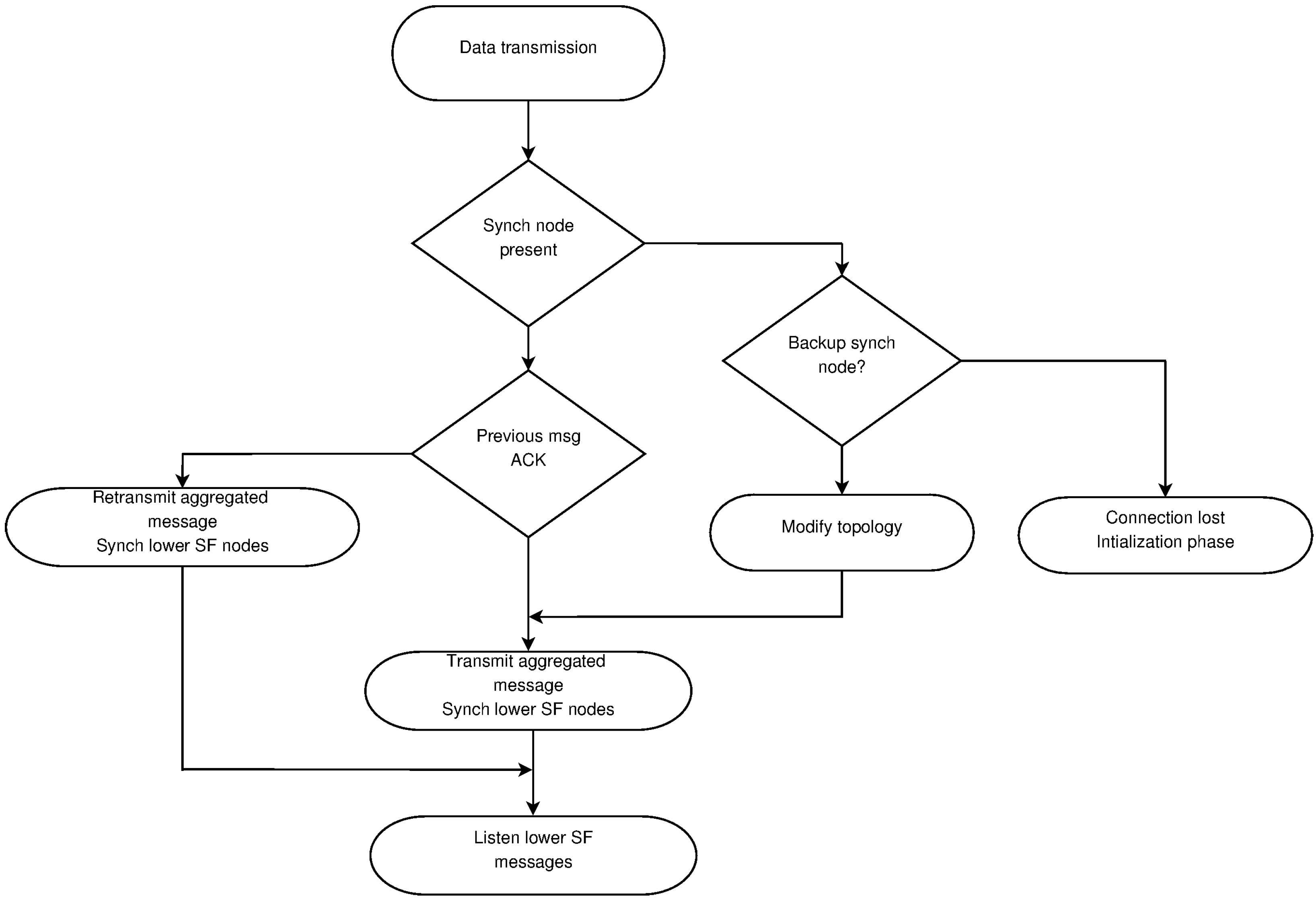
3.2.1. Clock Synchronization
The clocks synchronization is of major importance in a TDMA MAC protocol [
20,
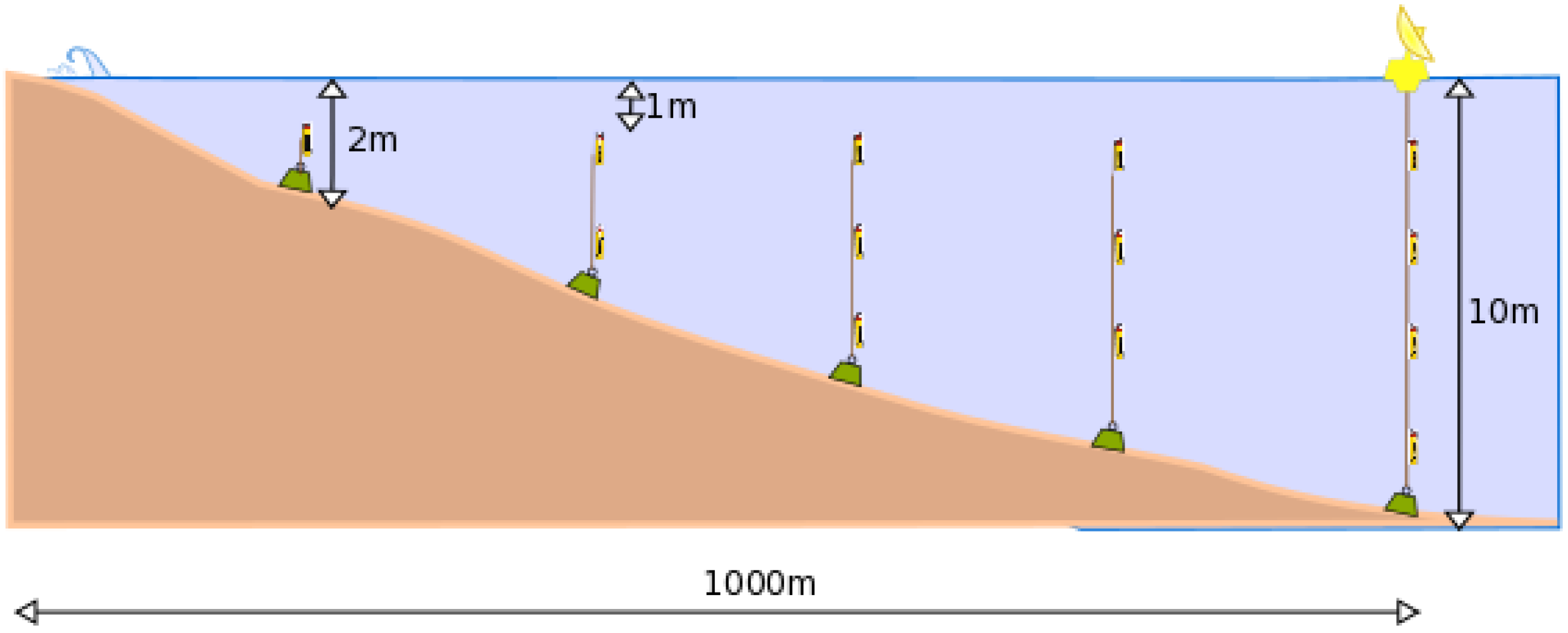
23]. Although the nodes count with a real-time clock (RTC), these usually have drifts; therefore, a synchronization process is necessary. Underwater acoustic signals propagate at an average of 1.5 km/s. With this speed, nodes within transmission range (but distant enough) receive the signals at significantly different times. Moreover, usually the time slot is shorter than the propagation delay; thus, the same message may be listened to by one node at a certain instant and later by another one.
Table 1 presents the propagation delay for different distances. If the transmission is set at 9600 b/s, which is a standard transmission rate for acoustic underwater transmissions, the time required for transmitting 256 bytes is 0.213 s. Therefore, nodes at more than 500 m receive the message after it has been completely sent at the source node, and a collision may take place without being noticed by the involved nodes.
The synchronization protocol is hierarchical. First, the nodes within the transmission range of the SB are synchronized. Once all of them are synchronized, they begin synchronizing nodes within their transmission range, and so on. In what follows, a detailed explanation is provided for the set of nodes in direct contact with the SB. The process is repeated once the synchronization nodes for the different sub-frames are selected.
In the case of underwater acoustic signals, the transmission range is not easy to determine, as it depends on the power of the transmitter, the sensibility of the receiver, the carrier frequency, the signal to noise ratio and several other factors, like water temperature, salinity, the depth of the sensors and currents. In fact, a node may discover nodes in its transmission range, but not the actual size of it. However, for the purpose of advancing in the analysis, we consider that in the design stage, it is possible to compute the communication range based on standard parameters of the zone in which the sensor network will operate.
At startup time (initialization phase), the network uses a carrier sense multiple access (CSMA) protocol for the clock synchronization and slot selection. As more than one node may try to use the channel simultaneously, there may be collisions. Nodes are not aware of the presence of their neighbors and the SB (
synchronization node); thus, they do not know when the synchronization message will arrive or the amount of answers it will receive. The SB (
synchronization node) sends a
synch message. This has an identification field (ID) for the node and the time stamp obtained from the UTC system. Nodes within transmission range of the SB (
synchronization node) would receive the
synch message at different instants depending on the delay, which is basically a function of the distance to the SB (
synchronization node), as shown in
Table 1. After the node receives the
synch message, it responds with an
asynch message. This message has an ID field for the node, the time at which the
synch message was received and the time at which the
asynch message was finally transmitted. Before transmitting, the node will sense the channel to detect activity; if it listens to some other node answering, it will wait and run a back-off algorithm. As the propagation delay is important, overlapped transmissions may be detected by the transmitting nodes or by the SB (
synchronization node). If the node finds the channel free and transmits, the message may suffer a collision later without being noticed by the node. For this reason, all messages should be acknowledged by the destination node, in this case the SB (
synchronization node). If no acknowledgment is received, the node assumes its message has been corrupted for some reason and the most probable one is a collision. Then, a back-off algorithm is used for retransmitting the message.
The back-off algorithm is similar to the basic ones used in CSMA networks. After the first collision is detected, the nodes involved choose successively and randomly a delay that varies from zero to 16 slots. In the first round, they choose between zero and one, in the second between zero and three slots. In the third round, they choose a delay between zero and seven slots and, finally, between zero and 15. These numbers may change if the nodes’ density in a particular area is high.
During the synchronization phase, the SB (
synchronization node) is not aware of the amount of nodes listening and the transmission delay to reach them. It is for this that the SB (
synchronization node) has to wait for a period of time large enough to allow the transmission of the nodes, as they may be waiting for the channel to be free. Given the maximum transmission range, the SB (
synchronization node) waits for a time equivalent to
maximum propagation delays, where
c is the expected number of nodes in direct contact with the SB (
synchronization node). The duration of this period is a parameter that can be enlarged or reduced according to the previous knowledge of the network topology. For example, assuming a maximum transmission range of 500 m and three nodes in direct contact, the waiting time will be 3.33 s according to
Table 1. After this period, the SB (
synchronization node) sends a new
synch message. This second message has the ID, time stamp and the IDs of successfully synchronized nodes and the adjusted time for each one. A node that has answered to the first
synch message, but is not acknowledge in the second with the adjusted time, is not synchronized and should send again the
asynch message.
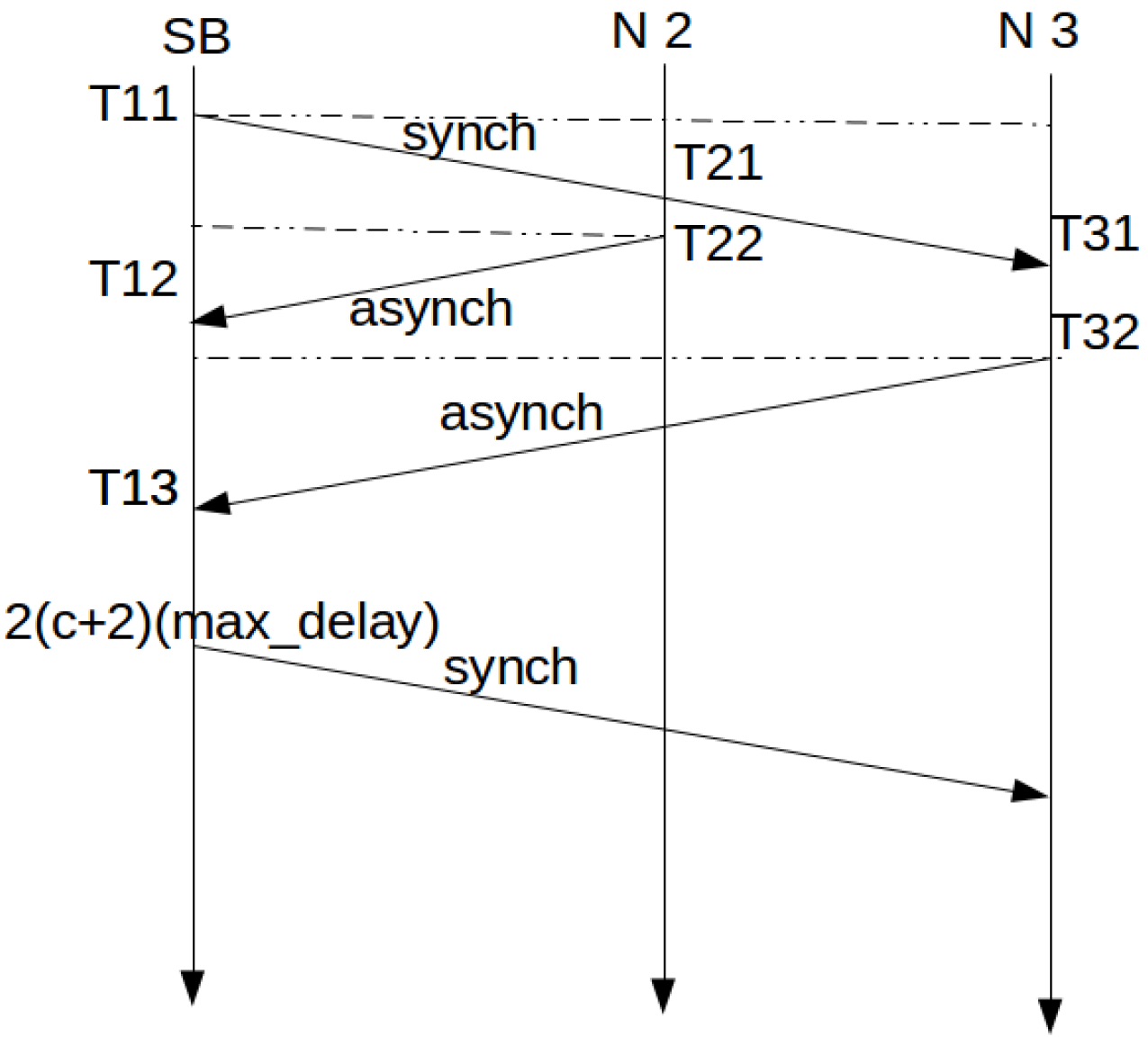
Figure 1 shows the message exchange and time evolution for the process when no collisions are produced.
In
Figure 1, when Node 2 receives the
synch message from the SB, it time stamps its own time as
. After that, in
, it is able to send the
asynch message to the SB. Node 3 is further away and repeats the actions of Node 2. At
, the SB receives the
asynch message from Node 2 and time stamps its own time. The
asynch message contains
,
and
. With this information, the synchronization can be performed at the SB.
The required correction is then obtained from:
This protocol is similar to the one proposed for time synchronization in the Internet, Network Time Protocol (NTP, RFC 5905) [
24].
The described process follows a top-down approach from the SB towards the end nodes. If a node has two or more parents, it has an equal number of possible synchronization sources. In this case, the node with the lower transmission delay is chosen as the synchronization node. In the case that two or more nodes have equal delay, the node listened first is selected.
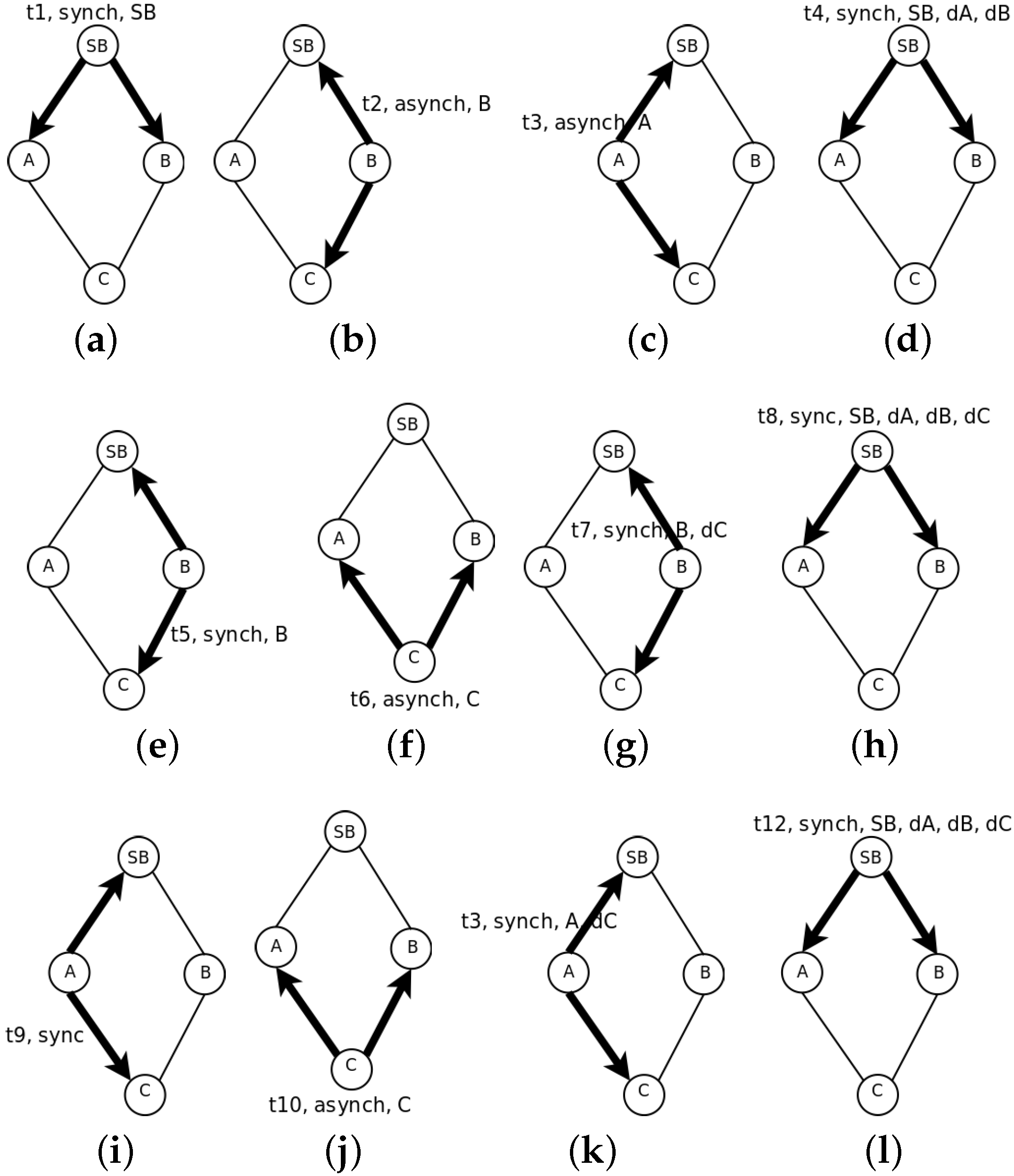
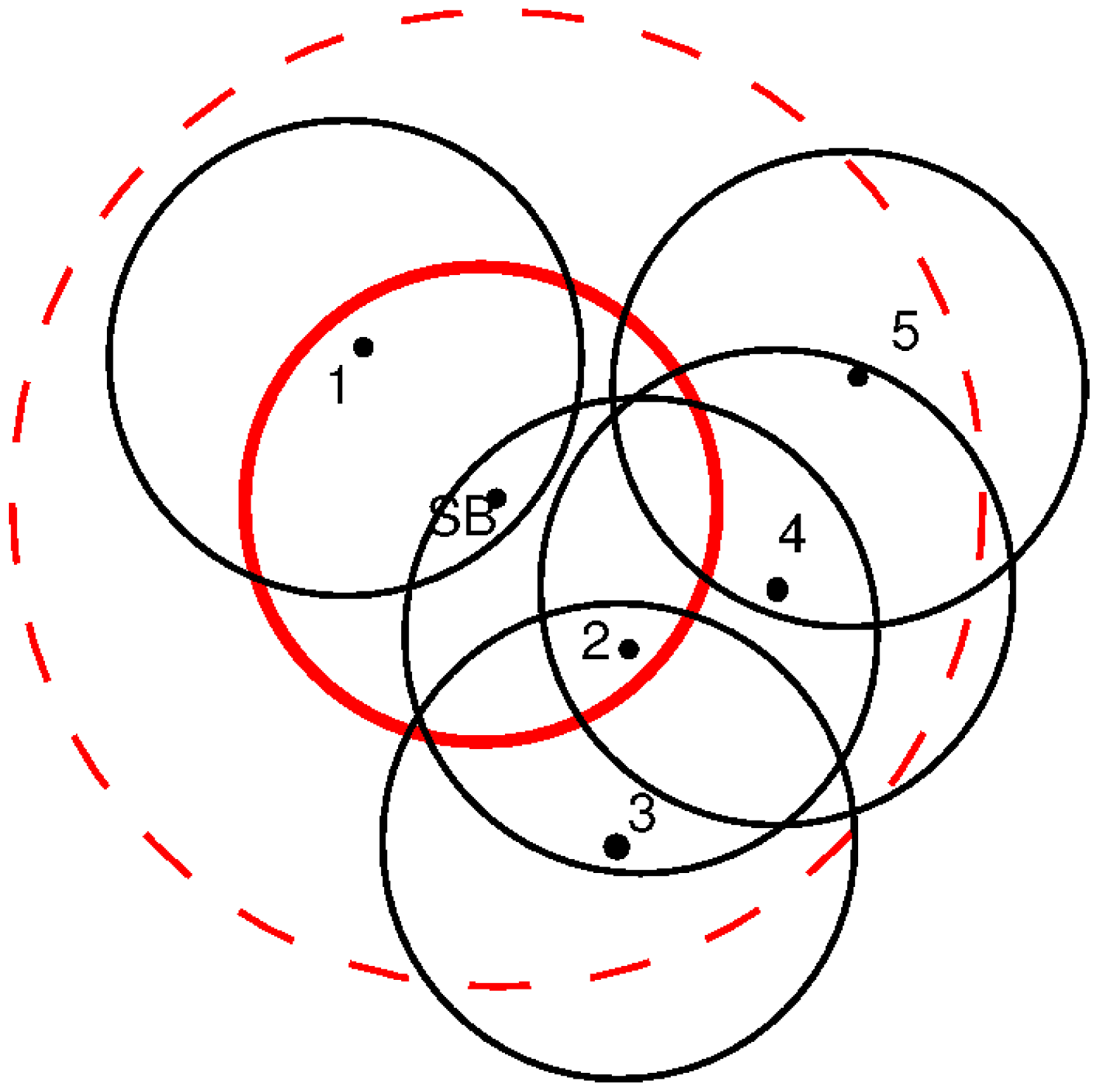
Figure 2 shows the synchronization process. First, the SB sends a
synch message (
Figure 2a). Both Nodes A and B listen to it. They are not aware of the presence of each other; therefore, they answer with the
asynch message following the protocol described before. Let us suppose there is no collision and that Nodes B and A answer one after the other (
Figure 2b,c). The SB recognizes both with a new
synch message indicating the time correction and the computed distance to the SB (
Figure 2d). With this message, both Nodes A and B learn about the presence of each other. As they both know the delay to the SB and this is the parameter used to order the synchronization process, Node B sends first a
synch message (
Figure 2e), and Node C recognizes it with an
asynch (
Figure 2f). Then, Node B sends a new
synch message with the time correction for Node C and its delay to Node B (
Figure 2g). The SB receives this message too and sends a new
synch message acknowledging the presence of C (
Figure 2h). Node A learns about Node C first by overhearing the exchange with Node B and after that, by the
synch message from the SB. Now, it is time for Node A to send a
synch message (
Figure 2i). Node C listens to it and detects that A has less delay than B; therefore, it changes its synchronization node and answers with an
asynch message (
Figure 2j). This message is received by Node B, which learns the change of C from B to A. This latter node recognizes it with a new
synch message indicating the time correction and its delay to A (
Figure 2k). This message is also received by the SB that updates its tree structure. It sends the last
synch message in which it indicates the time correction for each node and the delays to the SB (
Figure 2l). After this, the slot selection process may proceed.
The synchronization process is used by overhearing nodes in the network to determine the set of neighbor nodes that may help during the slot selection process. Even if nodes are not within transmission range, they may discover their presence by the following
synch messages. The synchronization process is similar to the leader election process [
25]. For each sub-frame, only one node acts as the synchronization source. The set of synchronization nodes are saved in
. The set of nodes synchronized by
is notated
; they are ordered by increasing transmission delay to
. If any
listens to more than one synchronization node, as shown in
Figure 2, only one of them is selected, and the rest are saved as back up. In the
asynch message, the node indicates with which node it is synchronized, and this information is passed to the upper layers up to the SB. The set of shared nodes that may be synchronized by more than one node is notated
. The nodes with this condition indicate the presence of all possible synchronization sources to the upper layer. This information is used later in the slot selection process, as explained in
Section 3.2.2. The information is confirmed in the following
synch messages.
Once the synchronization nodes have been selected, the information flow from the SB to the leafs and from the leafs to the SB is fixed, and it will last until a new initialization process has begun.
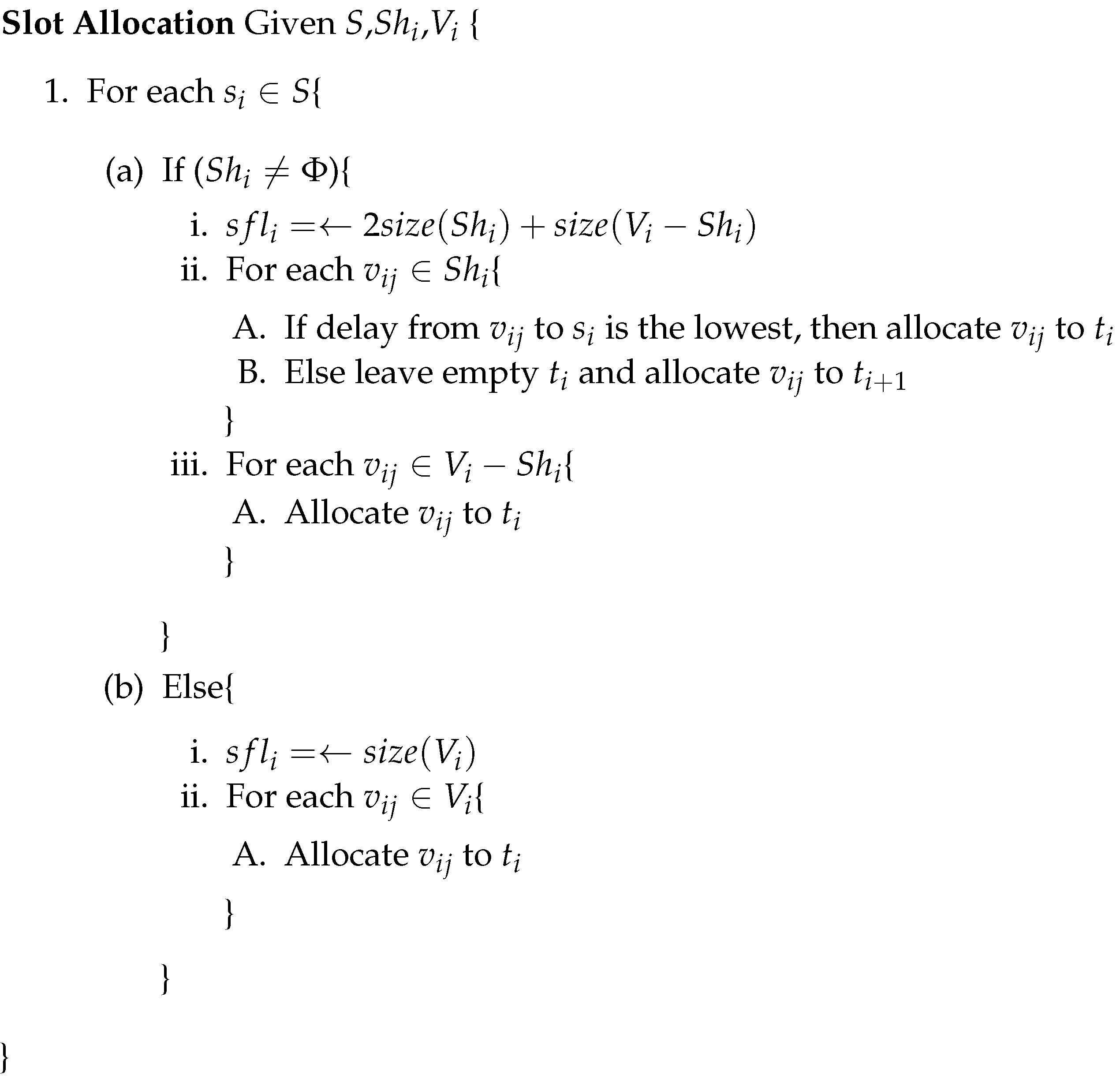
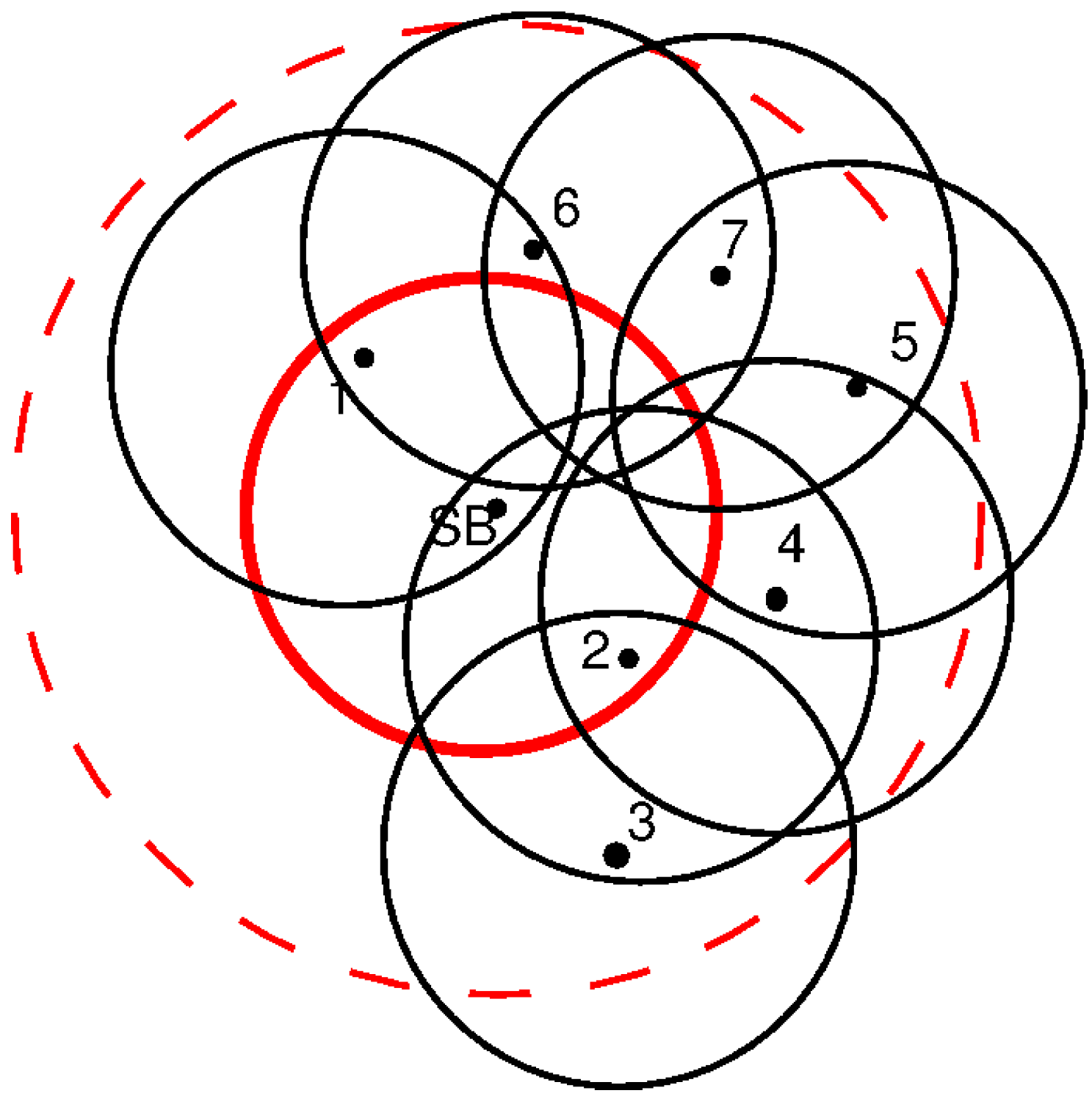
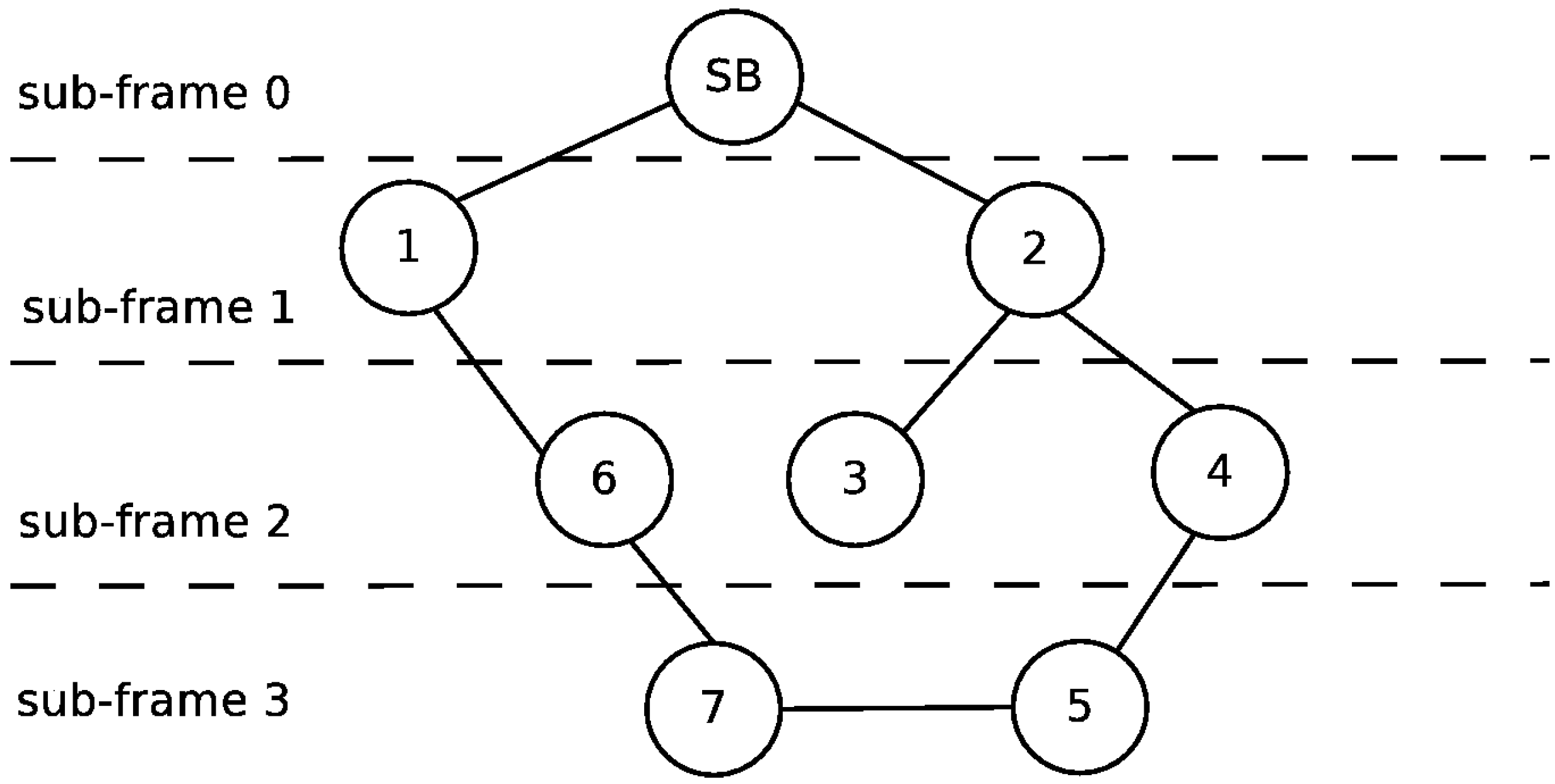
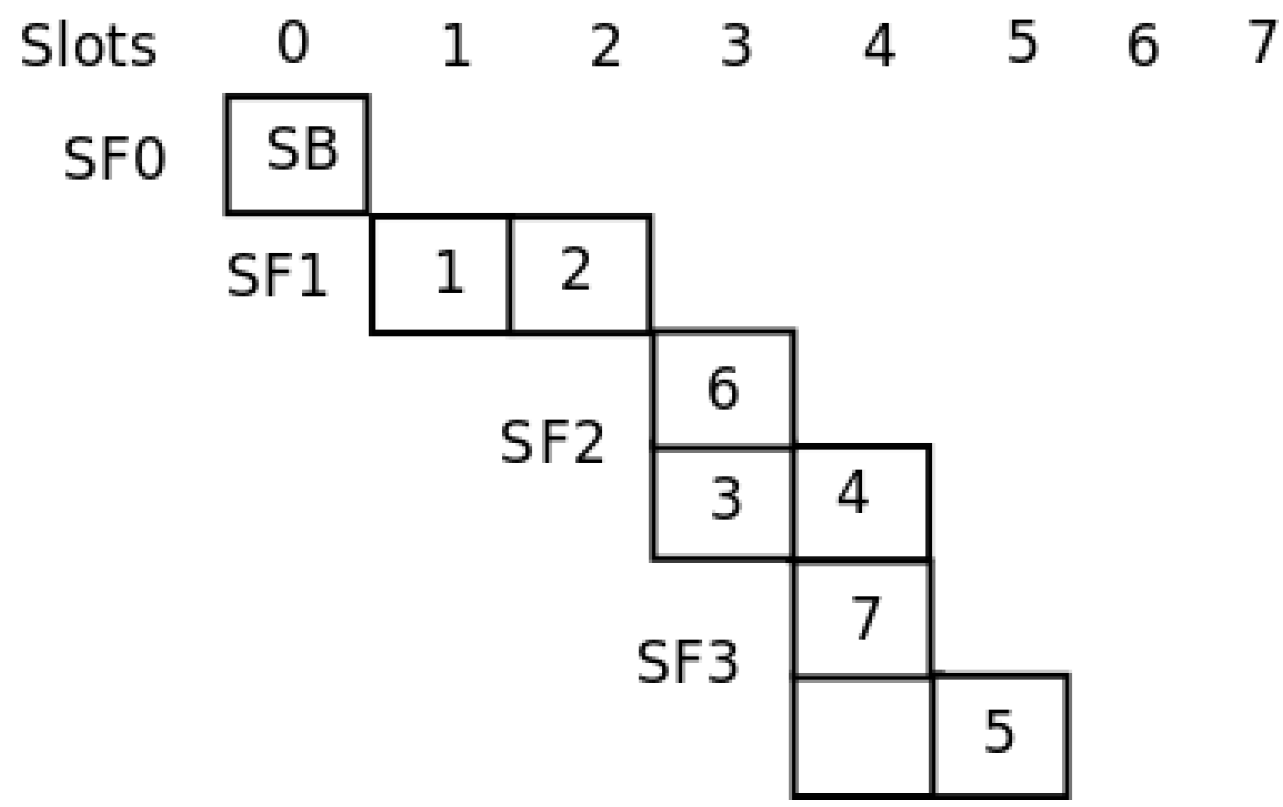
3.2.2. Slot Allocation
Once the nodes in the network are synchronized, the slot selection process can begin. This phase is again performed in a hierarchical way, beginning with the SB. The synchronization nodes are already selected for each sub-frame. The length of each sub-frame and the slot in which each node transmits should be defined. As the synchronization nodes already know which nodes are within their domain, they are able to setup the sub-frame length. With this information, they are able to allocate the slots in the following sub-frame. Messages sent by synchronization nodes are listened to both by downstream and upstream nodes; therefore, the network topology and sub-frames structure is propagated in both directions during the initialization phase.
We need to re-define the concept of simultaneous transmission. Two nodes transmit simultaneously if their messages produce a collision at some other node listening to both. To prevent this, the distance to the synchronizing node, or transmission delay already measured during the synchronization phase, should be used for ordering the slot allocation. The first slot is for the closer node and the last one for the one further away. In the case of
Figure 2, Nodes B and A would use the first and second slots, respectively. Although this allocation order prevents the hidden station problem while transmitting messages from the nodes in sub-frame
i towards the synchronizing node in sub-frame
, there may be collisions between nodes in the same sub-frame, but with different synchronizing nodes when a node (like C) uses more than one node for the synchronization. In
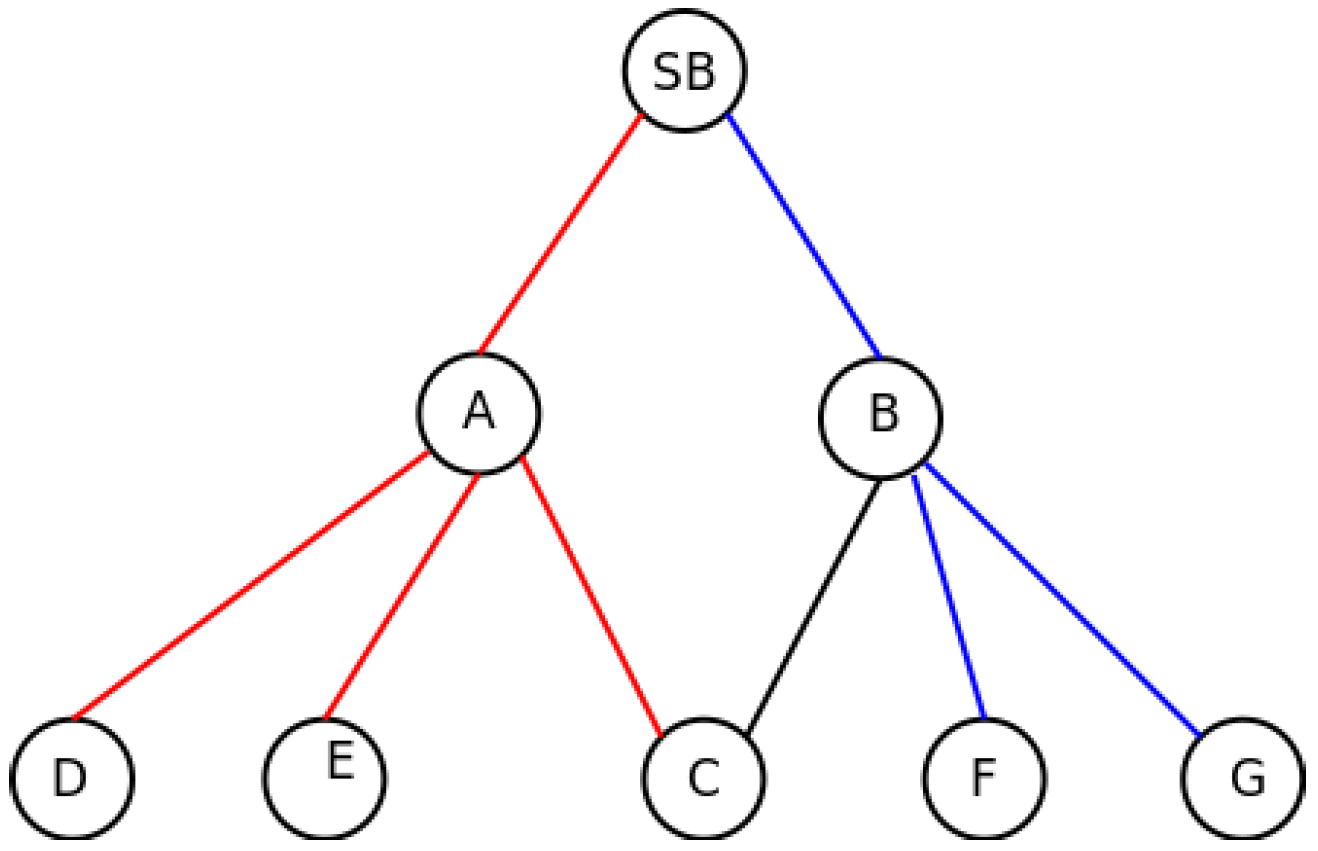
Figure 3, the previous example is extended. In red, we mark a synchronization branch and in blue, the other. In this case, although Node C is synchronized by Node A and therefore the slot allocation is decided by Node A, the possible hidden station problem should be considered in Node B, as Nodes F or G may transmit simultaneously with C.
The described situation should be addressed by Nodes A and B. Both nodes know that C is within transmission range of each other, so they have to share the slot allocated to C in such a way that no collisions are produced. In these cases, the slot allocation criteria are changed. For each sub-frame level, a set of slots is reserved for those nodes that are connected with more than one synchronizing node (shared nodes). The amount of slots reserved for them is two times the number of nodes in that situation. The rest of the nodes are allocated after these reserved slots following the delay criteria. Within the reserved slots, each synchronizing node allocates the possible conflicting nodes. This allocation repeats the previous criteria. The first node in the previous sub-frame allocates first the possible conflicting nodes, leaving empty the rest of the reserved slots. The procedure is repeated for the rest of the synchronizing nodes. If a collision is detected after this allocation process, the nodes detecting it inform the previous layer of the situation, and the conflicting nodes are rearranged.
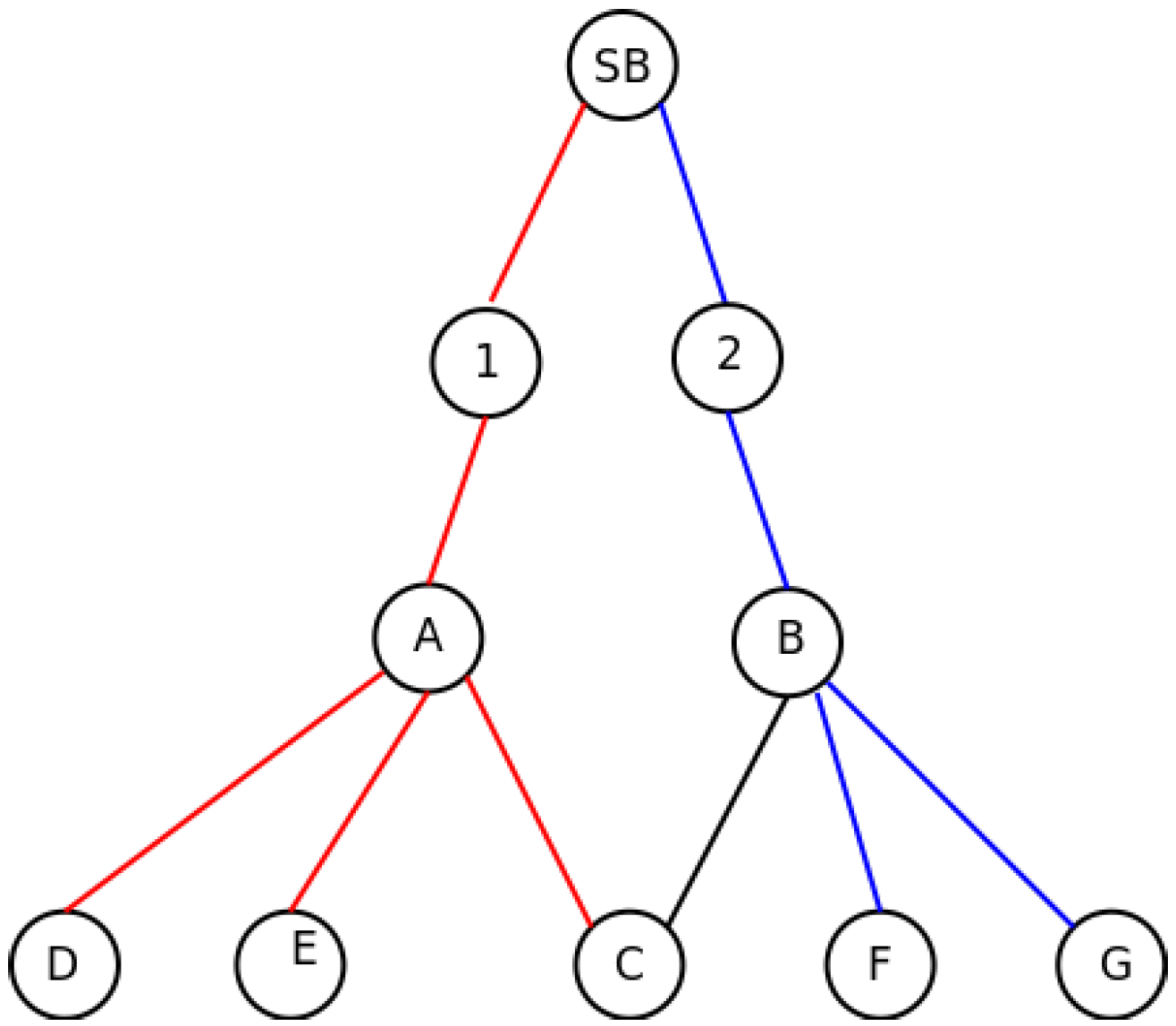
In the case described in
Figure 3, the synchronization nodes share the same sub-frame, as both of them are synchronized by the same node. In
Figure 4, the situation is repeated, but in this case, both possible synchronization nodes are in different sub-frames, as they are not synchronized by the SB, but by Nodes 1 and 2, respectively. In this case, as explained in
Section 3.2.1, Nodes A and B are aware of the presence of each other, because C informs about the presence of both of them in the
asynch message. Since they are not under the same synchronization node, they know that they are in different sub-frames, as well. This information is passed to Nodes 1 and 2, so they should include as many empty slots as shared nodes exist in the subsequent sub-frames to avoid the hidden station problem. In the example, Node 1 will generate a two-slot sub-frame for Node A, and Node 2 will do the same with Node B. In this way, A and B should use different slots to prevent the collision in Node C.
After several iterations, the allocation should converge to a stable solution, as there are more available slots than nodes to use them. The number of free slots in the sub-frame helps with the initialization process, but it introduces more latency in the network for data transmission.
A sub-frame synchronized by node
is notated
, where subindex
j indicates the hop number and
i the synchronizing node, and
indicates the amount of slots within the sub-frame.
Figure 5 presents the algorithm for the slot selection process. At this point, we can assure that the exposed station problem is not present in this configuration, because nodes within the transmission range of each other are allocated to different slots.
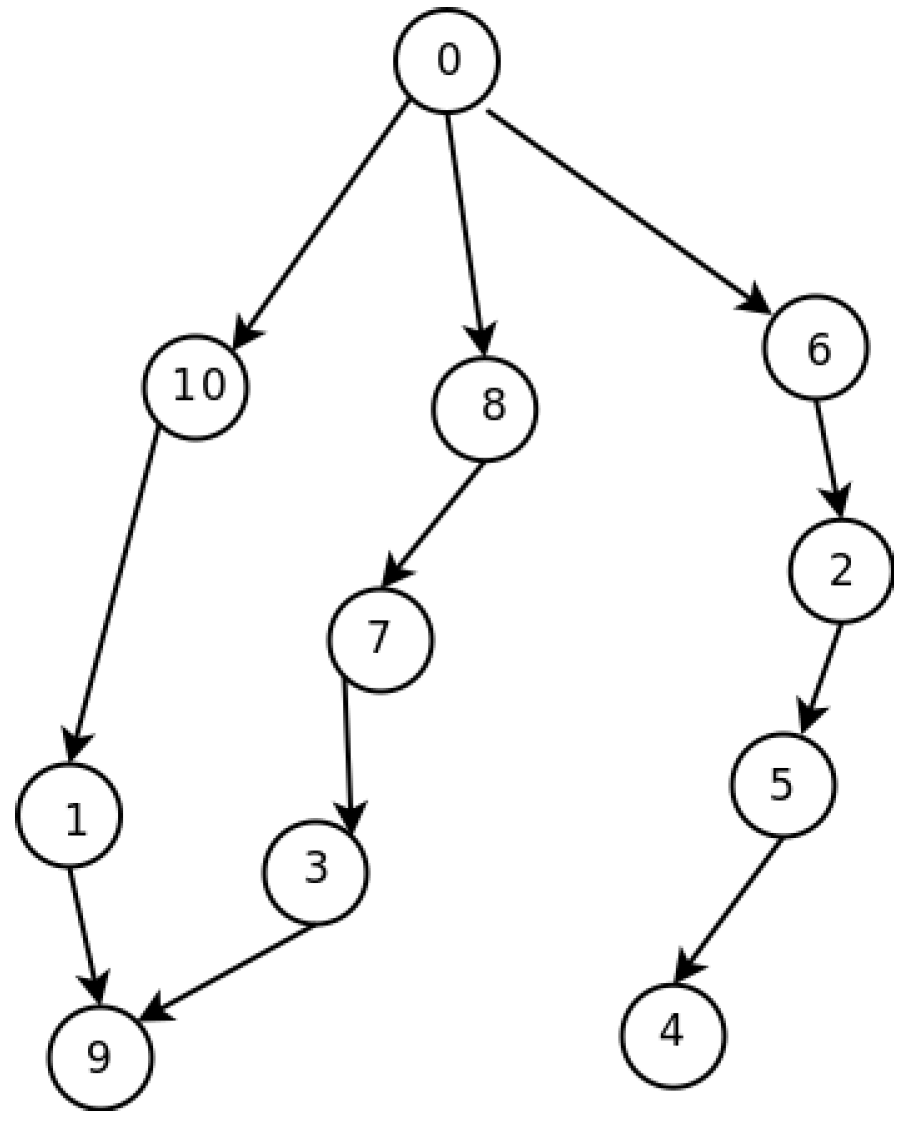
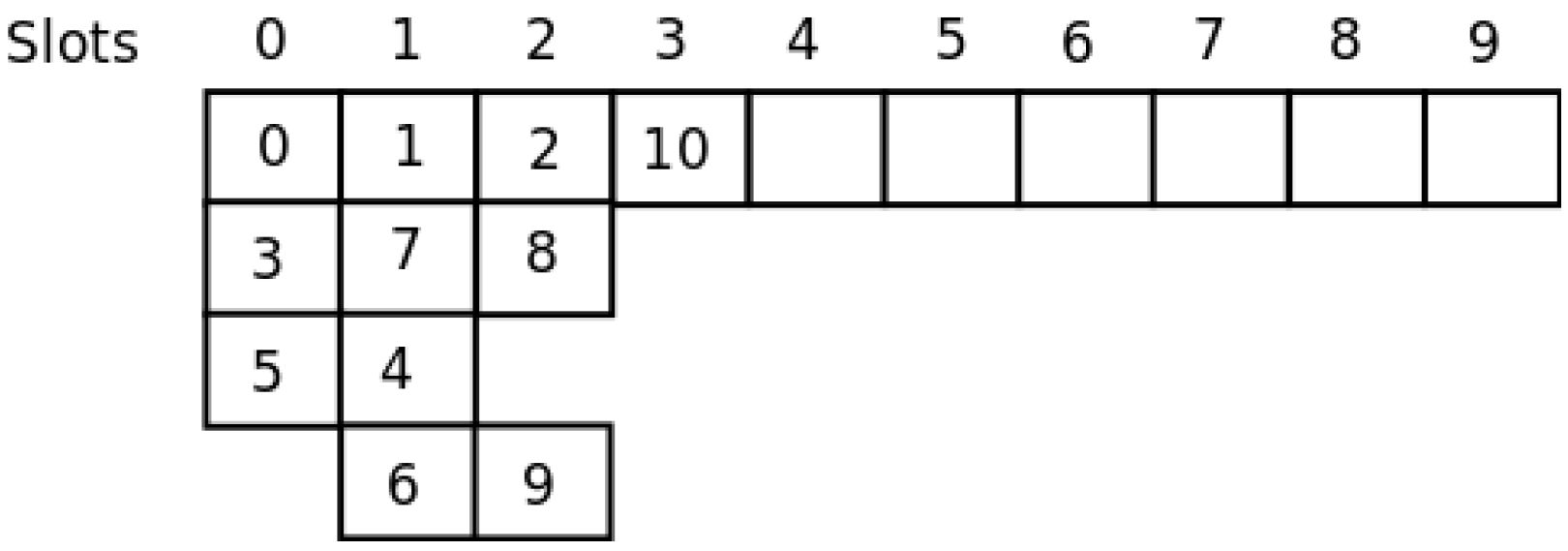
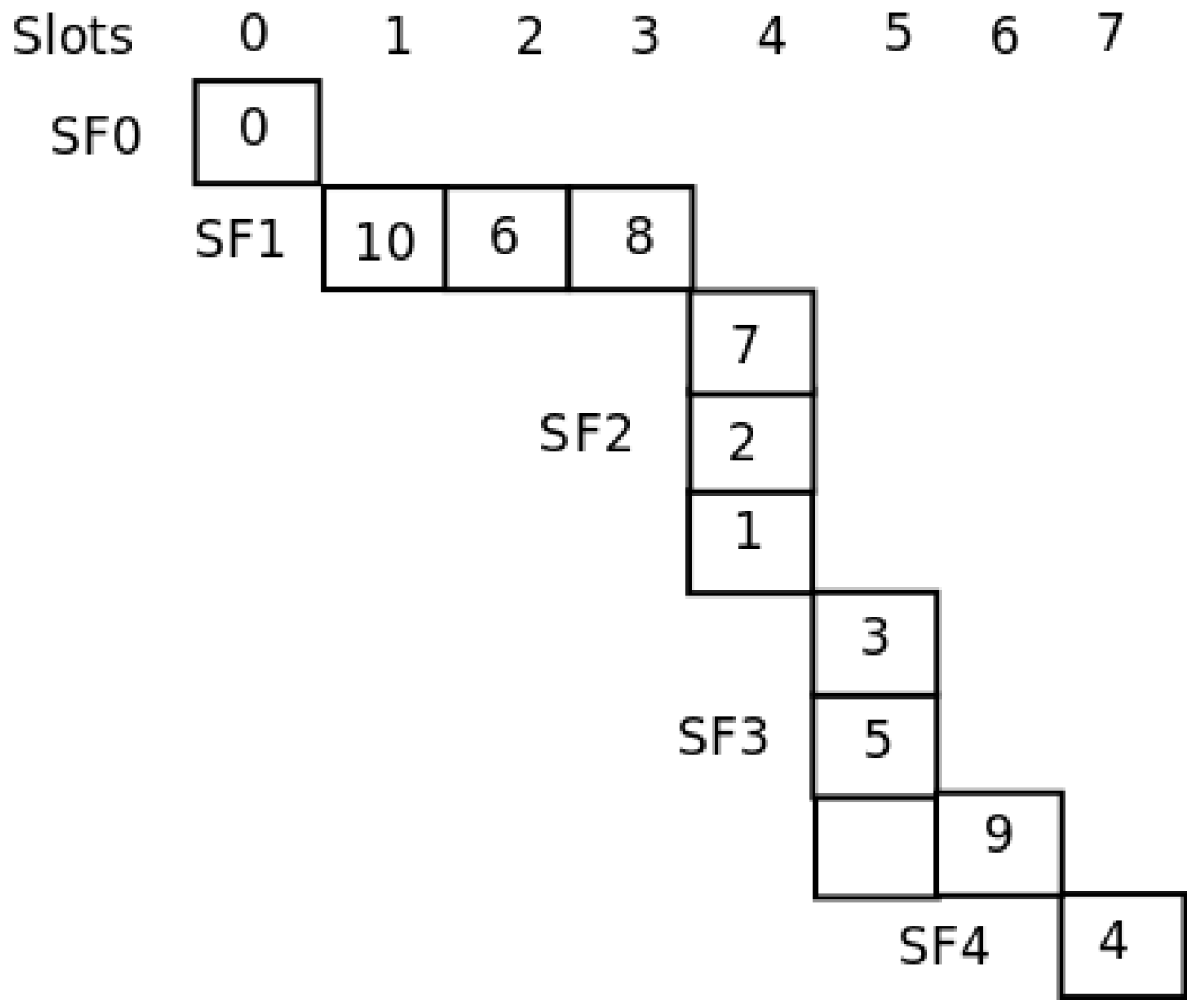
For the network shown in
Figure 6, in [
21], the authors show the way in which their template allocates the nodes to slots in a global optimum way.
Figure 7 shows the assignment. As can be seen, with only four slots, all nodes are able to send their messages to the sink. With our distributed method, the SO-UWSN allocates the slots according to
Figure 8. It requires some more slots, incrementing the latency. However, the method is distributed, and no previous knowledge of the nodes’ deployment is necessary. As the protocol proposes also a periodic re-initialization of the network, dead nodes can be removed from the graph and eventually new ones incorporated.