HEAD Access Control Metamodel: Distinct Design, Advanced Features, and New Opportunities
Abstract
1. Introduction
- Unify the heterogeneous concepts of policy models.
- A new generic metamodel that is able to include the heterogeneity of the existing models and the proposed metamodels.
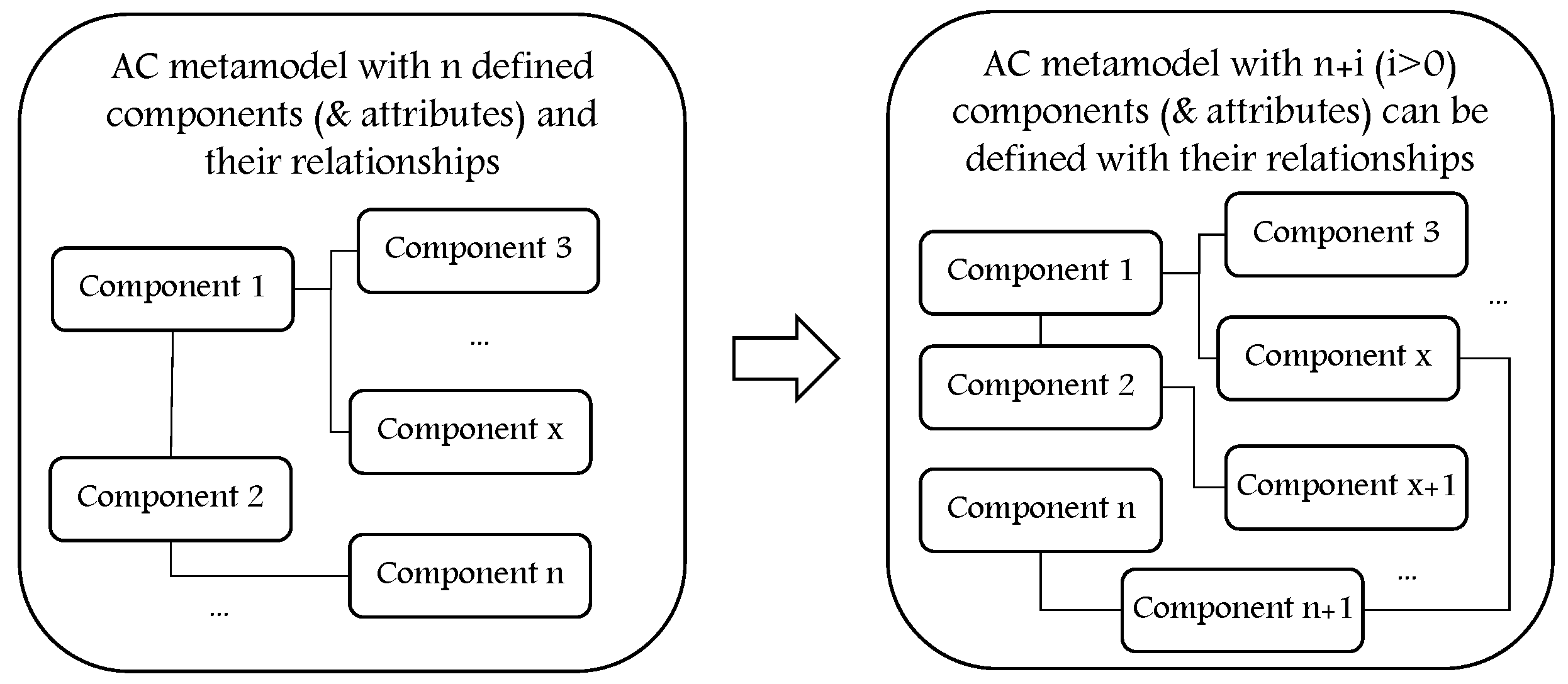
- Dynamic with the ability to create any needed component/attribute and the relationships between them.
- Extensible metamodel where any derived AC model can be extended and upgraded.
- Unlimited levels of components hierarchy.
- Allow instantiating non-existing AC models.
- Provides a complete plan for a distinct AC framework starting from the metamodel development phase and reaching to the policy enforcement phase.
- Opens new opportunities to develop and enhance the necessary services to answer the challenging AC requirements of today’s computing environments based on distinct design and advanced AC metamodel.
- Assists developers and security experts to include unified and generic components in designing secure ISs that conform to the organizational AC security policies.
2. Access Control Challenges within Dynamic and Heterogeneous Environments
- Access control serves as a protective shield for the existing resources in organizations, industries, homes, etc., against security risks that accompany transparency, shareability, and interoperability while answering users’ access requests within distributed and heterogeneous computing environments (e.g., IoT environments) where data is generated dynamically and on a real-time basis.
- Access control is highly essential to ensure secure communications in open, dynamic, and heterogeneous environments, especially with the existence of several contexts (network type, time, location, machine characteristics, etc.). For example, to provide an access decision, several or multi-level contexts must be considered. The context itself is a challenge since it could be defined, expressed, and interpreted in different ways according to the application domain, the needed objectives, and the existing techniques.
- Access control mechanism should be flexible and controllable enough to deal with various situations that confront users while requesting access to different types of resources, for example, rapid progressions, unexpected events, system failures, highly dynamic environments that need very quick and controlled response, various hierarchical organizational structures, the different contexts, dynamism of IoT devices, huge number of devices, etc.
- With the large adoption of telework, especially with the COVID-19 pandemic, employees can work anytime, anywhere, and sometimes using their own personal devices. With this fact, security and AC issues have been raised, especially that AC mechanisms should be adapted to users’ context, their profiles, their devices, the existing conditions, and many other parameters to improve system usability. With this fact, AC needs to be dynamically managed to minimize human intervention.
- The heterogeneity of implemented AC models in heterogeneous structures.
- Deciding upon the most relevant AC model(s) to implement in an organization that conform to its AC rules based on the type and sensitivity of resources they have.
- The necessity to enforce persistent AC policies with the current generation of dynamic and heterogeneous structures where information flows from the clouds and/or servers to everywhere (companies, hotels, homes, cars, etc.) without traditional borders.
- The possible need for several AC solutions within the same organization (or industry sector) where various technologies (e.g., local network, IoT, and cloud) may need to work in concert to fulfill the needed requirements of AC.
- The importance of upgrading AC policies and enforcing them in accordance with technology upgrades and due to dynamically changing conditions.
3. Access Control Models
3.1. The Background
3.2. The Development Stages
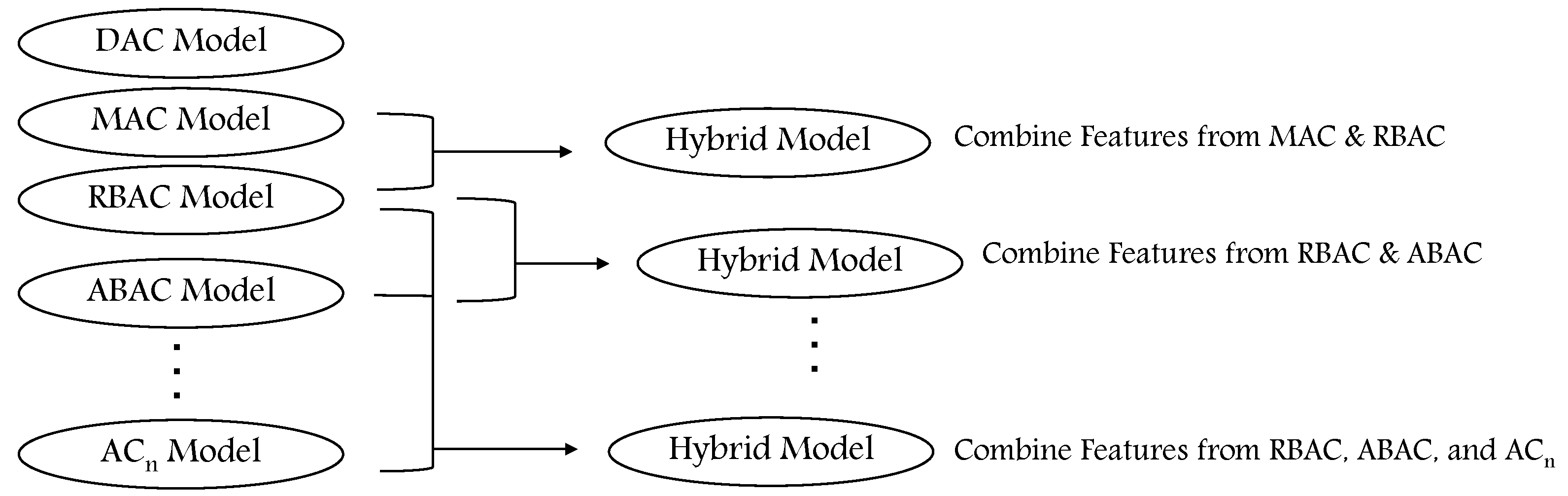
3.2.1. Combining AC Models
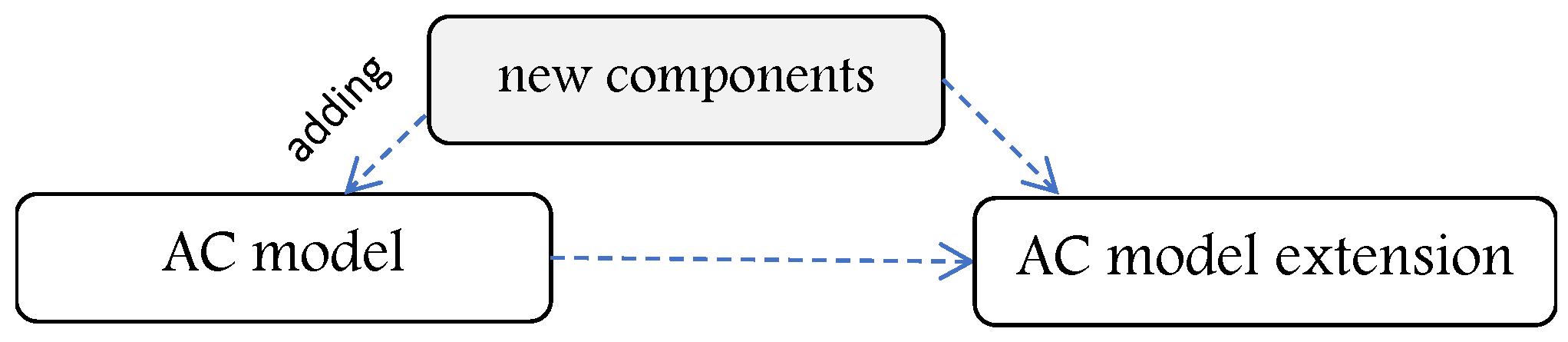
3.2.2. Extending AC Models
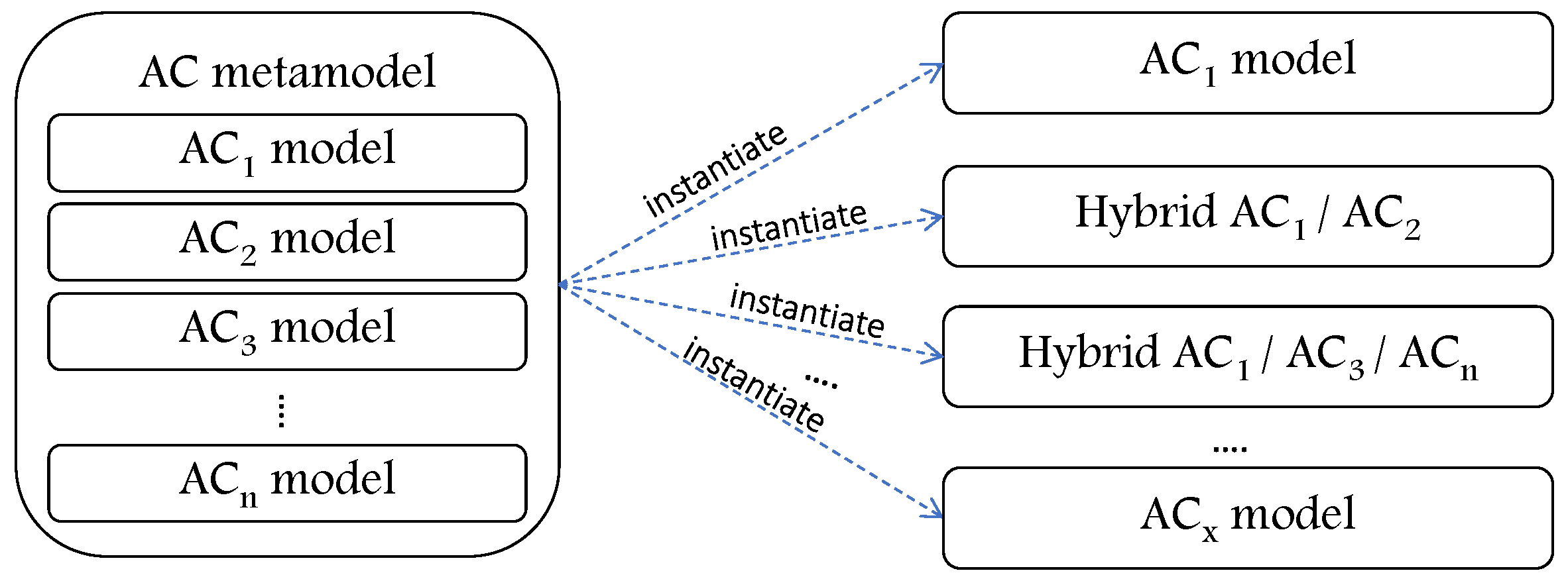
3.2.3. Abstracting AC Models
3.2.4. Access Control Metamodels
4. Issues and Limitations of the Existing AC Metamodels
4.1. Generality
4.2. Dynamism
4.3. Extensibility
4.4. Hierarchy of Components
4.5. Collaboration and Interoperability
4.6. Migration
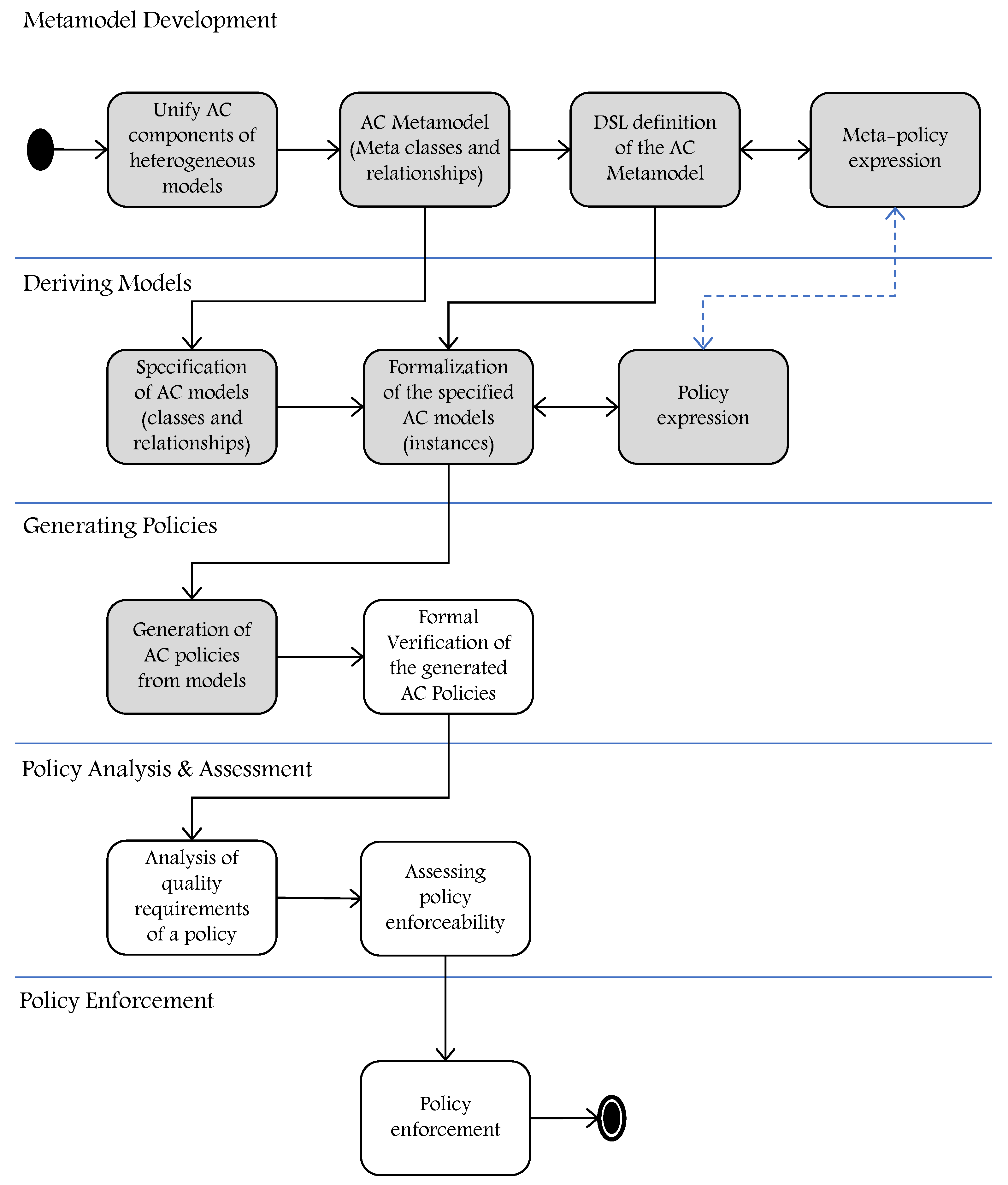
5. HEAD Metamodel: Development Approach to Access Control in Dynamic and Heterogeneous Environments
5.1. Metamodel Development
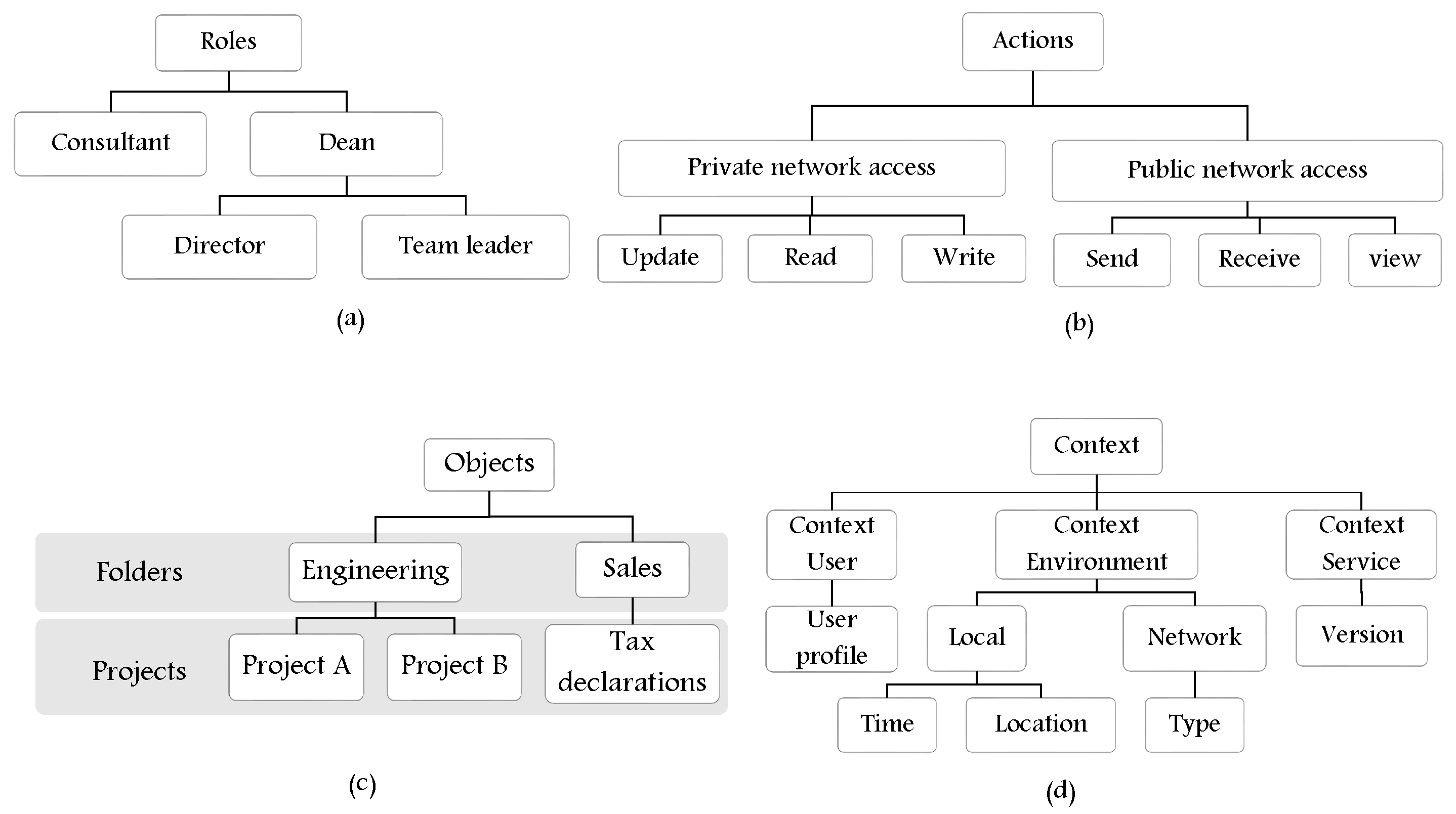
5.1.1. Unify AC Components of Heterogeneous Models
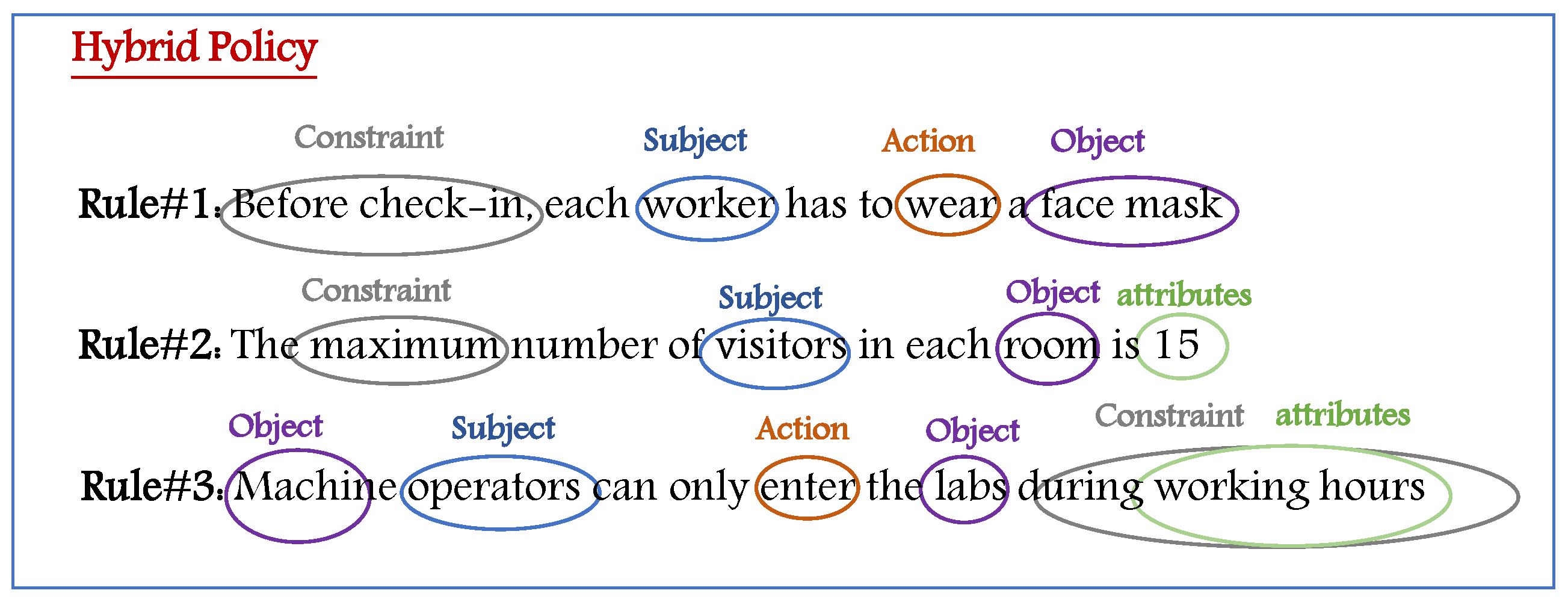
- EXPLICIT () components, those that refer to something that is real and exists (e.g., subjects and objects).
- IMPLICIT () components, those that refer to something described or explained in the guidelines or rules, and they include:
- –
- AUTHORIZATION UNITs (AU) (e.g., roles, security levels, categories, etc.).
- –
- PROCEDURAL UNITs (PU) (e.g., actions, permissions, etc.).
- SETTING (), which refers to components that are included to have more accurate and regulated access to resources (e.g., context, constraints, etc.).
5.1.2. HEAD Metamodel: Meta-Components and Relationships
- The relationship between and AU is to assign, for example, zero or many (0..*) subjects to roles, groups, categories, or any other authorization unit.
- The relationship between AU and PU, and PU and , is to represent which AUs are able to perform zero or many PU (e.g., actions, permissions, etc.) and access some, for example, objects or services.
- and components might have zero or many (e.g., contextual and/or non-contextual constraints) before accessing/performing tasks on some other components.
- The self-association edge exists on each of the classes to allow formulating AC models and hybrid models for different policies by allowing AUs to be associated with other AUs, PUs to be associated with other PUs, and so on.
- The hierarchical relationships are depicted by aggregation association for each of the entities, , AU, PU, and , to create a hierarchy of classes.
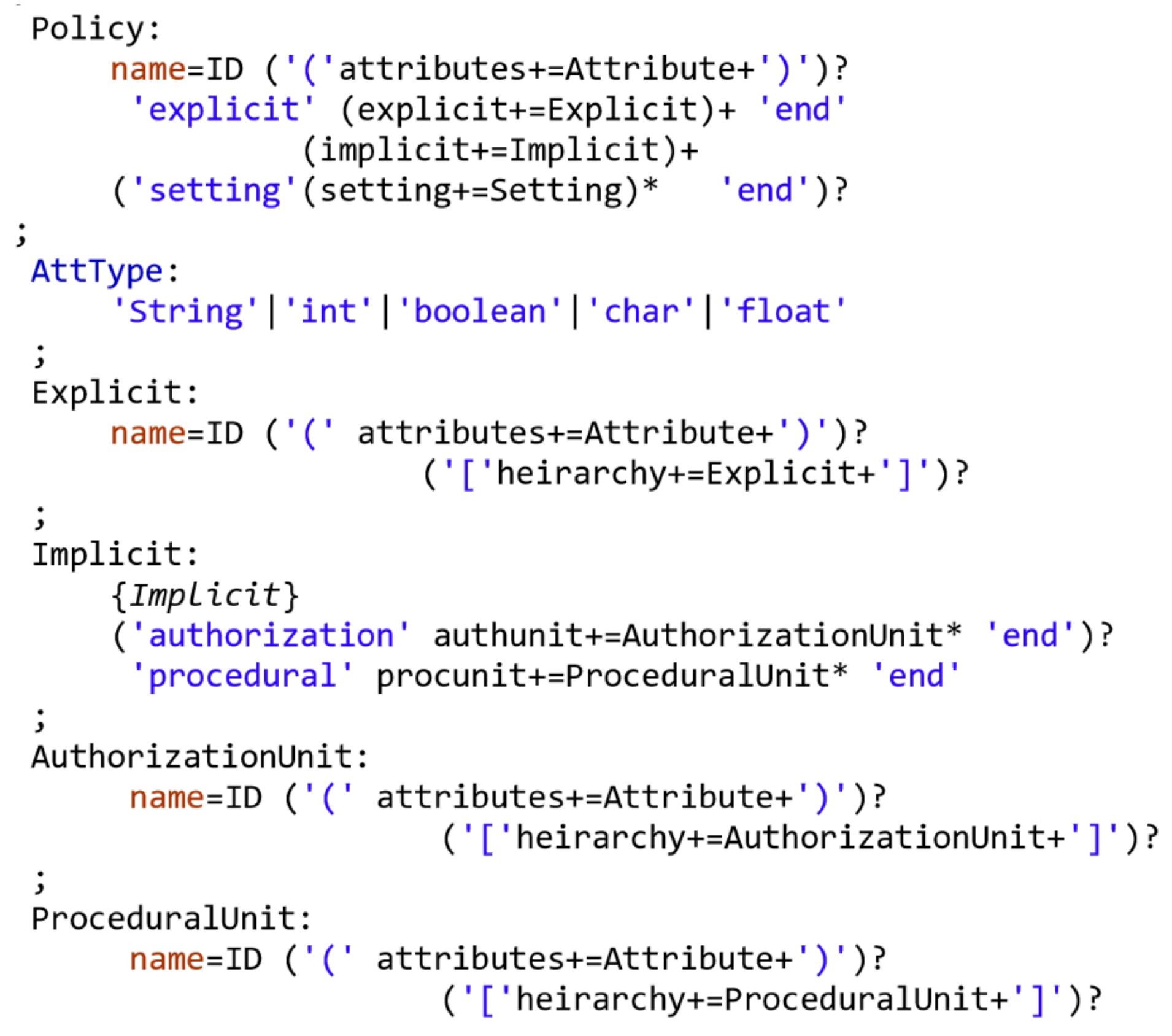
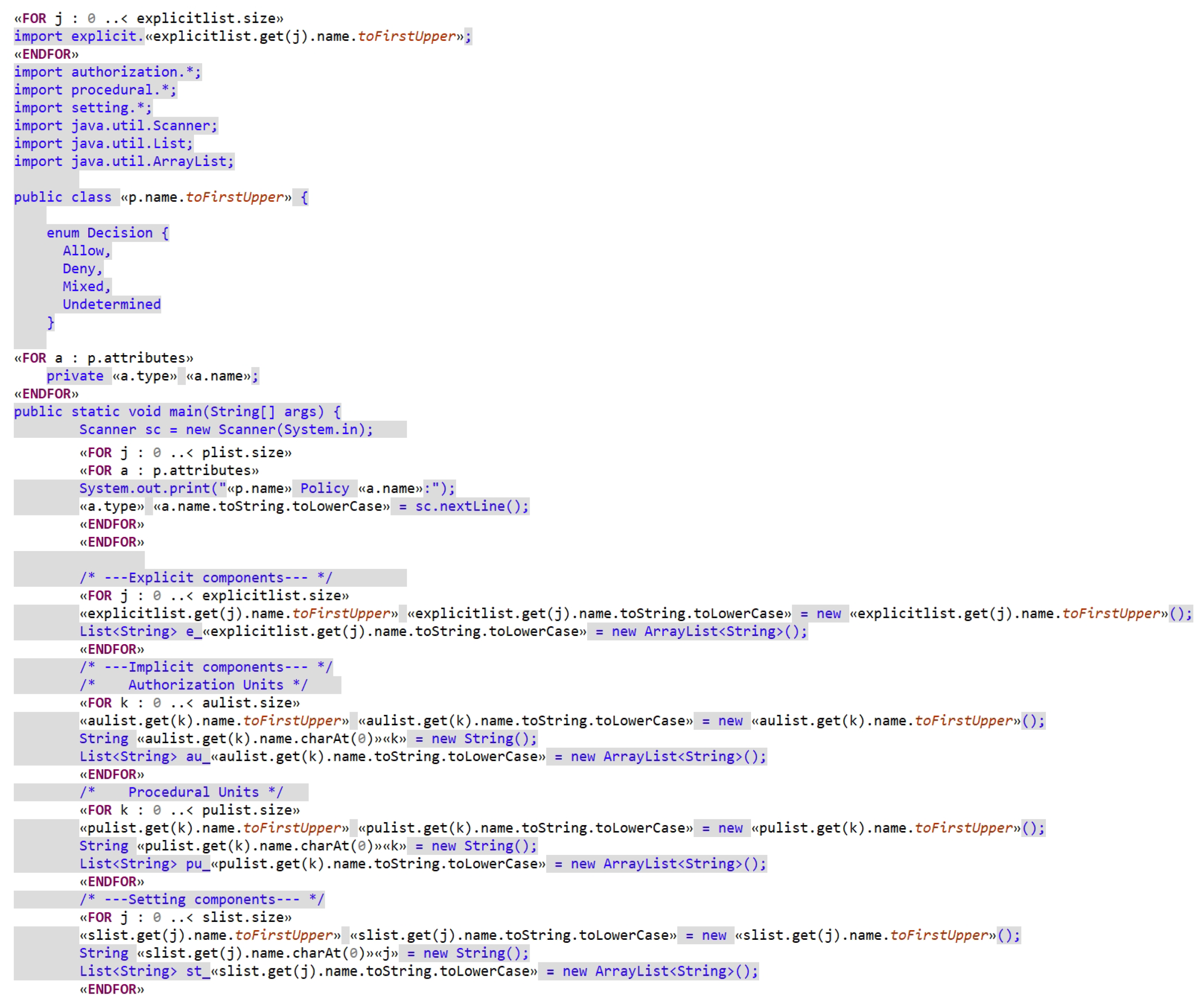
5.1.3. The DSL Definition of HEAD Metamodel
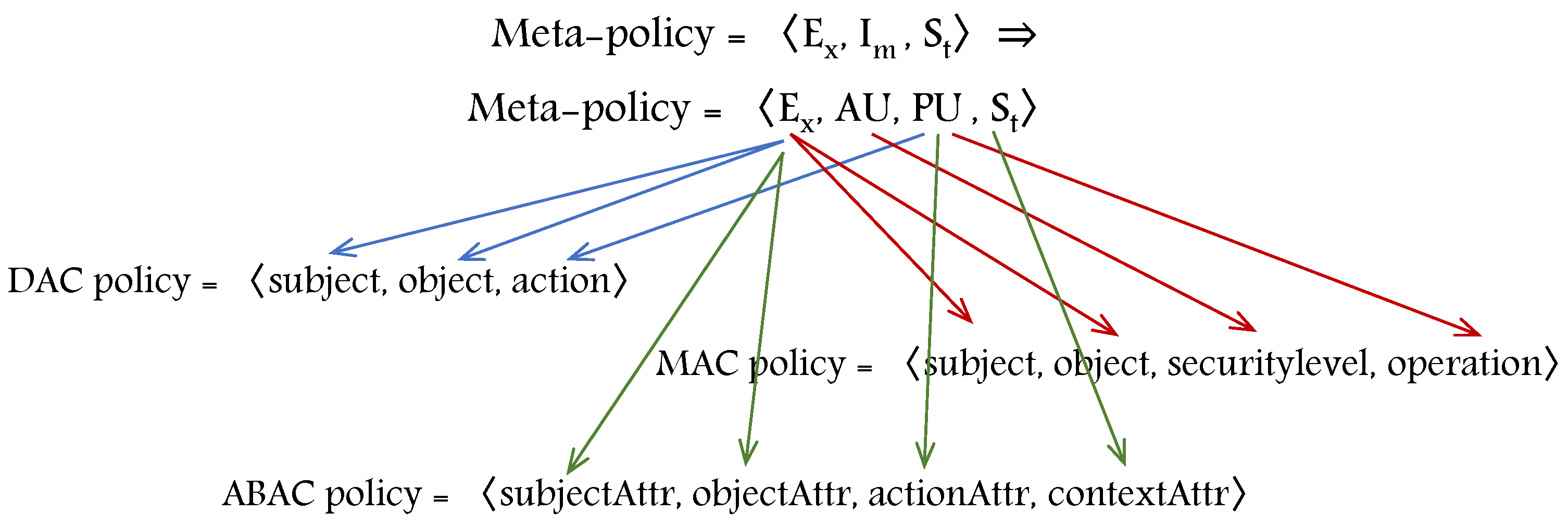
5.1.4. Meta-Policy Expression
5.2. Deriving Models
5.2.1. Specification of AC Models: Components and Relationships
5.2.2. Formalization of the Specified AC Models
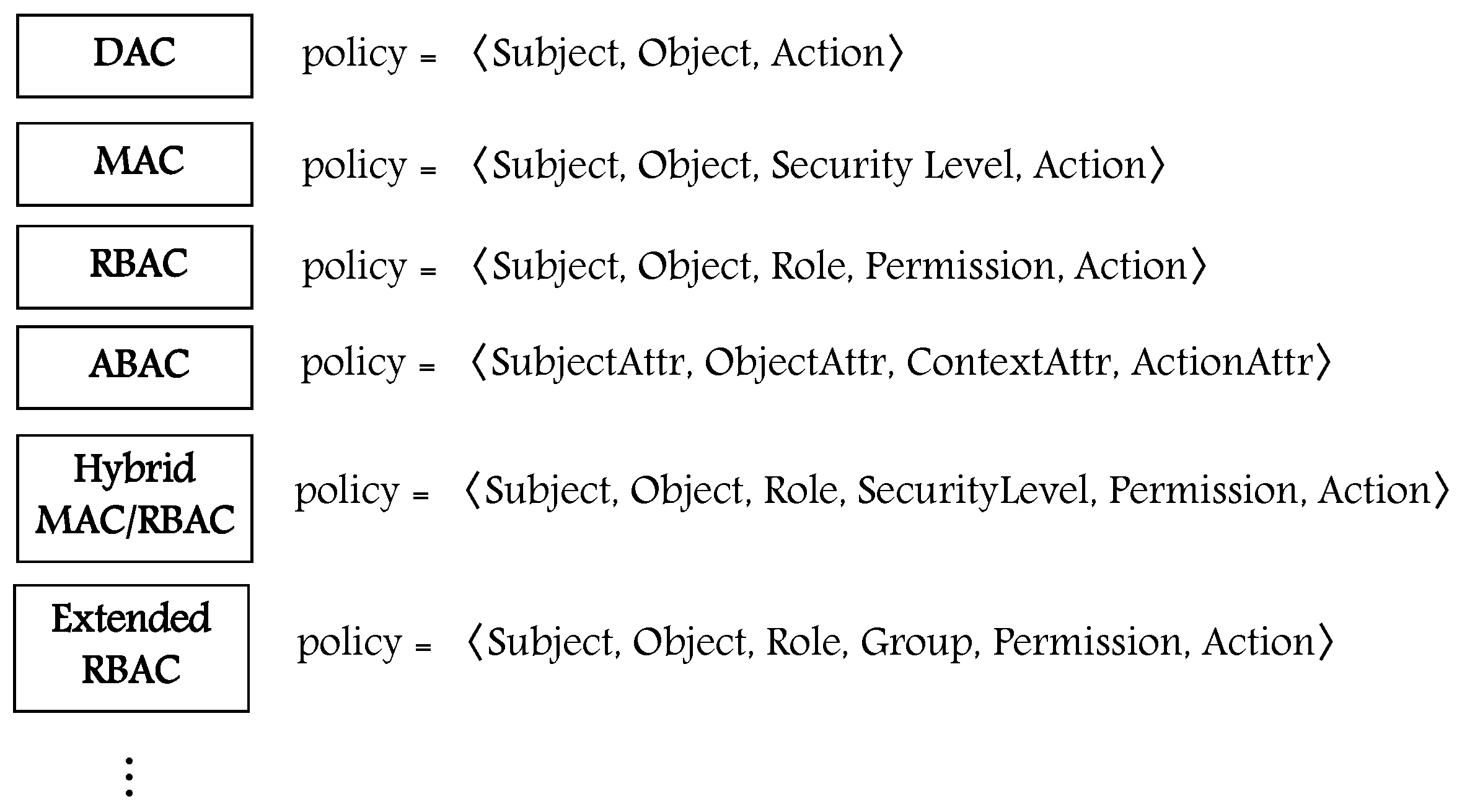
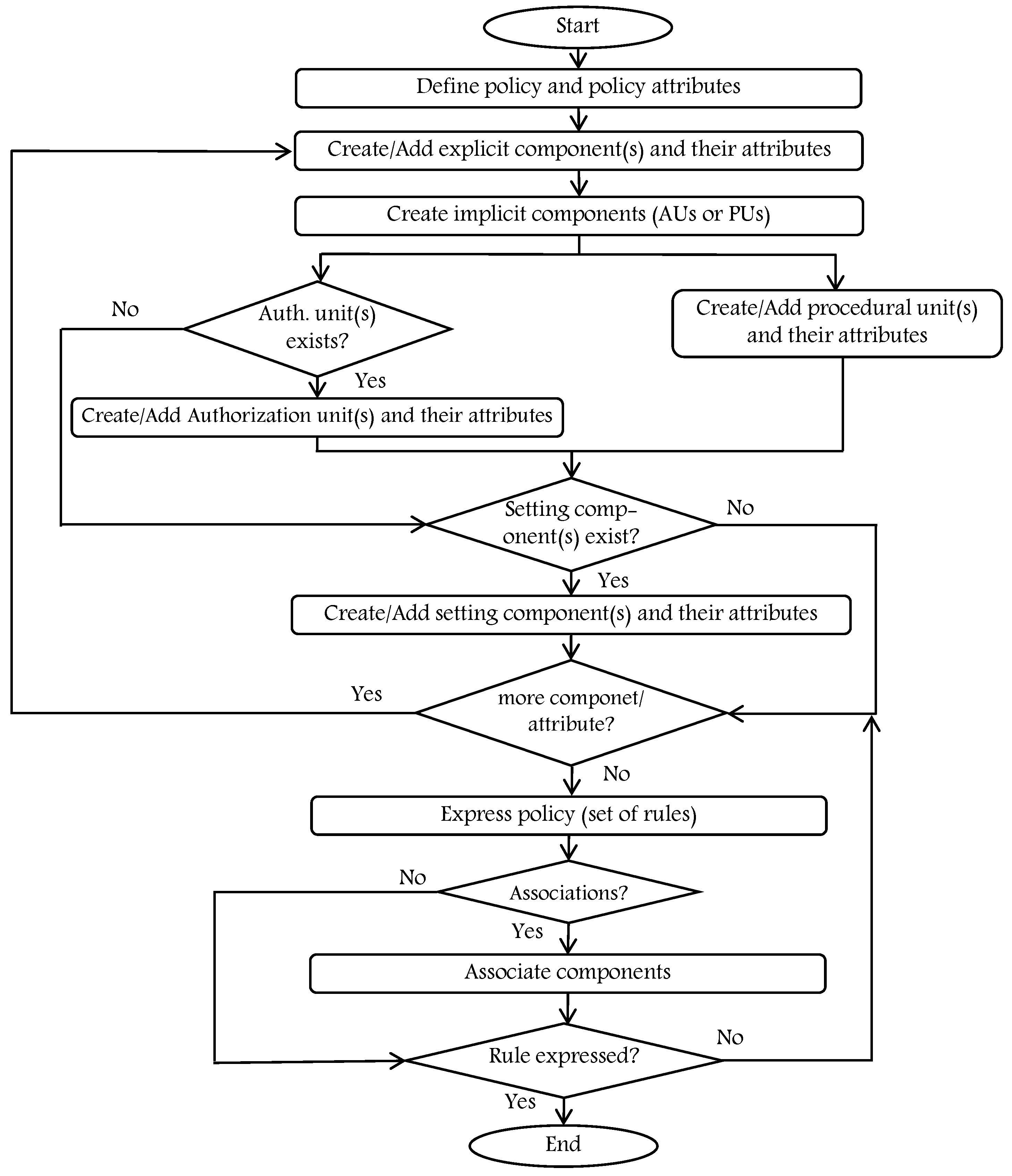
- Before defining any component(s), policy model should be specified with the needed attributes, for example, policy type (e.g., RBAC policy, ABAC policy, etc.), organization, etc.
- At least one (or more) Ex component must be created (with the needed attributes) since any AC model must include Ex entities (e.g., subject, object).
- Im components (AUs and/or PUs) should be identified and created. Note that an AC model might not include an AU component(s) if, for example, the needed AC model is DAC. If the model to be instantiated is MAC or RBAC, then there exists an AU component (security level or role). Moreover, an AC model must include at least one PU component, for example, action, and it should be created.
- An AC model might not include St component(s), for example, in the DAC model context, and constraint components do not exist.
- If there exists additional components/attributes, they should be created, for example, to upgrade a policy. The HEAD metamodel allows for adding them.
- Finally, if all the needed components/attributes are created, then associations of components are handled while expressing the needed rule(s).
5.2.3. Policy Expression
5.3. Generating Policies
5.3.1. Generation of AC Policies from the Specified Models
5.3.2. Formal Verification of the Generated AC Policies
5.4. Policy Analysis and Assessment
5.4.1. Analysis of Quality Requirements of a Policy
- Consistency means investigating that the obtained policies do not include both an allow and deny decision to the same subject for the action of an object.
- Relevance means checking if the obtained policies do not contain rules that do not apply to any action performed by subjects. In other words, making sure that subjects do not have any authorization to access object(s) and perform action(s) that they are not expected to execute.
- Minimality refers to investigating that the obtained policies do not include redundant or unnecessary policies.
- Completeness means that, for a given access request to access an object, there must be a corresponding policy, and any action to be executed by the subjects on any object the default decision that should be taken by AC model is to deny the access.
- Correctness refers to the process of checking that the policies conform with their intended goals and are in compliance with the system requirements.
5.4.2. Assessing Policy Enforceability
5.5. Policy Enforcement
6. Open Issues and New Opportunities
- HEAD metamodel could be enhanced to dynamically generate AC policies according to users’ context, profile, device, etc., since is based on a multi-level rule engine.
- In collaborative computing environments, distributed multiple cyber-physical areas interoperate with each other to provide an intelligent environment for users to achieve their collaborative activities. Hence, the features of the HEAD metamodel would facilitate fulfilling the collaboration and interoperability between the derived and heterogeneous AC models and their components among distributed multiple cyber-physical areas.
- The continuous technology upgrades impose the need to migrate AC policies from one model to another. The HEAD metamodel supports all the necessary tools to enhance with this new feature, in addition to its features.
- HEAD metamodel could be enhanced to implement and include built in packages or set of tools with predefined AC models, for example, the most used models DAC, MAC, RBAC, and ABAC. This could minimize the technical implementation efforts and facilitate administrative efforts to define policies.
- Since the definition for hundreds of thousands of attributes, expressing rules and policies, and performing implementation require a lot of time and resources, artificial intelligence (AI) techniques could be used, for example, object recognition to identify objects and define their attributes. Hence, the administrator could modify, add, or remove some attributes instead of creating hundreds of objects and thousands of attributes, especially in very large and complex systems.
- It could be enhanced and implemented to extract the data flow of an organization to define the rules after extracting the entities and attributes, then the administrator could be notified if there are some missing rules that must be defined.
- The features of the HEAD metamodel allow integrating AC to other systems, for example, intrusion detection systems.
- The flexible, upgradable, and dynamic nature of the HEAD metamodel makes it adaptable and applicable to distributed systems; hence, it allows developing and implementing blockchain-based AC systems.
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Quader, F.; Janeja, V.P. Insights into Organizational Security Readiness: Lessons Learned from Cyber-Attack Case Studies. J. Cybersecur. Priv. 2021, 1, 638–659. [Google Scholar] [CrossRef]
- Krehling, L.; Essex, A. A Security and Privacy Scoring System for Contact Tracing Apps. J. Cybersecur. Priv. 2021, 1, 597–614. [Google Scholar] [CrossRef]
- Kashmar, N.; Adda, M.; Ibrahim, H. HEAD Metamodel: Hierarchical, Extensible, Advanced, and Dynamic Access Control Metamodel for Dynamic and Heterogeneous Structures. Sensors 2021, 21, 6507. [Google Scholar] [CrossRef] [PubMed]
- Kashmar, N.; Adda, M.; Atieh, M.; Ibrahim, H. Access Control Metamodel for Policy Specification and Enforcement: From Conception to Formalization. Procedia Comput. Sci. 2021, 184, 887–892. [Google Scholar] [CrossRef]
- Kashmar, N.; Adda, M.; Atieh, M.; Ibrahim, H. A Review of Access Control Metamodels. Procedia Comput. Sci. 2021, 184, 445–452. [Google Scholar] [CrossRef]
- Kashmar, N.; Adda, M.; Atieh, M. From Access Control Models to Access Control Metamodels: A Survey. In Future of Information and Communication Conference; Springer: Cham, Switzerland, 2019; pp. 892–911. [Google Scholar] [CrossRef]
- Abd-Ali, J.; El Guemhioui, K.; Logrippo, L. A Metamodel for Hybrid Access Control Policies. J. Softw. 2015, 10, 784–797. [Google Scholar] [CrossRef][Green Version]
- Abramov, J.; Anson, O.; Dahan, M.; Shoval, P.; Sturm, A. A methodology for integrating access control policies within database development. Comput. Secur. 2012, 31, 299–314. [Google Scholar] [CrossRef]
- Kashmar, N.; Adda, M.; Ibrahim, H. Access Control Metamodels: Review, Critical Analysis, and Research Issues. J. Ubiquitous Syst. Pervasive Netw. 2021, 16, 2. [Google Scholar] [CrossRef]
- Wolfe, C. State of the Market: Access Control. Security Distributing and Marketing (SDM) Magazine, 5 April 2021. [Google Scholar]
- Al Kukhun, D. Steps Towards Adaptive Situation and Context-Aware Access: A Contribution to the Extension of Access Control Mechanisms within Pervasive Information Systems. Ph.D. Thesis, Université de Toulouse, Toulousen, France, 2012. [Google Scholar]
- Kashmar, N.; Adda, M.; Atieh, M.; Ibrahim, H. Deriving Access Control Models based on Generic and Dynamic Metamodel Architecture: Industrial Use Case. Procedia Comput. Sci. 2020, 177, 162–169. [Google Scholar] [CrossRef]
- Bertino, E.; Jabal, A.A.; Calo, S.; Verma, D.; Williams, C. The challenge of access control policies quality. J. Data Inf. Qual. 2018, 10, 1–6. [Google Scholar] [CrossRef]
- Soltani, N.; Jalili, R. Enforcing Access Control Policies over Data Stored on Untrusted Server. In Proceedings of the 2017 14th International ISC (Iranian Society of Cryptology) Conference on Information Security and Cryptology (ISCISC), Shiraz, Iran, 6–7 September 2017; pp. 119–124. [Google Scholar] [CrossRef]
- Kashmar, N.; Adda, M.; Atieh, M.; Ibrahim, H. Access Control in Cybersecurity and Social Media. In Cybersécurité et Médias Sociaux; Presses de l’Université: Laval, QC, Canada, 2021; Chapter 4. [Google Scholar]
- Hasiba, B.A.; Kahloul, L.; Benharzallah, S. A new hybrid access control model for multi-domain systems. In Proceedings of the 2017 4th International Conference on Control, Decision and Information Technologies (CoDIT), Barcelona, Spain, 5–7 April 2017; pp. 766–771. [Google Scholar] [CrossRef]
- Rajpoot, Q.M.; Jensen, C.D.; Krishnan, R. Integrating attributes into role-based access control. In Proceedings of the IFIP Annual Conference on Data and Applications Security and Privacy, Fairfax, VA, USA, 13 July 2015; Springer: Cham, Switzerland, 2015; pp. 242–249. [Google Scholar] [CrossRef]
- Kaiwen, S.; Lihua, Y. Attribute-role-based hybrid access control in the internet of things. In Proceedings of the Asia-Pacific Web Conference, Cham, Switzerland, 5 September 2014; pp. 333–343. [Google Scholar] [CrossRef]
- Oh, S. Permission-Centric Hybrid Access Control. In Advances in Web and Network Technologies, and Information Management; Springer: Berlin/Heidelberg, Germany, 2007; pp. 694–703. [Google Scholar] [CrossRef]
- Kim, S.; Kim, D.K.; Lu, L.; Song, E. Building hybrid access control by configuring RBAC and MAC features. Inf. Softw. Technol. 2014, 56, 763–792. [Google Scholar] [CrossRef]
- Ennahbaoui, M.; Elhajji, S. Study of access control models. Proc. World Congr. Eng. 2013, 2, 3–5. [Google Scholar]
- Aliane, L.; Adda, M. HoBAC: Toward a higher-order attribute-based access control model. Procedia Comput. Sci. 2019, 155, 303–310. [Google Scholar] [CrossRef]
- Servos, D.; Osborn, S.L. HGABAC: Towards a formal model of hierarchical attribute-based access control. In International Symposium on Foundations and Practice of Security; Springer: Cham, Switzerland, 2014; pp. 187–204. [Google Scholar] [CrossRef]
- Layouni, F.; Pollet, Y. Fi-orbac: A model of access control for federated identity platform. In Proceedings of the IADIS International Conference Information Systems, Barcelona, Spain, 27 February 2009. [Google Scholar]
- Nguyen, P.H.; Nain, G.; Klein, J.; Mouelhi, T.; Le Traon, Y. Model-driven adaptive delegation. In Proceedings of the 12th Annual International Conference on Aspect-Oriented Software Development, New York, NY, USA, 24 March 2013; pp. 61–72. [Google Scholar] [CrossRef]
- Klarl, H.; Molitorisz, K.; Emig, C.; Klinger, K.; Abeck, S. Extending Role-based Access Control for Business Usage. In Proceedings of the 2009 Third International Conference on Emerging Security Information, Systems and Technologies, Athens, Greece, 18–23 June 2009; pp. 136–141. [Google Scholar] [CrossRef]
- Adda, M.; Aliane, L. HoBAC: Fundamentals, principles, and policies. J. Ambient. Intell. Humaniz. Comput. 2020, 11, 5927–5941. [Google Scholar] [CrossRef]
- Barker, S. The next 700 access control models or a unifying meta-model? In Proceedings of the 14th ACM Symposium on Access Control Models and Technologies, New York, NY, USA, 3 June 2009; pp. 187–196. [Google Scholar] [CrossRef]
- Bertolissi, C.; Fernández, M. A metamodel of access control for distributed environments: Applications and properties. Inf. Comput. 2014, 238, 187–207. [Google Scholar] [CrossRef]
- Khamadja, S.; Adi, K.; Logrippo, L. Designing flexible access control models for the cloud. In Proceedings of the 6th International Conference on Security of Information and Networks, Aksaray, Turkey, 26–28 November 2013; pp. 225–232. [Google Scholar] [CrossRef]
- Trninić, B.; Sladić, G.; Milosavljević, G.; Milosavljević, B.; Konjović, Z. Policydsl: Towards generic access control management based on a policy metamodel. In Proceedings of the 2013 IEEE 12th International Conference on Intelligent Software Methodologies, Tools and Techniques (SoMeT), Budapest, Hungary, 22–24 September 2013. [Google Scholar] [CrossRef]
- Slimani, N.; Khambhammettu, H.; Adi, K.; Logrippo, L. UACML: Unified access control modeling language. In Proceedings of the 2011 4th IFIP International Conference on New Technologies, Mobility and Security, Paris, France, 7–10 February 2011; pp. 1–8. [Google Scholar] [CrossRef]
- Alves, S.; Degtyarev, A.; Fernández, M. Access control and obligations in the category-based metamodel: A rewrite-based semantics. In International Symposium on Logic-Based Program Synthesis and Transformation; Springer: Cham, Switzerland, 2014; pp. 148–163. [Google Scholar] [CrossRef]
- Korman, M.; Lagerström, R.; Ekstedt, M. Modeling enterprise authorization: A unified metamodel and initial validation. Complex Syst. Inform. Model. Q. 2016, 7, 1–24. [Google Scholar] [CrossRef]
- Ferraiolo, D.; Chandramouli, R.; Kuhn, R.; Hu, V. Extensible access control markup language (XACML) and next generation access control (NGAC). In Proceedings of the 2016 ACM International Workshop on Attribute Based Access Control, New Orleans, LA, USA, 11 March 2016; pp. 13–24. [Google Scholar] [CrossRef]
- Bertino, E.; Jabal, A.A.; Calo, S.; Makaya, C.; Touma, M.; Verma, D.; Williams, C. Provenance-based analytics services for access control policies. In Proceedings of the 2017 IEEE World Congress on Services (SERVICES), Honolulu, HI, USA, 25–30 June 2017; pp. 94–101. [Google Scholar] [CrossRef]
- Hu, V.C.; Kuhn, D.R.; Xie, T. Property verification for generic access control models. In Proceedings of the 2008 IEEE/IFIP International Conference on Embedded and Ubiquitous Computing, Shanghai, China, 17–20 December 2008; Volume 2, pp. 243–250. [Google Scholar] [CrossRef]
- Hu, V.C.; Kuhn, R.; Yaga, D. Verification and Test Methods for Access Control Policies/Models; NIST Special Publication: Gaithersburg, MD, USA, 2017; Volume 800, p. 192. [Google Scholar] [CrossRef]
- Vanickis, R.; Jacob, P.; Dehghanzadeh, S.; Lee, B. Access control policy enforcement for zero-trust-networking. In Proceedings of the 2018 29th Irish Signals and Systems Conference (ISSC), Belfast, UK, 21–22 June 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Norman, T. 5-Electronics Elements (High-Level Discussion). In Integrated Security Systems Design, 2nd ed.; Norman, T., Ed.; Butterworth-Heinemann: Boston, MA, USA, 2014; pp. 49–55. [Google Scholar] [CrossRef]
- Ouaddah, A.; Mousannif, H.; Abou Elkalam, A.; Ouahman, A.A. Access control in the Internet of Things: Big challenges and new opportunities. Comput. Netw. 2017, 112, 237–262. [Google Scholar] [CrossRef]
- Ravidas, S.; Lekidis, A.; Paci, F.; Zannone, N. Access control in Internet-of-Things: A survey. J. Netw. Comput. Appl. 2019, 144, 79–101. [Google Scholar] [CrossRef]







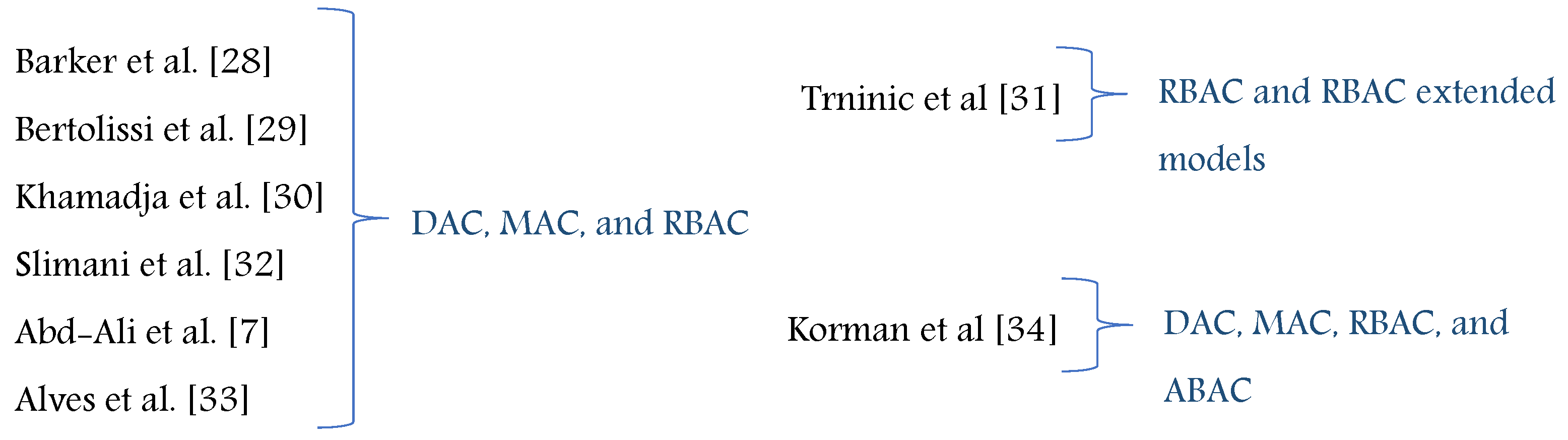


| Ref. | Year | Proposed for | Metamodel | Based on | Instances | Modeling Language |
|---|---|---|---|---|---|---|
| AC metamodels are proposed as generic metamodels | ||||||
| Barker [28] | 2009 | Enterprise | Barker’s metamodel | DAC, MAC, RBAC | RBAC, MAC | Rule/logic language |
| Bertolissi et al. [29] | 2014 | Distributed system of several sites | Distributed metamodel | DAC, MAC, RBAC | Hybrid models of DAC, MAC, RBAC | Rewrite-based operational semantics |
| Khamadja et al. [30] | 2013 | Cloud computing | CatBAC metamodel | DAC, MAC, RBAC | Hybrid models of DAC, MAC, RBAC | First-order logic |
| Trninić et al. [31] | 2013 | Set of systems | PolicyDSL | RBAC models | RBAC and hybrid models | Textual DSL |
| AC metamodels are proposed as hybrid AC metamodels | ||||||
| Slimani et al. [32] | 2011 | Enterprise | UACML metamodel | DAC, MAC, RBAC | Group based, MAC, RBAC, hybrid model | Object constraint language (OCL) |
| Abd-Ali et al. [7] | 2015 | Enterprise | Integration metamodel | CW, BLP, BIBA, RBAC | Hybrid models | First-order logic |
| AC metamodels are proposed as metamodel extension for some of the existing metamodels | ||||||
| Alves et al. [33] | 2014 | Enterprise | Obligations in CBAC metamodel | DAC, MAC, RBAC | Hybrid models of DAC, MAC, RBAC | Rewrite-based operational semantics |
| Korman et al. [34] | 2016 | Enterprise architecture framework | Unified metamodel | DAC, BLP, Biba, CW, RBAC, ABAC | DAC, BLP, CW, RBAC, ABAC | ArchiMate |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kashmar, N.; Adda, M.; Ibrahim, H. HEAD Access Control Metamodel: Distinct Design, Advanced Features, and New Opportunities. J. Cybersecur. Priv. 2022, 2, 42-64. https://doi.org/10.3390/jcp2010004
Kashmar N, Adda M, Ibrahim H. HEAD Access Control Metamodel: Distinct Design, Advanced Features, and New Opportunities. Journal of Cybersecurity and Privacy. 2022; 2(1):42-64. https://doi.org/10.3390/jcp2010004
Chicago/Turabian StyleKashmar, Nadine, Mehdi Adda, and Hussein Ibrahim. 2022. "HEAD Access Control Metamodel: Distinct Design, Advanced Features, and New Opportunities" Journal of Cybersecurity and Privacy 2, no. 1: 42-64. https://doi.org/10.3390/jcp2010004
APA StyleKashmar, N., Adda, M., & Ibrahim, H. (2022). HEAD Access Control Metamodel: Distinct Design, Advanced Features, and New Opportunities. Journal of Cybersecurity and Privacy, 2(1), 42-64. https://doi.org/10.3390/jcp2010004






