3.1. Partial Key Exposure Attack on CRT-RSA
Recently, May, Nowakowski, and Sarkar [
23] proposed an improved partial key exposure attack on CRT-RSA, which is based on the small CRT exponent attack working for
of [
18]. This attack applies to the range
, which smoothly covers the full interval of the CRT exponents. Let
be the CRT-RSA modulus, where
p and
q are prime numbers of the same bit-size. Assume that the public exponent is
, the CRT-exponents are
. The CRT-exponents can be written as
, where
and the LSB components
are known, whereas the MSB components
are unknown. Then, there exists a polynomial-time algorithm that outputs the secret information
using the given partial key exposure.
According to
and
, we have
for two positive integers
. Since the sizes of
e,
,
,
p, and
q are known, the upper bounds on
k and
ℓ are estimated as
Applying the Formula (
4), we have
, whose root is
. In addition, multiplying the Formula (
5) by
p and rearranging it gives
Similarly, we have
, whose root is
. Moreover, the Equations (
4) and (
5) can be rewritten as
and
. Multiplying them together gives
, and we obtain
Therefore, we have
, whose root is
. Combining the above modular polynomials, we obtain the following system of polynomial equations,
Their common root is
.
Considering the special algebraic relationship between the unknown variables, we use six variables, namely
instead of three variables. In this case, the relevant elements in certain monomials of the original polynomials need to be converted algebraically as follows.
Thus, we obtain linear polynomials after the conversion,
Combining known values
and
, the polynomials involved in the partial key exposure attack are as follows.
The root is , and the corresponding upper bounds are and .
We apply the lattice-based method to extract . The first step is to construct the shift polynomials. Before that, we need to define the monomial set, whose elements are contained in the shift polynomials. The monomial set is closely related to the columns of the lattice basis matrix in the second step, and directly affects the alignment of the matrix rows.
Definition 4. Let . The monomial set is defined asTo facilitate the exposition of the lattice construction, it is additional to define asFurthermore, is partitioned using five disjoint subsets as follows. The shift functions and the corresponding shift polynomials are defined based on the monomial sets and .
Definition 5. The shift functions are defined as follows. For a given monomial , the corresponding shift polynomial is determined as It is known that all the shift polynomials
have the common root
. The shift polynomials are further adapted by using the algebraic relation Formula (
7). We construct the updated shift polynomials under the following induced transformation rules.
Definition 6. Let u be a polynomial defined over . is defined as the updated polynomial after the following transformation rules.
- 1.
For all monomials, are converted to N,
- 2.
For monomials without , are converted to and are converted to ,
- 3.
For monomials with , are converted to and are converted to .
Thus, contains only monomials of the form and , i.e., variables with subscripts p and q do not appear in a monomial at the same time.
The second step is to construct the lattice-basis matrix . To do this, we need to define the monomial order and the polynomial order, which are used to arrange the order of columns and rows in the lattice-basis matrix. When we generate the lattice-basis matrix, a polynomial is first multiplied by some extra variables and then transformed by Definition 6. Finally, the upper bounds on the unknown variables are substituted and the polynomials are arranged in a one-to-one correspondence with the monomial order.
Definition 7. The monomial order is defined as follows. The lattice basis matrix and the polynomial order (namely the matrix row) are defined in the following way. The i-th column is related to the monomial , which is for even b and for odd b. The parameters are taken from the i-th smallest monomial in . For , the i-th row is associated with the coefficient vector of polynomial . For with even b, the i-th row takes . For with odd b, it takes . Then the lattice basis matrix is lower triangular.
We then apply the lattice reduction algorithm to generated by the basis matrix . The first few approximately shortest basis vectors of the output are converted to polynomial form , which make up the system of integer equations . The third step is to solve the above system of integer equations. We apply the Gröbner basis computation to extract . At this point, we finally obtain the secret information p and q. Under the above lattice-based solution process, we present the following theorem.
Theorem 2. Let be a sufficiently large CRT-RSA modulus, where p and q are prime numbers of the same bit-size. Assume that the public exponent is , the CRT exponents are . The CRT exponents are written as and , where and the LSB components are known, whereas the MSB components are unknown. Then given and ensuring , if the conditionholds then p and q can be computed in polynomial time in . Proof. We construct the lattice-basis matrix
and generate the
-dimensional full-rank lattice
. Hence, each diagonal element
of
contains the powers of
,
X,
Y, and
N,
, which are expressed as
To simplify the computation of the lattice determinant, we should multiply the polynomials of the rows by the following appropriate multiplicative inverse
to eliminate the effect of powers of
N and
. The updated diagonal elements are
. Meanwhile, the root solution remains
. Since it is assumed that
in the most favorable case, its influence can be ignored. The lattice determinant is calculated asymptotically as
, where the corresponding exponents are calculated as follows.
On the other hand, the dimension of the lattice
is
We apply the condition (
3), i.e.,
. By substituting
,
,
and
, we have
After simplification, we obtain . The running time mainly depends on the LLL algorithm, while the running time of the Gröbner basis computation is negligible in comparison. Thus, its time complexity is . Because m is a fixed number for generating the lattice, the time complexity is polynomial in . □
We elaborate on the details of the lattice-basis matrix in the partial key exposure attack on CRT-RSA and present the specific attack algorithm. Furthermore, to understand Theorem 2 and the order of columns and rows in the lattice construction more intuitively, we give a toy example of the lattice basis matrix for .
Example 1. According to Definition 7, the lattice basis matrix for is shown in Table 1, where and are the derived polynomials to be solved. It is clear that the lattice basis matrix is indeed a lower triangular matrix, and that each new shift polynomial introduces only one new monomial .
We present the partial key exposure attack on CRT-RSA in Algorithm 1, which is denoted by
.
| Algorithm 1 The partial key exposure attack algorithm . |
- Input:
CRT-RSA modulus N, public exponent e, and known LSBs - 1:
- 2:
- 3:
|
- 4:
| {construct the monomial set} |
- 5:
| {generate shift exponents} |
- 6:
|
- 7:
| {generate the lattice basis matrix} |
- 8:
| {compute reduced basis vectors} |
- 9:
| {construct the equation system} |
- 10:
| {extract the desired root} |
- 11:
return p and q - Output:
The factorization of
|
3.2. Polynomial Time Equivalence of Computing the CRT-RSA Secret Key and Factoring
We show an explicit demonstration on the polynomial-time equivalence of computing the CRT-RSA secret key and factoring by invoking the partial key exposure attack algorithm . It is specified in the following theorem.
Theorem 3. Let be a sufficiently large CRT-RSA modulus, where p and q are prime numbers of the same bit size. Let e be the public exponent and be the corresponding CRT-exponents. Then the following statements hold under the condition and ensuring .
Given , and can be computed in polynomial time,
Given , p and q can be computed in polynomial time.
When is close to the CRT-RSA modulus, the CRT-exponents satisfies the natural constraint (or ).
Note that the error term
is derived from the proof of Theorem 2. To simplify the lattice determinant computation, we multiply each row polynomial by an appropriate multiplicative inverse, i.e., (
11) to eliminate the effect of powers of
N and
. However,
is at least equal to 2 and hence its influence cannot be completely eliminated. We further check whether the assumption
holds in
Section 4. From an algorithmic perspective, this error term
affects the computation efficiency. To achieve the same attacking effect, a larger error term requires lattices with higher dimension and hence the corresponding factoring attack takes more time.
Proof. We divide the proof into two parts. One part proves that knowing
is sufficient to compute
and
in polynomial time. The other part proves that known
is sufficient to compute
p and
q in polynomial time. According to the key generation algorithm, we have
,
. When
is known, the values of
and
can be computed by applying the extended Euclidean algorithm. It is shown in Algorithm 2 and denoted by
.
| Algorithm 2 The CRT-RSA key computation algorithm |
- Input:
CRT-RSA public exponent e, modulus factorization p and q - 1:
- 2:
- 3:
whiledo - 4:
- 5:
- 6:
- 7:
end while - 8:
- 9:
- 10:
whiledo - 11:
- 12:
- 13:
- 14:
end while - 15:
return and - Output:
CRT-exponents and
|
It is known that the time complexity of the modular inverse computation is , so the CRT-RSA secret key computation algorithm can be done in polynomial time. To prove that knowing is sufficient to compute p and q in polynomial time, we slightly modify the original problem into the form of the partial key exposure attack on CRT-RSA. Denoting and letting , we have leaked LSBs . By calling the partial key exposure attack algorithm , we can extract p and q in polynomial time. The specific algorithm is shown in Algorithm 3 and denoted by .
| Algorithm 3 The CRT-RSA modulus factorization algorithm |
- Input:
CRT-RSA modulus N, public exponent e, CRT-exponents and - 1:
- 2:
- 3:
- 4:
- 5:
- 6:
|
- 7:
| {construct the monomial set} |
- 8:
| {generate shift exponents} |
- 9:
|
- 10:
| {generate the lattice basis matrix} |
- 11:
| {compute reduced basis vectors} |
- 12:
| {construct the equation system} |
- 13:
| {extract the desired root} |
- 14:
return p and q - Output:
The factorization of
|
The time complexity of the CRT-RSA modulus factorization algorithm depends mainly on the partial key exposure attack, which can be done in
according to Theorem 2. Thus,
runs in polynomial time in
. However, Algorithm 3 partially answers the research problem. It remains to show that the CRT exponents satisfy the natural constraint, i.e.,
for
. For this purpose, we further apply the judgment condition (
10) in Theorem 2. Assume that
,
,
, the partial key exposure attack on CRT-RSA works if
In Algorithm 3, we have the implication
, which shows that
Hence, it follows that
, i.e.,
. The CRT-RSA modulus factorization algorithm
is feasible for
, and the CRT-exponents are in the range of
. So far, our research goal is achieved. □
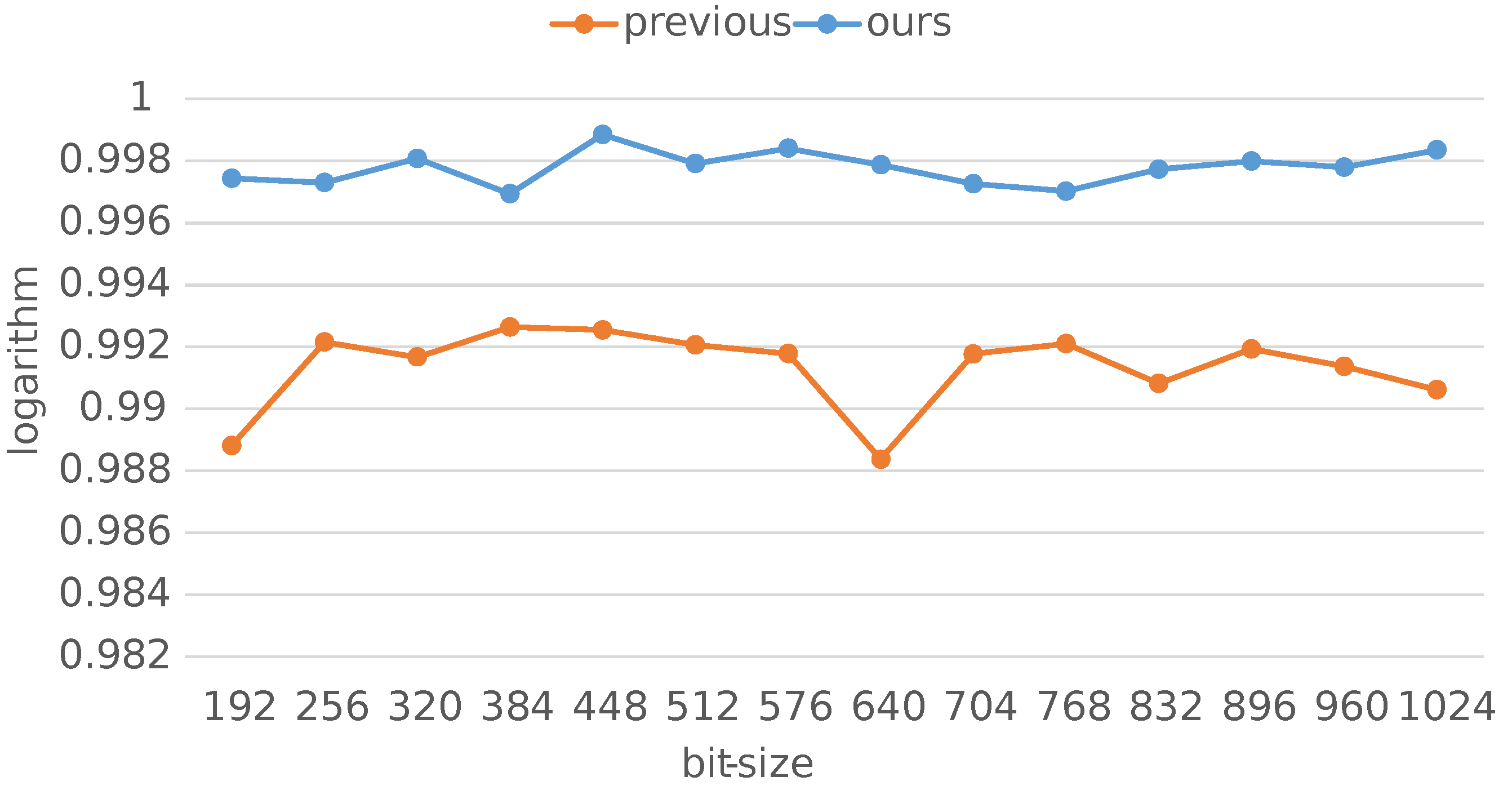
3.3. Validation Experiments
We implement the CRT-RSA key computation algorithm
and the CRT-RSA modulus factorization algorithm
based on SageMath [
36]. The experimental platform is a personal computer running Windows 10 with Intel(R) Core(TM) i5-10500 CPU 3.10 GHz and 8 GB RAM. All numbers in the validation experiments are randomly selected. We summarize the experimental results as follows. The CRT-RSA key computation algorithm
outputs the modular inverse values
and
quite efficiently. The CRT-RSA modulus factorization algorithm
runs with enough integer equations for solving the unknown variables and finally factors the modulus
N. To be specific, after running the LLL algorithm, we can obtain a sufficient number of approximately shortest basis vectors to meet the requirements in the lattice-based method. The desired root can be efficiently extracted by transforming the lattice vectors into a system of integer equations and then applying the Gröbner basis computation.
As the CRT-RSA key computation algorithm is a direct call to the extended Euclidean algorithm, we focus on the CRT-RSA modulus factorization algorithm. In the experiments, we first choose an appropriate m to control the construction of the shift polynomials. We then construct the lattice basis matrix and the -dimensional full-rank lattice . The LLL algorithm is applied to , and we transform the first few output vectors into a system of integer equations. We finally solve the system of integer equations using the Gröbner basis computation and extract the desired root.
The detailed experimental results are given in
Table 2. The
column provides the bit size of the CRT-RSA modulus of the generated instance. The
column provides the bit size of the public exponent
e. The
column provides the bit size of the CRT exponents in our attacks. The lattice settings for conducting the factoring algorithms are indicated by the
m and
columns. The time consumption (recorded in seconds) of the LLL algorithm and the Gröbner basis computation are given in the Time-column. Two particular numerical CRT-RSA examples are given in Examples 2 and 3.
Example 2. In order to check the correctness and validity of the CRT-RSA modulus factorization algorithm, we choose the following specific parameters and generate the test example.
- 1.
Randomly generate 512-bit prime numbers p, q and the modulus ,
- 2.
Randomly generate 103-bit CRT exponents and ,
- 3.
Generate the public exponent e based on above p, q and , ,
- 4.
Denote the CRT-RSA key information as .
The values of the numerical CRT-RSA example are as follows. In the CRT-RSA modulus factorization algorithm , we choose , which means that we need to apply the LLL algorithm to the lattice with . After running for almost 84221
s, the approximately shortest basis vectors that meet the solvable condition are obtained. The system of integer equations to be solved is then derived by transforming vectors into polynomials. We finally solve it by applying the Gröbner basis computation in less than one second and recover One may check that does hold, so the CRT-RSA modulus factorization algorithm successfully outputs the factorization of .
To show that the CRT-RSA key computation algorithm also runs in polynomial time, we use the above CRT-RSA example and apply extended Euclidean algorithm. It runs in less than one second and outputs Example 3. In order to further check the correctness and validity of the CRT-RSA modulus factorization algorithm for smaller e and larger CRT exponents, we choose the following specific parameters and generate the test example.
- 1.
Randomly generate 512-bit prime numbers p, q, and the modulus ,
- 2.
Randomly generate 200-bit public exponent e,
- 3.
Generate 768-bit CRT-exponents and based on above p, q, and e,
- 4.
Denote the CRT-RSA key information as .
The values of the numerical CRT-RSA example are as follows. In the CRT-RSA modulus factorization algorithm , we choose , which means that we need to apply the LLL algorithm to the lattice with . After running for almost 2482
s, the approximately shortest basis vectors that meet the solvable condition are obtained. The system of integer equations to be solved is then derived by transforming vectors into polynomials. We finally solve it by applying the Gröbner basis computation in less than one second and recover One may check that does hold, so the CRT-RSA modulus factorization algorithm successfully outputs the factorization of .
To show that the CRT-RSA key computation algorithm also runs in polynomial time, we use the above CRT-RSA example and apply extended Euclidean algorithm. It runs in less than one second and outputs and .