Privacy-Aware Secure Routing through Elliptical Curve Cryptography with Optimal RSU Distribution in VANETs
Abstract
1. Introduction
- Enhancing the performance of high-speed VANETs in terms of security and computational overhead is concentrated.
- Proposed a privacy-aware secure routing using elliptical curve cryptography with optimal RSU distribution to improve the performance of VANETs
- Through the elliptical curve cryptography, the trusted authority becomes highly secured, which leads to improving the authentication and confidentiality of VANETs.
- To control the computational overhead of VANETs optimal RSU distribution is performed using a Genetic Algorithm.
- Thread models such as Sybil attacks and black hole attacks are introduced to analyze the performance of the network.
2. Related Works
2.1. Optimization-Based Approaches
2.2. Security-Based Approaches
3. Basic Assumptions
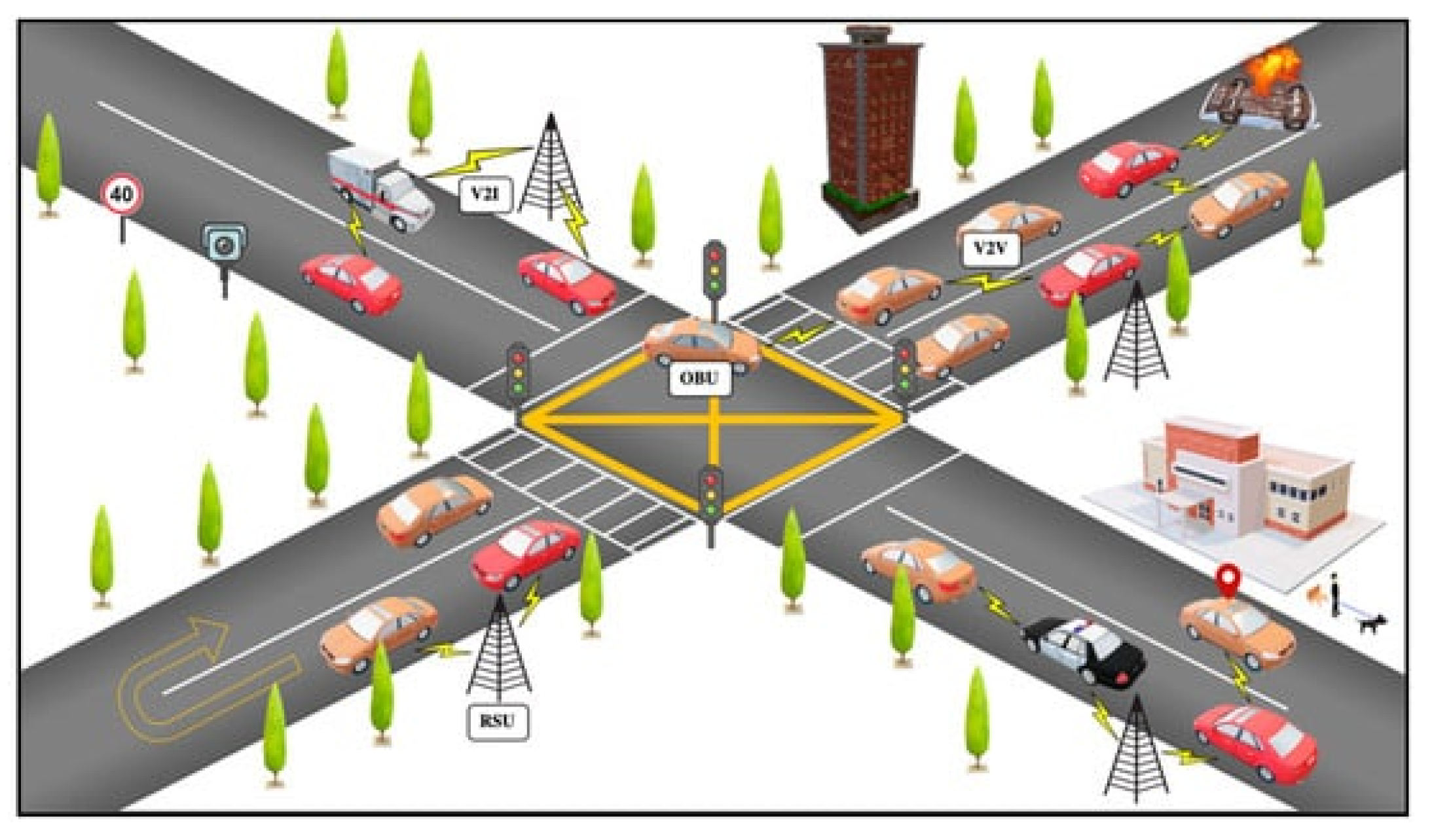
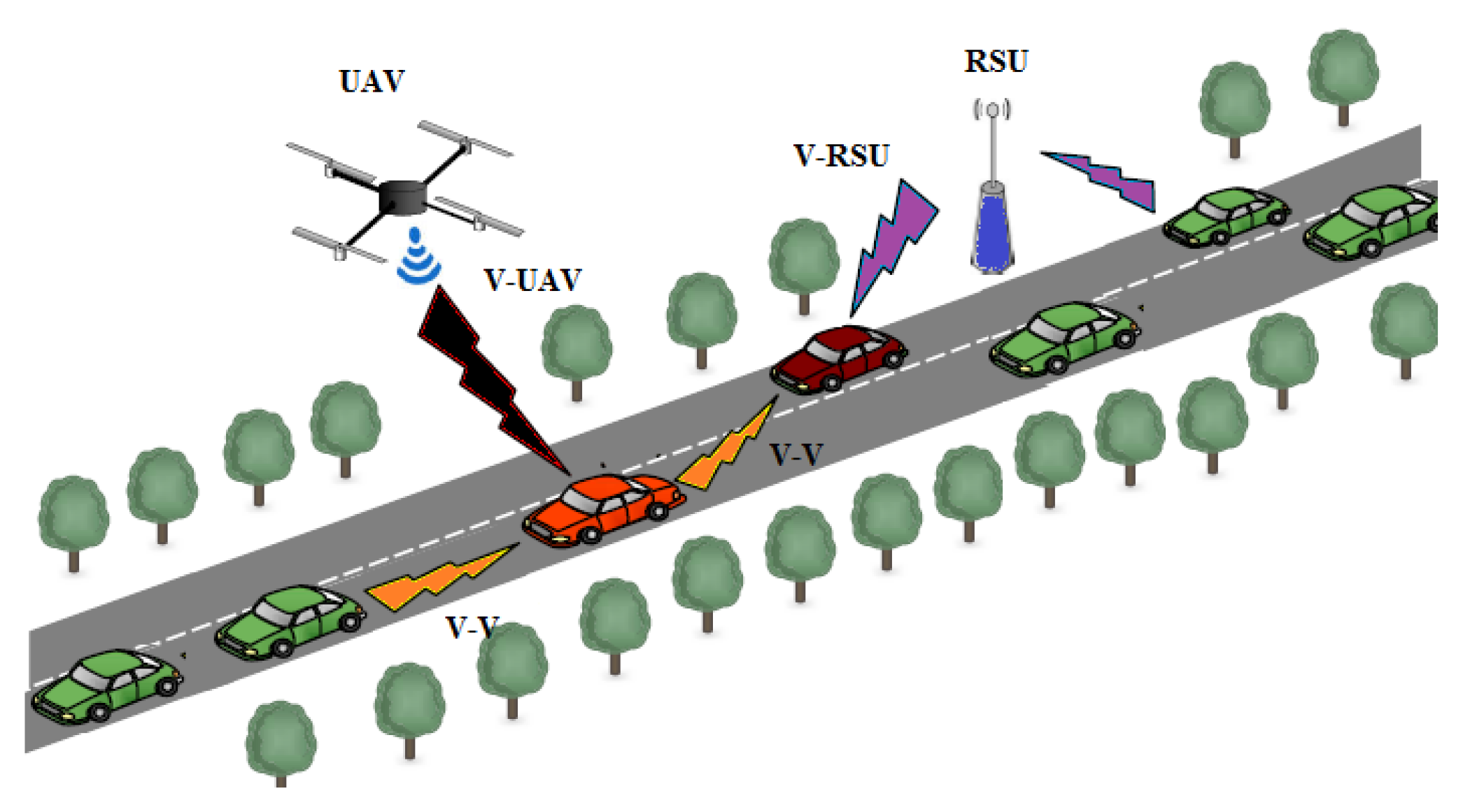
3.1. Network Model
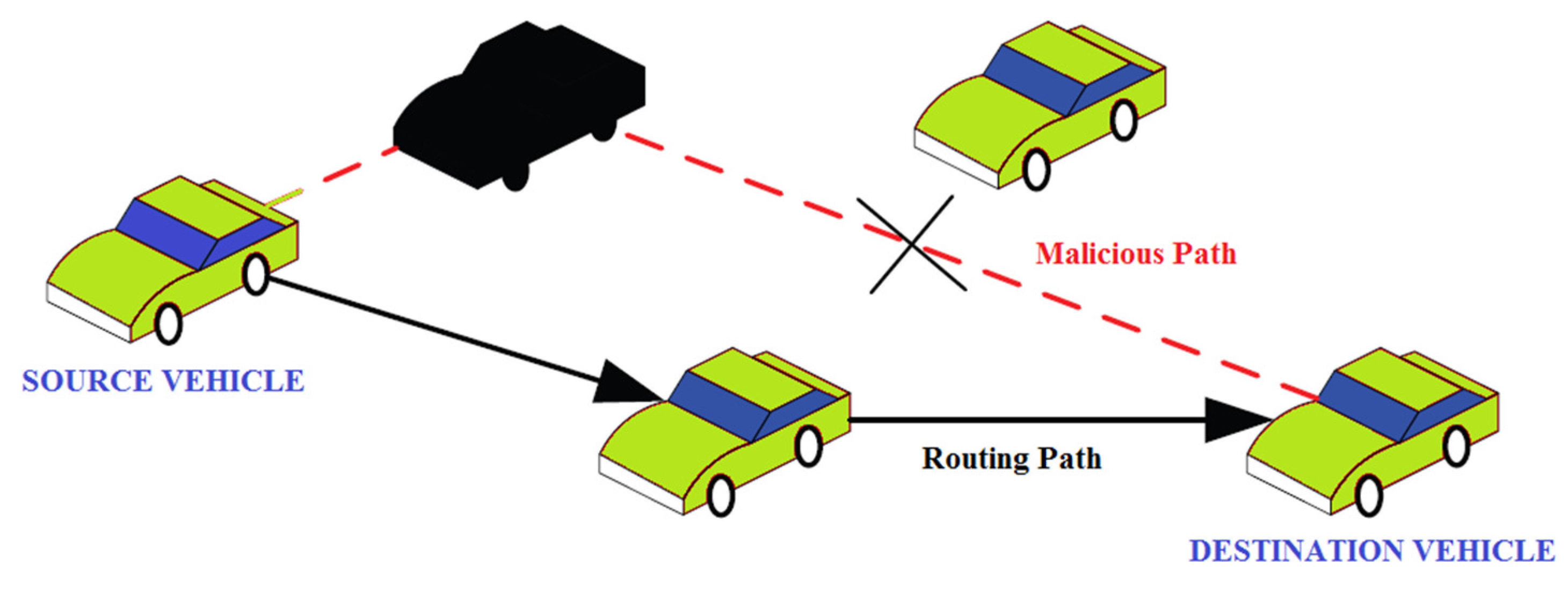
3.2. Thread Model
3.2.1. Sybil Attack
3.2.2. Black Hole Attack
3.3. Background of Elliptic Curve Cryptography (ECC) Algorithm
4. Proposed ECC-GA-PASR Approach
4.1. Genetic Algorithm (GA)-Based Optimized RSU Distribution
4.1.1. Best Road Segment Selection
- Chromosome Encoding and Estimation: To achieve a viable stream of GA [35], a string of paired unravel chromosomes is used. During the evaluation, the fitness function is calculated then Basic Safety Message (BSM) is transmitted from SVs to RSU. The process of best road segment selection is described in Figure 7.
- Phenotype and Genotype: In general, the genotype is defined as the digital data of the genetic code, and phenotype is represented as the genuine protest that acts as a visualization of the genotype.
- Fundamental Operations: After finding the initial population, the fundamental operations are taken care of, such as Selection, Crossover, and Mutation. The initial process is parent selection; here, the finest individuals from the initial population are chosen to transfer the genetic data to the subsequent generation, and then one finest individual with the highest fitness value will turn into a talented parent. Secondly, crossover operation, in this process, any two talented parents are chosen to generate a new individual. For this process, the default recombination operator is used. Finally, Mutation operation, here probabilistic mutation is conducted, and it provides diversity to the population to avoid local minimal clarification with a constant probability. The procedure in the mutation process follows genotype so as to make one alteration in each individual on average.
4.1.2. Optimal RSU Distribution
4.2. ECC-Based Authentication for the Trusted Authority (TA)

5. Simulation and Experimental Results
5.1. ECC-Based Authentication for the Trusted Authority (TA)
Result Discussion Concerning Vehicles
5.2. Performance Analysis Concerning Varying Speed
Result Discussion Concerning Varying Speed
5.3. Performance Analysis Concerning Malicious Activities
Result Discussion Concerning Malicious Activities
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Alshudukhi, J.S.; Mohammed, B.A.; Al-Mekhlafi, Z.G. Conditional Privacy-Preserving Authentication Scheme without Using Point Multiplication Operations Based on Elliptic Curve Cryptography (ECC). IEEE Access 2020, 8, 222032–222040. [Google Scholar] [CrossRef]
- Li, X.; Liu, T.; Obaidat, M.S.; Wu, F.; Vijayakumar, P.; Kumar, N. A Lightweight Privacy-Preserving Authentication Protocol for VANETs. IEEE Syst. J. 2020, 14, 3547–3557. [Google Scholar] [CrossRef]
- Al-Heety, O.S.; Zakaria, Z.; Ismail, M.; Shakir, M.M.; Alani, S.; Alsariera, H. A comprehensive survey: Benefits, Services, Recent works, Challenges, Security and Use cases for SDN-VANET. IEEE Access 2020, 8, 91028–91047. [Google Scholar] [CrossRef]
- Waqas, M.; Niu, Y.; Li, Y.; Ahmed, M.; Jin, D.; Chen, S.; Han, Z. Mobility-Aware Device-to-Device Communication: Principles, Practice and Challenges. IEEE Commun. Surv. Tutor. 2020, 22, 1863–1886. [Google Scholar] [CrossRef]
- Habelalmateen, M.I.; Ahmed, A.J.; Abbas, A.H.; Rashid, S.A. TACRP: Traffic-Aware Clustering-Based Routing Protocol for Vehicular Ad-Hoc Networks. Designs 2022, 6, 89. [Google Scholar] [CrossRef]
- Abbas, A.H.; Mansour, H.S.; Al-Fatlawi, A.H. Self-Adaptive Efficient Dynamic Multi-Hop Clustering (SA-EDMC) Approach for Improving VANET’s Performance. Int. J. Interact. Mob. Technol. 2022, 17, 136–151. [Google Scholar] [CrossRef]
- Abbas, A.H.; Ahmed, A.J.; Rashid, S.A. A Cross-Layer Approach MAC/NET with Updated-GA (MNUG-CLA)-Based Routing Protocol for VANET Network. World Electr. Veh. J. 2022, 13, 87. [Google Scholar] [CrossRef]
- Wang, P.; Liu, Y. SEMA: Secure and Efficient Message Authentication Protocol for VANETs. IEEE Syst. J. 2021, 15, 846–855. [Google Scholar] [CrossRef]
- Li, B.; Liang, R.; Zhu, D.; Chen, W.; Lin, Q. Blockchain-Based Trust Management Model for Location Privacy Preserving in VANET. IEEE Trans. Intell. Transp. Syst. 2020, 22, 3765–3775. [Google Scholar] [CrossRef]
- Lo, N.W.; Tsai, J.L. CPPA-D: Efficient Conditional Privacy-Preserving Authentication Scheme with Double-Insurance in VANETs. IEEE Trans. Veh. Technol. 2021, 70, 3456–3468. [Google Scholar]
- Jan, S.A.; Amin, N.U.; Othman, M.; Ali, M.; Umar, A.I.; Basir, A. A Survey on Privacy-Preserving Authentication Schemes in VANETs: Attacks, Challenges and Open Issues. IEEE Access 2021, 9, 153701–153726. [Google Scholar] [CrossRef]
- Nazib, R.A.; Moh, S. Reinforcement Learning-Based Routing Protocols for Vehicular Ad Hoc Networks: A Comparative Survey. IEEE Access 2021, 9, 27552–27587. [Google Scholar] [CrossRef]
- Sindhwani, M.; Singh, R.; Sachdeva, A.; Singh, C. Imprvisation of optimization technique and AODV routing protocol in VANET. Mater. Today Proc. 2022, 49, 3457–3461. [Google Scholar] [CrossRef]
- Rashid, S.A.; Alhartomi, M.; Audah, L.; Hamdi, M.M. Reliability-Aware Multi-Objective Optimization-Based Routing Protocol for VANETs Using Enhanced Gaussian Mutation Harmony Searching. IEEE Access 2022, 10, 26613–26627. [Google Scholar] [CrossRef]
- Gao, Z.; Wu, H.-C.; Cai, S.; Tan, G. Tight Approximation Ratios of Two Greedy Algorithms for Optimal RSU Deployment in One-Dimensional VANETs. IEEE Trans. Veh. Technol. 2021, 70, 3–17. [Google Scholar] [CrossRef]
- Jiang, B.; Givigi, S.N.; Delamer, J.-A. A MARL Approach for Optimizing Positions of VANET Aerial Base-Stations on a Sparse Highway. IEEE Access 2021, 9, 133989–134004. [Google Scholar] [CrossRef]
- Bello-Salau, H.; Onumanyi, A.J.; Abu-Mahfouz, A.M.; Adejo, A.O.; Mu’Azu, M.B. New Discrete Cuckoo Search Optimization Algorithms for Effective Route Discovery in IoT-Based Vehicular Ad-Hoc Networks. IEEE Access 2020, 8, 145469–145488. [Google Scholar] [CrossRef]
- Singh, G.D.; Prateek, M.; Kumar, S.; Verma, M.; Singh, D.; Lee, H.N. Hybrid Genetic Firefly Algorithm-Based Routing Protocol for VANETs. IEEE Access 2022, 10, 9142–9151. [Google Scholar] [CrossRef]
- Hossain, M.A.; Noor, R.M.; Yau, K.-L.A.; Azzuhri, S.R.; Z’Abar, M.R.; Ahmedy, I.; Jabbarpour, M.R. Multi-Objective Harris Hawks Optimization Algorithm Based 2-Hop Routing Algorithm for CR-VANET. IEEE Access 2021, 9, 58230–58242. [Google Scholar] [CrossRef]
- Khan, A.A.; Abolhasan, M.; Ni, W.; Lipman, J.; Jamalipour, A. A Hybrid-Fuzzy Logic Guided Genetic Algorithm (H-FLGA) Approach for Resource Optimization in 5G VANETs. IEEE Trans. Veh. Technol. 2019, 68, 6964–6974. [Google Scholar] [CrossRef]
- Bagga, P.; Das, A.K.; Wazid, M.; Rodrigues, J.J.; Choo KK, R.; Park, Y. On the Design of Mutual Authentication and Key Agreement Protocol in Internet of Vehicles-Enabled Intelligent Transportation System. IEEE Trans. Veh. Technol. 2021, 70, 1736–1751. [Google Scholar] [CrossRef]
- Aman, M.N.; Javaid, U.; Sikdar, B. A Privacy-Preserving and Scalable Authentication Protocol for the Internet of Vehicles. IEEE Internet Things J. 2020, 8, 1123–1139. [Google Scholar] [CrossRef]
- Yang, L.; Moubayed, A.; Shami, A. MTH-IDS: A Multi-Tiered Hybrid Intrusion Detection System for Internet of Vehicles. IEEE Internet Things J. 2021, 9, 616–632. [Google Scholar] [CrossRef]
- Zhang, J.; Yang, F.; Ma, Z.; Wang, Z.; Liu, X.; Ma, J. A Decentralized Location Privacy-Preserving Spatial Crowdsourcing for Internet of Vehicles. IEEE Trans. Intell. Transp. Syst. 2020, 22, 2299–2313. [Google Scholar] [CrossRef]
- Vangala, A.; Bera, B.; Saha, S.; Das, A.K.; Kumar, N.; Park, Y.H. Blockchain-Enabled Certificate-Based Authentication for Vehicle Accident Detection and Notification in Intelligent Transportation Systems. IEEE Sens. J. 2020, 21, 15824–15838. [Google Scholar] [CrossRef]
- Kumar, A.; Varadarajan, V.; Kumar, A.; Dadheech, P.; Choudhary, S.S.; Kumar, V.A.; Panigrahi, B.; Veluvolu, K.C. Black hole attack detection in vehicular ad-hoc network using secure AODV routing algorithm. Microprocess. Microsyst. 2021, 80, 103352. [Google Scholar] [CrossRef]
- Kudva, S.; Badsha, S.; Sengupta, S.; La, H.; Khalil, I.; Atiquzzaman, M. A scalable blockchain based trust management in VANET routing protocol. J. Parallel. Distrib. Comput. 2021, 152, 144–156. [Google Scholar] [CrossRef]
- Vasudev, H.; Deshpande, V.; Das, D.; Das, S.K. A Lightweight Mutual Authentication Protocol for V2V Communication in Internet of Vehicles. IEEE Trans. Veh. Technol. 2020, 69, 6709–6717. [Google Scholar] [CrossRef]
- Lin, X.; Wu, J.; Mumtaz, S.; Garg, S.; Li, J.; Guizani, M. Blockchain-Based On-Demand Computing Resource Trading in IoV Assisted Smart City. IEEE Trans. Emerg. Top. Comput. 2020, 9, 1373–1385. [Google Scholar] [CrossRef]
- Limbasiya, T.; Das, D.; Das, S.K. MComIoV: Secure and Energy-Efficient Message Communication Protocols for Internet of Vehicles. IEEE/ACM Trans. Netw. 2021, 29, 1349–1361. [Google Scholar] [CrossRef]
- Li, J.; Xue, Z.; Li, C.; Liu, M. RTED-SD: A Real-Time Edge Detection Scheme for Sybil DDoS in the Internet of Vehicles. IEEE Access 2021, 9, 11296–11305. [Google Scholar] [CrossRef]
- Oberoi, V. Enhancement of QoS in Security Algorithm for Blackhole Attack in VANET. In Proceedings of the 2020 IEEE Pune Section International Conference (PuneCon), Pune, India, 16–18 December 2020; pp. 33–37. [Google Scholar]
- Lyu, J.; Chen, C.; Tian, H. Secure Routing Based on Geographic Location for Resisting Blackhole Attack in Three-dimensional VANETs. In Proceedings of the 2020 IEEE/CIC International Conference on Communications in China (ICCC), Chongqing, China, 9–11 August 2020; pp. 1168–1173. [Google Scholar]
- Sharma, S.; Kaushik, B.; Rahmani, M.K.I.; Ahmed, E. Cryptographic Solution-Based Secure Elliptic Curve Cryptography Enabled Radio Frequency Identification Mutual Authentication Protocol for Internet of Vehicles. IEEE Access 2021, 9, 147114–147128. [Google Scholar] [CrossRef]
- Zhang, G.; Wu, M.; Duan, W.; Huang, X. Genetic Algorithm Based QoS Perception Routing Protocol for VANETs. Wirel. Commun. Mob. Comput. 2018, 2018, 3897857. [Google Scholar] [CrossRef]
- Sankaranarayanan, M.; Mala, C.; Mathew, S. Genetic Algorithm Based Efficient RSU Distribution to Estimate Travel Time for Vehicular Users. In Proceedings of the Second International Conference on Soft Computing and Machine Intelligence, Hong Kong, 23–24 November 2015. [Google Scholar]
- Safavat, S.; Rawat, D.B. On the Elliptic Curve Cryptography for Privacy-Aware Secure ACO-AODV Routing in Intent-Based Internet of Vehicles for Smart Cities. IEEE Trans. Intell. Transp. Syst. 2020, 22, 5050–5059. [Google Scholar] [CrossRef]

















| Ref. | Objectives | Algorithms Used | Limitations |
|---|---|---|---|
| [13] | To provide the best path selection in AODV | Improved Ant Colony Optimization in AODV | High overhead and low vehicle density |
| [14] | To provide optimization in VANETs | Reliability Aware Multi-Objective Optimization Based VANETs Routing (RAMO) and Enhanced Gaussian Mutation Harmony Searching (EGMHS) | Low throughput |
| [17] | To provide optimization and routing performance in VANETs | Two discretized variants of the Cuckoo search optimization (CSO) | Low vehicle density scenario |
| [18] | To improve the optimization of VANETs routing | Hybrid Genetic Firefly Algorithm-based Routing Protocol (HGFA) | High overhead |
| [19] | To provide traffic congestion control in VANETs | Multi-Objective Harris Hawks Optimization (2HMO-HHO) algorithm | Low vehicle density scenario |
| [20] | To create delay aware VANETs network | hybrid-fuzzy logic guided genetic algorithm (H-FLGA) approach | Packet delivery ratio and throughput are moderate |
| [21] | To improve the security, anonymity, and untraceability of the VANETs | A new mutual authentication and key agreement protocol | Throughput is moderate |
| [22] | To provide security against attacks | Physical Unclonable Functions | Low vehicle density scenario |
| [23] | To improve detection accuracy of VANETs | A multi-tiered hybrid IDS | Throughput and bandwidth are low |
| [24] | To provide security against attacks | A multi-level privacy preservation | Low vehicle density scenario |
| [25] | To improve security in VANETs | Novel blockchain-enabled certificate-based authentication scheme | Packet delivery ratio and throughput are moderate |
| [26] | To provide security to VANETs | A cryptography function-based encryption and decryption | Throughput is moderate |
| [27] | To provide security of VANETs | A two-level detection system | Low vehicle density scenario |
| Symbols | Descriptions |
|---|---|
| SV | Smart Vehicle |
| RSU | Road Side Unit |
| TA | Trusted Authority |
| RC | Remote Cloud |
| DDoS | Denial of Services |
| RoS | Rank of Service |
| SV1 | Source Smart Vehicle |
| SV2 | Destination Smart Vehicle |
| Public Keys (Bits) | In Ratio | |||
|---|---|---|---|---|
| Security (Bits) | DSA/RSA | ECC | ECC to DSA/RSA | Validity |
| 80 | 1024 | 160–223 | 1:6 | Up to 2010 |
| 112 | 2048 | 224–255 | 1:9 | Up to 2030 |
| 128 | 3037 | 256–383 | 1:12 | Beyond 2031 |
| 192 | 7680 | 384–511 | 1:20 | Beyond 2031 |
| 256 | 15,360 | 512+ | 1:30 | Beyond 2031 |
| Type | A | B | C | D |
|---|---|---|---|---|
| Momentum | 0.0 to 0.3 | 0.3 to 0.6 | 0.06 to 0.09 | 0.09 to <1.0 |
| Traffic | 900 | 1350 | 2000 | 2300 |
| Genetic Code | 0 | 1 | 0 | 1 | 1 | 0 | 1 | 1 | 1 |
| Road Division | 1 | 2 | 2 | 3 | 4 | 4 | 5 | …… | n |
| Parameters | Values |
|---|---|
| Simulator Version | NS-2.35 |
| Simulation Time | 200 ms |
| Simulation Coverage Area | 1500 × 1500 m |
| MAC interface | MAC/802.11 |
| No of Vehicles | 500 vehicles [37] |
| Malicious Vehicles | 50 Vehicles [37] |
| Network Speed | 50 to 250 (KM/Hr) [37] |
| Channel | Channel/Wireless |
| Radio Propagation Model | Two-Ray Propagation Model |
| Connections | Multiple |
| Mobility Model | Random Mobility Model |
| Antenna Type | Omni-directional Antenna |
| Queue Type | DropTail |
| Data Packet Size | 512 bytes |
| Traffic Agent Type | Transmission Control Protocol |
| Traffic Application Type | Constant Bit Rate |
| Parameters | No. Vehicles | S-AODV | ES-AODV | ECC-ACO-AODV | ECC-GA-PASR | S-AODV |
|---|---|---|---|---|---|---|
| Energy Efficiency (%) | 100 | 5.22 | 8.17 | 15.21 | 39.24 | 5.22 |
| 200 | 15.34 | 19.34 | 39.93 | 45.24 | 15.34 | |
| 300 | 28.13 | 34.71 | 52.71 | 61.76 | 28.13 | |
| 400 | 58.47 | 61.74 | 81.25 | 88.76 | 58.47 | |
| 500 | 76.46 | 82.46 | 88.78 | 95.17 | 76.46 | |
| Packet Delivery Ratio (%) | 100 | 5.24 | 8.76 | 11.44 | 15.93 | 5.24 |
| 200 | 18.44 | 25.33 | 31.64 | 38.33 | 18.44 | |
| 300 | 38.28 | 45.76 | 51.38 | 59.48 | 38.28 | |
| 400 | 58.24 | 65.13 | 71.25 | 78.76 | 58.24 | |
| 500 | 75.18 | 82.19 | 88.17 | 98.28 | 75.18 | |
| Overhead (packets) | 100 | 1028 | 964 | 527 | 56 | 1028 |
| 200 | 1537 | 1264 | 857 | 128 | 1537 | |
| 300 | 2186 | 1537 | 1128 | 248 | 2186 | |
| 400 | 2968 | 2046 | 1538 | 358 | 2968 | |
| 500 | 3586 | 2578 | 1867 | 486 | 3586 | |
| Packet Loss (packets) | 100 | 196 | 145 | 96 | 64 | 196 |
| 200 | 329 | 221 | 146 | 105 | 329 | |
| 300 | 419 | 347 | 247 | 145 | 419 | |
| 400 | 528 | 428 | 317 | 196 | 528 | |
| 500 | 658 | 589 | 386 | 246 | 658 |
| Parameters | Speed | S-AODV | ES-AODV | ECC-ACO-AODV | ECC-GA-PASR | S-AODV |
|---|---|---|---|---|---|---|
| Energy Efficiency (%) | 50 | 75.16 | 81.25 | 88.96 | 99.85 | 75.16 |
| 100 | 72.49 | 78.23 | 88.15 | 98.81 | 72.49 | |
| 150 | 65.39 | 76.89 | 87.25 | 97.25 | 65.39 | |
| 200 | 61.23 | 71.28 | 6.17 | 97.56 | 61.23 | |
| 250 | 55.78 | 65.23 | 85.13 | 96.28 | 55.78 | |
| Packet Delivery Ratio (%) | 50 | 76.18 | 81.26 | 89.13 | 98.17 | 76.18 |
| 100 | 71.89 | 80.56 | 87.47 | 98.18 | 71.89 | |
| 150 | 65.24 | 79.17 | 85.01 | 97.16 | 65.24 | |
| 200 | 59.27 | 75.46 | 81.13 | 97.02 | 59.27 | |
| 250 | 55.47 | 65.23 | 75.16 | 96.25 | 55.47 | |
| Overhead (packets) | 50 | 1246 | 964 | 429 | 56 | 1246 |
| 100 | 1934 | 1426 | 758 | 128 | 1934 | |
| 150 | 2571 | 1967 | 1025 | 215 | 2571 | |
| 200 | 3467 | 2864 | 1438 | 358 | 3467 | |
| 250 | 4278 | 3587 | 1868 | 458 | 4278 | |
| Packet Loss (packets) | 50 | 434 | 386 | 128 | 62 | 434 |
| 100 | 587 | 474 | 217 | 118 | 587 | |
| 150 | 715 | 628 | 346 | 147 | 715 | |
| 200 | 864 | 794 | 458 | 196 | 864 | |
| 250 | 945 | 857 | 578 | 254 | 945 |
| Parameters | Malicious Vehicle | S-AODV | ES-AODV | ECC-ACO-AODV | ECC-GA-PASR | S-AODV |
|---|---|---|---|---|---|---|
| Energy Efficiency (%) | 0 | 78.46 | 81.46 | 92.47 | 99.99 | 78.46 |
| 10 | 72.48 | 79.17 | 90.47 | 98.45 | 72.48 | |
| 20 | 68.17 | 75.47 | 88.27 | 97.26 | 68.17 | |
| 30 | 65.17 | 71.25 | 87.26 | 97.13 | 65.17 | |
| 40 | 60.41 | 65.49 | 85.46 | 96.28 | 60.41 | |
| 50 | 55.23 | 60.28 | 83.74 | 95.34 | 55.23 | |
| Packet Delivery Ratio (%) | 0 | 79.13 | 83.79 | 92.76 | 99.95 | 79.13 |
| 10 | 75.46 | 79.17 | 88.26 | 98.46 | 75.46 | |
| 20 | 68.24 | 75.23 | 87.49 | 98.12 | 68.24 | |
| 30 | 61.21 | 71.22 | 86.28 | 97.96 | 61.21 | |
| 40 | 52.76 | 68.29 | 85.74 | 97.21 | 52.76 | |
| 50 | 45.49 | 63.77 | 84.21 | 97.03 | 45.49 | |
| Overhead(packets) | 0 | 1567 | 1056 | 754 | 43 | 1567 |
| 10 | 2167 | 1536 | 965 | 102 | 2167 | |
| 20 | 2967 | 2134 | 1086 | 146 | 2967 | |
| 30 | 3867 | 2567 | 1524 | 168 | 3867 | |
| 40 | 4538 | 3289 | 1856 | 186 | 4538 | |
| 50 | 4937 | 3674 | 2286 | 209 | 4937 | |
| Packet Loss(packets) | 0 | 156 | 102 | 56 | 23 | 156 |
| 10 | 201 | 146 | 102 | 86 | 201 | |
| 20 | 286 | 206 | 143 | 91 | 286 | |
| 30 | 361 | 294 | 167 | 125 | 361 | |
| 40 | 412 | 356 | 186 | 154 | 412 | |
| 50 | 496 | 379 | 201 | 169 | 496 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Shayea, G.G.; Mohammed, D.A.; Abbas, A.H.; Abdulsattar, N.F. Privacy-Aware Secure Routing through Elliptical Curve Cryptography with Optimal RSU Distribution in VANETs. Designs 2022, 6, 121. https://doi.org/10.3390/designs6060121
Shayea GG, Mohammed DA, Abbas AH, Abdulsattar NF. Privacy-Aware Secure Routing through Elliptical Curve Cryptography with Optimal RSU Distribution in VANETs. Designs. 2022; 6(6):121. https://doi.org/10.3390/designs6060121
Chicago/Turabian StyleShayea, Ghadeer Ghazi, Dheyaa Abdulameer Mohammed, Ali Hashim Abbas, and Nejood Faisal Abdulsattar. 2022. "Privacy-Aware Secure Routing through Elliptical Curve Cryptography with Optimal RSU Distribution in VANETs" Designs 6, no. 6: 121. https://doi.org/10.3390/designs6060121
APA StyleShayea, G. G., Mohammed, D. A., Abbas, A. H., & Abdulsattar, N. F. (2022). Privacy-Aware Secure Routing through Elliptical Curve Cryptography with Optimal RSU Distribution in VANETs. Designs, 6(6), 121. https://doi.org/10.3390/designs6060121







