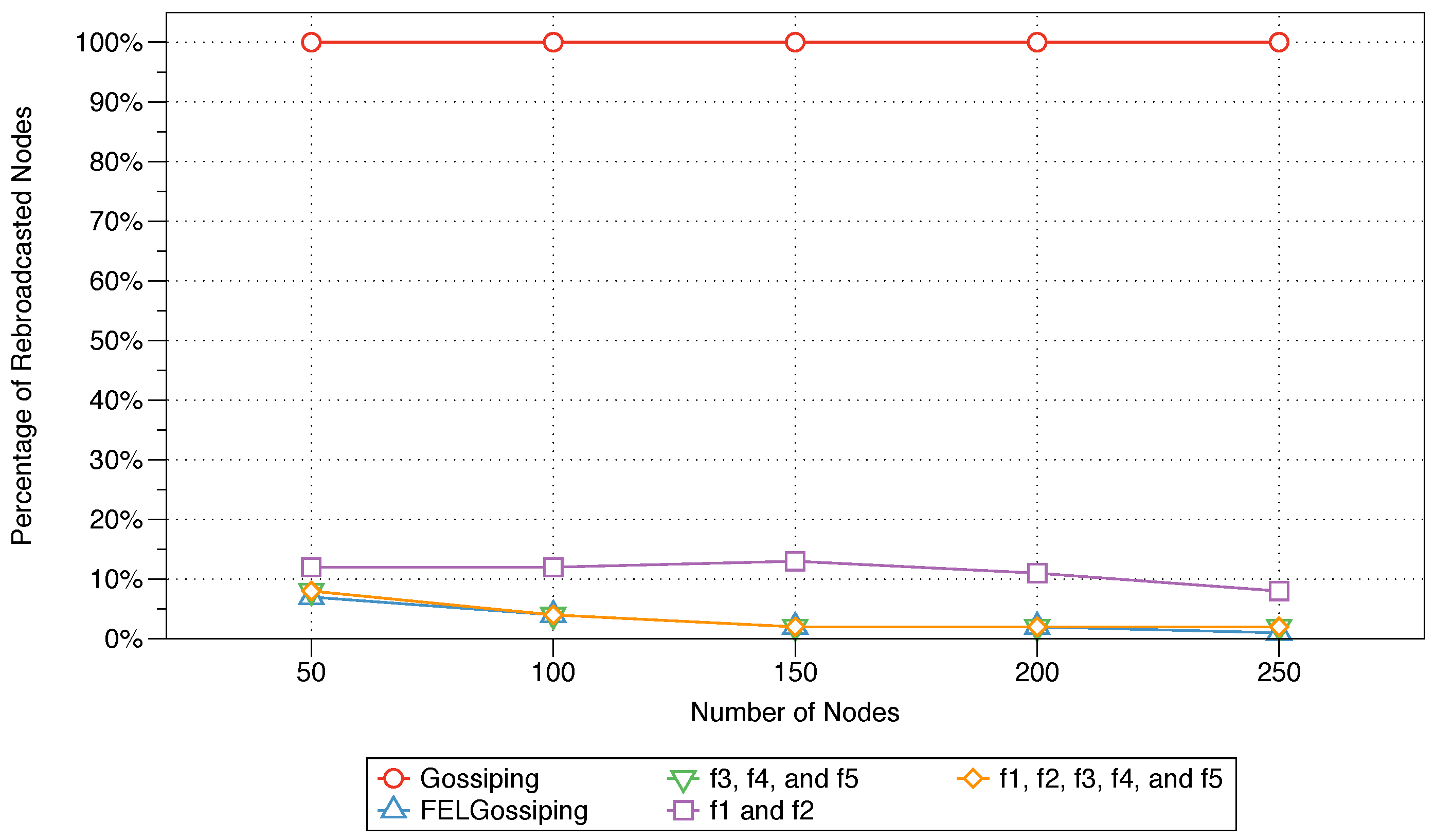
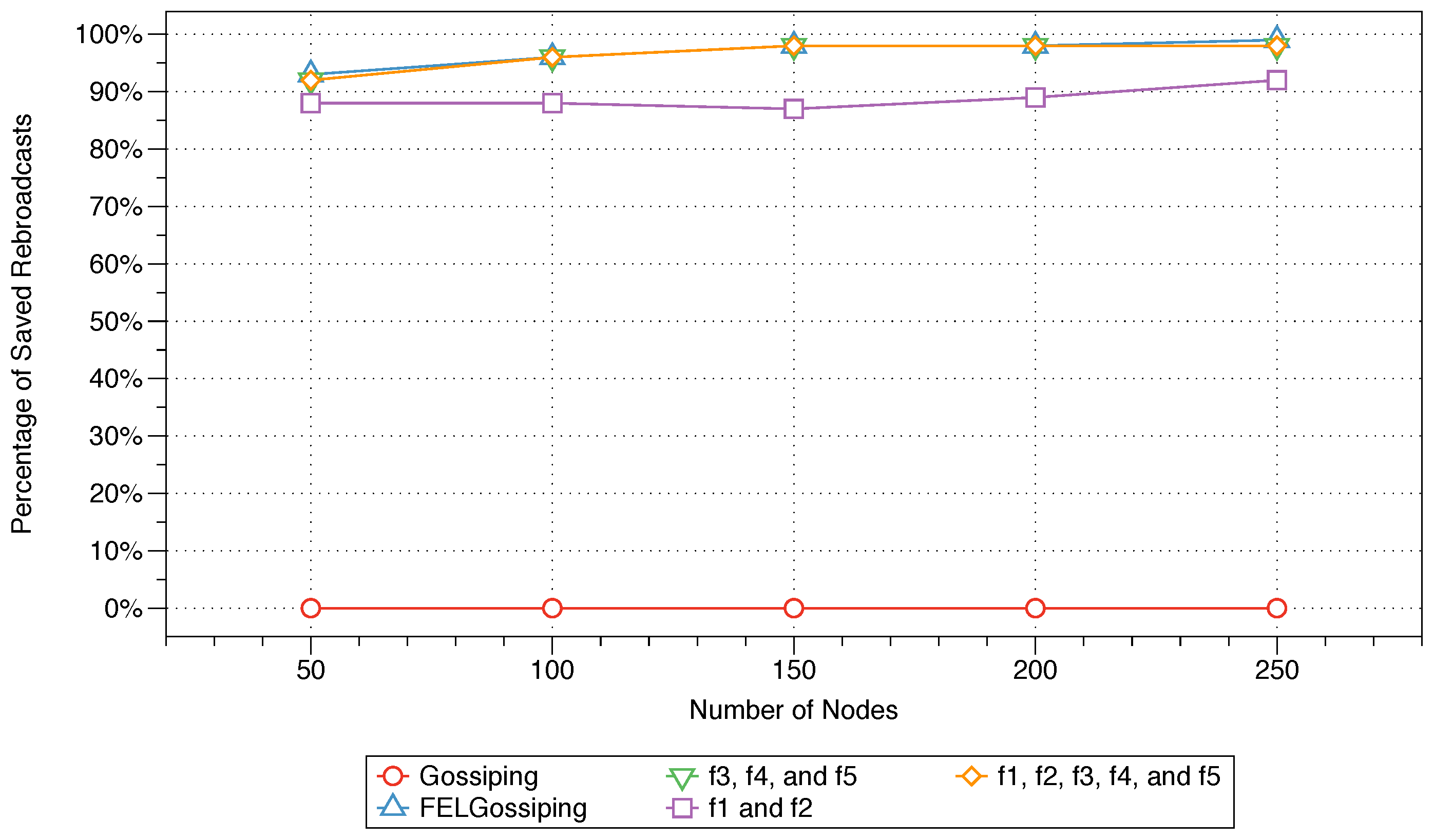
In this paper, a communication mechanism based on a gossiping protocol is proposed. The new protocol utilises knowledge regarding the network context and message priority. The protocol is made context-aware by its ability to gather information about its environment, i.e., neighbors and sink, to adapt its procedure and guide its response accordingly. The main contributions of this paper are threefold. First, a new protocol is proposed that uses a multi-factor weight function (MFWF) to allow the sensors in an IoT network to effectively communicate and propagate messages. This weight function takes several parameters into account: residual energy, Chebyshev distances to neighbouring nodes and to the sink node, node density, and message priority. Second, a simulation model is presented that was built to examine the performance of the proposed protocol in terms of the end-to-end delay, rebroadcast nodes, saved rebroadcasts, and network lifetime by examining each parameter individually. The findings show that the choice among parameters or certain combinations of parameters depends on the application requirements. Third, this paper reports further simulations that were conducted to examine the impact of parameter variability on three categories of applications within the IoT context: critical, bandwidth-intensive, and energy-efficient applications. In these simulations, the performance of the proposed protocol was evaluated in comparison with the original gossiping protocol and the Fair Efficient Location-based Gossiping (FELGossiping) protocol [
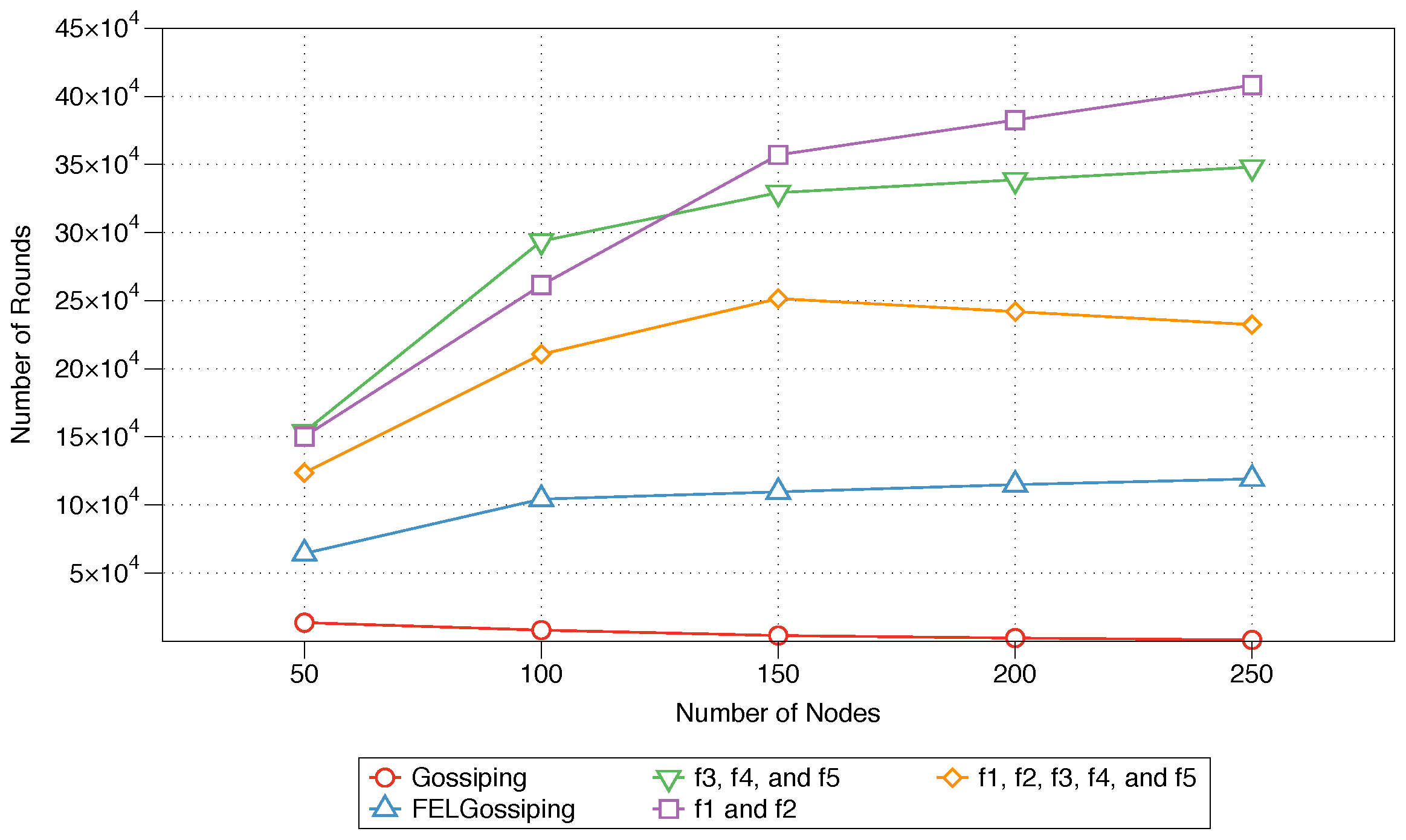
19]. The experimental results show that the proposed protocol better satisfies the requirements of each analysed type of IoT applications: it reduces the end-to-end delay for critical applications, achieves fewer rebroadcast nodes and an increased percentage of saved broadcasts for bandwidth-intensive applications, and improves the network lifetime for energy-efficient applications.
The remainder of this paper is organised as follows.
Section 2 reviews variants of the gossiping protocols for WSNs. Next, the motivating scenario underlying this work is presented in
Section 3. The system design is introduced in
Section 4, detailing the weight function, the parameters considered, and the proposed variant of the gossiping protocol. In
Section 5, the experimental configuration used for conducting the simulations is described. This section also presents and discusses the experimental results.
Section 6 assesses the performance of the proposed gossiping protocol in comparison with well-established benchmarks and reports the results. Finally,
Section 7 summarises and concludes the paper and briefly discusses future work.
2. Related Work
Various characteristics of gossiping protocols have been investigated, including their handling of bounded and small-sized messages, low-frequency interactions between nodes, random peer selection, and the unreliable interaction assumption [
20]. The power of a gossiping protocol lies in its symmetric simplicity, meaning that each node runs identical algorithms. A gossiping protocol will also operate correctly and adequately on a variety of topologies; thus, such protocols can arguably be considered topologically independent. Well-designed gossiping protocols can also eliminate the risk of disruptive load surges due to their production of bounded, almost negligible, loads. Despite these advantages, gossiping protocols also suffer from several limitations due to their bounded message sizes and low periodic message exchange rates. These limitations result in a distributed system with a severely limited information carrying capacity. The rest of this section reviews several research efforts that have focused on proposing modifications to the original gossiping protocol to address its limitations.
The Location-based Gossiping (LGossiping) protocol was developed as an improved gossiping-based method of message distribution that is based on the locations of all nodes in the network [
21]. This means that nodes reliably forward messages to known neighbours using the Global Positioning System (GPS). According to a comparative performance analysis with the original gossiping protocol as the benchmark, LGossiping, to some extent, solves the delay problem of the original protocol. Nevertheless, there are many instances in which the data fail to reach the sink. In addition, the network size was fixed to 100 nodes throughout the experiments. An improved version of the LGossiping protocol, Energy Location-based Gossiping (ELGossiping), bases its selection of the next node on its distance to the sink [
22]. Therefore, when an event is detected by a node, the next hop is determined by selecting the neighbouring node with the maximum energy and the minimum distance to the sink. The performance of ELGossiping in terms of the number of live nodes, the energy consumption, and the packet loss was comparatively assessed against the performances of Gossiping and LGossiping. The findings showed that ELGossiping outperforms the other two protocols, with an increased network lifetime, a reduced number of hops and lower energy consumption. However, the authors did not mention how the distance to the main station is measured or determined.
A chance-based gossiping protocol, CHGossiping, was proposed to overcome the delay problems of the LGossiping algorithm and to reduce the number of non-input events at the sink [
23]. Similar to ELGossiping [
22], this routing algorithm considers both a node’s energy and its distance to the sink. In CHGossiping, the next-hop node is randomly selected with a probability based on the remaining energy of a node and its distance to the sink. A node’s chance for selection is increased when it is closer to the sink and contains more residual energy. This approach decreases the delay and consumes energy more efficiently. The performance of CHGossiping was comparatively assessed against the performances of the original gossiping protocol and LGossiping [
21] with regard to the network lifetime, energy consumption, and packet loss. The findings showed that CHGossiping performs better than the other two routing protocols; it proved to be more reliable and energy efficient, with an increased network lifetime. Although the chance parameter is calculated using both the node’s energy and distance to sink, it is still sent in the node greeting packet along with the other parameters. This would cause some network overhead which was not considered in the design of the CHGossiping protocol.
The Fair Efficient Location-based Gossiping (FELGossiping) protocol was later proposed to control the energy consumption of the nodes in a WSN during communication and thus to increase the network’s lifetime [
19]. The selection of the next node in FELGossiping is based on its residual energy and distance to the sink. In FELGossiping, when a node detects an event and wants to send information, it determines its next hop based on its neighbouring nodes’ residual energy levels and hop counts. This procedure continues until the message reaches the sink. Thus, it effectively increases the energy available to the network and maximises its lifetime. The performance of the proposed protocol was compared with the performances of three other algorithms, namely, the original gossiping protocol, LGossiping [
21], and ELGossiping [
22], in terms of the packet loss, number of live nodes, energy consumption, and delay. FELGossiping outperformed the other protocols by achieving a high packet delivery ratio, reduced delays, a fair energy balance among nodes, and an increased node lifetime. Nevertheless, FELGossiping uses hop counts for distance measurement; however, it is very loosely correlated with the distances as it represents the number of intermediate nodes in which data pass between the source and destination nodes.
Fuzzy-Gossip is a modified gossiping protocol that uses fuzzy logic to reduce the energy waste caused by recirculation redundancies, thus improving the network lifetime [
24]. The proposed protocol determines the next node from among a set of candidate nodes by favouring nodes with the highest remaining energy levels and the shortest distances to the sink. This is made possible through the use of fuzzy logic to determine a selection cost for each candidate node based on a series of five membership functions. The effectiveness of Fuzzy-Gossip in comparison with three other protocols, i.e., the original gossiping protocol, LGossiping [
21], and ELGossiping [
22], was demonstrated through simulations. Compared with these protocols, Fuzzy-Gossip was found to reduce message routing redundancy and balance energy consumption more effectively while also maximising the network lifetime. However, this protocol is arguably unscalable because the computational overhead due to the processing of the fuzzified values can lead to high energy consumption.
A probabilistic approach is adopted in a new variant of the gossiping protocol, Gossiping-PS, which introduces new mechanisms for the selection of the next node based on a probability function [
25]. The motivation for this proposal was to reduce the routing delay and improve the network lifetime. The probability function is inspired by the ant colony function [
26] and determines the node to be selected based on two factors: the residual energy of the node and its visibility [
27]. The node with the highest probability, i.e., a node with a high level of energy and a close distance to the sink, will thus be selected as the next hop for routing. The performance of Gossiping-PS was compared with that of the simple gossiping protocol in terms of the response time, network lifetime, and residual energy. The findings showed that the Gossiping-PS protocol reduces the response time and prolongs the network lifetime in comparison with those achieved with the original gossiping protocol. Nonetheless, the probability function that combines both the residual energy of the node and its visibility was not mentioned in the study.
An energy-efficient variant of the gossiping protocol was proposed based on fuzzy logic and Chebyshev distances [
28]. In this approach, a distance-based scheme is adopted to determine the path of a message from its source to its destination by favouring nodes with the most residual energy and the shortest distances to the sink. The performance of this new routing algorithm was compared against those of the traditional flooding and gossiping protocols in terms of the energy consumption, hop count, and network lifetime. The results showed that the new protocol enhances the performance of a WSN and increases its lifespan. Nevertheless, despite the use of the resource-saving Chebyshev distance computation, the fuzzy logic calculations consume considerable computational resources—resources that often need to be preserved to maximise a WSN’s lifetime.
Another gossiping protocol variant, Fitness-Gossiping (FGP), uses a fitness function to select the optimal next node [
29]. This is done to decrease the energy consumption of the simple gossiping protocol and thus increase the network lifetime. The fitness function considers the remaining energy, next-node distance, and sink distance in order to select the node with the highest fitness to which to pass along the packet. The proposed protocol was compared against the simple gossiping protocol in terms of the delay, energy consumption, and number of live nodes. The results confirmed that FGP outperforms the simple gossiping protocol by balancing the power consumption more effectively, thereby enhancing the network lifetime. However, the authors compared their work with the traditional gossiping protocols and did not consider other protocols.
Similar to the previously mentioned gossiping protocols, DGossip bases its selection of the next node on its distance to the sink and residual energy [
30]. The value used for node selection is computed by means of a factor function that considers each node’s energy and distance to the sink as well as the initial energy and the total distance from the source to the destination. The performance of DGossip was compared against that of the original gossiping protocol to determine its effectiveness in terms of energy, latency, and the number of live nodes. The results showed an improvement in energy dissipation and efficiency when utilising the DGossip protocol, which, in turn, increases the network lifetime and reduces latency. Similar to FGP, the authors did not consider other types of protocols in the evaluation.
Table 1 summarises the reviewed literature on gossiping protocol variants. For package dissemination, the majority of these works adopt various computations that utilise the distance to the sink and/or the residual energy as the primary parameter(s) for determining the next node for selection [
22,
23,
24,
25,
28,
30]. Other parameters examined include the distance to each neighbour node [
29], the locations of the nodes [
21], and the hop count to the sink [
19]. These modified gossiping protocols have typically been evaluated in comparison with the conventional gossiping protocol or other modified gossiping protocols using various metrics. The energy consumption has been most commonly utilised to assess the performance of a proposed protocols against the performances of other protocols in a fixed-size network (100 nodes) [
19,
21,
22,
23,
24,
25,
28,
29,
30], followed by the hop count [
22,
23,
28,
29,
30], the number of live nodes [
19,
24,
28,
29,
30], the packet loss [
19,
21,
22,
23], and the network lifetime [
22,
23,
25]. The results of these works reflect the positive impact of utilising adjusted parameters and computations to enhance the performance of the original gossiping protocol.
In the context of IoT applications and networks, this paper aims to expand on previous works that have addressed the issues of energy consumption and the distances to the sink and the nearest neighbour in gossiping protocols by also considering the node density (number of one-hop neighbours) and message priority. The impact of each of the five parameters is closely examined for various types of IoT applications to determine the ideal parameter balance that can satisfy the needs of each type of application.
4. System Design
The main objective of any IoT application is to allow its end users to access services and information that are specific to their time, environment, and location. Therefore, devices and sensors must be aware of their surroundings as well as the main objective of the underlying application. For the purpose of facilitating data dissemination in an IoT environment, this paper proposes a communication mechanism, based on the conventional gossiping protocol, that utilises both the content of the distributed messages and the network context. Designing an efficient mechanism for communication among sensors in an IoT application involves several challenges related to the following concerns:
Power consumption
Storage capacity
Bandwidth limitations
These challenges are addressed in the proposed protocol by allowing the sensors used in an IoT application to communicate effectively using a multi-factor weighting function (MFWF). The proposed content- and context-aware protocol can be simply described as follows:
When a source node has new data to send to the sink node, it will first communicate with its neighbouring nodes to gather information related to their energy levels and physical locations.
Once the node has gathered the neighbouring nodes’ information, it will assign a weight value to each neighbouring node. The weight value (
w) is calculated for each neighbouring node as follows:
where
n is the total number of parameters used in the function and
is the weighting factor for parameter
. The value of the weighting factor can be set to either 0 or 1. If it is set to 1, then the corresponding parameter is considered in the calculation; otherwise, it is not.
The next node to be selected will depend on the weight value computed. The node with the highest weight value is selected, and the message is forwarded. If multiple neighbouring nodes have the same highest weight value, then the source node will randomly select one node from among them.
This procedure will continue at every selected node, i.e., sender node, until the message is received by the sink node.
The main objective of designing the MFWF as shown in Equation (
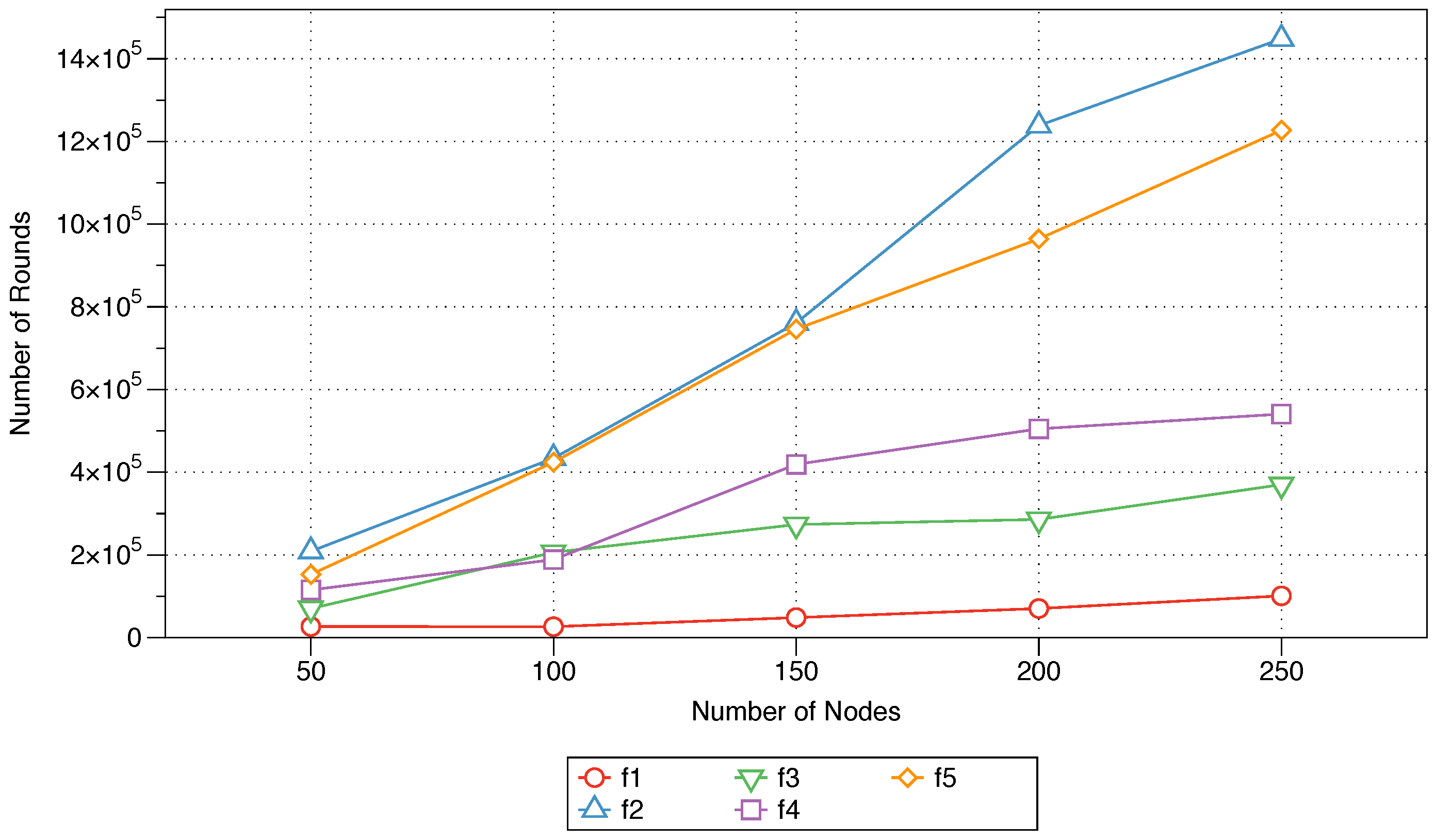
1) is to allow the impact of each parameter on the efficiency of the underlying IoT application to be investigated individually. Moreover, the MFWF is scalable, as new parameters can be added in the future to further improve efficiency, thus ensuring the continued growth of the proposed protocol to maximise its robustness and flexibility. The detailed procedure is shown in Algorithm 1. The weight function includes the following parameters: residual energy, next-node distance, sink distance, node density, and message priority. The rest of this section describes each of the parameters considered in the MFWF.
| Algorithm 1 The algorithm for the proposed protocol |
| 1: | ▹ Initial energy |
| 2: | |
| 3: | |
| 4: | |
| 5: | ▹ zero if low and one if high |
| 6: | |
| 7: | |
| 8: | |
| 9: | |
| 10: | |
| 11: | whiledo |
| 12: | if data sensed ‖ packet received then |
| 13: | for all node n : neighbours do |
| 14: | |
| 15: | |
| 16: | |
| 17: | |
| 18: | |
| 19: | |
| 20: | |
| 21: | |
| 22: | |
| 23: | |
| 24: | |
| 25: | add to SelectionList |
| 26: | end for |
| 27: | SortDescending (SelectionList) |
| 28: | Send data to the first node in SelectionList |
| 29: | end if |
| 30: | end while |
4.1. Energy
This parameter represents the remaining energy (residual energy,
) of a neighbouring node. Therefore, when a source node has data to send, it requests its neighbours to send their residual energy values. The energy parameter for a neighbouring node is based on Equation (
2):
where
E is the node’s initial energy.
4.2. Next-Node Distance
This parameter represents the Chebyshev distance between the source node and its neighbouring node. The use of the Chebyshev distance instead of the Euclidean distance is inspired by Dutta et al. [
28]. The Chebyshev distance is defined as the maximum difference between two vectors in any coordinate. In a two-dimensional space, the Chebyshev distance between two points
p and
q with Cartesian coordinates (
) and (
) can thus be expressed as
.
An assumption is made that the coordinates of all neighbouring nodes are known and distributed throughout the network during the set-up phase. Therefore, the distance can be calculated directly according to Equation (
3):
where
denotes the source node’s coordinates and
denotes the neighbouring node’s coordinates.
4.3. Sink Distance
This parameter represents the Chebyshev distance between the neighbouring node and the sink node. The sink distance parameter for each neighbouring node is calculated based on Equations (4)–(6):
where
denotes the sink node’s coordinates,
is the Chebyshev distance between the source node and the sink node and
is the Chebyshev distance between the neighbouring node and the sink node.
4.4. Node Density
This parameter represents the fraction of nodes that are considered one-hop neighbours of the neighbouring node. In our proposed protocol, nodes that have a larger number of neighbours are favoured to ensure reliable message delivery. Once the total number of neighbours is determined, the parameter can be calculated according to Equation (
7):
where
is the total number of neighbours of the neighbouring node and
N is the total number of nodes in the network.
4.5. Message Priority
In the IoT context, different types of messages with varying levels of criticality are propagated through a network. For instance, in this article’s motivating scenario (see
Section 3), a message indicating an emergency, such as a lack of motion from Mrs. Fatimah, should be given high priority to indicate the need for a fast delivery protocol to ensure that Norah can adjust her route immediately to reach Mrs. Fatimah. In the proposed protocol, messages are classified into two levels of priority: high and low. Setting the message priority will be done through the application itself. Therefore, for high priority messages, this parameter is set to 1; while for low priority messages, this parameter is set to 0. This is shown in Equation (
8):
7. Conclusions and Future Work
This paper proposed a flexible context-aware variant of the gossiping routing protocol for utilisation in WSNs. The new protocol uses an MFWF to enable effective communication among resource-constrained sensors. This MFWF considers several parameters that impact the performance of an IoT network or WSN; these parameters include the residual energy, the distances to the next node and to the sink, the neighbour density, and the message priority. The effects of these parameters on several performance measures were examined to assist in the selection of the most relevant parameters or combinations of parameters for three types of IoT applications (critical, bandwidth-intensive, and energy-efficient). This resulted in three tailored MFWFs, one for each of the application categories (see Equations (
10)–(
12)).The performances of these three MFWFs were then comparatively assessed against those of the traditional gossiping and FELGossiping [
19] protocols and summarised in
Table 5. Both critical and bandwidth-intensive MFWFs proved proficient for critical IoT applications, as it took the least delay to reach its destination at varying network scales. For energy-efficient IoT applications, both the energy-efficient MFWF and critical MFWF demonstrated their capability of improving the network lifetime. In the case of bandwidth-intensive IoT applications, three protocols proved equally applicable: critical MFWF, bandwidth-intensive MFWF, and FELGossiping.
Several limitations of the proposed protocol lend themselves to future work. For instance, in this paper, the weighting factors were set only to either 0 or 1; however, considering the possibility of using fractional numbers between 0 and 1 will be valuable. Also, exploring other new parameters and factors to include in the proposed function can make the proposed protocol more adaptive to the requirements of different IoT applications. Additionally, the MFWF parameters were examined in isolation from each other; therefore, the effect of the parameters on each other was not considered experimentally. In the future, this effect will be studied between two or more parameters to better inform the construction of the MFWFs for various IoT applications. Moreover, the overhead caused by message exchanging among nodes will be eliminated by transmitting only neighbouring node’s information that has been changed. The three IoT application discussed in this paper, were considered separately and it would be valuable to study the effect of a mixed traffic IoT and its impact on their performances. Finally, a more thorough investigation of the proposed algorithm will be considered to comparatively assess its performance against other gossip variants and popular IoT protocols.