Dynamical Analysis and Optimal Control for a SEIR Model Based on Virus Mutation in WSNs
Abstract
:1. Introduction
1.1. Research Background
1.2. Related Work
1.3. Contributions
- An SEIR model based on virus mutation is established to describe the propagation process of mutated virus in WSNs.
- Calculating the basic reproduction number R0 of the improved model by the next generation matrix method. Besides, the local and global stability of the two equilibria are proved and simulated by the Routh criterion and the Lyapunov stability method. Moreover, the influence of the repair rate γ1 and γ2 on the basic reproduction number is also revealed in the simulation part.
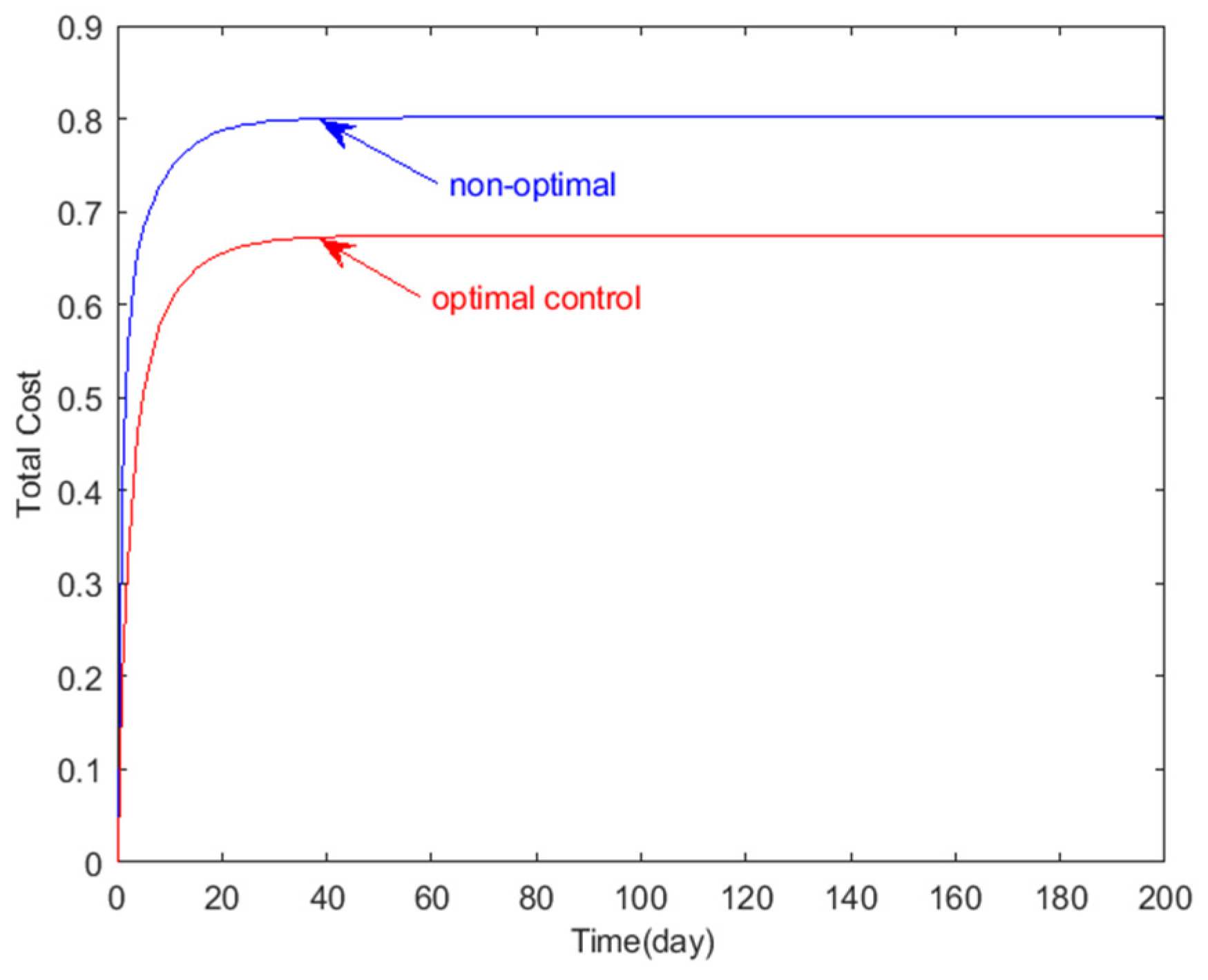
- Based on the Pontryagin maximum principle, the optimal control variable pairs of the repair ratio of infected nodes and the repair ratio of mutated infected nodes are obtained. The simulation results show that the optimal control strategy ensures the security of wireless sensor networks and minimizes the maintenance cost.
2. Modeling
2.1. Dynamic Equation
2.2. Calculation of the Equilibrium Point and the Basic Reproduction Number
3. Dynamic Analysis and Optimal Strategy
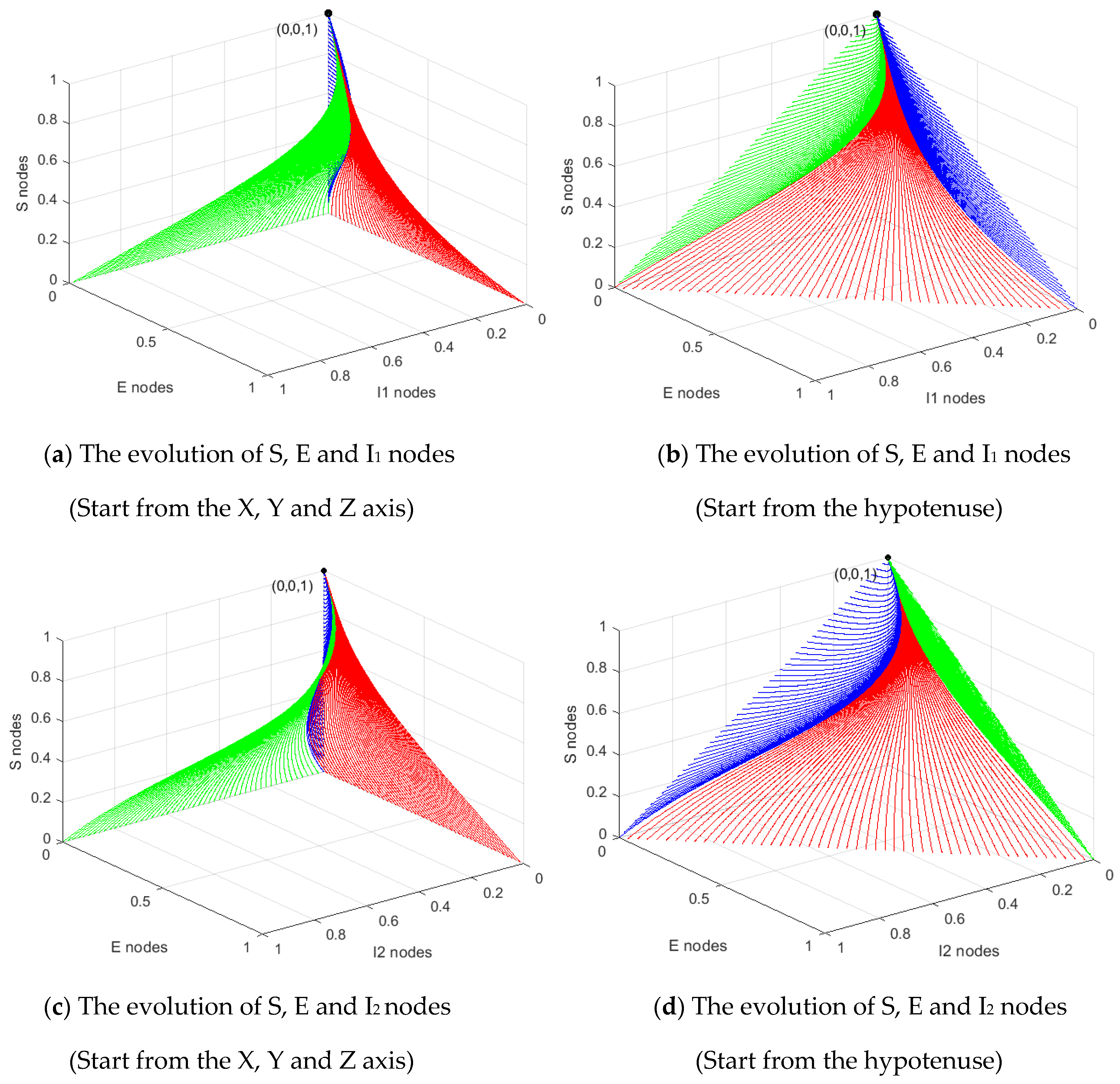
3.1. Subs Stability Analysis of P0
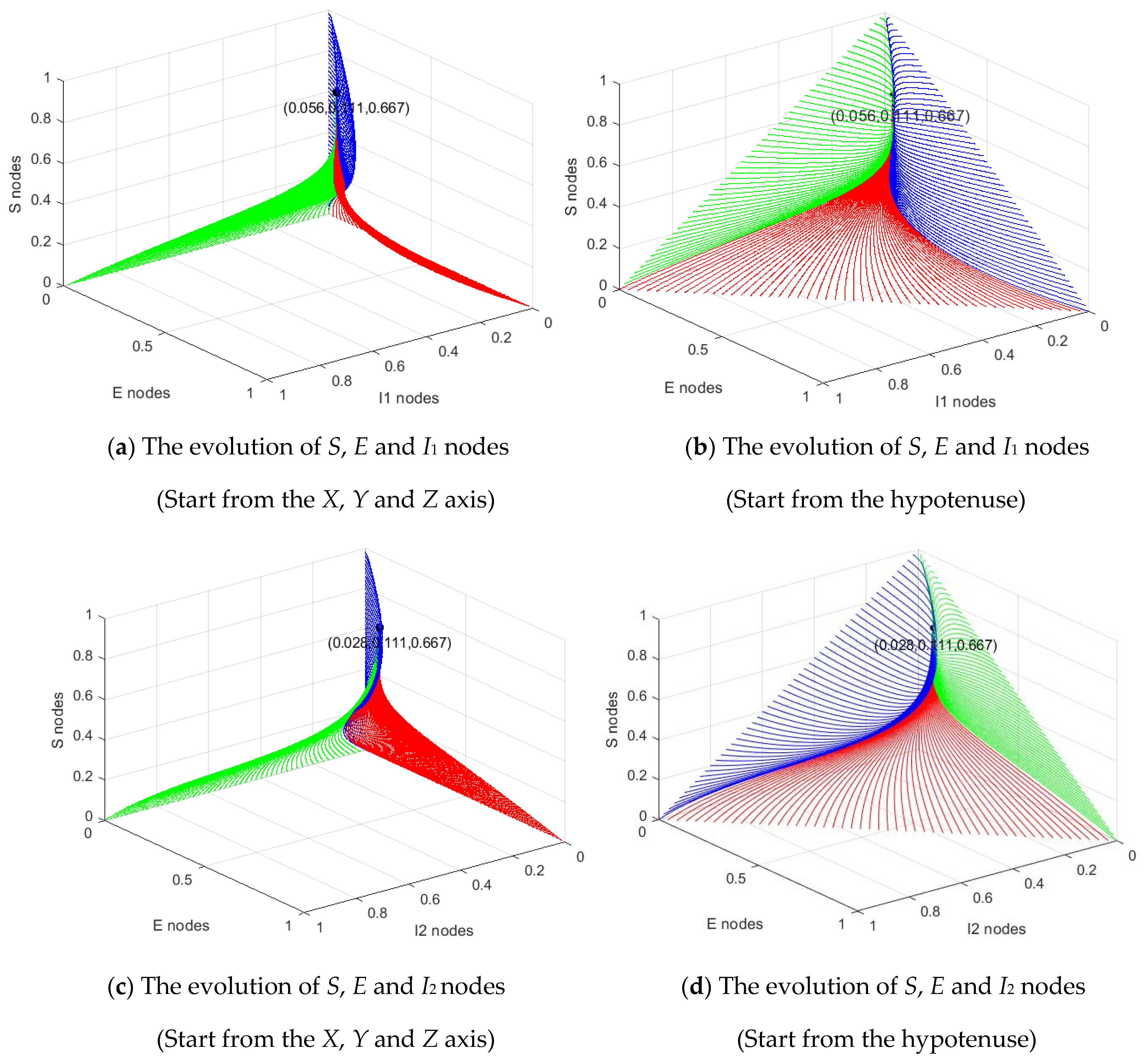
3.2. Stability Analysis of P*
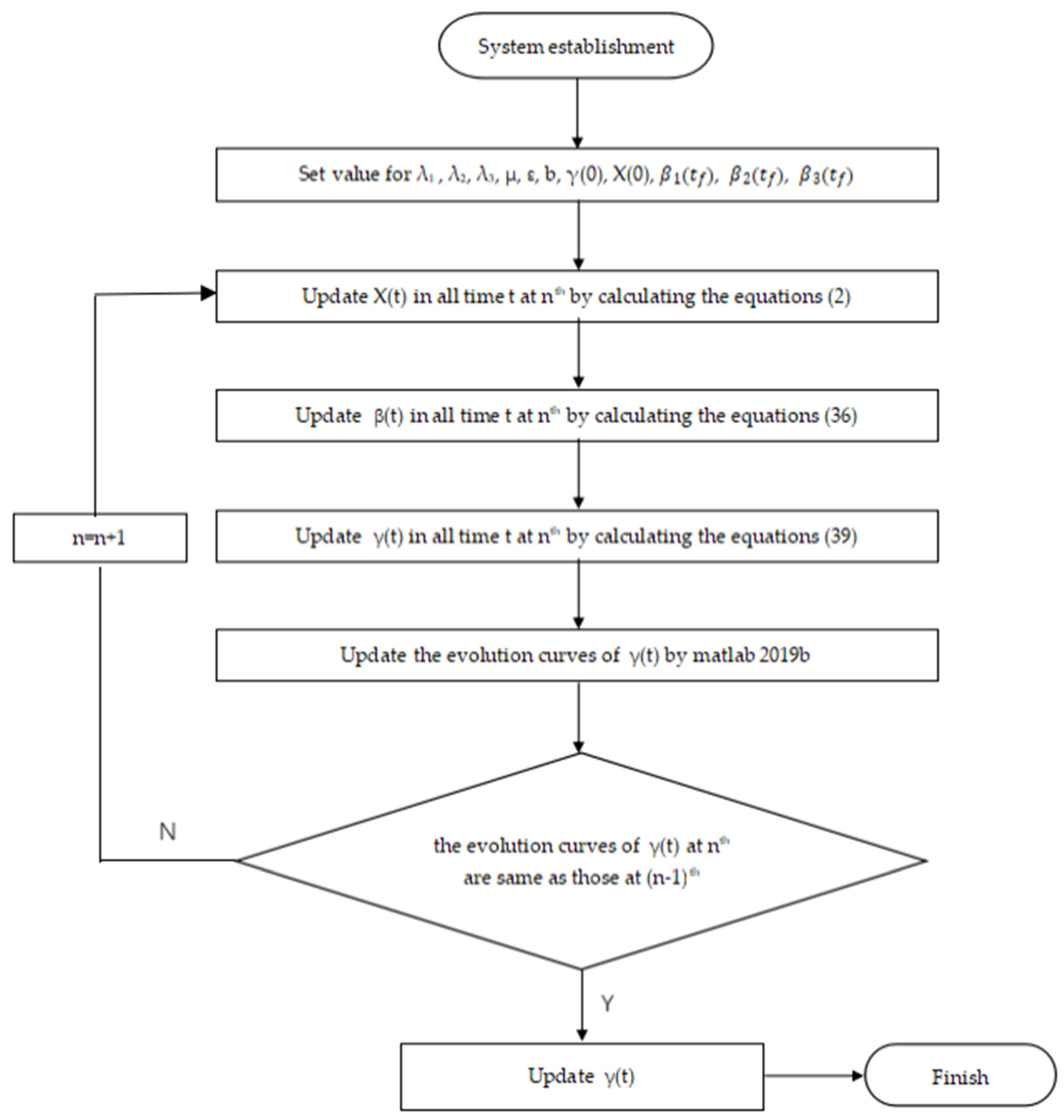
3.3. Optimal Strategy
4. Simulation
4.1. Stable Analysis of Disease-Free Equilibrium
4.2. Stable Analysis of Epidemic Equilibrium
4.3. Optimal Control
4.3.1. Evolution of Sensor Nodes
4.3.2. Total Cost and Control Variables
4.3.3. Influence of Control Variables on the Basic Reproduction Number R0
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Akyildiz, I.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar] [CrossRef] [Green Version]
- Liang, C.-J.M.; Musăloiu, E.R.; Terzis, A. Typhoon: A reliable data dissemination protocol for wireless sensor networks. In Wireless Sensor Networks; Verdone, R., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 4913, pp. 268–285. [Google Scholar]
- Lenin, R.B.; Ramaswamy, S. Performance analysis of wireless sensor networks using queuing networks. Ann. Oper. Res. 2013, 233, 237–261. [Google Scholar] [CrossRef]
- Rashid, B.; Rehmani, M.H. Applications of wireless sensor networks for urban areas: A survey. J. Netw. Comput. Appl. 2016, 60, 192–219. [Google Scholar] [CrossRef]
- Rasheed, A.; Mahapatra, R.N. The three-tier security scheme in wireless sensor networks with mobile sinks. IEEE Trans. Parallel Distrib. Syst. 2010, 23, 958–965. [Google Scholar] [CrossRef]
- Reina, D.; Toral, S.; Johnson, P.; Barrero, F. A survey on probabilistic broadcast schemes for wireless ad hoc networks. Ad Hoc Netw. 2015, 25, 263–292. [Google Scholar] [CrossRef] [Green Version]
- De, P.; Liu, Y.; Das, S. An epidemic theoretic framework for vulnerability analysis of broadcast protocols in wireless sensor networks. IEEE Trans. Mob. Comput. 2008, 8, 413–425. [Google Scholar] [CrossRef]
- Zanero, S. Wireless malware propagation: A reality check. IEEE Secur. Priv. Mag. 2009, 7, 70–74. [Google Scholar] [CrossRef]
- Yan, G.; Eidenbenz, S. Modeling propagation dynamics of bluetooth worms (extended version). IEEE Trans. Mob. Comput. 2008, 8, 353–368. [Google Scholar] [CrossRef]
- Agapow, P.M. Computational brittleness and the evolution of computer viruses. In International Conference on Parallel Problem Solving from Nature; Springer: Berlin/Heidelberg, Germany, 1996; pp. 1–11. [Google Scholar]
- Jia, X.; Xiong, X.; Jing, J.; Liu, P. Using purpose capturing signatures to defeat computer virus mutating. In International Conference on Information Security Practice and Experienceeless; Springer: Berlin/Heidelberg, Germany, 2010; pp. 153–171. [Google Scholar]
- Li, D.; Li, C.; Xu, Y. The stability of a class of SEIR epidemic model with virus mutate. Harbin Sci. Technol. 2014, 19, 106–109. [Google Scholar]
- Gao, J.; Zhang, T. Analysis on an SEIR epidemic model with logistic death rate of virus mutation. J. Math. Res. Appl. 2019, 39, 43–52. [Google Scholar]
- Rui, M.; Youping, Y. Global dynamics of an avian influenza A(H7N9) epidemic model with latent period and nonlinear recovery rate. Comput. Math. Methods Med. 2018, 2018, 1–11. [Google Scholar]
- Yang, Y. Viral dynamics of an HIV model with pulse antiretroviral therapy and adherence. J. Nonlinear Sci. Appl. 2018, 11, 516–528. [Google Scholar] [CrossRef]
- Kephart, J.; White, S. Directed-graph epidemiological models of computer viruses. In Proceedings of the 1991 IEEE Computer Society Symposium on Research in Security and Privacy, Oakland, CA, USA, 20–22 May 1991. [Google Scholar]
- Kephart, J.; White, S. Measuring and modeling computer virus prevalence. In Proceedings of the 1993 IEEE Computer Society Symposium on Research in Security and Privacy, Oakland, CA, USA, 24–26 May 1993. [Google Scholar]
- Murray, W. The application of epidemiology to computer viruses. Comput. Secur. 1988, 7, 139–145. [Google Scholar] [CrossRef]
- Newman, M.E.J. Spread of epidemic disease on networks. Phys. Rev. E 2002, 66, 016128. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Tang, S.; Mark, B.L. Analysis of virus spread in wireless sensor networks: An epidemic model. In Proceedings of the 2009 7th International Workshop on Design of Reliable Communication Networks, Washington, DC, USA, 25–28 October 2009; pp. 86–91. [Google Scholar] [CrossRef] [Green Version]
- Mishra, B.K.; Keshri, N. Mathematical model on the transmission of worms in wireless sensor network. Appl. Math. Model. 2013, 37, 4103–4111. [Google Scholar] [CrossRef]
- Mishra, B.K.; Srivastava, S.K. A quarantine model on the spreading behavior of worms in wireless sensor network. Trans. IoT Cloud Comput. 2014, 2, 1–12. [Google Scholar]
- Zizhen, Z. Dynamics of an epidemic model of computer virus with delays. J. Zhejiang Univ. Ed. 2015, 42, 677–686. [Google Scholar]
- Srivastava, P.K.; Ojha, R.P.; Sharma, K.; Awasthi, S.; Sanyal, G.; Sanya, G. Effect of quarantine and recovery on infectious nodes in wireless sensor network. Int. J. Sens. Wirel. Commun. Control. 2018, 8, 26–36. [Google Scholar] [CrossRef]
- Mishra, B.K.; Tyagi, I. Defending against malicious threats in wireless sensor network: A mathematical model. Int. J. Inf. Technol. Comput. Sci. 2014, 6, 12–19. [Google Scholar] [CrossRef] [Green Version]
- Zhu, L.; Zhao, H. Dynamical analysis and optimal control for a malware propagation model in an information network. Neurocomputing 2015, 149, 1370–1386. [Google Scholar] [CrossRef]
- Batista, F.K.; Del Rey, A.M.; Queiruga-Dios, A. A new individual-based model to simulate malware propagation in wireless sensor networks. Mathematics 2020, 8, 410. [Google Scholar] [CrossRef] [Green Version]
- Huang, D.-W.; Yang, L.-X.; Yang, X.; Wu, Y.; Tang, Y.Y. Towards understanding the effectiveness of patch injection. Phys. A Stat. Mech. Its Appl. 2019, 526, 120956. [Google Scholar] [CrossRef]
- Zhang, Z.; Kundu, S.; Wei, R. A delayed epidemic model for propagation of malicious codes in wireless sensor network. Mathematics 2019, 7, 396. [Google Scholar] [CrossRef] [Green Version]
- Liu, G.; Peng, B.; Zhong, X.; Lan, X. Differential Games of Rechargeable Wireless Sensor Networks against Malicious Programs Based on SILRD Propagation Model. Complexity 2020, 2020, 5686413. [Google Scholar] [CrossRef]
- Zhu, L.; Zhou, M.; Zhang, Z. Dynamical analysis and control strategies of rumor spreading models in both homogeneous and heterogeneous networks. J. Nonlinear Sci. 2020, 30, 1–32. [Google Scholar] [CrossRef]
- Ojha, R.P.; Srivastava, P.K.; Sanyal, G.; Gupta, N. Improved model for the stability analysis of wireless sensor network against malware attacks. Wirel. Pers. Commun. 2021, 116, 2525–2548. [Google Scholar] [CrossRef]
- Shen, S.; Zhou, H.; Feng, S.; Liu, J.; Zhang, H.; Cao, Q. An epidemiology-based model for disclosing dynamics of malware propagation in heterogeneous and mobile WSNs. IEEE Access 2020, 8, 43876–43887. [Google Scholar] [CrossRef]
- Schöneburg, E. Neural networks hunt computer viruses. Neurocomputing 1991, 2, 243–248. [Google Scholar] [CrossRef]
- Rad, B.B. Metamorphic Computer Virus Detection: Using Hidden Markov Model; LAP Lambert: Saarbrücken, Germany, 2016; p. 276. [Google Scholar]
- Liu, G.; Peng, B.; Zhong, X.; Cheng, L.; Li, Z. Attack-Defense Game between Malicious Programs and Energy-Harvesting Wireless Sensor Networks Based on Epidemic Modeling. Complexity 2020, 2020, 3680518. [Google Scholar] [CrossRef]
- Guillén, J.D.H.; Del Rey, Á.M.; Vara, R.C. On the optimal control of a malware propagation model. Mathematics 2020, 8, 1518. [Google Scholar] [CrossRef]
- Marinoschi, G. Identification and control of SARS-CoV-2 epidemic model parameters. arXiv 2009, arXiv:2009.13470. [Google Scholar]
- Khouzani, M.H.R.; Sarkar, S. Maximum damage battery depletion attack in mobile sensor networks. IEEE Trans. Autom. Control. 2011, 56, 2358–2368. [Google Scholar] [CrossRef] [Green Version]
- Liu, G.; Peng, B.; Zhong, X. A novel epidemic model for wireless rechargeable sensor network security. Sensors 2020, 21, 123. [Google Scholar] [CrossRef] [PubMed]
- Huang, Y.; Zhu, Q. A Differential game approach to decentralized virus-resistant weight adaptation policy over complex networks. IEEE Trans. Control Netw. Syst. 2019, 7, 944–955. [Google Scholar] [CrossRef] [Green Version]
- Liu, G.; Peng, B.; Zhong, X. Epidemic Analysis of Wireless Rechargeable Sensor Networks Based on an Attack–Defense Game Model. Sensors 2021, 21, 594. [Google Scholar] [CrossRef]
- Lyapunov, A.M. The general problem of the stability of motion. Int. J. Control 1992, 55, 531–534. [Google Scholar] [CrossRef]
- Gubar, E.; Taynitskiy, V.; Zhu, Q. Optimal control of heterogeneous mutating viruses. J. Games 2018, 9, 103. [Google Scholar] [CrossRef] [Green Version]
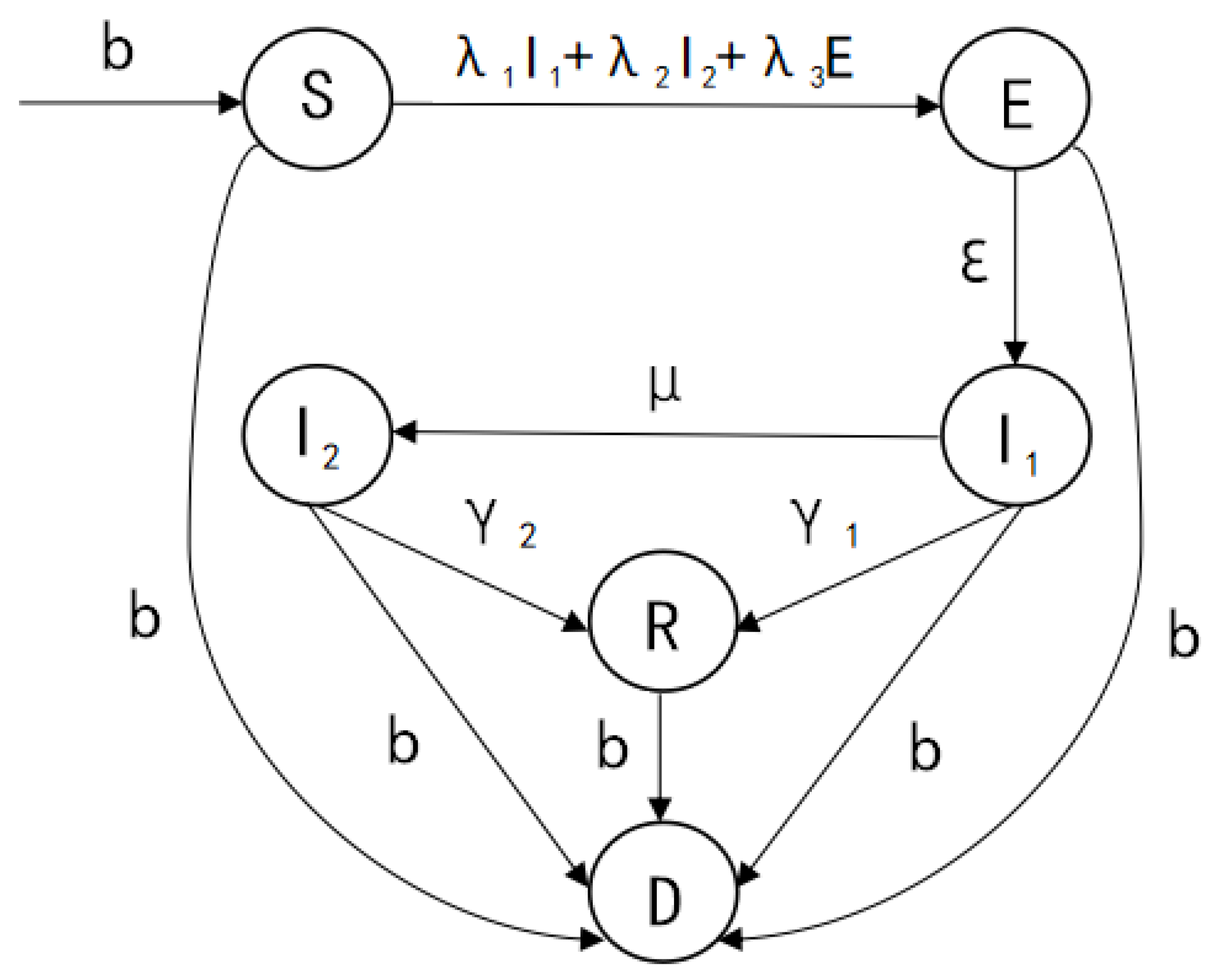




| Symbol | Description |
|---|---|
| b | Birth rate or Death rate |
| λ1 | Transmission rate of I1 nodes |
| λ2 | Transmission rate of I2 nodes |
| λ3 | Transmission rate of E nodes |
| ε | Probability at which E nodes are converted to I1 nodes |
| μ | Probability of virus mutation |
| γ1 | Repair rate of I1 nodes |
| γ2 | Repair rate of I2 nodes |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, G.; Chen, J.; Liang, Z.; Peng, Z.; Li, J. Dynamical Analysis and Optimal Control for a SEIR Model Based on Virus Mutation in WSNs. Mathematics 2021, 9, 929. https://doi.org/10.3390/math9090929
Liu G, Chen J, Liang Z, Peng Z, Li J. Dynamical Analysis and Optimal Control for a SEIR Model Based on Virus Mutation in WSNs. Mathematics. 2021; 9(9):929. https://doi.org/10.3390/math9090929
Chicago/Turabian StyleLiu, Guiyun, Jieyong Chen, Zhongwei Liang, Zhimin Peng, and Junqiang Li. 2021. "Dynamical Analysis and Optimal Control for a SEIR Model Based on Virus Mutation in WSNs" Mathematics 9, no. 9: 929. https://doi.org/10.3390/math9090929
APA StyleLiu, G., Chen, J., Liang, Z., Peng, Z., & Li, J. (2021). Dynamical Analysis and Optimal Control for a SEIR Model Based on Virus Mutation in WSNs. Mathematics, 9(9), 929. https://doi.org/10.3390/math9090929







