Abstract
The CRT-RSA cryptosystem is the most widely adopted RSA variant in digital applications. It exploits the properties of the Chinese remainder theorem (CRT) to elegantly reduce the size of the private keys. This significantly increases the efficiency of the RSA decryption algorithm. Nevertheless, an attack on RSA may also be applied to this RSA variant. One of the attacks is called partially known private key attack, that relies on the assumption that the adversary has knowledge of partial bits regarding RSA private keys. In this paper, we mount this type of attack on CRT-RSA. By using partial most significant bits (MSBs) of one of the RSA primes, p or q and its corresponding private exponent, d, we obtain an RSA intermediate. The intermediate is derived from and RSA public key, e. The analytical and novel reason on the success of our attack is that once the adversary has obtained the parameters: approximation of private exponent , approximation of p, and the public exponent e where where such that and has determined the largest prime of , it will enable the adversary to factor the RSA modulus . Although the parameter space to find the prime factor is large, we show that one can adjust its “success appetite” by applying prime-counting function properties. By comparing our method with contemporary partial key attacks on CRT-RSA, upon determining a suitable predetermined “success appetite” value, we found out that our method required fewer bits of the private keys in order to factor N.
1. Introduction
RSA algorithm is known as one of the earliest public-key cryptosystems, introduced in 1977 [1]. However, its practical applications multiply in numbers with the coming of the digital age that requires swift key transportation mechanism to establish secure communication, either by encrypting a key or verifying a digital certificate. To ensure the encryption (or signing) and decryption (or verification) of RSA works, an RSA modulus is introduced where and . To encrypt or sign, an RSA public exponent, e is required such that it satisfies where is Euler’s totient function. To decrypt or verify, an RSA private exponent, d is required such that it satisfies the RSA key equation,
One of the hard mathematical problems that become the sources of security for RSA is embedded in N and called an integer factorization problem. Since p and q are very large n-bit primes (typically ), the best current algorithm to factor N is still running in sub-exponential times using a method called general number field sieve [2]. Therefore, no modern computers yet can threaten the security of RSA.
As RSA algorithms need to be flexible and meet the demands of their applications, a lot of RSA variants have been introduced over the years. In this paper, we focus on a variant of RSA called Chinese remainder theorem (CRT) RSA cryptosystem [3]. This variant applies the result from the Chinese remainder theorem by utilizing two private exponents, and , instead of a single private exponent in standard RSA. These private exponents are derived from the original d with respect to its corresponding RSA primes, p and q. The addition in numbers of private exponents in CRT-RSA may require additional modular exponentiations, but the computations in CRT-RSA are significantly faster compared to the computations in standard RSA, since and are significantly smaller in size compared to the original d [4]. Due to this speed up, CRT-RSA is ubiquitous in many cryptographic implementations today.
For the past attacks on RSA and its variants to be successful, an adversary needs to gain certain advantages. One of the advantages is that the adversary knows partial bits of RSA private parameters, d and p and/or q. The bits may be derived from their most significant bits (MSBs) or least significant bits (LSBs). This assumption is realistic since there is a method called side-channel attacks that is helpful to retrieve certain bits of parameters from cryptographic devices [5].
Using the partially known bits, an adversary can conduct an attack called partial key exposure attack. This kind of attack initially was executed on a standard RSA cryptosystem by [6], where they showed that bits of p or q are required to factor N using an integer programming technique. Then, Ref. [7] reduced the required value of bits to using the LLL algorithm. This method utilizes a lattice-based approach to find the small solution of polynomials modulo N that consequently results in the factorization of N. It then proliferated other partial key exposure attacks on standard RSA cryptosystem [8,9,10]. For the collection of this type of attack on standard RSA cryptosystem, refer to [11].
In 2003, Ref. [12] showed that partial key exposure attack can also be conducted on CRT-RSA. Given an approximation , called , that has half of the MSBs of , they showed that factorization of N can be solved easily. Particularly, satisfies within the CRT-RSA key equation, and given such that for some that satisfy where e is the public exponent of CRT-RSA, then N can be factored in polynomial time. It then can be generalized to if e is very small, which occurs greatly in most implementations. This result utilized an approach using lattice-based approximation which has been extended in [13,14,15].
Another method of attacking CRT-RSA is using a key reconstruction algorithm by [16]. The method is motivated by the capability of a newly introduced side-channel attack called cold boot attacks [17]. It systematically constructs bits of RSA private keys namely RSA private exponent and RSA primes from any random bit positions as its initial point. The method only requires at least 0.27 bits from any bit position of . If this condition is fulfilled, then the adversary can solve the factorization of N in polynomial time using the lattice-based method. In more recent work, Ref. [18] proposed an improvement of past attacks by showing an attack that requires less amount of leaked MSBs for all . The attack can be conducted by selecting better lattice constructions of the underlying polynomials created from the obtained partial information.
Our contribution. We take a novel approach in conducting partial key exposure attack on CRT-RSA by proving that by knowing the largest prime factor of called , N can be factored in polynomial time if the conditions on the approximations of and p are satisfied. We also extend this result by showing the difficulties of finding can be reduced by having sufficient combinations of computing power and success appetites.
Organization of the article. In Section 2, we show the CRT-RSA key generation algorithm in its full form. We also introduce a certain theorem, definition and lemmas that will be utilized in our attack. In Section 3, we introduce our attack by parts. First, we show the conditions required to conduct our attack. Then, we proceed with the attack by proving that by knowing the largest prime factor of called , our attack can factor N in polynomial time using conditions from the first part of the attack. In Section 4, we estimate the number of primes that can be the candidates for the largest prime factor of using a theorem provided before. Then, in Section 5, we estimate the number of primes that can be the candidates for the largest prime factor of if based on various success appetites which have been pre-defined. By using this estimation, we discuss our method compared to other methods that attacked CRT-RSA in Section 6 before we finally conclude our paper in Section 7.
2. Preliminaries
One of the earliest variations of the RSA cryptosystem is to decrypt the plaintext using Chinese remainder theorem or CRT (more on CRT can be read here [19]). This variant, called CRT-RSA, is proposed by the creators of RSA in their patent application [3]. The rationale of using the concept is to utilize much smaller parameter size in the decryption algorithm specifically during computing the modular exponentiation computation. As we shall see, in Algorithm 1, the key generation algorithm of CRT-RSA employs almost similar computations compared to the standard process. However, the difference lies in additional computations of
and
which we called CRT exponents as in Algorithm 1 (line 5 and line 6). The CRT-RSA key generation algorithm is as follows:
| Algorithm 1 Chinese remainder theorem (CRT)-RSA Key Generation Algorithm |
| Input: Security parameter, n |
| Output: RSA public keys , and RSA private keys |
|
In this paper, supposing , we assume that the adversary is given a fraction of the MSBs of and p (or q). We shall see that by having this information, the adversary can derive an important intermediate that allows us to find d in polynomial time, thus factoring N in polynomial time. However, to find the greatest prime factor of the intermediate that can enable our attack, we need to count the number of primes that can be the suitable candidates for our greatest prime factor. To achieve that, we need to utilize the prime counting function as follows: (See [20], (Theorem 6.9)).
Theorem 1.
Let be a function estimating number of primes . Then
for .
After the adversary can count the number of primes that can be the suitable candidates for our greatest prime factor, the adversary need to know the probability of finding the prime in a known parameter space. This probability will help the adversary to adjust the success appetite of the attack and consequently determine whether the attack is feasible, based on the computational ability of the adversary. To estimate the probability, we require an application of the prime number theorem called Dickman’s function. Given a real number value, this function computes the probability of the greatest prime factor of an integer to be less than the given value. We call this function a Dickman’s function [21,22] and it is defined as below:
Definition 1
(Dickman’s function). The probability function that a random integer between 1 and N will have its greatest prime factor less than is defined through the integral equation
for .
Dickman’s function is defined in a form of cumulative distribution function. It is important to determine the distribution of the greatest prime factor of a given value. For example, let then
This means that for any random integer N, there is a probability of 0.3068 that its greatest prime factor is less than . Next, we require these two lemmas to help us in the attack.
Lemma 1.
Let where . If and such that , then .
Proof.
Observe that
Since
and
Since and are integers, . □
This result will help us to enable the attack later presented in Theorem 2.
Lemma 2.
If an integer H divides then .
Proof.
Let for some integer and where . Then
If H divides then H will also divides . Hence for some integer . That is,
Then
The above results will help us to enable the attack later presented in Theorem 2.
3. The Attack
The initial strategy in our attack is to find the conditions on the approximations of and p to enable our attack. By using these conditions, we shall prove mathematically that there exists an unknown intermediate that will help us to find the factorization of N in polynomial time.
First, to find the conditions on the approximations of and p, we need the following lemma regarding an approximation of p.
Lemma 3.
Let with . If there exists where then .
Proof.
From we know
and
Suppose . This implies shares the same a fraction of the MSBs with p and subsequently . Thus
This completes the proof. □
The next lemma assumes that , then we show that, by having a fraction of the MSBs of p and q of CRT-RSA modulus, we can get an approximation of p to a certain bound.
Lemma 4.
Let be an CRT-RSA modulus with . If a fraction α of the MSBs of p or q are known then we can find such that .
Proof.
We know that if then . Observe . If a fraction of the MSBs of p are known then we can find which consists of a fraction of the MSBs of p such that
On the side of q, since , if a fraction of the MSBs of q are known, then
Since q and shares the same a fraction of the MSBs, then . Given , we can compute which satisfies
This completes the proof. □
From Lemma 4, we know that by having a fraction of MSBs of p or q, we can obtain an approximation of p called where . This approximation of p will enable the next lemma to find given a fraction of the MSBs of and where and .
Lemma 5.
Let be an CRT-RSA modulus with . Suppose be a valid public exponent with and be its corresponding private exponent which satisfies CRT-RSA key equation . If a fraction α of the MSBs of and p (or q) are known, then the constant in the key equation can be determined, up to a small constant additive error, in time polynomial in .
Proof.
Recall that one of the private exponent of CRT-RSA satisfies . So, we can write
If a fraction of the MSBs of are known, then we have such that . From Lemma 4, if we have a fraction of the MSBs of p (or q) are known then we have such that . is given by
for some , reveals some of the most significant bits of . In particular, notice that
If as in Lemma 3, then (11) will be
for large N. Hence, the constant will be in the range . Since can be computed in time polynomial in . This completes the proof. □
Lemma 5 shows the significance of knowing a fraction of the MSBs of d and p, in order to find . It also shows that the conditions presented in Lemma 5 must be carried throughout the attack since it enables the attack. The value of obtained in Lemma 5 is utilized in the next proposition.
Proposition 1.
Let be an CRT-RSA modulus with and . Suppose be a valid public exponent with and be its corresponding private exponent, which satisfies . Let for some then .
Proof.
Rearranging (14), we have
This implies that . Since is always an integer, . Now, we can see that
This completes the proof. □
Remark 1.
Equation (18) shows that under assumption of Proposition 1, which values and are known, it is crucial that is kept secret.
The next theorem shows the implication of the results from Proposition 1 in our aim to factor CRT-RSA modulus in polynomial time.
Theorem 2.
Let be a CRT-RSA modulus with . Suppose be a valid public exponent with and be its corresponding private exponent which satisfies . Let for some . Let be one of the prime factor of such that . Suppose and such that . If and a fraction α of the MSBs of and p (or q) are known then N can be factored in polynomial time.
Proof.
If satisfies , and and such that , from Lemma 1, we obtain
Lemma 2 implies if divides then . This also implies
From Proposition 1,
If and a fraction of the MSBs of are known, based on Lemma 5, we can find in polynomial time. Then, we can compute as . If is known, we can compute in (21). Using the value of , we can obtain p by computing and factorizes N. This completes the proof. □
Remark 2.
We have shown that given α most significant bits of and p, the complexity of factoring N depends on knowing the factor of . This demonstrates that we have reduced one of the hard problems of RSA from factoring N to factoring . However, the complexity of factorization is still sub-exponential according to the current factorization technique.
We construct an algorithm based on our attack. The parameters used in the algorithm are described in Table 1:

Table 1.
List of Parameters Used in the Attack.
The algorithm takes the input of RSA public keys and a prime factor of that satisfies , given a fraction of the MSBs of and . The algorithm is as follows:
Remark 3.
Since we assume that the value of is already known in Algorithm 2, the algorithm runs in polynomial time.
The following is an example to illustrate Algorithm 2.
| Algorithm 2 Factoring N of CRT-RSA via Theorem 2 |
| Input: CRT-RSA public keys , and prime factor of |
| Output: |
|
Example 1.
We use RSA-2048 in this example. Specifically, we are given
and which is about . Let
where a fraction α of the MSBs of are given such that . In this case, or about 10% (103-bits) bits of its original, . Then, let
where a fraction α of the MSBs of p (or q) are also given, such that . From Lemma 5, given and , we obtain and proceed to recover in polynomial time. Then, we compute
Given that we also know one of the prime factor of ,
such that . Then
By knowing , we can get
and
N has been successfully factored.
Figure 1 shows the flowchart based on Algorithm 2:
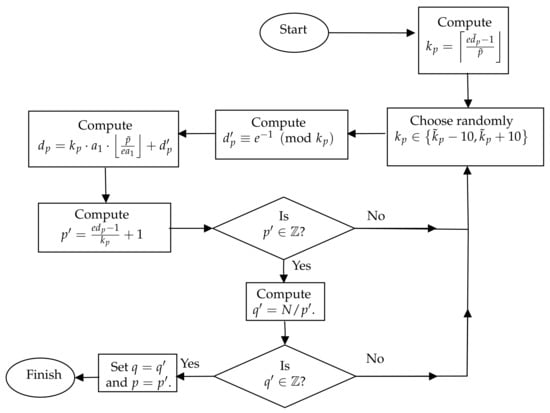
Figure 1.
Flowchart of Algorithm 2.
Our Attack in RSA Implementation
In most RSA implementations, RSA public exponent e is a small integer. The reason for this choice is to optimize the computing time of the RSA encryption algorithm. In this part, we investigate the implication of the size of e in our attack. Typically, . Since we set in our attack, observe that
in the implementation of RSA-2048.
This implicates that our attack requires or about 32 bits of and p to be exposed since and . The exposed bits may come from the side-channel attack or a brute-force method, since the number of bits that are required are quite small. The number of exposed bits that are required can be reduced, if the size of N or e is smaller.
4. Estimating Number of Candidates for
To find an that satisfy posed in Theorem 2, we can anticipate that to be the largest prime factor of . We need to estimate the number of primes that are eligible to be . However, first, the next lemma modifies the result by [20] and applies it to show an estimation of the number of primes between two bounds.
Lemma 6.
Let and respectively be the upper and lower bounds of where . Then, the number of primes between and will be less than .
Proof.
Let F be the number of primes less than the upper bound of and G be the number of primes less than the lower bound of . Then, according to Theorem 1,
and
To estimate the number of candidates of , we need to calculate
as . This completes the proof. □
Then, we need to find the upper and lower bounds of that satisfy the condition posed in Theorem 2.
Proposition 2.
Let be a CRT-RSA modulus with . Suppose is a valid public exponent with and be its corresponding private exponent which satisfies . Let for some . Let a fraction α of the MSBs of and p (or q) are known. If be one of the prime factor of such that then will be bounded as .
Proof.
We know that where . Then
Thus, is the lower bound for . For the upper bound, we know that as is a factor of . Then
Thus, . This follows the result. □
After we know the upper and lower bounds of , we can estimate the number of primes between the bounds. To achieve that, we use the estimation in Lemma 6. The estimation is as follows in the next proposition.
Proposition 3.
Let be an CRT-RSA modulus with . Suppose be a valid public exponent with and be its corresponding private exponent which satisfies . Let for some . Let a fraction α of the MSBs of and p (or q) are known. If be one of the prime factor of such that then the number of candidates of that satisfies Theorem 2. will be less than
Proof.
We use results from Lemma 6 to count the sum of primes that satisfy Theorem 2. Thus, we changes and in Lemma 6 to and respectively based on the bounds in Proposition 2. Equation (22) will become
This completes the proof. □
The following is an example to illustrate the result from Proposition 3.
Example 2.
In this example, we try to illustrate the number of primes that are eligible to be the candidates of .To do that, we set to imitate the lowest possible estimation of the number of primes. We also substitute the value of N from Example 1 into (23) which approximates to
This is the approximation of the amount of primes that are eligible to be the candidates of .
5. Estimating the Number of Candidates for with Various Success Appetite
To reduce the number of the candidates of to be manipulated by an adversary, we define the “success appetite” terminology to best describe our findings.
Definition 2.
CRT-RSA Success Appetite, is the conditional probability of successfully finding the largest prime factor of , ; where is less than , given that is greater than where and for suitable .
Remark 4.
Success appetite as described in this paper relates to the success probability of the adversary to find the actual value of from a certain set of primes. The adversary can choose his success appetite, depending on computing resources available to the adversary. The probability of success for the adversary depends on the size of the set of prime candidates where resides. As such, success appetite and probability of success are two different concepts.
Since further experiment and analysis must be completed to be corroborated with the independent nature of Dickman’s function and randomized values of , we put forward the next conjecture that defines CRT-RSA success appetite quantitatively.
Conjecture 1.
Given i different RSA moduli, that are randomly generated in RSA key generation algorithm, then the largest number of RSA moduli of which the greatest prime factor of is between its intended success-dependent upper and lower bound is .
By having the CRT-RSA success appetite, an adversary can evaluate it using the next corollary.
Proposition 4.
Let be an RSA modulus. Let be an RSA public exponent and d be an RSA private exponent where . Let be one of the prime factors of . Suppose B is a known integer larger than and . Let be the Dickman’s function. If is the CRT-RSA success appetite, then the number of candidates of that satisfies Theorem 2 will be less than
where .
Proof.
Let or be the probability function for a random integer between 1 and X to have the greatest prime factor less than as defined in Definition 1 (Dickman’s function). Let be the upper bound of and to be the lower bound of , then (23) can also be written as
Next, we define
- to be the probability of X having its greatest prime factor less than ;
- to be the probability of X having its greatest prime factor less than ; and
- to be the probability of X not having its greatest prime factor less than .
Let be the success appetite as defined in Definition 2, we can rewrite as the probability of having its largest prime factor less than , given that it has no largest prime factor less than . Using the definition of conditional probability, observe that
From (25),
According to Proposition 2, . Substitute values of and into (24), we obtain
where □
Proposition 4 shows that an adversary can adjust the upper bound of according to the success appetite preferred by the adversary. In the next section, we can see how this adjustment can reduce the number of primes eligible to be the significant candidates of .
6. Comparative Analysis
In this section, we show two comparisons. In the first comparison, we compare the changes of the number of candidates of , in terms of (where ) when the success appetite, changes. We also set and to see the changes in . The full details of the values are shown in Table 2.

Table 2.
Comparison in Number of Candidates of In Terms of Logarithm to Base N with Respect to and .
Based on Table 2, when progressively reduces from 1 to 0.01, for , the number of candidates also slowly reduces from to , to for , to for , to for and to for . In general, the number of candidates decreases as the values of the success appetites decrease. A similar pattern occurs when the values of increases. This means that the best situation for an adversary to conduct an attack against CRT-RSA using our method is when MSBs of d and p (or q) are known with a consideration of a success appetite that is as small as possible.
In the second comparison, we intend to compare our attack with results from [12,13,14,15,16]. All of these results require some bits of to be known beforehand. In [15], Takayatsu et al. provided a result which includes bits of . A comparison with our results is shown in Table 3.

Table 3.
Comparison of Our Method Against Existing Methods to Conduct Partial-Key Exposure Attack Against CRT-RSA.
Based on Table 3, Ref. [16] requires at least 0.27 random bits of all . The attack also used random reconstruction algorithm. On another hand, attack by [12] requires an approximation of called to be given, such that where . The suitable size of e used in the attack is . The methodology used in [12] can also be applied in many conditions, since we can see that the extension of the results in [13,14,15] are also using the similar lattice-based approach.
Meanwhile, our attack requires an approximation of and p called and to be given, such that . As , this means that the suitable range for e in our case is . based on Table 3, Ref. [12] needs the approximation of to be between 0 and from the actual . Meanwhile, in our case, we need the approximation of and p to be between and from the actual values of and p. This means that our attack is less stringent and requires less MSBs of private keys to be known than [12] (although our attack needs two approximations of private keys). In addition, our method takes a different approach compared to other results, since we detach our method from the common approach of partial key attack on CRT-RSA by using the lattice-based method to finding the largest prime factor of with versatile success appetites.
7. Conclusions
We have successfully factored the modulus of CRT-RSA in polynomial time using our new method under specific conditions. Given , where , the method requires an approximation of private exponent called and approximation of p called to be known, such that . Our attack also requires the largest prime factor of . By utilizing Dickman’s theorem, we showed a practical approach to identify the prime from a set of primes that the factor most likely resides in. The approach manipulates a versatile self-defined value known as the success appetite value that can be referred to by the adversary based on the computational power at hand. This makes our attack less stringent and requires fewer MSBs of private keys to be known than existing attacks. For a future extension of this work, one may develop a new method to find from a smaller set of primes. The method should include a marked up algorithm that identifies , where its respective success appetite is compared with the number of candidates of in terms of the logarithm to base N, as shown in Table 2. Another interesting future approach to tackle the problem of finding is by using synchronized machine learning with the aid of cloud systems for its storage space, as shown in [23].
Author Contributions
Conceptualization, A.H.A.G. and M.R.K.A.; methodology, formal analysis, investigation, writing—original draft preparation, A.H.A.G.; writing—review and editing, A.H.A.G., M.R.K.A., S.M.Y. and S.H.S.; supervision and funding acquisition, M.R.K.A. All authors have read and agreed to the published version of the manuscript.
Funding
The research was supported by Ministry of Higher Education of Malaysia with Fundamental Research Grant Scheme (FRGS/1/2019/STG06/UPM/02/8).
Acknowledgments
The research was supported by Ministry of Higher Education of Malaysia with Fundamental Research Grant Scheme (FRGS/1/2019/STG06/UPM/02/8).
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| LSB | Least significant bits |
| MSB | Most significant bits |
| RSA | Rivest–Shamir–Adleman |
References
- Rivest, R.L.; Shamir, A.; Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 1978, 21, 120–126. [Google Scholar] [CrossRef]
- Buhler, J.P.; Lenstra, H.W.; Pomerance, C. Factoring integers with the number field sieve. In The Development of the Number Field Sieve; Springer: Berlin/Heidelberg, Germany, 1993; pp. 50–94. [Google Scholar]
- Rivest, R.L.; Shamir, A.; Adleman, L.M. Cryptographic Communications System and Method. U.S. Patent 4,405,829, 20 September 1983. [Google Scholar]
- Hinek, M.J. Cryptanalysis of RSA and Its Variants; CRC Press: Boca Raton, FL, USA, 2009. [Google Scholar]
- Kocher, P.; Jaffe, J.; Jun, B.; Rohatgi, P. Introduction to differential power analysis. J. Cryptogr. Eng. 2011, 1, 5–27. [Google Scholar] [CrossRef]
- Rivest, R.L.; Shamir, A. Efficient factoring based on partial information. In Workshop on the Theory and Application of of Cryptographic Techniques; Springer: Berlin/Heidelberg, Germany, 1985; pp. 31–34. [Google Scholar]
- Coppersmith, D. Finding a small root of a bivariate integer equation; factoring with high bits known. In International Conference on the Theory and Applications of Cryptographic Techniques; Springer: Berlin/Heidelberg, Germany, 1996; pp. 178–189. [Google Scholar]
- Boneh, D.; Durfee, G.; Frankel, Y. Exposing an RSA private key given a small fraction of its bits. Full Version Work. Asiacrypt 1998, 98, 25–34. [Google Scholar]
- Ernst, M.; Jochemsz, E.; May, A.; De Weger, B. Partial key exposure attacks on RSA up to full size exponents. In Annual International Conference on the Theory and Applications of Cryptographic Techniques; Springer: Berlin/Heidelberg, Germany, 2005; pp. 371–386. [Google Scholar]
- Sarkar, S.; Maitra, S.; Sarkar, S. RSA Cryptanalysis with Increased Bounds on the Secret Exponent using Less Lattice Dimension. IACR Cryptol. ePrint Arch. 2008, 2008, 315. [Google Scholar]
- Abd Ghafar, A.H.; Ariffin, M.R.K.; Johari, M.A.M.; Asbullah, M.A. A Survey of Partial Key Exposure Attacks on RSA Cryptosystem. Embrac. Math. Divers. 2019, 1, 24. [Google Scholar]
- Blömer, J.; May, A. New partial key exposure attacks on RSA. In Annual International Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 2003; pp. 27–43. [Google Scholar]
- Lu, Y.; Zhang, R.; Lin, D. New partial key exposure attacks on CRT-RSA with large public exponents. In International Conference on Applied Cryptography and Network Security; Springer: Cham, Switzerland, 2014; pp. 151–162. [Google Scholar]
- Sarkar, S.; Venkateswarlu, A. Partial key exposure attack on CRT-RSA. In International Conference on Cryptology in India; Springer: Berlin/Heidelberg, Germany, 2014; pp. 255–264. [Google Scholar]
- Takayasu, A.; Kunihiro, N. Partial key exposure attacks on CRT-RSA: Better cryptanalysis to full size encryption exponents. In International Conference on Applied Cryptography and Network Security; Springer: Cham, Switzerland, 2015; pp. 518–537. [Google Scholar]
- Heninger, N.; Shacham, H. Reconstructing RSA private keys from random key bits. In Advances in Cryptology-CRYPTO 2009; Springer: Berlin/Heidelberg, Germany, 2009; pp. 1–17. [Google Scholar]
- Halderman, J.A.; Schoen, S.D.; Heninger, N.; Clarkson, W.; Paul, W.; Calandrino, J.A.; Feldman, A.J.; Appelbaum, J.; Felten, E.W. Lest we remember: Cold-boot attacks on encryption keys. Commun. ACM 2009, 52, 91–98. [Google Scholar] [CrossRef]
- Takayasu, A.; Kunihiro, N. Partial key exposure attacks on CRT-RSA: General improvement for the exposed least significant bits. In International Conference on Information Security; Springer: Berlin/Heidelberg, Germany, 2016; pp. 35–47. [Google Scholar]
- Ireland, K.; Rosen, M. A Classical Introduction to Modern Number Theory; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2013; Volume 84. [Google Scholar]
- Dusart, P. Estimates of some functions over primes without RH. arXiv 2010, arXiv:1002.0442. [Google Scholar]
- Dickman, K. On the frequency of numbers containing prime factors of a certain relative magnitude. ARkiv Mat. Astron. Och Fys. 1930, 22, 1–14. [Google Scholar]
- Donald, E.K. The Art of Computer Programming, Vol. 2: Seminumerical Algorithms; Addison-Wesley: Boston, MA, USA, 1981. [Google Scholar]
- Çatak, F.Ö.; Mustacoglu, A.F. CPP-ELM: Cryptographically privacy-preserving extreme learning machine for cloud systems. Int. J. Comput. Intell. Syst. 2018, 11, 33–44. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).