Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher
Abstract
1. Introduction
2. Basic Theories
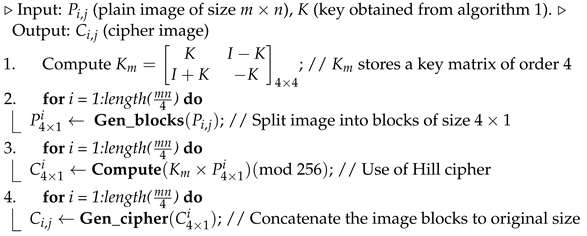
2.1. Mathematical Concept of Elliptical Curves
- (i)
- Public element: Select an elliptic curve with the parameters , with q a large prime of at least 160-bit length and a generator point G of order r, i.e., on the elliptic curve.
- (ii)
- User A Generate: Select a random private key and calculate
- (iii)
- User B Generate: Select a random private key and calculate
- (iv)
- User A calculate secret key:
- (v)
- User B calculate secret key:
2.2. Affine Hill Cipher
The 3D Arnold Map
3. Scheme Proposed by Dawahdeh et al. [7]
| Algorithm 1: Elliptic curve key generation over some . |
▹ Input: ▹ Output:
|
| Algorithm 2: Encryption algorithm of the scheme [7]. |
 |
4. Cryptanalysis and Improvement
4.1. Brute Force Attack on the Scheme in [7]
4.2. Improvement
5. Proposed Methodology of the Improved Scheme
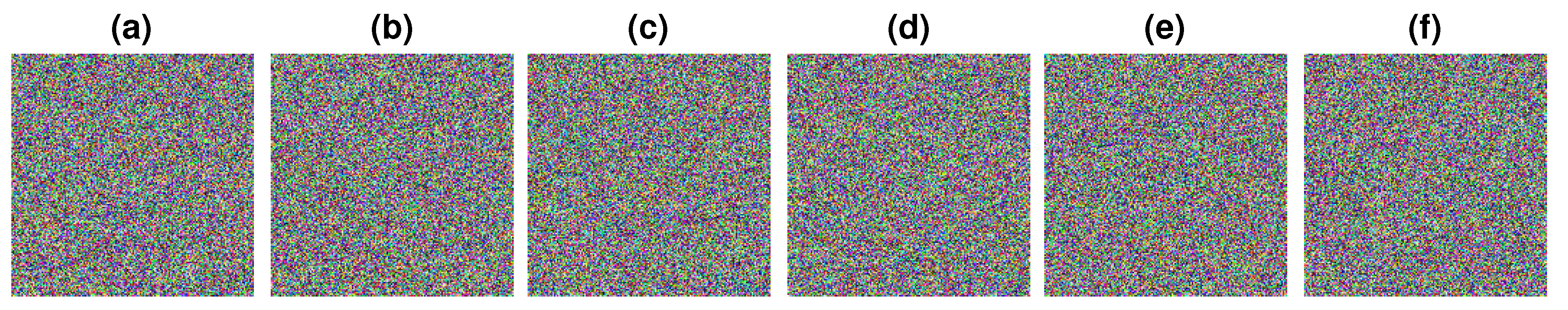
| Algorithm 3:Proposed encryption scheme. |
 |
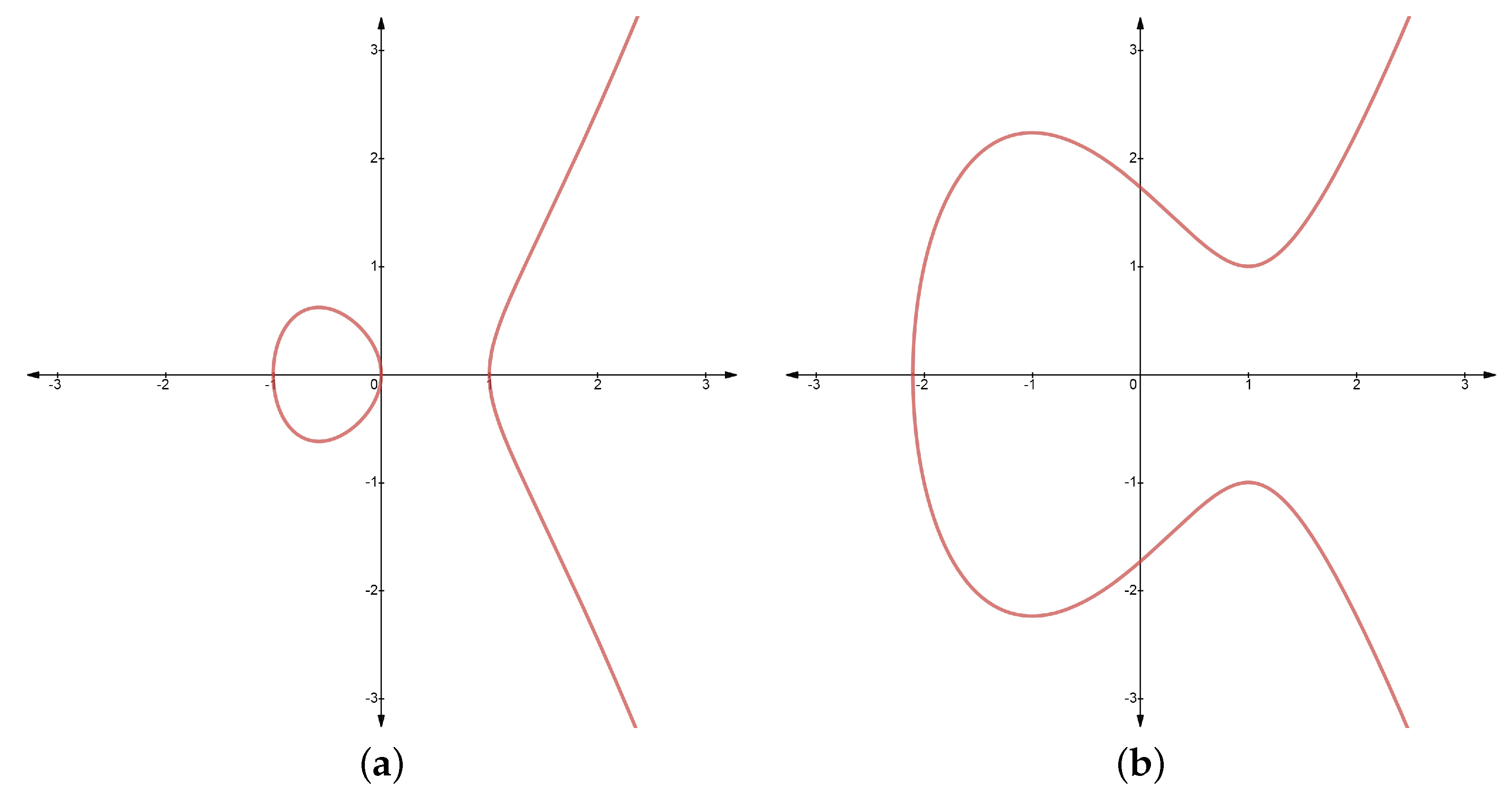
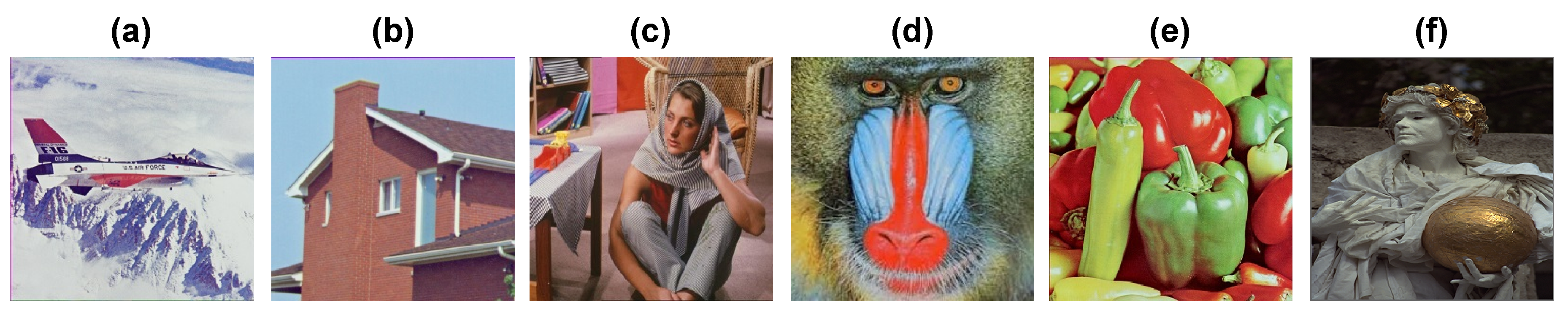
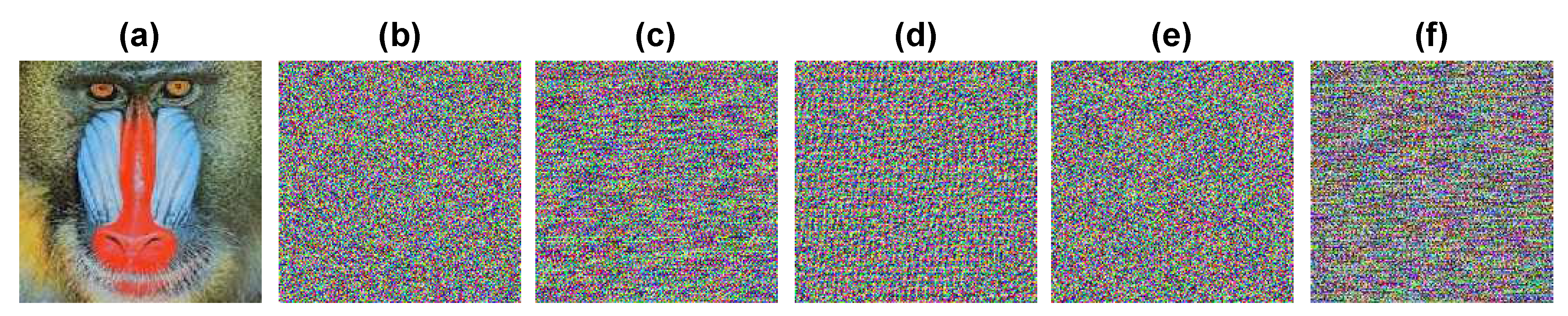
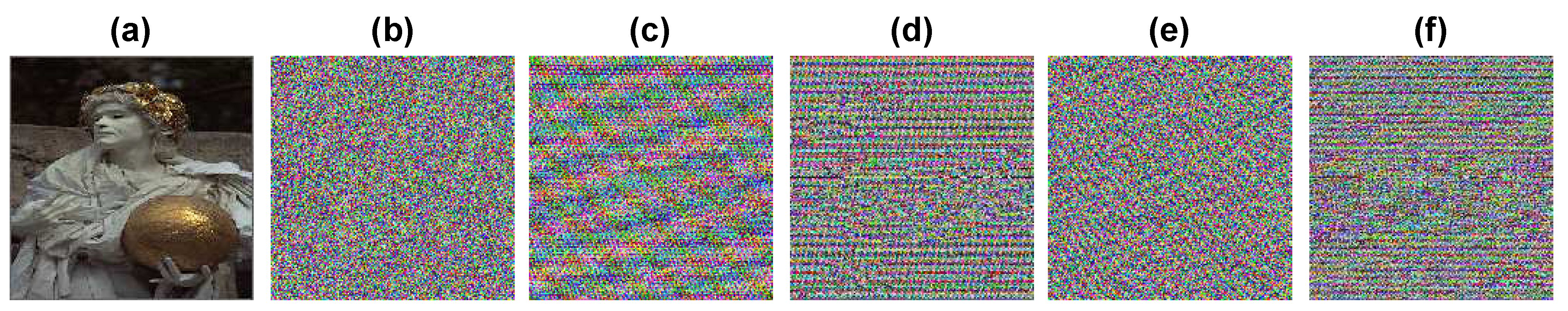
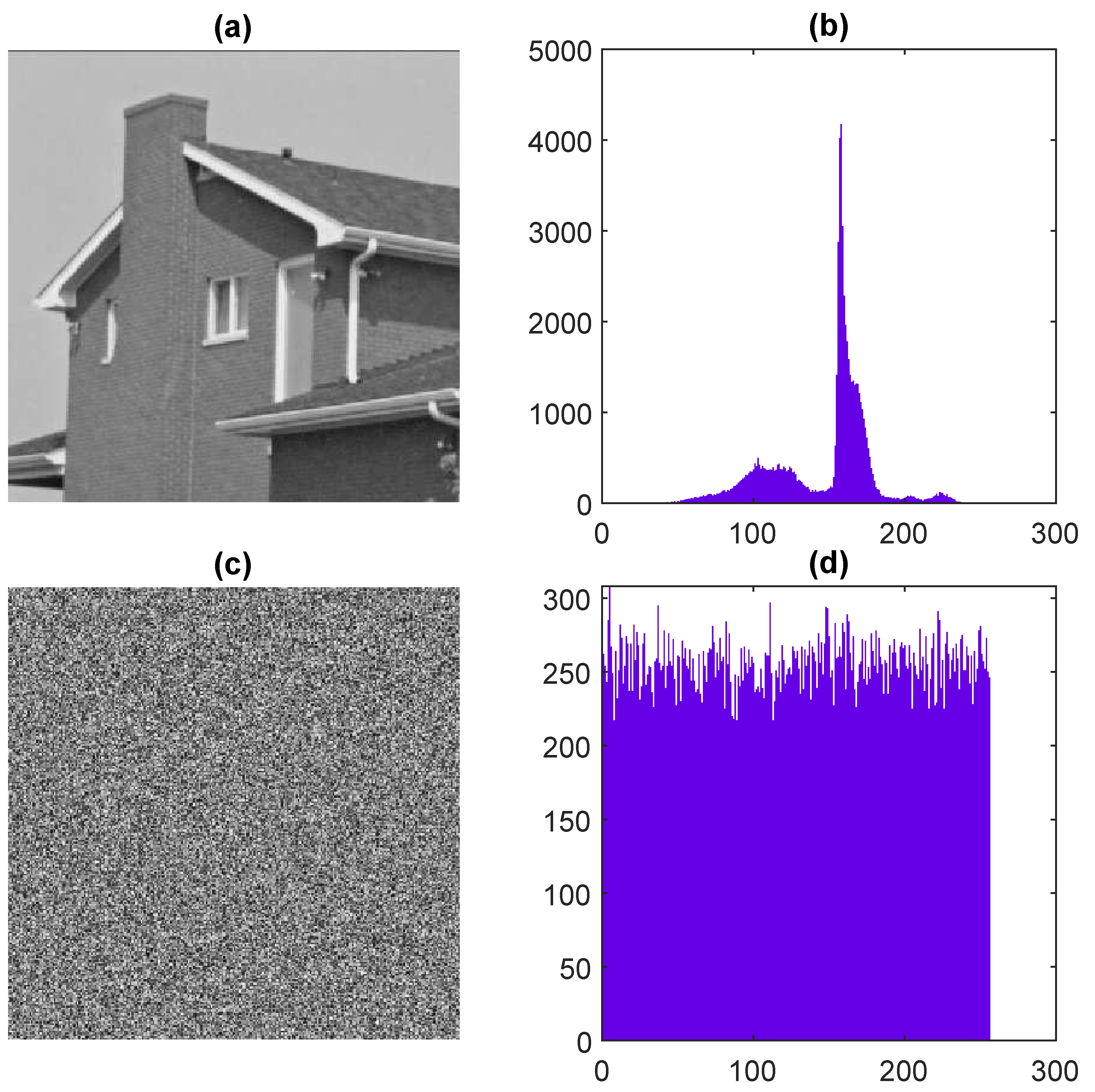
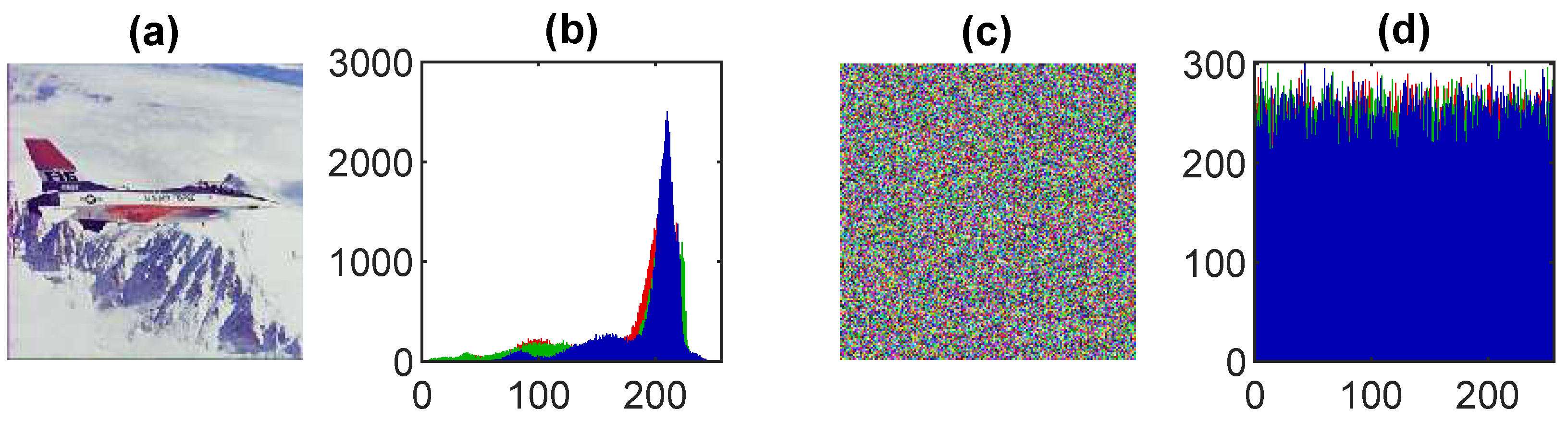
6. Experimental Results
7. Security Analysis
7.1. Key Space Analysis
- The choices for during the encryption process are defined as follows:
- works as an additive key element in the affine Hill cipher, with possible choices .
- The publicly shared parameters for the Arnold map through ECC can be reduced up to choices.
7.2. Key Sensitivity
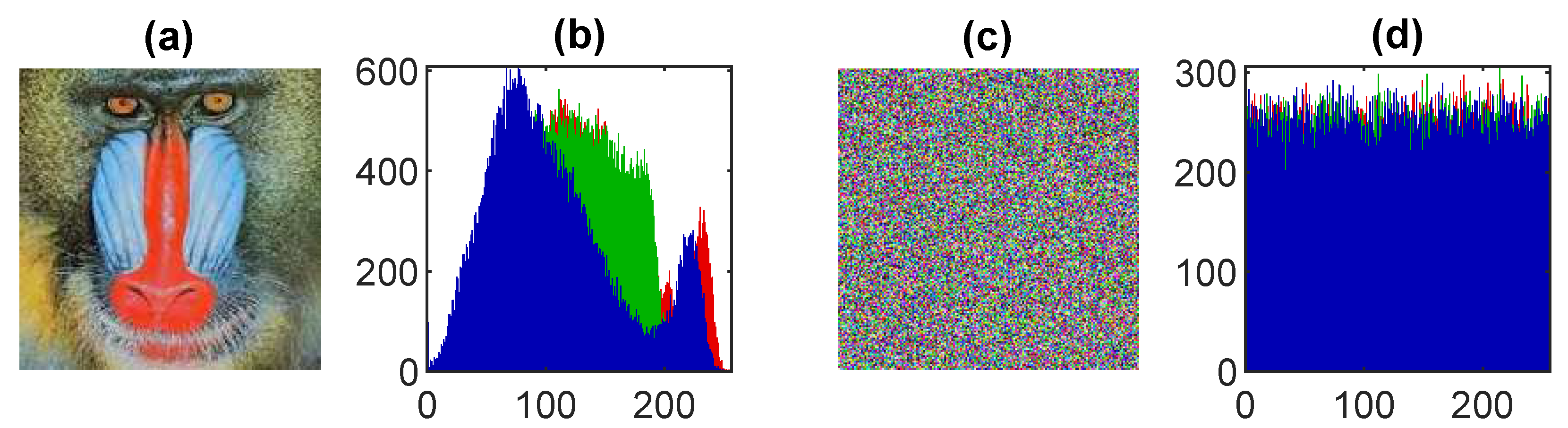
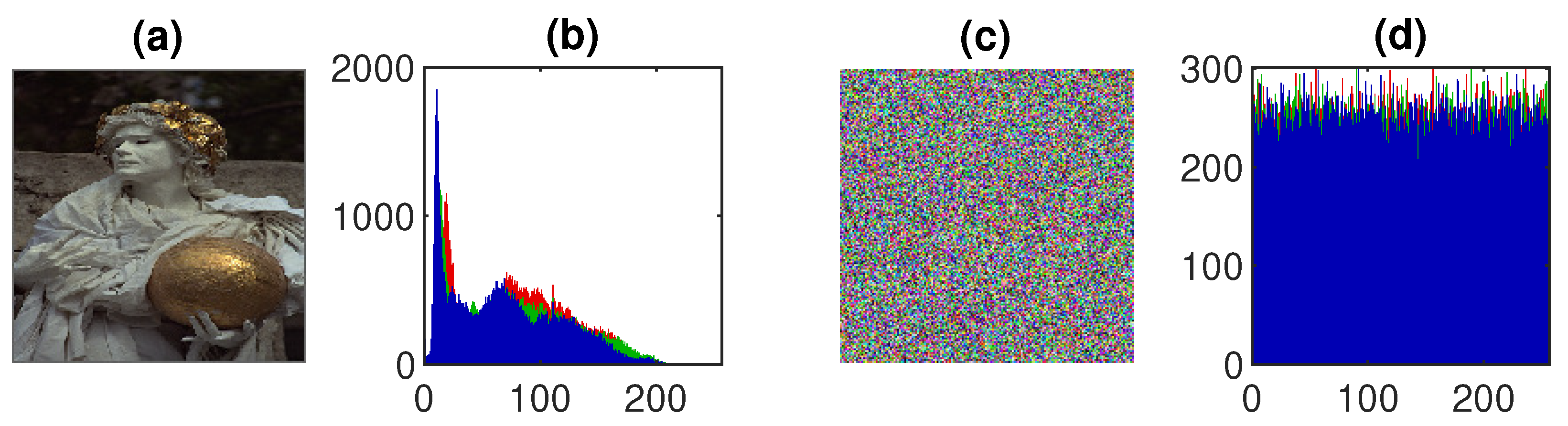
7.3. Histogram Analysis
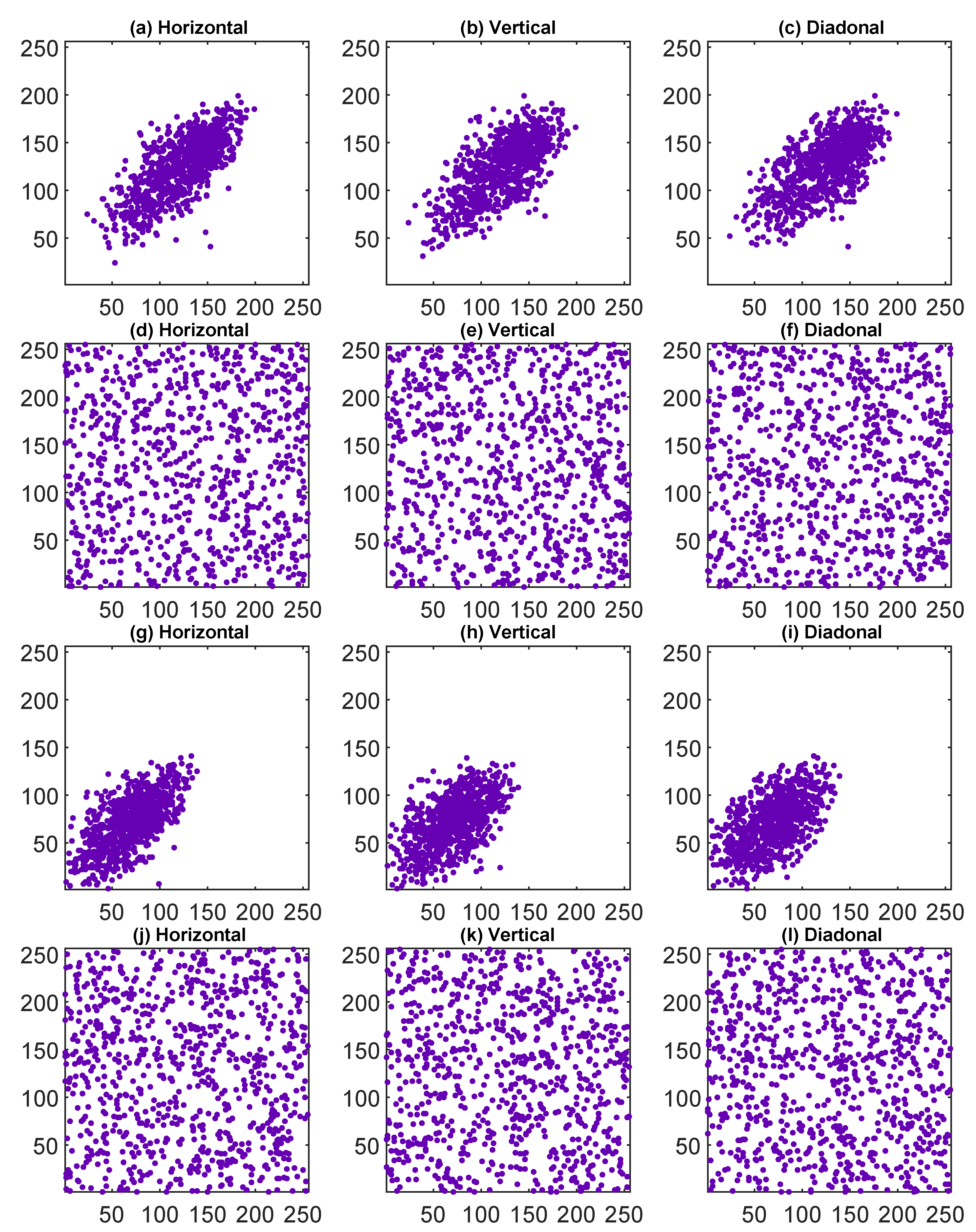
7.4. Correlation Analysis
7.5. Quality Measure
7.5.1. Mean Square Error (MSE)
7.5.2. Peak Signal to Noise Ratio (PSNR)
7.5.3. Structural Similarity Index (SSIM)
7.6. Differential Attack Analysis
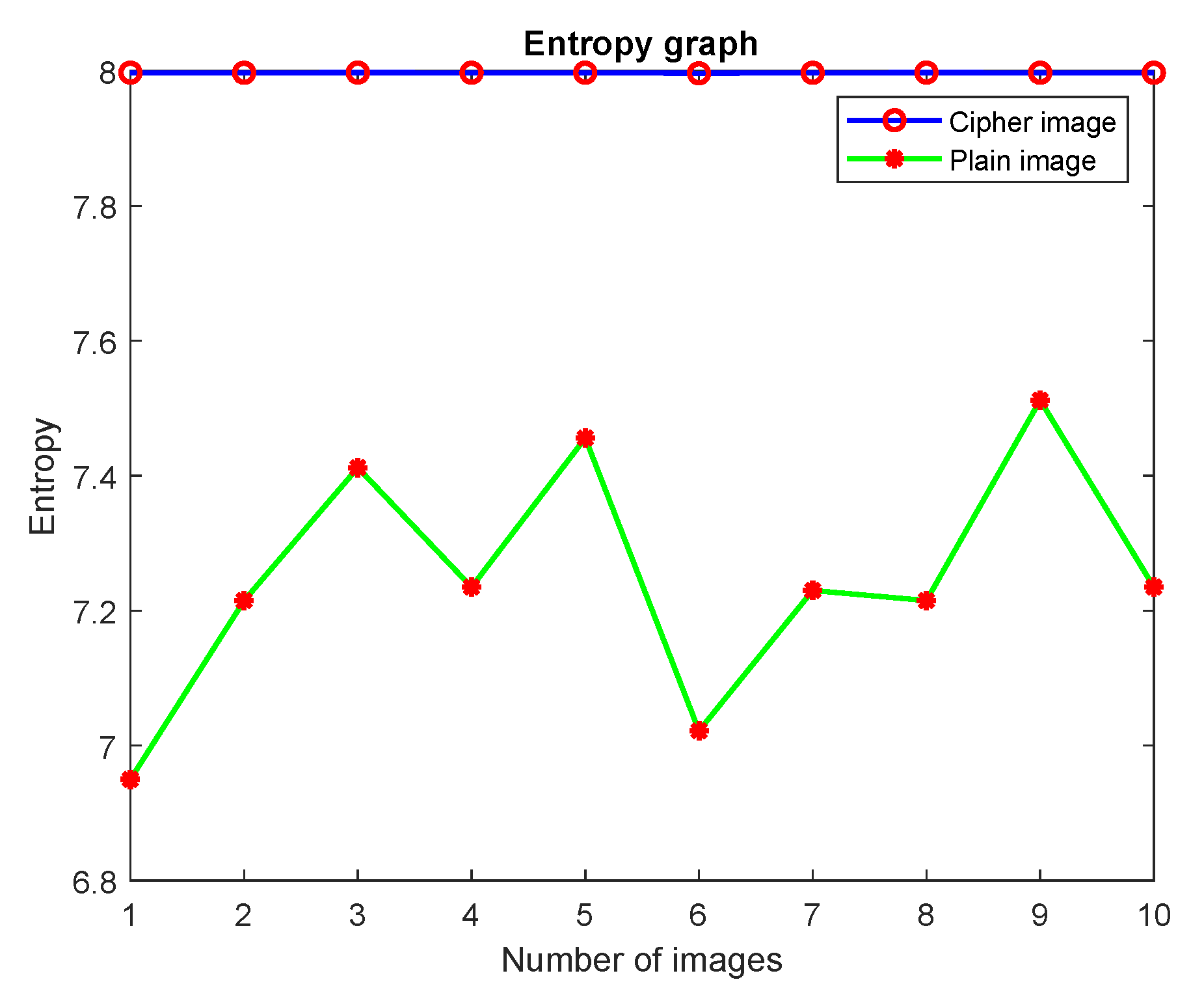
7.7. Shannon’s Entropy Analysis
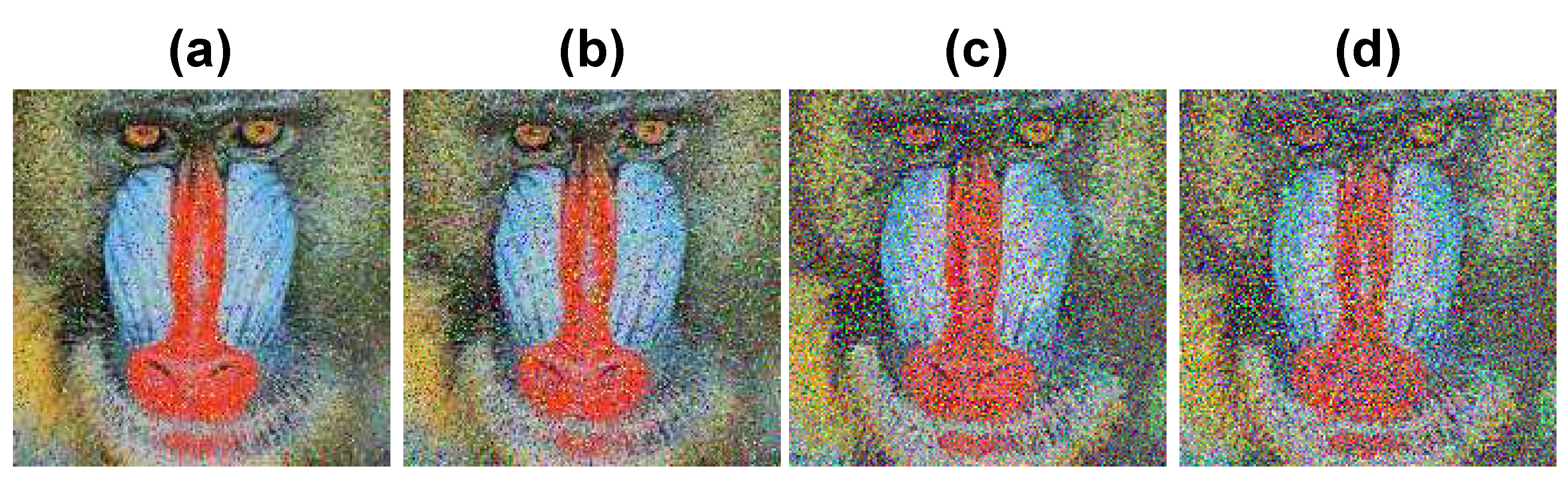
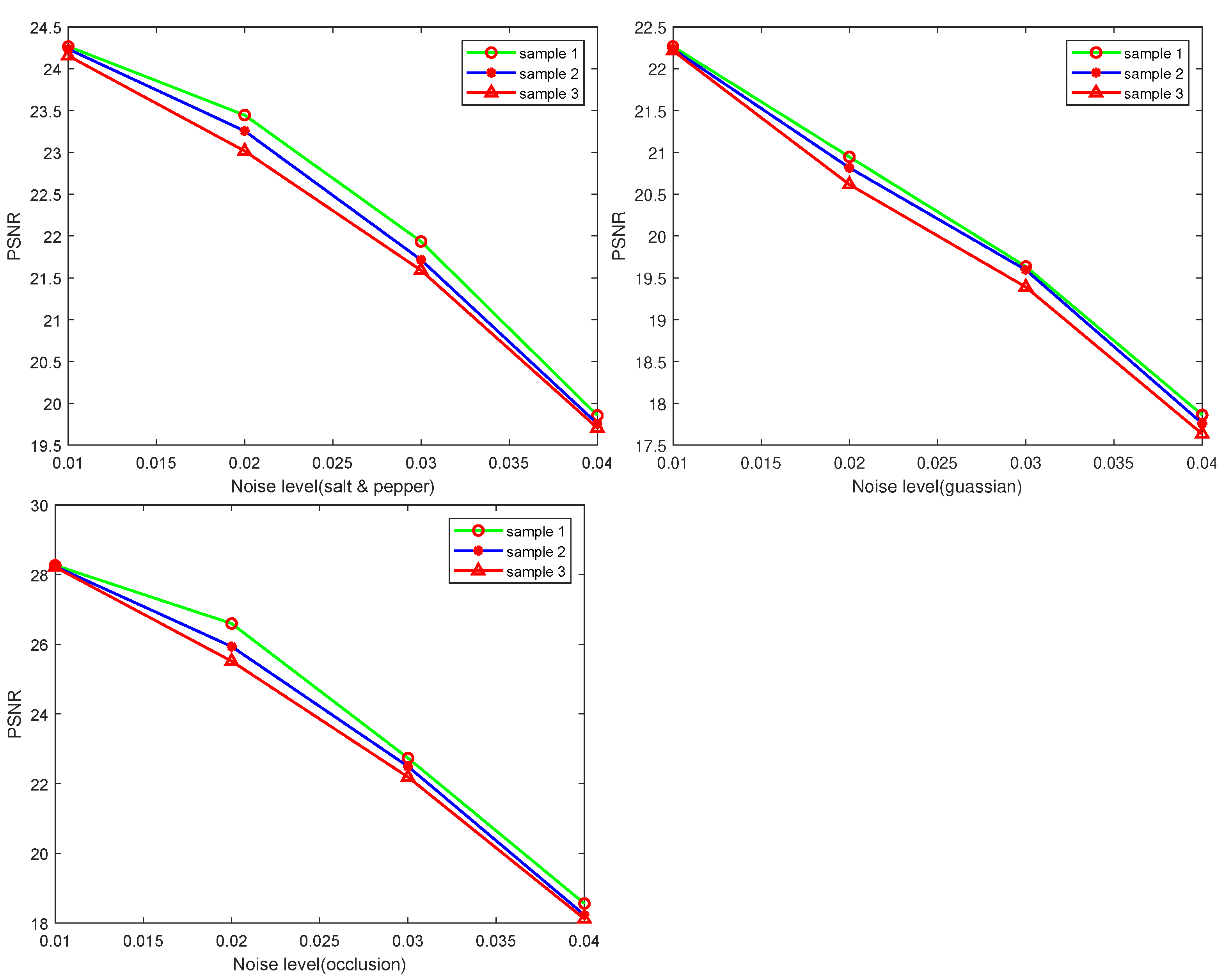
7.8. Noise Attacks
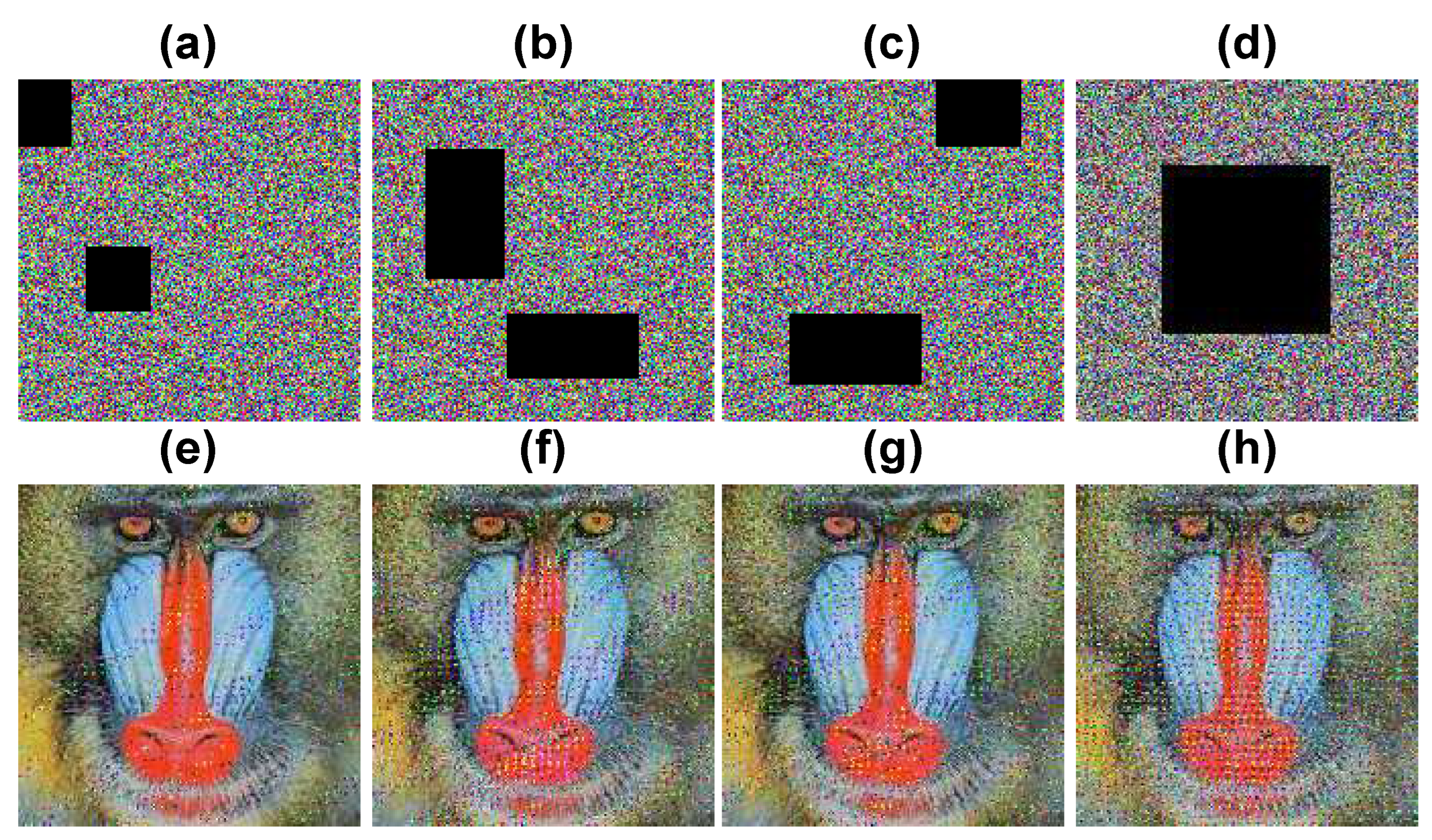
7.9. Occlusion Attack
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Koul, N.; Kumar, N.; Sayeed, A.; Verma, C.; Raboaca, M.S. Data Exchange Techniques for Internet of Robotic Things: Recent Developments. IEEE Access 2022, 10, 102087–102106. [Google Scholar] [CrossRef]
- Hankerson; Menezes, A.J.; Vanstone, S.A. Guide to Elliptic Curve Cryptography, 2004 ed.; Springer Professional Computing; Springer: New York, NY, USA, 2004. [Google Scholar]
- Gura, N.; Patel, A.; Wander, A.; Eberle, H.; Shantz, S.C. Comparing Elliptic Curve Cryptography and RSA on 8-bit CPUs. In International Workshop on Cryptographic Hardware and Embedded Systems, Proceedings of the Cryptographic Hardware and Embedded Systems-CHES 2004, Cambridge, MA, USA, 11–13 August 2004; Joye, M., Quisquater, J.J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 119–132. [Google Scholar]
- Malan, D.; Welsh, M.; Smith, M. A public-key infrastructure for key distribution in TinyOS based on elliptic curve cryptography. In Proceedings of the 2004 First Annual IEEE Communications Society Conference on Sensor and Ad Hoc Communications and Networks, IEEE SECON 2004, Santa Clara, CA, USA, 4–7 October 2004; pp. 71–80. [Google Scholar] [CrossRef]
- Li, L.; Abd El-Latif, A.A.; Niu, X. Elliptic curve ElGamal based homomorphic image encryption scheme for sharing secret images. Signal Process. 2012, 92, 1069–1078. [Google Scholar] [CrossRef]
- Paar, C.; Pelzl, J. Understanding Cryptography, 2010 ed.; Springer: Berlin, Germany, 2014. [Google Scholar]
- Dawahdeh, Z.E.; Yaakob, S.N.; Razif bin Othman, R. A new image encryption technique combining Elliptic Curve Cryptosystem with Hill Cipher. J. King Saud Univ.-Comput. Inf. Sci. 2018, 30, 349–355. [Google Scholar] [CrossRef]
- Hayat, U.; Ullah, I.; Azam, N.A.; Azhar, S. A Novel Image Encryption Scheme Based on Elliptic Curves over Finite Rings. Entropy 2022, 24, 571. [Google Scholar] [CrossRef]
- Tawalbeh, L.; Mowafi, M.; Aljoby, W. Use of elliptic curve cryptography for multimedia encryption. IET Inf. Secur. 2013, 7, 67–74. [Google Scholar] [CrossRef]
- Abd El-Latif, A.A.; Niu, X. A hybrid chaotic system and cyclic elliptic curve for image encryption. AEU-Int. J. Electron. Commun. 2013, 67, 136–143. [Google Scholar] [CrossRef]
- Obaid, Z.K.; Saffar, N.F.H.A. Image encryption based on elliptic curve cryptosystem. Int. J. Electr. Comput. Eng. 2021, 11, 1293–1302. [Google Scholar] [CrossRef]
- Singh, L.D.; Singh, K.M. Image Encryption using Elliptic Curve Cryptography. Procedia Comput. Sci. 2015, 54, 472–481. [Google Scholar] [CrossRef]
- Kumar, M.; Iqbal, A.; Kumar, P. A new RGB image encryption algorithm based on DNA encoding and elliptic curve Diffie–Hellman cryptography. Signal Process. 2016, 125, 187–202. [Google Scholar] [CrossRef]
- Khoirom, M.S.; Laiphrakpam, D.S.; Themrichon, T. Cryptanalysis of multimedia encryption using elliptic curve cryptography. Optik 2018, 168, 370–375. [Google Scholar] [CrossRef]
- Liu, H.; Liu, Y. Cryptanalyzing an image encryption scheme based on hybrid chaotic system and cyclic elliptic curve. Opt. Laser Technol. 2014, 56, 15–19. [Google Scholar] [CrossRef]
- Mir, U.; Singh, D.; Mishra, D.; Lone, P. Multilayer Security of RGB Image in Discrete Hartley Domain. Appl. Appl. Math. Int. J. (AAM) 2020, 15, 1213–1229. [Google Scholar]
- Mir, U.H.; Singh, D.; Lone, P.N. Color image encryption using RSA cryptosystem with a chaotic map in Hartley domain. Inf. Secur. J. A Glob. Perspect. 2022, 31, 49–63. [Google Scholar] [CrossRef]
- Lone, P.N.; Singh, D.; Mir, U.H. Image Encryption Using DNA Coding and Three-Dimensional Chaotic Systems. Multimed. Tools Appl. 2022, 81, 5669–5693. [Google Scholar] [CrossRef]
- Lone, P.N.; Singh, D. Application of algebra and chaos theory in security of color images. Optik 2020, 218, 165155. [Google Scholar] [CrossRef]
- Sabir, S.; Guleria, V. Multi-layer color image encryption using random matrix affine cipher, RP2DFrHT and 2D Arnold map. Multimed. Tools Appl. 2021, 80, 27829–27853. [Google Scholar] [CrossRef]
- Liu, H.; Zhu, Z.; Jiang, H.; Wang, B. A Novel Image Encryption Algorithm Based on Improved 3D Chaotic Cat Map. In Proceedings of the 2008 The 9th International Conference for Young Computer Scientists, Zhangjiajie, China, 18–21 November 2008; pp. 3016–3021. [Google Scholar] [CrossRef]
- Joshi, A.B.; Kumar, D.; Gaffar, A.; Mishra, D. Triple color image encryption based on 2D multiple parameter fractional discrete Fourier transform and 3D Arnold transform. Opt. Lasers Eng. 2020, 133, 106139. [Google Scholar] [CrossRef]
- Acharya, B.; Rath, G.; Patra, S.; Panigrahy, S.K. Novel Methods of Generating Self-Invertible Matrix for Hill Cipher Algorithm. Int. J. Secur. 2007, 1, 14–21. [Google Scholar]
- Alvarez, G.; Li, S. Some Basic Cryptographic Requirements for Chaos-based Cryptosystems. Int. J. Bifurc. Chaos 2006, 16, 2129–2151. [Google Scholar] [CrossRef]
- Schneier, B. Applied Cryptography, 20th ed.; John Wiley & Sons: Nashville, TN, USA, 2015. [Google Scholar]
- Kumar, S.; Paar, C.; Pelzl, J.; Pfeiffer, G.; Schimmler, M. Breaking Ciphers with COPACOBANA—A Cost-Optimized Parallel Code Breaker. In International Workshop on Cryptographic Hardware and Embedded Systems, Proceedings of the Cryptographic Hardware and Embedded Systems-CHES 2006, Yokohama, Japan, 10–13 October 2006; Goubin, L., Matsui, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; pp. 101–118. [Google Scholar]
- Levine, J. Some Applications of High-Speed Computers to the Case n = 2 of Algebraic Cryptography. Math. Comput. 1961, 15, 254–260. [Google Scholar]
- Lone, P.N.; Singh, D.; Mir, U.H. A novel image encryption using random matrix affine cipher and the chaotic maps. J. Mod. Opt. 2021, 68, 507–521. [Google Scholar] [CrossRef]



| Cipher Image | Values | ||||
|---|---|---|---|---|---|
| R | G | B | Average | ||
| Jet | 284.2314 | 218.6172 | 232.1876 | 245.0120 | accept |
| House | 223.2356 | 286.2349 | 267.2496 | 258.9067 | accept |
| Barbara | 262.1451 | 258.2149 | 287.2350 | 269.1983 | accept |
| Baboon | 289.2571 | 267.8561 | 300.2225 | 285.7785 | accept |
| Pepper | 279.1311 | 297.2389 | 299.2314 | 291.8671 | accept |
| Lady | 252.1421 | 289.1563 | 301.4568 | 280.9184 | accept |
| Images | Input | Cipher | ||||
|---|---|---|---|---|---|---|
| H | V | D | H | V | D | |
| Jet | 0.9231 | 0.9568 | 0.9425 | 0.0002 | −0.0024 | 0.0026 |
| House | 0.9654 | 0.9452 | 0.9624 | −0.0019 | 0.0001 | 0.0029 |
| Barbara | 0.9568 | 0.9214 | 0.8745 | 0.0017 | −0.0020 | 0.0047 |
| Baboon | 0.8469 | 0.8456 | 0.8989 | 0.0021 | 0.0011 | 0.0011 |
| pepper | 0.8548 | 0.8791 | 0.9399 | 0.0004 | 0.0019 | 0.0003 |
| Lady | 0.9269 | 0.9765 | 0.9578 | 0.0023 | 0.0041 | 0.0014 |
| Methods | Input | Cipher | ||||
|---|---|---|---|---|---|---|
| H | V | D | H | V | D | |
| Proposed | 0.9123 | 0.9207 | 0.9293 | 0.0008 | 0.0004 | 0.0021 |
| Ref. [10] | 0.9473 | 0.9544 | 0.9122 | 0.0010 | 0.0017 | 0.0125 |
| Ref. [13] | 0.9326 | 0.9624 | 0.9097 | 0.0035 | −0.0040 | −0.0410 |
| Ref. [19] | 0.9487 | 0.8994 | 0.8734 | 0.0000 | 0.0004 | −0.0009 |
| Ref. [20] | 0.9677 | 0.9829 | 0.9532 | 0.0719 | −0.3188 | −0.0017 |
| Images | MSE | PSNR | SSIM | ||||||
|---|---|---|---|---|---|---|---|---|---|
| R | G | B | R | G | B | R | G | B | |
| Jet | 8.145 | 7.547 | 7.128 | 0.002 | 0.005 | 0.005 | |||
| House | 8.254 | 8.548 | 8.489 | 0.001 | 0.000 | 0.001 | |||
| Barbara | 8.189 | 9.512 | 8.178 | 0.009 | 0.006 | 0.008 | |||
| Baboon | 6.235 | 7.249 | 6.954 | 0.006 | 0.001 | 0.003 | |||
| Pepper | 9.517 | 8.865 | 8.562 | 0.002 | 0.000 | 0.002 | |||
| Baboon | 7.214 | 9.121 | 8.128 | 0.001 | 0.002 | 0.001 | |||
| Images | NPCR | UACI | ||||||
|---|---|---|---|---|---|---|---|---|
| R Layer | G Layer | B Layer | Average | R Layer | G Layer | B Layer | Average | |
| Jet | 99.5832 | 99.6321 | 99.6154 | 99.6102 | 33.4425 | 33.3901 | 33.3956 | 33.4049 |
| House | 99.6039 | 99.6412 | 99.6423 | 99.6294 | 33.4213 | 33.3452 | 33.2845 | 33.3503 |
| Barbara | 99.6234 | 99.6481 | 99.6321 | 99.6345 | 33.3425 | 33.3614 | 33.3329 | 33.3456 |
| Baboon | 99.6231 | 99.5931 | 99.6548 | 99.6236 | 33.2956 | 33.2814 | 33.3621 | 33.3130 |
| Pepper | 99.6513 | 99.6059 | 99.6623 | 99.6398 | 33.2956 | 33.3521 | 33.3089 | 33.3188 |
| Lady | 99.5956 | 99.5759 | 99.5973 | 99.5896 | 33.4732 | 33.4623 | 33.3993 | 33.4449 |
| Methods | Image | NPCR | UACI |
|---|---|---|---|
| Proposed | Barbara | 99.6345 | 33.3456 |
| Ref. [7] | – | 30.4814 | |
| Ref. [9] | 99.2996 | 33.5844 | |
| Ref. [19] | 99.6220 | 33.5268 | |
| Ref. [10] | 99.5 | 33.3 |
| Images | Entropy | Average | ||
|---|---|---|---|---|
| R | G | B | ||
| Jet | 7.9978 | 7.9979 | 7.9978 | 7.9978 |
| Home | 7.9979 | 7.9977 | 7.9979 | 7.9978 |
| Barbara | 7.9979 | 7.9979 | 7.9979 | 7.9979 |
| Baboon | 7.9979 | 7.9978 | 7.9978 | 7.9978 |
| Pepper | 7.9976 | 7.9975 | 7.9977 | 7.9976 |
| Lady | 7.9975 | 7.9978 | 7.9975 | 7.9976 |
| Method | Image | Entropy |
|---|---|---|
| Ref. [7] | 7.9970 | |
| Ref. [9] | 7.9969 | |
| Ref. [10] | 7.9973 | |
| Ref. [19] | 7.9974 | |
| Ref. [20] | 5.3390 | |
| Proposed | Barbara (256 × 256) | 7.9979 |
| Images (256 × 256) | Entropy | PSNR | UACI |
|---|---|---|---|
| Home | 7.9982 | 7.4523 | 33.1245 |
| Barbara | 7.9979 | 7.1133 | 33.2814 |
| Baboon | 7.9979 | 6.1576 | 33.7852 |
| Pepper | 7.9983 | 7.4121 | 33.3089 |
| Average | 7.9983 | 7.4121 | 33.3089 |
| Ref. [7] | 7.9970 | 8.5777 | 30.4817 |
| Ref. [11] | – | 7.6568 | 34.0998 |
| Attacks | Image | PSNR | SSIM |
|---|---|---|---|
| Salt & pepper | |||
| Intensity = 0.01 | Baboon | 24.2459 | 0.8756 |
| Intensity = 0.02 | – | 21.2134 | 0.7245 |
| Intensity = 0.01 | Lady | 22.5689 | 0.7423 |
| Intensity = 0.02 | – | 17.6542 | 0.6359 |
| Gaussian | |||
| Variance = 0.001 | Baboon | 17.1245 | 0.6235 |
| Variance = 0.002 | – | 15.5478 | 0.5932 |
| Variance = 0.001 | Lady | 14.5687 | 0.4851 |
| Variance = 0.002 | – | 12.5645 | 0.4315 |
| Occlusion attack | |||
| Occlude = 9% | Lena | 28.1214 | 0.8932 |
| Occlude = 20% | – | 22.2547 | 0.7532 |
| Occlude = 18% | – | 23.3265 | 0.7589 |
| Occlude = 25% | – | 18.6549 | 0.6489 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lone, P.N.; Singh, D.; Stoffová, V.; Mishra, D.C.; Mir, U.H.; Kumar, N. Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher. Mathematics 2022, 10, 3878. https://doi.org/10.3390/math10203878
Lone PN, Singh D, Stoffová V, Mishra DC, Mir UH, Kumar N. Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher. Mathematics. 2022; 10(20):3878. https://doi.org/10.3390/math10203878
Chicago/Turabian StyleLone, Parveiz Nazir, Deep Singh, Veronika Stoffová, Deep Chandra Mishra, Umar Hussain Mir, and Neerendra Kumar. 2022. "Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher" Mathematics 10, no. 20: 3878. https://doi.org/10.3390/math10203878
APA StyleLone, P. N., Singh, D., Stoffová, V., Mishra, D. C., Mir, U. H., & Kumar, N. (2022). Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher. Mathematics, 10(20), 3878. https://doi.org/10.3390/math10203878






