Wireless Communication Technologies for Safe Cooperative Cyber Physical Systems
Abstract
1. Introduction
2. Technical Background
2.1. Co-CPSs Safety Definitions
2.2. Safety Approach in SafeCOP
- a safety-assurance framework for Co-CPS,
- a reference “Runtime Manager” is able to detect at runtime abnormal behaviour, triggering, if needed, a safe degraded mode.
2.3. Security vs. Wireless Communication
2.4. Security Approach in SafeCOP
2.5. SafeCOP Use Cases
- (A)
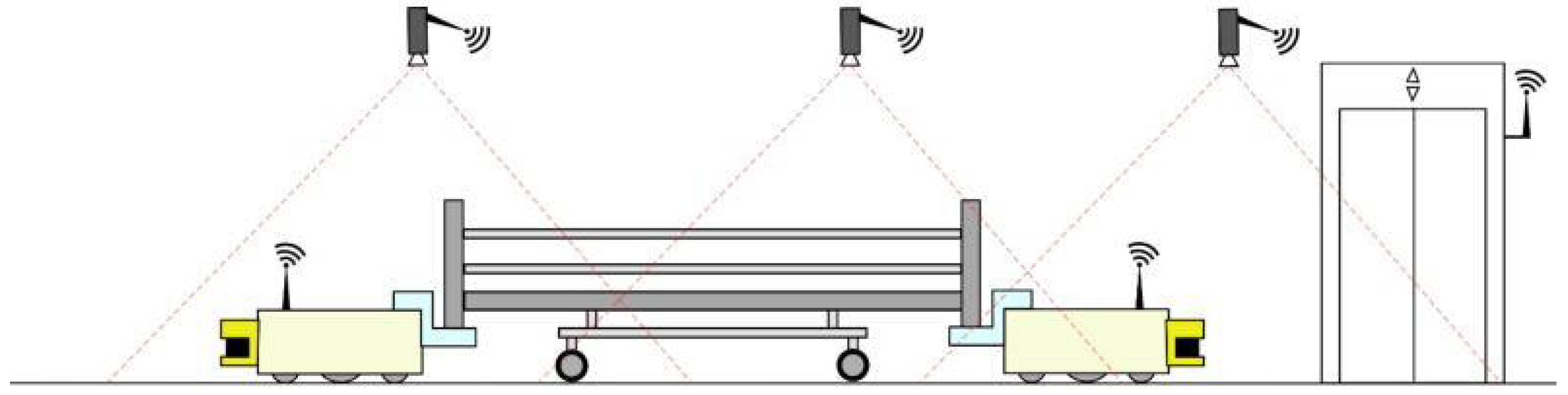
- Hospital Application: Autonomous Hospital BedsTo reduce the risk of contamination and spread of disease, hospital beds are thoroughly cleaned before being used by a new patient. In most hospitals, the cleaning is performed manually on site in each patient room, even in hospitals where they have a centralized bed-washing facility (CBWF). This is because moving the bed to and from the CBWF takes about the same amount of time as cleaning the bed in the ward. Both manually cleaning a bed and transporting beds to the CBWF are tasks that require hard physical labor and non-ergonomic motions and positions. To avoid unnecessary strain on hospital workers, and to free up a large amount of their time, this use case proposes an automated solution using two small mobile robots, designated MiR00. After the discharge of a patient, the MiR100s will autonomously transport the bed from the ward to the CBWF for washing, and then bring a clean bed from the CBWF back to the ward. A MiR100 will be attached to each end of the bed, and coordinate and synchronize their movement through the use of safe communication. As the MiR100s are small, their vision is quite limited. To assist in navigation and obstacle detection, a network of cameras will be installed in the hospital hallways. These cameras will act as remote eyes, allowing the robots to maneuver in restricted spaces and keep out of peoples’ way.Figure 1 provides the layout of the hospital beds testbeds, where two individual mobile robots are moving in the corridor covered by wireless access points.
- (B)
- Maritime Application: Autonomous Boat PlatoonsSince international shipping is responsible for approximately 90% of world trade transportations, the safety of vessels is critical to the global economy. Human errors account for approximately 75% of the almost 15,000 marine liability insurance claims analyzed over five years, which correspond to over $1.6 bn [41]. Autonomous/semi-autonomous ships could improve maritime safety but revolutionize the movement of ships [42]. International Maritime Organization (IMO, London, UK) has received a proposal supported by a number of countries to include autonomous ships on its agenda. The IMO Maritime Safety Committee will establish a new international legal framework for the safe operation of autonomous vessels. It is evident that safety considerations are crucial in this respect. The main barrier to the development of autonomous shipping is represented by the concerns related to the risk of collision between manned and unmanned vessels. Moreover, as the number of cyber threats are increasing, a great concern is raised on specific cyber-attacks targeting the control of autonomous vessels [43]. To reduce inherent risk, cybersecurity should be taken at a high priority when developing autonomous ships.Among various explorations of autonomous ships, bathymetry (Bathymetry is the study of underwater depth of lake or ocean floors. Bathymetric charts are typically produced to support geophysical exploration and environmental monitoring) is a very attractive application [44]. Bathymetry is usually performed by sailing a boat with a multi-beam sonar in a rather repetitive lawn-mover pattern. The data acquisition should ideally be going on 24/7, but when using manned survey boats this possibility may be limited due to crew Health and Safety Executive (HSE) regulations. This is an ideal task for an unmanned surface vehicle (USV) that sails these repetitive patterns 24/7. USV application to bathymetry will result in a twofold gain: saving costs and reducing HSE risk for survey personnel [45]. This gain increases for bathymetry measurements in extreme conditions like the Arctic Ocean, where USV may replace a fully-crewed ship and shows better performance in adverse environments and inclement weather.At the current stage, the USV has to be remotely controlled by a human operator who is located on another vessel. Such cooperation between the USV and the manned vessel can dramatically increase navigation safety while heavily relying on wireless communications between them, as illustrated in Figure 2. The USV and manned vessel have to periodically exchange critical information, such as vessel speed, course and position, to maintain a certain formation. The USV receives instructions and commands from the manned vessel to maneuver or stop. When safety-critical events occur (e.g., potential collisions), the manned vessel sends safety control commands to the USV, which has to respond within a certain time to avoid collisions. Therefore, packets carrying critical information and safety control commands are subject to very low latency requirements.
- (C)
- Vehicular ApplicationsSafety, comfort and efficiency of both roads and vehicles have improved considerably over the last decade. However, our transportation system still suffers from many problems. The fast growth of urban areas causes an increasing trend of vehicular traffic and road accidents, resulting in serious socioeconomic problems. According to the latest report from the United States (U.S.) National Highway Traffic Safety Administration (NHTSA, Washington, DC, USA), the annual casualties of motor vehicle crashes was a total of 32,999 fatalities and 3.9 million injuries on the roadways of the U.S., which is equal to the annual economic loss to $836 billion [46]. Moreover, in 2014, highway users in the U.S. spend extra unnecessary 6.9 billion hours in traffic jams and consume an additional 3.1 billion gallons of fuel, adding up to an annual economic loss of $160 billion [47].To address these problems, there have been worldwide efforts by automotive companies, universities, and governments to provide applications, services, and technologies that connect a vehicle to its surroundings. Examples of such applications and services may include adaptive cruise control, automate braking, remote vehicle diagnostics, hazards, and blind spot warnings. Typically, a connected vehicle (CV) includes interactive advanced driver-assistance systems (ADAS) and cooperative intelligent transport systems (C-ITS), where vehicle awareness concerning its current traffic context is aided by information exchange with surrounding vehicles through vehicle-to-vehicle (V2V) communication, close roadside units through vehicle-to-infrastructure (V2I) communication or people through vehicle-to-pedestrian (V2P) communication, collectively referred as V2X. The use of V2X communications can expand the horizon of on-board sensing systems, thereby eliminating 80% of the current road accidents and providing a smarter and safer ground transportation system [48]. These technologies are anticipated to offer significant benefits, including: reduced driver stress and possibility for passengers to rest and work while traveling; reduced driver costs of paid drivers for taxis and commercial transport; mobility for non-drivers including disabled people, therefore reducing the need for motorists to chauffeur non-drivers, and to subsidize public transport; increased road safety and therefore crash costs and insurance premiums; reduce high-risk driving, such as when impaired e.g., by alcohol consumption; efficient parking, increasing motorist convenience and reducing total parking costs; increase fuel efficiency and reduce pollution emissions. SafeCOP defined three use cases related to the vehicular applications, as described in the following.
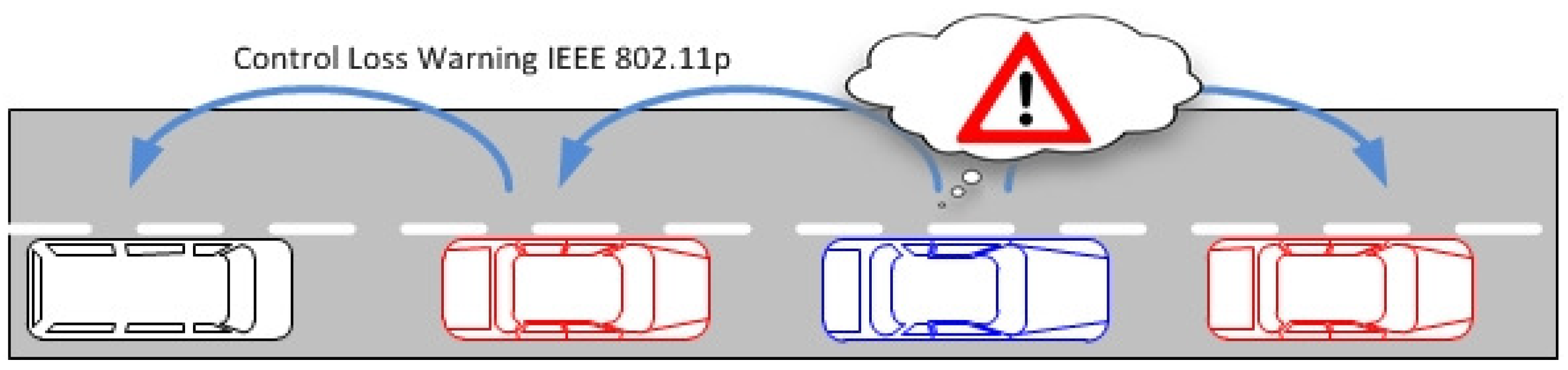
- Vehicle Control Loss WarningThe goal of this use case is to demonstrate how we can apply and extend wireless technologies to support automotive cooperative V2x-based systems such as auto-braking in vehicle platooning. Besides inter-vehicle networking, this use case is also exploring intra-vehicle communication. Therefore, we consider a scenario where a platoon of vehicles is traveling along a motorway, and Control Loss Warning (CLW) system should be able to detect any safety relevant occurrence that may compromise the vehicle’s platooning ability, such as a braking system failure. Upon detection, the system should send a CLW alert to the other elements involved in the process, e.g., other cars in the platoon.The operation in this use case is illustrated in Figure 3. In case of control loss of any vehicle (the blue vehicle in the figure), CLW alert is delivered from car to car forward and backward using the V2V communication infrastructure, and eventually each vehicle gains knowledge about the CLW and can react in a pre-defined manner, by entering in a safe mode. In addition, a wireless network of in-vehicle sensors and actuators is exchanging data with the on-board unit to inform about the status of different automotive systems.
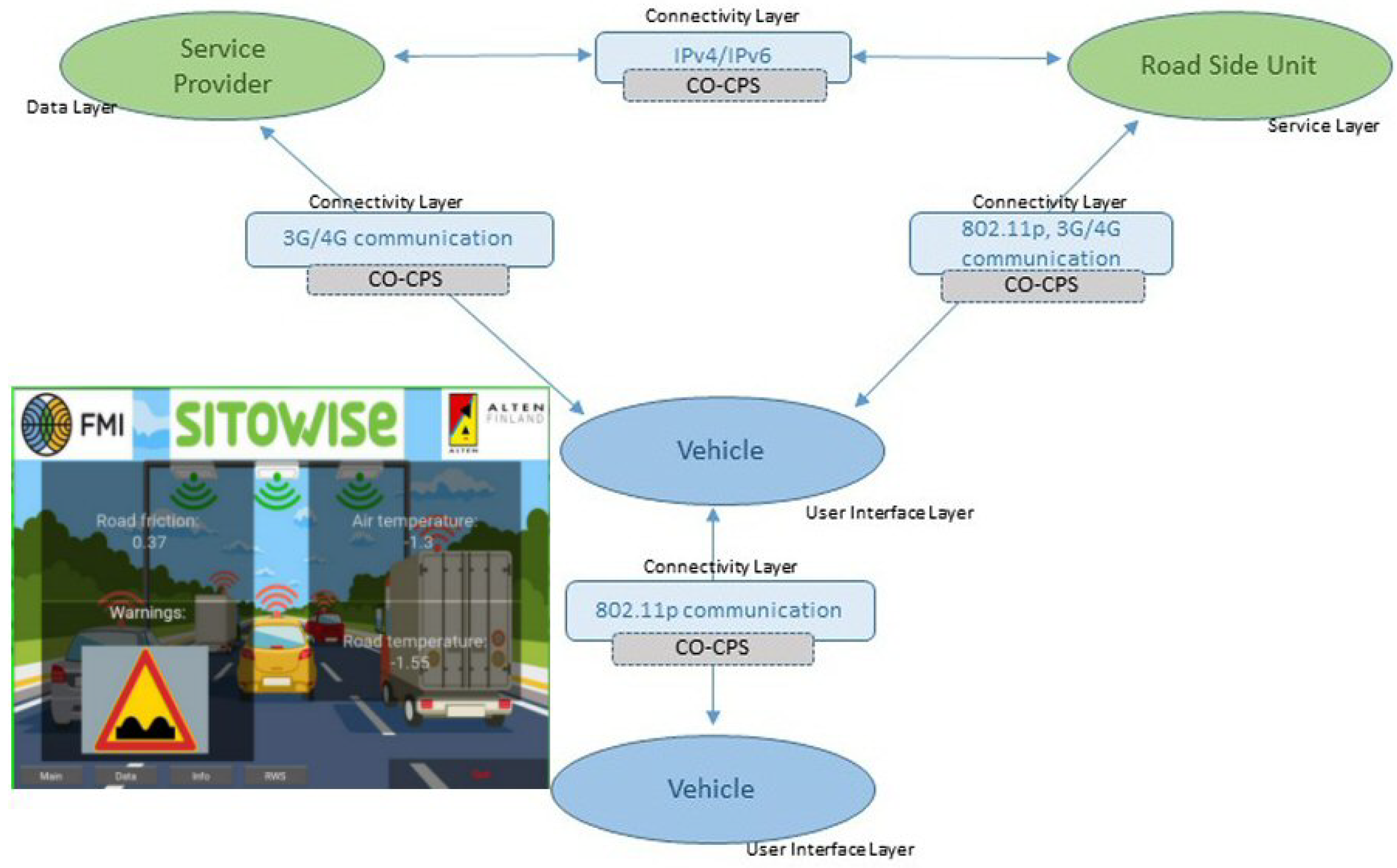
- Vehicles and Roadside Unit (RSU) interactionThis use case has been built upon the data exchange between the roadside road weather station and a passing vehicle. Road weather stations (RWS) are typically installed to fixed locations beside the road, collecting different measurement parameters related to weather and traffic, and delivering this data to a single data collection point, typically being the road administrator. Within its operative RWS and vehicular measurement entity, FMI demonstrates this operational environment [49]. During the RWS pass, the vehicle receives up-to-date local road weather information. As an exchange, vehicle can also deliver its own observational information back to RWS, to be used as local supporting data in meteorological services. In this vehicle-roadside unit interaction, we must ensure that the delivered data is not altered or violated by a third party or some communication malfunctioning.The primary scenario in this use case is data exchange between vehicle and RWS, when and where the vehicle is passing the RWS. The basic scenario is introduced in [50]. This scenario is extended to cover also data exchange between two vehicles (scenario 2). In this case, both vehicles share the data received from the latest RWS, and as a result both vehicles will obtain up-to-date road weather data from the area ahead. The communication in this scenario is naturally local area communication. In the final extension (scenario 3), we employ an IoT cloud as communication entity, and instead of direct data exchanges between vehicles and RWSs, the IoT cloud shares the location-based relevant data with vehicles and RWSs. The architecture of these resulting three scenarios are presented in Figure 4. A vehicle and a roadside unit are participating in the first scenario (vehicle-to-infrastructure), two vehicles in the second scenario (vehicle-to-vehicle) and, finally, a service provider, a vehicle and a roadside unit to the final (third) IoT-cloud scenario.
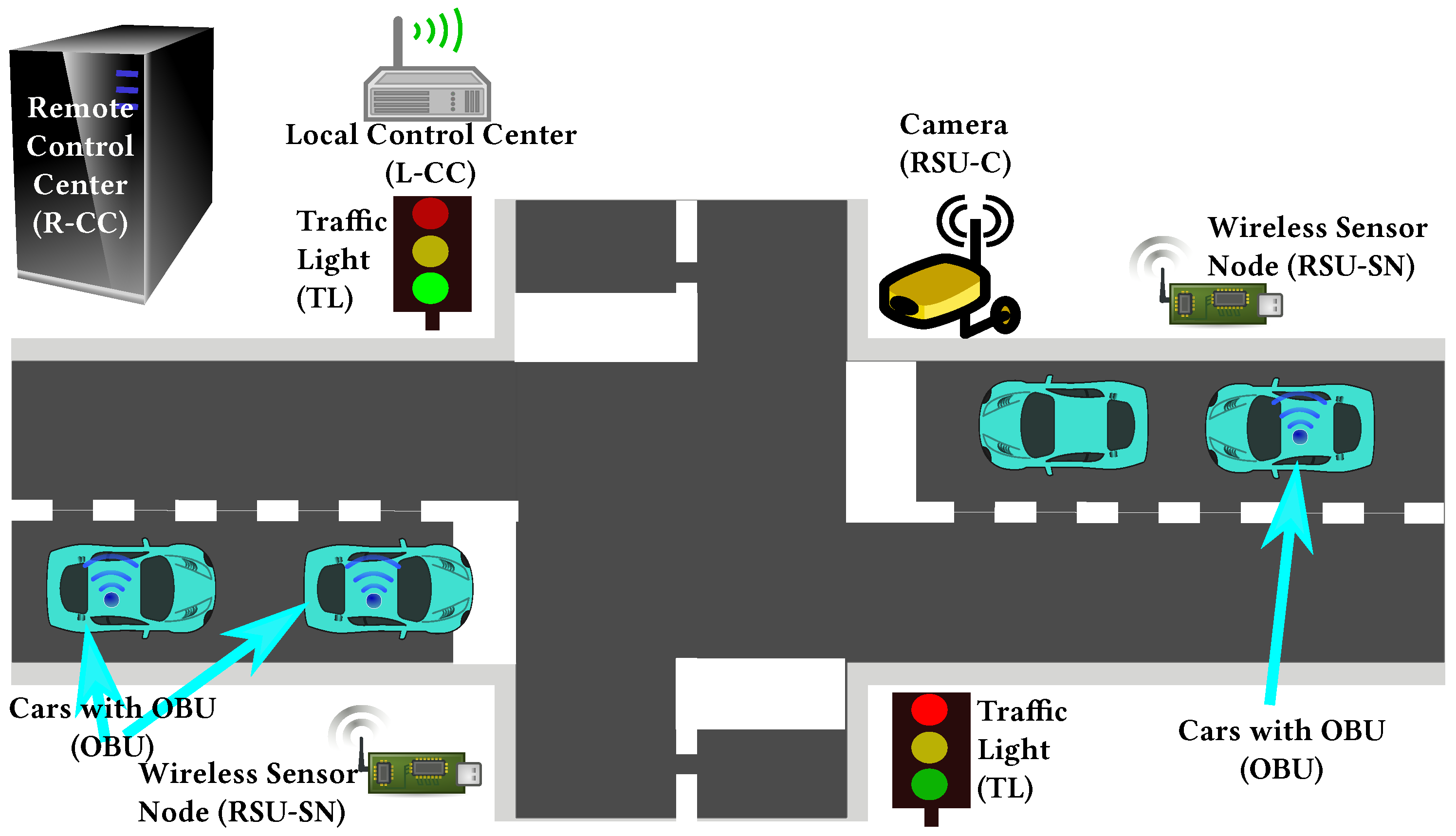
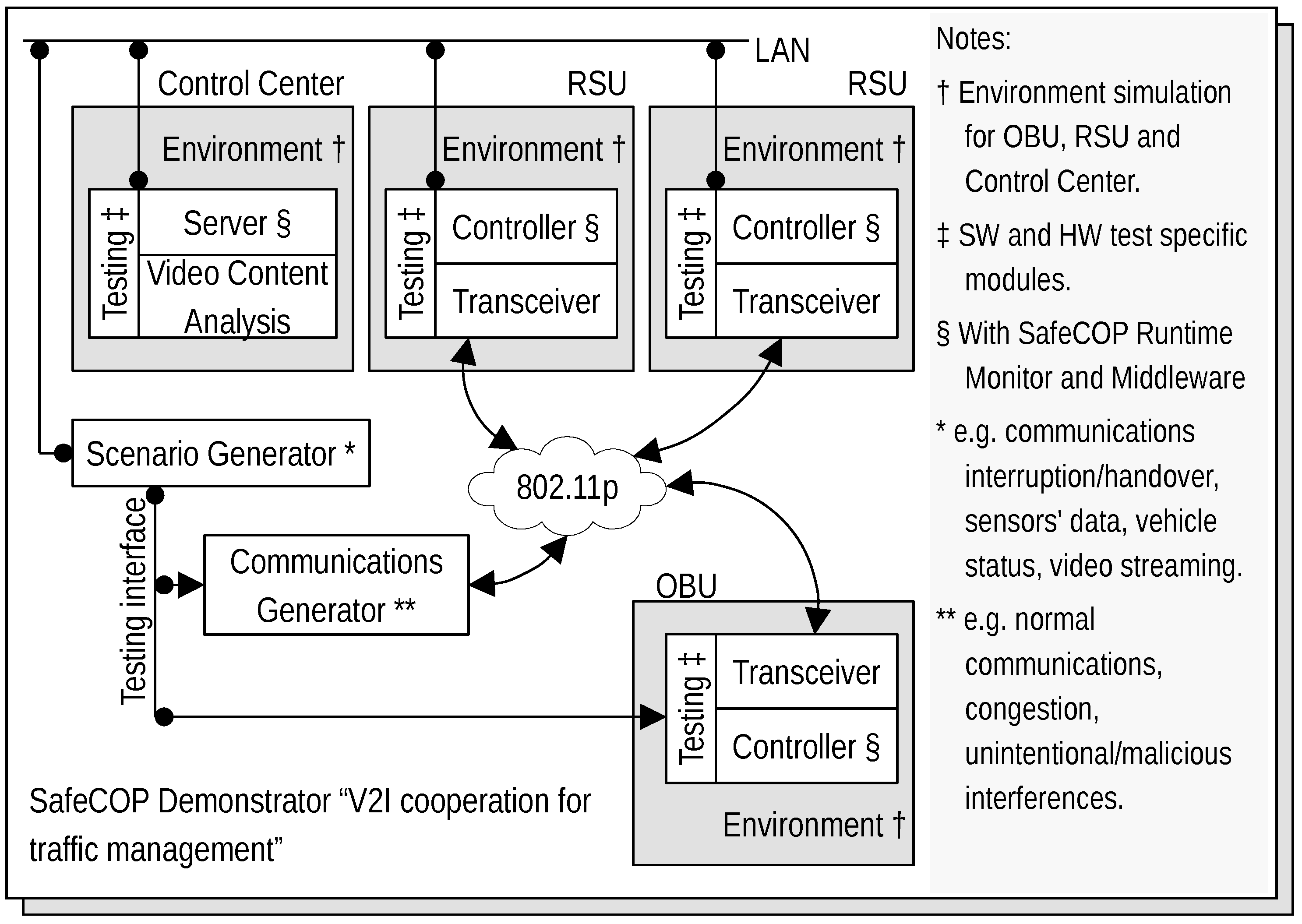
- V2I Cooperation for Traffic ManagementThis use case aims at providing an innovative platform that integrates into the V2I network both traffic management (TM) and Video Content Analysis (VCA) functionalities, as shown in Figure 5. VCA consists in the acquisition from video cameras (referred to as RSU-C in Figure 5) and subsequent elaboration through appropriate algorithms. Active road safety (ARS) programmes will strongly benefit from this integration, which enables, via VCA, the early-detection of possible dangerous road events/situations (e.g., vehicles slowing down, vehicles queue, motionless objects) and, via TM applications, the fast drivers’ alert of such traffic anomalies [51,52].The probability of traffic accidents will decrease by providing assistance to drivers exploiting both ARS (e.g., collision avoidance systems) and other management applications, like Adaptive Traffic Light Systems (A-TLSs) and dedicated wireless sensor networks (WSNs). A-TLSs change the traffic lights signaling plan (the duration of red, yellow and green phases) according to a set of control parameters, e.g., the time and the day. A-TLS improvements enabled by VCA allow the optimization of the signaling plan according to the changing traffic conditions, usually by extending the green phase when vehicles are closely spaced.Figure 6 shows the architecture of the envisaged system. It integrates several SafeCOP framework components, including runtime mechanisms for safety assurance and distributed safety-critical cooperation techniques (based on extensions to IEEE 802.11p), into a Traffic Management Application, which runs in a distributed way. This system will represent one of the SafeCOP demonstrators. It is composed of on-board (OBU) and road side (RSU) units, and a server-based Control Center. Communications between the parts of the demonstrator system are performed through radio frequency front-ends which transmit and receive on-the-air, or through attenuators and noise generators for testing purposes. The OBU integrates radio communication and inertial sensors, allowing additional information on vehicle behavior to be received by the RSU. The RSU acquires video from the camera and performs the necessary initial elaboration to reduce communication times, aggregates information from vehicles in its operating range, and transmits the information over a wired connection to the remote Control Center.
3. Communication Technologies for SafeCOP Co-CPSs
3.1. Hospital Application
3.2. Maritime Application
3.3. Vehicular Applications
4. Safety and Security for SafeCOP Co-CPSs
4.1. Autonomous Hospital Beds
4.2. Autonomous Boat Platoons
- Messages authentication ensures that the message is received in the same condition as it is sent out with no bits inserted, missing or modified. If the message is modified en route, then the receiver will certainly detect this. Without message authentication, the message, which is either corrupted or modified during transmission, carries the wrong information/command and may lead the USV to an unsafe-state, e.g., colliding with an obstacle.
- Message timeliness mechanism effectively limits the age of validly of delivered messages. Thus, if an attack diverts the validated messages for replay much later, the receiver can detect the delay introduced by this attack. Without timeliness constraint, the message which is not modified/corrupted but delayed may lead the USV to an unsafe-state. For example, if the command that the USV shall reduce the speed to avoid a potential collision is delivered to the USV too late, the USV may not have sufficient time to reduce its speed to avoid collision.
- Message sequence can be used to detect message loss, repetition and insertion. Without this mechanism, the attacker may intercept messages or insert malicious messages without being detected.
4.3. Vehicle Control Loss Warning
4.4. Vehicles and Roadside Unit (RSU) Interaction
4.5. V2I Cooperation for Traffic Management
- Early detection of communication errors, i.e., packet loss, packet insertion, packet replication, packet inversion.
- Bounding to a known upper limit the WSN communication latency to the roadside unit.
- Executing image processing for VCA on two different HW components (i.e., locally on the camera and remotely on the Network Video Recorder).
5. 5G Open Challenges
- The higher service-centric layers modeling the business implementations driven by the vertical use cases.
- The lower network-centric layers representing the physical implementation and its abstraction based on software network technologies like software defined networking (SDN) and Network Function Virtualization (NFV).
5.1. Autonomous Hospital Beds
- MCData Service shall enable the control of robots;
- MCData Service shall provide a common transmission framework to use and control robots;
- MCData Service shall provide a default control latency depending on the robots type under (400 ms for a terrestrial unmanned vehicle).
5.2. Autonomous Boat Platoons
5.3. Vehicular Applications
5.3.1. Vehicle Control Loss Warning
5.3.2. Vehicles and Roadside Unit (RSU) Interaction
- Between User Equipment (UE) supporting V2X application and RSU via another UE supporting V2X application with conditionally and fully automated driving, where the payload message could vary from 50–1200 bytes and latency to 20–50 ms.
- Between RSU and UE supporting V2X application with again partially or fully automated driving, where the payload message is lower around 100 bytes and latency to 10–50 ms.
5.3.3. V2I Cooperation for Traffic Management
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Chaâri, R.; Ellouze, F.; Koubâa, A.; Qureshi, B.; Pereira, N.; Youssef, H.; Tovar, E. Cyber-physical systems clouds: A survey. Comput. Netw. 2016, 108, 260–278. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A Survey on Internet of Things: Architecture, Enabling Technologies, Security and Privacy, and Applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Lu, Y. Industry 4.0: A survey on technologies, applications and open research issues. J. Ind. Inf. Integr. 2017, 6, 1–10. [Google Scholar] [CrossRef]
- Karoui, O.; Khalgui, M.; Koubâa, A.; Guerfala, E.; Li, Z.; Tovar, E. Dual mode for vehicular platoon safety: Simulation and formal verification. Inf. Sci. 2017, 402, 216–232. [Google Scholar] [CrossRef]
- Li, Z.; Karoui, O.; Koubaa, A.; Khalgui, M.; Guerfala, E.; Tovar, E.; Wu, N. System and Method for Operating a Follower Vehicle in a Vehicle Platoon. U.S. Patent US20170329348A1, 2017. [Google Scholar]
- Balador, A.; Bohm, A.; Uhlemann, E.; Calafate, C.T.; Cano, J.C. A Reliable Token-Based MAC Protocol for Delay Sensitive Platooning Applications. In Proceedings of the 2015 IEEE 82nd Vehicular Technology Conference (VTC2015-Fall), Boston, MA, USA, 6–9 September 2015; pp. 1–5. [Google Scholar] [CrossRef]
- Pomante, L.; Marchesani, S.; Pugliese, M.; Santucci, F. A Middleware Approach to Provide Security in IEEE 802.15.4 Wireless Sensor Networks. In Proceedings of the Mobilware, Bologna, Italy, 11–13 November 2013. [Google Scholar]
- Pomante, L.; Pugliese, M.; Tiberti, W.; Bozzi, L.; Santic, M.; Santucci, F.; Giuseppe, L.D. TinyWIDS: A WPM-based Intrusion Detection System for TinyOS2.x/802.15.4 Wireless Sensor Networks. In Proceedings of the HiPEAC Conference CS2 2018, Manchester, UK, 24 January 2018. [Google Scholar]
- Kurunathan, H.; Severino, R.; Koubâa, A.; Tovar, E. IEEE 802.15.4e in a Nutshell: Survey and Performance Evaluation. IEEE Commun. Surv. Tutor. 2018, PP, 1. [Google Scholar] [CrossRef]
- SafeCOP Project’s Website. Available online: http://www.safecop.eu/ (accessed on 14 November 2018).
- Shi, J.; Wan, J.; Yan, H.; Suo, H. A survey of Cyber-Physical Systems. In Proceedings of the 2011 International Conference on Wireless Communications and Signal Processing (WCSP), Nanjing, China, 9–11 November 2011; pp. 1–6. [Google Scholar] [CrossRef]
- McKee, D.W. Survey of advances and challenges in intelligent autonomy for distributed cyber-physical systems. CAAI Trans. Intell. Technol. 2018, 3, 75–82. [Google Scholar] [CrossRef]
- Qutqut, M. A Survey of IoT Open Source Operating Systems. IET Wirel. Sens. Syst. 2018. [Google Scholar] [CrossRef]
- Dey, N.; Ashour, A.S.; Shi, F.; Fong, S.J.; Tavares, J.M.R.S. Medical cyber-physical systems: A survey. J. Med. Syst. 2018, 42, 74. [Google Scholar] [CrossRef] [PubMed]
- Abbaspour Asadollah, S.; Inam, R.; Hansson, H. A Survey on Testing for Cyber Physical System. In Testing Software and Systems; El-Fakih, K., Barlas, G., Yevtushenko, N., Eds.; Springer International Publishing: Cham, Switzerland, 2015; pp. 194–207. [Google Scholar]
- Xu, L.D.; Duan, L. Big data for cyber physical systems in industry 4.0: A survey. Enterp. Inf. Syst. 2018, 1–22. [Google Scholar] [CrossRef]
- Gürdür, D.; Asplund, F. A systematic review to merge discourses: Interoperability, integration and cyber-physical systems. J. Ind. Inf. Integr. 2018, 9, 14–23. [Google Scholar] [CrossRef]
- Bartocci, E.; Deshmukh, J.; Donzé, A.; Fainekos, G.; Maler, O.; Ničković, D.; Sankaranarayanan, S. Specification-Based Monitoring of Cyber-Physical Systems: A Survey on Theory, Tools and Applications. In Lectures on Runtime Verification: Introductory and Advanced Topics; Bartocci, E., Falcone, Y., Eds.; Springer International Publishing: Cham, Switzerland, 2018; pp. 135–175. [Google Scholar] [CrossRef]
- Giraldo, J.; Urbina, D.; Cardenas, A.; Valente, J.; Faisal, M.; Ruths, J.; Tippenhauer, N.O.; Sandberg, H.; Candell, R. A Survey of Physics-Based Attack Detection in Cyber-Physical Systems. ACM Comput. Surv. 2018, 51, 76:1–76:36. [Google Scholar] [CrossRef]
- Bou-Harb, E. A Brief Survey of Security Approaches for Cyber-Physical Systems. In Proceedings of the 2016 8th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Larnaca, Cyprus, 21–23 November 2016; pp. 1–5. [Google Scholar] [CrossRef]
- Shi, L.; Dai, Q.; Ni, Y. Cyber–physical interactions in power systems: A review of models, methods, and applications. Electr. Power Syst. Res. 2018, 163, 396–412. [Google Scholar] [CrossRef]
- Schmidt, M.; Åhlund, C. Smart buildings as Cyber-Physical Systems: Data-driven predictive control strategies for energy efficiency. Renew. Sustain. Energy Rev. 2018, 90, 742–756. [Google Scholar] [CrossRef]
- Moness, M.; Moustafa, A.M. A Survey of Cyber-Physical Advances and Challenges of Wind Energy Conversion Systems: Prospects for Internet of Energy. IEEE Internet Things J. 2016, 3, 134–145. [Google Scholar] [CrossRef]
- Bolbot, V.; Theotokatos, G.; Bujorianu, M.L.; Boulougouris, E.; Vassalos, D. Vulnerabilities and safety assurance methods in Cyber-Physical Systems: A comprehensive review. Reliab. Eng. Syst. Saf. 2018. [Google Scholar] [CrossRef]
- Wolf, M.; Serpanos, D. Safety and Security in Cyber-Physical Systems and Internet-of-Things Systems. Proc. IEEE 2018, 106, 9–20. [Google Scholar] [CrossRef]
- Rajkumar, R.; Lee, I.; Sha, L.; Stankovic, J. Cyber-physical systems: The next computing revolution. In Proceedings of the Design Automation Conference, Anaheim, CA, USA, 13–18 June 2010; pp. 731–736. [Google Scholar] [CrossRef]
- MÃŒller, H.A. The Rise of Intelligent Cyber-Physical Systems. Computer 2017, 50, 7–9. [Google Scholar] [CrossRef]
- Avizienis, A.; Laprie, J.; Randell, B.; Landwehr, C. Basic Concepts and Taxonomy of Dependable and Secure Computing. IEEE Trans. Dependable Secure Comput. 2004, 1, 11–33. [Google Scholar] [CrossRef]
- Risk Management—Guidelines; ISO 31000:2018; Technical Report; ISO: Geneva, Switzerland, 2018.
- Principles for Barrier Management in the Petroleum Industry; Technical Report; Petroleum Safety Authority Norway: Stavanger, Norway, 2013.
- Leveson, N. A new accident model for engineering safer systems. Saf. Sci. 2004, 42, 237–270. [Google Scholar] [CrossRef]
- United States Department of Defense. Procedures for Performing a Failure Mode, Effects and Criticality Analysis 1949; MIL-P-1629A; Technical Report; United States Department of Defense: Arlington, VA, USA, 1980.
- Rausand, M.A.H. System Reliability Theory: Models, Statistical Methods, and Applications; John Wiley and Sons: Hoboken, NJ, USA, 2004. [Google Scholar]
- International Electrotechnical Commission. Functional Safety of Electrical/ Electronic/Programmable Electronic Safety Related Systems—Part 3: Software Requirements, 65A/550/FDIS, IEC; Technical Report IEC 61508; International Electrotechnical Commission: Geneva, Switzerland, 2009. [Google Scholar]
- The CIS Security Metrics; Technical Report; The Center for Internet Security (CIS): East Greenbush, NY, USA, 2010.
- Kert, M.J.; Lopez, E.B. State-of-the-Art of Secure ICT Landscape. Technical Report; Network Information Security (NIS) Platform WG3. 2014. Available online: https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=1&ved=2ahUKEwj27v-GveTeAhUBzLwKHVhGB80QFjAAegQICRAC&url=https%3A%2F%2Fresilience.enisa.europa.eu%2Fnis-platform%2Fshared-documents%2Fwg3-documents%2Fstate-of-the-art-of-the-secure-ict-landscape%2Fat_download%2Ffile&usg=AOvVaw1_wGpwogadXeAgSaBYnClw (accessed on 20 November 2018).
- Zou, Y.; Zhu, J.; Wang, X.; Hanzo, L. A Survey on Wireless Security: Technical Challenges, Recent Advances, and Future Trends. Proc. IEEE 2016, 104, 1727–1765. [Google Scholar] [CrossRef]
- Horn, G.P.S. Towards 5G Security, Nokia Networks. In Proceedings of the 14th IEEE International Conference on Trust, Security and Privacy in Computing and Communication, Helsinki, Finland, 20–22 August 2015. [Google Scholar]
- Huawei. 5G Security: Forward Thinking, Huawei White Paper; Huawei: Shenzhen, China, 2015. [Google Scholar]
- Ericsson. 5G Security, Ericsson White Paper; Ericsson: Stockholm, Sweden, 2015. [Google Scholar]
- An Annual Review of Trends and Developments in Shipping Losses and Safety. Allianz Global Corporate & Specialty, 2018. Available online: http://www.agcs.allianz.com (accessed on 14 November 2018).
- Rodseth, O.J.; Burmeister, H.C. Developments toward the Unmanned Ship. Available online: www.unmanned-ship.org/munin/wp-content/uploads/2012/08/R%C3%B8dseth-Burmeister-2012-Developments-toward-the-unmanned-ship.pdf (accessed on 21 November 2018).
- Katsikas, S.K. Cyber Security of the Autonomous Ship. In Proceedings of the 3rd ACM Workshop on Cyber-Physical System Security, Abu Dhabi, UAE, 2 April 2017; pp. 55–56. [Google Scholar] [CrossRef]
- Suhari, K.T.; Karim, H.; Gunawan, P.H.; Purwanto, H. Small Rov Marine Boat for Bathymetry Surveys of Shallow Waters—Potential Implementation in Malaysia. ISPRS Int. Arch. Photogramm. Remote Sens. Spat. Inf. Sci. 2017, XLII-4/W5, 201–208. [Google Scholar] [CrossRef]
- Giordano, F.; Mattei, G.; Parente, C.; Peluso, F.; Santamaria, R. Integrating Sensors into a Marine Drone for Bathymetric 3D Surveys in Shallow Waters. Sensors 2016, 16, 41. [Google Scholar] [CrossRef] [PubMed]
- Blincoe, L.; Miller, T.R.; Zaloshnja, E.; Lawrence, B. The Economic and Societal Impact of Motor Vehicle Crashes, 2010 (Revised); Technical Report; U.S. National Highway Traffic Safety Administration (NHTSA): Washington, DC, USA, 2015.
- Schrank, D.; Eisele, B.; Lomax, T.; Bak, J. Urban Mobility Scorecard; Technical Report; Texas A&M Transportation Institute: College Station, TX, USA, 2015. [Google Scholar]
- Harding, J.; Powell, G.R.; Yoon, R.; Fikentscher, J.; Doyle, C.; Sade, D.; Lukuc, M.; Simons, J.; Wang, J. Vehicle-to-Vehicle Communications: Readiness of V2V Technology for Application; Technical Report, DOT HS 812 014; U.S. National Highway Traffic Safety Administration (NHTSA): Washington, DC, USA, 2014.
- Sukuvaara, T. ITS-Enabled advanced road weather services and infrastructures for vehicle winter testing, professional traffic fleets and future automated driving. In Proceedings of the 2018 ITS World Congress, Copenhagen, Denmark, 17–21 September 2018. [Google Scholar]
- Sukuvaara, T.; Ylitalo, R.; Katz, M. IEEE 802.11p Based Vehicular Networking Operational Pilot Field Measurement. IEEE J. Sel. Areas Commun. 2013, 31, 409–417. [Google Scholar] [CrossRef]
- Agosta, G.; Barenghi, A.; Brandolese, C.; Fornaciari, W.; Pelosi, G.; Delucchi, S.; Massa, M.; Mongelli, M.; Ferrari, E.; Napoletani, L.; et al. V2I Cooperation for Traffic Management with SafeCop. In Proceedings of the 2016 Euromicro Conference on Digital System Design (DSD), Limassol, Cyprus, 31 August–2 September 2016; pp. 621–627. [Google Scholar] [CrossRef]
- Agneessens, A.; Buemi, F.; Delucchi, S.; Massa, M.; Agosta, G.; Barenghi, A.; Brandolese, C.; Fornaciari, W.; Pelosi, G.; Ferrari, E.; et al. Safe cooperative CPS: A V2I traffic management scenario in the SafeCOP project. In Proceedings of the 2016 International Conference on Embedded Computer Systems: Architectures, Modeling and Simulation (SAMOS), Samos, Greece, 15–19 July 2016; pp. 320–327. [Google Scholar] [CrossRef]
- Guinaldo, M.; Fábregas, E.; Farias, G.; Dormido-Canto, S.; Chaos, D.; Sánchez, J.; Dormido, S. A Mobile Robots Experimental Environment with Event-Based Wireless Communication. Sensors 2013, 13, 9396–9413. [Google Scholar] [CrossRef] [PubMed]
- Jiménez-González, A.; Martínez-de Dios, J.R.; Ollero, A. An Integrated Testbed for Cooperative Perception with Heterogeneous Mobile and Static Sensors. Sensors 2011, 11, 11516–11543. [Google Scholar] [CrossRef] [PubMed]
- Sanchez-Matamoros, J.M.; de Dios, J.R.M.; Ollero, A. Cooperative localization and tracking with a camera-based WSN. In Proceedings of the 2009 IEEE International Conference on Mechatronics, Malaga, Spain, 14–17 April 2009; pp. 1–6. [Google Scholar] [CrossRef]
- Jiang, Z.; Chen, S. Cooperative control system of multiple robots using visual location. In Proceedings of the 2017 Eighth International Conference on Intelligent Control and Information Processing (ICICIP), Hangzhou, China, 3–5 November 2017; pp. 168–172. [Google Scholar] [CrossRef]
- Suh, J.; You, S.; Choi, S.; Oh, S. Vision-Based Coordinated Localization for Mobile Sensor Networks. IEEE Trans. Autom. Sci. Eng. 2016, 13, 611–620. [Google Scholar] [CrossRef]
- Løfaldli, A.; Birkeland, R. Implementation of a Software Defined Radio Prototype Ground Station for CubeSats. In Proceedings of the ESA Small Satellites Systems and Services Symposium, Valletta, Malta, 30 May–3 June 2016. [Google Scholar] [CrossRef]
- 3GPP. Technical Report. 2016. Available online: www.3gpp.org (accessed on 14 November 2018).
- ETSI EN 302 637-2 V1. Vehicular Communications; Basic Set of Applications; Part 2: Specification of Cooperative Awareness Basic Service; Technical Report; ETSI: Sophia Antipolis, France, 2014; Available online: www.etsi.org (accessed on 14 November 2018).
- ETSI ES 302 637. Vehicular Communications; Basic Set of Applications; Part 3: Specifications of Decentralized Environmental Notification Basic Service; Technical Report; ETSI: Sophia Antipolis, France, 2014; Available online: www.etsi.org (accessed on 14 November 2018).
- EN 50159. Railway Applications. Communication, Signaling and Processing Systems. Safety-Related Communication in Transmission Systems; Technical Report; BSI: London, UK, 2010. [Google Scholar]
- IEC 61784-3. Industrial Communication Networks—Functional Safety Fieldbuses; Technical Report; IEC: Geneva, Switzerland, 2016. [Google Scholar]
- Oncu, S.; van de Wouw, N.; Nijmeijer, H. Cooperative adaptive cruise control: Tradeoffs between control and network specifications. In Proceedings of the 2011 14th International IEEE Conference on Intelligent Transportation Systems (ITSC), Washington, DC, USA, 5–7 October 2011; pp. 2051–2056. [Google Scholar] [CrossRef]
- Xu, L.; Wang, L.Y.; Yin, G.; Zhang, H. Communication Information Structures and Contents for Enhanced Safety of Highway Vehicle Platoons. IEEE Trans. Veh. Technol. 2014, 63, 4206–4220. [Google Scholar] [CrossRef]
- Ge, J.; Orosz, G. Dynamics of connected vehicle systems with delayed acceleration feedback. Transp. Res. Part C Emerg. Technol. 2014, 46, 46–64. [Google Scholar] [CrossRef]
- Santini, S.; Salvi, A.; Valente, A.S.; PescapÃ, A.; Segata, M.; Cigno, R.L. A Consensus-Based Approach for Platooning with Intervehicular Communications and Its Validation in Realistic Scenarios. IEEE Trans. Veh. Technol. 2017, 66, 1985–1999. [Google Scholar] [CrossRef]
- Meinke, K. Learning-Based Testing of Cyber-Physical Systems-of-Systems: A Platooning Study. In Computer Performance Engineering; Reinecke, P., Di Marco, A., Eds.; Springer International Publishing: Cham, Switzerland, 2017; pp. 135–151. [Google Scholar]
- Mongelli, M.; Ferrari, E.M.M.F.A. Performance validation of vehicle platooning via intelligible analytics. IET Cyber-Phys. Syst. Theory Appl. 2018. [Google Scholar] [CrossRef]
- Li, K.; Ni, W.; Tovar, E.; Guizani, M. LCD: Low Latency Command Dissemination for a Platoon of Vehicles. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Trihinas, D.; Pallis, G.; Dikaiakos, M.D. ADMin: Adaptive monitoring dissemination for the Internet of Things. In Proceedings of the IEEE INFOCOM 2017- IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017; pp. 1–9. [Google Scholar] [CrossRef]
- Li, K.; Kurunathan, H.; Severino, R.; Tovar, E. Cooperative Key Generation for Data Dissemination in Cyber-physical Systems. In Proceedings of the 9th ACM/IEEE International Conference on Cyber-Physical Systems, Porto, Portugal, 11–13 April 2018; pp. 331–332. [Google Scholar] [CrossRef]
- Sadi, Y.; Ergen, S.C. Optimal Power Control, Rate Adaptation, and Scheduling for UWB-Based Intravehicular Wireless Sensor Networks. IEEE Trans. Veh. Technol. 2013, 62, 219–234. [Google Scholar] [CrossRef]
- Demir, U.; Ergen, S.C. ARIMA-based time variation model for beneath the chassis UWB channel. EURASIP J. Wirel. Commun. Netw. 2016, 2016, 178. [Google Scholar] [CrossRef]
- Parthasarathy, D.; Whiton, R.; Hagerskans, J.; Gustafsson, T. An in-vehicle wireless sensor network for heavy vehicles. In Proceedings of the 2016 IEEE 21st International Conference on Emerging Technologies and Factory Automation (ETFA), Berlin, Germany, 6–9 September 2016; pp. 1–8. [Google Scholar] [CrossRef]
- Kurunathan, H.; Severino, R.; Koubâa, A.; Tovar, E. Worst-Case Bound Analysis for the Time-Critical MAC behaviors of IEEE 802.15. 4e. In Proceedings of the 13th IEEE International Workshop on Factory Communication Systems Communication in Automation (WFCS 2017), Limassol, Cyprus, 31 May–2 June 2017. [Google Scholar]
- Kurunathan, H.; Severino, R.; Koubâa, A.; Tovar, E. An Efficient Approach to Multisuperframe Tuning for DSME Networks: Poster Abstract. In Proceedings of the 17th ACM/IEEE International Conference on Information Processing in Sensor Networks, Porto, Portugal, 11–13 April 2018; IEEE Press: Piscataway, NJ, USA, 2018; pp. 162–163. [Google Scholar] [CrossRef]
- Mongelli, M.; Aiello, M.; Cambiaso, E.; Papaleo, G. Detection of DoS attacks through Fourier transform and mutual information. In Proceedings of the 2015 IEEE International Conference on Communications (ICC), London, UK, 8–12 June 2015; pp. 7204–7209. [Google Scholar]
- Pomante, L.; Pugliese, M.; Marchesani, S.; Santucci, F. Definition and Development of a Topology-based Cryptographic Scheme for Wireless Sensor Networks. In Sensor Systems and Software; Springer: Cham, Switzerland, 2013. [Google Scholar]
- Agosta, G.; Barenghi, A.; Maggi, M.; Pelosi, G. Design space extension for secure implementation of block ciphers. IET Comput. Dig. Tech. 2014, 8, 256–263. [Google Scholar] [CrossRef]
- Kaloxylos, A. A Survey and an Analysis of Network Slicing in 5G Networks. IEEE Commun. Stand. Mag. 2018, 2, 60–65. [Google Scholar] [CrossRef]
- Project, T.M. Metis. 2012. Available online: https://www.metis2020.com (accessed on 14 November 2018).
- Consortium, M. Scenarios, Requirements and KPIs for 5G Mobile and Wireless System; ICT-317669 METIS; ICT: Trondheim, Norway, 2013. [Google Scholar]
- 5G Infrastructure Public Private Partnership. 5GPPP. 2013. Available online: https://5g-ppp.eu/ (accessed on 14 November 2018).
- ICT318115-CROWD. Connectivity Management for eneRgy Optimised Wireless Dense Networks. 2013. Available online: http://www.ict-crowd.eu/ (accessed on 14 November 2018).
- NGMN 5G Initiative. NGMN 5G White Paper; NGMN Alliance: Frankfurt am Main, Germany, 2015. [Google Scholar]
- View on 5G Architecture. 5GPPP; Technical Report. Available online: https://5g-ppp.eu/ (accessed on 14 November 2018).
- Detailed Specifications of the Terrestrial Radio Interfaces of International Mobile Telecommunications-Advanced. ITU-R M.2012; Technical Report M.2012, ITU-R. 2015. Available online: www.itu.int (accessed on 14 November 2018).
- Access Layer Specification for Intelligent Transport Systems Operating in the 5 GHz Frequency Band; ETSI ES 302 663; Technical Report; ETSI: Sophia Antipolis, France, 2012; Available online: www.etsi.org (accessed on 14 November 2018).
- European Profile Standard for the Physical and Medium Access Control Layer of Intelligent Transport Systems Operating in the 5 GHz Frequency Band; ETSI ES 202 663; Technical Report; ETSI: Sophia Antipolis, France, 2009; Available online: www.etsi.org (accessed on 14 November 2018).
- 5G Automotive Vision. 5GPPP; Technical Report, 5GPPP. 2015. Available online: https://5g-ppp.eu/ (accessed on 14 November 2018).
- Vehicular Communications; GeoNetworking; Part 4: Geographical Addressing and Forwarding for Point-to-Point and Point-to-Multipoint Communications; Sub-Part 1: Media-Independent Functionality; ETSI ES 302 636; Technical Report; ETSI: Sophia Antipolis, France, 2013; Available online: www.etsi.org (accessed on 14 November 2018).
- ETSI ES 302 800. Vehicular Communications; Basic Set of Applications; Local Dynamic Map (LDM); Technical Report; ETSI: Sophia Antipolis, France, 2014; Available online: www.etsi.org (accessed on 14 November 2018).
- ETSI ES 102 637. Vehicular Communications; Basic Set of Applications; Part 1: Functional Requirements; Technical Report; ETSI: Sophia Antipolis, France, 2009; Available online: www.etsi.org (accessed on 14 November 2018).
- Puleri, M.; Sabella, R.; Osseiran, A. Cloud Robotics: 5G Paves the Way for Mass-Market Automation. Technical Report, Ericsson Technology Review. 2016. Available online: https://www.ericsson.com/en (accessed on 14 November 2018).
- 3GPP TS 22.281. Mission Critical Video Services over LTE; Technical Report; Rel. 14, v.14.3.0; 3GPP: Sophia Antipolis, France, 2017.
- 3GPP TS 22.282. Mission Critical Video Services over LTE; Technical Report; Rel. 14, v.14.3.0; 3GPP: Sophia Antipolis, France, 2017.
- Soldani, D.; Fadini, F.; Rasanen, H.; Duran, J.; Niemela, T.; Chandramouli, D.; Hoglund, T.; Doppler, K.; Himanen, T.; Laiho, J.; et al. 5G Mobile Systems for Healthcare. In Proceedings of the IEEE VTC Spring, Sydney, NSW, Australia, 4–7 June 2017. [Google Scholar]
- Mission Critical Services in 3GPP. Available online: http://www.3gpp.org/news-events/3gpp-news/1875-mc_services (accessed on 14 November 2018).
- Levander, O. Autonomous ships on the high seas. IEEE Spectr. 2017, 54, 26–31. [Google Scholar] [CrossRef]
- TR38.811. Study on New Radio (NR) to Support non Terrestrial Networks; Technical Report; Rel. 15, v0.2.1; 3GPP: Sophia Antipolis, France, 2017.
- Höyhtyä, M.; Huusko, J.; Kiviranta, M.; Solberg, K.; Rokka, J. Connectivity for autonomous ships: Architecture, use cases, and research challenges. In Proceedings of the 2017 International Conference on Information and Communication Technology Convergence (ICTC), Jeju Island, Korea, 18–20 October 2017; pp. 345–350. [Google Scholar] [CrossRef]
- TR22.885. Study on LTE Support for Vehicle to Everything (V2X) Services; Technical Report; v14.0; 3GPP: Sophia Antipolis, France, 2015.
- TR 22.886. Study on Enhancement of 3GPP Support for 5G V2X Services; Technical Report; v15.1.0; 3GPP: Sophia Antipolis, France, 2017.
- Campolo, C.; Molinaro, A.; Iera, A.; Meninchella, F. 5G Network Slicing for vehicle-to-everything service. IEEE Wirel. Commun. 2017, 24, 38–45. [Google Scholar] [CrossRef]
- Shah, S.A.A.; Ahmed, E.; Imran, M.; Zeadally, S. 5G for Vehicular Communications. IEEE Commun. Mag. 2018, 56, 111–117. [Google Scholar] [CrossRef]
- Liu, J.; Wan, J.; Jia, D.B.Z.; Li, D.; Hsu, C.H.; Chen, H. High-Efficiency Urban Traffic Management in Context-Aware Computing and 5G Communication. IEEE Commun. Mag. 2017, 55, 34–40. [Google Scholar] [CrossRef]

| Use Case | 4G | 5G |
|---|---|---|
| Heathcare | Energy efficiency issue on radio interfaces | Femtocell solution for indoor comms Support scalability |
| Maritime | Radio signal degradation | Satellite transmission but latency concerns |
| Vehicle control loss warning | ProSe to be upgraded | natively supported |
| Vehicles and roadside units interaction | ProSe to be upgraded | natively supported |
| V2I cooperation for traffic management | latency concerns | natively supported |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Balador, A.; Kouba, A.; Cassioli, D.; Foukalas, F.; Severino, R.; Stepanova, D.; Agosta, G.; Xie, J.; Pomante, L.; Mongelli, M.; et al. Wireless Communication Technologies for Safe Cooperative Cyber Physical Systems. Sensors 2018, 18, 4075. https://doi.org/10.3390/s18114075
Balador A, Kouba A, Cassioli D, Foukalas F, Severino R, Stepanova D, Agosta G, Xie J, Pomante L, Mongelli M, et al. Wireless Communication Technologies for Safe Cooperative Cyber Physical Systems. Sensors. 2018; 18(11):4075. https://doi.org/10.3390/s18114075
Chicago/Turabian StyleBalador, Ali, Anis Kouba, Dajana Cassioli, Fotis Foukalas, Ricardo Severino, Daria Stepanova, Giovanni Agosta, Jing Xie, Luigi Pomante, Maurizio Mongelli, and et al. 2018. "Wireless Communication Technologies for Safe Cooperative Cyber Physical Systems" Sensors 18, no. 11: 4075. https://doi.org/10.3390/s18114075
APA StyleBalador, A., Kouba, A., Cassioli, D., Foukalas, F., Severino, R., Stepanova, D., Agosta, G., Xie, J., Pomante, L., Mongelli, M., Pierini, P., Petersen, S., & Sukuvaara, T. (2018). Wireless Communication Technologies for Safe Cooperative Cyber Physical Systems. Sensors, 18(11), 4075. https://doi.org/10.3390/s18114075









