A Novel Image Encryption Algorithm Based on Compressive Sensing and a Two-Dimensional Linear Canonical Transform
Abstract
1. Introduction
2. Preliminaries
2.1. Linear Canonical Transform
2.2. Compressive Sensing
2.3. Lorenz’s Hyper-Chaotic System
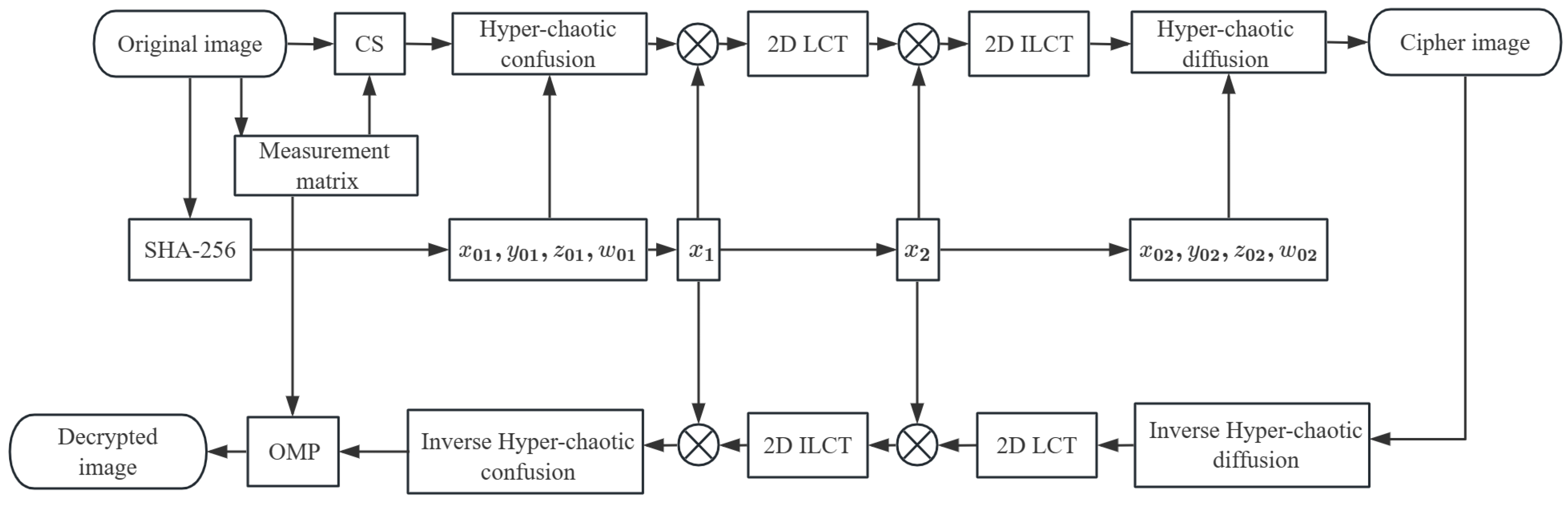
3. The Proposed Image Encryption and Decryption Algorithm
3.1. Encryption Process
3.1.1. Key Generation
3.1.2. The Compression–Encryption Steps
3.1.3. Permutation and Diffusion
3.1.4. CRPMs and 2D LCT Encryption
4. Simulation Results and Security Analysis
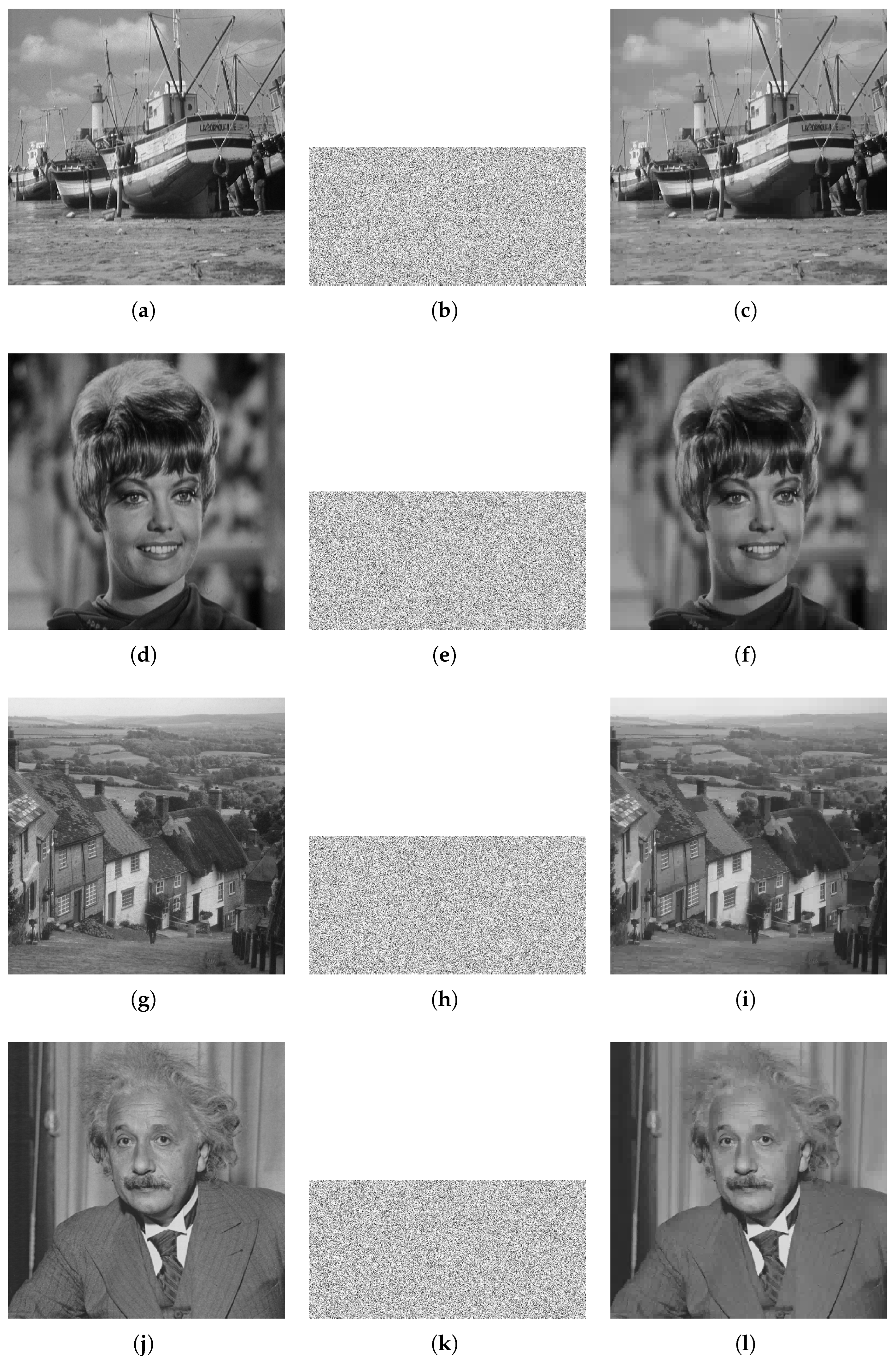
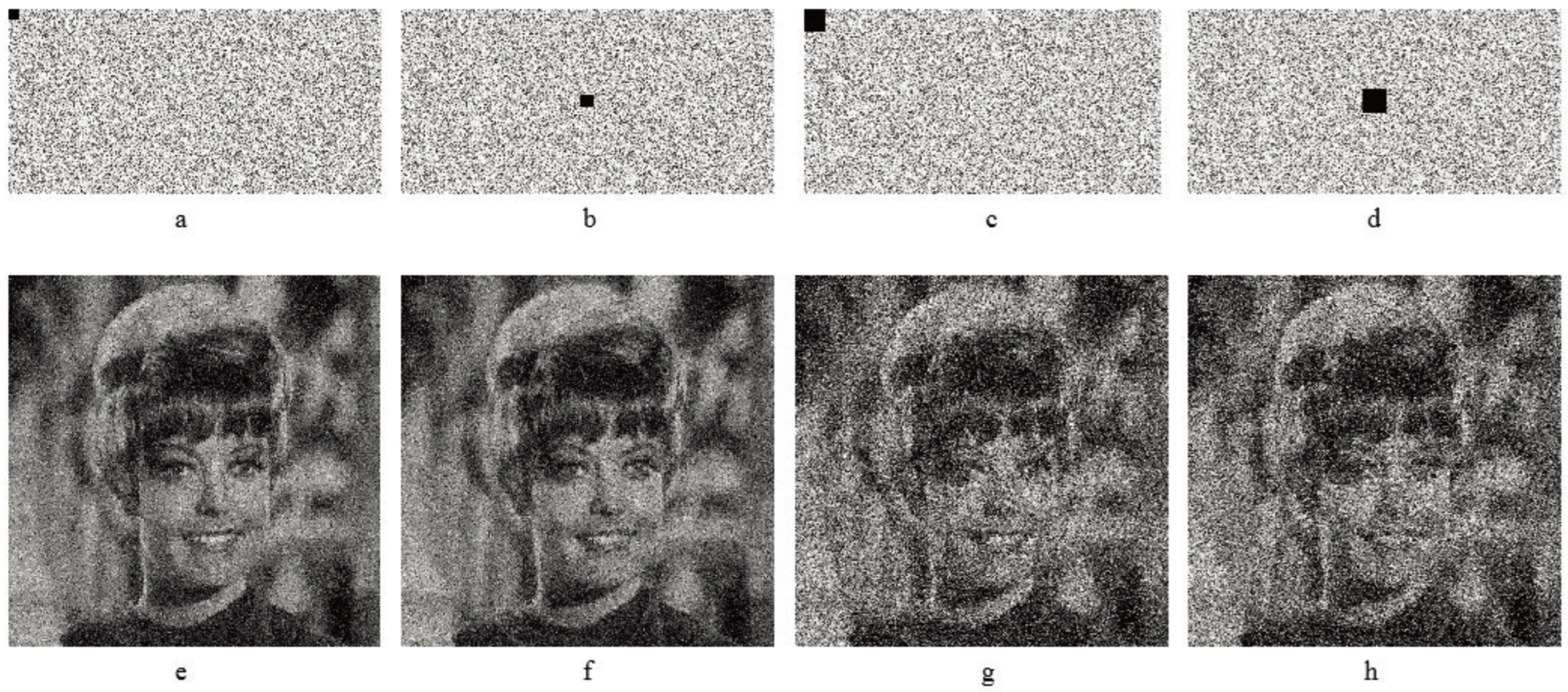
4.1. Results of Encryption and Decryption
4.2. Security Evaluation
4.2.1. Analysis of Key Spaces
4.2.2. Histogram Analysis
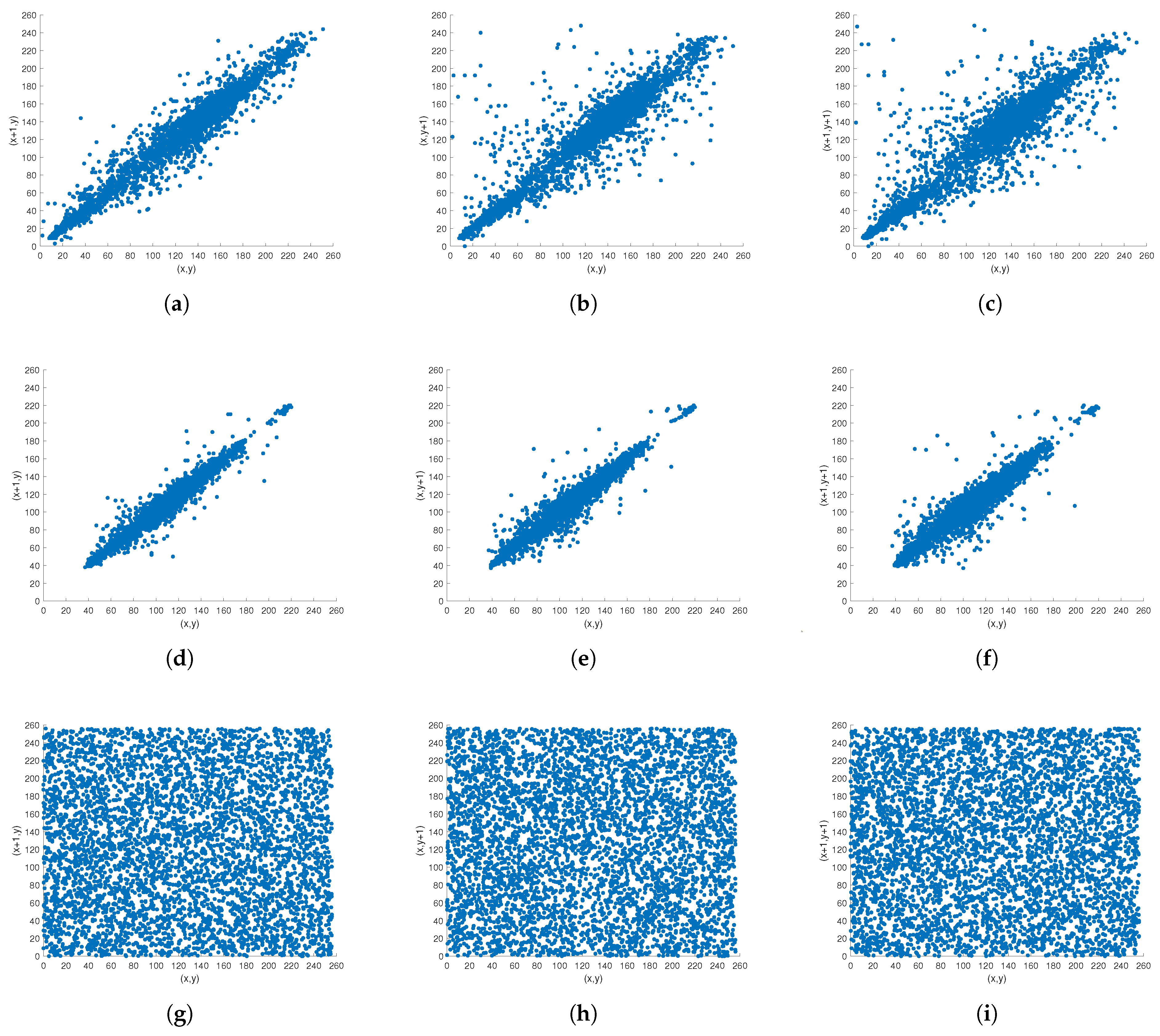
4.2.3. Analysis of Correlation Coefficients
4.2.4. Analysis of Information Entropy
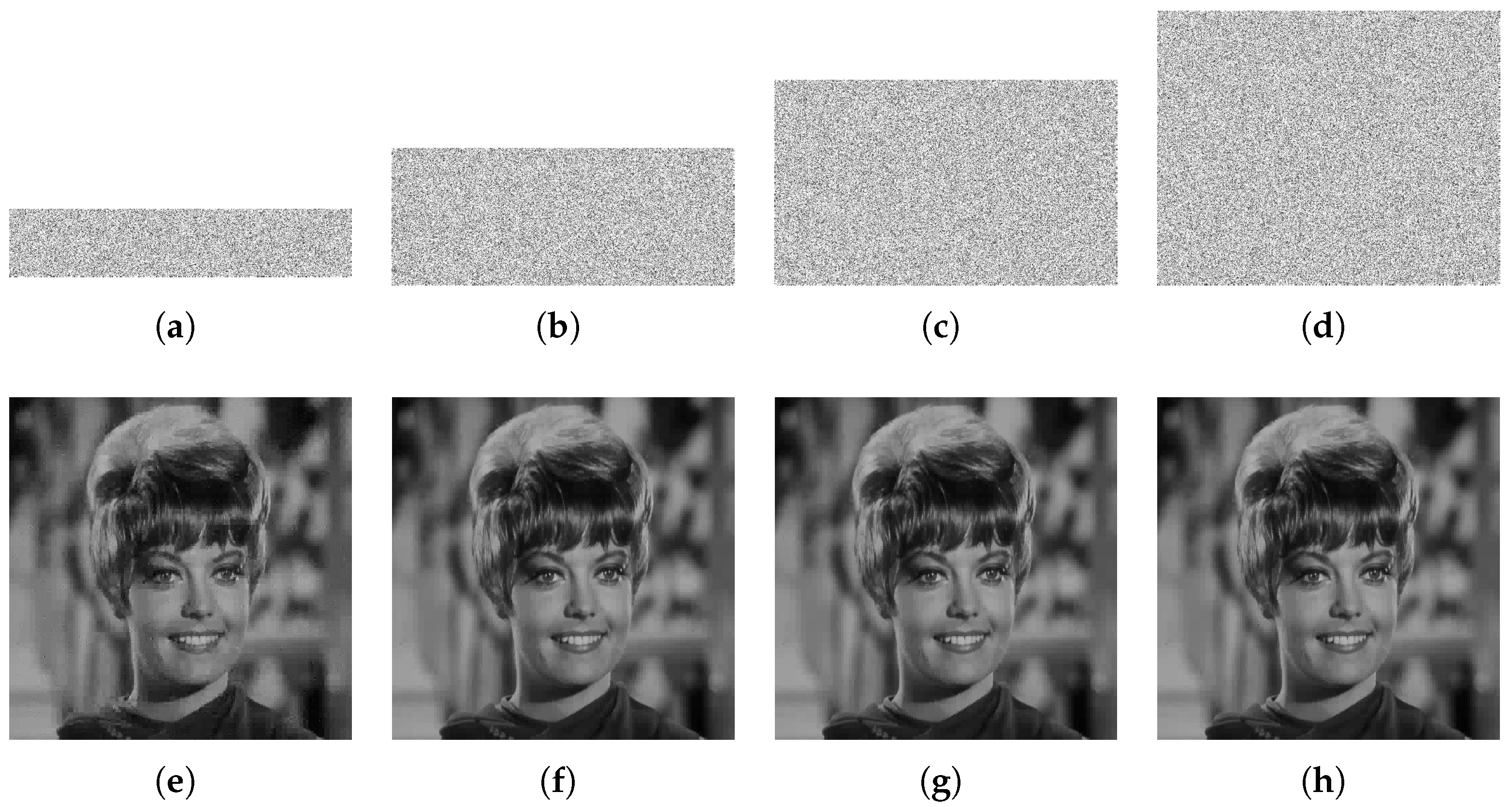
4.2.5. Analysis of Cropping Attacks
4.2.6. Crucial Sensitivity Testing
4.2.7. Analysis of Differential Attacks
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Matoba, O.; Nomura, T.; Perez-Cabre, E.; Millan, M.S.; Javidi, B. Optical techniques for information security. Proc. IEEE 2009, 97, 1128–1148. [Google Scholar] [CrossRef]
- Wang, Y.; Liu, Z.; Xu, J.; Yan, W. Heterogeneous network representation learning approach for ethereum identity identification. IEEE Trans. Comput. Soc. Syst. 2022, 10, 890–899. [Google Scholar] [CrossRef]
- Zhao, J.; Lv, Y. Output-feedback Robust Tracking Control of Uncertain Systems via Adaptive Learning. Int. J. Control Autom. Syst. 2023, 21, 1108–1118. [Google Scholar] [CrossRef]
- Refregier, P.; Javidi, B. Optical image encryption based on input plane and Fourier plane random encoding. Opt. Lett. 1995, 20, 767–769. [Google Scholar] [CrossRef]
- Situ, G.; Zhang, J. Double random-phase encoding in the Fresnel domain. Opt. Lett. 2004, 29, 1584–1586. [Google Scholar] [CrossRef]
- Chen, J.X.; Zhu, Z.L.; Fu, C.; Yu, H. Optical image encryption scheme using 3-D chaotic map based joint image scrambling and random encoding in gyrator domains. Opt. Commun. 2015, 341, 263–270. [Google Scholar] [CrossRef]
- Wang, X.; Zhao, D. Simultaneous nonlinear encryption of grayscale and color images based on phase-truncated fractional Fourier transform and optical superposition principle. Appl. Opt. 2013, 52, 6170–6178. [Google Scholar] [CrossRef]
- Javidi, B.; Artur Carnicer, E.A. Roadmap on optical security. J. Opt. 2016, 18, 83001. [Google Scholar] [CrossRef]
- Zhou, N.; Wang, Y.; Gong, L. Novel optical image encryption scheme based on fractional Mellin transform. Opt. Commun. 2011, 284, 3234–3242. [Google Scholar] [CrossRef]
- Qin, W.; Peng, X. Asymmetric cryptosystem based on phase-truncated Fourier transforms. Opt. Lett. 2010, 35, 118–120. [Google Scholar] [CrossRef]
- Zhou, N.; Wang, Y.; Wu, J. Image encryption algorithm based on the multi-order discrete fractional Mellin transform. Opt. Commun. 2011, 284, 5588–5597. [Google Scholar] [CrossRef]
- Patra, A.; Saha, A.; Bhattacharya, K. Multiplexing and encryption of images using phase grating and random phase mask. Opt. Eng. 2020, 59, 33105. [Google Scholar] [CrossRef]
- Wei, D.; Wang, R.; Li, Y.M. Random discrete linear canonical transform. J. Opt. Soc. Am. A Opt. Image Sci. Vis. 2016, 33, 2470–2476. [Google Scholar] [CrossRef]
- Huang, Z.J.; Cheng, S.; Gong, L.H.; Zhou, N.R. Nonlinear optical multi-image encryption scheme with two-dimensional linear canonical transform. Opt. Lasers Eng. 2020, 124, 105821. [Google Scholar] [CrossRef]
- Rakheja, P.; Vig, R.; Singh, P. Double image encryption using 3D Lorenz chaotic system, 2D non-separable linear canonical transform and QR decomposition. Opt. Quantum Electron. 2020, 52, 103. [Google Scholar] [CrossRef]
- Fridrich, J. Symmetric ciphers based on two-dimensional chaotic maps. Int. J. Bifurc. Chaos 1998, 8, 1259–1284. [Google Scholar] [CrossRef]
- Song, C.Y.; Qiao, Y.L.; Zhang, X.Z. An image encryption scheme based on new spatiotemporal chaos. Optik 2013, 124, 3329–3334. [Google Scholar] [CrossRef]
- Wang, X.; Xu, D. A novel image encryption scheme based on Brownian motion and PWLCM chaotic system. Nonlinear Dyn. 2014, 75, 345–353. [Google Scholar] [CrossRef]
- Li, C.; Liu, Y.; Xie, T.; Chen, M.Z.Q. Breaking a novel image encryption scheme based on improved hyperchaotic sequences. Nonlinear Dyn. 2013, 73, 2083–2089. [Google Scholar] [CrossRef]
- Quadri, S.Z.A. Multiple-information security system using spherical wave and chaotic random phase mask encoding. Opt. Eng. 2018, 57, 93103. [Google Scholar] [CrossRef]
- Bechikh, R.; Hermassi, H.; El-Latif, A.A.A.; Rhouma, R.; Belghith, S. Breaking an image encryption scheme based on a spatiotemporal chaotic system. Signal Process. Image Commun. 2015, 39, 151–158. [Google Scholar] [CrossRef]
- Arroyo, D.; Rhouma, R.; Alvarez, G.; Li, S.; Fernandez, V. On the security of a new image encryption scheme based on chaotic map lattices. Chaos 2008, 18, 33112. [Google Scholar] [CrossRef]
- Saljoughi, A.S.; Mirvaziri, H. A new method for image encryption by 3D chaotic map. Pattern Anal. Appl. 2019, 22, 243–257. [Google Scholar] [CrossRef]
- Ghazanfaripour, H.; Broumandnia, A. Designing a digital image encryption scheme using chaotic maps with prime modular. Opt. Laser Technol. 2020, 131, 106339. [Google Scholar] [CrossRef]
- Li, Y.; Wang, C.; Chen, H. A hyper-chaos-based image encryption algorithm using pixel-level permutation and bit-level permutation. Opt. Lasers Eng. 2017, 90, 238–246. [Google Scholar] [CrossRef]
- Xu, Q.; Sun, K.; Cao, C.; Zhu, C. A fast image encryption algorithm based on compressive sensing and hyperchaotic map. Opt. Lasers Eng. 2019, 121, 203–214. [Google Scholar] [CrossRef]
- Luo, Y.; Lin, J.; Liu, J.; Wei, D.; Cao, L.; Zhou, R.; Cao, Y.; Ding, X. A robust image encryption algorithm based on Chua’s circuit and compressive sensing. Signal Process. 2019, 161, 227–247. [Google Scholar] [CrossRef]
- Candes, E.; Romberg, J.; Tao, T. Robust uncertainty principles: Exact signal reconstruction from highly incomplete frequency information. IEEE Trans. Inf. Theory 2006, 52, 489–509. [Google Scholar] [CrossRef]
- Candes, E.; Wakin, M. An introduction to compressive sampling. IEEE Signal Process. Mag. 2008, 25, 21–30. [Google Scholar] [CrossRef]
- Huang, X.; Dong, Y.; Ye, G.; Shi, Y. Meaningful image encryption algorithm based on compressive sensing and integer wavelet transform. Front. Comput. Sci. 2023, 17, 173804. [Google Scholar] [CrossRef]
- Zhou, N.; Li, H.; Wang, D.; Pan, S.; Zhou, Z. Image compression and encryption scheme based on 2D compressive sensing and fractional Mellin transform. Opt. Commun. 2015, 343, 10–21. [Google Scholar] [CrossRef]
- Chai, X.; Zheng, X.; Gan, Z.; Han, D.; Chen, Y. An image encryption algorithm based on chaotic system and compressive sensing. Signal Process. 2018, 148, 124–144. [Google Scholar] [CrossRef]
- Huang, R.; Rhee, K.H.; Uchida, S. A parallel image encryption method based on compressive sensing. Multimed. Tools Appl. 2014, 72, 71–93. [Google Scholar] [CrossRef]
- Zhou, N.; Zhang, A.; Zheng, F.; Gong, L. Novel image compression–encryption hybrid algorithm based on key-controlled measurement matrix in compressive sensing. Opt. Laser Technol. 2014, 62, 152–160. [Google Scholar] [CrossRef]
- Chai, X.; Gan, Z.; Chen, Y.; Zhang, Y. A visually secure image encryption scheme based on compressive sensing. Signal Process. 2017, 134, 35–51. [Google Scholar] [CrossRef]
- Zhang, L.Z.; Zhou, X.; Wang, D.; Li, N.N.; Bai, X.; Wang, Q.H. Multiple-image encryption based on optical scanning holography using orthogonal compressive sensing and random phase mask. Opt. Eng. 2020, 59, 1. [Google Scholar] [CrossRef]
- Hu, G.; Xiao, D.; Wang, Y.; Xiang, T.; Zhou, Q. Securing image information using double random phase encoding and parallel compressive sensing with updated sampling processes. Opt. Lasers Eng. 2017, 98, 123–133. [Google Scholar] [CrossRef]
- Wei, D.; Li, Y. Convolution and Multichannel Sampling for the Offset Linear Canonical Transform and Their Applications. IEEE Trans. Signal Process. 2019, 67, 6009–6024. [Google Scholar] [CrossRef]
- Wolf, K.B. Construction and Properties of Canonical Transforms; Springer: Berlin/Heidelberg, Germany, 1979; pp. 381–416. [Google Scholar]
- Chen, S.S.; Donoho, D.L.; Saunders, M.A. Atomic decomposition by basis pursuit. Siam Rev. 2001, 43, 129–159. [Google Scholar] [CrossRef]
- Pati, Y.; Rezaiifar, R.; Krishnaprasad, P. Orthogonal matching pursuit: Recursive function approximation with applications to wavelet decomposition. In Proceedings of the 27th Asilomar Conference on Signals, Systems and Computers, Pacific Grove, CA, USA, 1–3 November 1993; pp. 40–44. [Google Scholar]
- Needell, D.; Tropp, J.A. CoSaMP: Iterative signal recovery from incomplete and inaccurate samples. Commun. ACM 2010, 53, 93–100. [Google Scholar] [CrossRef]
- Zhou, N.; Zhang, A.; Wu, J.; Pei, D.; Yang, Y. Novel hybrid image compression–encryption algorithm based on compressive sensing. Optik 2014, 125, 5075–5080. [Google Scholar] [CrossRef]
- Alvarez, G.; Li, S. Some basic cryptographic requirements for chaos-based crytosystems. Int. J. Bifurc. Chaos 2006, 16, 2129–2151. [Google Scholar] [CrossRef]
- Xingyuan, W.; Junjian, Z.; Guanghui, C. An image encryption algorithm based on ZigZag transform and LL compound chaotic system. Opt. Laser Technol. 2019, 119, 105581. [Google Scholar] [CrossRef]
- Awad, A.; Awad, D. Efficient image chaotic encryption algorithm with no propagation error. Etri J. 2010, 32, 774–783. [Google Scholar] [CrossRef]
- Zhou, K.; Fan, J.; Fan, H.; Li, M. Secure image encryption scheme using double random-phase encoding and compressed sensing. Opt. Laser Technol. 2020, 121, 105769. [Google Scholar] [CrossRef]
- Wu, Y.; Noonan, J.P.; Agaian, S. NPCR and UACI Randomness Tests for Image Encryption. J. Sel. Areas Telecommun. 2011, 1, 31–37. [Google Scholar]




| CR | Ref. [43] | Ref. [32] | Ref. [26] | Ours |
|---|---|---|---|---|
| 0.25 | 22.62 | 26.06 | 26.52 | 24.76 |
| 0.5 | 26.87 | 29.82 | 29.23 | 33.10 |
| 0.75 | 30.82 | 29.56 | 29.22 | 33.44 |
| Image | Encryption Time | Decryption Time |
|---|---|---|
| Boat | 0.2301 | 8.7842 |
| Zelda | 0.2057 | 9.8499 |
| Gold hill | 0.2257 | 7.8853 |
| Einstein | 0.2156 | 8.7155 |
| Image | MSE |
|---|---|
| Boat | 48,196.2 |
| Zelda | 43,602.8 |
| Gold hill | 47,532.0 |
| Einstein | 45,190.7 |
| Algorithms | Ref. [26] | Ref. [32] | Ref. [45] | Ours |
|---|---|---|---|---|
| Key Space |
| Image | Ref. [30] | Ours |
|---|---|---|
| Boat | 0.9520 | 0.9522 |
| Zelda | - | 0.9586 |
| Gold hill | 0.9634 | 0.9625 |
| Einstein | 0.9578 | 0.9552 |
| Images | Horizontal | Vertical | Diagonal |
|---|---|---|---|
| Boat | 0.9383 | 0.9729 | 0.9250 |
| 0.0175 | −0.0022 | −0.0089 | |
| Zelda | 0.9829 | 0.9917 | 0.9783 |
| −0.0061 | 0.01533 | 0.0035 | |
| Einstein | 0.9750 | 0.9801 | 0.9588 |
| 0.0142 | 0.0182 | −0.005 | |
| Peppers | 0.9803 | 0.9811 | 0.9699 |
| −0.0101 | 0.0011 | −0.0094 | |
| Man | 0.9631 | 0.9700 | 0.9453 |
| 0.0094 | 0.0103 | −0.0037 | |
| Gold hill | 0.9718 | 0.9729 | 0.9525 |
| 0.0056 | −0.0093 | −0.0282 | |
| Couple | 0.9480 | 0.9511 | 0.9124 |
| −0.0027 | 0.0081 | 0.0097 |
| Direction | Horizontal | Vertical | Diagonal |
|---|---|---|---|
| Lena () | 0.9706 | 0.9853 | 0.9588 |
| Ref. [34] | 0.0846 | 0.0583 | 0.0931 |
| Ref. [43] | 0.0198 | 0.0141 | 0.0026 |
| Ref. [31] | 0.0104 | 0.0299 | 0.0062 |
| Ours | 0.0071 | 0.0121 | −0.0073 |
| Image | Entropy | |
|---|---|---|
| Plaintext | Ciphertext | |
| Boat | 7.1914 | 7.9971 |
| Zelda | 7.2668 | 7.9973 |
| Einstein | 6.8667 | 7.9974 |
| Peppers | 7.5936 | 7.9968 |
| Man | 7.1926 | 7.9972 |
| Gold hill | 7.4778 | 7.9971 |
| Couple | 7.0581 | 7.9973 |
| Methods | Ref. [26] | Ref. [25] | Ref. [47] | Ours |
|---|---|---|---|---|
| Cipher | 7.9935 | 7.9972 | 7.9973 | 7.9974 |
| Images | Zelda | Einstein | Boat | Ideal | |
|---|---|---|---|---|---|
| NPCR | 99.5995 | 99.6323 | 99.5842 | 99.6094 | |
| UACI | 33.5848 | 33.4644 | 33.5536 | 33.4635 | |
| NPCR | 99.6117 | 99.6307 | 99.6155 | 99.6094 | |
| UACI | 33.4146 | 33.5056 | 33.3489 | 33.4635 | |
| NPCR | 99.5544 | 99.6002 | 99.5979 | 99.6094 | |
| UACI | 33.4352 | 33.4323 | 33.4231 | 33.4635 | |
| Images | NPCR | UACI |
|---|---|---|
| Ideal | 99.6094 | 33.4635 |
| Zelda | 99.6071 | 33.3957 |
| Einstein | 99.5941 | 33.7801 |
| Boat | 99.6300 | 33.8602 |
| Couple | 99.6506 | 33.9060 |
| Crowded | 99.5529 | 33.0163 |
| Goldhill | 99.6452 | 33.7717 |
| Flinstones | 99.6132 | 33.6949 |
| Bridge | 99.5651 | 32.9519 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, Y.-M.; Jiang, M.; Wei, D.; Deng, Y. A Novel Image Encryption Algorithm Based on Compressive Sensing and a Two-Dimensional Linear Canonical Transform. Fractal Fract. 2024, 8, 92. https://doi.org/10.3390/fractalfract8020092
Li Y-M, Jiang M, Wei D, Deng Y. A Novel Image Encryption Algorithm Based on Compressive Sensing and a Two-Dimensional Linear Canonical Transform. Fractal and Fractional. 2024; 8(2):92. https://doi.org/10.3390/fractalfract8020092
Chicago/Turabian StyleLi, Yuan-Min, Mingjie Jiang, Deyun Wei, and Yang Deng. 2024. "A Novel Image Encryption Algorithm Based on Compressive Sensing and a Two-Dimensional Linear Canonical Transform" Fractal and Fractional 8, no. 2: 92. https://doi.org/10.3390/fractalfract8020092
APA StyleLi, Y.-M., Jiang, M., Wei, D., & Deng, Y. (2024). A Novel Image Encryption Algorithm Based on Compressive Sensing and a Two-Dimensional Linear Canonical Transform. Fractal and Fractional, 8(2), 92. https://doi.org/10.3390/fractalfract8020092






